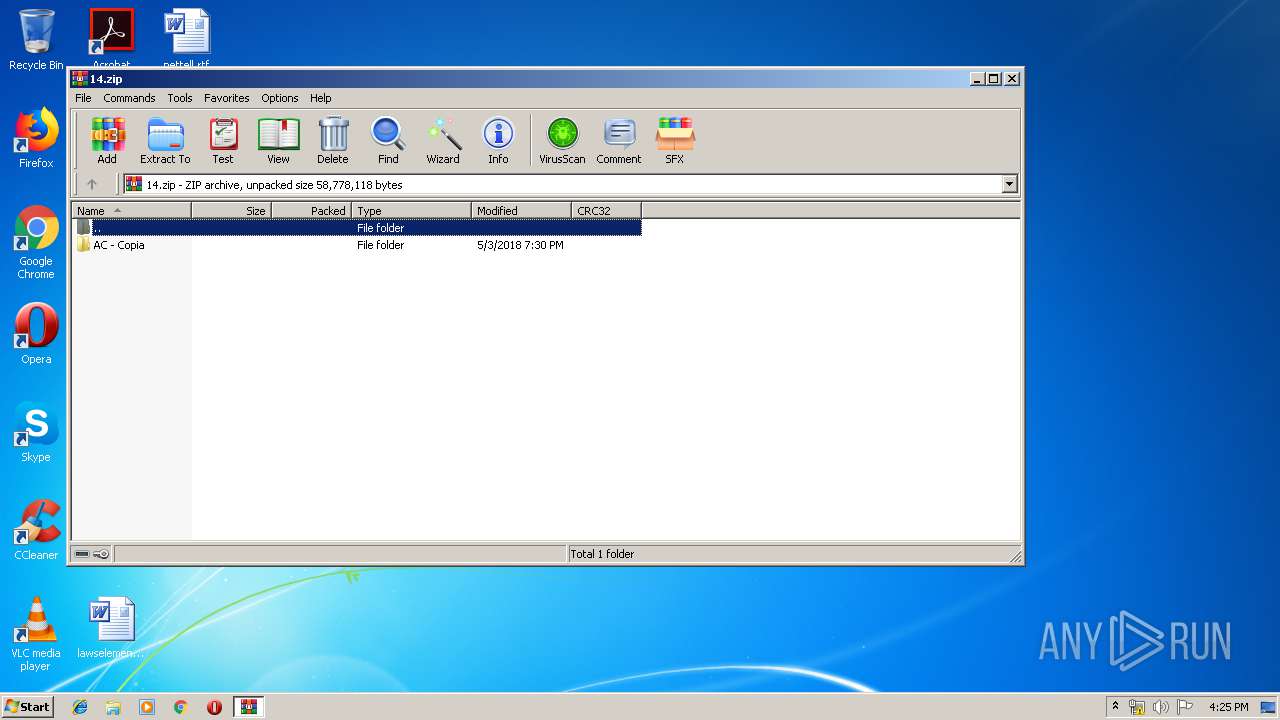
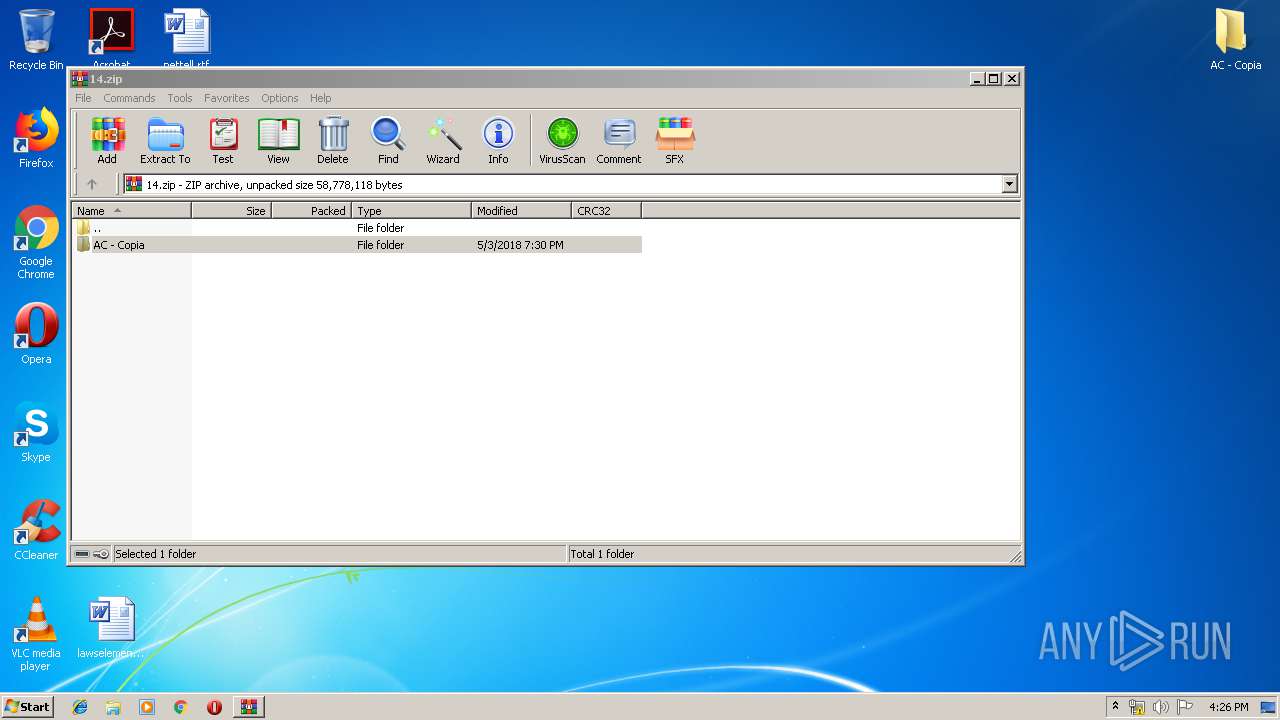
| File name: | 14.zip |
| Full analysis: | https://app.any.run/tasks/8a4a1900-8331-497a-9912-874ef8b3f776 |
| Verdict: | Malicious activity |
| Analysis date: | May 13, 2019, 15:25:22 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 67A23874609513C37B82972C518B3935 |
| SHA1: | 2DA5E8AD4E64AE2EE132DC6A7E89BCA66605A4DC |
| SHA256: | B5921C16AF5991C5061ADAFE2B11544BEFBCD348A3D632966C7B0E84A2687279 |
| SSDEEP: | 393216:nAu58kO6RxHncoG8zqBvUzgriXablOazIKBZOMk5DhjwT:nAgRxwHvUNXabl7zLk5DhUT |
MALICIOUS
Loads dropped or rewritten executable
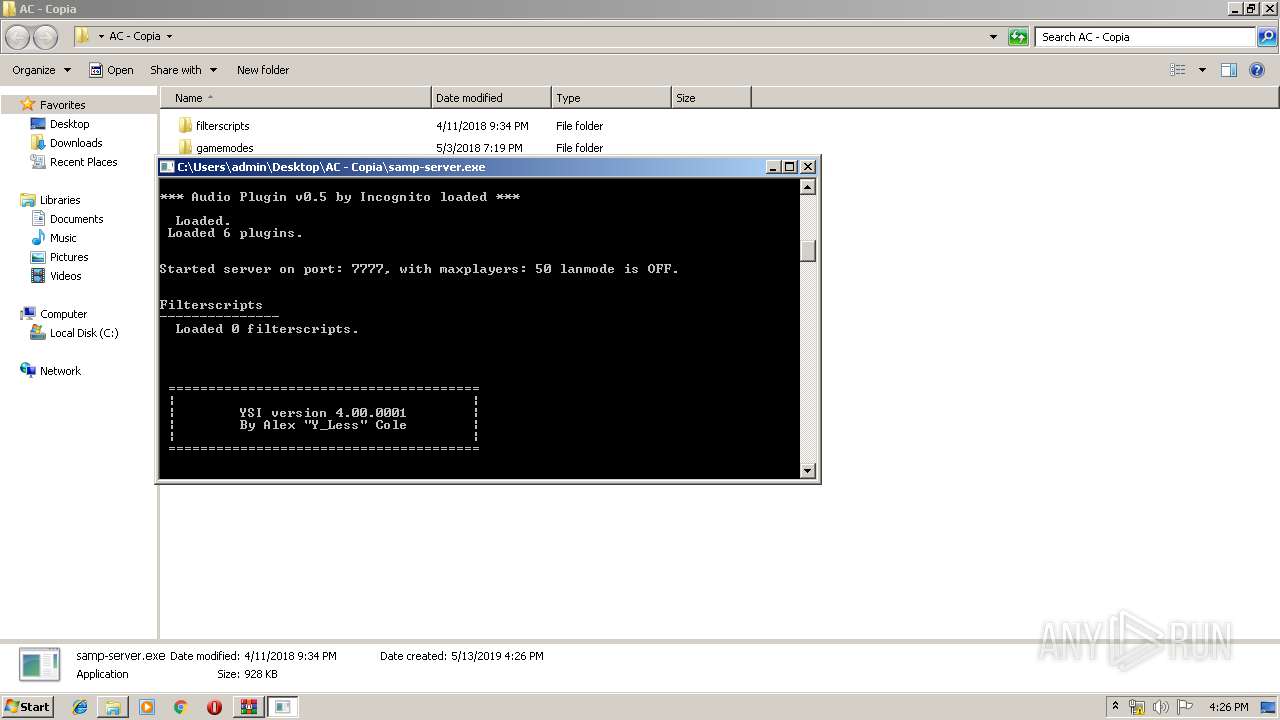
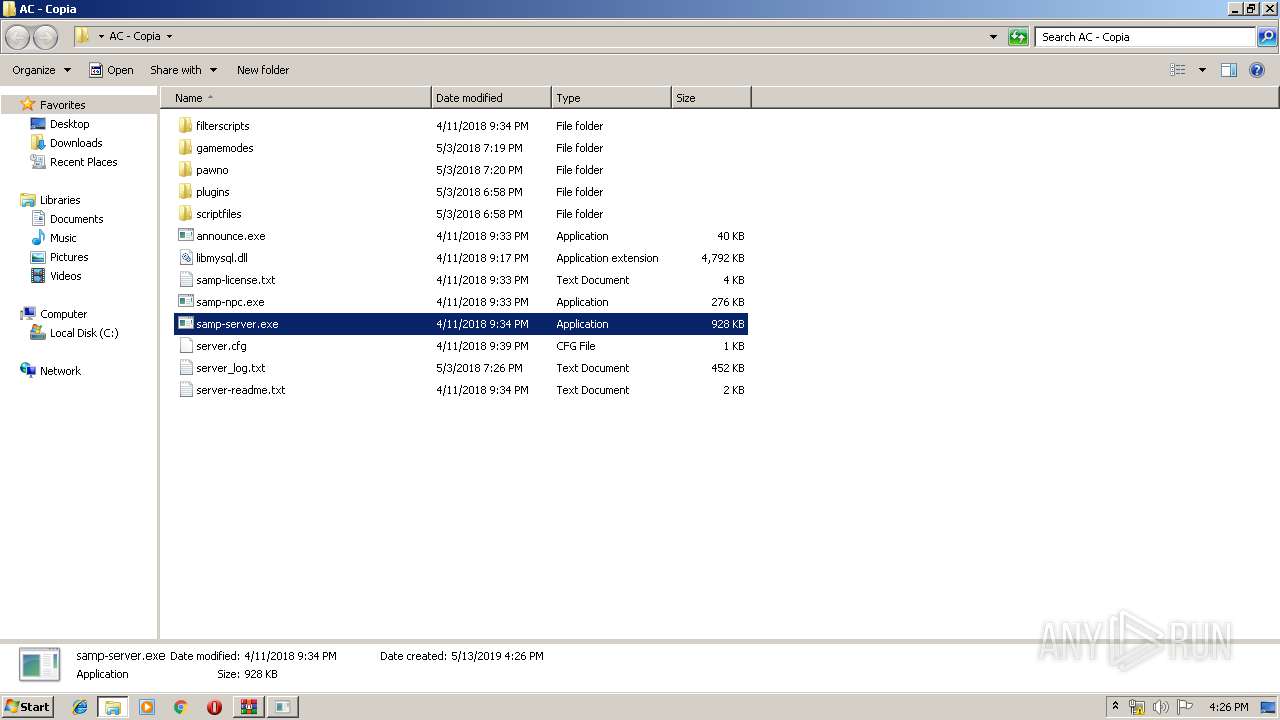
- samp-server.exe (PID: 1732)
- explorer.exe (PID: 116)
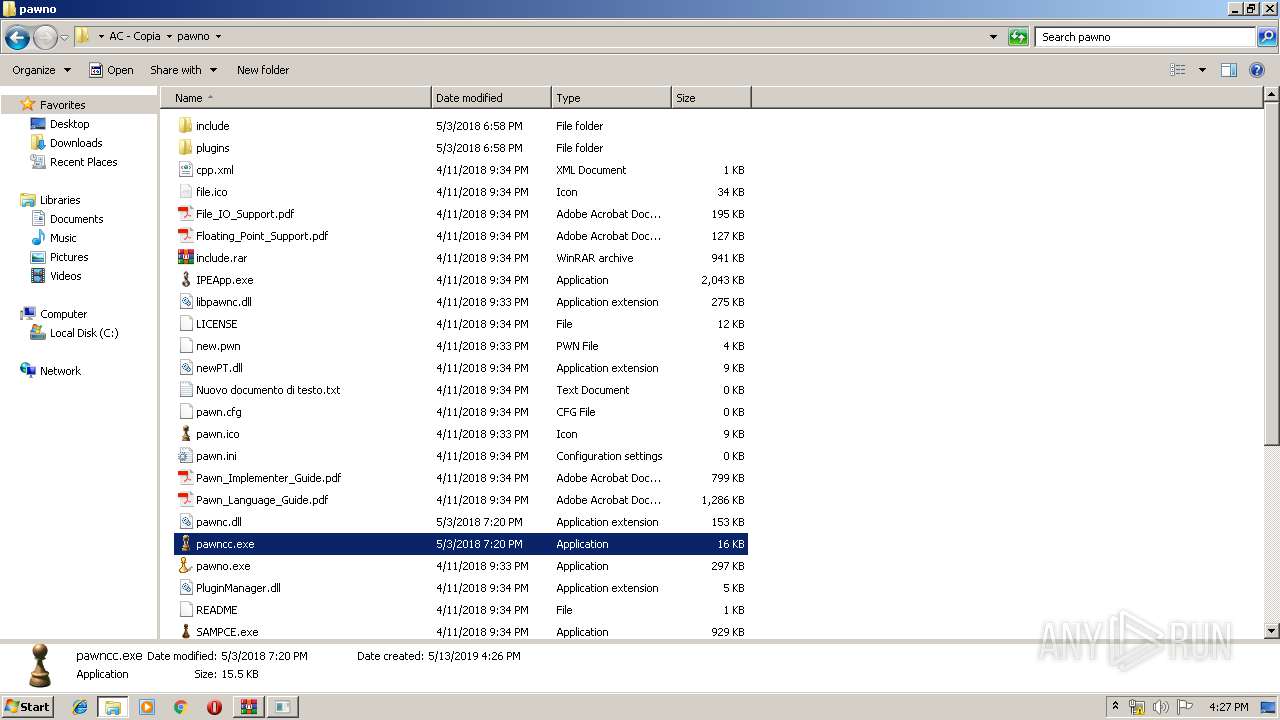
- pawncc.exe (PID: 3080)
- SAMPCE.exe (PID: 3700)
- SearchProtocolHost.exe (PID: 2044)
Application was dropped or rewritten from another process
- samp-server.exe (PID: 1732)
- samp-npc.exe (PID: 3884)
- announce.exe (PID: 1396)
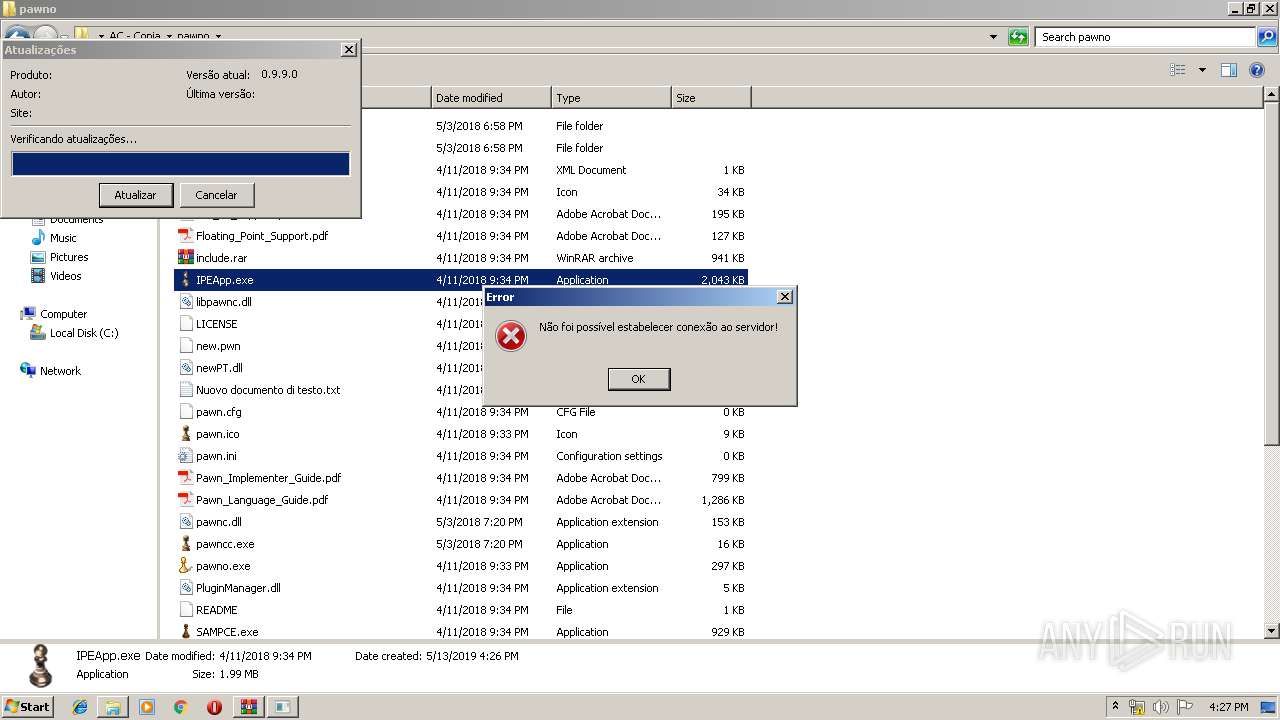
- IPEApp.exe (PID: 3828)
- pawncc.exe (PID: 3080)
- pawno.exe (PID: 1936)
- SAMPCE.exe (PID: 3700)
SUSPICIOUS
Reads Internet Cache Settings
- explorer.exe (PID: 116)
Creates files in the user directory
- explorer.exe (PID: 116)
- notepad++.exe (PID: 864)
Executable content was dropped or overwritten
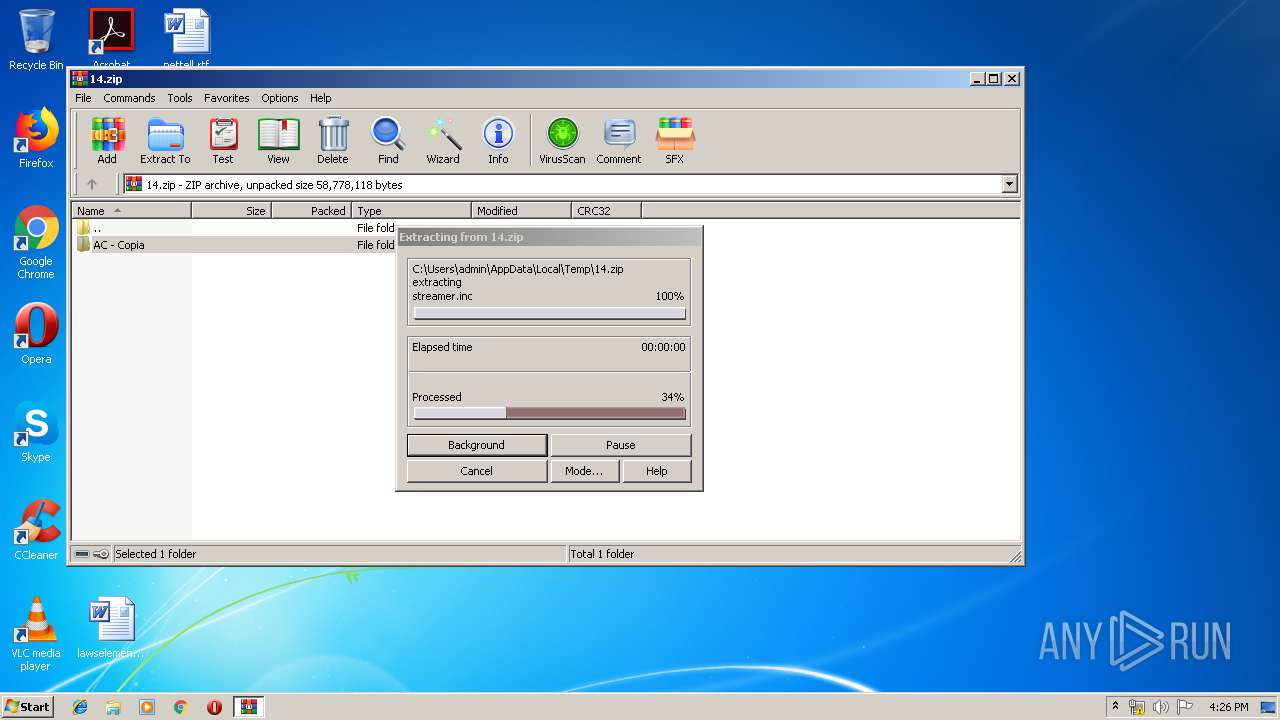
- WinRAR.exe (PID: 1872)
INFO
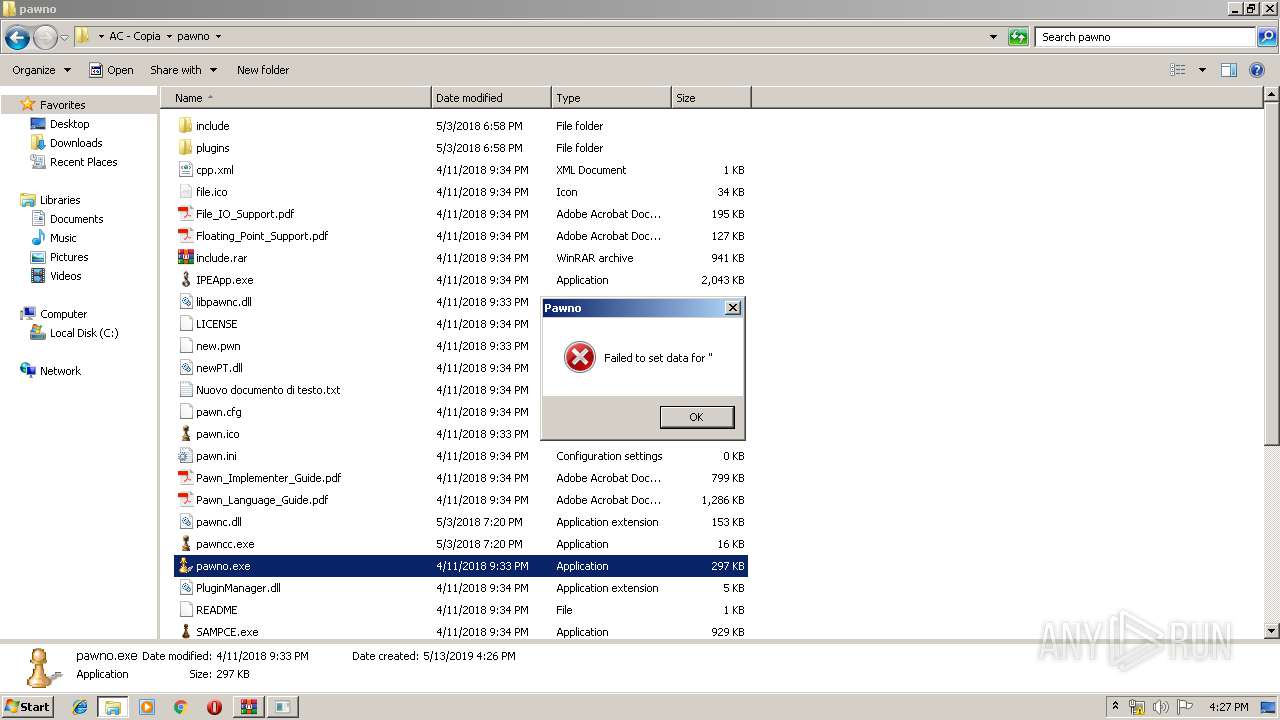
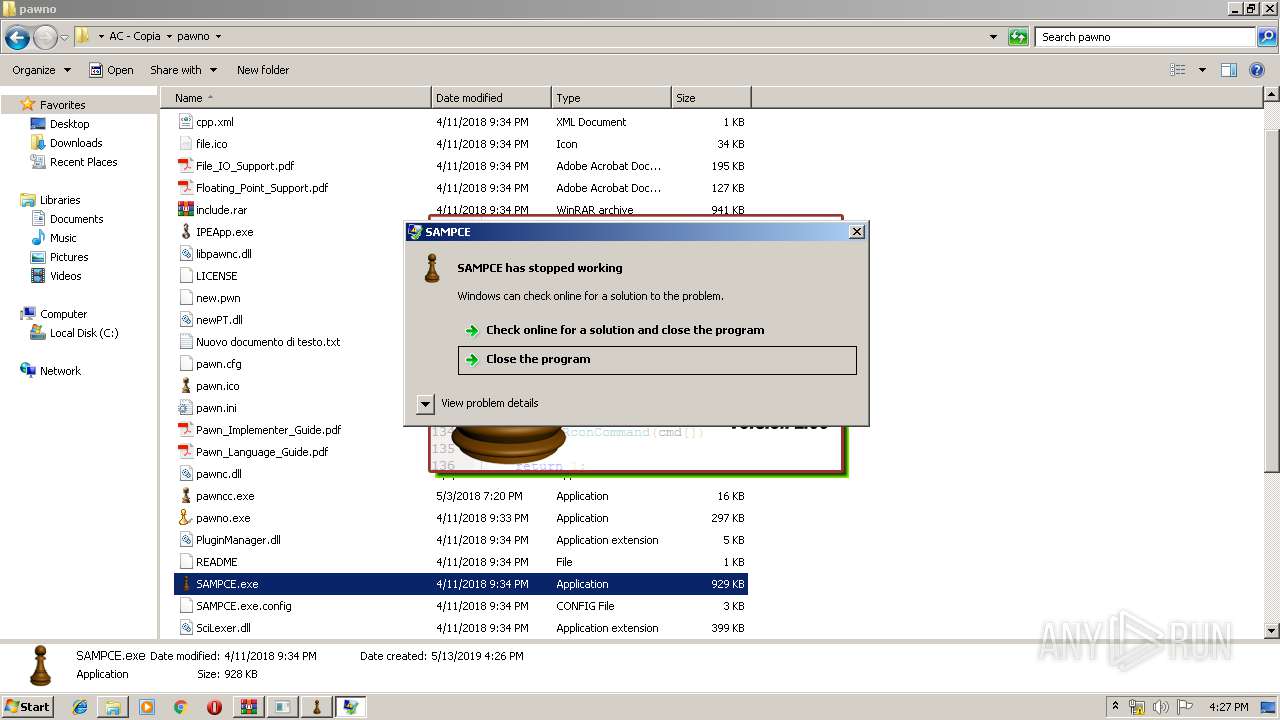
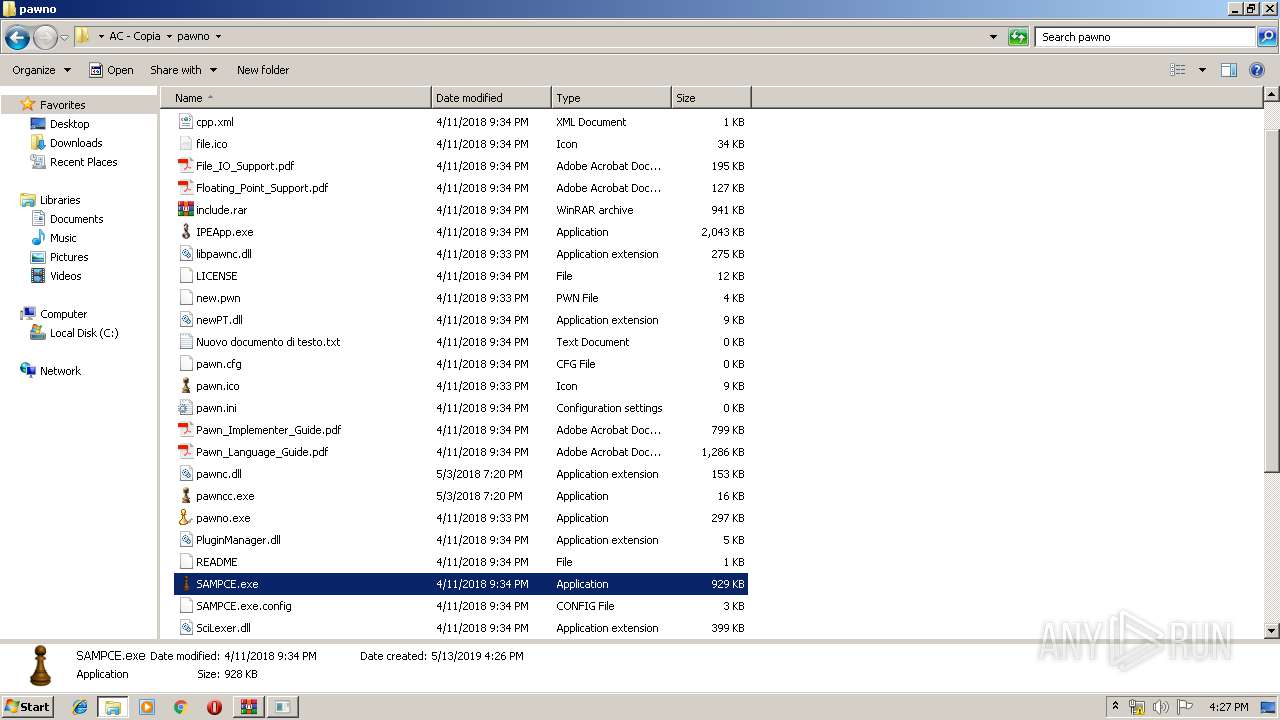
Application was crashed
- SAMPCE.exe (PID: 3700)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2018:05:03 20:30:05 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
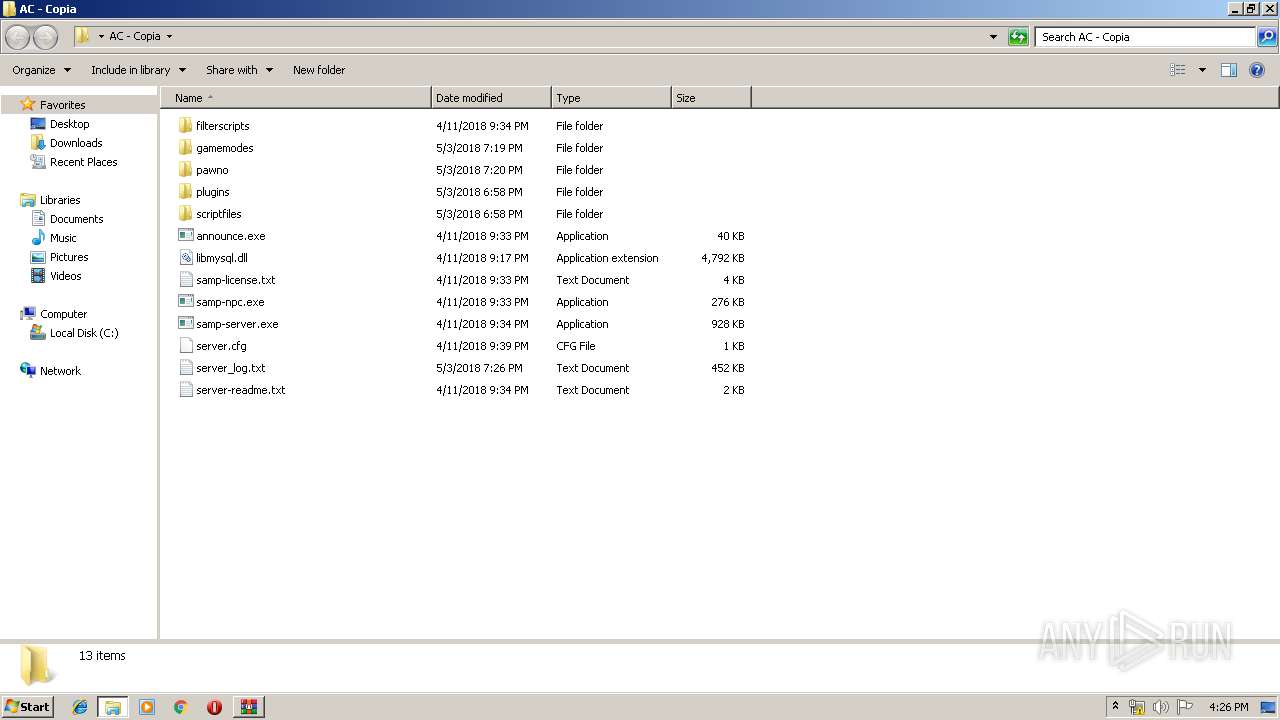
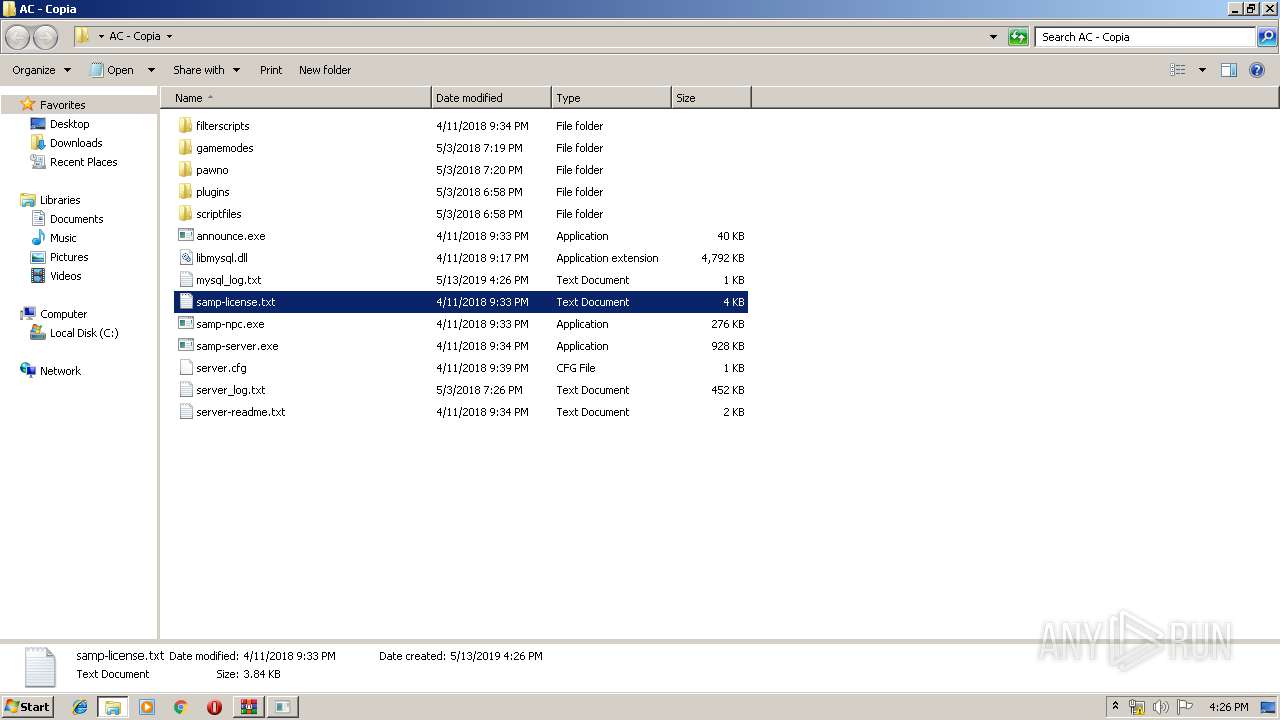
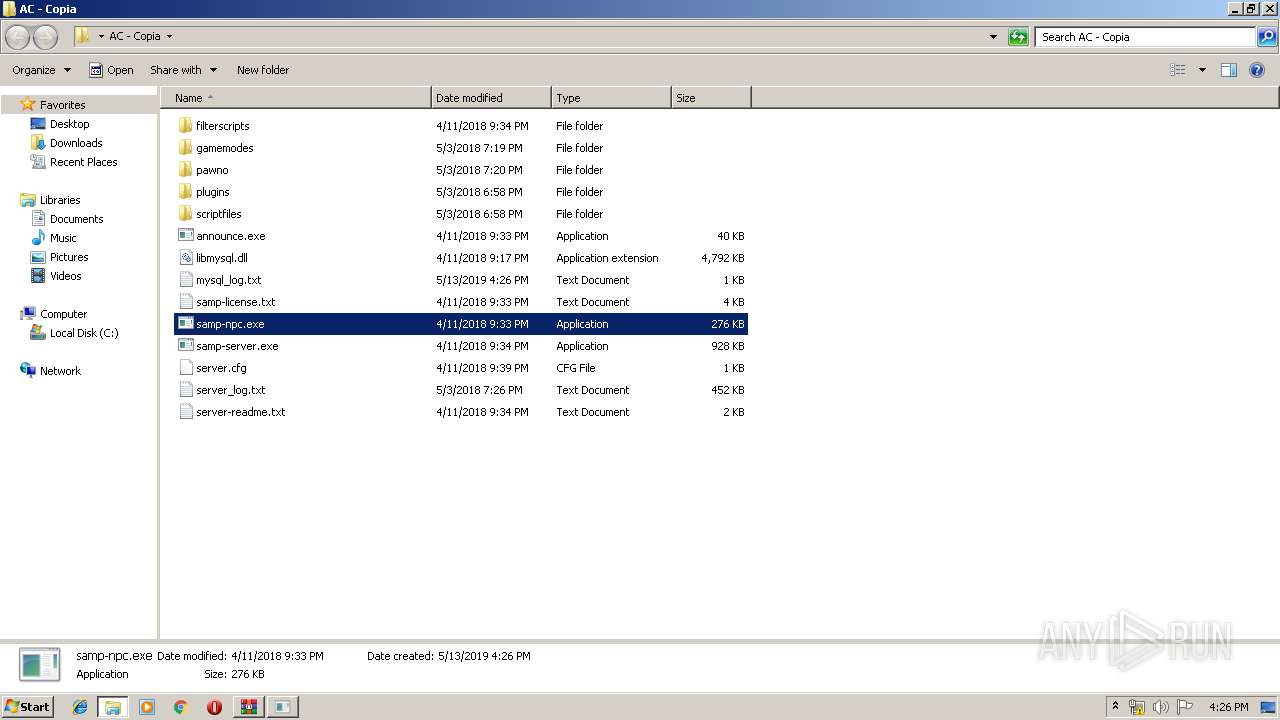
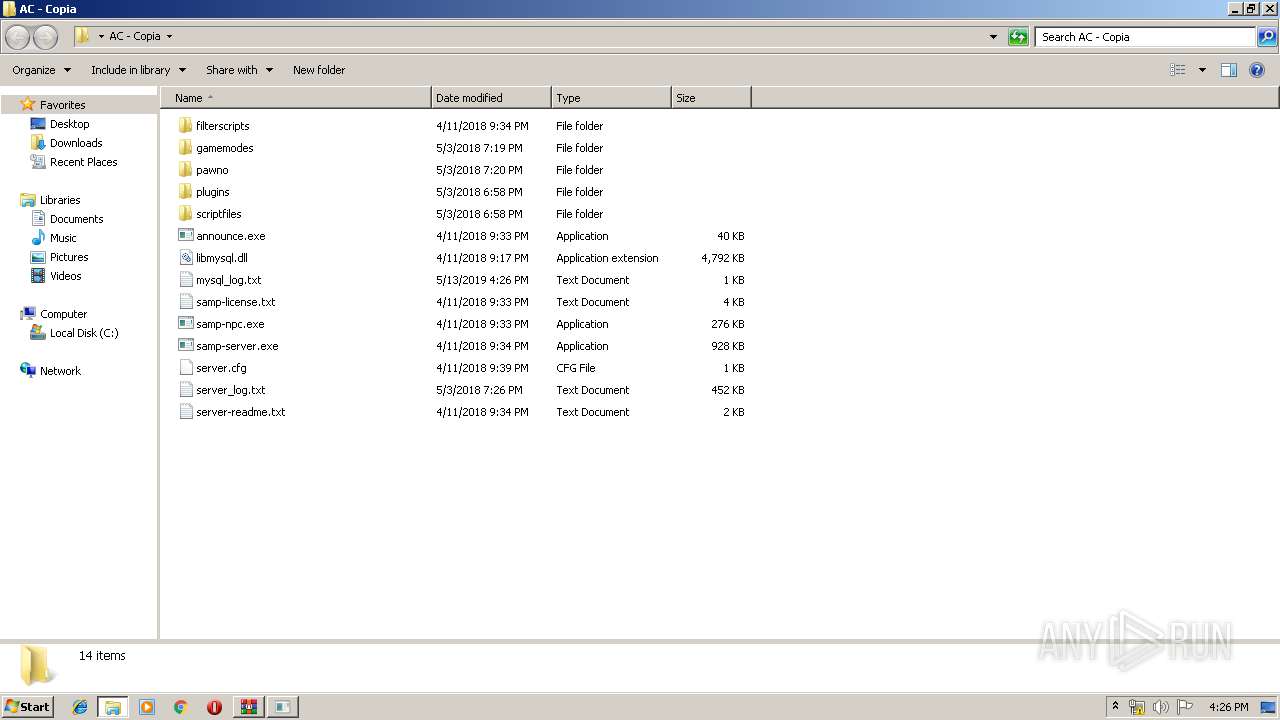
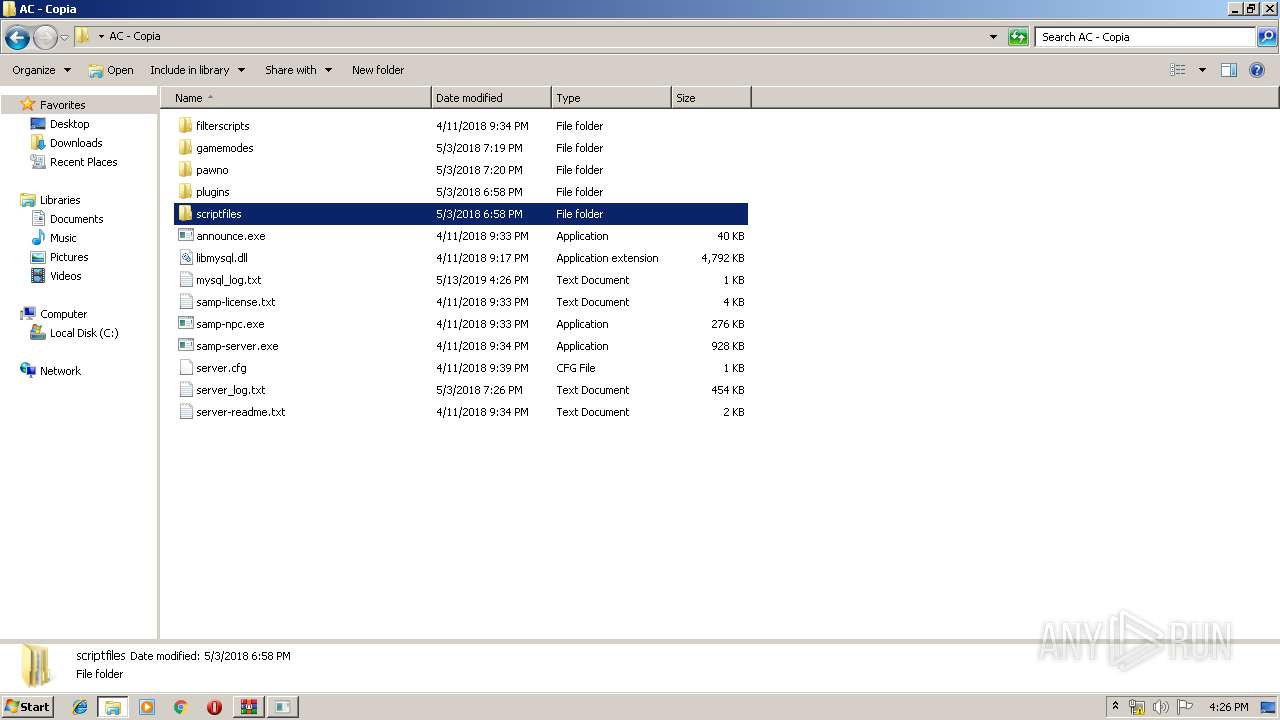
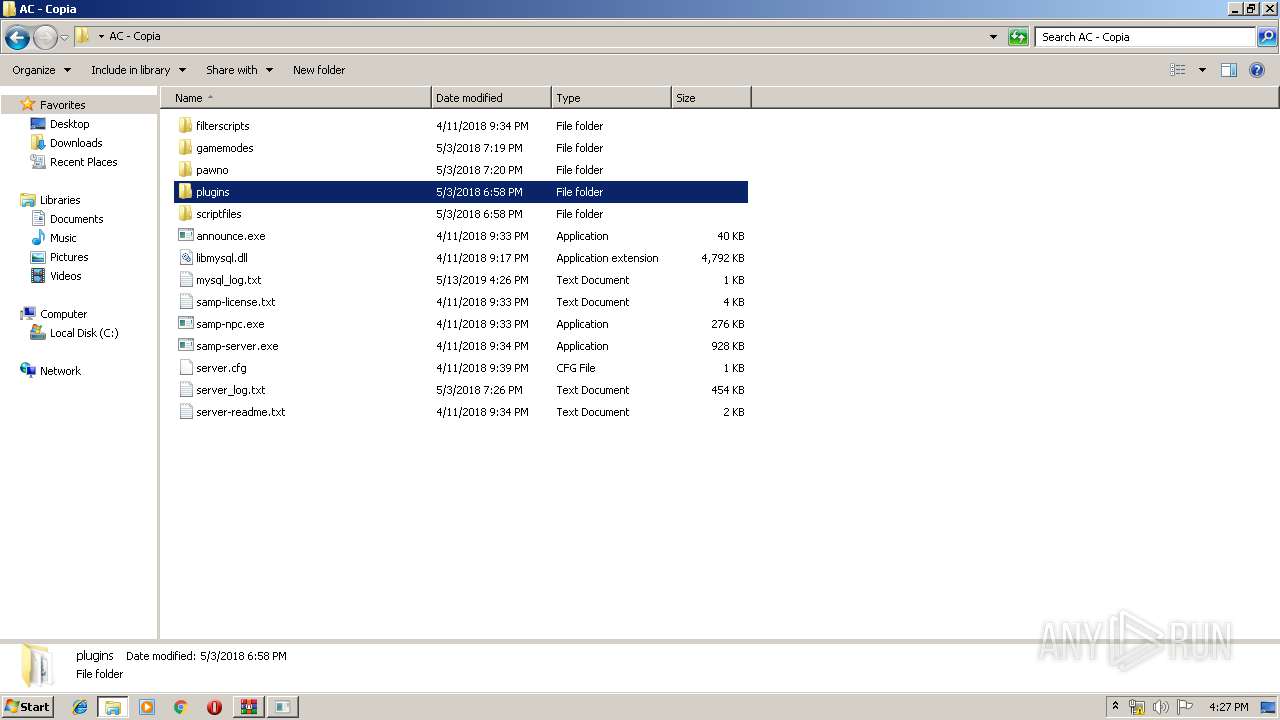
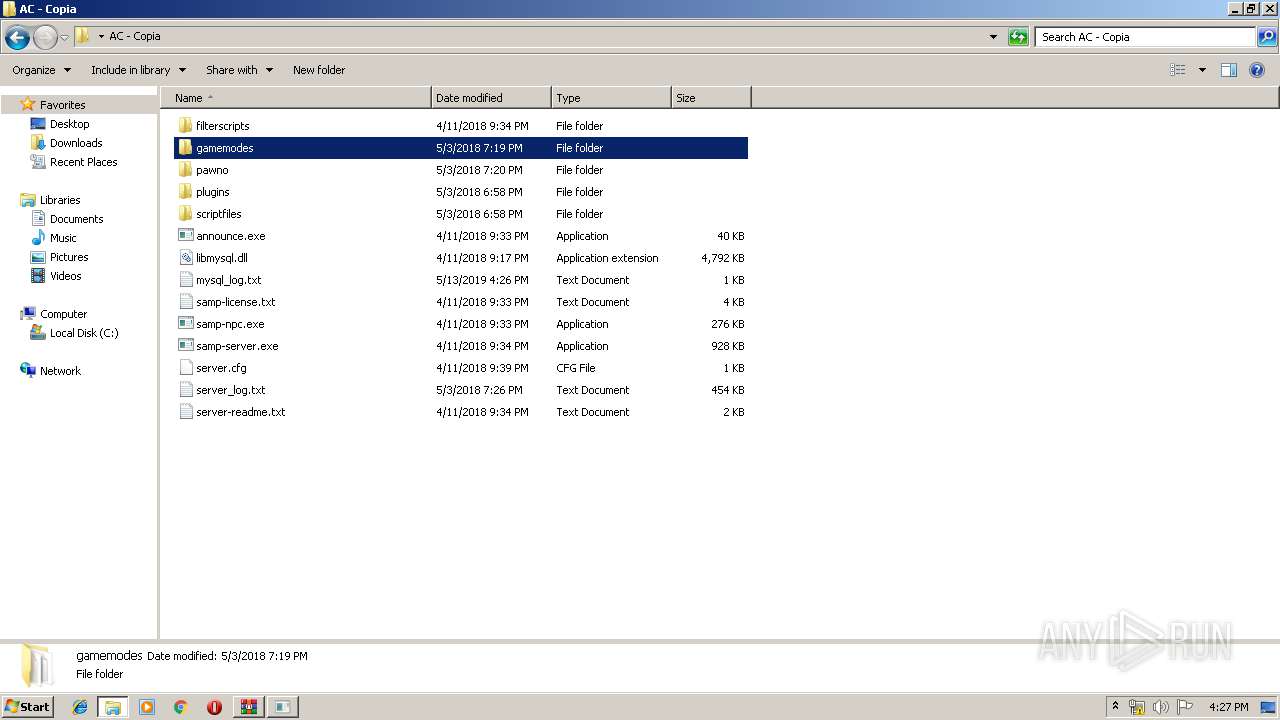
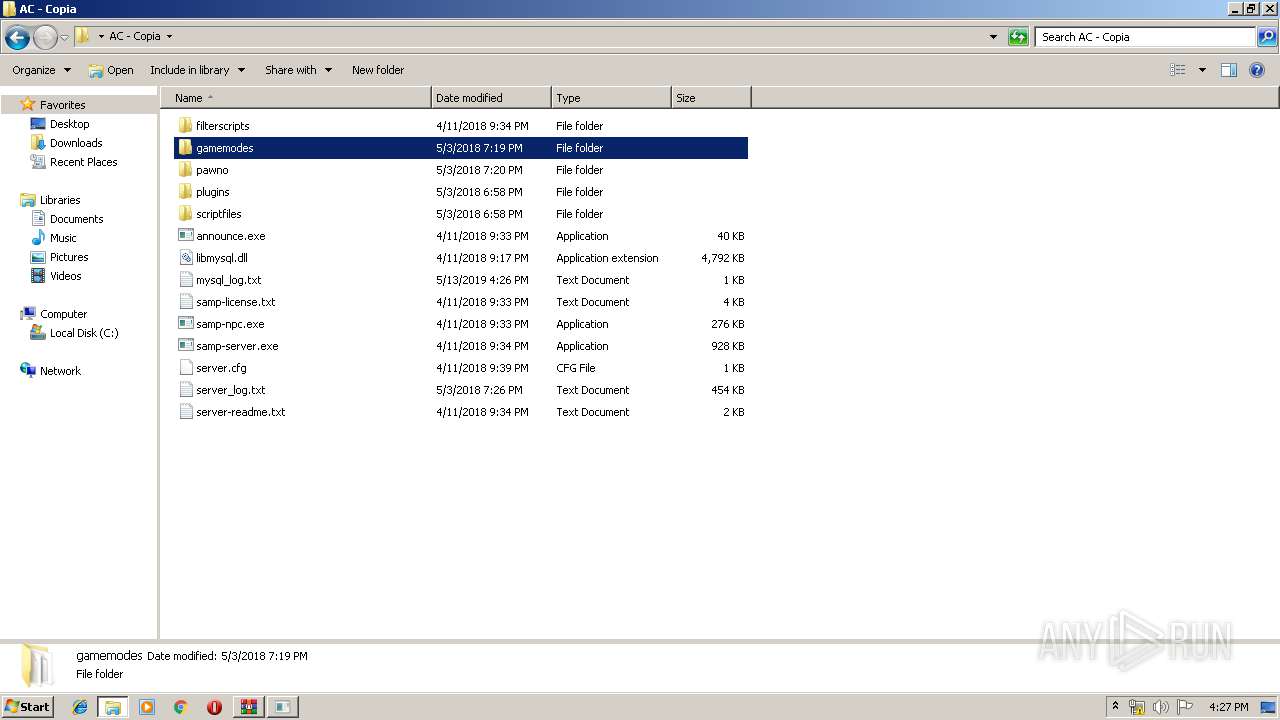
| ZipFileName: | AC - Copia/ |
Total processes
56
Monitored processes
14
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
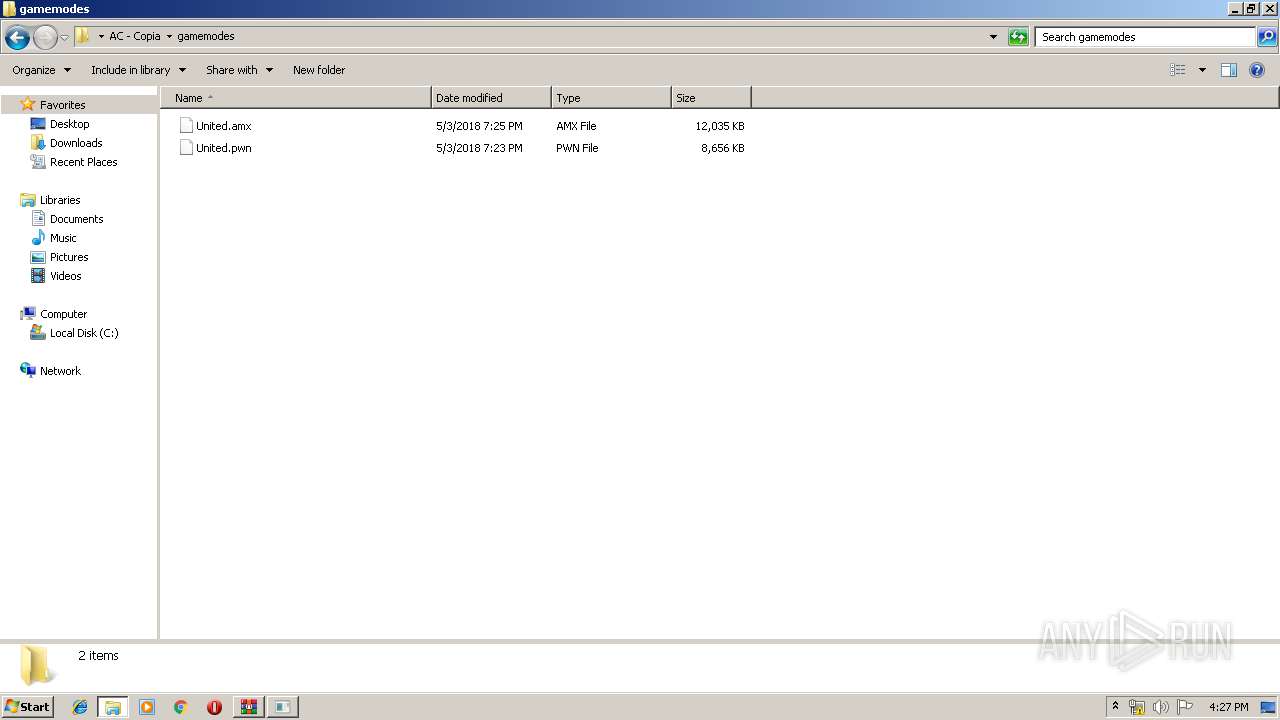
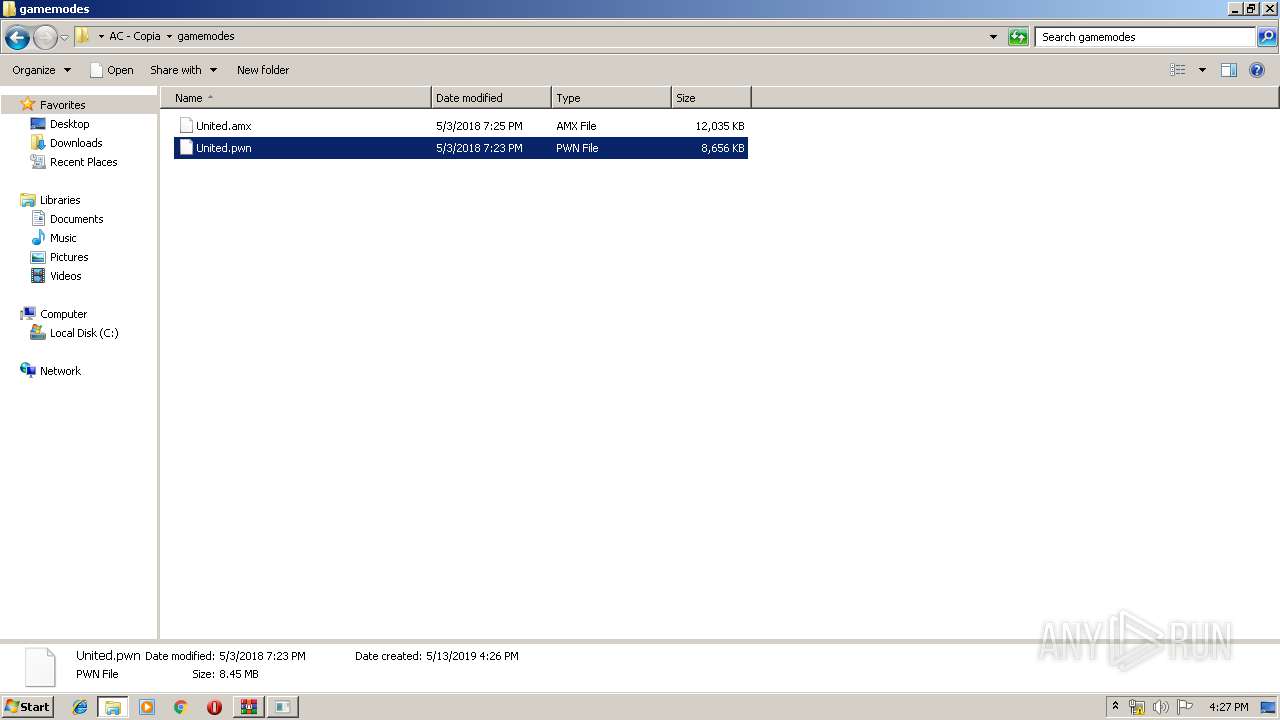
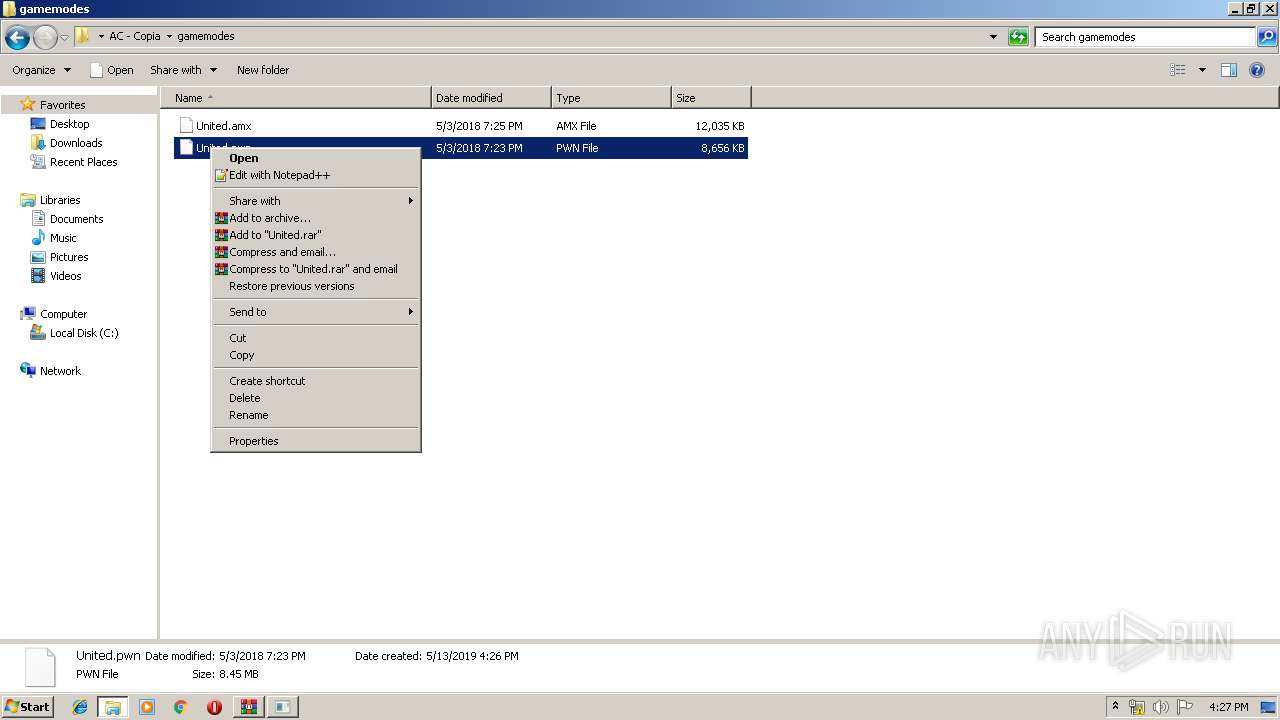
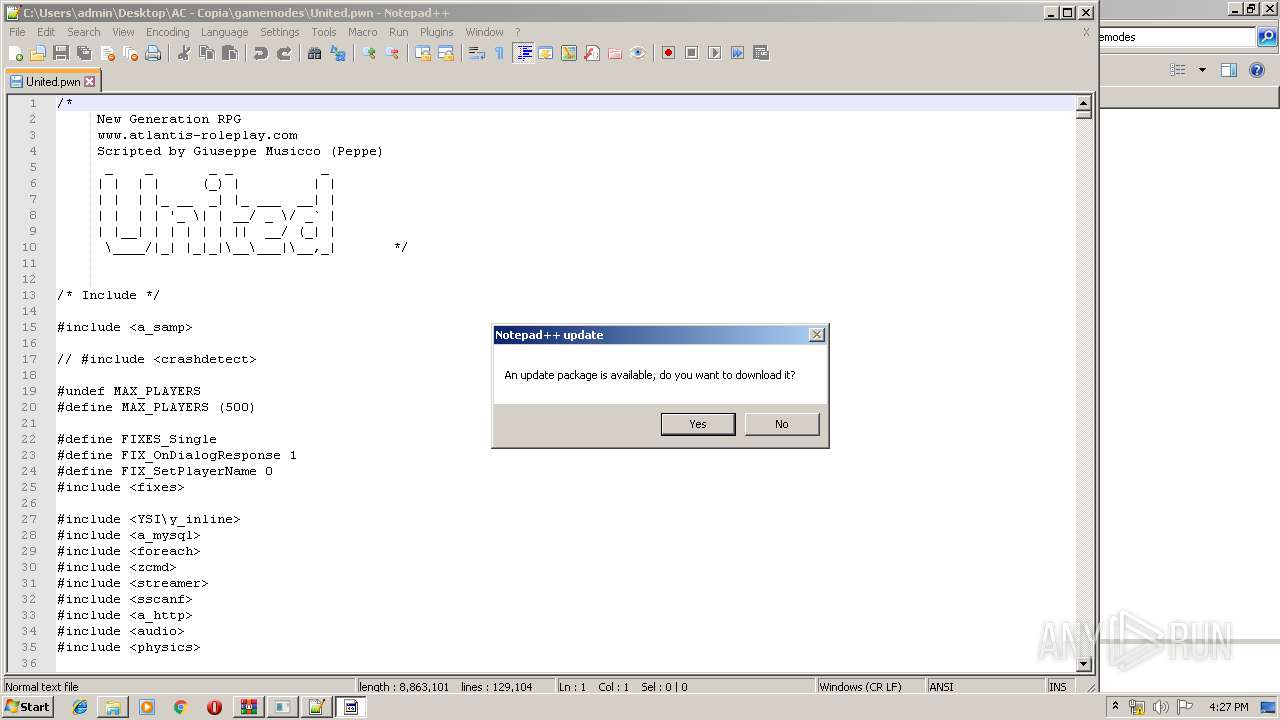
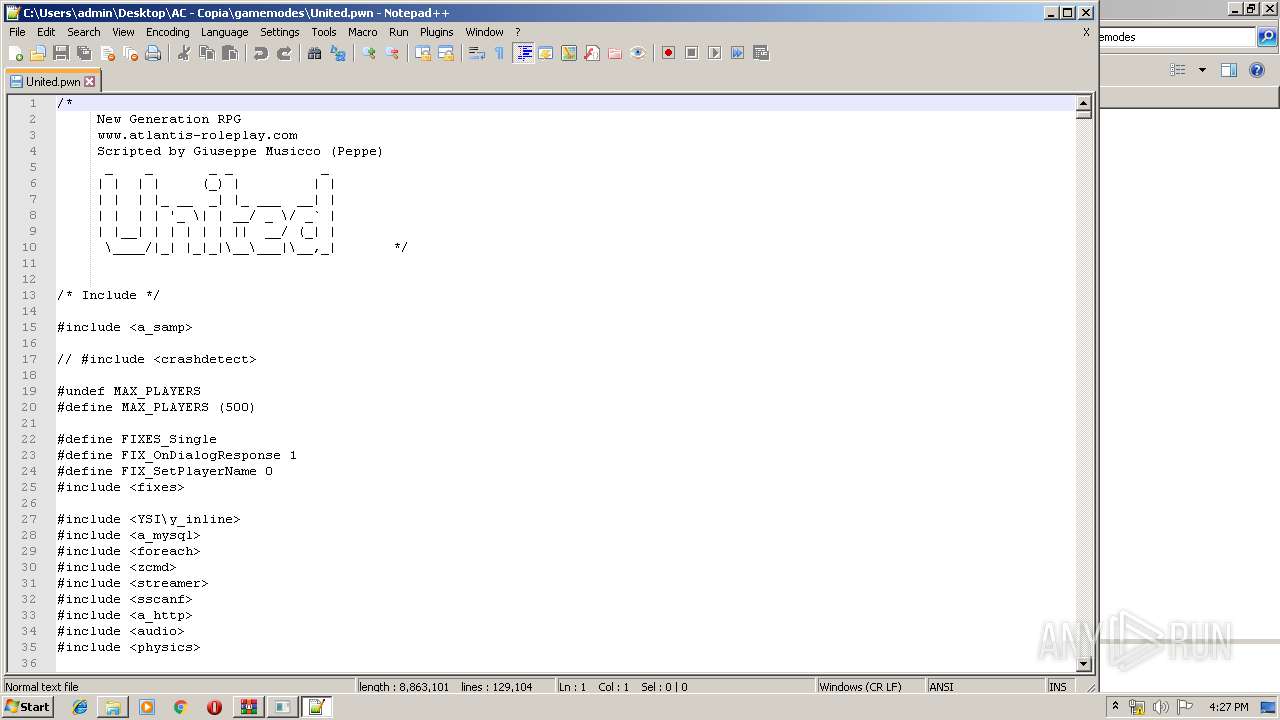
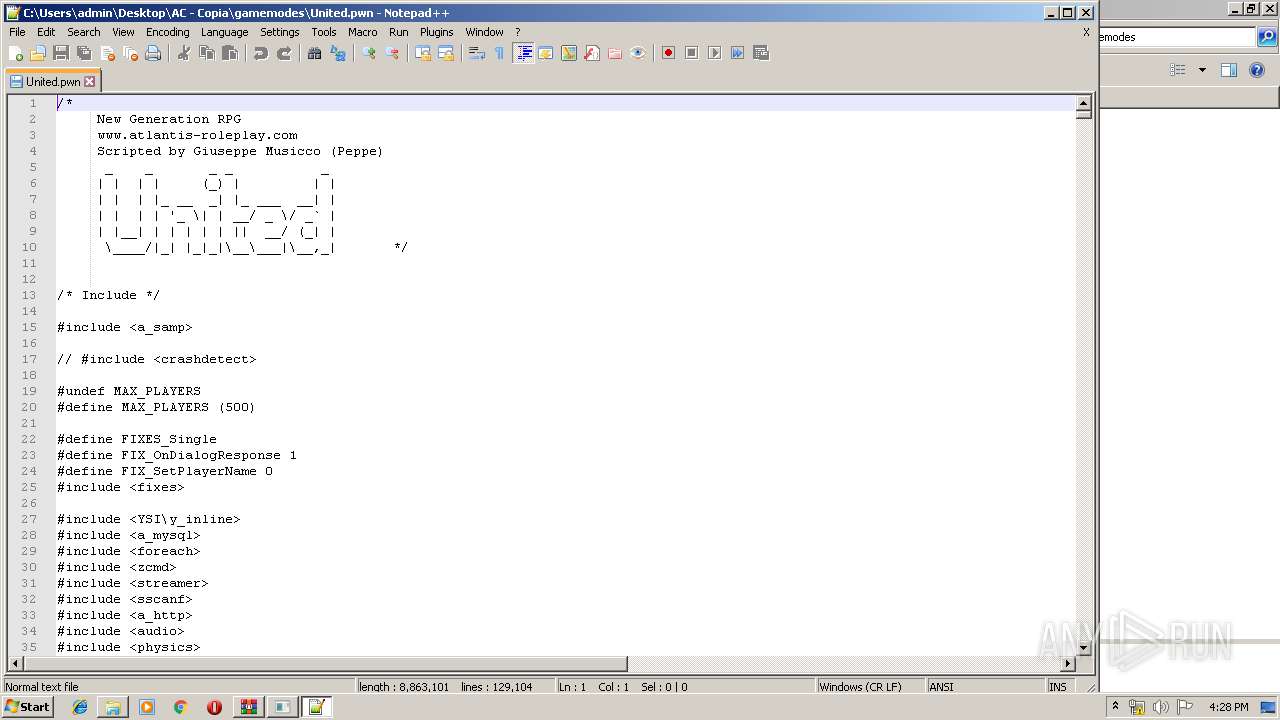
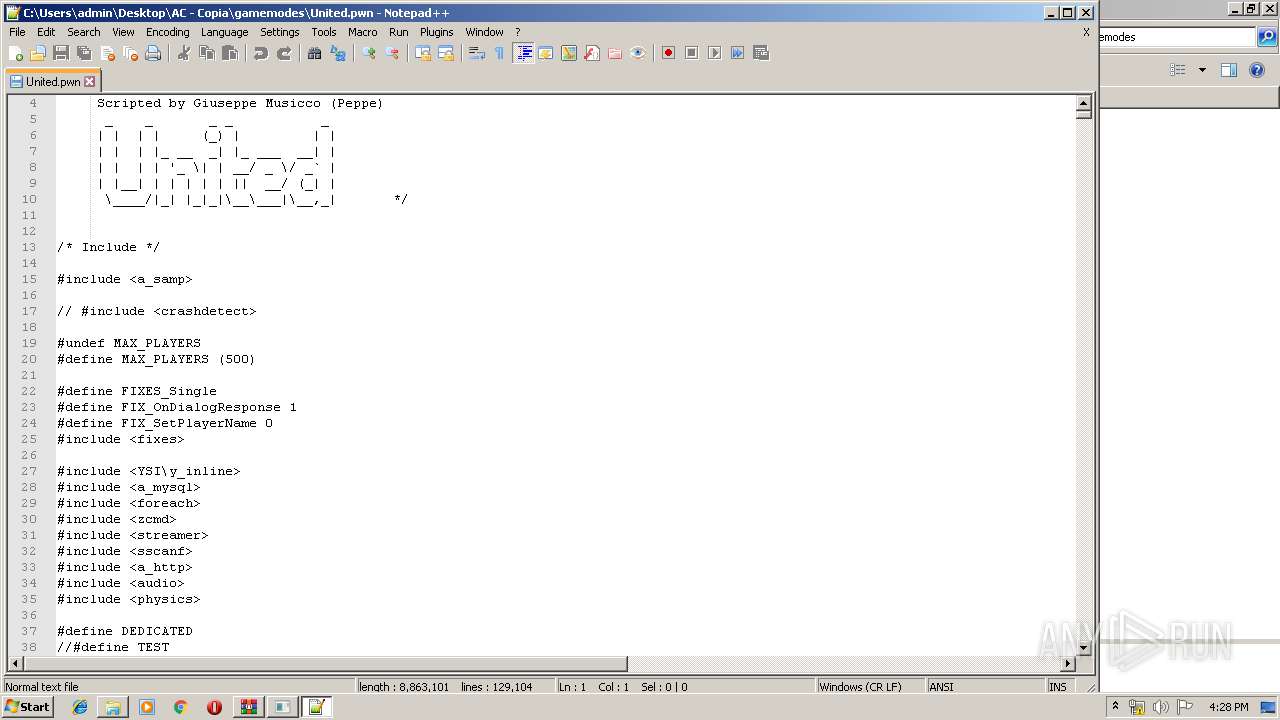
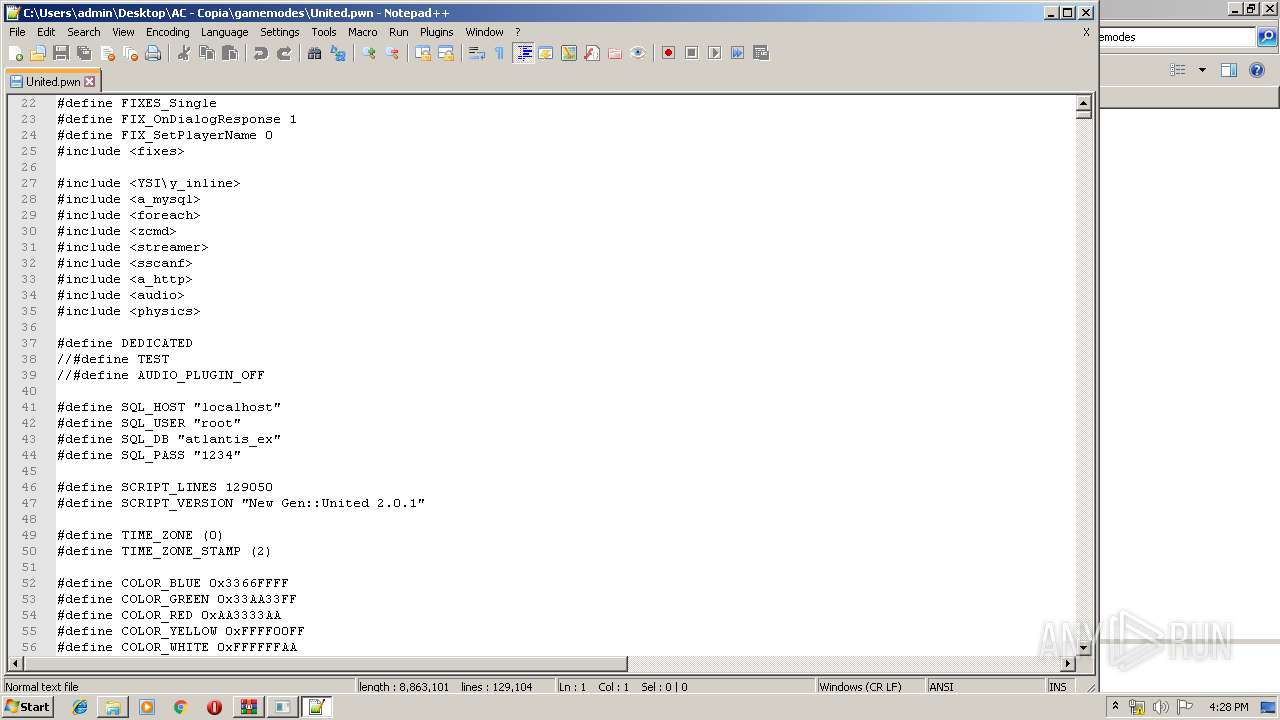
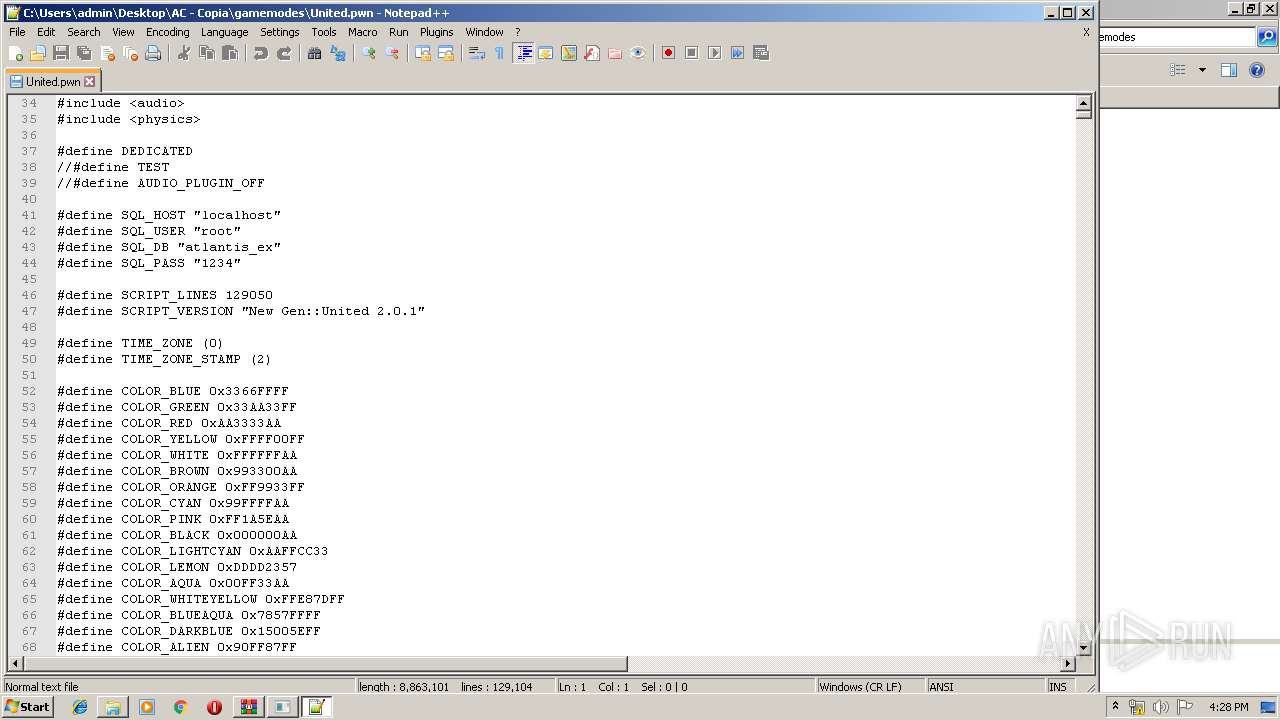
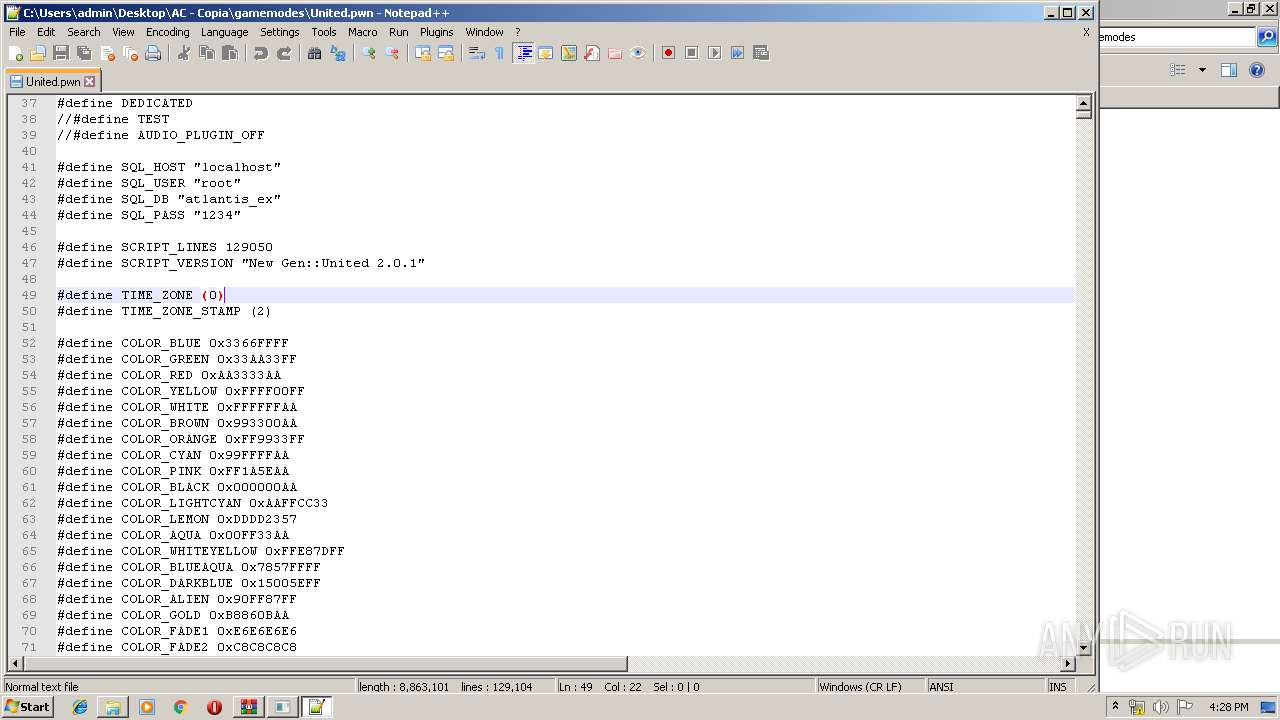
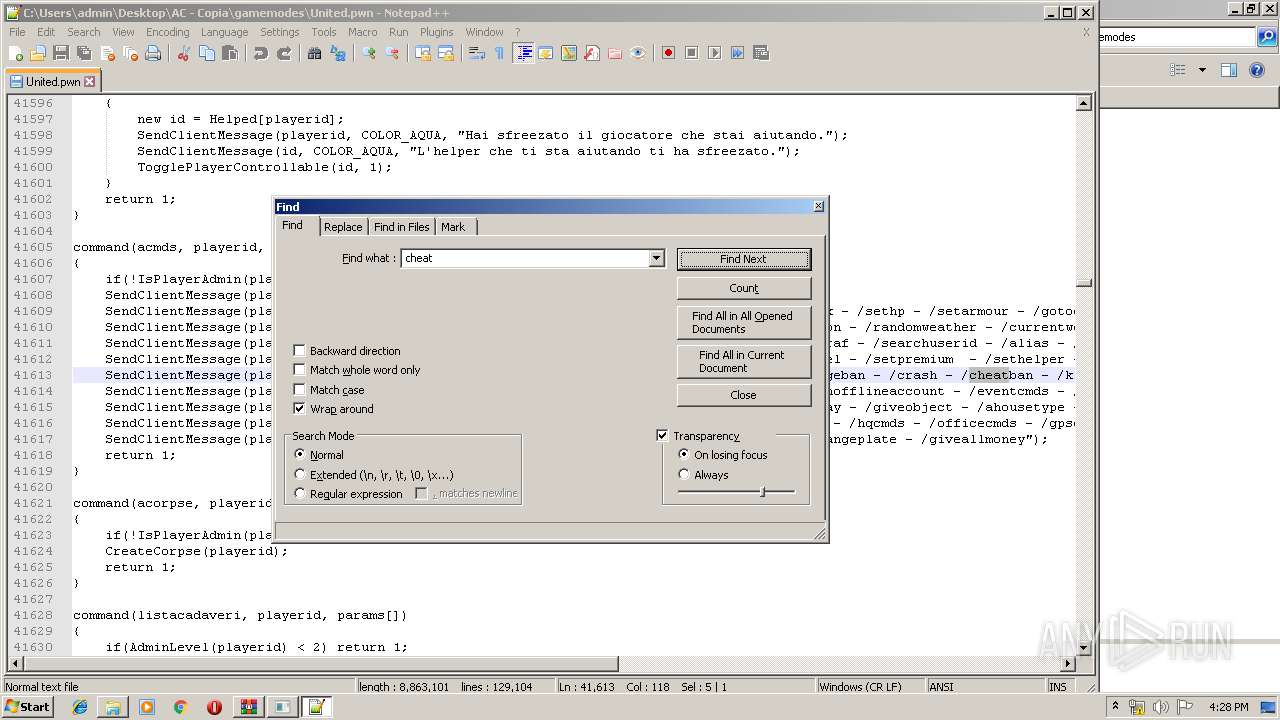
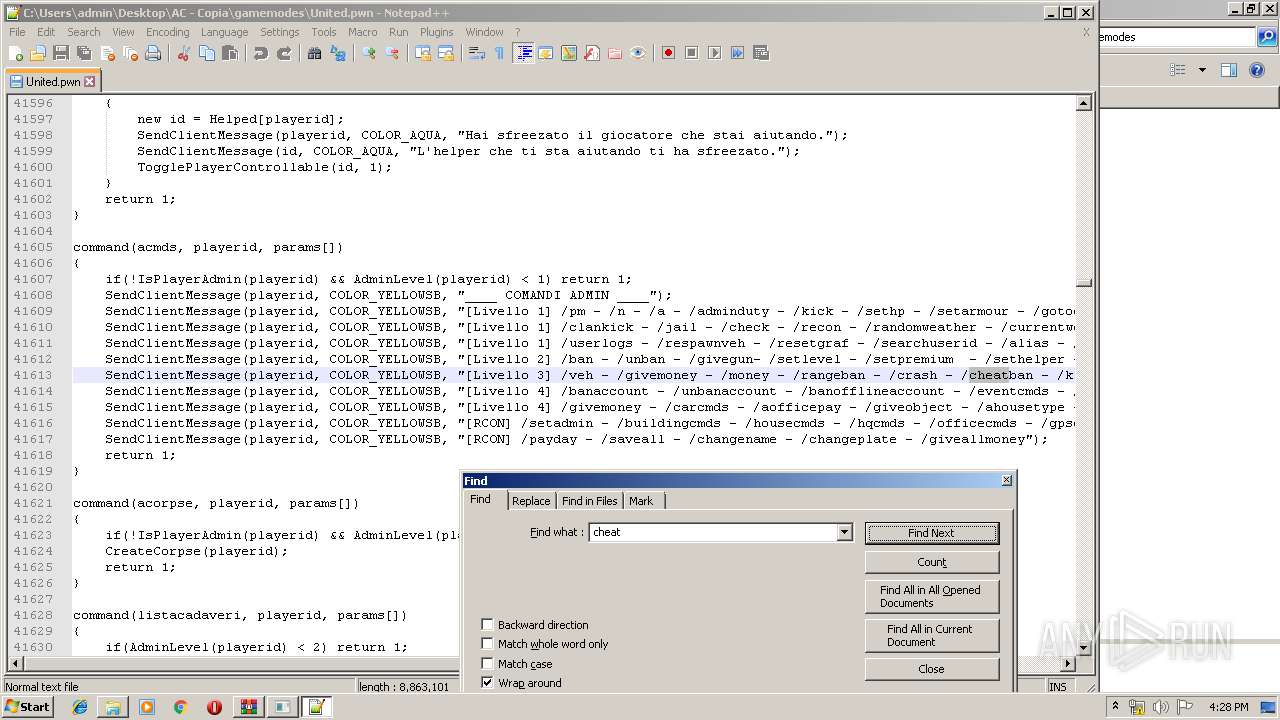
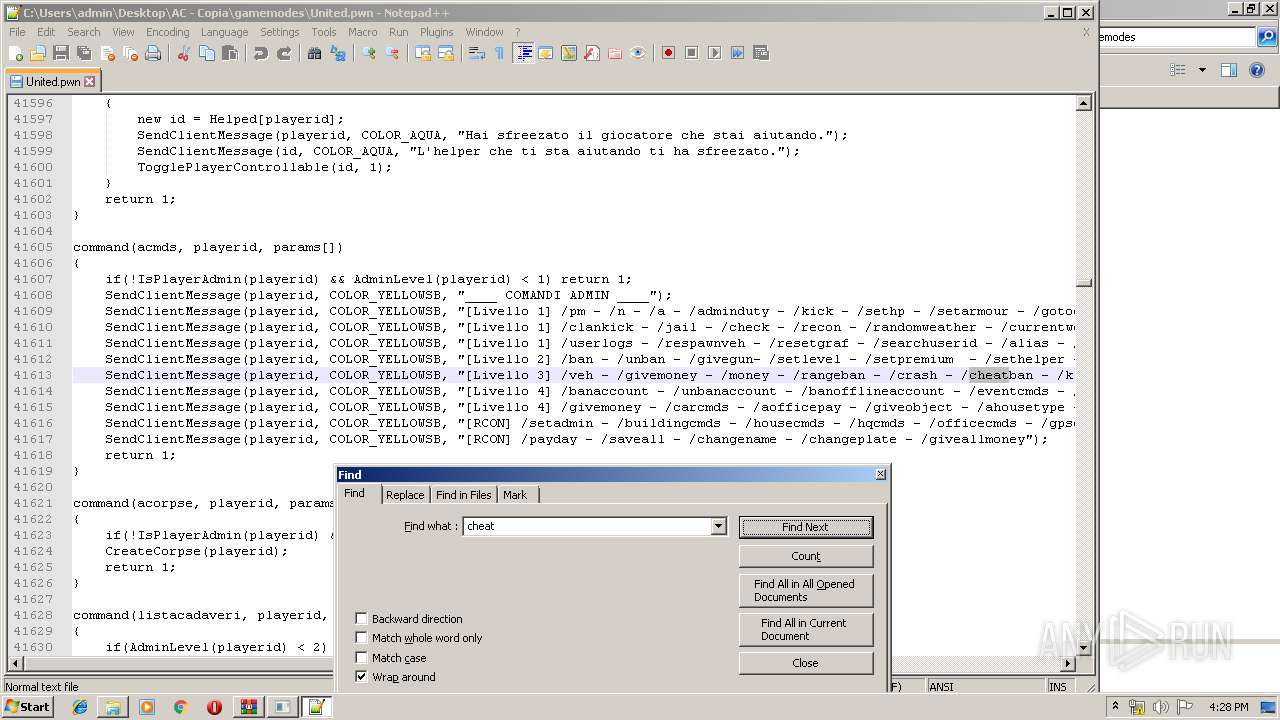
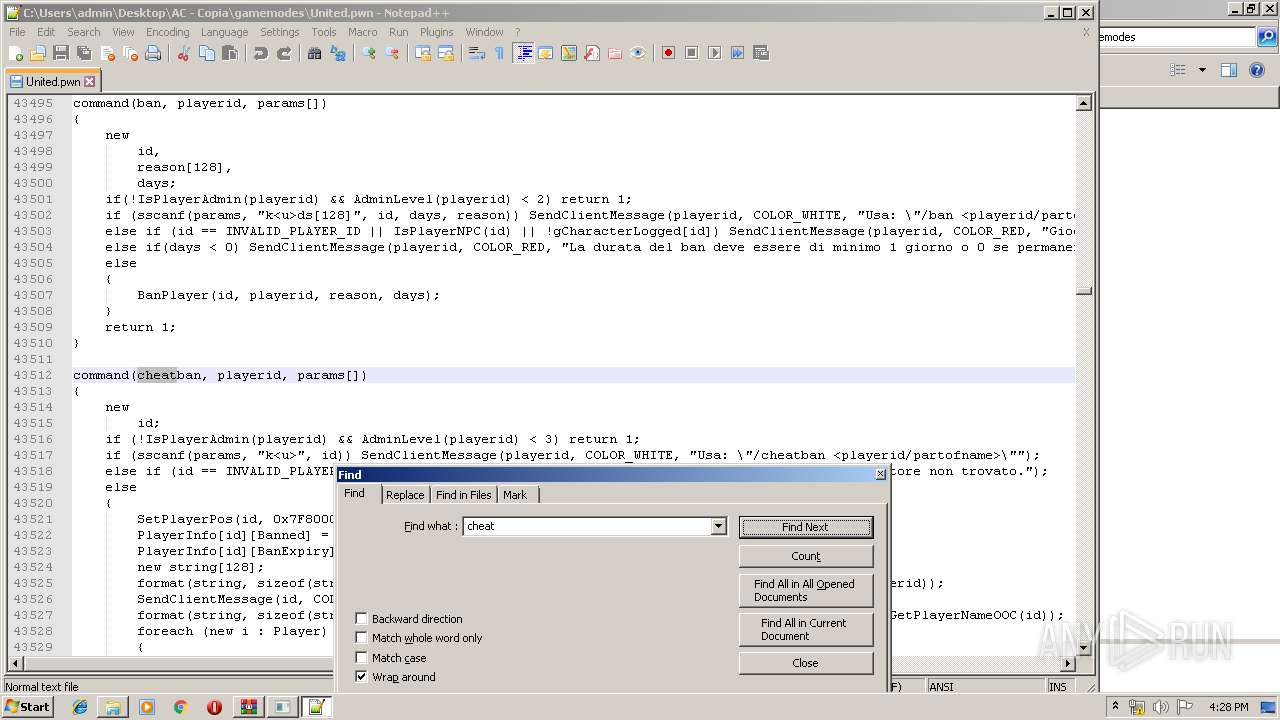
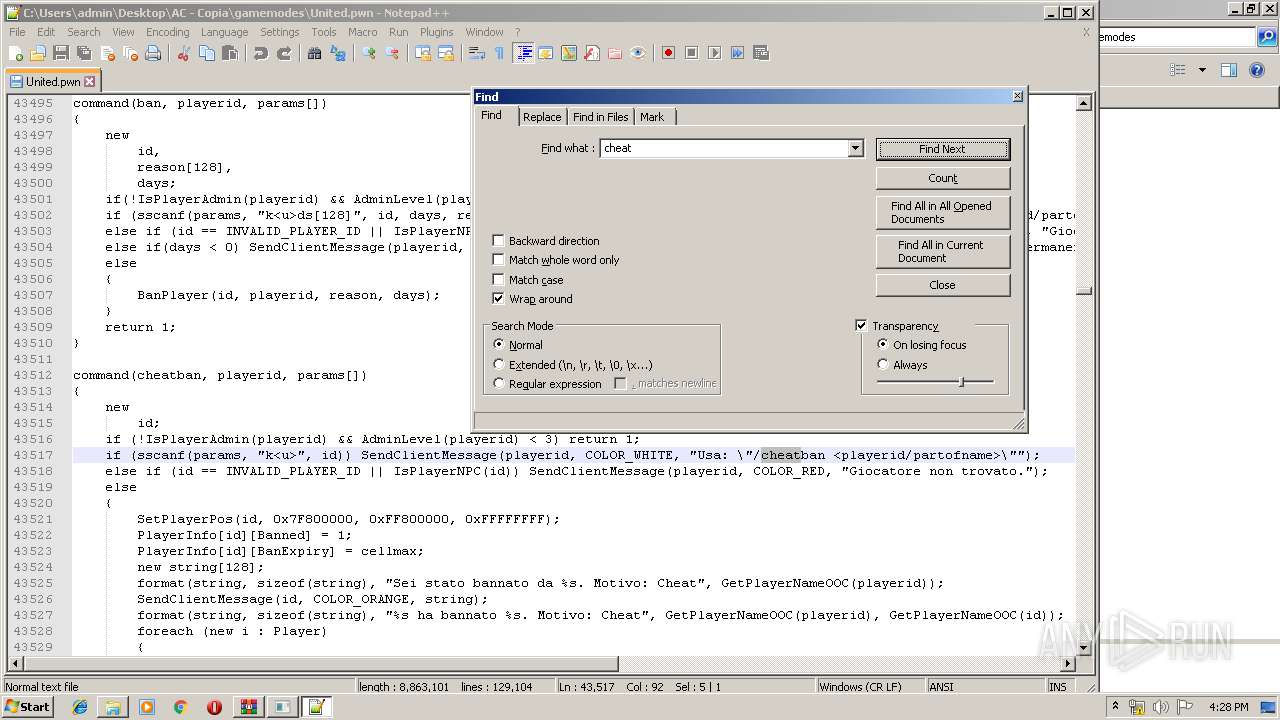
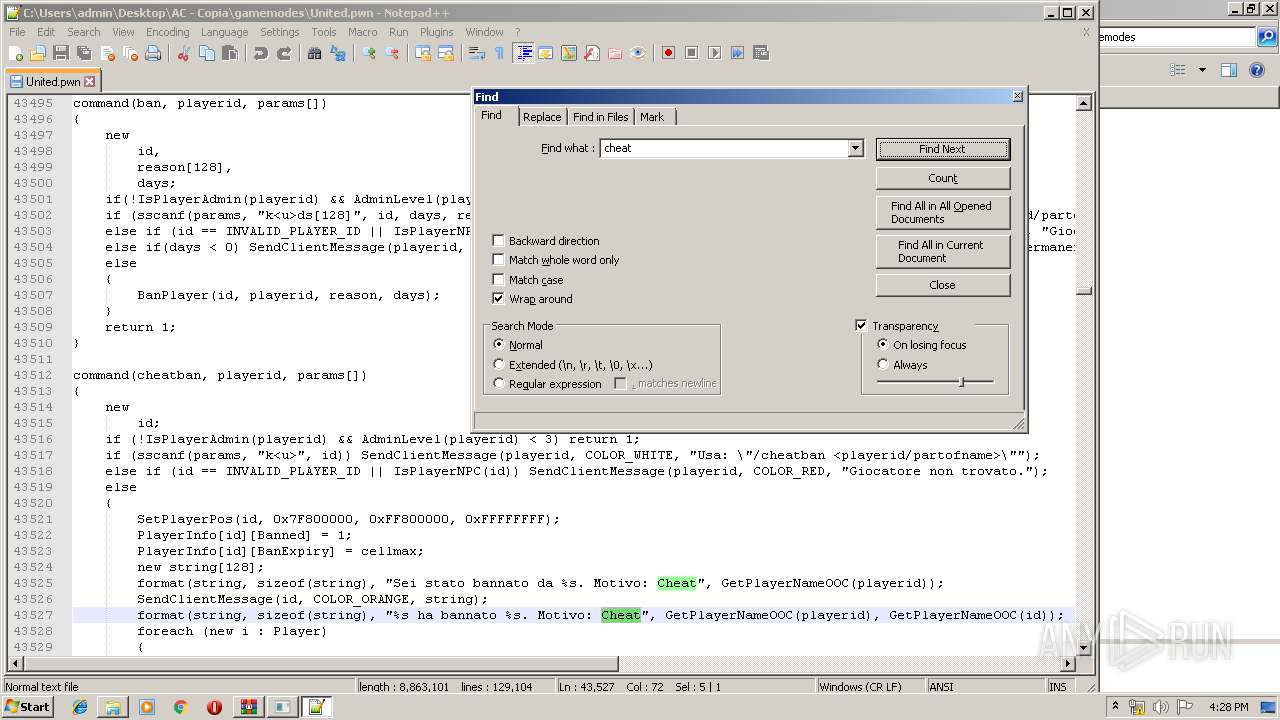
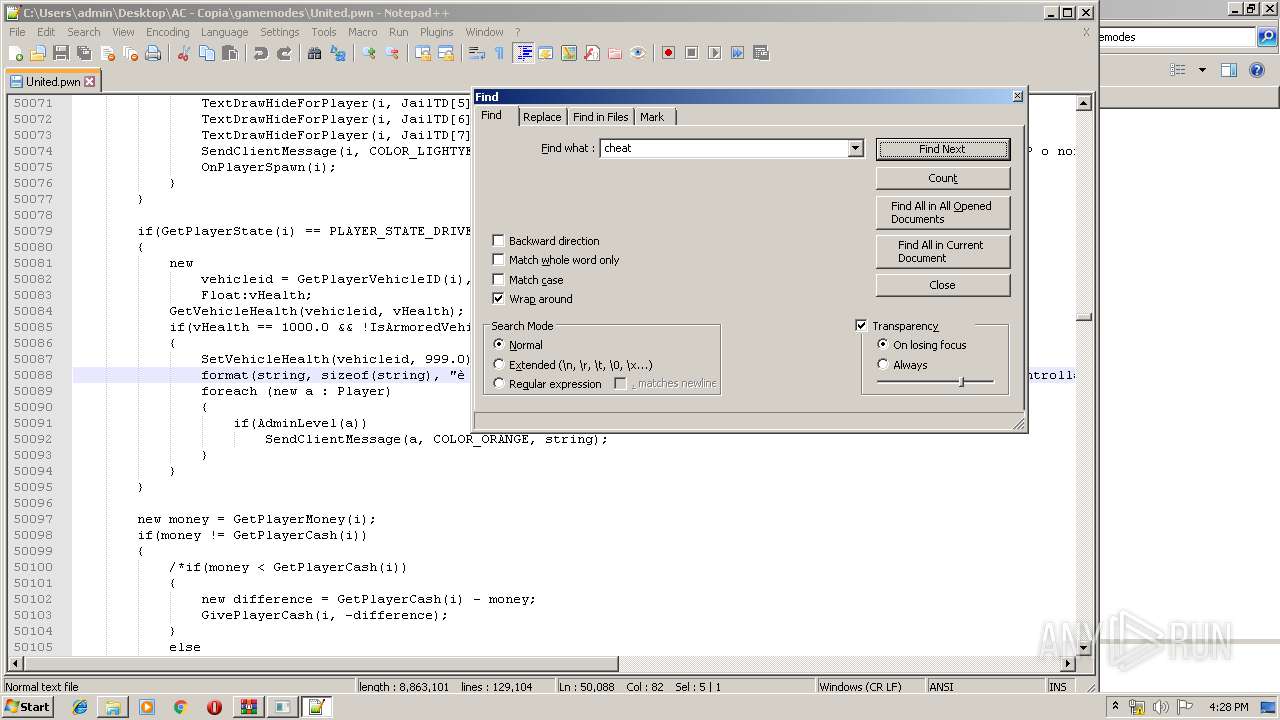
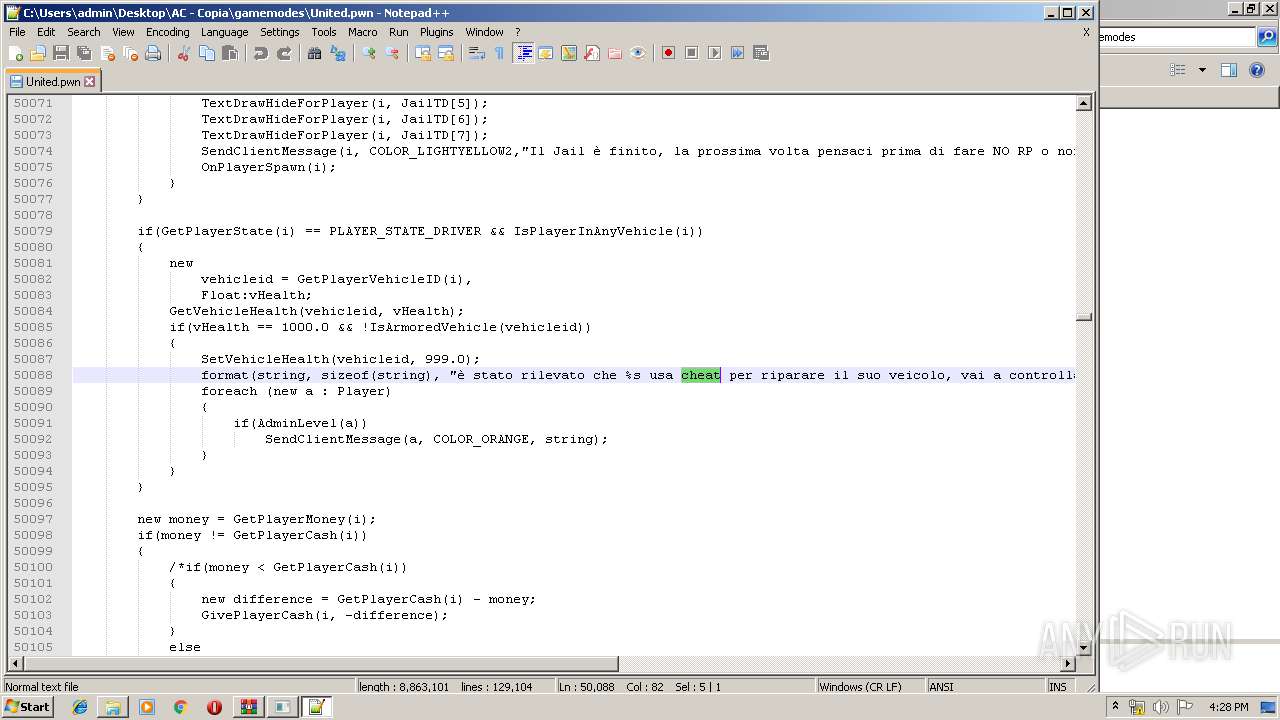
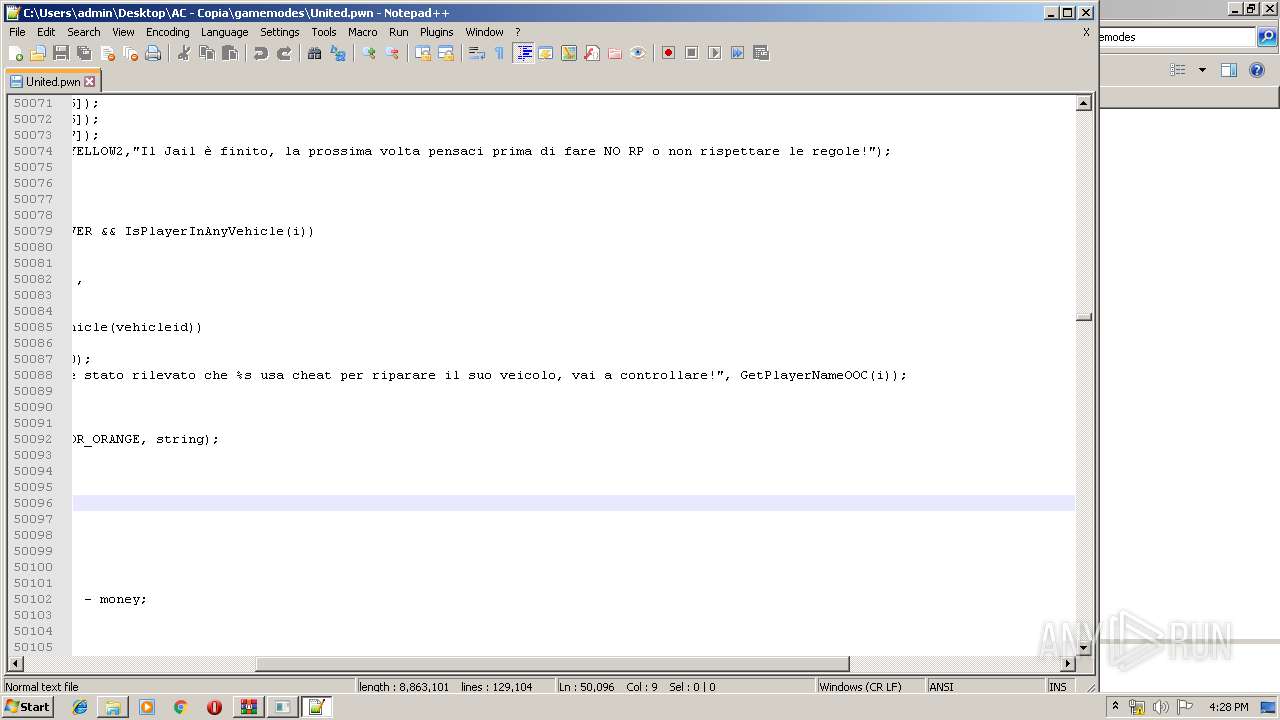
| 864 | "C:\Program Files\Notepad++\notepad++.exe" "C:\Users\admin\Desktop\AC - Copia\gamemodes\United.pwn" | C:\Program Files\Notepad++\notepad++.exe | explorer.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Exit code: 0 Version: 7.51 Modules
| |||||||||||||||
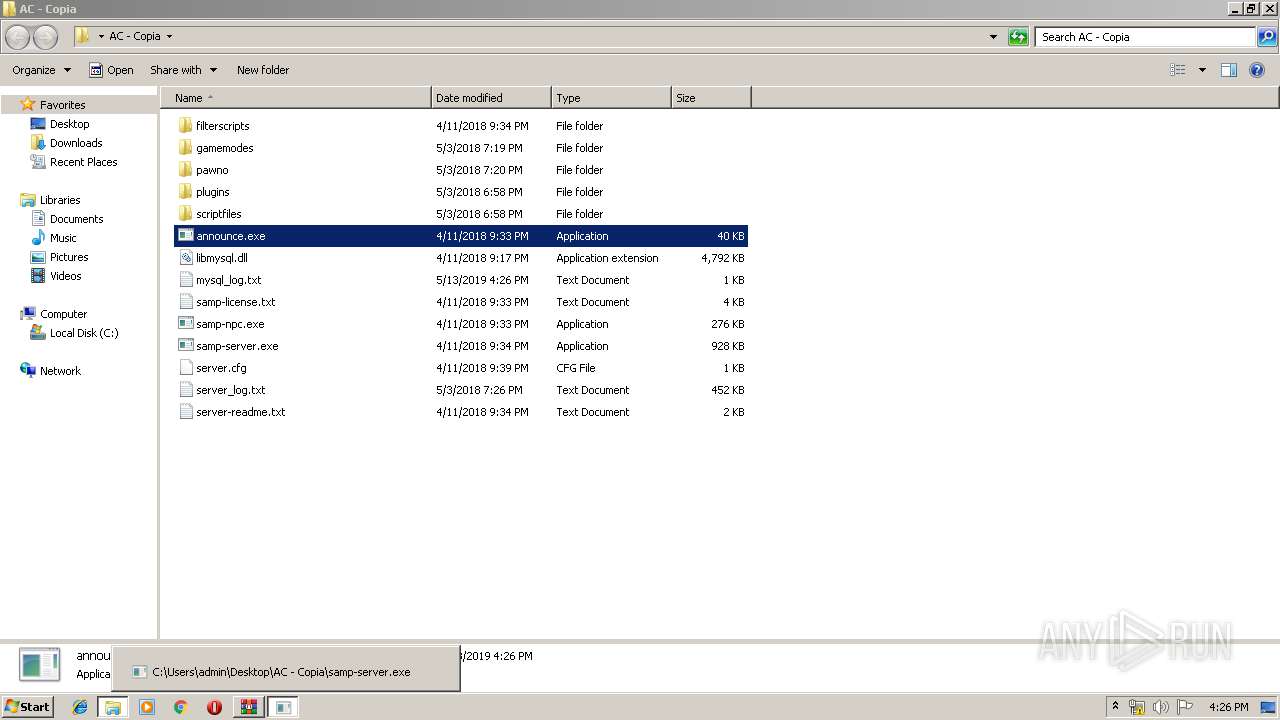
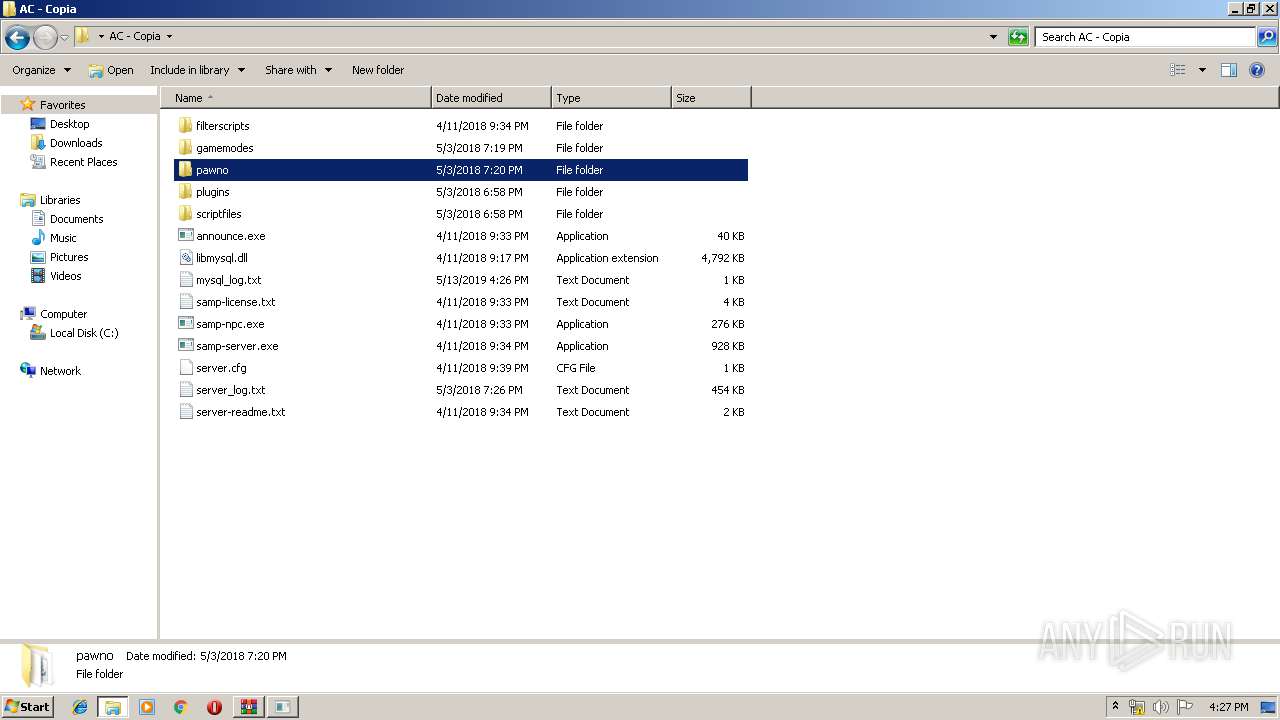
| 1396 | "C:\Users\admin\Desktop\AC - Copia\announce.exe" | C:\Users\admin\Desktop\AC - Copia\announce.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1704 | dw20.exe -x -s 776 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\dw20.exe | — | SAMPCE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Error Reporting Shim Exit code: 0 Version: 2.0.50727.4927 (NetFXspW7.050727-4900) Modules
| |||||||||||||||
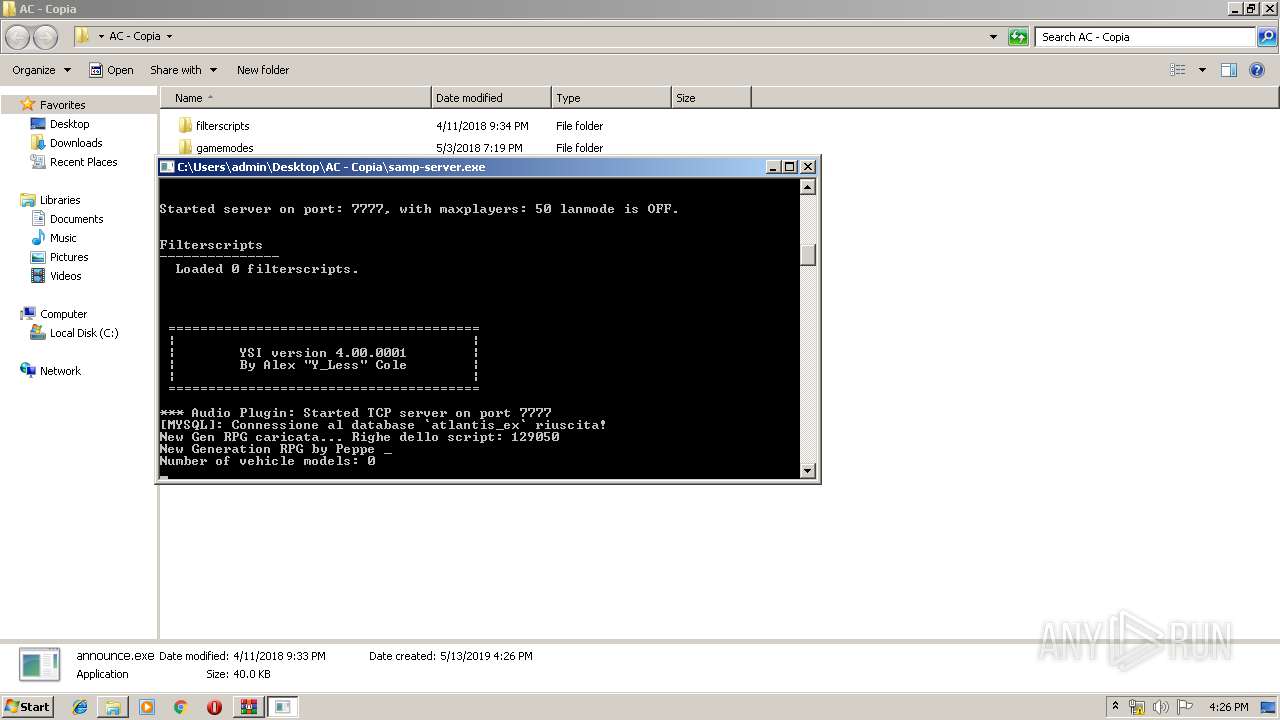
| 1732 | "C:\Users\admin\Desktop\AC - Copia\samp-server.exe" | C:\Users\admin\Desktop\AC - Copia\samp-server.exe | explorer.exe | ||||||||||||
User: admin Company: SA-MP Team Integrity Level: MEDIUM Description: SA-MP dedicated server Exit code: 0 Version: 0.3.7.0 Modules
| |||||||||||||||
| 1872 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\14.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
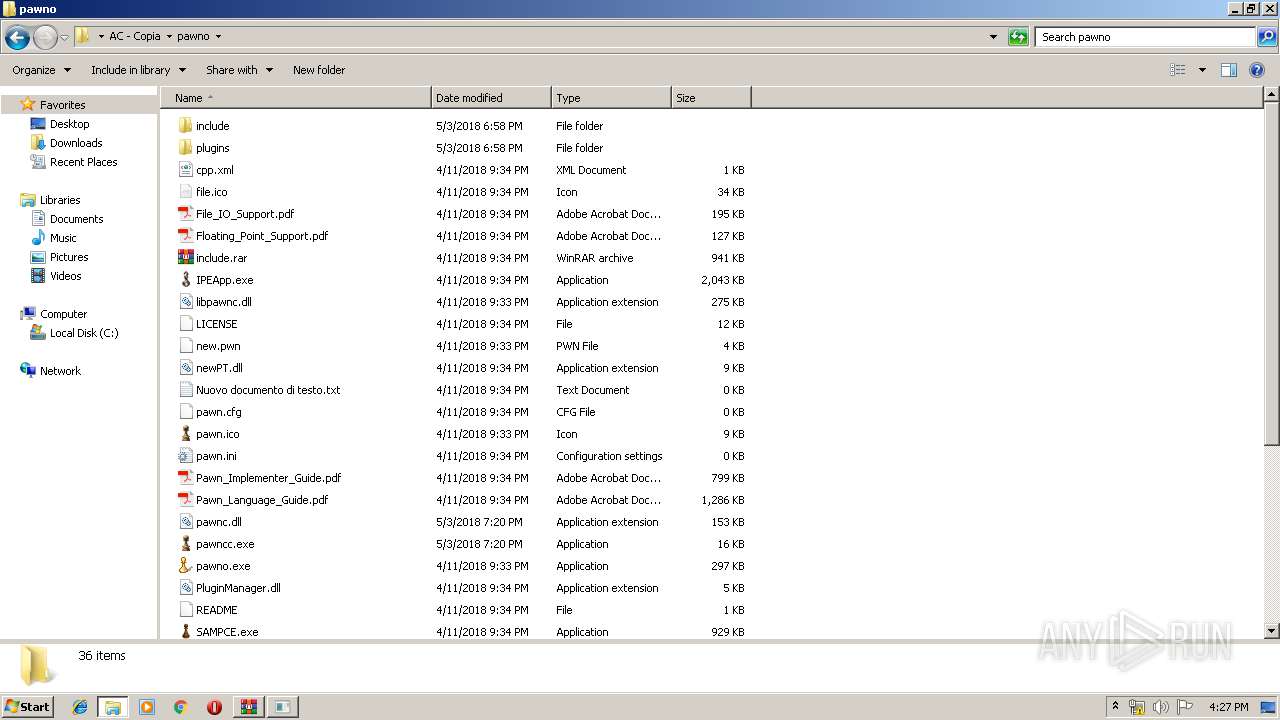
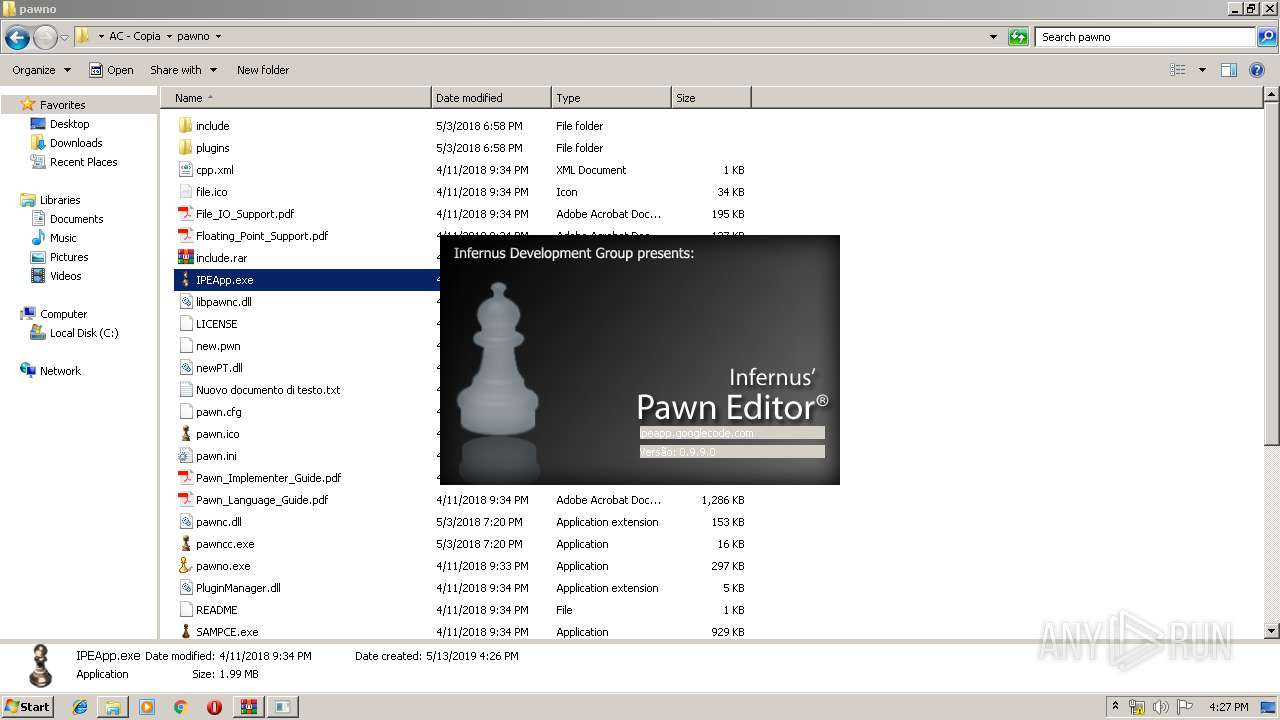
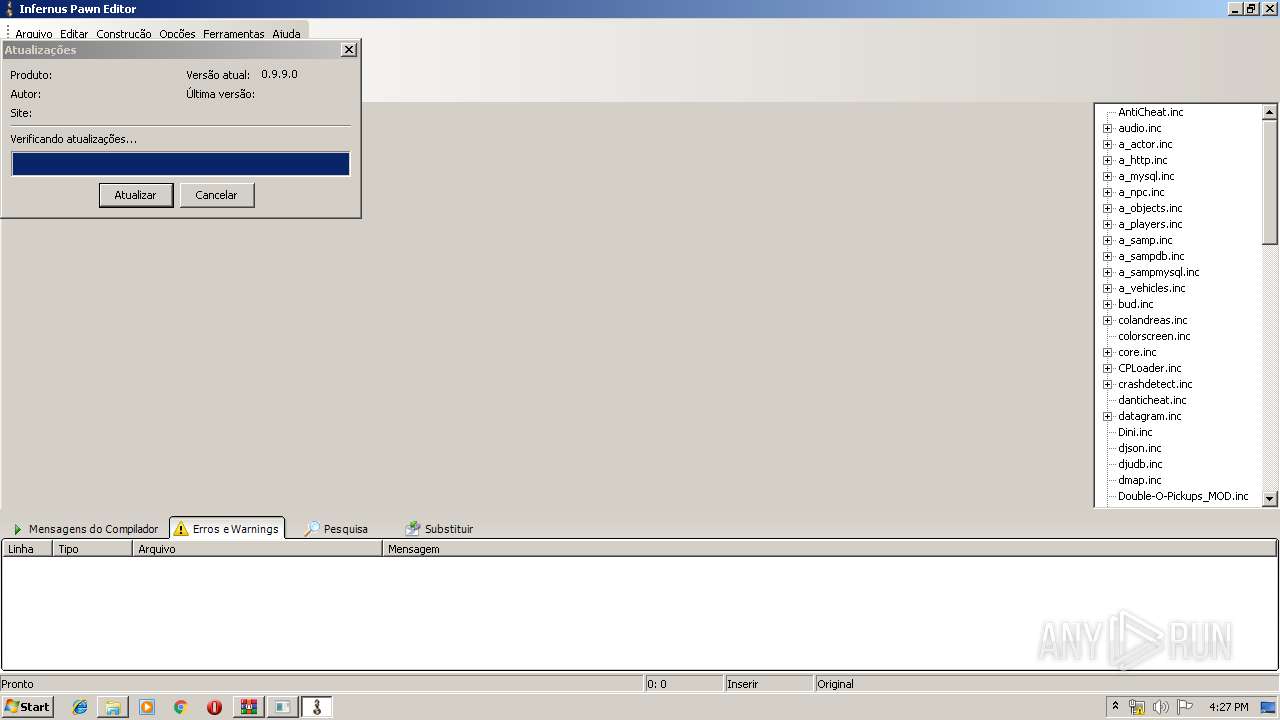
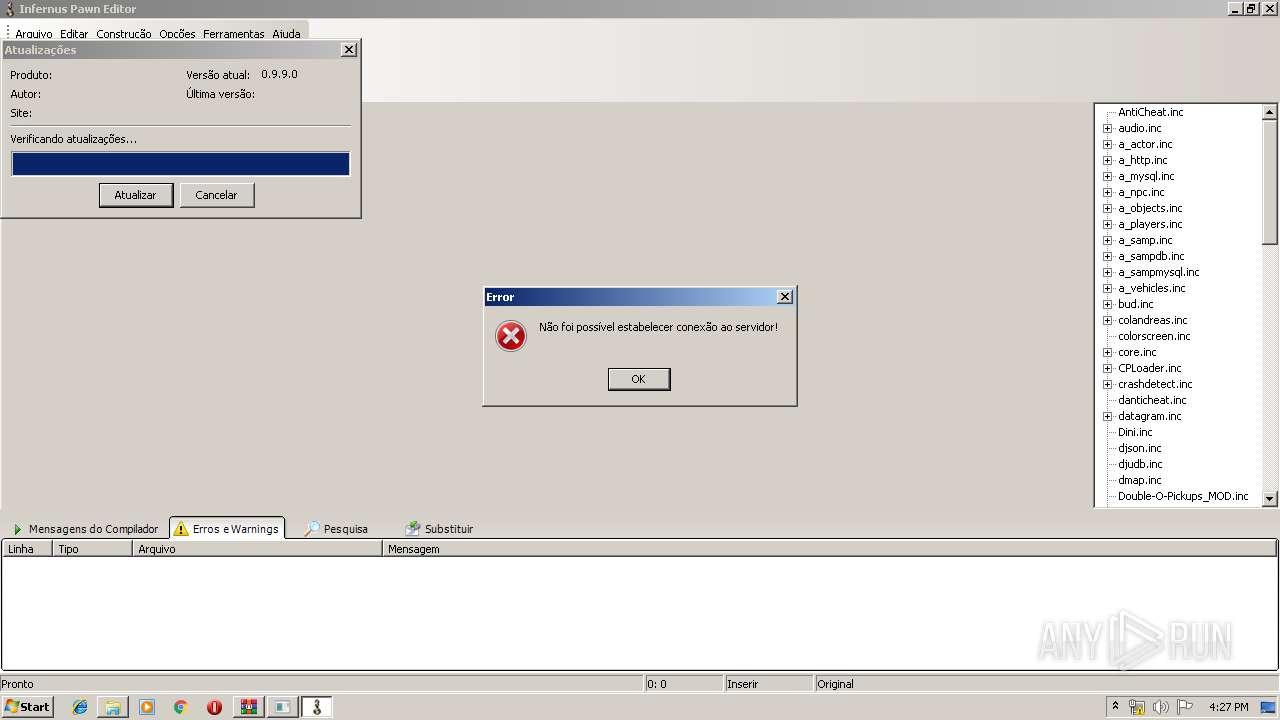
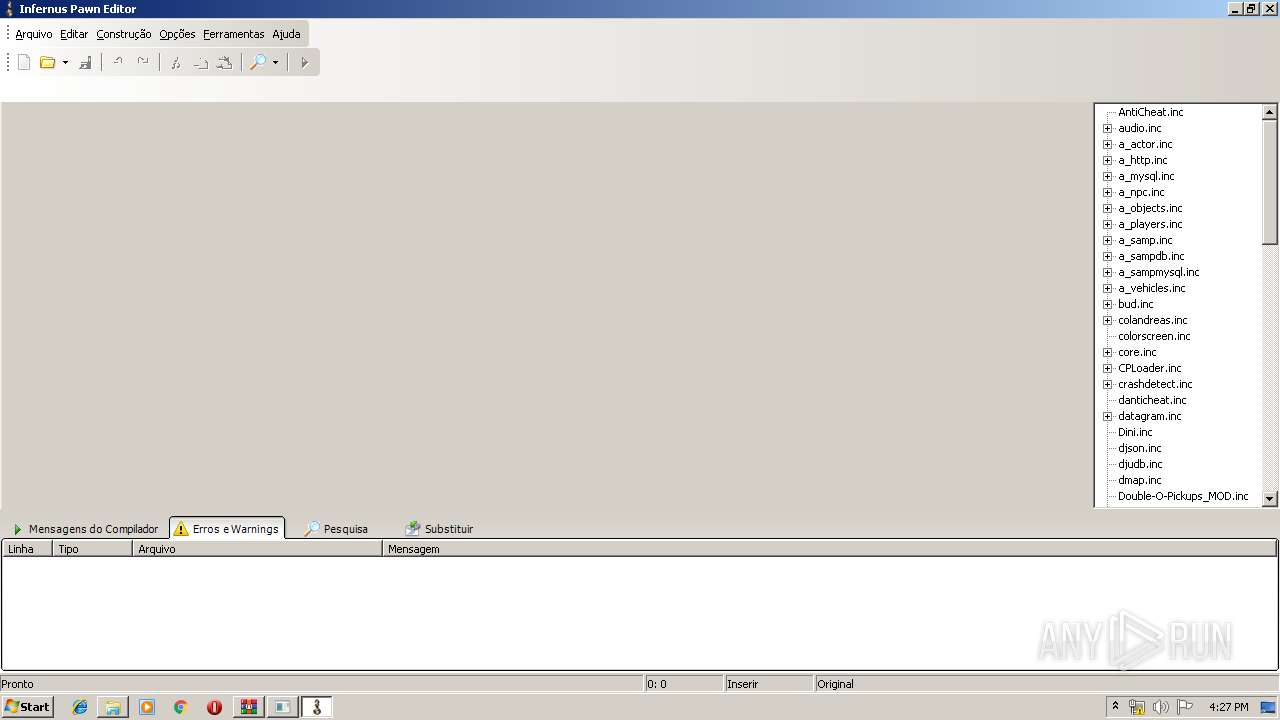
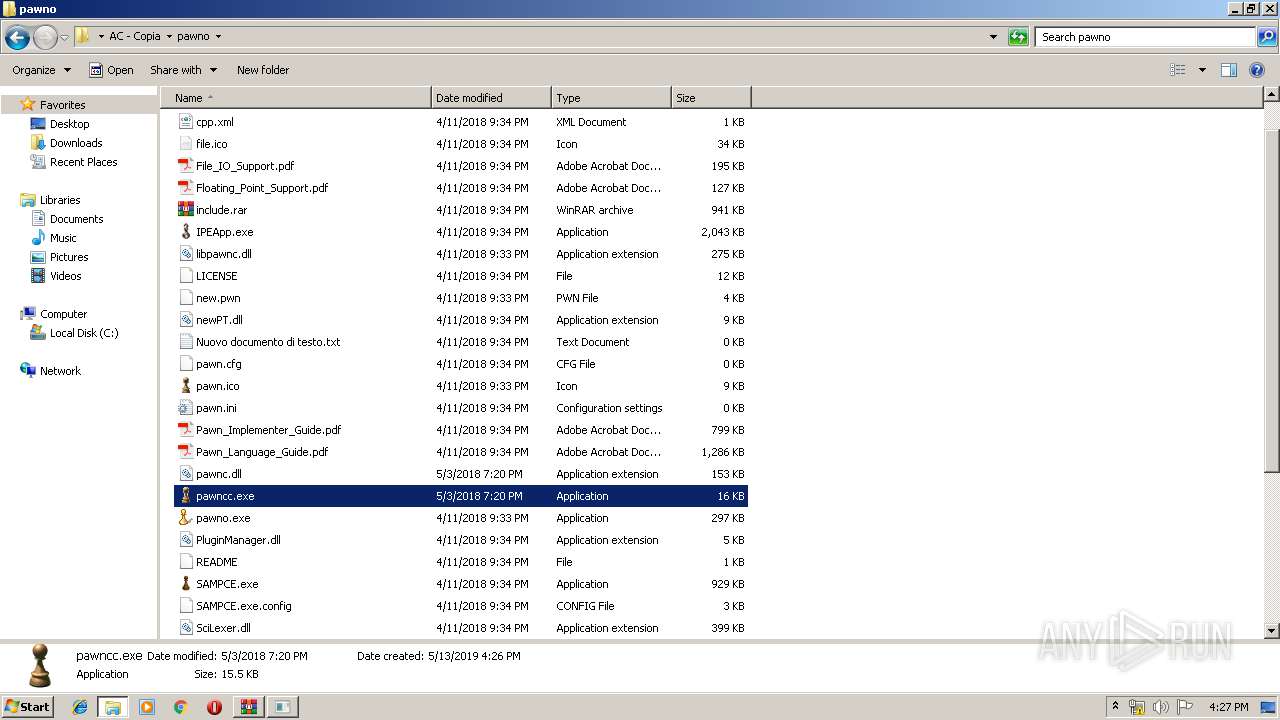
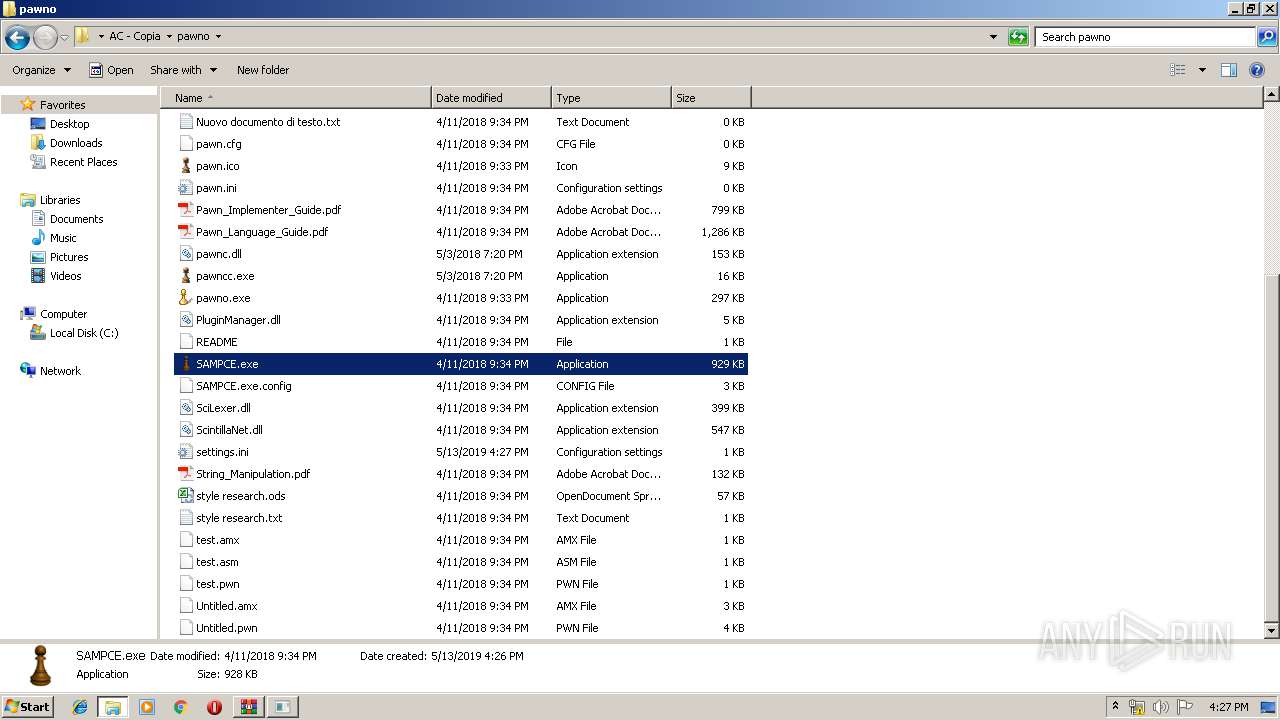
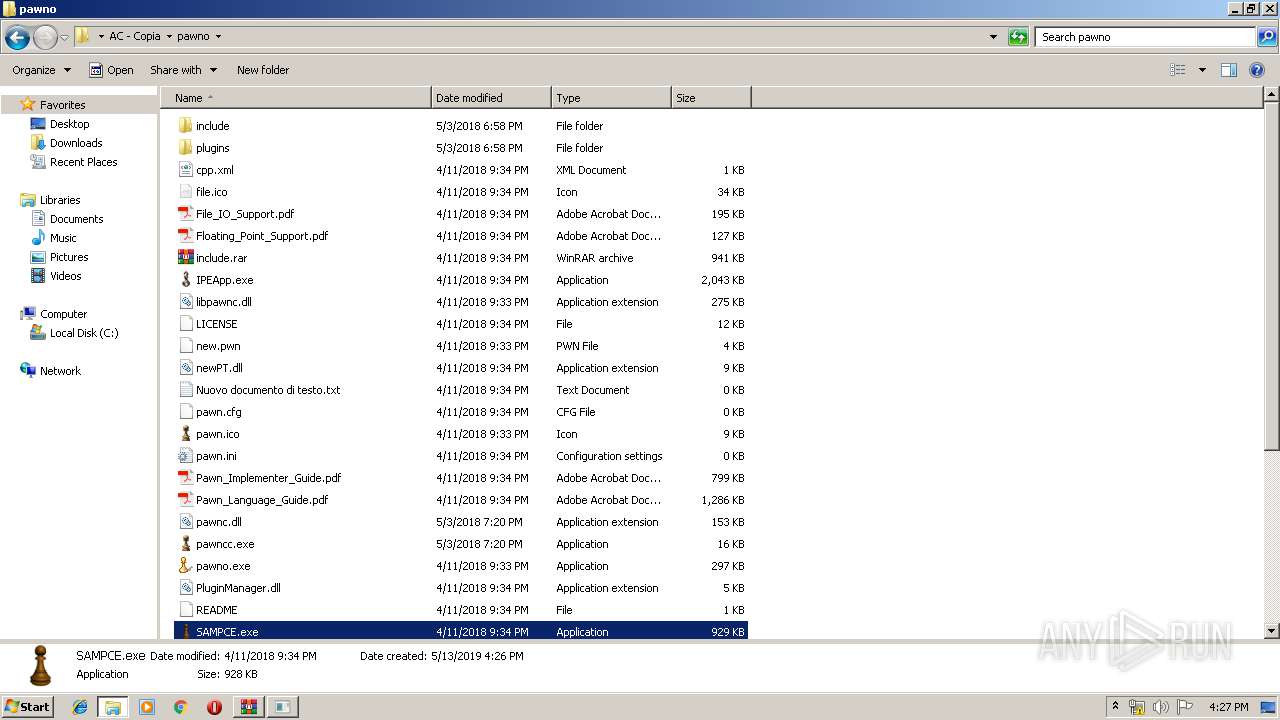
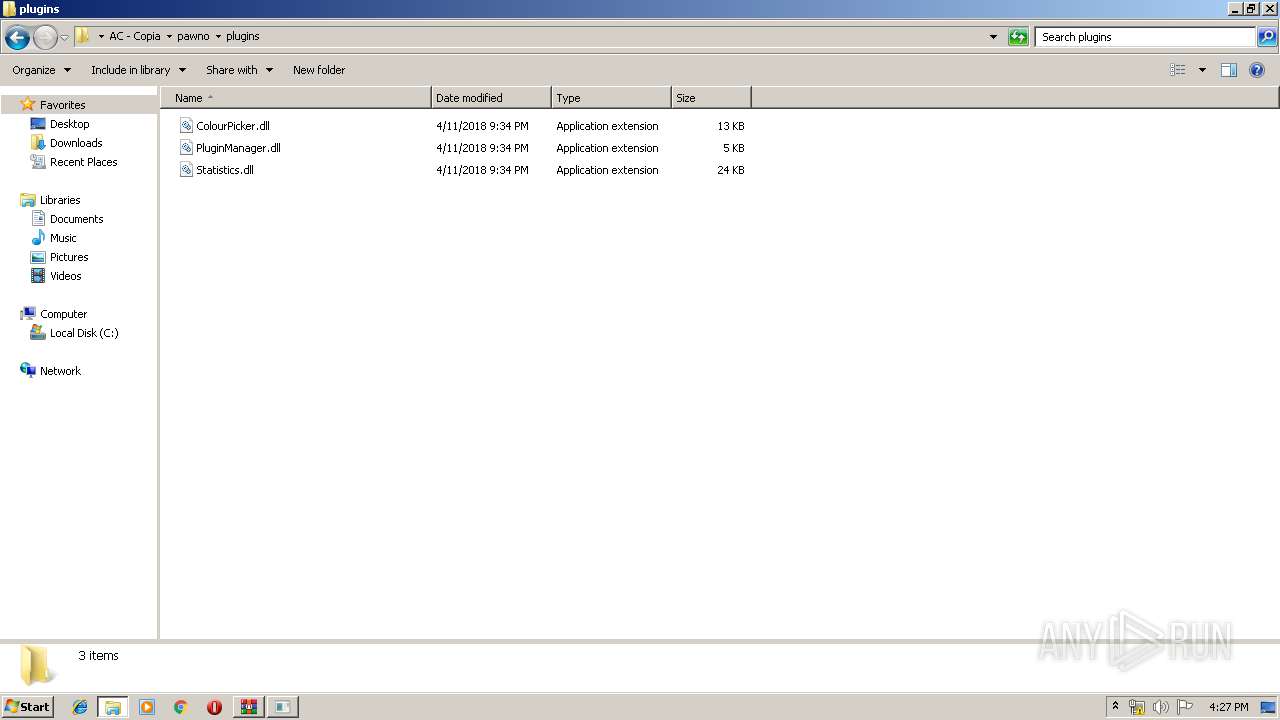
| 1936 | "C:\Users\admin\Desktop\AC - Copia\pawno\pawno.exe" | C:\Users\admin\Desktop\AC - Copia\pawno\pawno.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
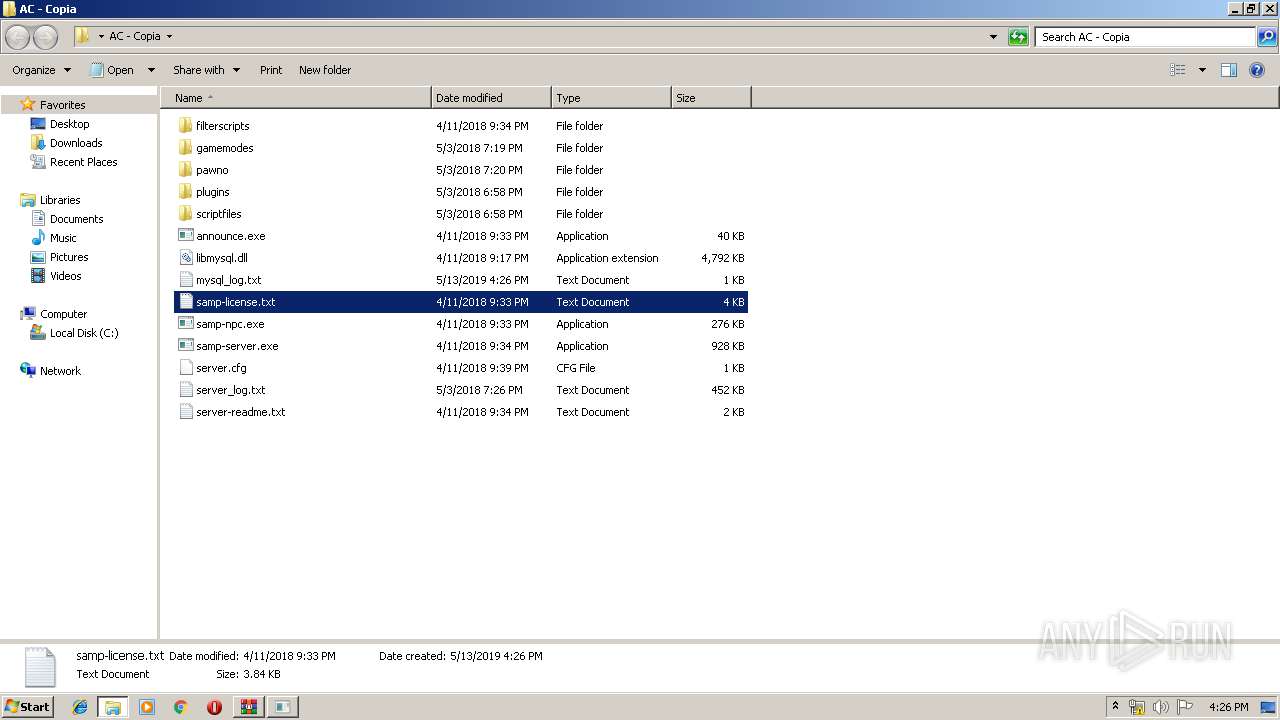
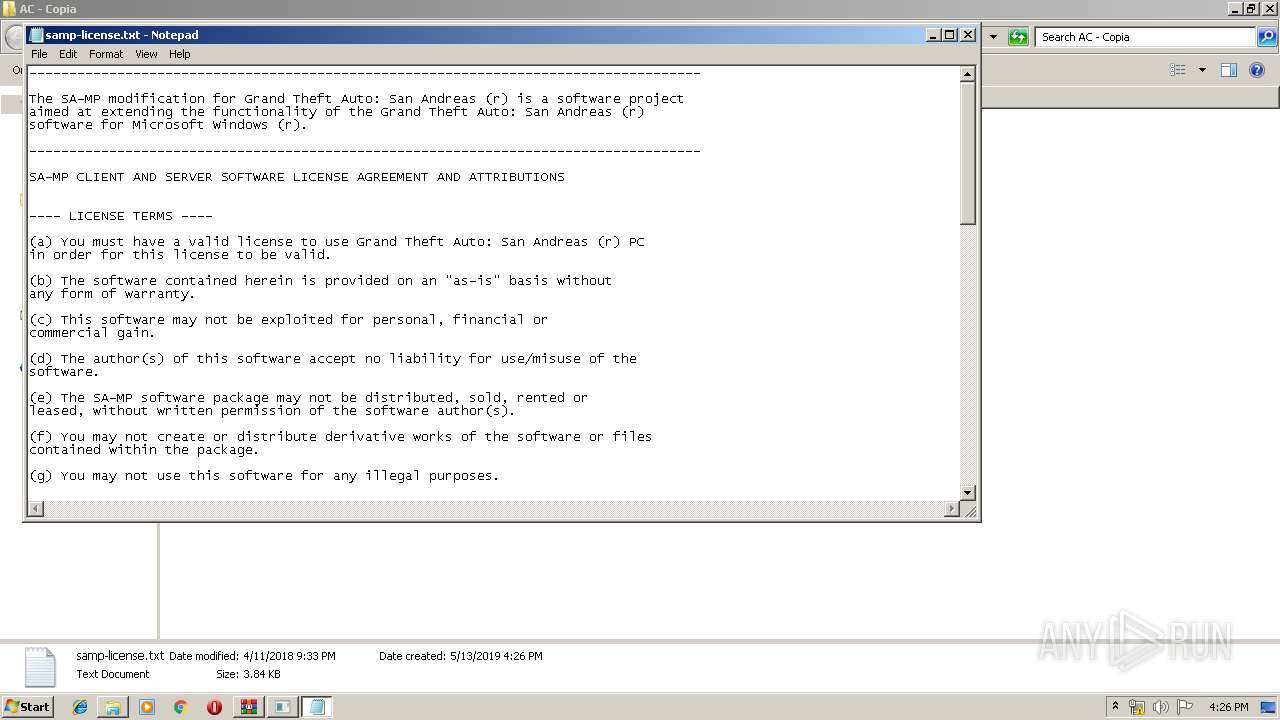
| 1976 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\AC - Copia\samp-license.txt | C:\Windows\system32\NOTEPAD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2044 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe4_ Global\UsGthrCtrlFltPipeMssGthrPipe4 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
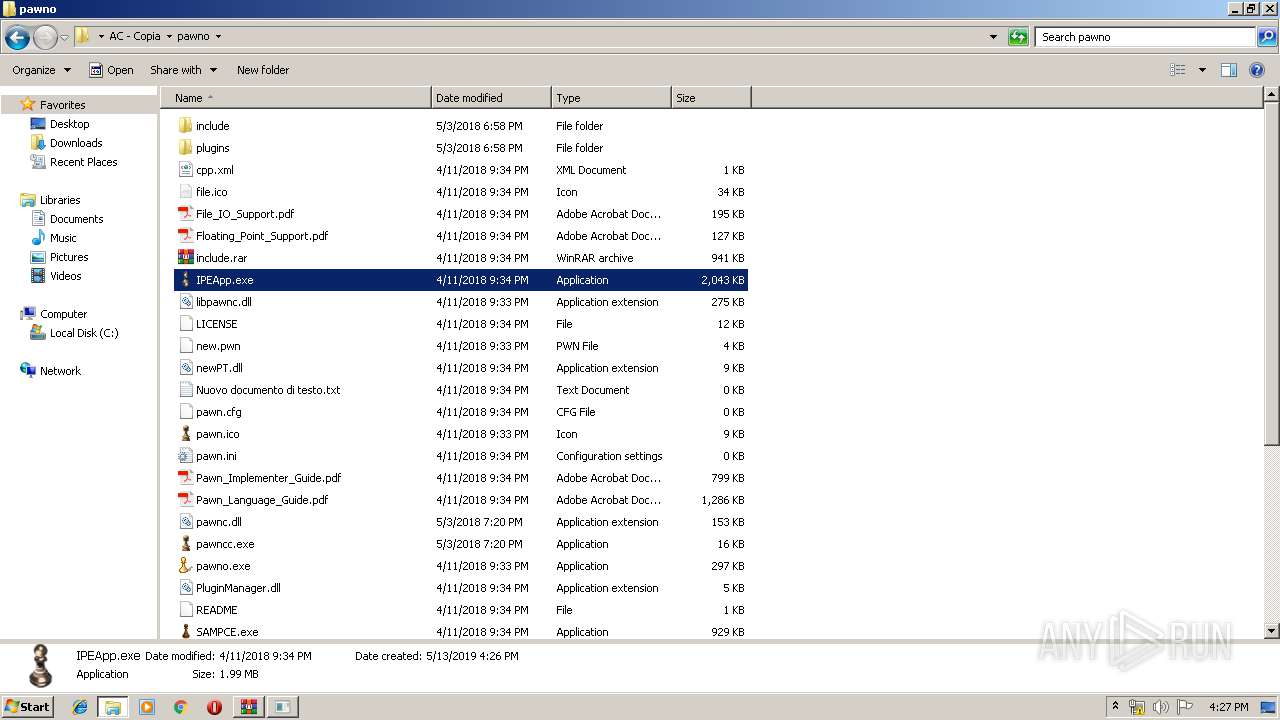
| 3080 | "C:\Users\admin\Desktop\AC - Copia\pawno\pawncc.exe" | C:\Users\admin\Desktop\AC - Copia\pawno\pawncc.exe | — | explorer.exe | |||||||||||
User: admin Company: ITB CompuPhase Integrity Level: MEDIUM Description: Pawn Compiler library Exit code: 3 Version: 3.2.3664 Modules
| |||||||||||||||
Total events
5 917
Read events
5 227
Write events
690
Delete events
0
Modification events
| (PID) Process: | (1872) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1872) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1872) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1872) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\14.zip | |||
| (PID) Process: | (1872) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1872) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1872) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1872) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (116) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.zip\OpenWithList |
| Operation: | write | Name: | a |
Value: WinRAR.exe | |||
| (PID) Process: | (116) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.zip\OpenWithList |
| Operation: | write | Name: | MRUList |
Value: a | |||
Executable files
32
Suspicious files
11
Text files
545
Unknown types
16
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1872 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1872.18121\AC - Copia\gamemodes\United.amx | — | |
MD5:— | SHA256:— | |||
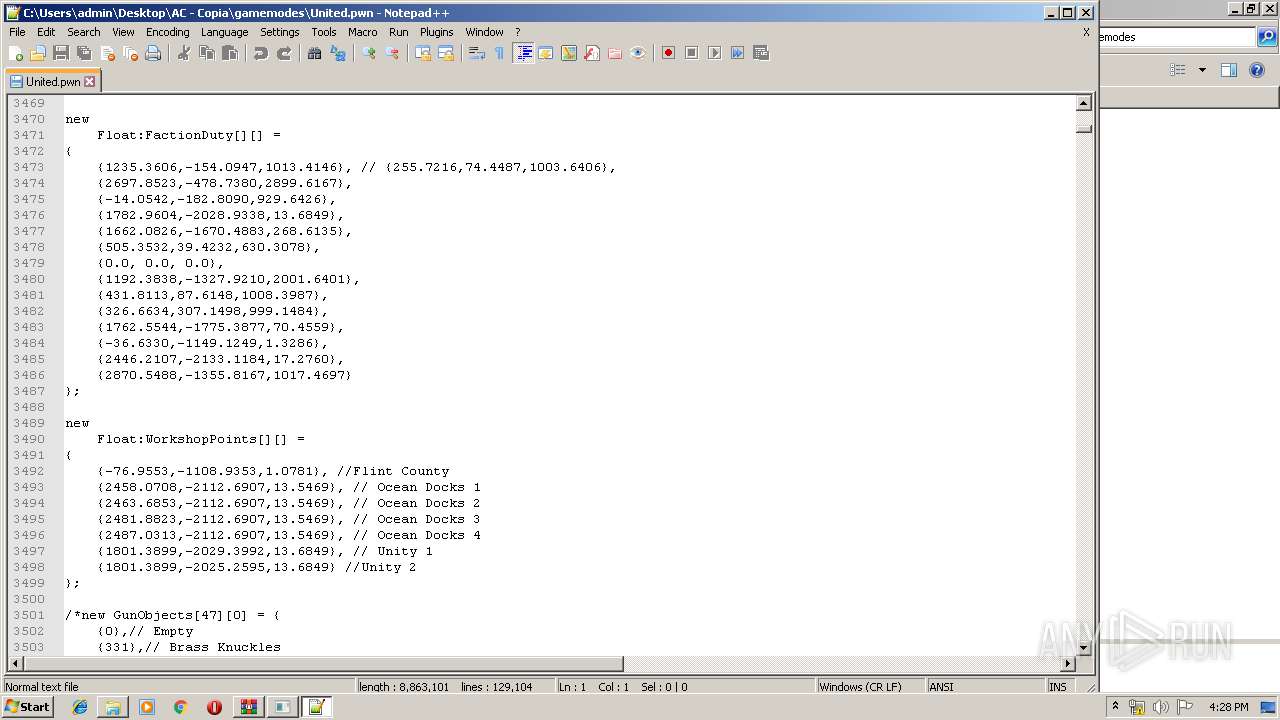
| 1872 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1872.18121\AC - Copia\gamemodes\United.pwn | — | |
MD5:— | SHA256:— | |||
| 1872 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1872.18121\AC - Copia\pawno\file.ico | image | |
MD5:— | SHA256:— | |||
| 1872 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1872.18121\AC - Copia\pawno\File_IO_Support.pdf | ||
MD5:— | SHA256:— | |||
| 1872 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1872.18121\AC - Copia\pawno\include\amx\amx.inc | text | |
MD5:— | SHA256:— | |||
| 1872 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1872.18121\AC - Copia\pawno\include.rar | compressed | |
MD5:— | SHA256:— | |||
| 1872 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1872.18121\AC - Copia\pawno\Floating_Point_Support.pdf | ||
MD5:— | SHA256:— | |||
| 1872 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1872.18121\AC - Copia\pawno\include\amx\amx_header.inc | text | |
MD5:— | SHA256:— | |||
| 1872 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1872.18121\AC - Copia\pawno\include\amx\amx_memory.inc | text | |
MD5:— | SHA256:— | |||
| 1872 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1872.18121\AC - Copia\pawno\include\amx\asm.inc | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
3
DNS requests
3
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3828 | IPEApp.exe | GET | 404 | 74.125.140.82:80 | http://ipeapp.googlecode.com/files/update.htm | US | html | 1.54 Kb | suspicious |
3828 | IPEApp.exe | GET | 404 | 74.125.140.82:80 | http://ipeapp.googlecode.com/files/update.htm | US | html | 1.54 Kb | suspicious |
— | — | GET | 200 | 2.20.189.204:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | unknown | der | 1.37 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3828 | IPEApp.exe | 74.125.140.82:80 | ipeapp.googlecode.com | Google Inc. | US | whitelisted |
4068 | gup.exe | 37.59.28.236:443 | notepad-plus-plus.org | OVH SAS | FR | whitelisted |
— | — | 2.20.189.204:80 | isrg.trustid.ocsp.identrust.com | Akamai International B.V. | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ipeapp.googlecode.com |
| suspicious |
notepad-plus-plus.org |
| whitelisted |
isrg.trustid.ocsp.identrust.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3828 | IPEApp.exe | Potential Corporate Privacy Violation | ET POLICY Suspicious Malformed Double Accept Header |
3828 | IPEApp.exe | Potential Corporate Privacy Violation | ET POLICY Suspicious Malformed Double Accept Header |
Process | Message |
|---|---|
samp-npc.exe | ----- NPC Starting ----- |
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | 42C4C5846BB675C74E2B2C90C69AB44366401093
|