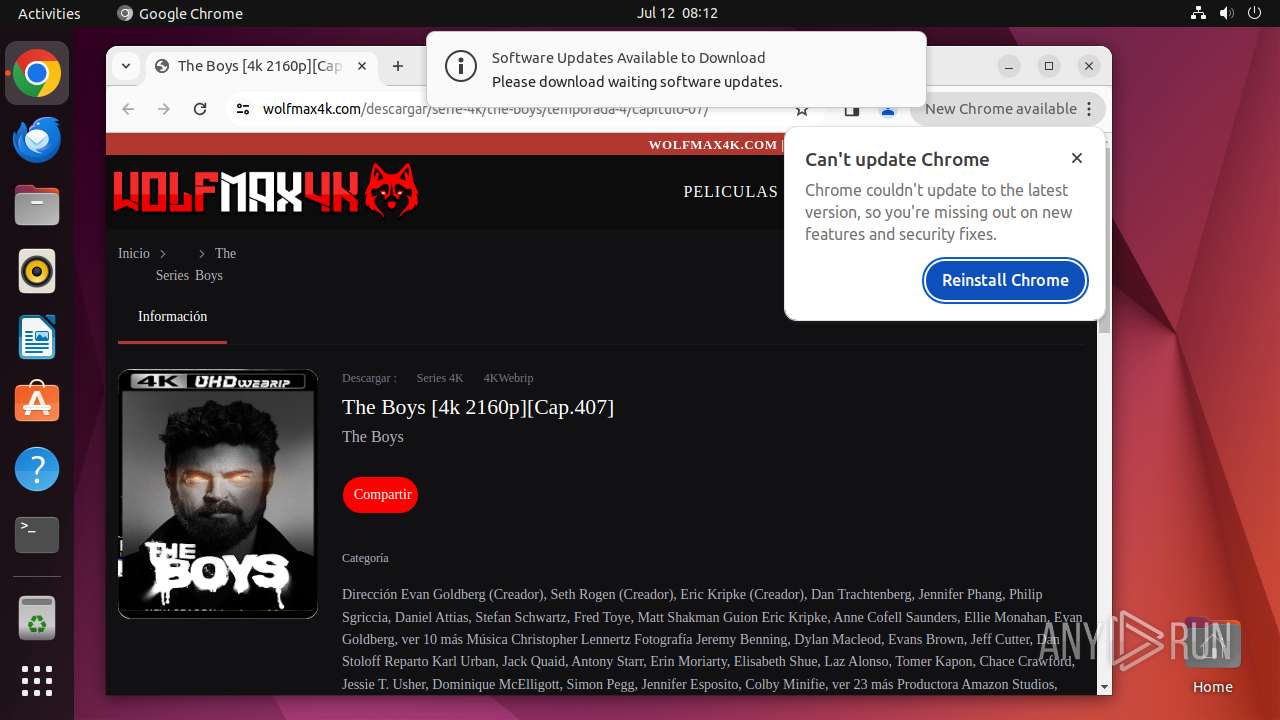
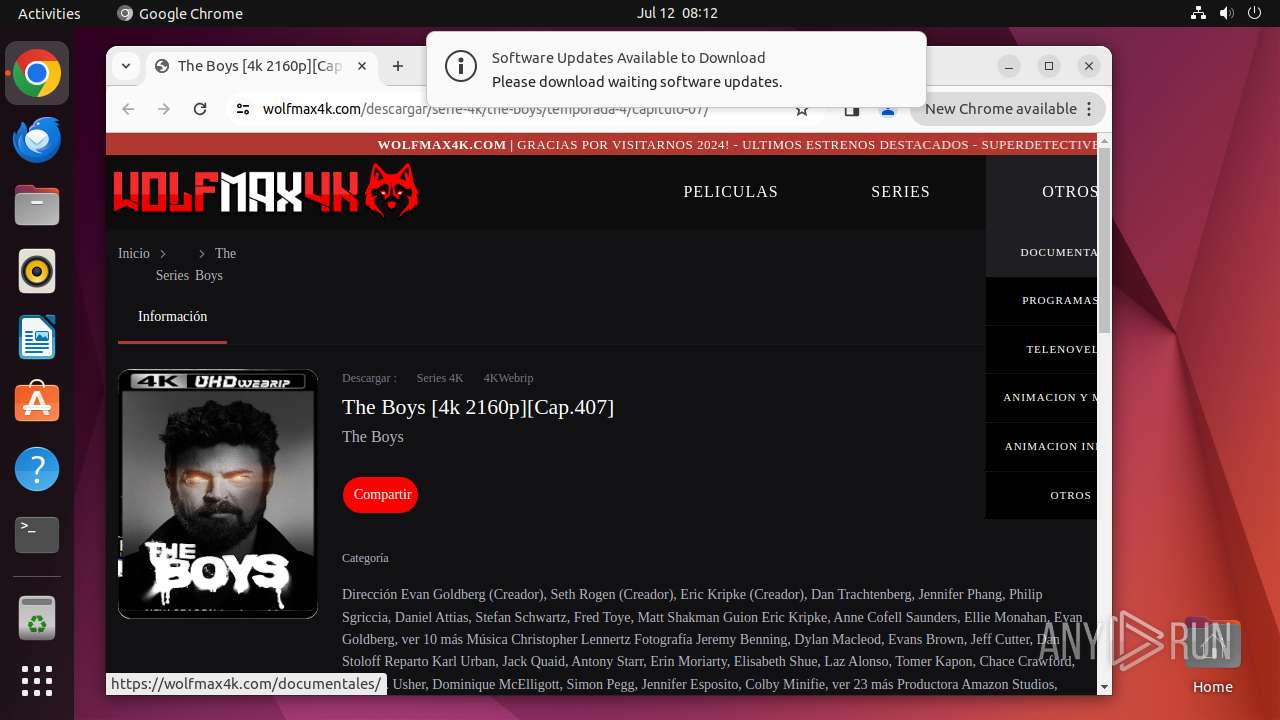
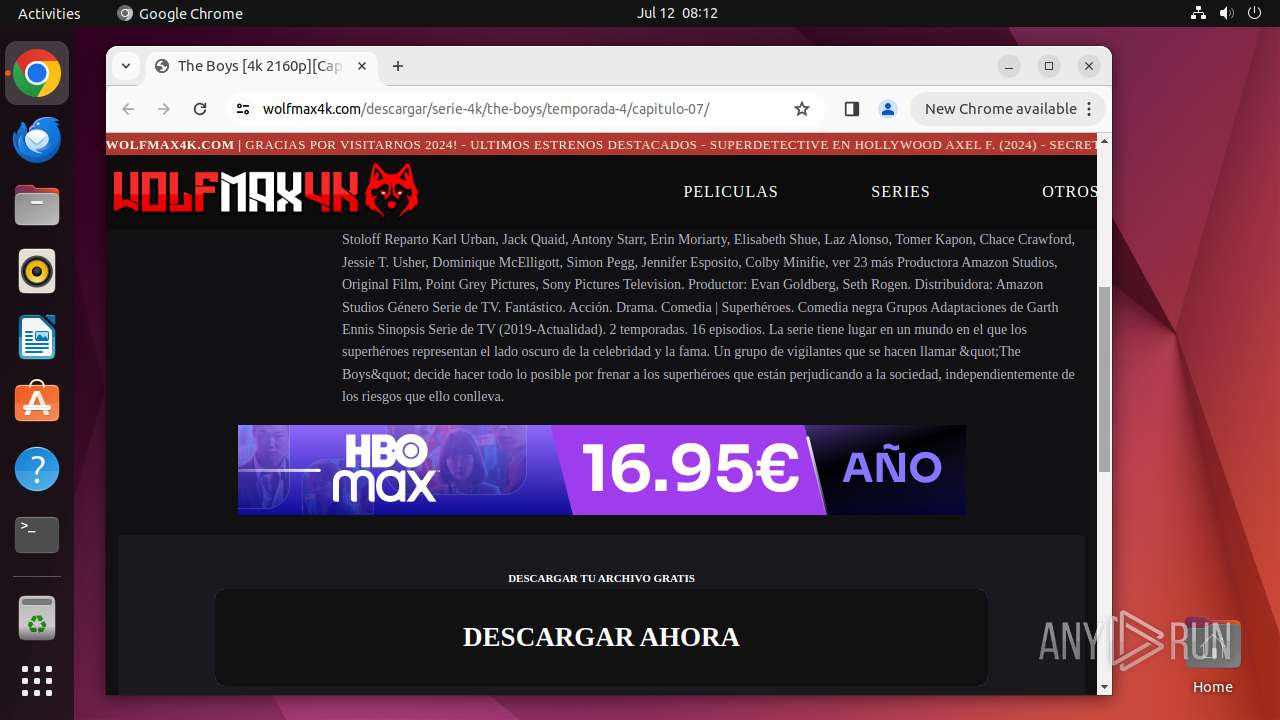
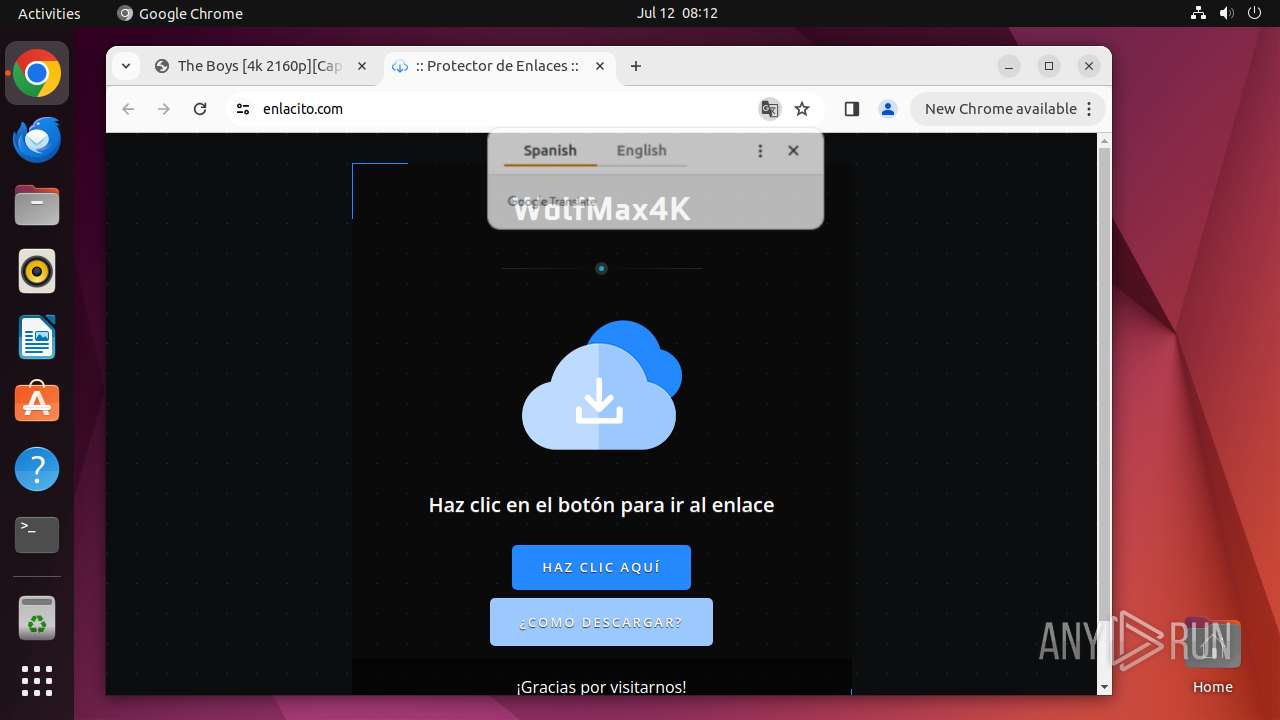
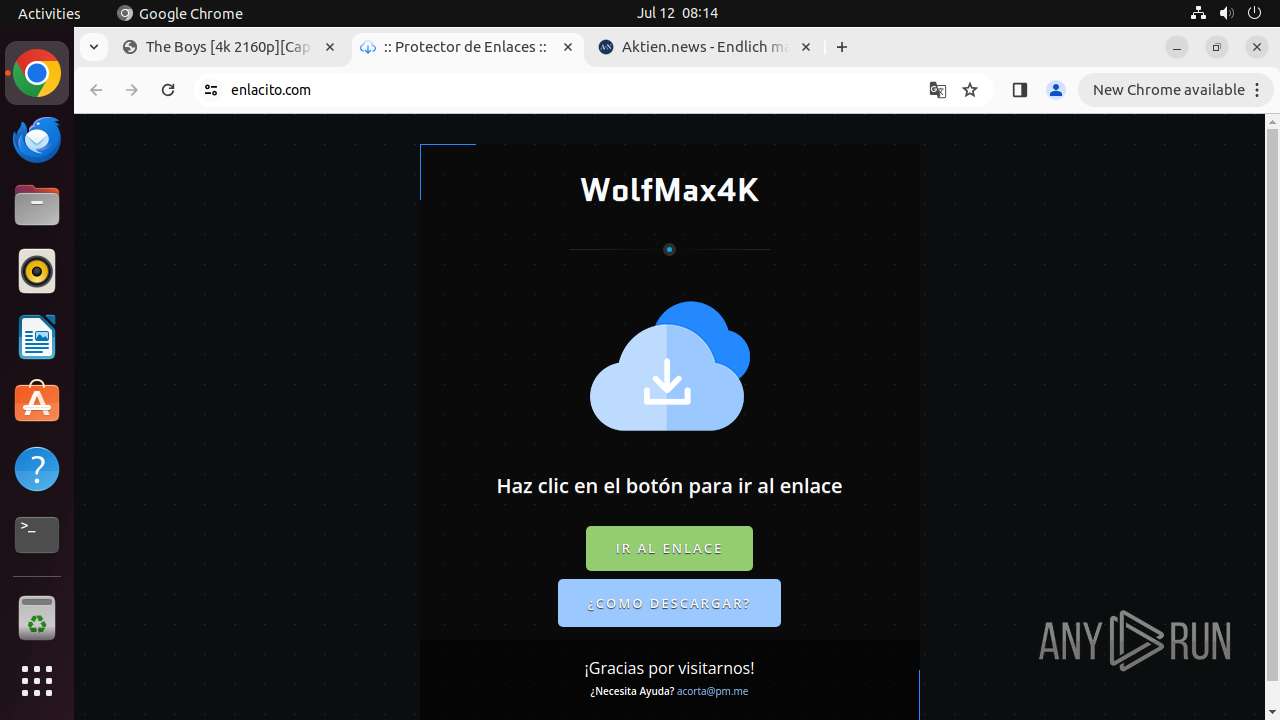
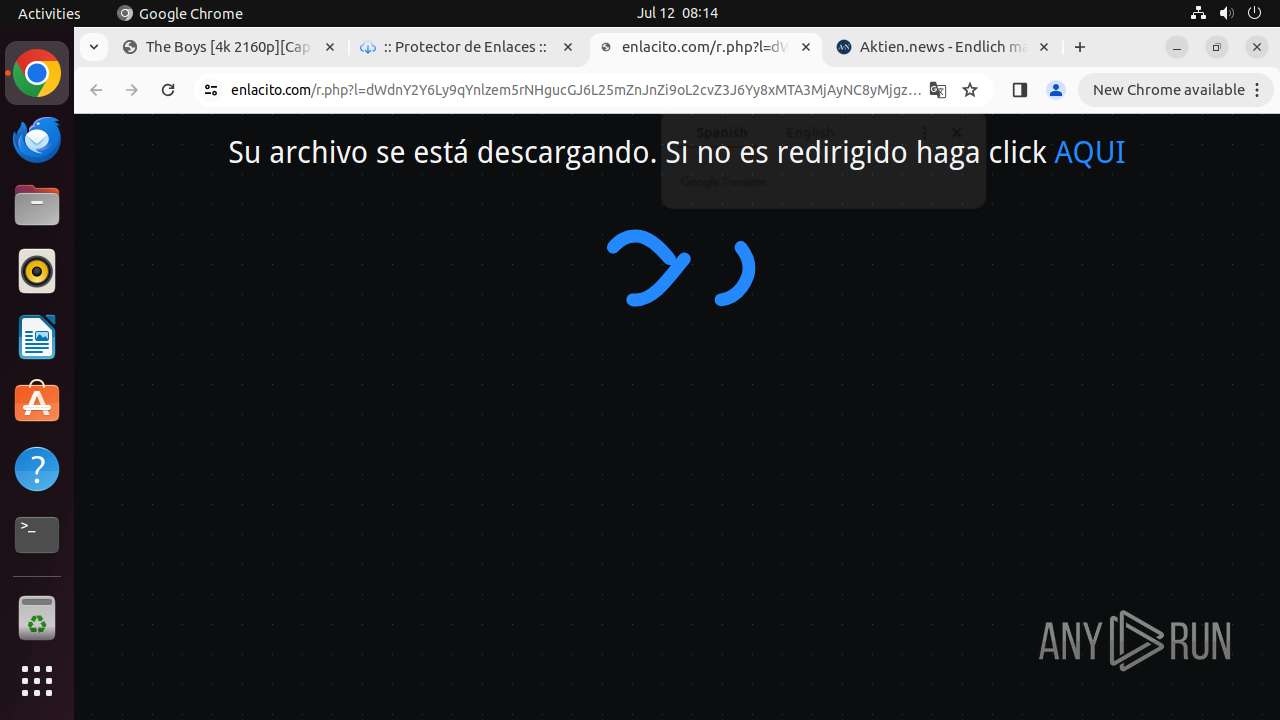
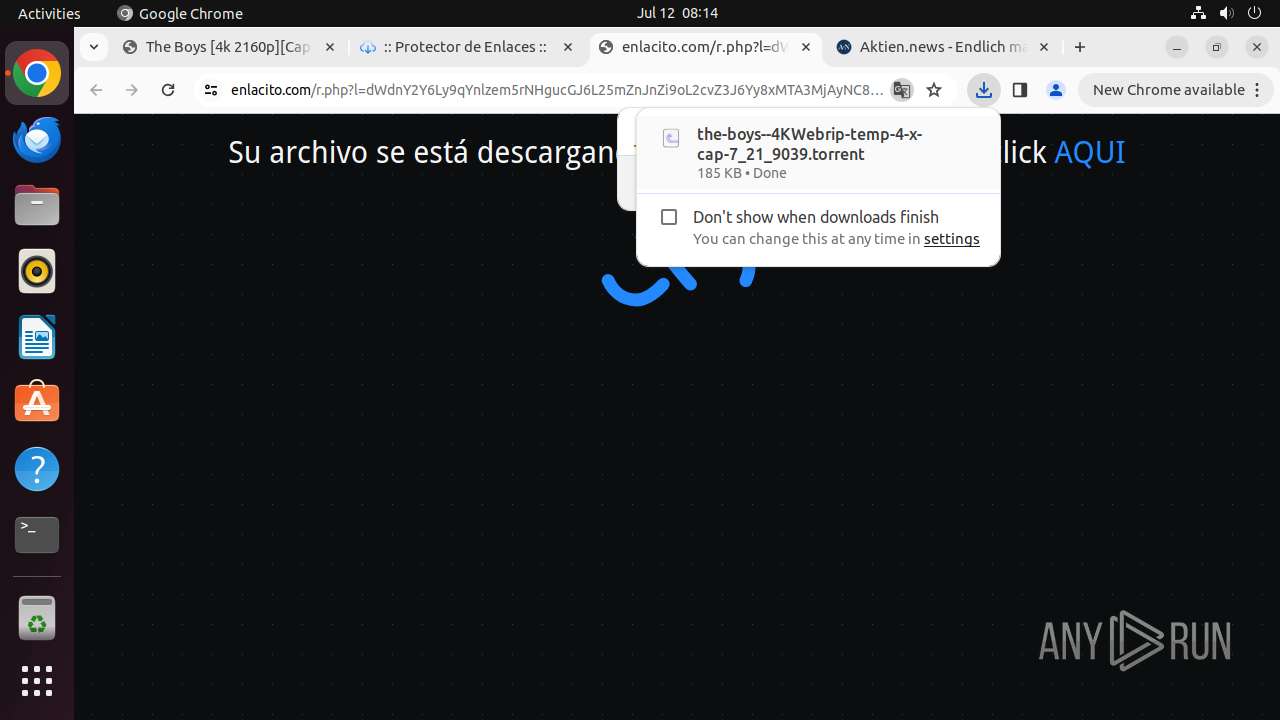
| URL: | https://wolfmax4k.com/descargar/serie-4k/the-boys/temporada-4/capitulo-07/ |
| Full analysis: | https://app.any.run/tasks/d5f8ad9d-aeab-4e1e-9dc2-298ce833f22e |
| Verdict: | Malicious activity |
| Analysis date: | July 12, 2024, 07:12:15 |
| OS: | Ubuntu 22.04.2 |
| MD5: | 9C38D41DD71125DC7CF37E51FD3CCEAB |
| SHA1: | 7387526EE2587BC070237DCC531915CE5F5AF9B0 |
| SHA256: | B5919801DCBB0950F7F3F0A856AC811A768434BD83A97F2CB4A9BB8978FA7631 |
| SSDEEP: | 3:N8bJUHR2WbiXuXeXtp:2OgtXuu9p |
MALICIOUS
No malicious indicators.SUSPICIOUS
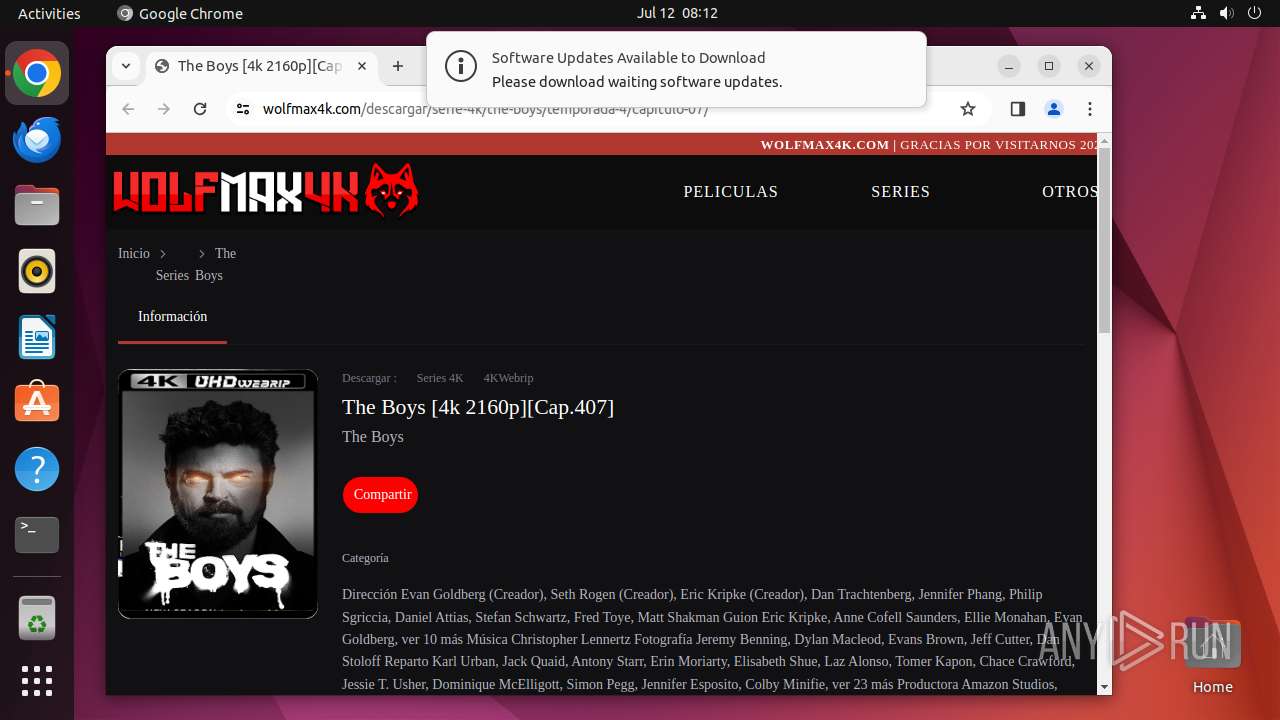
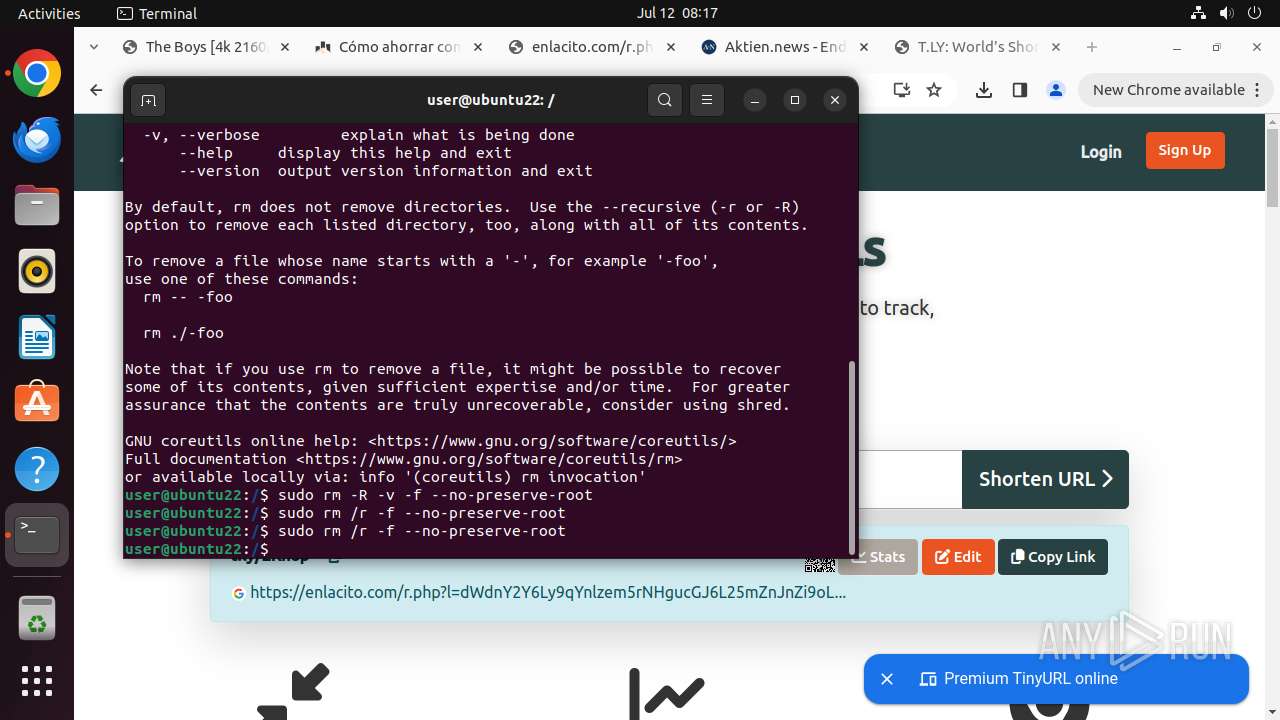
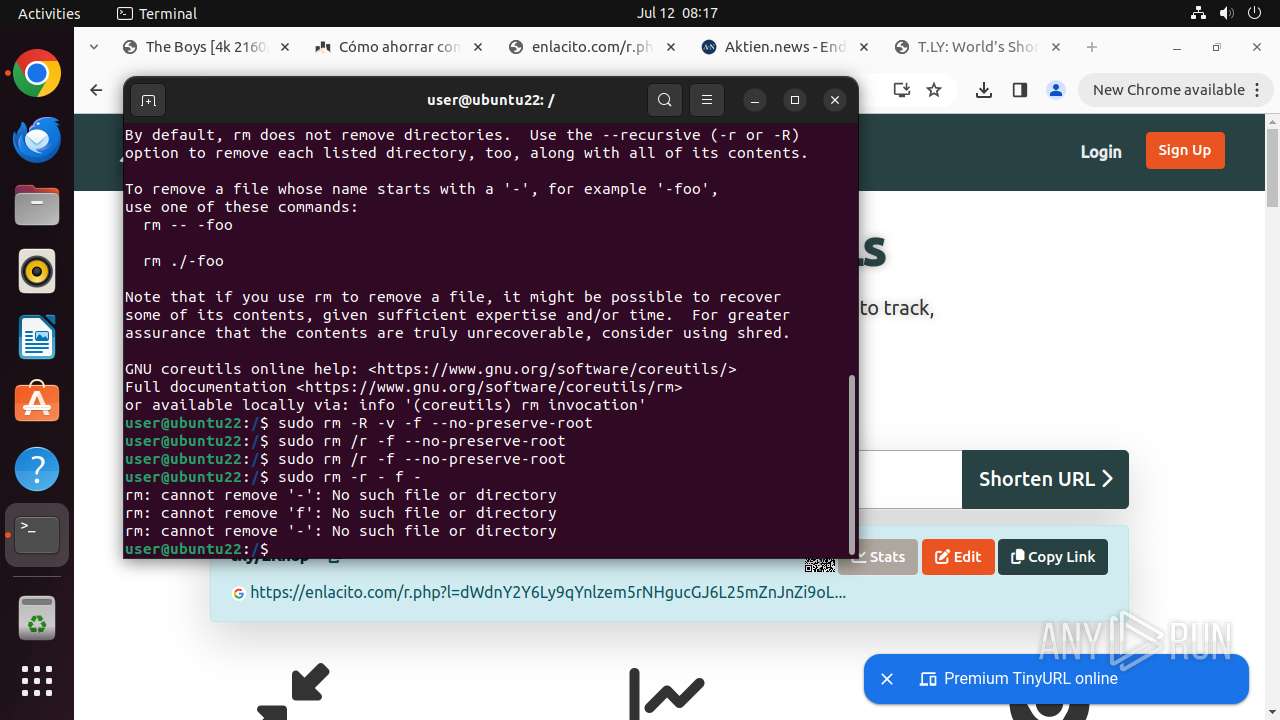
Executes commands using command-line interpreter
- update-notifier (PID: 13480)
- gnome-terminal-server (PID: 13639)
- cron (PID: 13684)
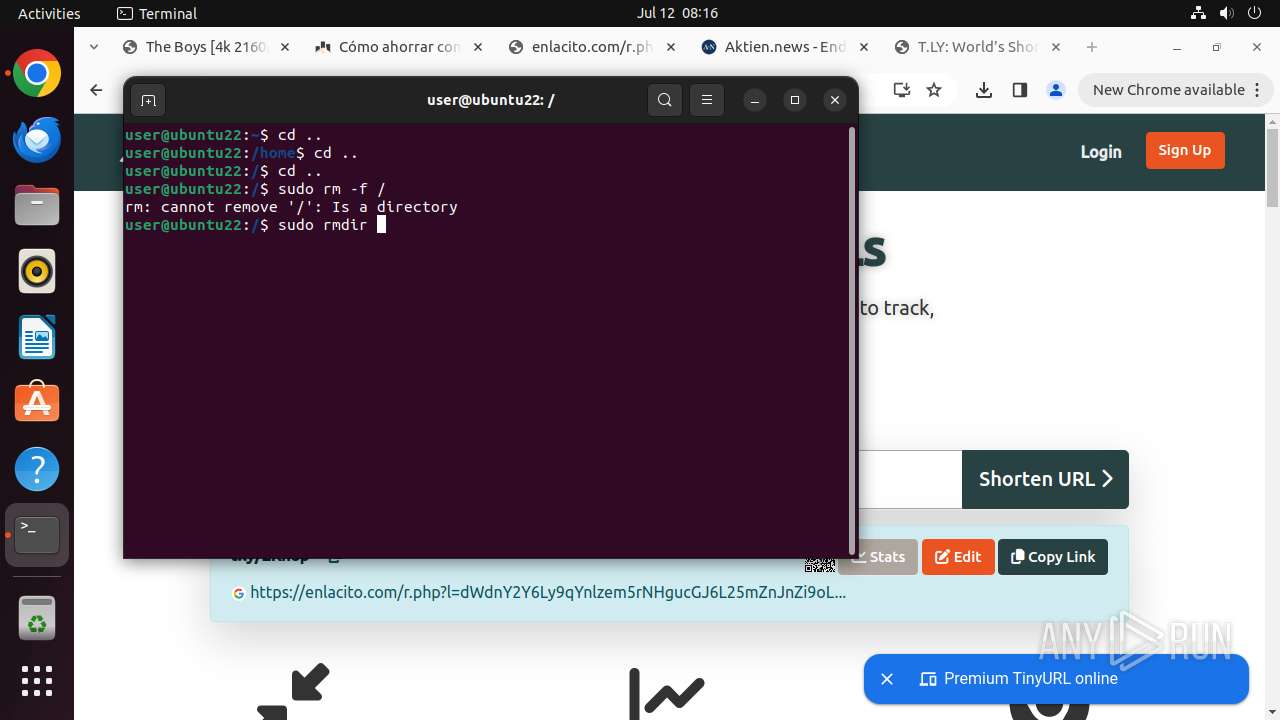
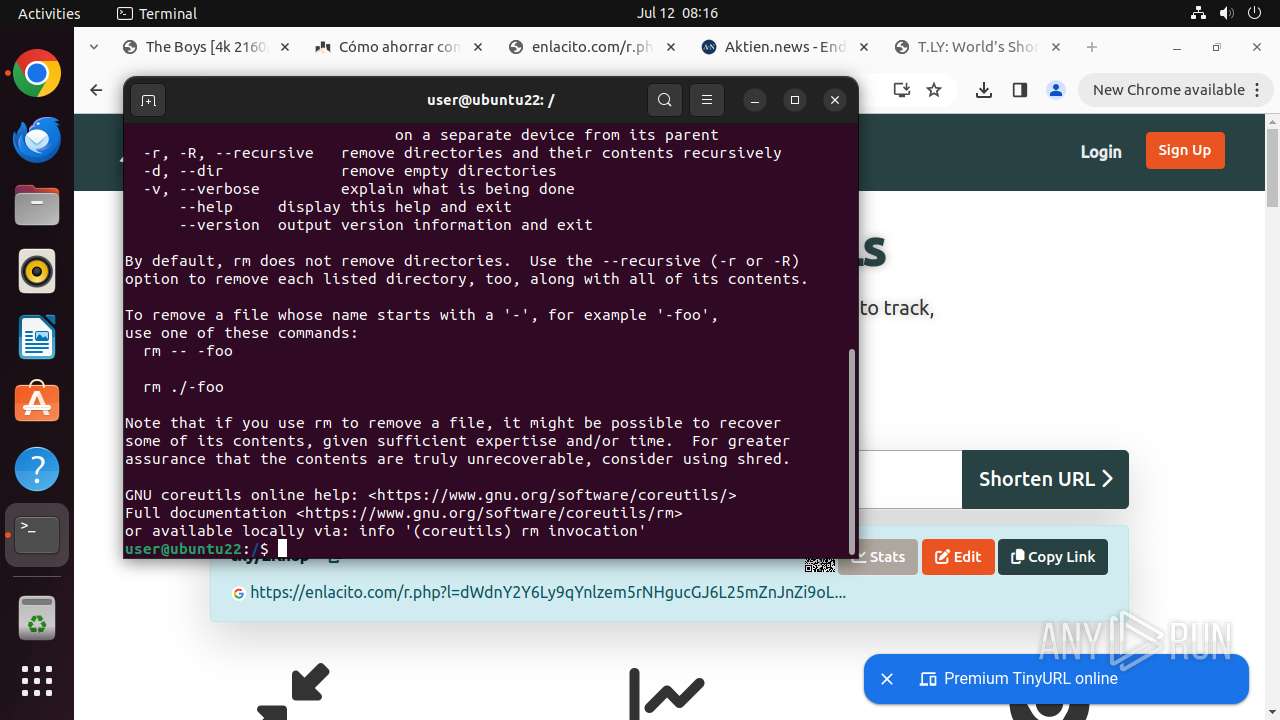
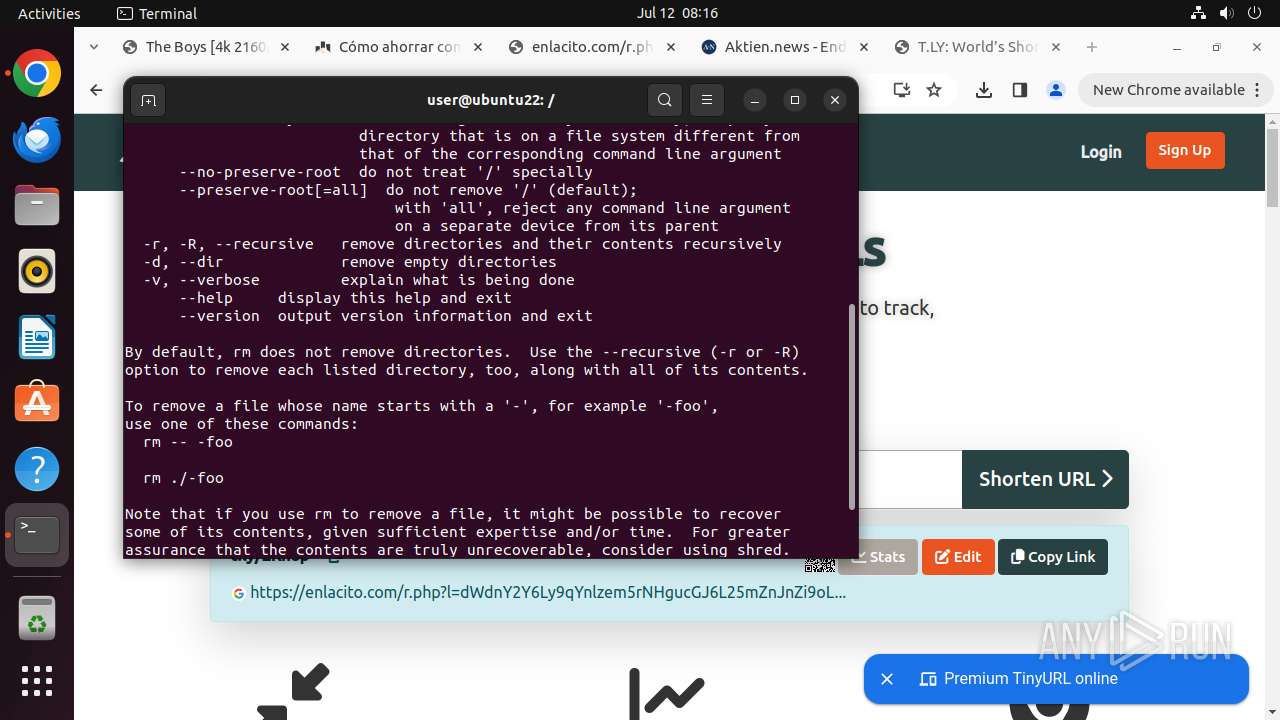
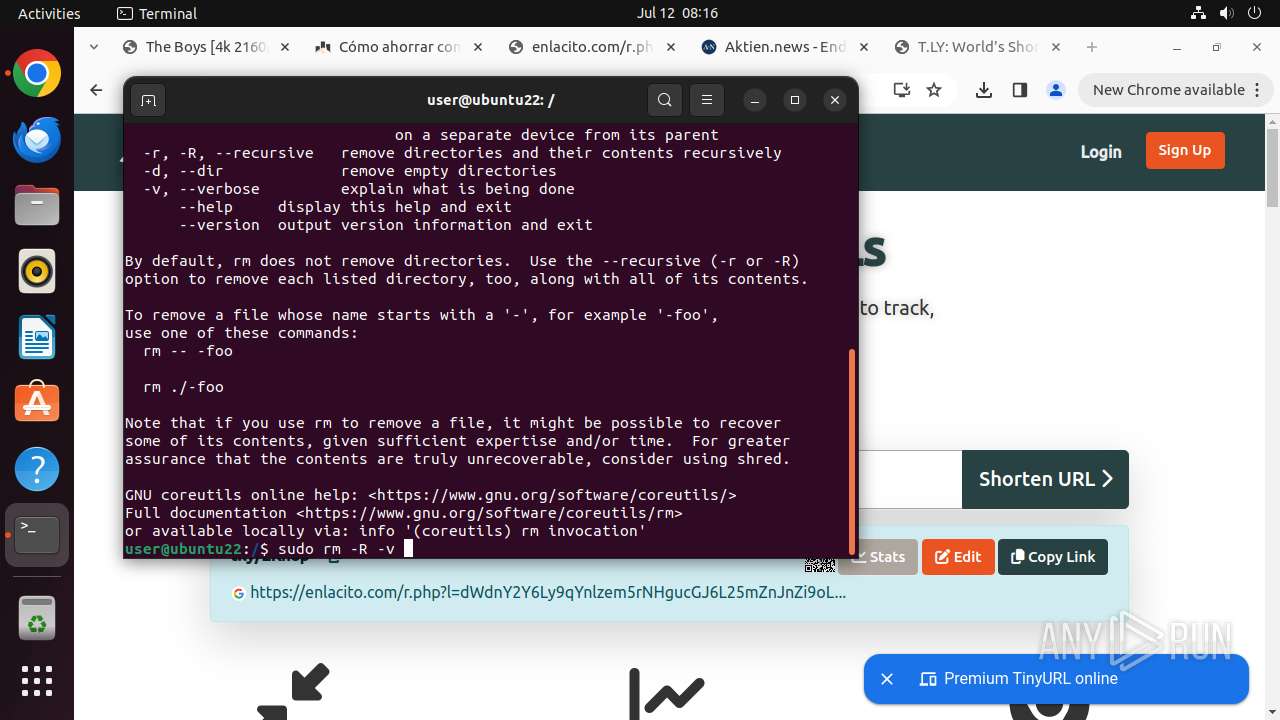
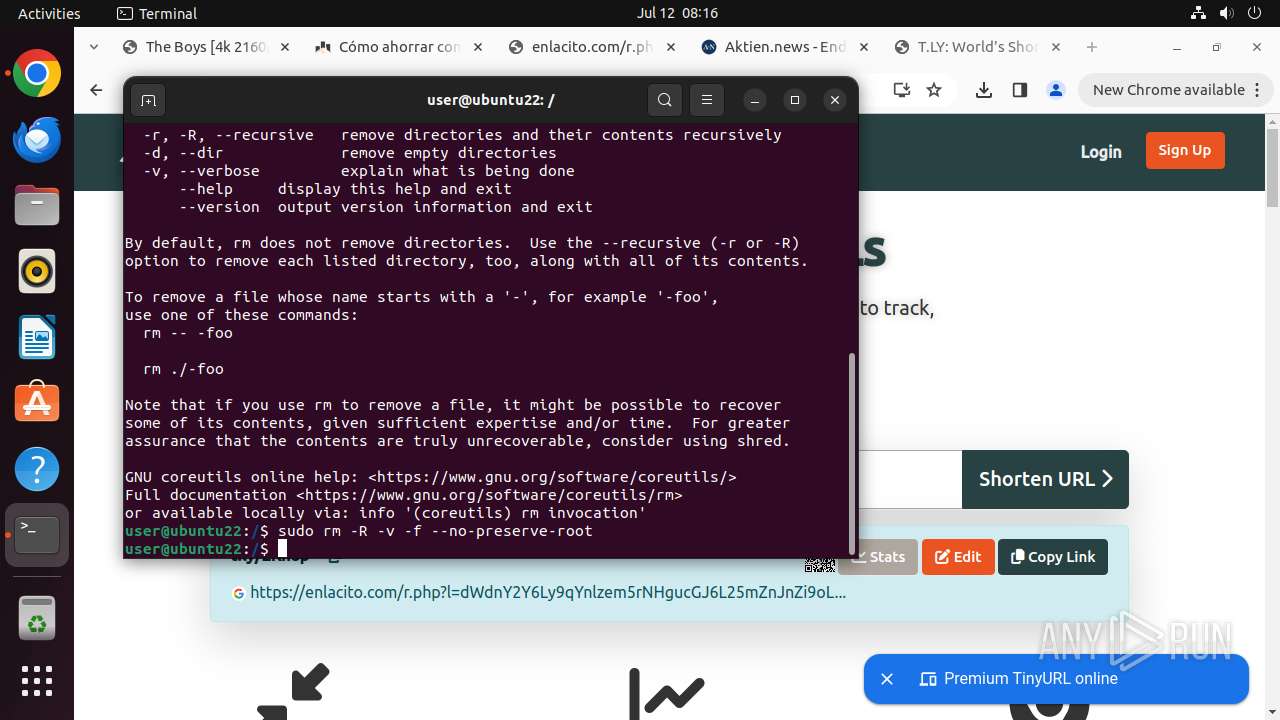
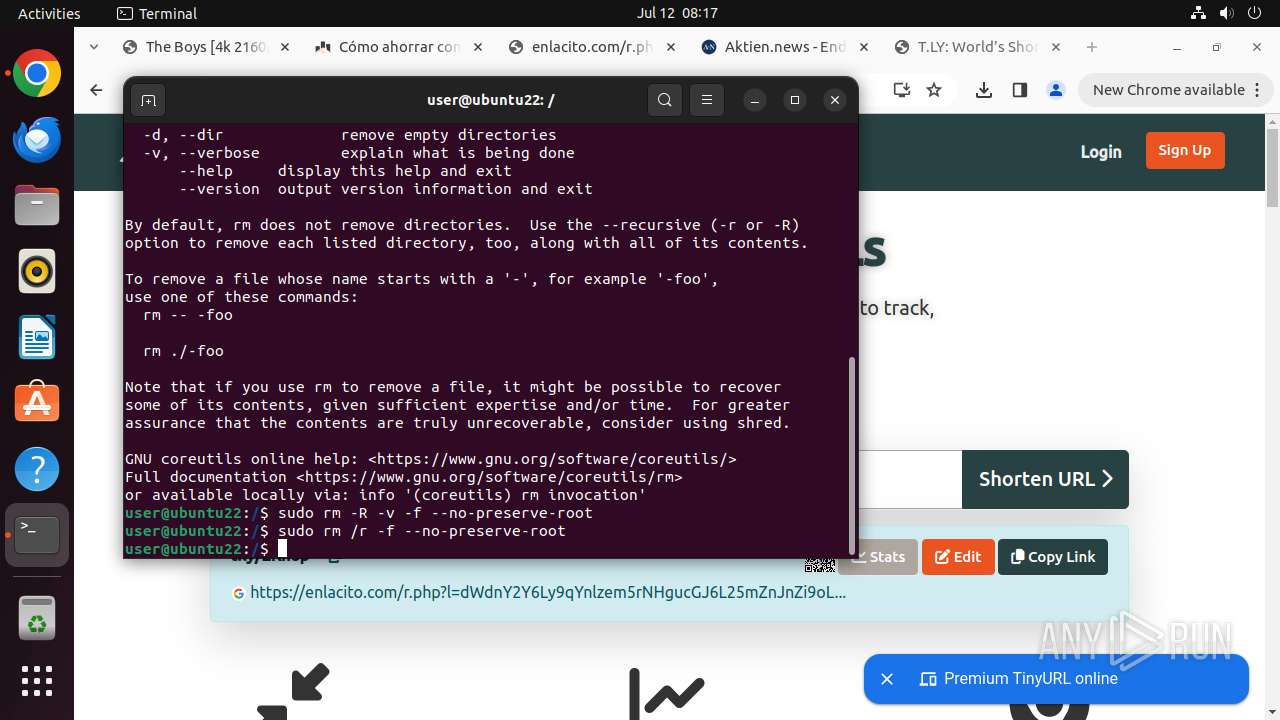
Executes the "rm" command to delete files or directories
- sudo (PID: 13671)
- sudo (PID: 13678)
- sudo (PID: 13691)
- sudo (PID: 13688)
- sudo (PID: 13682)
- sudo (PID: 13694)
Checks the user who created the process
- cron (PID: 13684)
Reads /proc/mounts (likely used to find writable filesystems)
- check-new-release-gtk (PID: 13482)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
385
Monitored processes
170
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 12931 | /bin/sh -c "DISPLAY=:0 sudo -iu user google-chrome https://wolfmax4k\.com/descargar/serie-4k/the-boys/temporada-4/capitulo-07/ " | /bin/sh | — | any-guest-agent |
User: root Integrity Level: UNKNOWN | ||||
| 12932 | sudo -iu user google-chrome https://wolfmax4k.com/descargar/serie-4k/the-boys/temporada-4/capitulo-07/ | /usr/bin/sudo | — | sh |
User: root Integrity Level: UNKNOWN | ||||
| 12933 | /usr/bin/google-chrome https://wolfmax4k.com/descargar/serie-4k/the-boys/temporada-4/capitulo-07/ | /opt/google/chrome/chrome | sudo | |
User: user Integrity Level: UNKNOWN | ||||
| 12934 | /usr/bin/locale-check C.UTF-8 | /usr/bin/locale-check | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 12935 | readlink -f /usr/bin/google-chrome | /usr/bin/readlink | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 12936 | dirname /opt/google/chrome/google-chrome | /usr/bin/dirname | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 12937 | mkdir -p /home/user/.local/share/applications | /usr/bin/mkdir | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 12938 | cat | /usr/bin/cat | — | chrome |
User: user Integrity Level: UNKNOWN | ||||
| 12939 | cat | /usr/bin/cat | — | chrome |
User: user Integrity Level: UNKNOWN | ||||
| 12940 | /opt/google/chrome/chrome | — | chrome | |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
Executable files
7
Suspicious files
520
Text files
46
Unknown types
44
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 12933 | chrome | /home/user/.config/google-chrome/ShaderCache/data_3 | binary | |
MD5:— | SHA256:— | |||
| 12933 | chrome | /home/user/.config/google-chrome/ShaderCache/data_2 | vxd | |
MD5:— | SHA256:— | |||
| 12933 | chrome | /home/user/.config/google-chrome/ShaderCache/data_0 | binary | |
MD5:— | SHA256:— | |||
| 12933 | chrome | /home/user/.config/google-chrome/Default/GPUCache/data_3 | vxd | |
MD5:— | SHA256:— | |||
| 12933 | chrome | /home/user/.config/google-chrome/Default/GPUCache/data_2 | vxd | |
MD5:— | SHA256:— | |||
| 12933 | chrome | /home/user/.config/google-chrome/Default/GPUCache/data_0 | vxd | |
MD5:— | SHA256:— | |||
| 12933 | chrome | /home/user/.config/google-chrome/Default/DawnCache/data_3 | vxd | |
MD5:— | SHA256:— | |||
| 12933 | chrome | /home/user/.config/google-chrome/Default/DawnCache/data_2 | vxd | |
MD5:— | SHA256:— | |||
| 12933 | chrome | /home/user/.config/google-chrome/Default/DawnCache/data_0 | vxd | |
MD5:— | SHA256:— | |||
| 13077 | chrome | /home/user/.cache/mesa_shader_cache/index | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
289
DNS requests
260
Threats
11
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/n4jhhmkouwdq5a5pt3k6lmblae_456/lmelglejhemejginpboagddgdfbepgmp_456_all_ZZ_adatthpmxfx3v7y6geszldjbsq2a.crx3 | unknown | — | — | whitelisted |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ojhxwvpzdxwgve6bpgoze4e7eu_20240628.650087159.14/obedbbhbpmojnkanicioggnmelmoomoc_20240628.650087159.14_all_ENGB500000_adezrvdzerc7uewsyz4rwzqbgpdq.crx3 | unknown | — | — | whitelisted |
— | — | GET | 204 | 185.125.190.96:80 | http://connectivity-check.ubuntu.com/ | unknown | — | — | whitelisted |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvZjQwNTJmYzgtMzk5Yi00OTMxLTk0ZTQtMDlmZDM1MDk0MDM5/1.0.0.16_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | unknown | — | — | whitelisted |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/diffgen-puffin/khaoiebndkojlmppeemjhbpbandiljpe/1.a9dcdb84b51dfb80ecd937f7775193f7c50fab755f256202e382db7a49207190/1.1471c6c104c7e11f08fd446f83dcdb396b1fef335f4e3c744007c2272064f538/cf7a3395d1c87e8889d87c7cfe0924969f2dfcdb282fd8d974db8069017ee67d.puff | unknown | — | — | whitelisted |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/diffgen-puffin/kiabhabjdbkjdpjbpigfodbdjmbglcoo/1.f6cc30e6a2d15e778f6701074d1f4b4505db1f516e06c9969160e0d6c62c5837/1.153e9301be7e862a33e2cab936a0a97e2f8bdf2dae1be516d6fe8a5f184ce028/abe599c5e7c450e0e3bfebef2d768b2903a8f50780214f1b81006d26589c3fc9.puff | unknown | — | — | whitelisted |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/diffgen-puffin/jflookgnkcckhobaglndicnbbgbonegd/1.e232391b105870e13719796efea3025cbd6ac95d2a97b88d4404c92eed8eb8c2/1.888ebbd183d017421d0f23a0a1ea9eaedffefd772878d86c67536c138ef62ada/e14cfc1fc47e48a5521008562d65b5093e414f7b64b555abe6c2c4990f7c5179.puff | unknown | — | — | whitelisted |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad7xh6r5xfkfvg6hbt67stcajfga_8927/hfnkpimlhhgieaddgfemjhofmfblmnib_8927_all_d7z5zv5d6pjpg2inojimrjfz5y.crx3 | unknown | — | — | whitelisted |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad6jo3mvdsele4tqkopcoszo5t4a_2024.7.10.0/niikhdgajlphfehepabhhblakbdgeefj_2024.07.10.00_all_adnawimxi6ejyg73g5el2z3actia.crx3 | unknown | — | — | whitelisted |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/bp5dqz6qlmqfelmwljejpxtis4_2024.7.10.1/jflhchccmppkfebkiaminageehmchikm_2024.07.10.01_all_krggxevftl6z7zoi24jgowttbu.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
470 | avahi-daemon | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 185.125.190.48:80 | connectivity-check.ubuntu.com | Canonical Group Limited | GB | unknown |
— | — | 91.189.91.96:80 | connectivity-check.ubuntu.com | Canonical Group Limited | US | unknown |
— | — | 185.125.190.96:80 | connectivity-check.ubuntu.com | Canonical Group Limited | GB | unknown |
— | — | 156.146.33.15:443 | odrs.gnome.org | Datacamp Limited | DE | unknown |
— | — | 142.250.186.99:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
— | — | 64.233.166.84:443 | accounts.google.com | GOOGLE | US | unknown |
— | — | 142.250.186.42:443 | safebrowsingohttpgateway.googleapis.com | GOOGLE | US | whitelisted |
— | — | 104.21.49.132:443 | wolfmax4k.com | — | — | unknown |
12933 | chrome | 239.255.255.250:1900 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
connectivity-check.ubuntu.com |
| whitelisted |
google.com |
| whitelisted |
odrs.gnome.org |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| whitelisted |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
wolfmax4k.com |
| unknown |
api.snapcraft.io |
| whitelisted |
google-ohttp-relay-safebrowsing.fastly-edge.com |
| unknown |
ajax.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
425 | systemd-resolved | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
425 | systemd-resolved | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
425 | systemd-resolved | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
— | — | Misc activity | ET INFO Observed ZeroSSL SSL/TLS Certificate |
— | — | Misc activity | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |
— | — | Misc activity | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |
— | — | Misc activity | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |
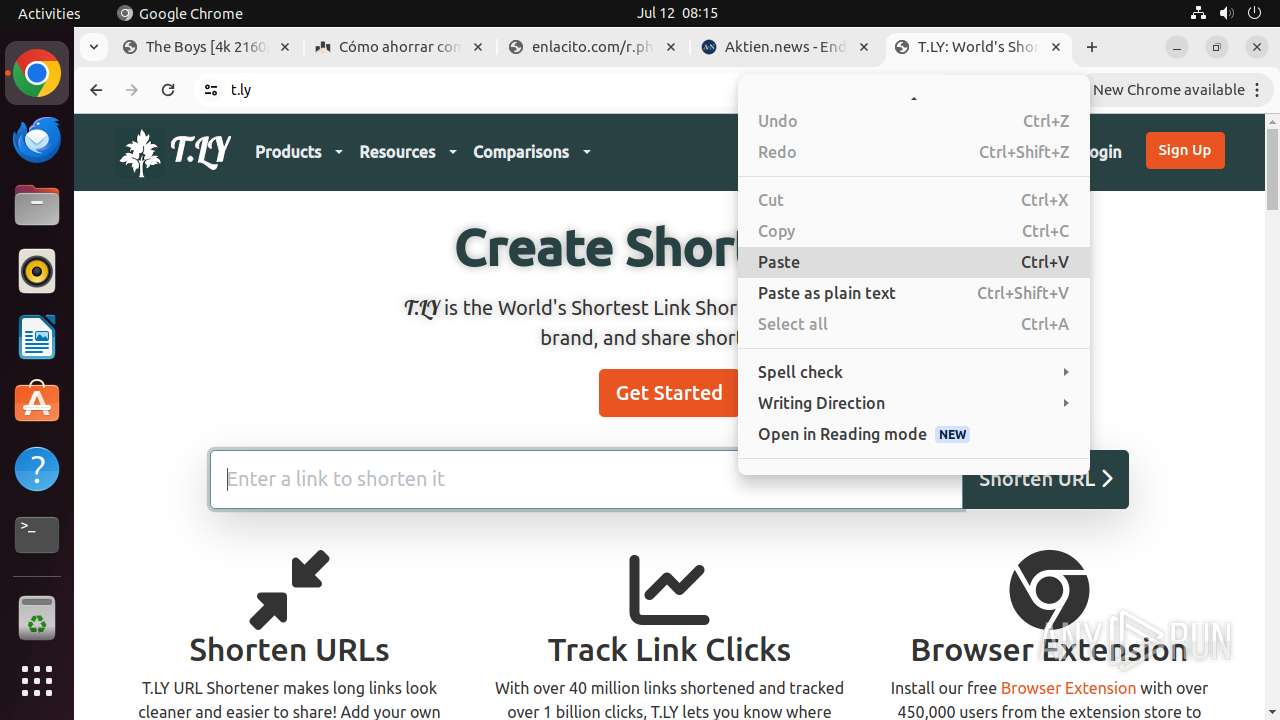
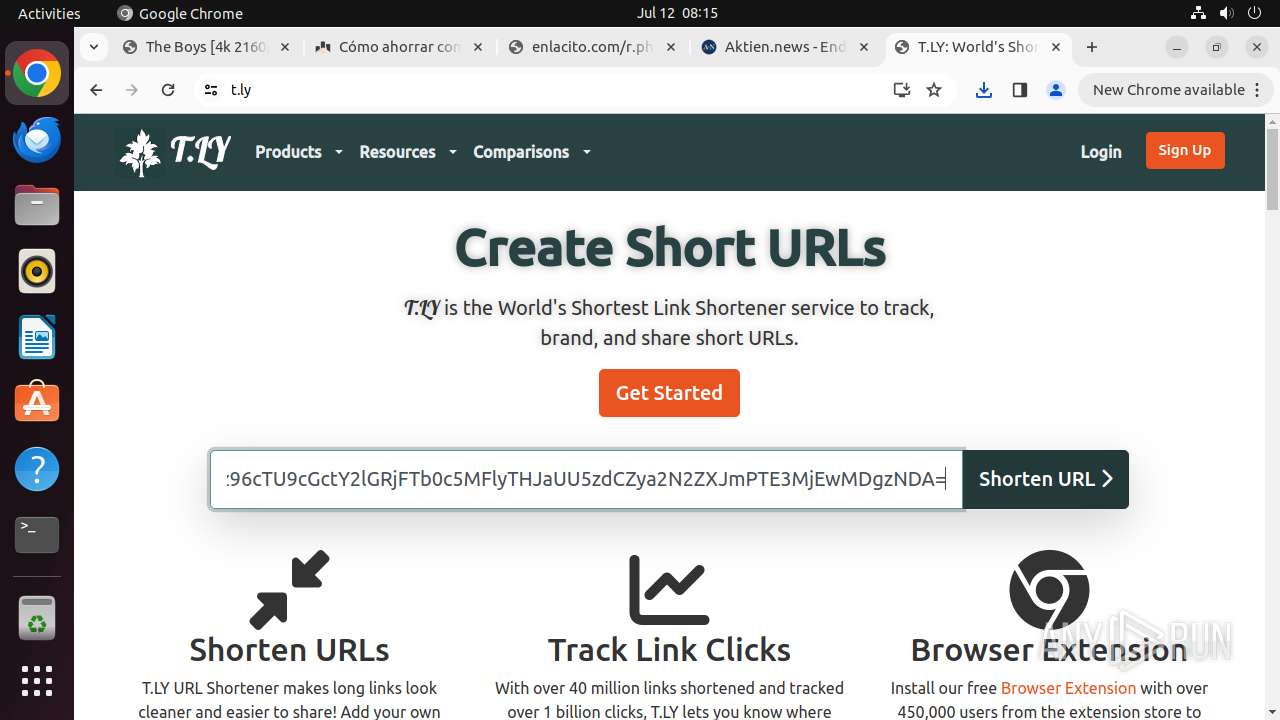
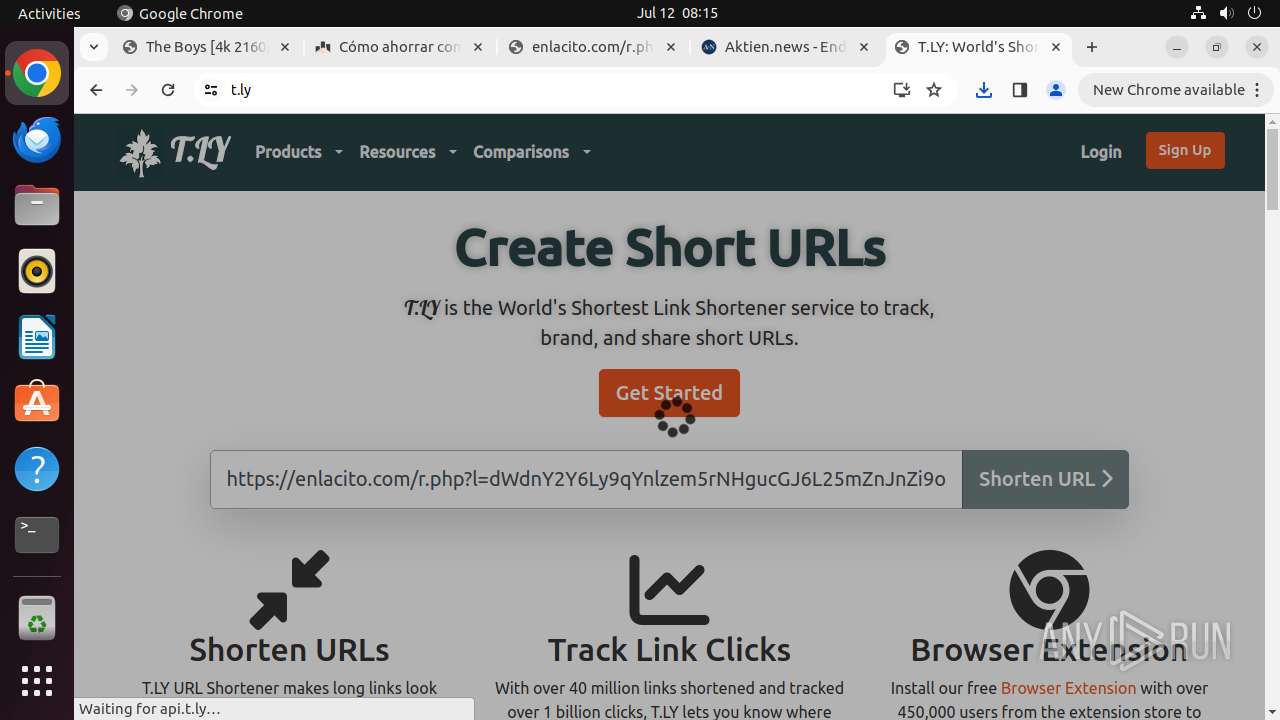
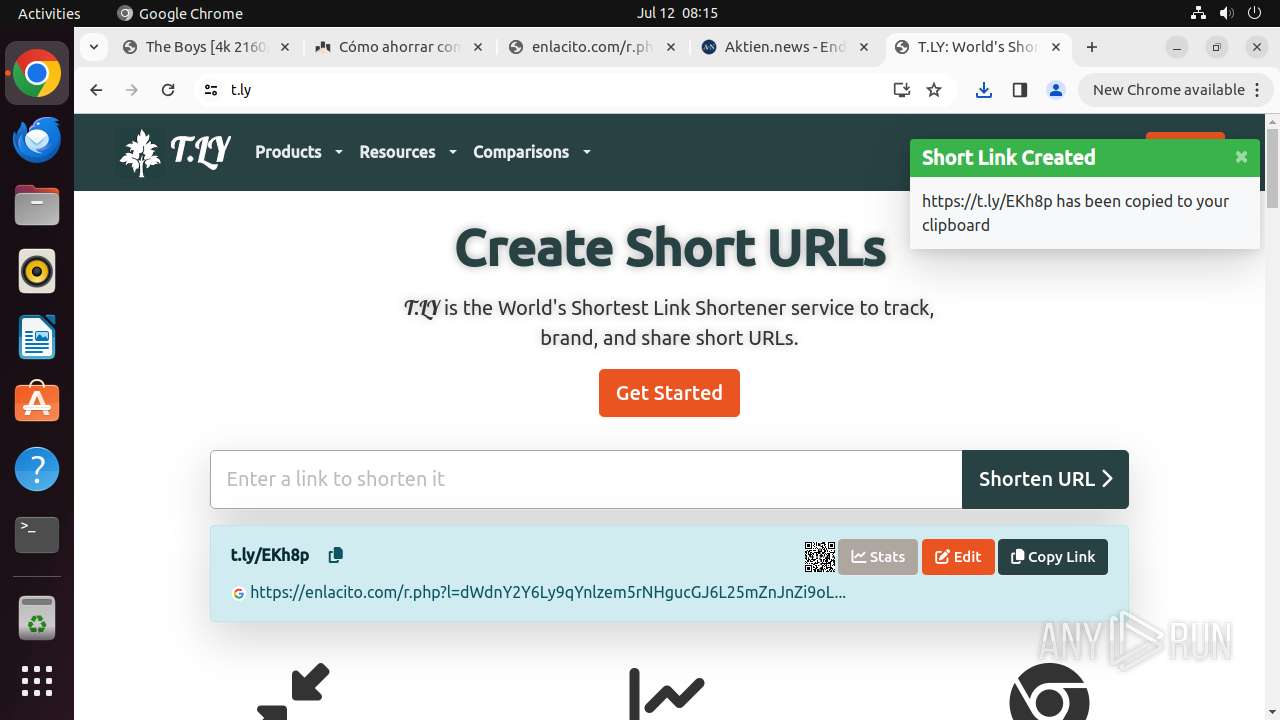
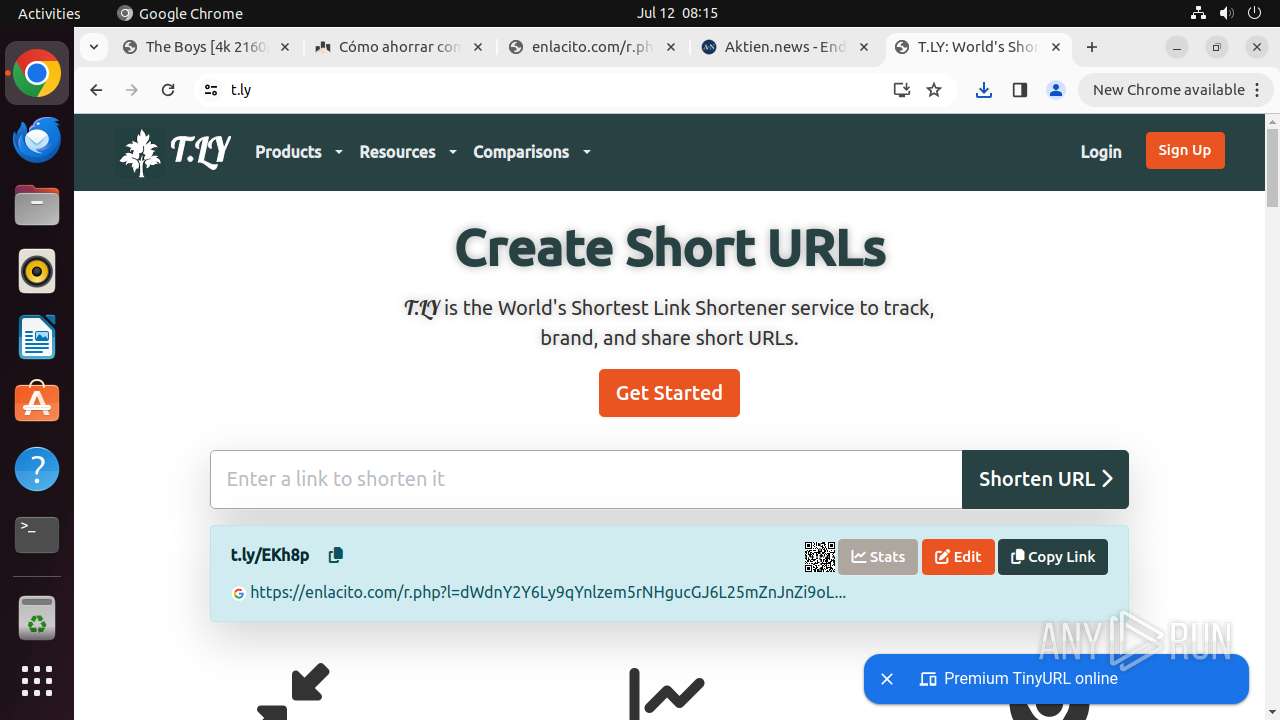
425 | systemd-resolved | Misc activity | ET INFO URL Shortening Service Domain in DNS Lookup (t .ly) |
— | — | Misc activity | ET INFO Observed URL Shortening Service Domain (t .ly in TLS SNI) |
425 | systemd-resolved | Misc activity | ET INFO URL Shortening Service Domain in DNS Lookup (t .ly) |