| File name: | C:\Users\admin\Desktop\zsvc.exe |
| Full analysis: | https://app.any.run/tasks/4ad09fa4-0d62-4a7a-9358-5c1da6b3cd5d |
| Verdict: | Malicious activity |
| Analysis date: | February 24, 2021, 18:05:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows |
| MD5: | CD0F46C33129913FEECE4A83ACF63A82 |
| SHA1: | 64B458ADD6C9A65891F2B48D19E7721B3051EDE4 |
| SHA256: | B58584134061786E3CEF8866D5836742E0EF88D053B260FCF44102990EB39D35 |
| SSDEEP: | 3072:dfaJb/HHzTGsbVY6XfRPLlv3vJMiGndRRBmRKuvZb6FMQ+6d1:Wb/HzTXPJR3v9Gn3X8Ksts |
MALICIOUS
Changes the autorun value in the registry
- zsvc.exe (PID: 2988)
- reg.exe (PID: 1500)
Runs injected code in another process
- sqhost.exe (PID: 1464)
Application was injected by another process
- conhost.exe (PID: 2728)
SUSPICIOUS
Creates files in the user directory
- cmd.exe (PID: 1400)
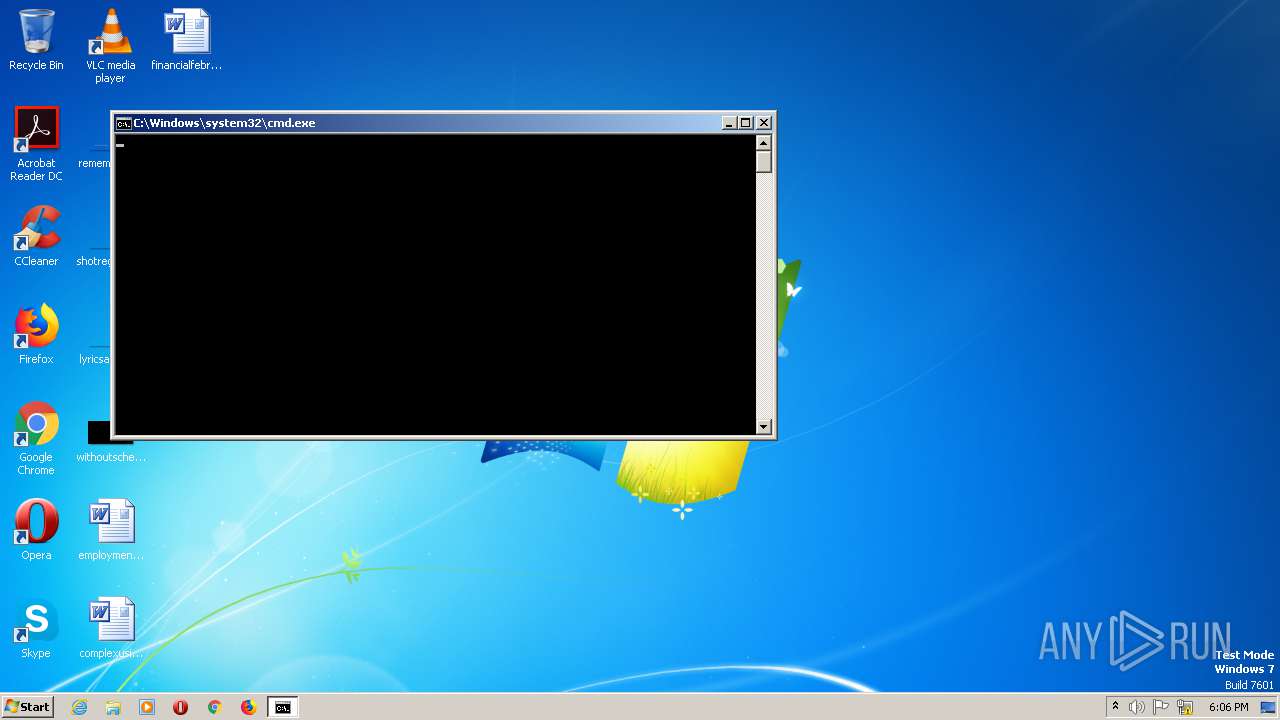
Starts CMD.EXE for commands execution
- zsvc.exe (PID: 2988)
- sqhost.exe (PID: 1464)
Starts SC.EXE for service management
- cmd.exe (PID: 1392)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 3008)
Executable content was dropped or overwritten
- cmd.exe (PID: 1400)
Starts itself from another location
- zsvc.exe (PID: 2988)
Uses NETSH.EXE for network configuration
- cmd.exe (PID: 2900)
Application launched itself
- sqhost.exe (PID: 1464)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (87.1) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.4) |
| .exe | | | DOS Executable Generic (6.4) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2020:11:16 00:50:28+01:00 |
| PEType: | PE32+ |
| LinkerVersion: | 12 |
| CodeSize: | 151552 |
| InitializedDataSize: | 4096 |
| UninitializedDataSize: | 19300352 |
| EntryPoint: | 0x128d530 |
| OSVersion: | 5.2 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.0.0.0 |
| ProductVersionNumber: | 2.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Microsoft Corporation |
| FileDescription: | Host Process for Windows Service |
| FileVersion: | 2.0.0.0 |
| InternalName: | sqhost.exe |
| LegalCopyright: | Copyright (C) 2016 |
| OriginalFileName: | sqhost.exe |
| ProductName: | sqhost.exe |
| ProductVersion: | 2.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_AMD64 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 15-Nov-2020 23:50:28 |
| Detected languages: |
|
| CompanyName: | Microsoft Corporation |
| FileDescription: | Host Process for Windows Service |
| FileVersion: | 2.0.0.0 |
| InternalName: | sqhost.exe |
| LegalCopyright: | Copyright (C) 2016 |
| OriginalFilename: | sqhost.exe |
| ProductName: | sqhost.exe |
| ProductVersion: | 2.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_AMD64 |
| Number of sections: | 3 |
| Time date stamp: | 15-Nov-2020 23:50:28 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00F0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x01268000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x01269000 | 0x00025000 | 0x00024800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.89862 |
.rsrc | 0x0128E000 | 0x00001000 | 0x00000800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.22618 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.91161 | 381 | UNKNOWN | English - United States | RT_MANIFEST |
Imports
ADVAPI32.dll |
CRYPT32.dll |
KERNEL32.DLL |
OLEAUT32.dll |
PSAPI.DLL |
SHELL32.dll |
USER32.dll |
WS2_32.dll |
ole32.dll |
wevtapi.dll |
Total processes
51
Monitored processes
13
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 260 | "C:\Users\admin\appdata\roaming\intel\sqhost.exe" -watchdog | C:\Users\admin\appdata\roaming\intel\sqhost.exe | — | sqhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Service Exit code: 0 Version: 2.0.0.0 Modules
| |||||||||||||||
| 1392 | cmd.exe /c sc query UPlugPlay | C:\Windows\system32\cmd.exe | — | zsvc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1060 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1400 | "C:\Windows\System32\cmd.exe" /C copy /y "c:\users\admin\appdata\local\temp\zsvc.exe" "c:\users\admin\appdata\roaming\intel\sqhost.exe" | C:\Windows\System32\cmd.exe | zsvc.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1464 | "C:\Users\admin\appdata\roaming\intel\sqhost.exe" | C:\Users\admin\appdata\roaming\intel\sqhost.exe | zsvc.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Service Exit code: 0 Version: 2.0.0.0 Modules
| |||||||||||||||
| 1500 | reg add HKCU\Software\Microsoft\Windows\CurrentVersion\Run /v UPlugPlay /t REG_SZ /d "c:\users\admin\appdata\roaming\intel\sqhost.exe Dcomsvc" /f | C:\Windows\system32\reg.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1548 | Auditpol /set /subcategory:"Logon" /failure:enable | C:\Windows\system32\auditpol.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Audit Policy Program Exit code: 1314 Version: 6.1.7601.23915 (win7sp1_ldr.170913-0600) Modules
| |||||||||||||||
| 2620 | sc query UPlugPlay | C:\Windows\system32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: A tool to aid in developing services for WindowsNT Exit code: 1060 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2692 | netsh advfirewall firewall delete rule name="Banned brute IPs" | C:\Windows\system32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Network Command Shell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2728 | \??\C:\Windows\system32\conhost.exe "1106765551-21395338964453642311268605135-1389127936-1309395963-937110001332332590" | C:\Windows\system32\conhost.exe | csrss.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2728 | "C:\Windows\System32\cmd.exe" /C Auditpol /set /subcategory:"Logon" /failure:enable | C:\Windows\System32\cmd.exe | — | sqhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1314 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 224
Read events
1 105
Write events
119
Delete events
0
Modification events
| (PID) Process: | (2988) zsvc.exe | Key: | HKEY_CURRENT_USER\Software\Intel\Support |
| Operation: | write | Name: | CommId |
Value: YYT7EEONL2QC3RZO | |||
| (PID) Process: | (2988) zsvc.exe | Key: | HKEY_CURRENT_USER\Software\Intel\Support |
| Operation: | write | Name: | MachineKeyId |
Value: c9s9Dbkk6q3sD12p | |||
| (PID) Process: | (2988) zsvc.exe | Key: | HKEY_CURRENT_USER\Software\Intel\Support |
| Operation: | write | Name: | EncryptedMachineKeyId |
Value: FuRGaUBA3gbRTdazT2wmRfsReTgrd0le0n3O3M5IPWQCQeFX1/g+kY4d/ny72SzHRiI67+x5ur90FnjQRfQLRR7l6SnqnIi6Z5LlstRsu4BACSsFtBkWbhc8EMzQCxKmjb/F20a7lWizcKWH0ANNRrVG67Pv6ySunszNaeXvbBs= | |||
| (PID) Process: | (1500) reg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | UPlugPlay |
Value: c:\users\admin\appdata\roaming\intel\sqhost.exe Dcomsvc | |||
| (PID) Process: | (1464) sqhost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1464) sqhost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1464) sqhost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1464) sqhost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2692) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2692) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\p2pcollab.dll,-8042 |
Value: Peer to Peer Trust | |||
Executable files
1
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1400 | cmd.exe | C:\users\admin\appdata\roaming\intel\sqhost.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1464 | sqhost.exe | 88.198.246.242:80 | p1.feefreepool.net | Hetzner Online GmbH | DE | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
p1.feefreepool.net |
| malicious |