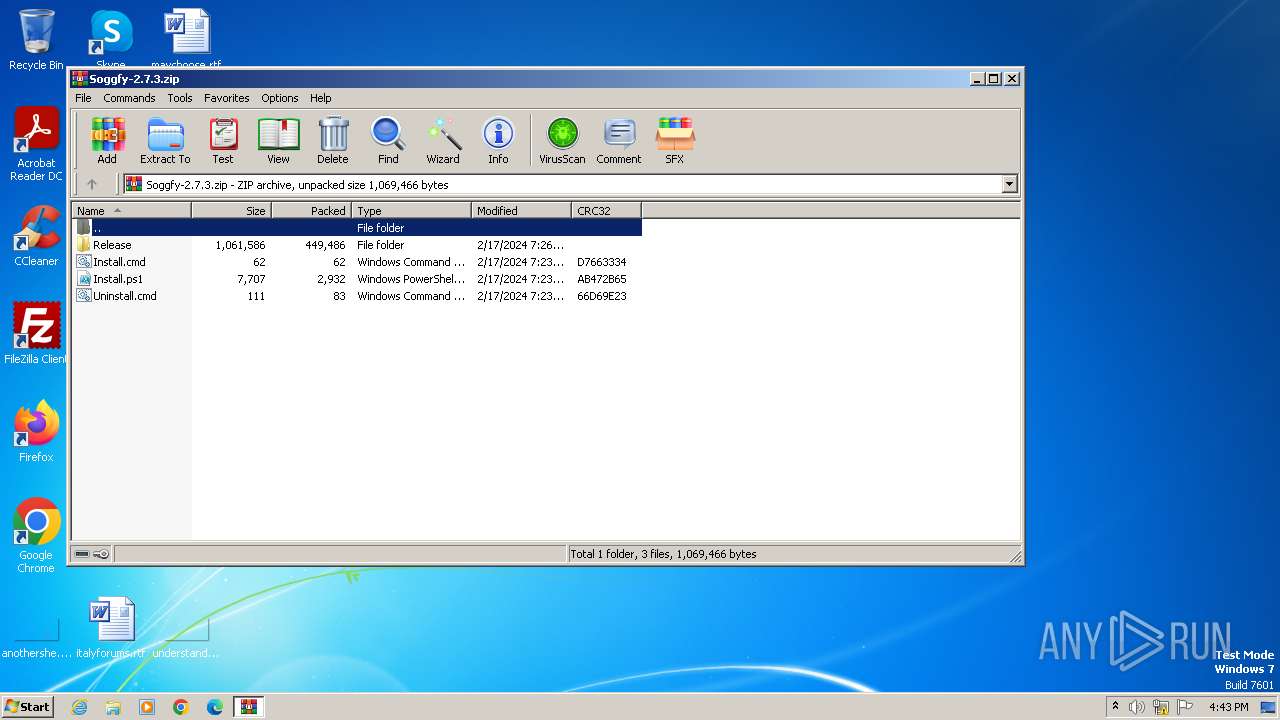
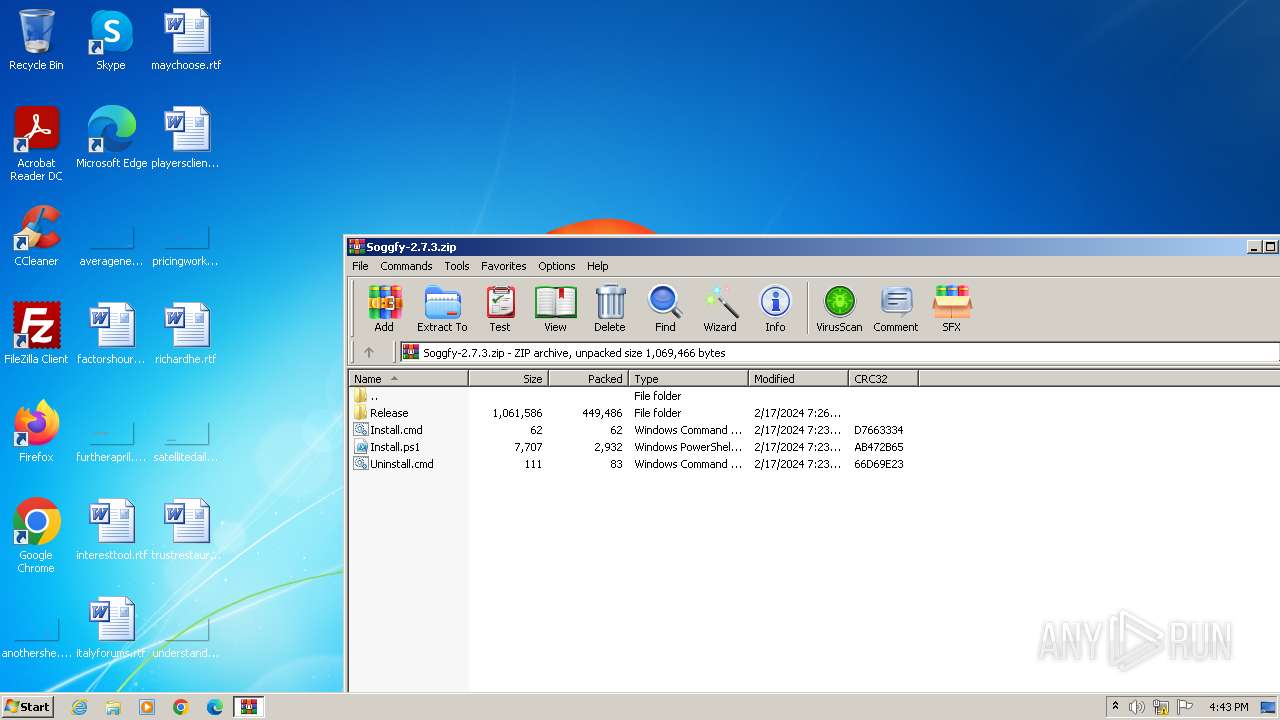
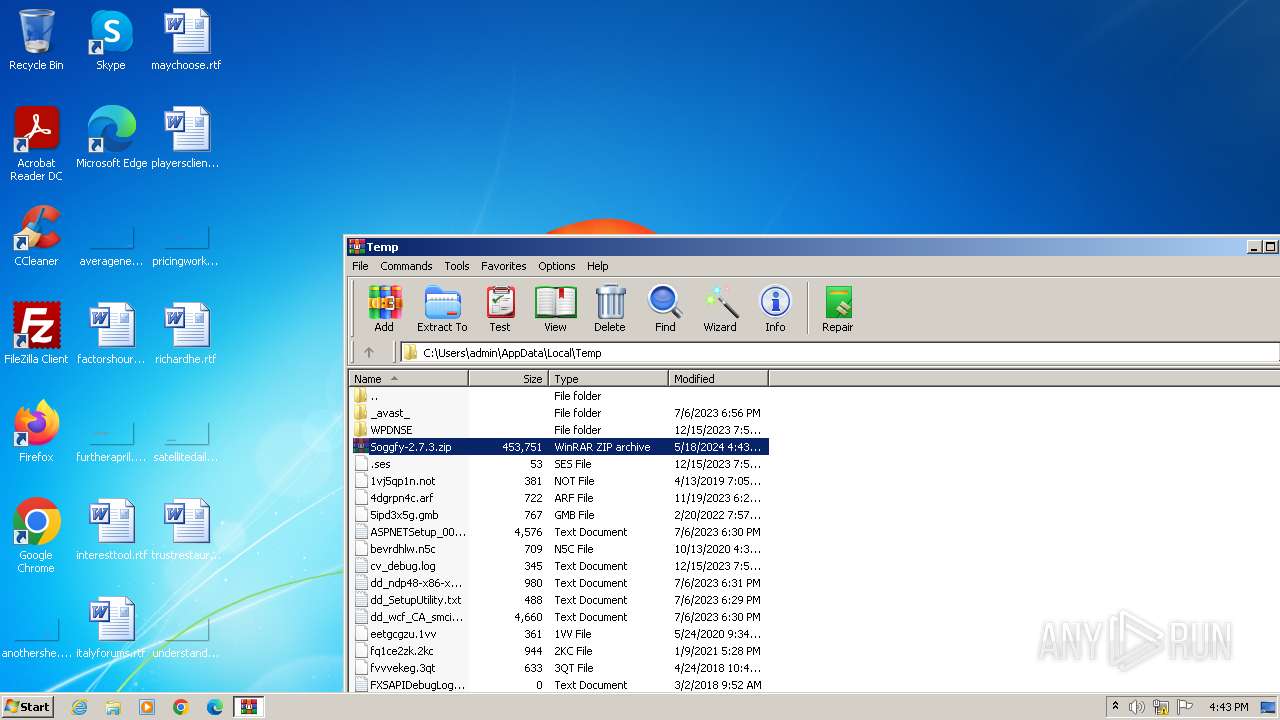
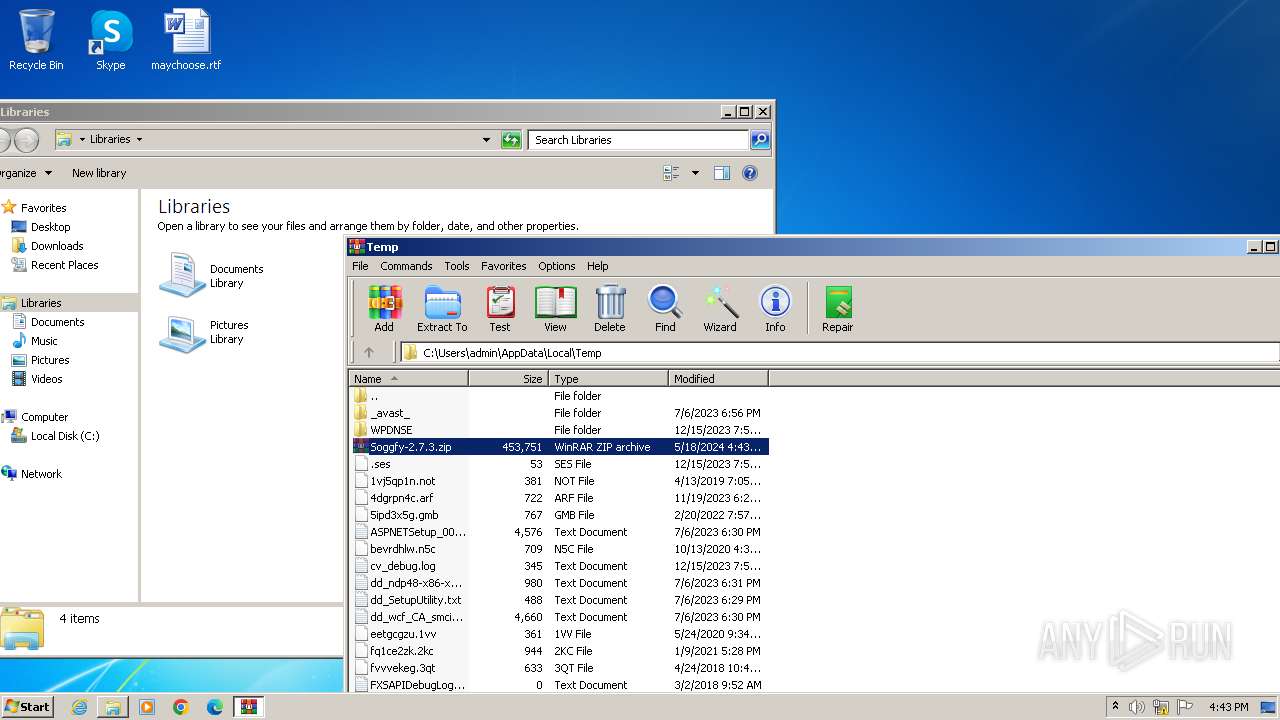
| File name: | Soggfy-2.7.3.zip |
| Full analysis: | https://app.any.run/tasks/c41b5612-73cd-44e7-86f5-2018ebc6b0b6 |
| Verdict: | Malicious activity |
| Analysis date: | May 18, 2024, 15:43:22 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | 608BEA798F0138B782887964DBA670D1 |
| SHA1: | 1FD7E62C718A894AFFB3A29CE4F1B8D486772BC4 |
| SHA256: | B5817F1F083C34340A84792C26F173416429ED3640626A32C3A031C9898E036B |
| SSDEEP: | 24576:pT3KGQjJoQTmHiOBfNCTWPPKzmi87/8MzidWOv4oXdKnup:pT3fQjJoQTmHiONNCTWPPKyi87/8Mzil |
MALICIOUS
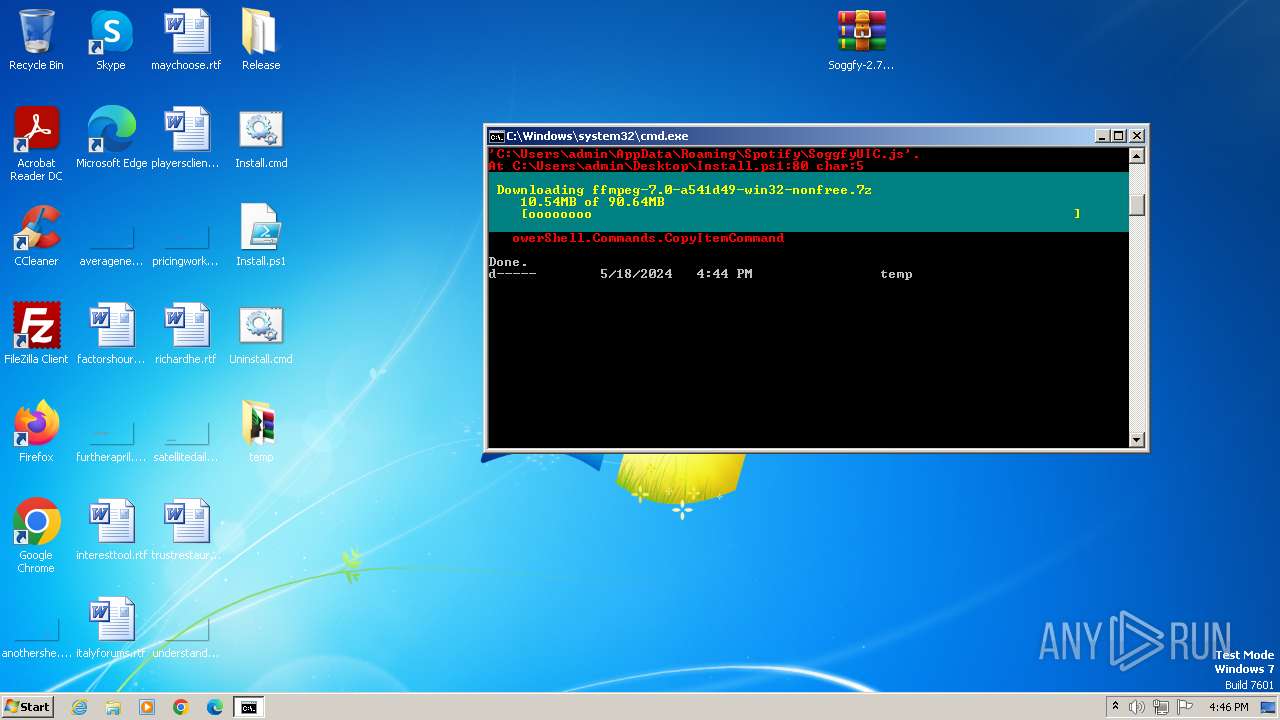
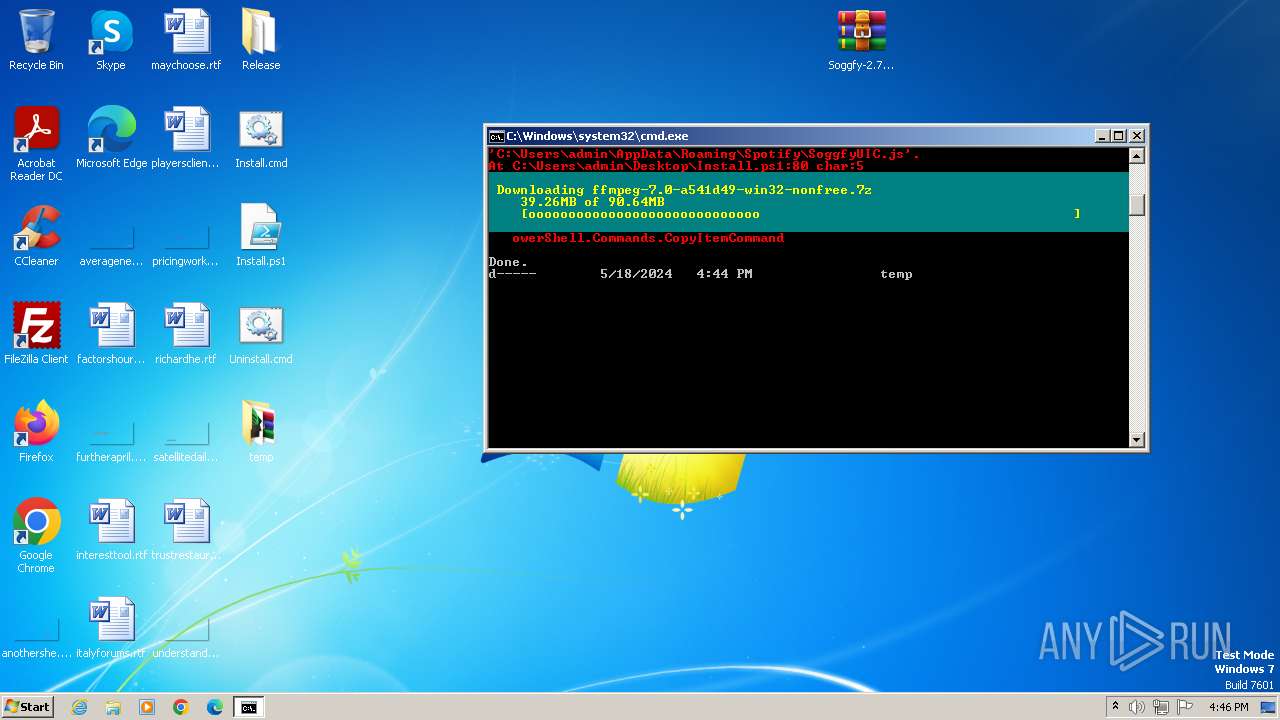
Drops the executable file immediately after the start
- WinRAR.exe (PID: 3976)
- powershell.exe (PID: 2356)
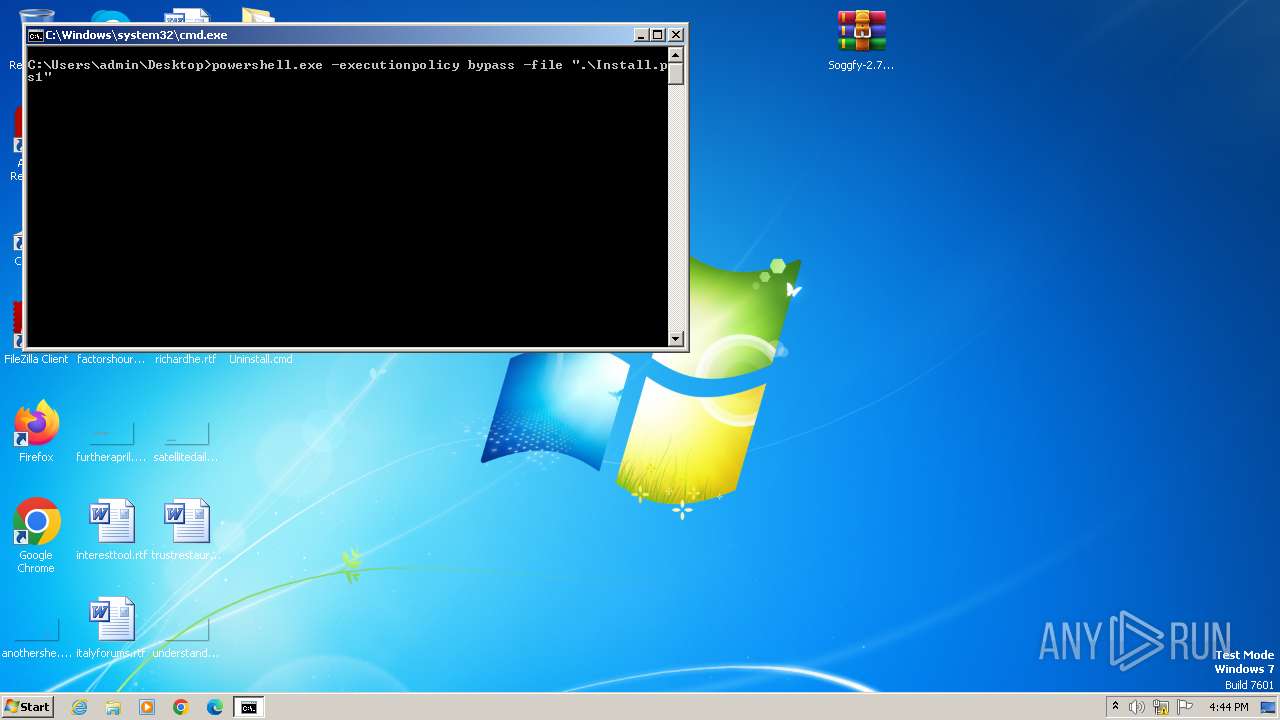
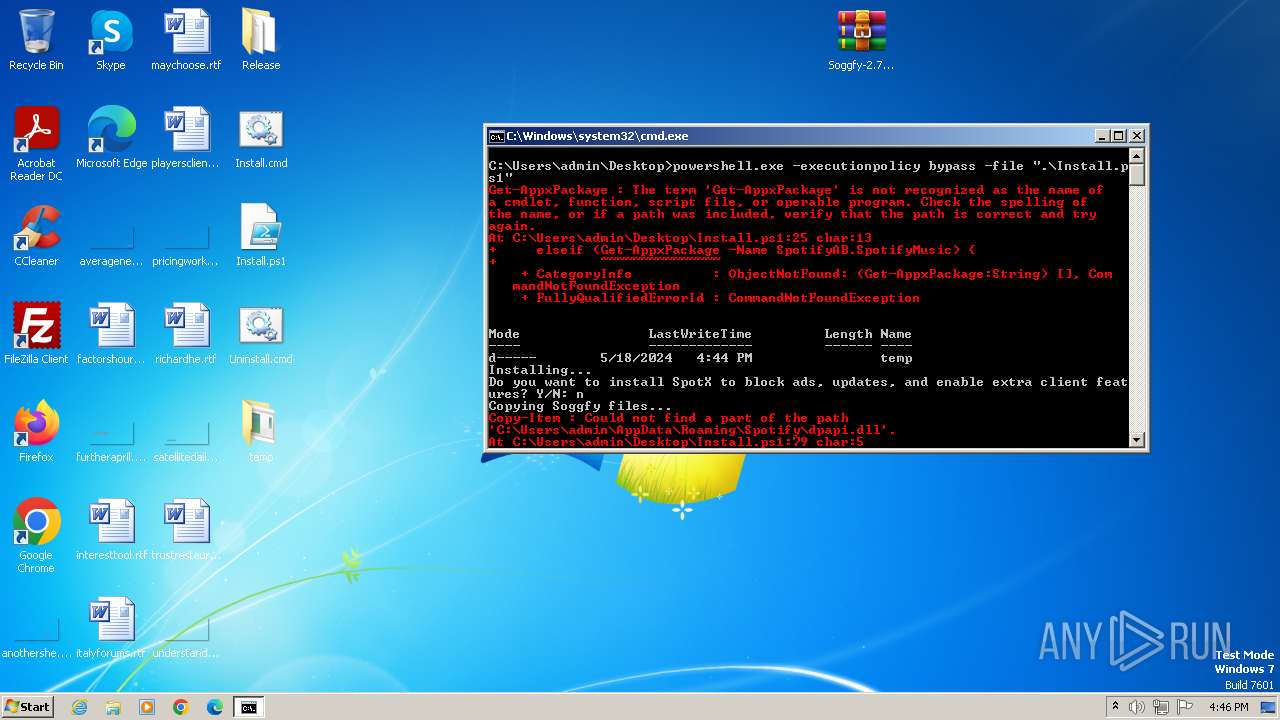
Bypass execution policy to execute commands
- powershell.exe (PID: 2356)
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 1980)
SUSPICIOUS
The process executes Powershell scripts
- cmd.exe (PID: 1980)
Reads the Internet Settings
- powershell.exe (PID: 2356)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 1980)
Using PowerShell to operate with local accounts
- powershell.exe (PID: 2356)
Unusual connection from system programs
- powershell.exe (PID: 2356)
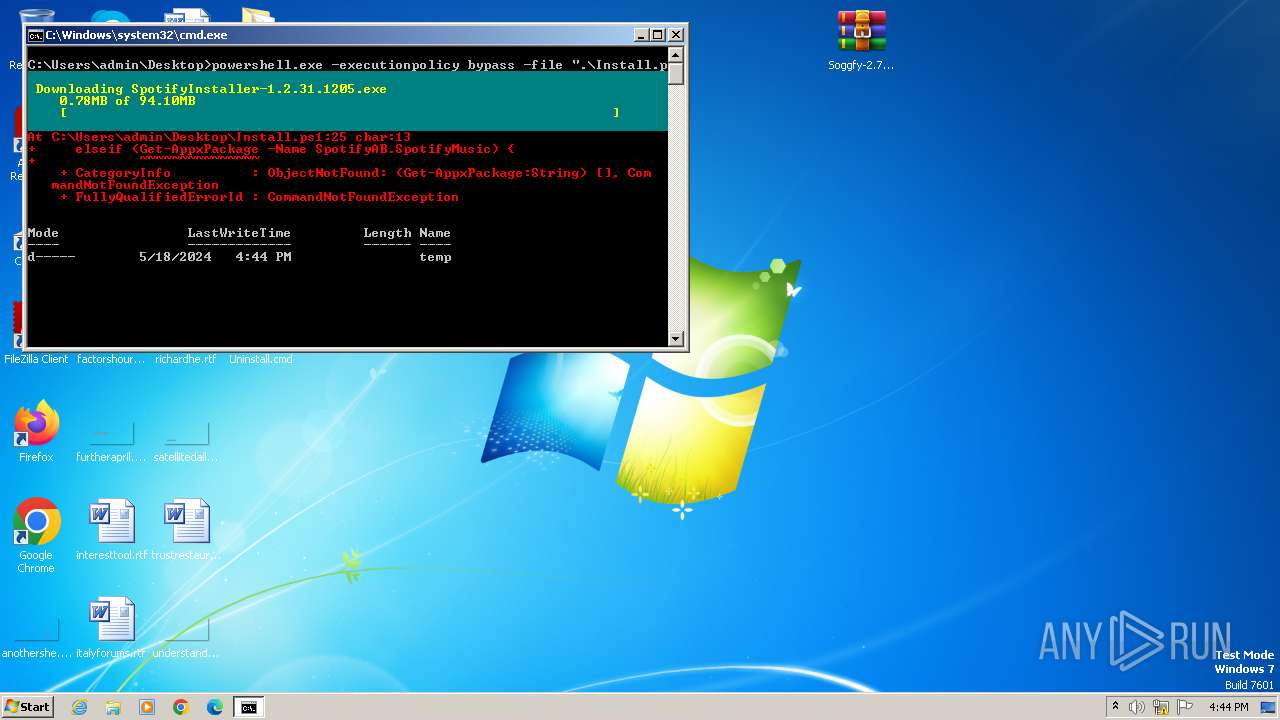
The Powershell connects to the Internet
- powershell.exe (PID: 2356)
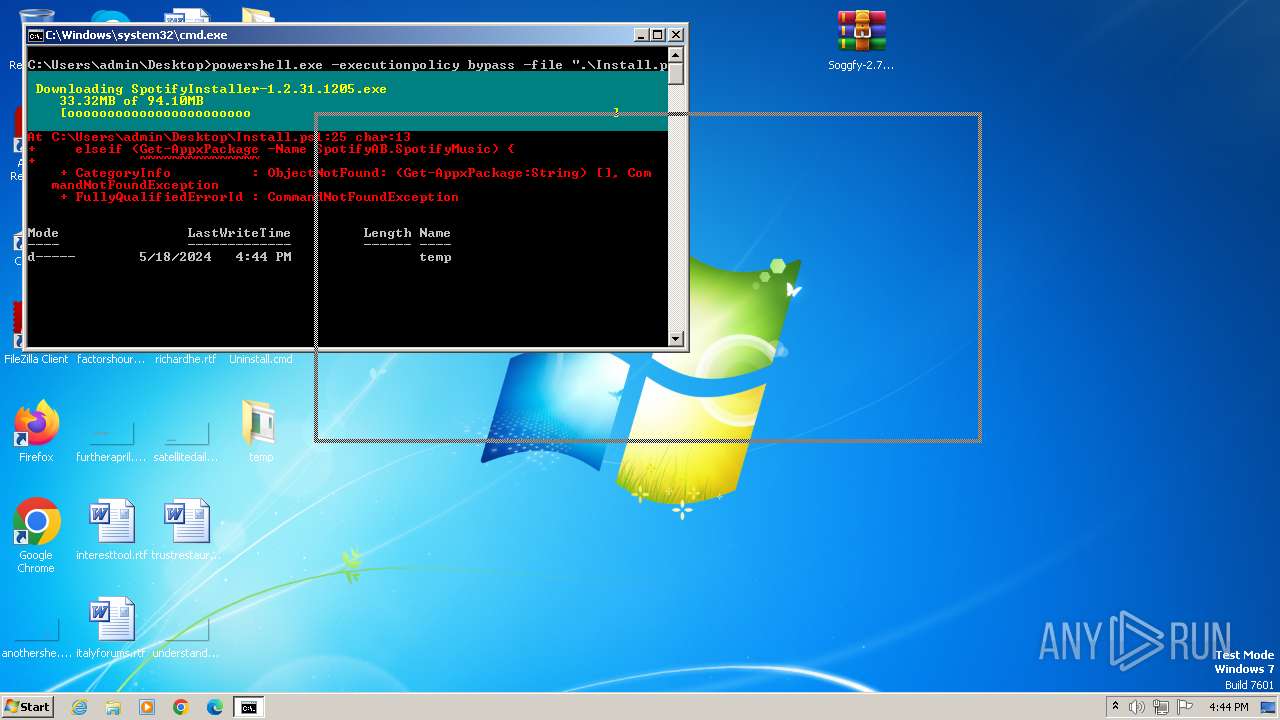
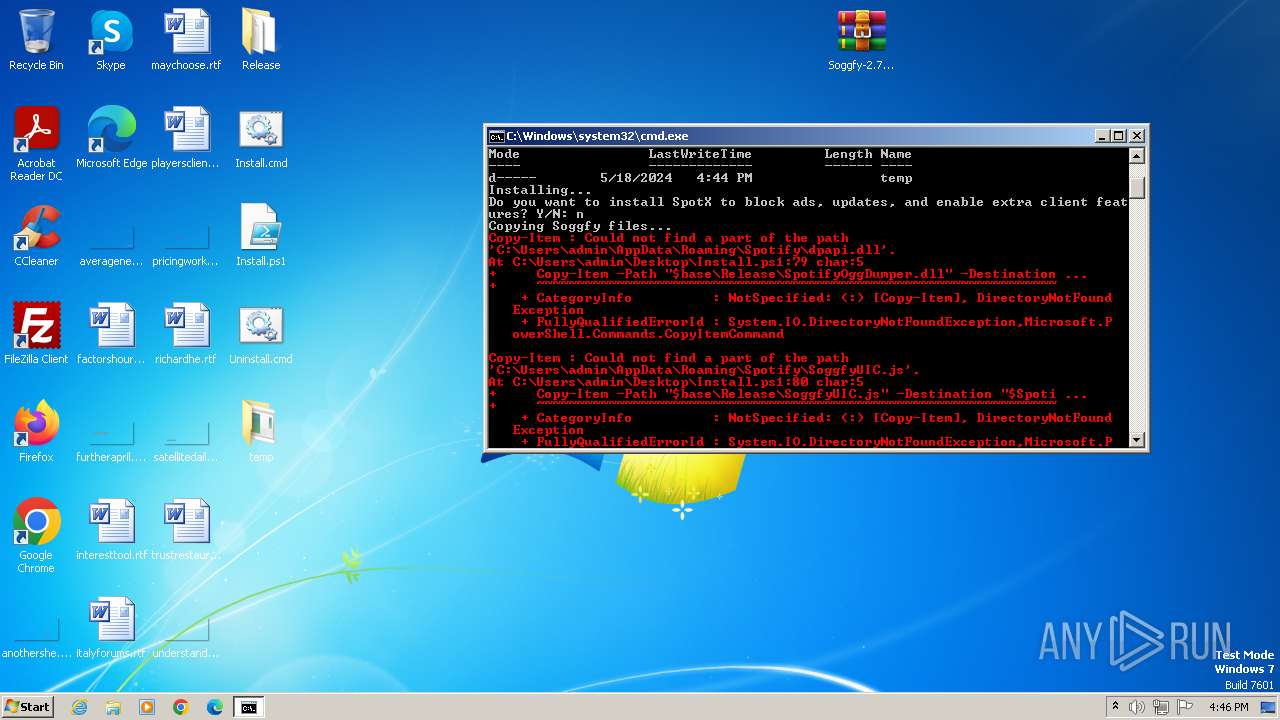
Creates a directory (POWERSHELL)
- powershell.exe (PID: 2356)
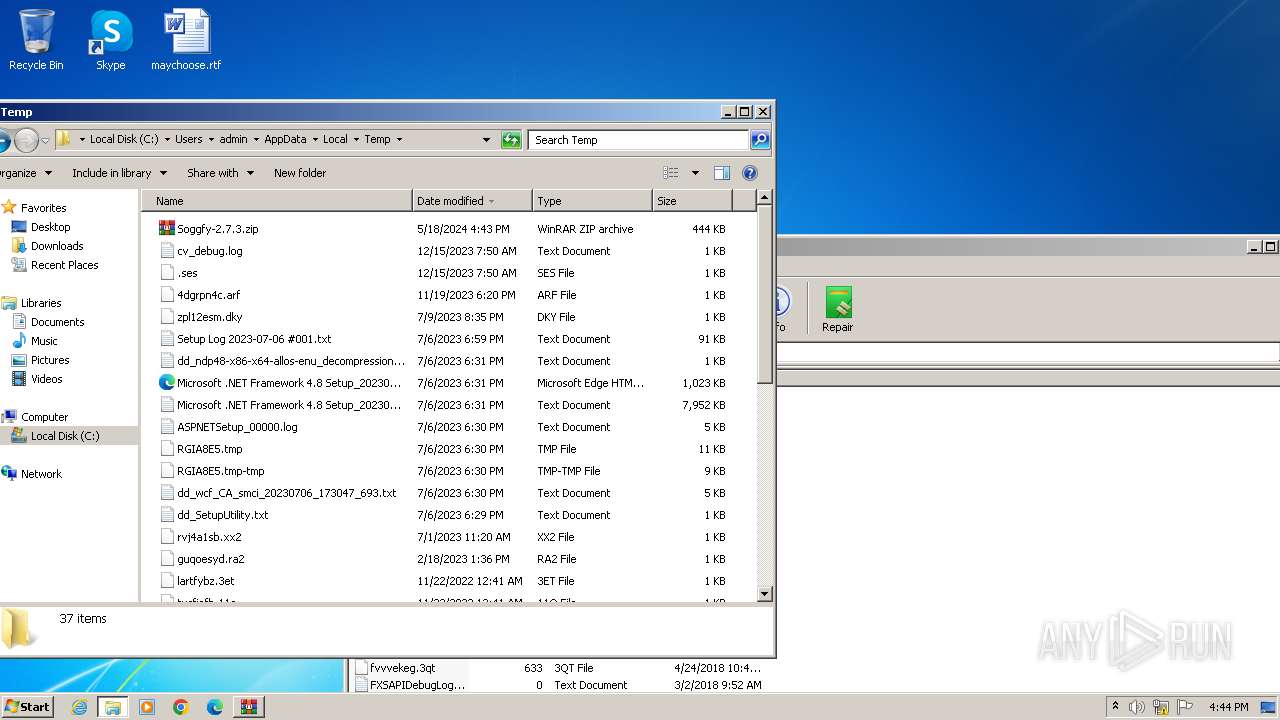
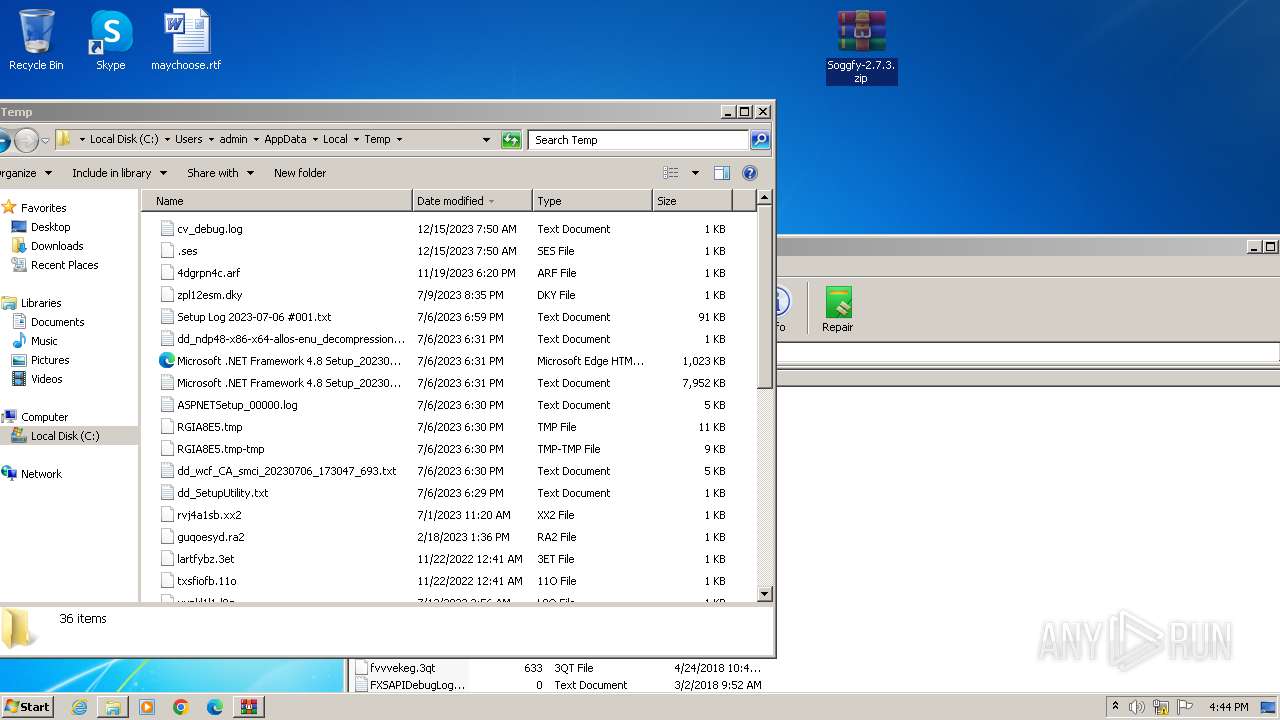
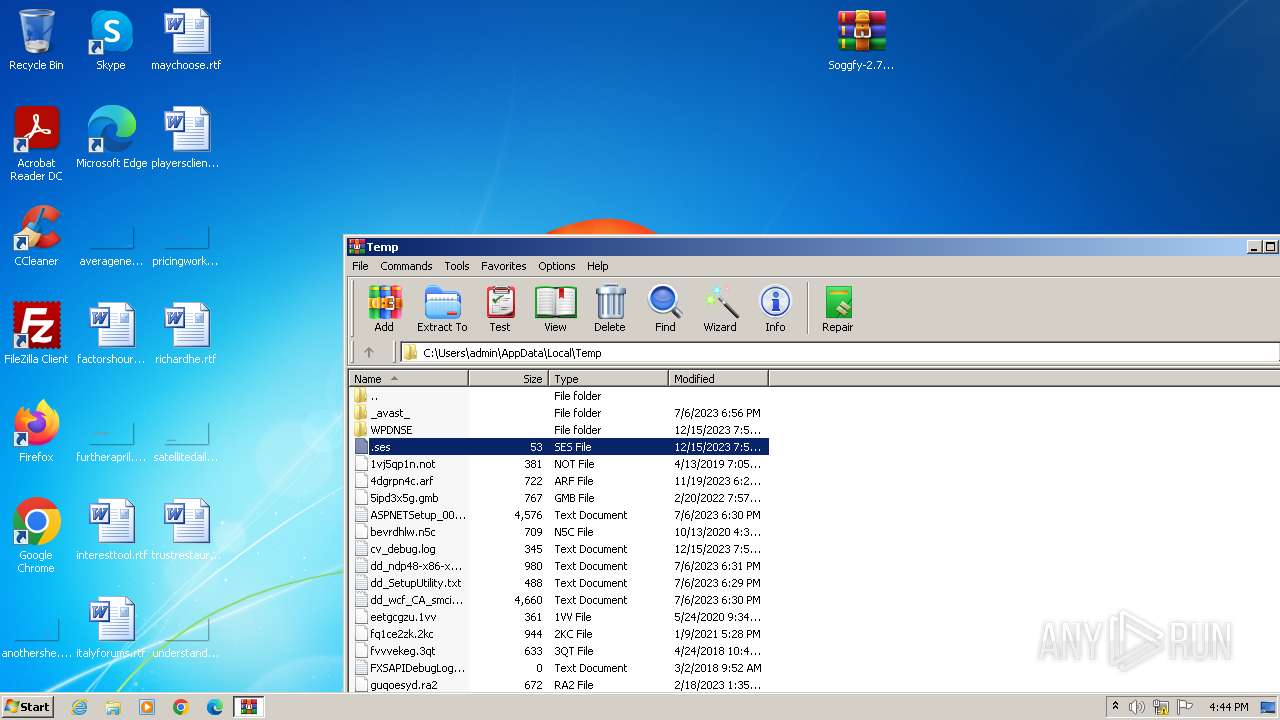
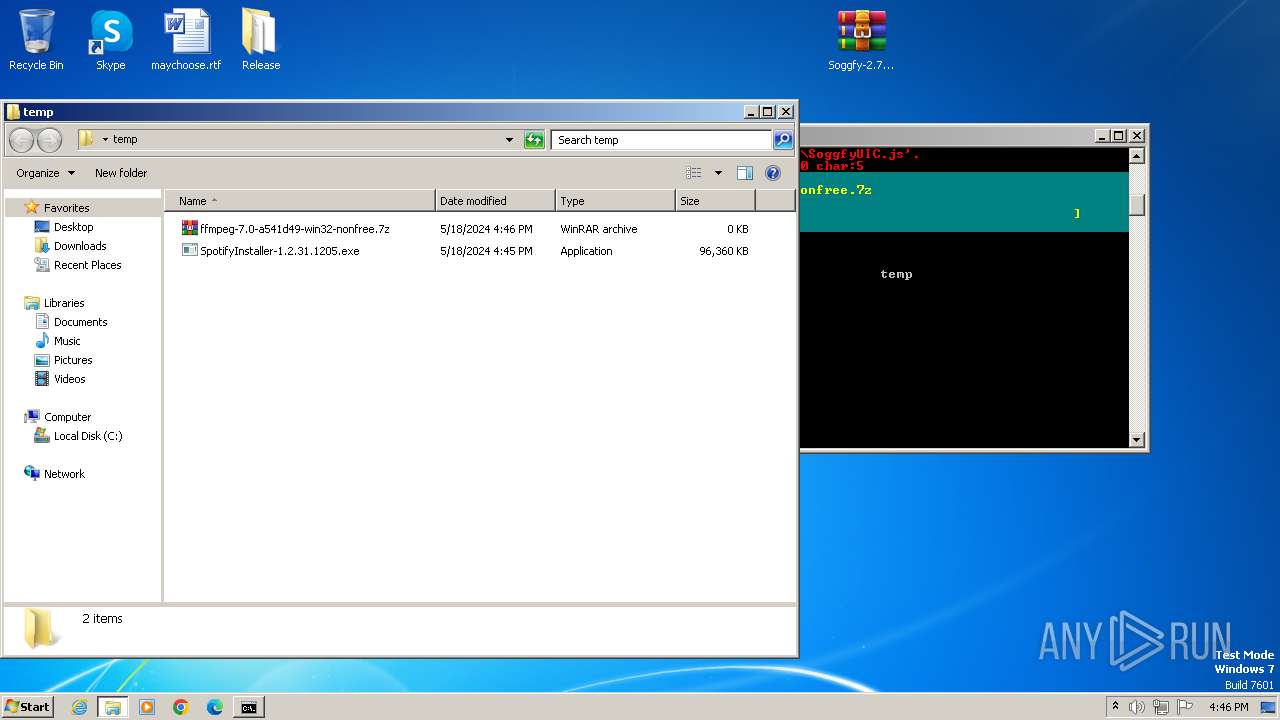
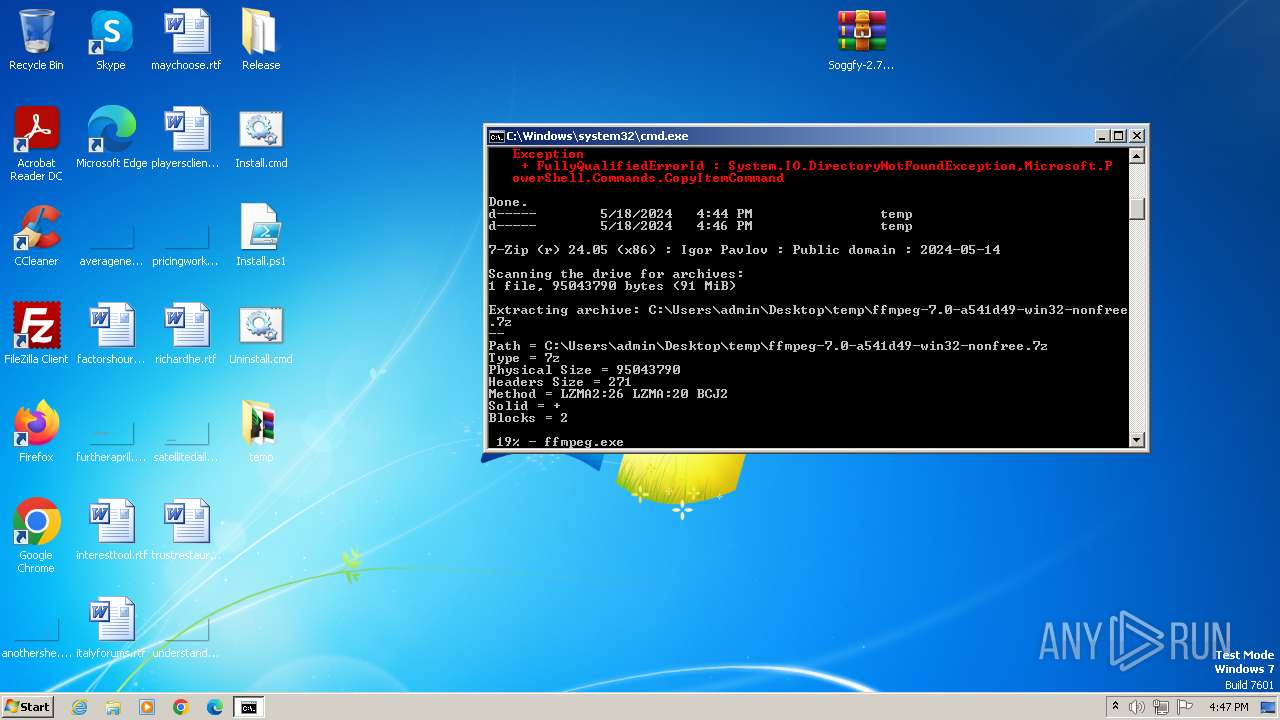
Drops 7-zip archiver for unpacking
- powershell.exe (PID: 2356)
Executable content was dropped or overwritten
- powershell.exe (PID: 2356)
INFO
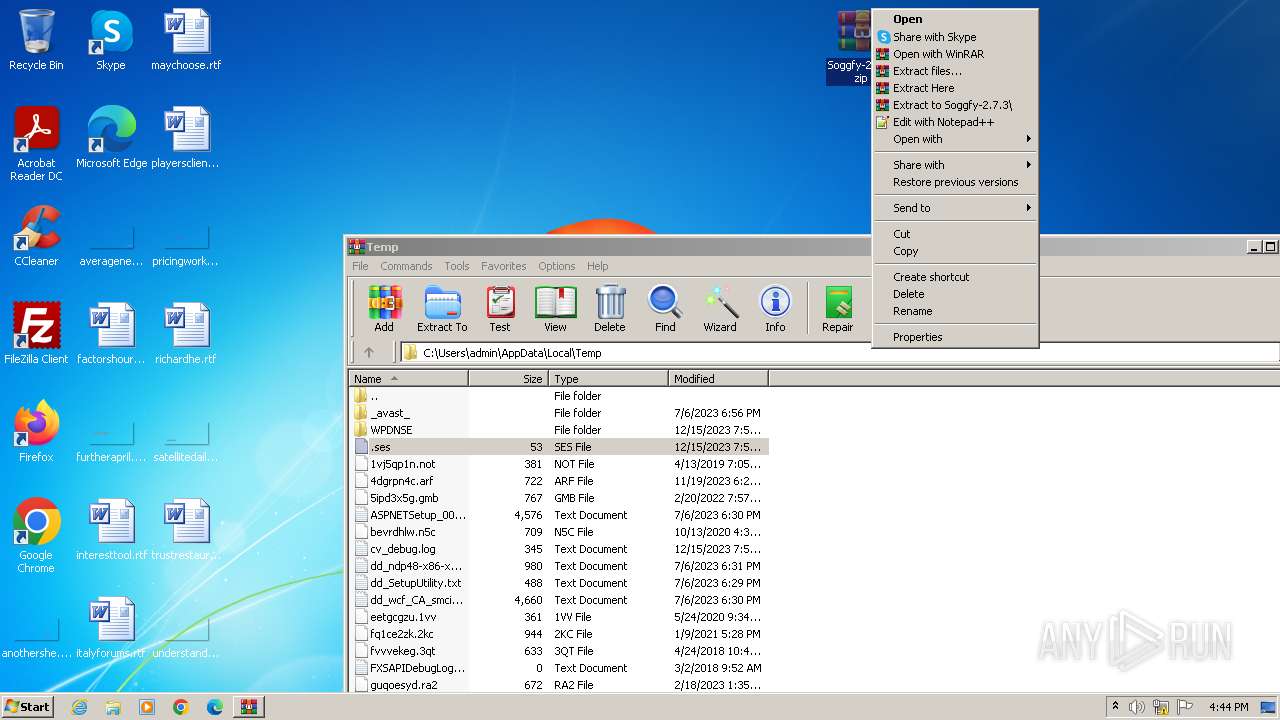
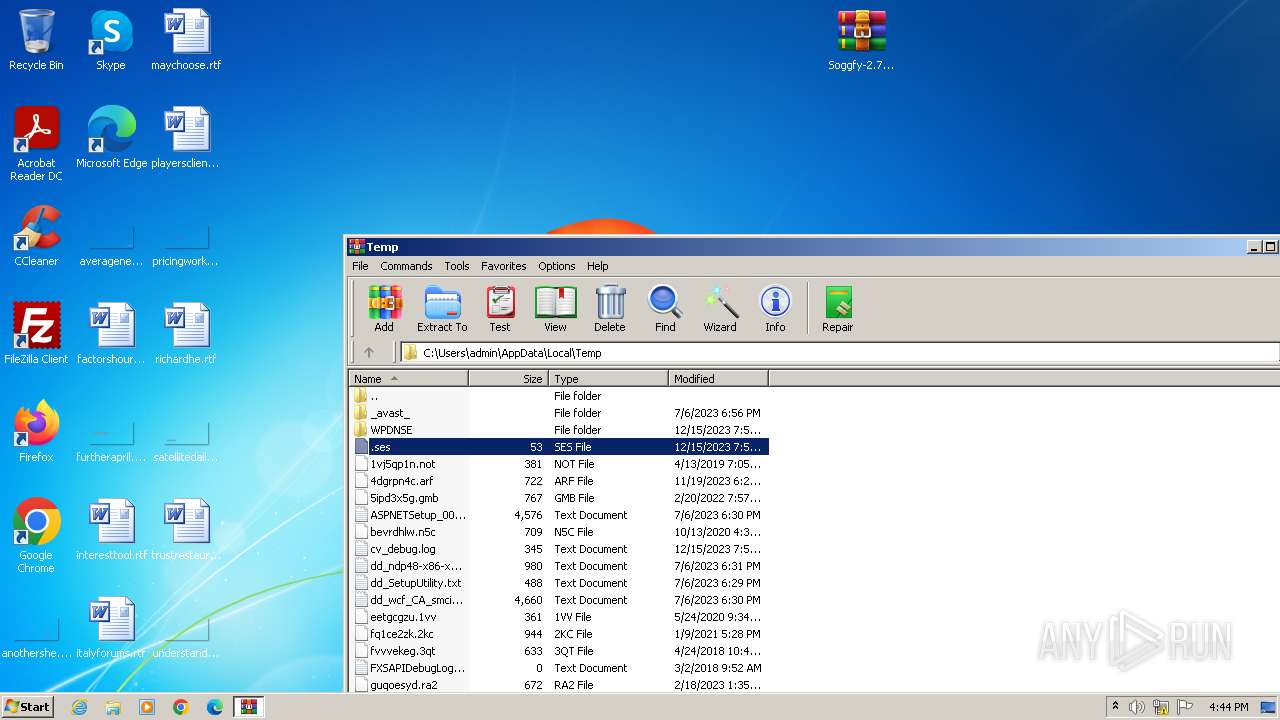
Manual execution by a user
- explorer.exe (PID: 4020)
- WinRAR.exe (PID: 2328)
- cmd.exe (PID: 1980)
- wmpnscfg.exe (PID: 1408)
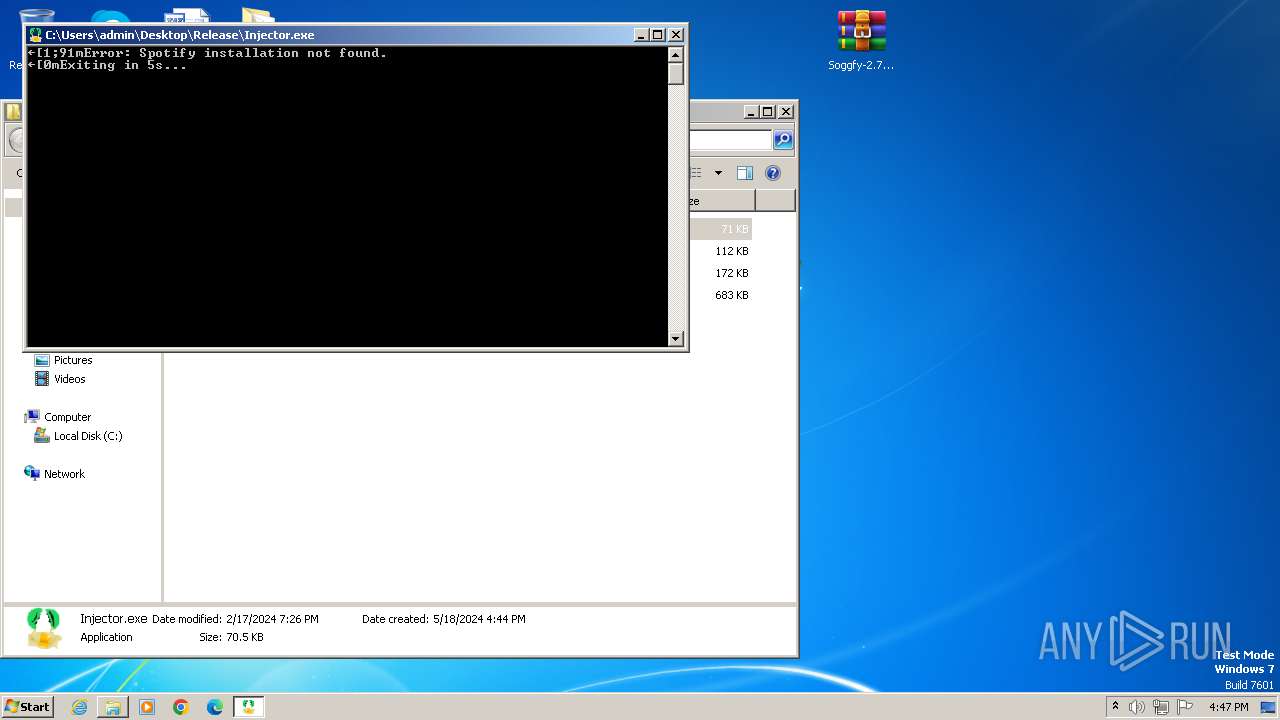
- Injector.exe (PID: 2896)
- cmd.exe (PID: 3080)
- cmd.exe (PID: 3176)
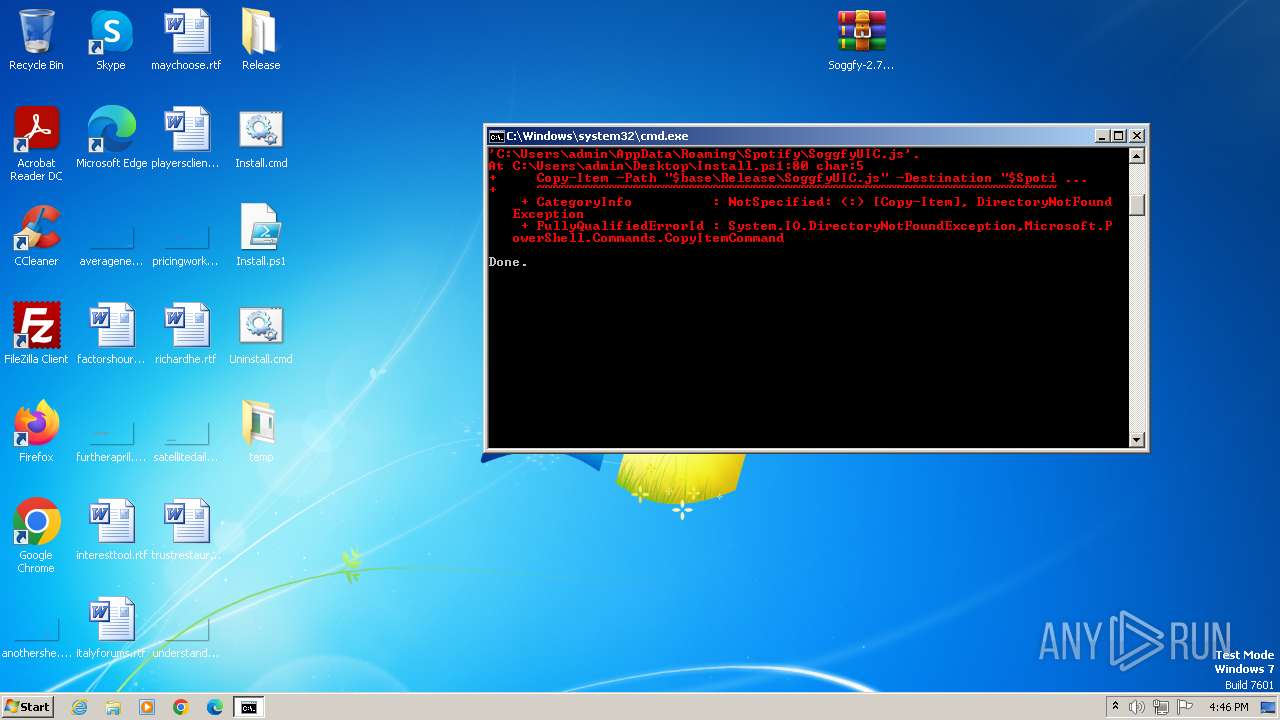
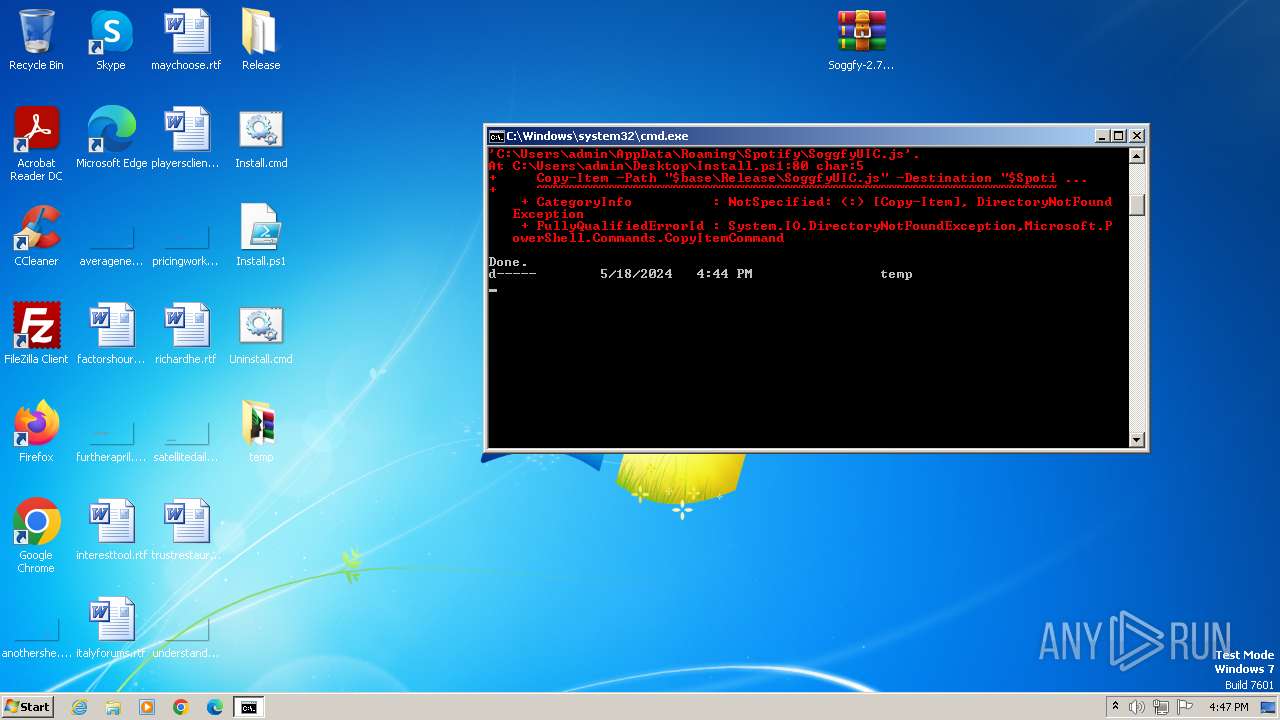
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 2356)
Disables trace logs
- powershell.exe (PID: 2356)
Checks supported languages
- wmpnscfg.exe (PID: 1408)
- SpotifyInstaller-1.2.31.1205.exe (PID: 2560)
- Injector.exe (PID: 2896)
- 7zr.exe (PID: 1312)
Reads the computer name
- wmpnscfg.exe (PID: 1408)
- 7zr.exe (PID: 1312)
Drops the executable file immediately after the start
- WinRAR.exe (PID: 2328)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2328)
Gets or sets the time when the file was last written to (POWERSHELL)
- powershell.exe (PID: 2356)
Gets data length (POWERSHELL)
- powershell.exe (PID: 2356)
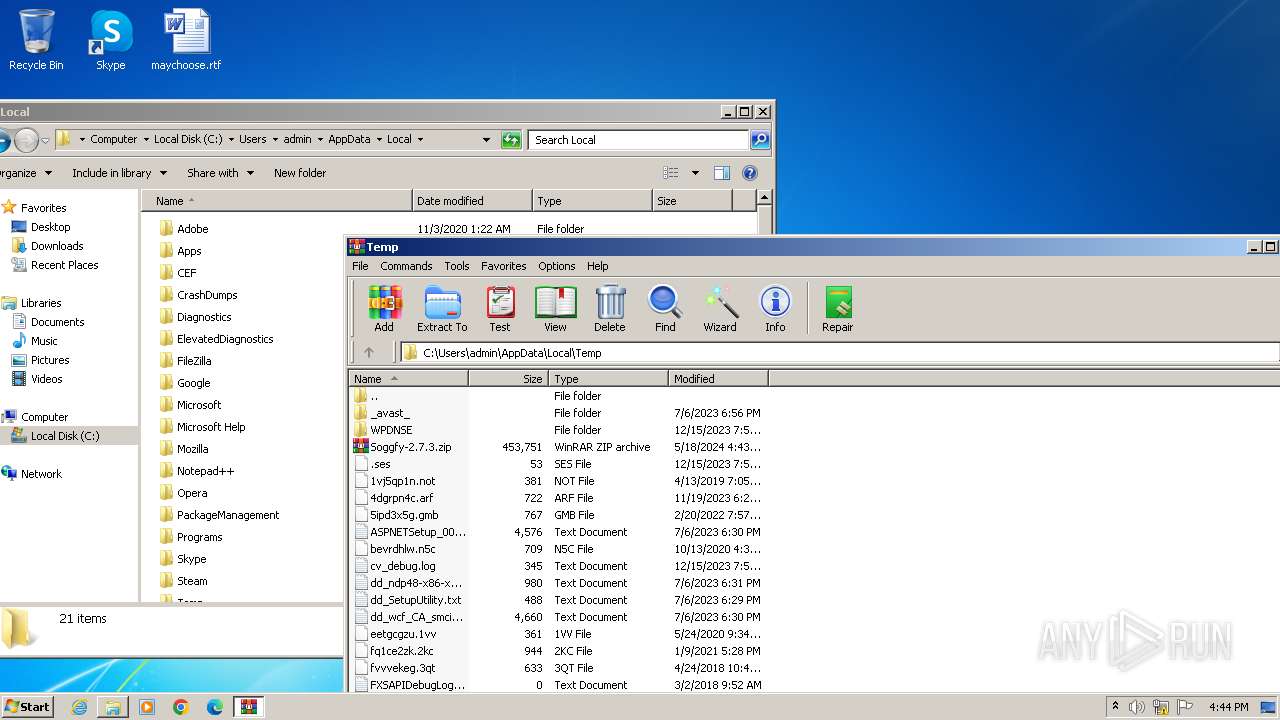
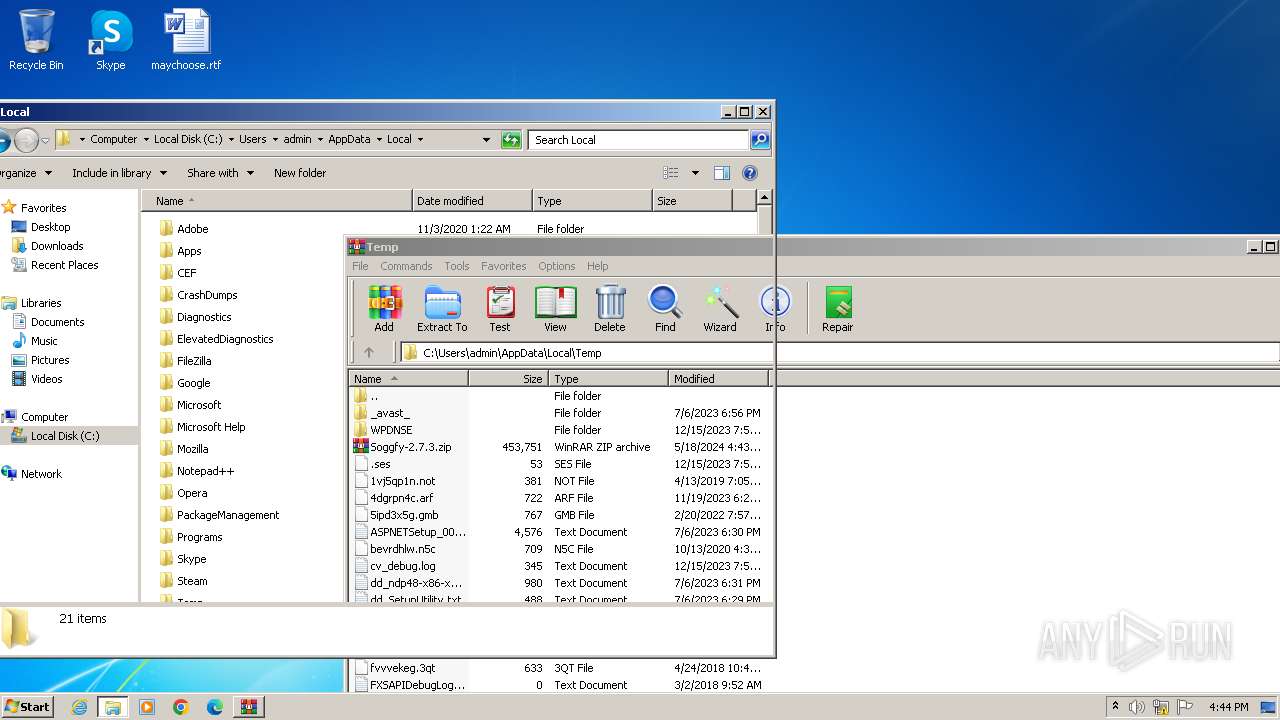
Creates files or folders in the user directory
- 7zr.exe (PID: 1312)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xpi | | | Mozilla Firefox browser extension (66.6) |
|---|---|---|
| .zip | | | ZIP compressed archive (33.3) |
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2024:02:17 19:23:04 |
| ZipCRC: | 0xd7663334 |
| ZipCompressedSize: | 62 |
| ZipUncompressedSize: | 62 |
| ZipFileName: | Install.cmd |
Total processes
58
Monitored processes
13
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1280 | "C:\Windows\system32\where.exe" /q ffmpeg | C:\Windows\System32\where.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Where - Lists location of files Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1312 | "C:\Users\admin\Desktop\temp\7zr.exe" e C:\Users\admin\Desktop\temp\ffmpeg-7.0-a541d49-win32-nonfree.7z -y -oC:\Users\admin\AppData\Local\Soggfy\ffmpeg\ ffmpeg.exe | C:\Users\admin\Desktop\temp\7zr.exe | — | powershell.exe | |||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7-Zip Reduced Standalone Console Exit code: 0 Version: 24.05 Modules
| |||||||||||||||
| 1408 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
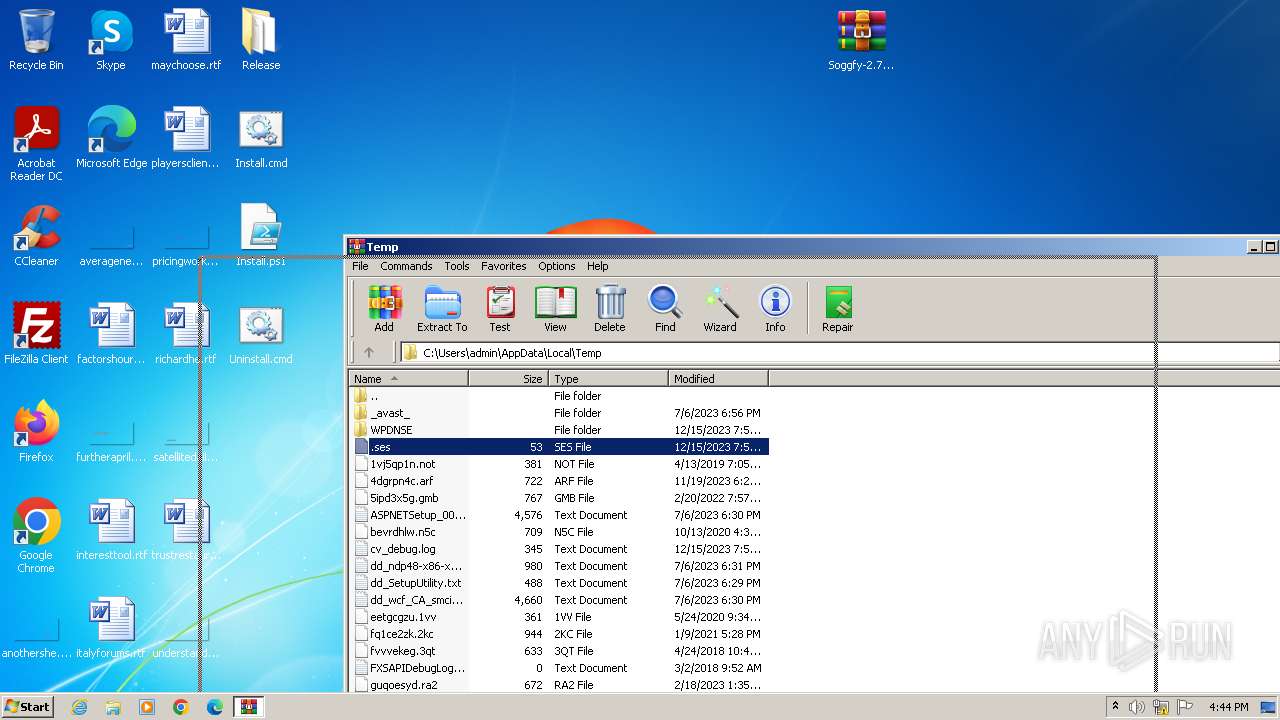
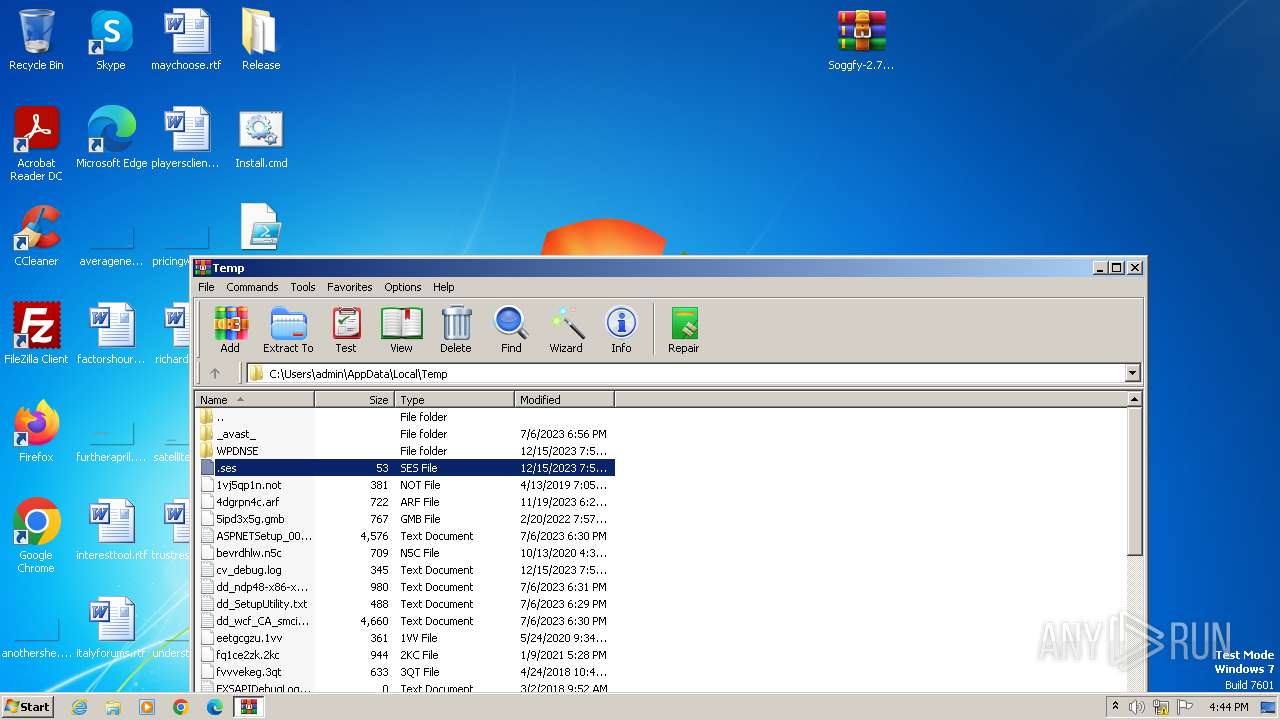
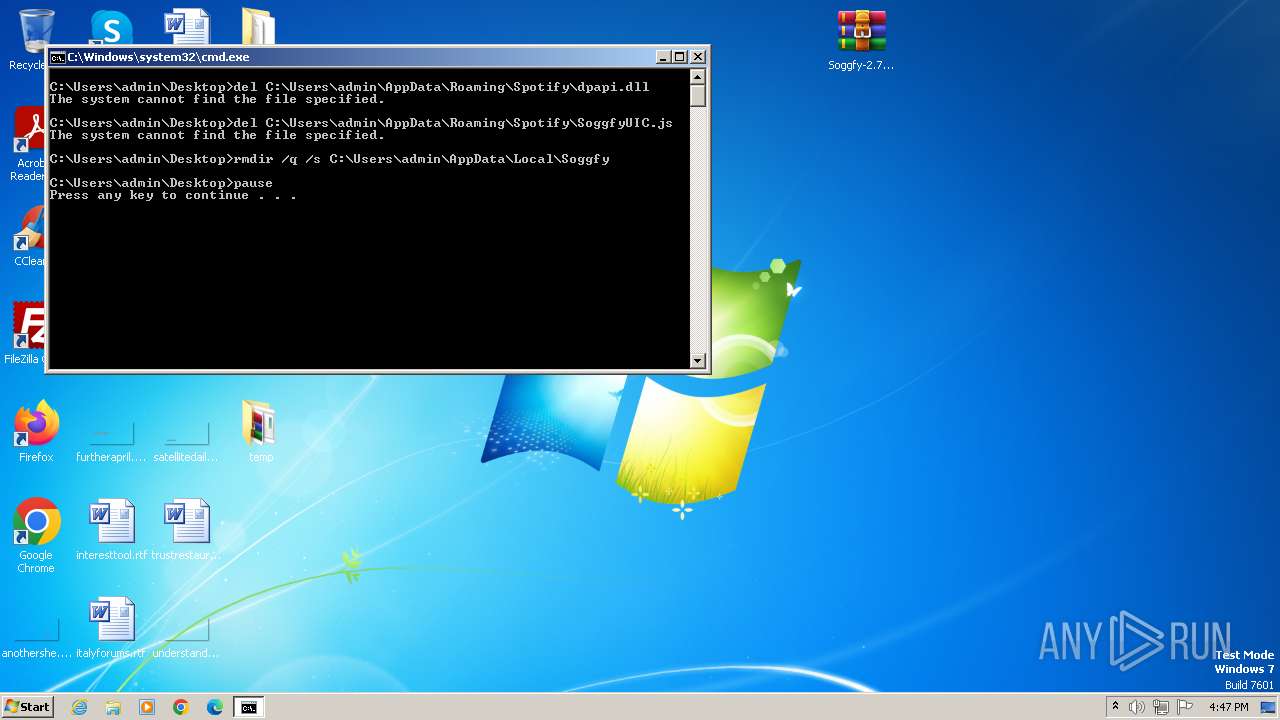
| 1980 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\Desktop\Install.cmd" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2328 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Desktop\Soggfy-2.7.3.zip" C:\Users\admin\Desktop\ | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
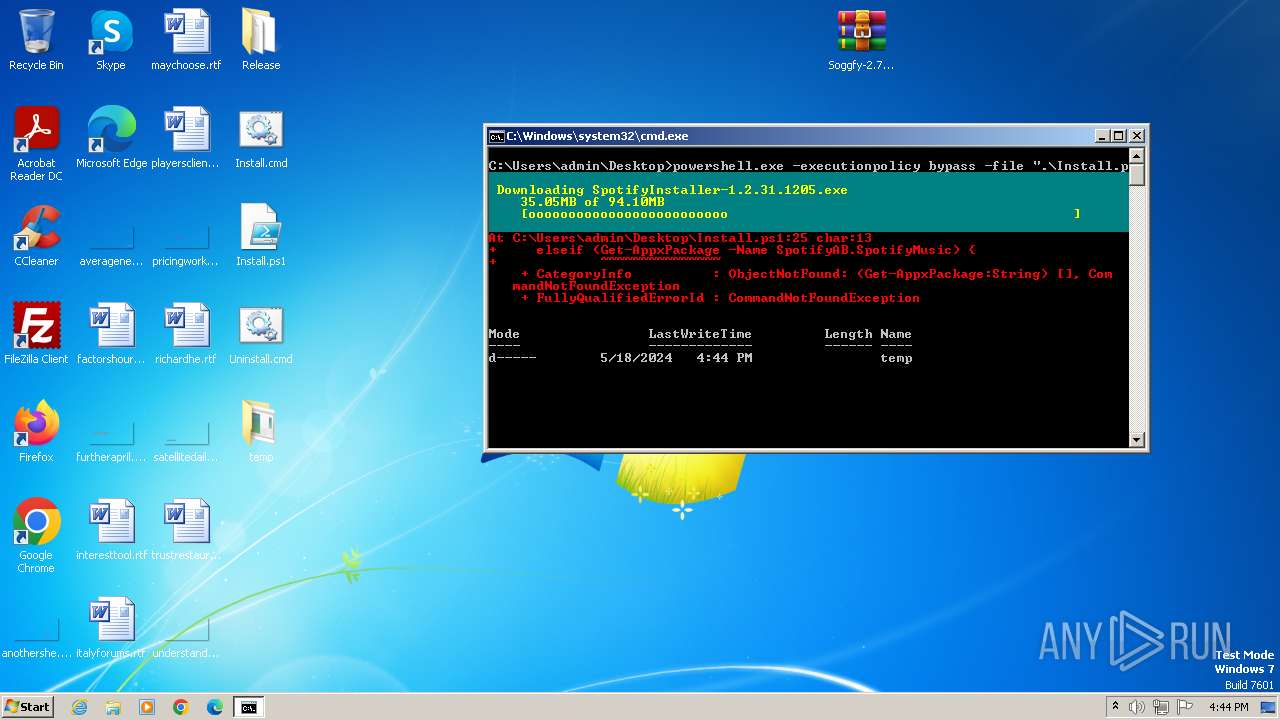
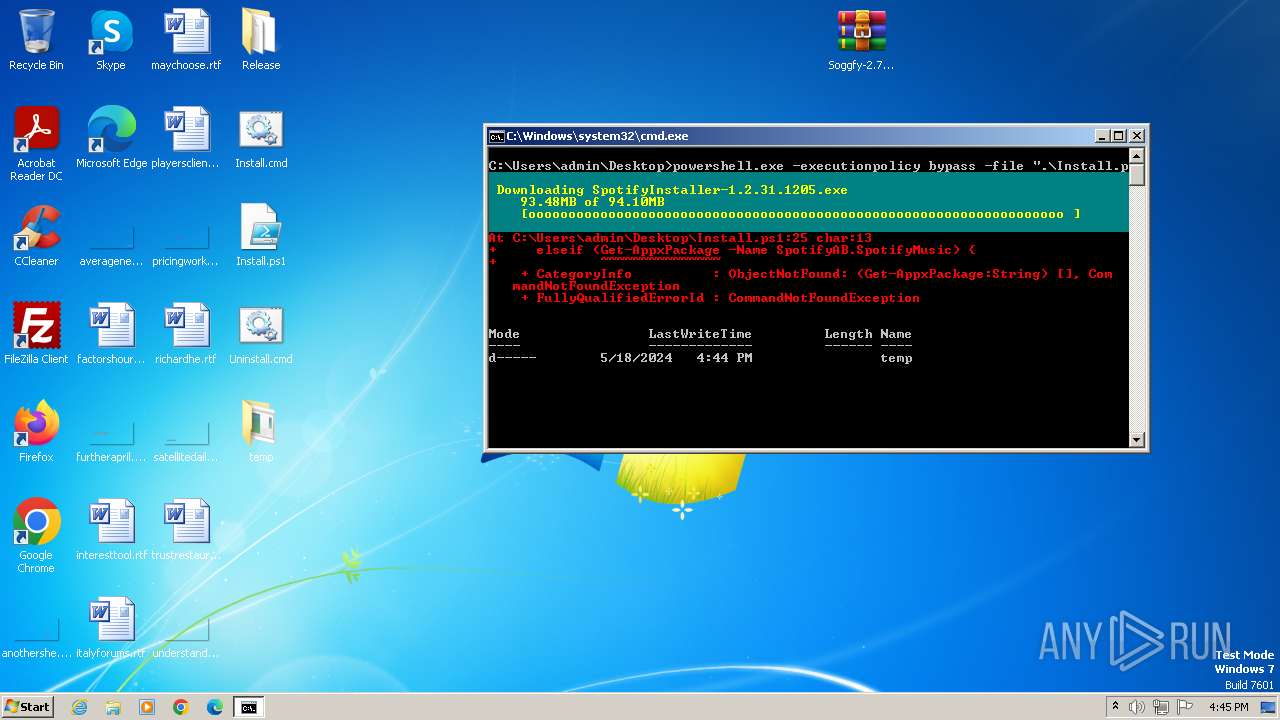
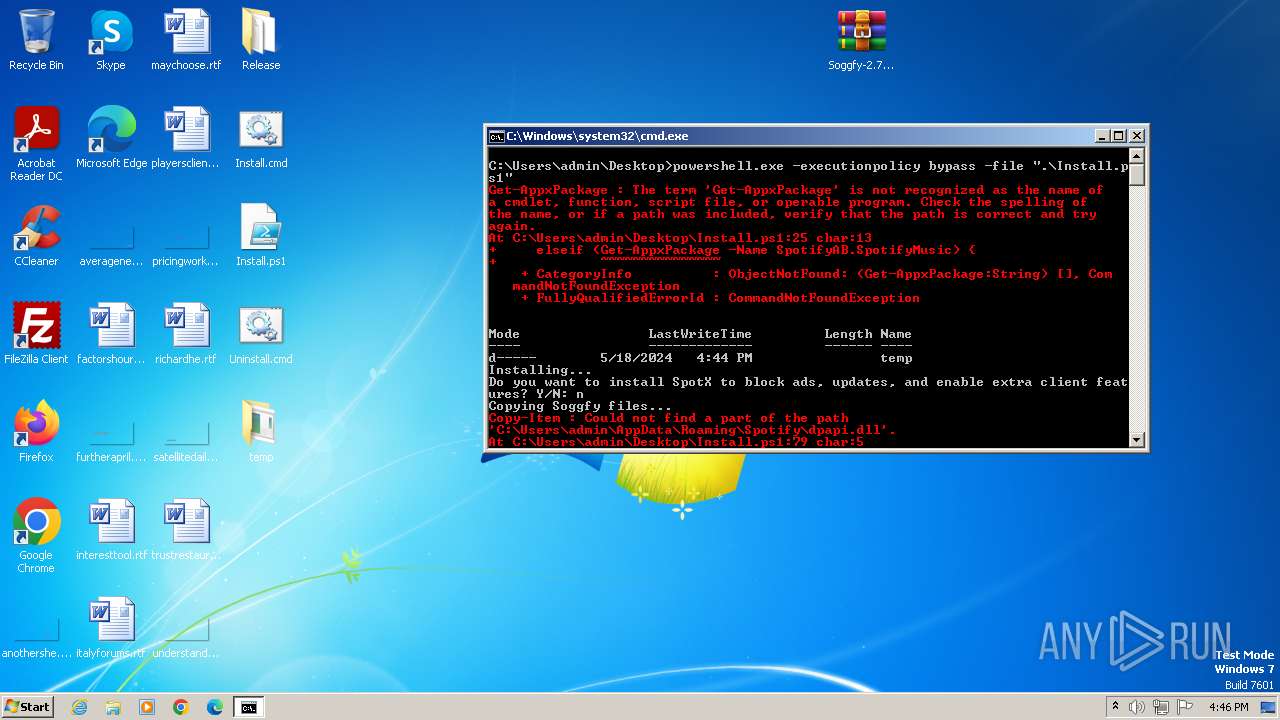
| 2356 | powershell.exe -executionpolicy bypass -file ".\Install.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 2560 | "C:\Users\admin\Desktop\temp\SpotifyInstaller-1.2.31.1205.exe" /silent /skip-app-launch | C:\Users\admin\Desktop\temp\SpotifyInstaller-1.2.31.1205.exe | — | powershell.exe | |||||||||||
User: admin Company: Spotify Ltd Integrity Level: MEDIUM Description: SpotifyInstaller Exit code: 22 Version: 0,0,0,0 Modules
| |||||||||||||||
| 2660 | "C:\Windows\system32\where.exe" /q spicetify | C:\Windows\System32\where.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Where - Lists location of files Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
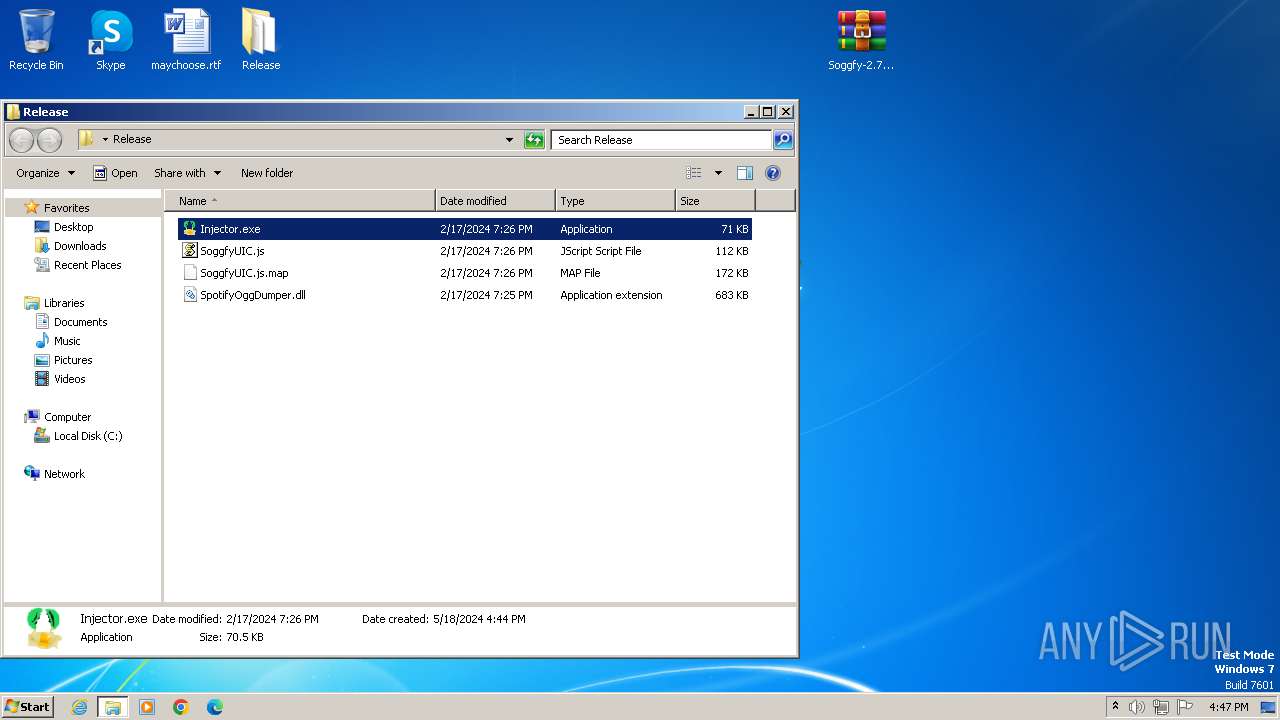
| 2896 | "C:\Users\admin\Desktop\Release\Injector.exe" | C:\Users\admin\Desktop\Release\Injector.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
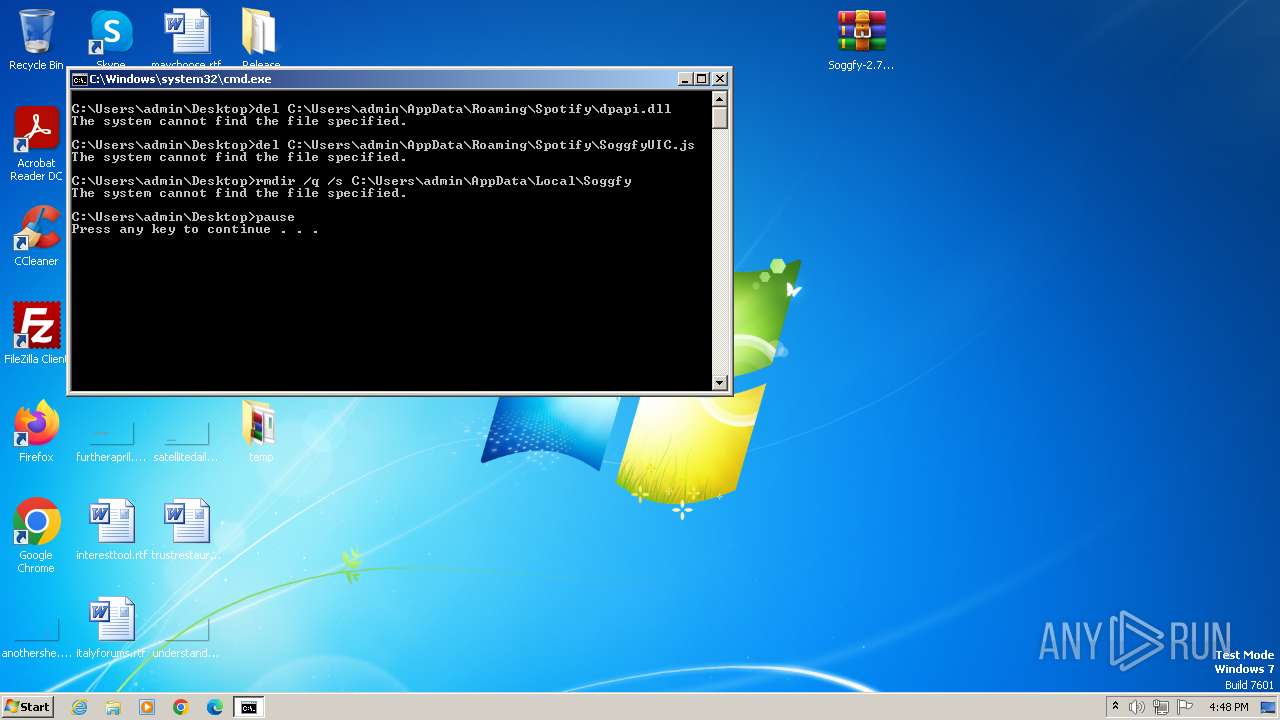
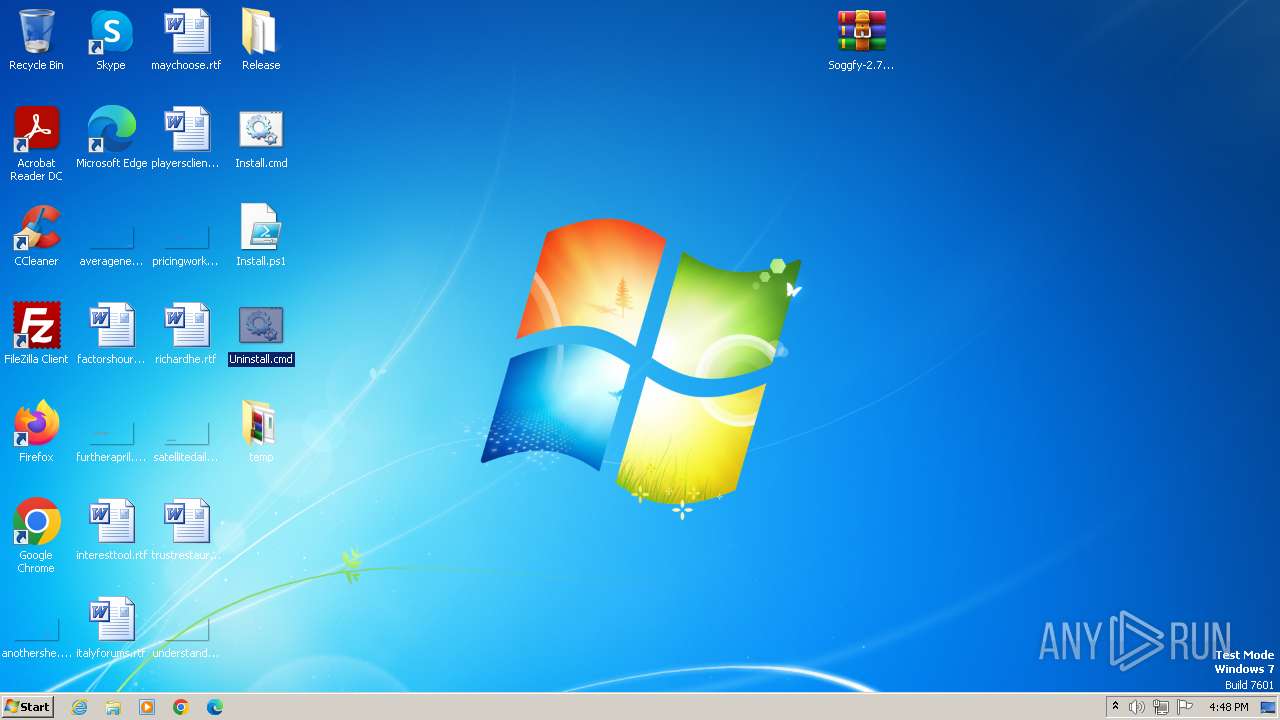
| 3080 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\Desktop\Uninstall.cmd" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
10 548
Read events
10 490
Write events
58
Delete events
0
Modification events
| (PID) Process: | (3976) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3976) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3976) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3976) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (3976) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (3976) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (3976) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
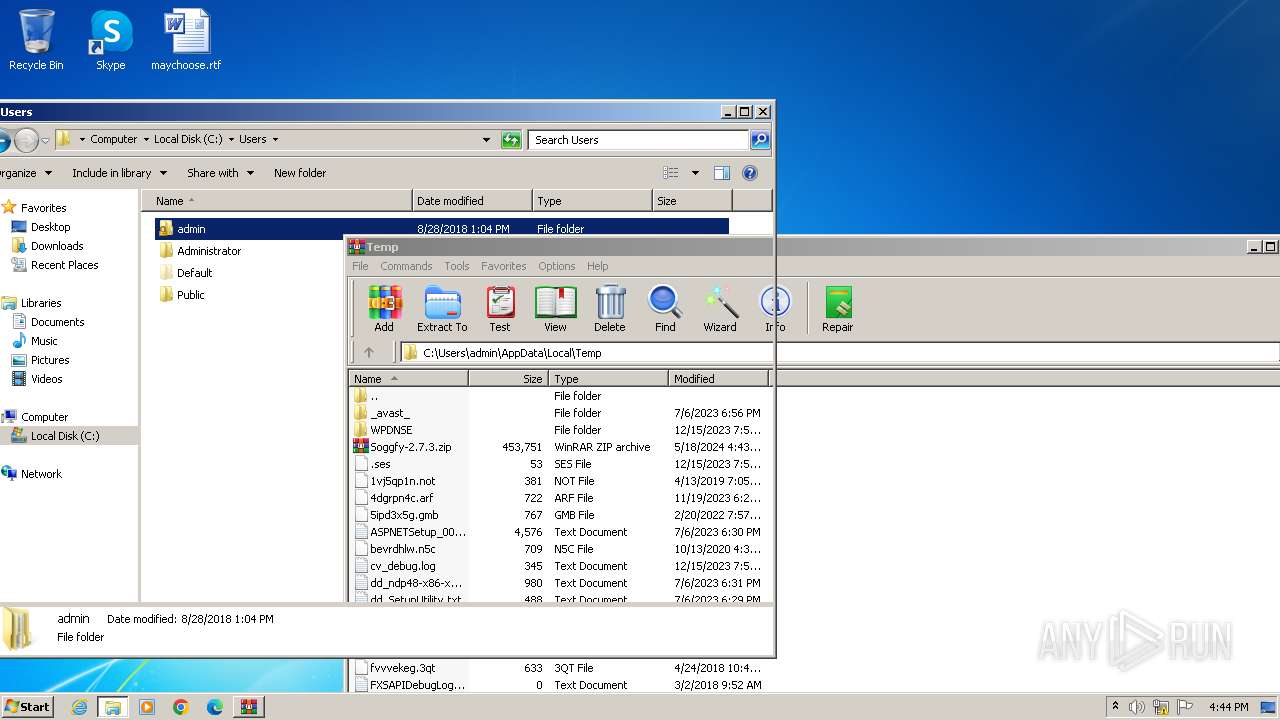
Value: C:\Users\admin\AppData\Local\Temp\Soggfy-2.7.3.zip | |||
| (PID) Process: | (3976) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3976) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3976) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
Executable files
3
Suspicious files
5
Text files
3
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1312 | 7zr.exe | C:\Users\admin\AppData\Local\Soggfy\ffmpeg\ffmpeg.exe | — | |
MD5:— | SHA256:— | |||
| 2356 | powershell.exe | C:\Users\admin\AppData\Local\Temp\z5oewklb.eve.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
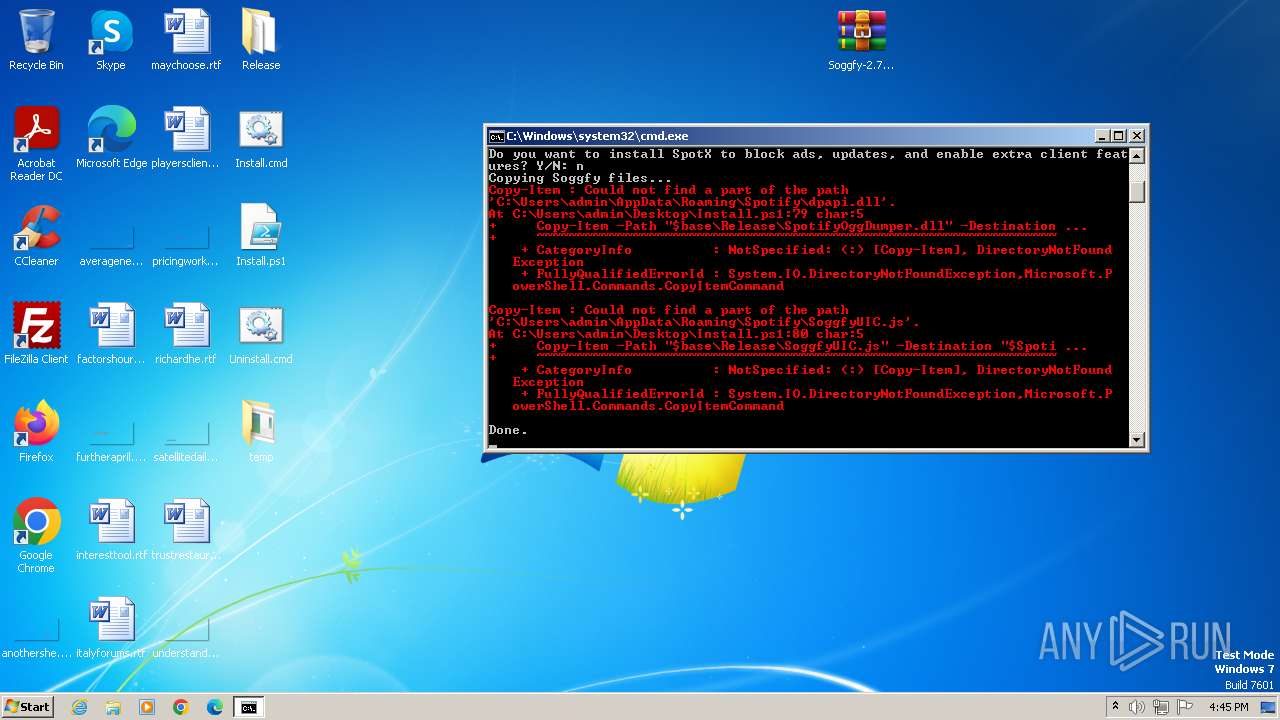
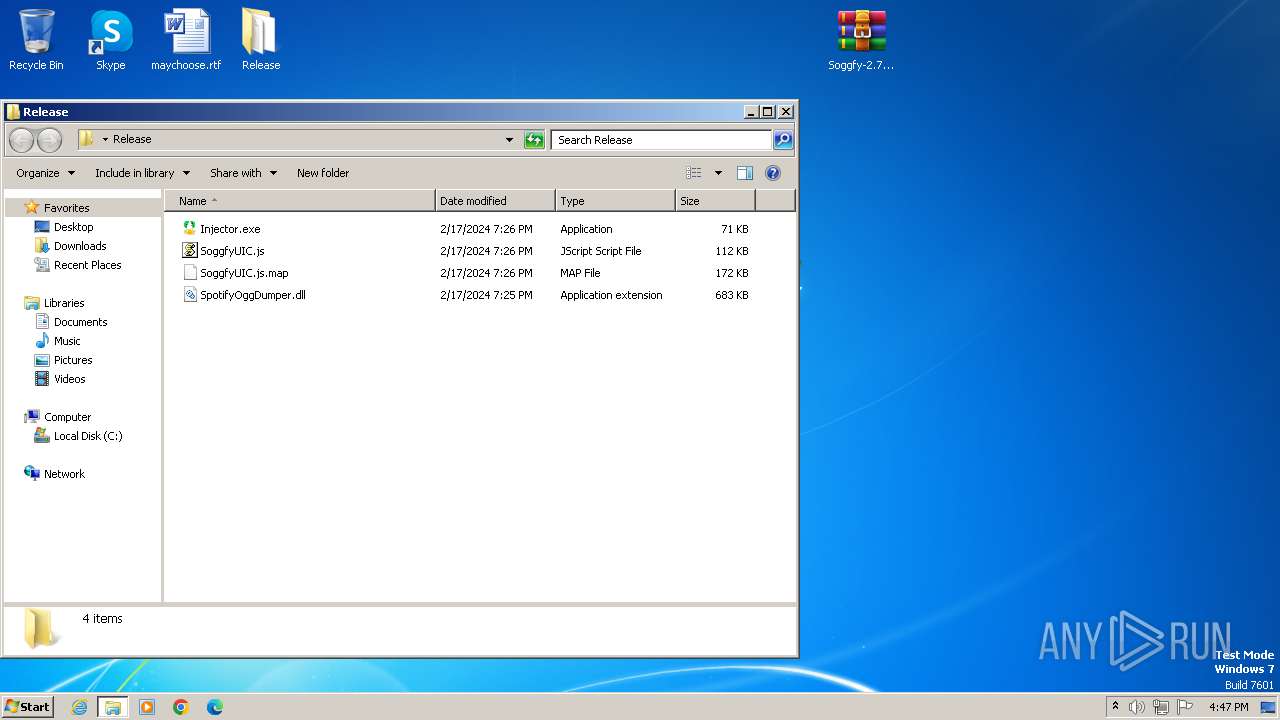
| 2328 | WinRAR.exe | C:\Users\admin\Desktop\Release\SoggfyUIC.js | s | |
MD5:717C1170196586A6EA3806BB1EA48489 | SHA256:E311DF6F3F492FEA55FB4799ED110B4BE391BA6665CD65CFB6854E8F9C627D29 | |||
| 2356 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\ModuleAnalysisCache | binary | |
MD5:DE3E389E155C6845D43C07185A11ACF1 | SHA256:6761E2D1F087BBAA8A8DB8B1294E66088FDBE0B9B7FC6E43476D8B2ABDB79E56 | |||
| 2328 | WinRAR.exe | C:\Users\admin\Desktop\Install.ps1 | text | |
MD5:9C2061D354D7FBC8157F7A46D7051F4E | SHA256:E9EF6E02095AA6130F1EDD86FC99702C1208A4D024F1C0F873046BFDDAF5C551 | |||
| 2328 | WinRAR.exe | C:\Users\admin\Desktop\Install.cmd | text | |
MD5:65EBBC8B0D5805614BD5A84B7E018717 | SHA256:C62E48A2F4F48379056A77D2F37F0A8777FE23FE73C1D275AC16B68E0B93FD03 | |||
| 2356 | powershell.exe | C:\Users\admin\Desktop\temp\7zr.exe | executable | |
MD5:E877ED2D9463E6729DB5768F23640AA4 | SHA256:2E2E69B6E3DA6D3BB46207D1393D6253E96ECB7DD1C4D6A41EC41A55F1516549 | |||
| 2356 | powershell.exe | C:\Users\admin\AppData\Local\Temp\pr1wb5v0.wtx.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 2328 | WinRAR.exe | C:\Users\admin\Desktop\Release\SpotifyOggDumper.dll | executable | |
MD5:FDFCCFA09F0A90E9D24E9A59F23A3168 | SHA256:3CB1DDEAA168063A24AF6D6B3EB9FACD09B7F4A1CB4186B10C83248268C59C13 | |||
| 2328 | WinRAR.exe | C:\Users\admin\Desktop\Uninstall.cmd | text | |
MD5:AB35FD2E4E1B3F7B8B08FFDCDE0557C9 | SHA256:EB30BEB18B15AA56F30AA8AAF8C79BA883F8D851F3E6C2347F0C338942A32BC8 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
10
DNS requests
6
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1088 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2356 | powershell.exe | 199.232.210.248:443 | upgrade.scdn.co | FASTLY | US | unknown |
2356 | powershell.exe | 140.82.121.6:443 | api.github.com | GITHUB | US | unknown |
2356 | powershell.exe | 140.82.121.4:443 | github.com | GITHUB | US | unknown |
2356 | powershell.exe | 185.199.108.133:443 | objects.githubusercontent.com | FASTLY | US | unknown |
2356 | powershell.exe | 49.12.202.237:443 | 7-zip.org | Hetzner Online GmbH | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
upgrade.scdn.co |
| unknown |
api.github.com |
| whitelisted |
github.com |
| shared |
objects.githubusercontent.com |
| shared |
7-zip.org |
| unknown |