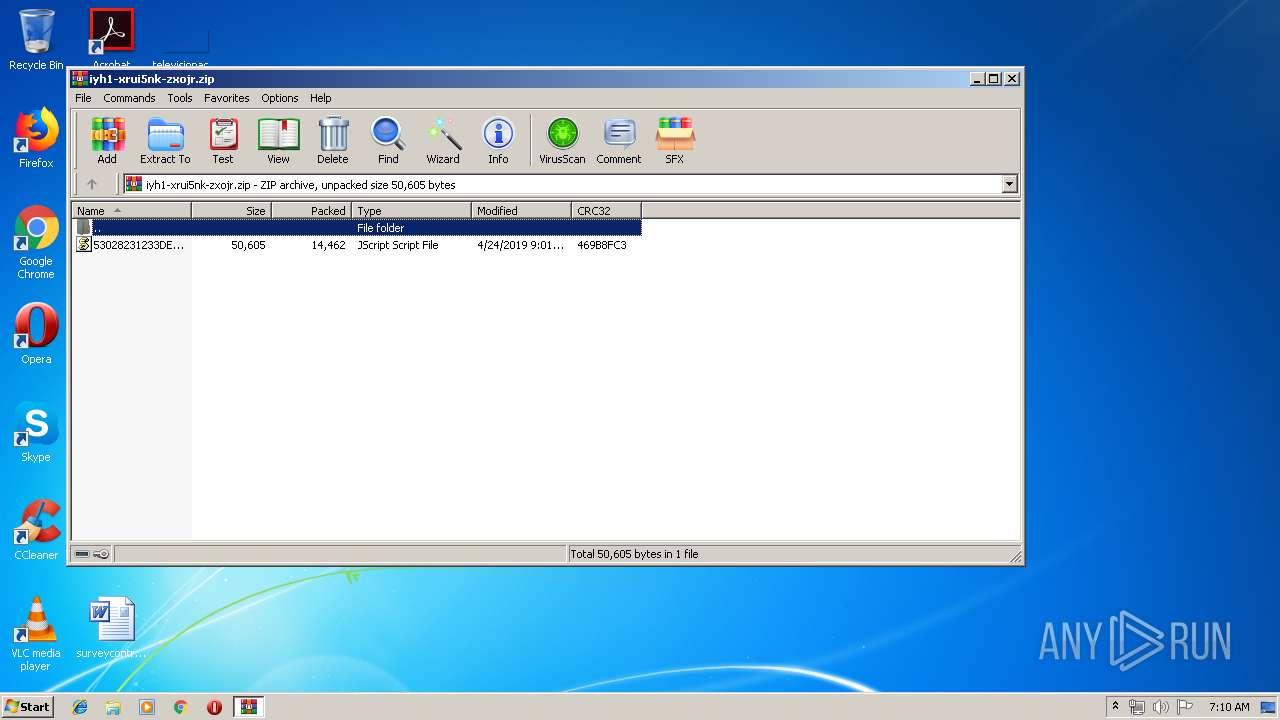
| download: | iyh1-xrui5nk-zxojr |
| Full analysis: | https://app.any.run/tasks/9b3e0972-d6cf-45aa-b92e-5d0ba2a78b8b |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | April 24, 2019, 06:09:47 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 785B32617D628D3A44D8E6021C6021F9 |
| SHA1: | 48A25342A34DDEFE20A7A7AA175BCBA43C8BED6E |
| SHA256: | B5808CF7C9AA4DAA76255F81CE55E6D4F4B2F138FCEFBA583B48D94AA1E5C928 |
| SSDEEP: | 384:mNZ1OvLoQ9HxbK2XeZh/9e7J0nz2xJ5BlrNGSvZ7yP05E:CZE0Q6hVe7J0qxJ3iSvZePB |
MALICIOUS
Application was dropped or rewritten from another process
- 9f4t3ncyh.exe (PID: 2740)
- soundser.exe (PID: 2368)
- 9f4t3ncyh.exe (PID: 3468)
- soundser.exe (PID: 3252)
- XsuCuPCvvp2aGJrw.exe (PID: 3424)
- soundser.exe (PID: 3332)
- soundser.exe (PID: 3780)
- XsuCuPCvvp2aGJrw.exe (PID: 2364)
EMOTET was detected
- soundser.exe (PID: 3252)
- soundser.exe (PID: 3780)
Changes the autorun value in the registry
- soundser.exe (PID: 3252)
Emotet process was detected
- soundser.exe (PID: 3332)
- soundser.exe (PID: 2368)
Connects to CnC server
- soundser.exe (PID: 3780)
- soundser.exe (PID: 3252)
SUSPICIOUS
Executable content was dropped or overwritten
- 9f4t3ncyh.exe (PID: 2740)
- WScript.exe (PID: 2968)
- soundser.exe (PID: 3252)
- XsuCuPCvvp2aGJrw.exe (PID: 2364)
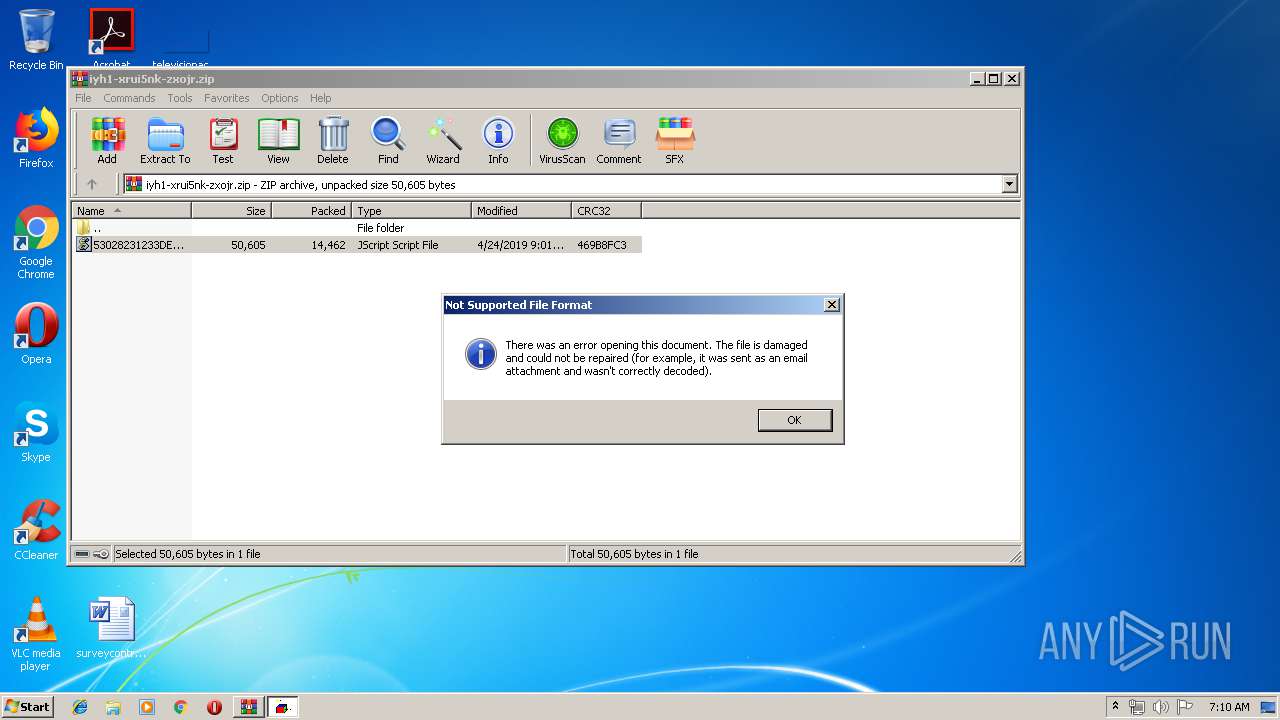
Executes scripts
- WinRAR.exe (PID: 2656)
Application launched itself
- XsuCuPCvvp2aGJrw.exe (PID: 3424)
- soundser.exe (PID: 2368)
- soundser.exe (PID: 3332)
Creates files in the user directory
- WScript.exe (PID: 2968)
Starts itself from another location
- 9f4t3ncyh.exe (PID: 2740)
- XsuCuPCvvp2aGJrw.exe (PID: 2364)
Connects to server without host name
- soundser.exe (PID: 3252)
- soundser.exe (PID: 3780)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0002 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:04:24 09:01:02 |
| ZipCRC: | 0x469b8fc3 |
| ZipCompressedSize: | 14462 |
| ZipUncompressedSize: | 50605 |
| ZipFileName: | 53028231233DE_April_24_2019.js |
Total processes
40
Monitored processes
10
Malicious processes
10
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2364 | --550947cf | C:\Users\admin\AppData\Local\soundser\XsuCuPCvvp2aGJrw.exe | XsuCuPCvvp2aGJrw.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Memory Diagnostic Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2368 | "C:\Users\admin\AppData\Local\soundser\soundser.exe" | C:\Users\admin\AppData\Local\soundser\soundser.exe | 9f4t3ncyh.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2656 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\iyh1-xrui5nk-zxojr.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2740 | --86b3304e | C:\Users\admin\AppData\Local\Temp\9f4t3ncyh.exe | 9f4t3ncyh.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2968 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\Rar$DIa2656.23628\53028231233DE_April_24_2019.js" | C:\Windows\System32\WScript.exe | WinRAR.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 3252 | --3ab57678 | C:\Users\admin\AppData\Local\soundser\soundser.exe | soundser.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3332 | "C:\Users\admin\AppData\Local\soundser\soundser.exe" | C:\Users\admin\AppData\Local\soundser\soundser.exe | XsuCuPCvvp2aGJrw.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Memory Diagnostic Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3424 | "C:\Users\admin\AppData\Local\soundser\XsuCuPCvvp2aGJrw.exe" | C:\Users\admin\AppData\Local\soundser\XsuCuPCvvp2aGJrw.exe | — | soundser.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Memory Diagnostic Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3468 | "C:\Users\admin\AppData\Local\Temp\9f4t3ncyh.exe" | C:\Users\admin\AppData\Local\Temp\9f4t3ncyh.exe | — | WScript.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3780 | --3ab57678 | C:\Users\admin\AppData\Local\soundser\soundser.exe | soundser.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Memory Diagnostic Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
980
Read events
920
Write events
60
Delete events
0
Modification events
| (PID) Process: | (2656) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2656) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2656) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2656) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\iyh1-xrui5nk-zxojr.zip | |||
| (PID) Process: | (2656) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2656) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2656) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2656) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2656) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\wshext.dll,-4804 |
Value: JScript Script File | |||
| (PID) Process: | (2656) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
4
Suspicious files
0
Text files
2
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2968 | WScript.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@robertwatton.co[1].txt | text | |
MD5:— | SHA256:— | |||
| 2968 | WScript.exe | C:\Users\admin\AppData\Local\Temp\9f4t3ncyh.exe | executable | |
MD5:— | SHA256:— | |||
| 3252 | soundser.exe | C:\Users\admin\AppData\Local\soundser\XsuCuPCvvp2aGJrw.exe | executable | |
MD5:— | SHA256:— | |||
| 2740 | 9f4t3ncyh.exe | C:\Users\admin\AppData\Local\soundser\soundser.exe | executable | |
MD5:— | SHA256:— | |||
| 2364 | XsuCuPCvvp2aGJrw.exe | C:\Users\admin\AppData\Local\soundser\soundser.exe | executable | |
MD5:— | SHA256:— | |||
| 2656 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa2656.23628\53028231233DE_April_24_2019.js | text | |
MD5:— | SHA256:— | |||
| 2968 | WScript.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\IETldCache\index.dat | dat | |
MD5:D7A950FEFD60DBAA01DF2D85FEFB3862 | SHA256:75D0B1743F61B76A35B1FEDD32378837805DE58D79FA950CB6E8164BFA72073A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
6
DNS requests
1
Threats
22
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3252 | soundser.exe | POST | — | 70.116.68.186:80 | http://70.116.68.186/balloon/window/ | US | — | — | malicious |
3780 | soundser.exe | POST | — | 70.116.68.186:80 | http://70.116.68.186/acquire/ | US | — | — | malicious |
3780 | soundser.exe | POST | — | 68.229.130.39:80 | http://68.229.130.39/srvc/child/ | US | — | — | malicious |
3252 | soundser.exe | POST | 200 | 190.112.228.47:443 | http://190.112.228.47:443/health/ | CW | binary | 120 Kb | malicious |
2968 | WScript.exe | GET | — | 185.11.240.11:80 | http://robertwatton.co.uk/uo_LL/ | GB | — | — | suspicious |
3252 | soundser.exe | POST | — | 68.229.130.39:80 | http://68.229.130.39/site/balloon/ringin/ | US | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2968 | WScript.exe | 185.11.240.11:80 | robertwatton.co.uk | UK Webhosting Ltd | GB | suspicious |
3252 | soundser.exe | 68.229.130.39:80 | — | Cox Communications Inc. | US | malicious |
3780 | soundser.exe | 68.229.130.39:80 | — | Cox Communications Inc. | US | malicious |
3252 | soundser.exe | 190.112.228.47:443 | — | Columbus Communications Curacao NV | CW | malicious |
3252 | soundser.exe | 70.116.68.186:80 | — | Time Warner Cable Internet LLC | US | malicious |
— | — | 70.116.68.186:80 | — | Time Warner Cable Internet LLC | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
robertwatton.co.uk |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2968 | WScript.exe | Misc activity | SUSPICIOUS [PTsecurity] Cmd.Powershell.Download HTTP UserAgent (Win7) |
2968 | WScript.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2968 | WScript.exe | A Network Trojan was detected | ET CURRENT_EVENTS Likely Evil EXE download from MSXMLHTTP non-exe extension M2 |
2968 | WScript.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
3252 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
3252 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
3252 | soundser.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 11 |
3252 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
3252 | soundser.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |
3780 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
12 ETPRO signatures available at the full report