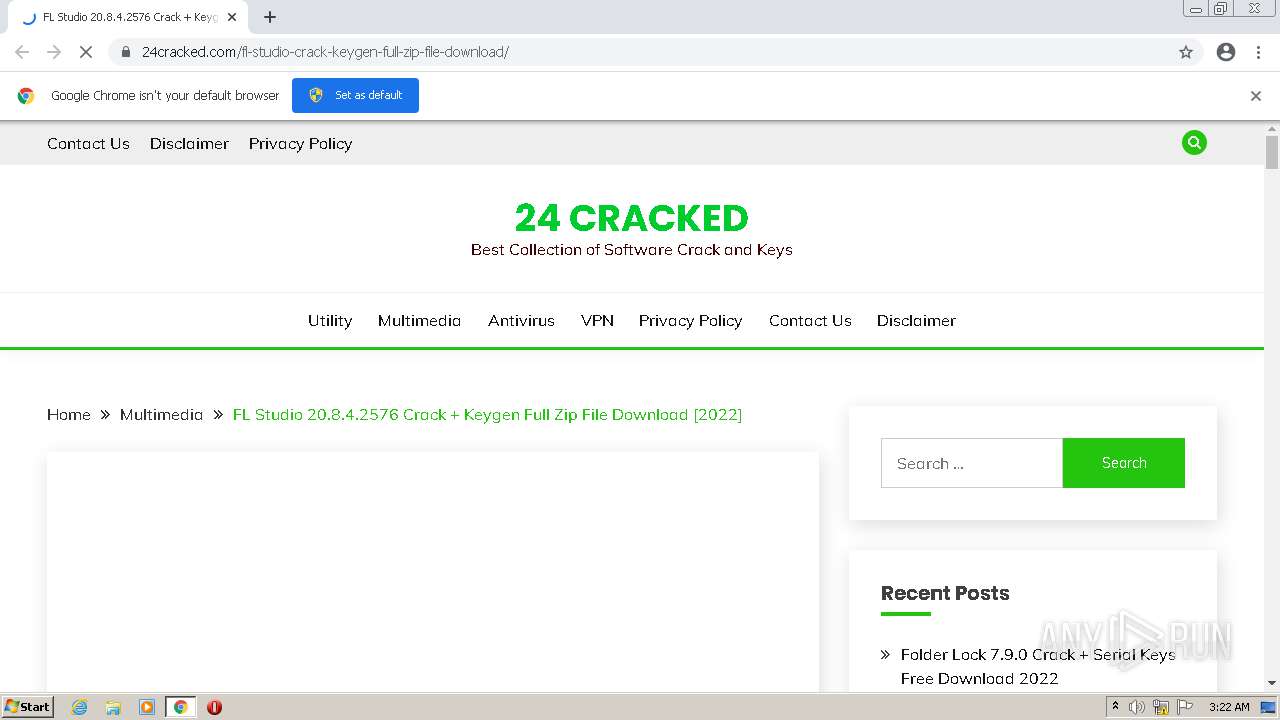
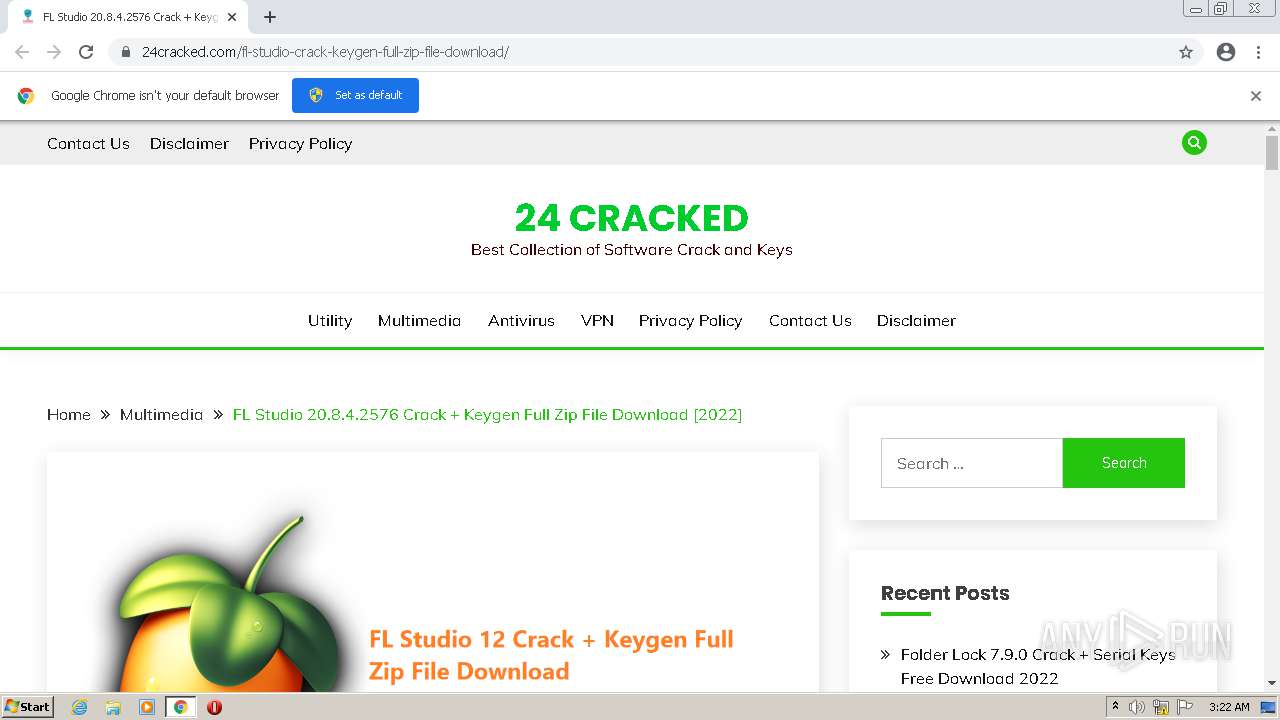
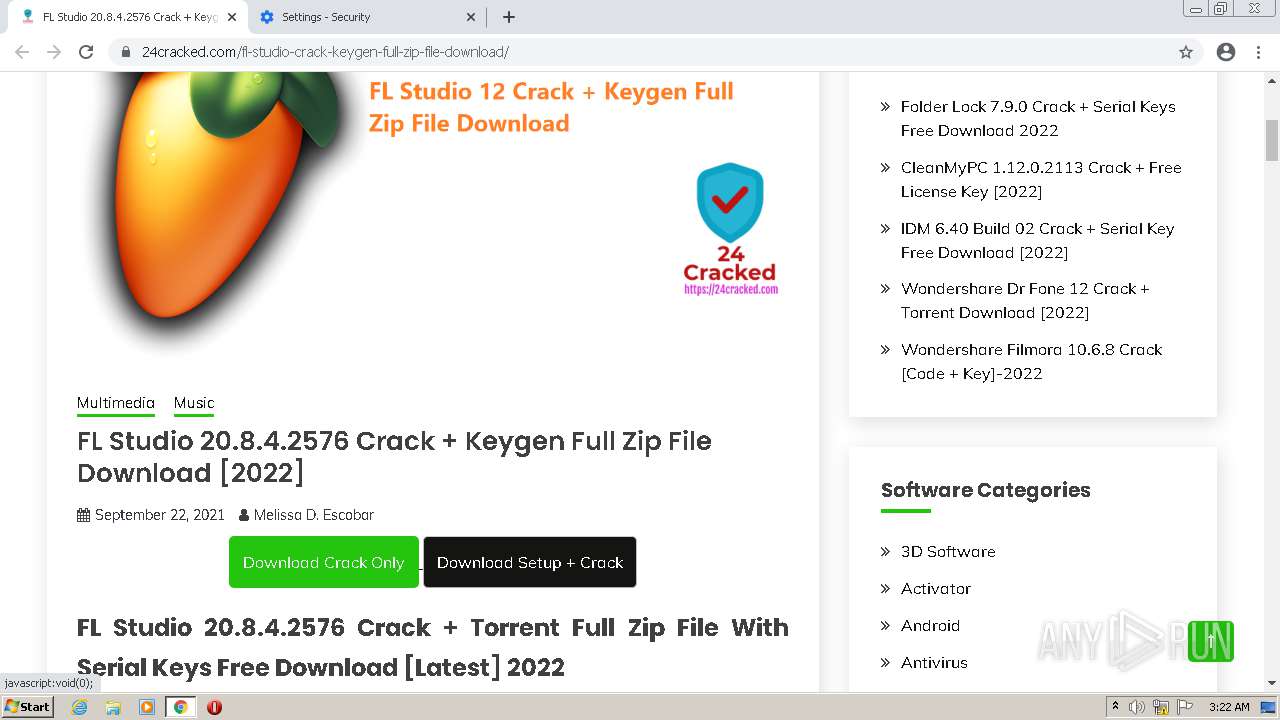
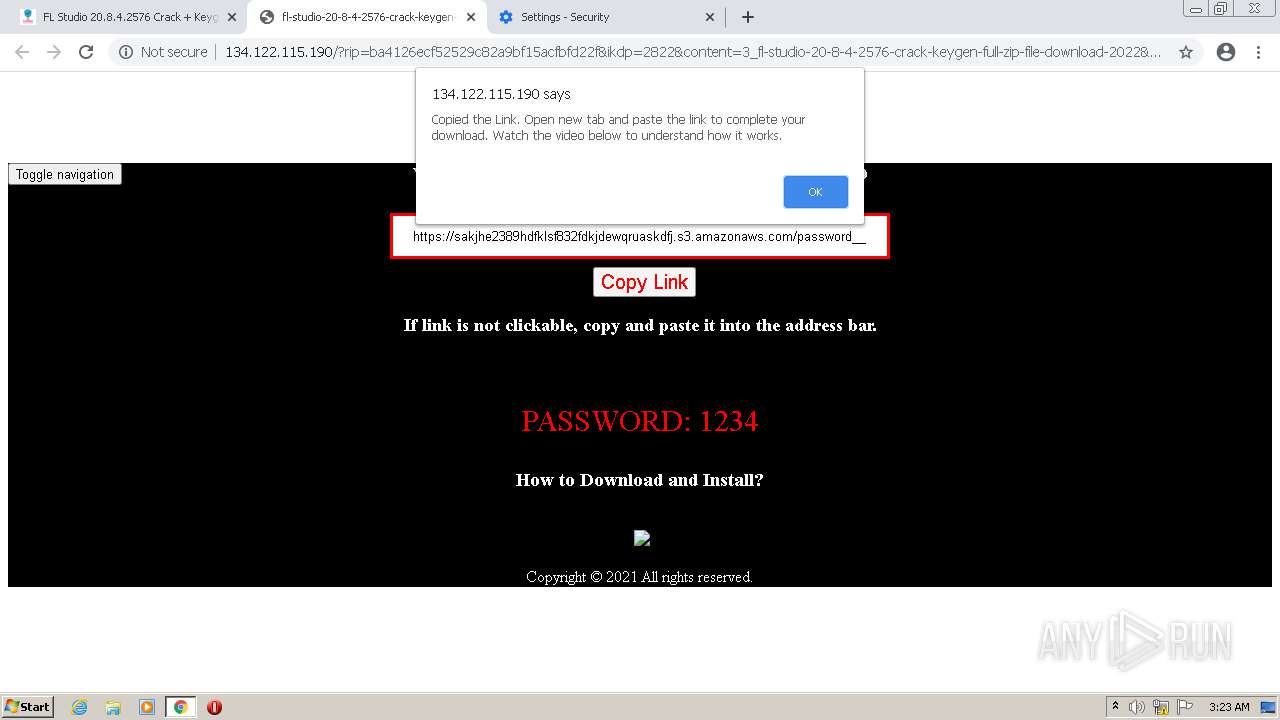
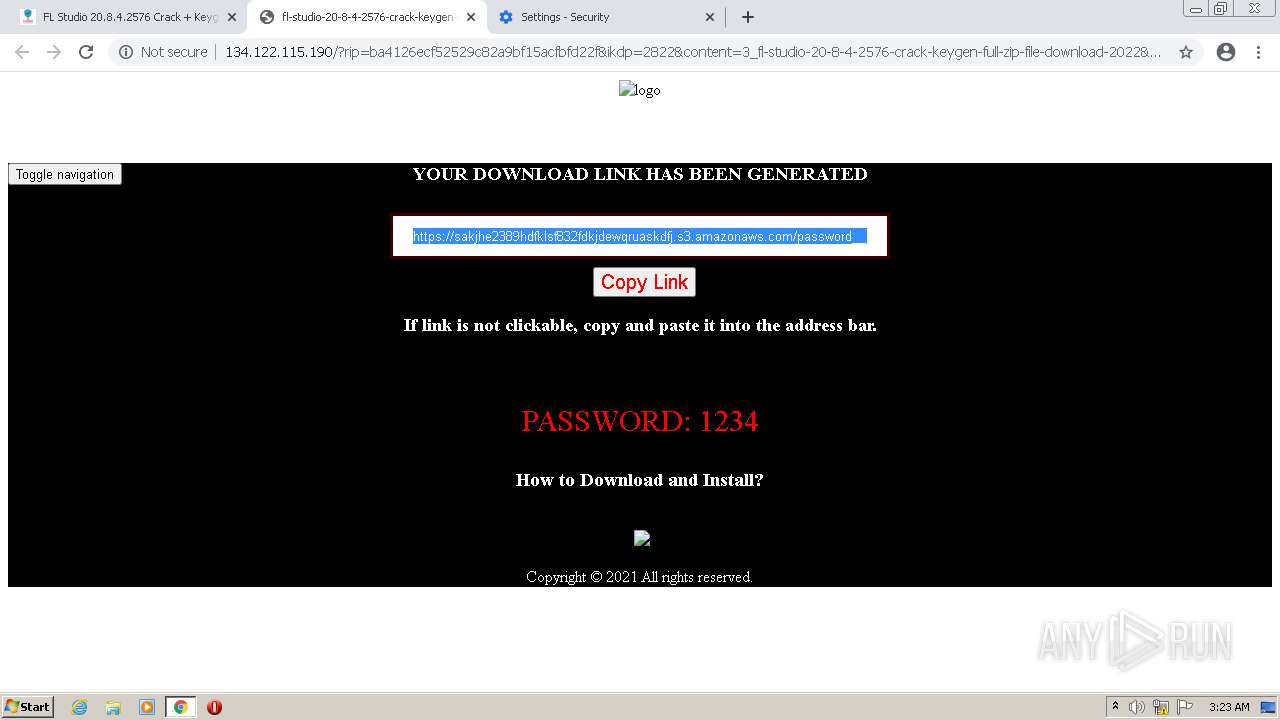
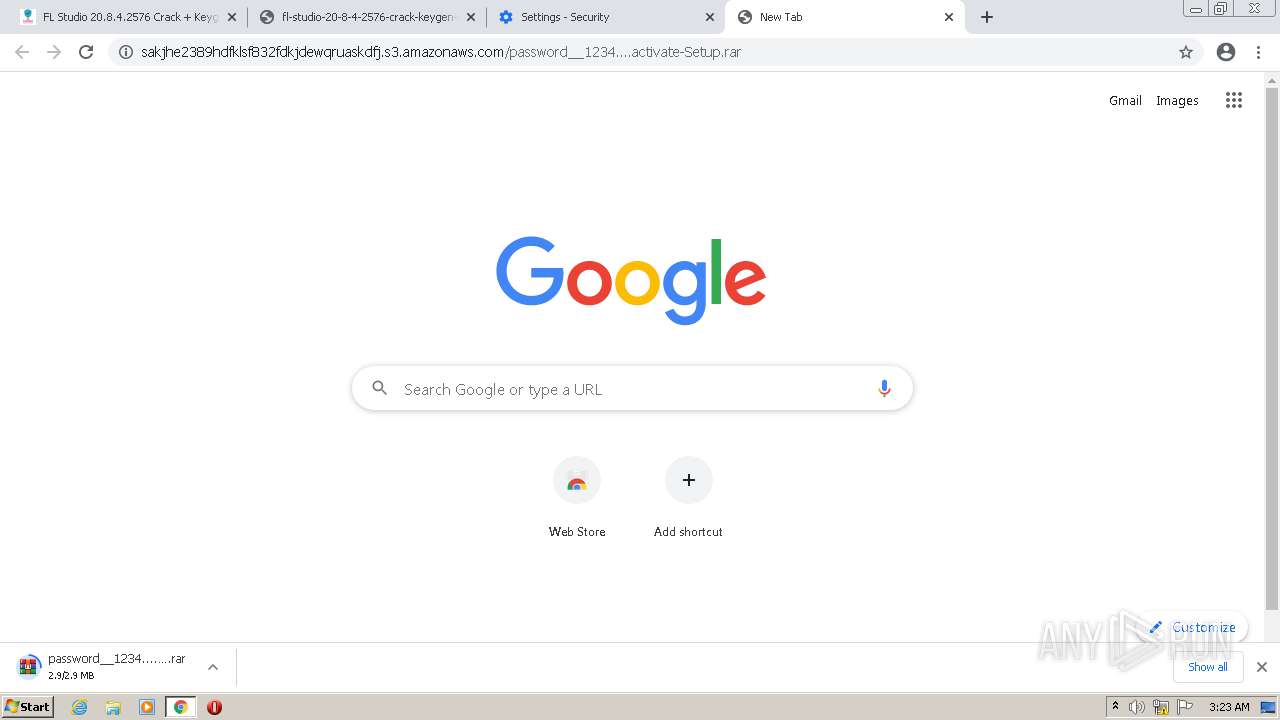
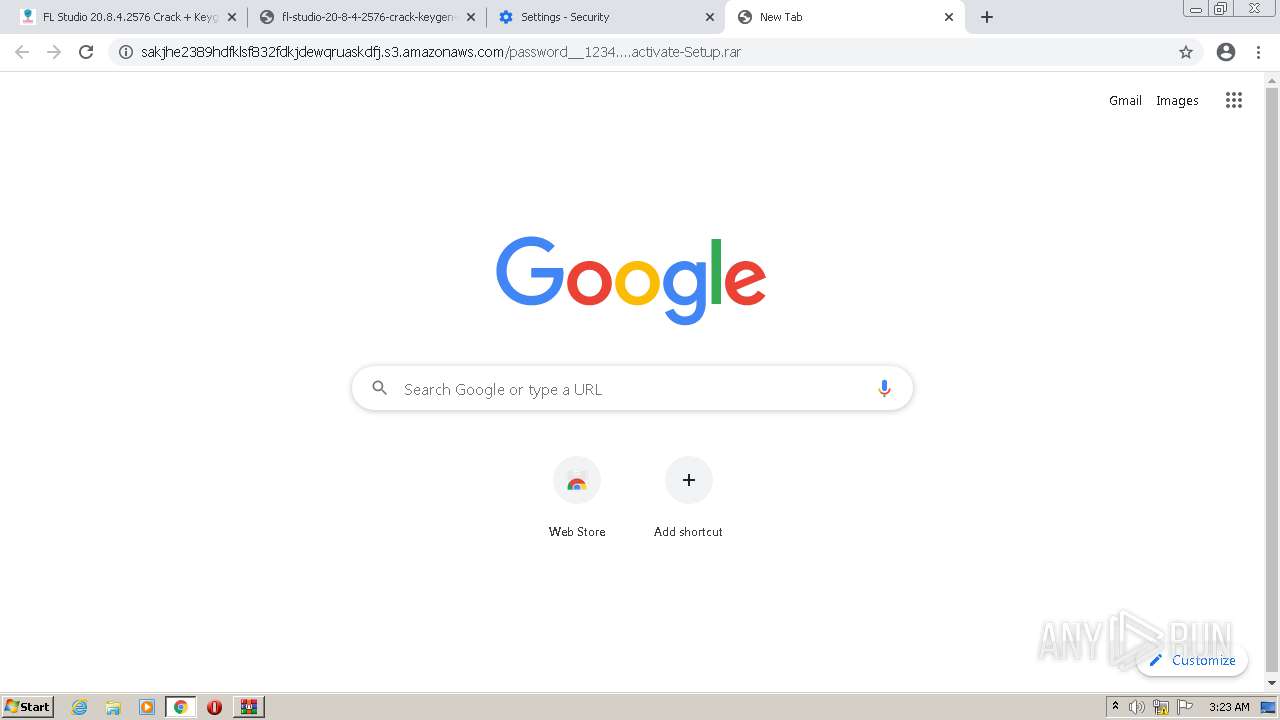
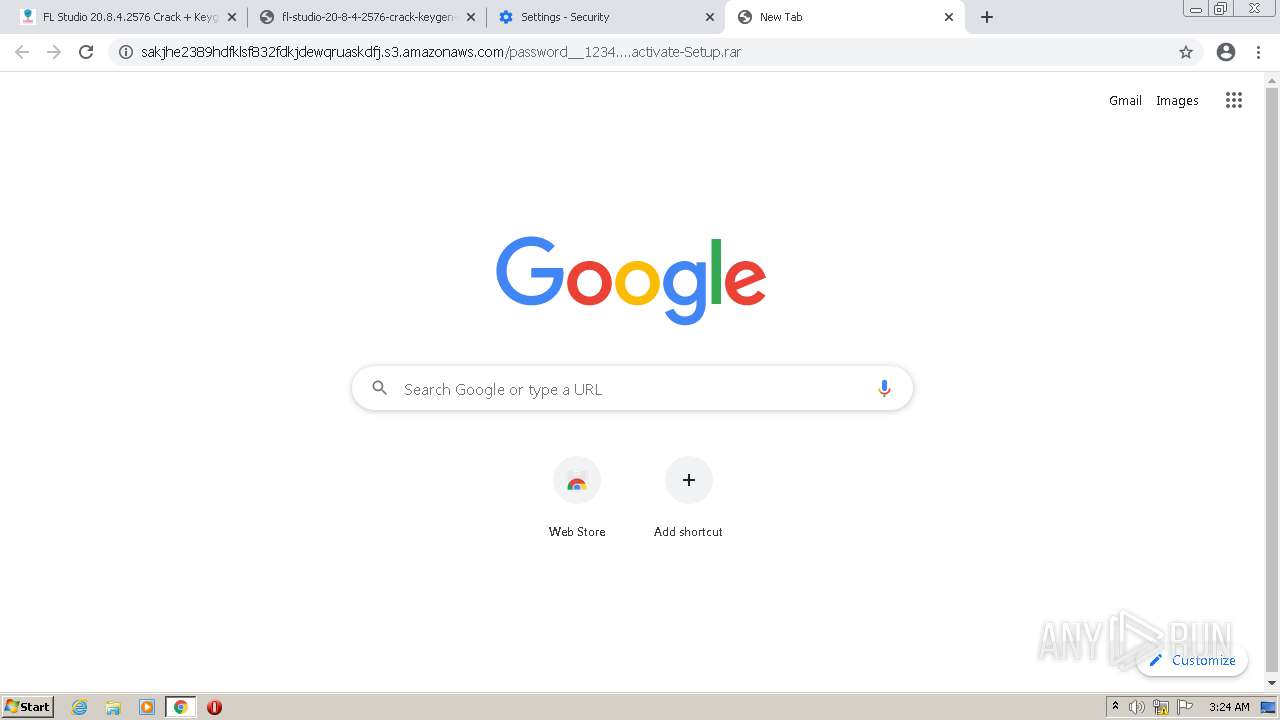
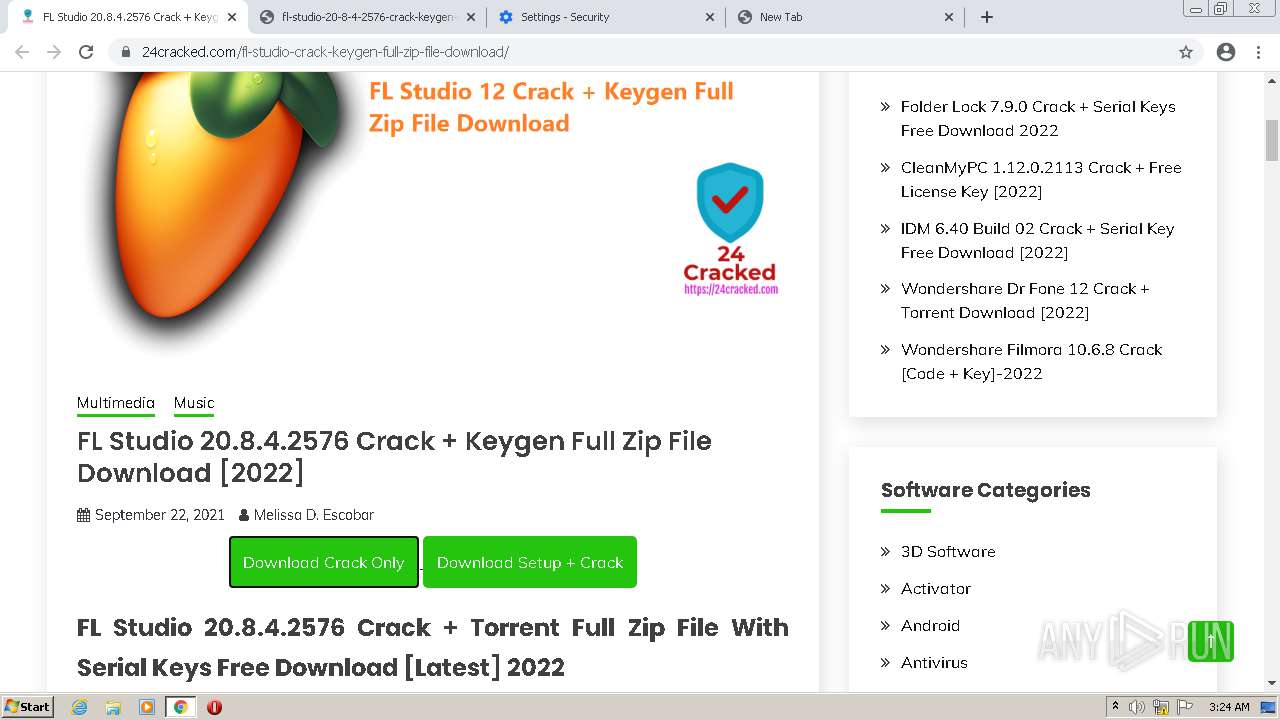
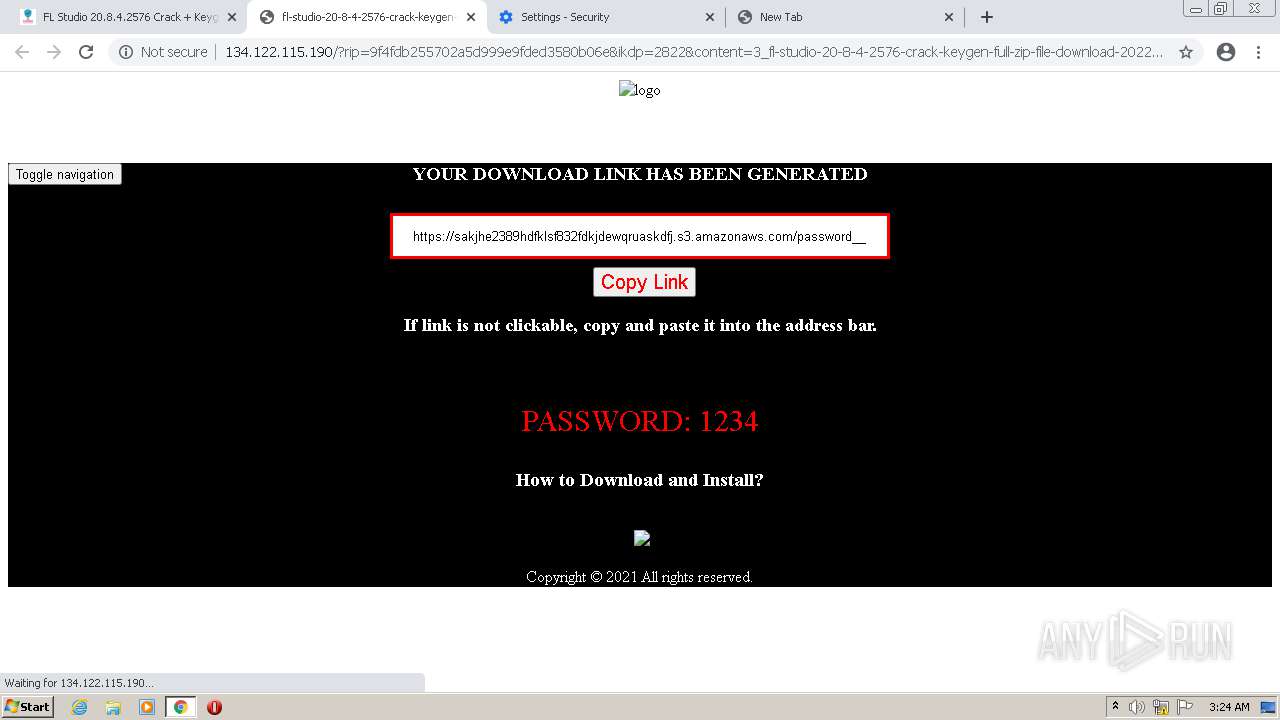
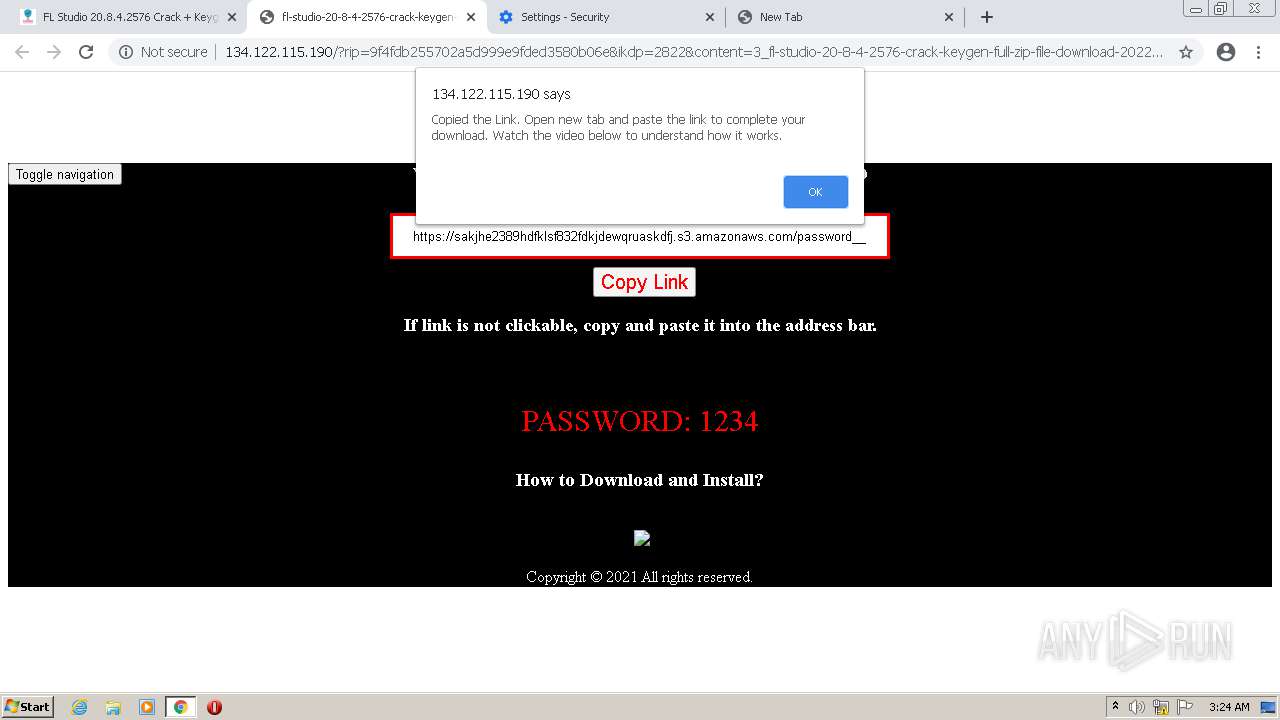
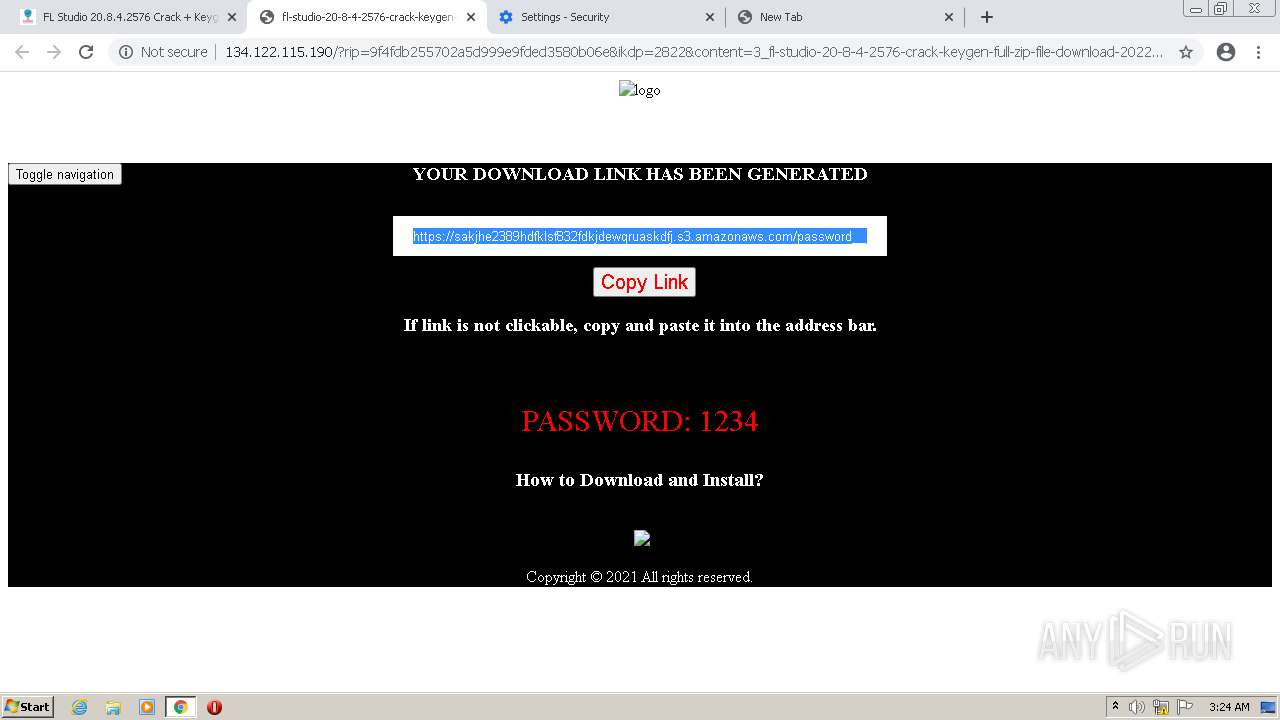
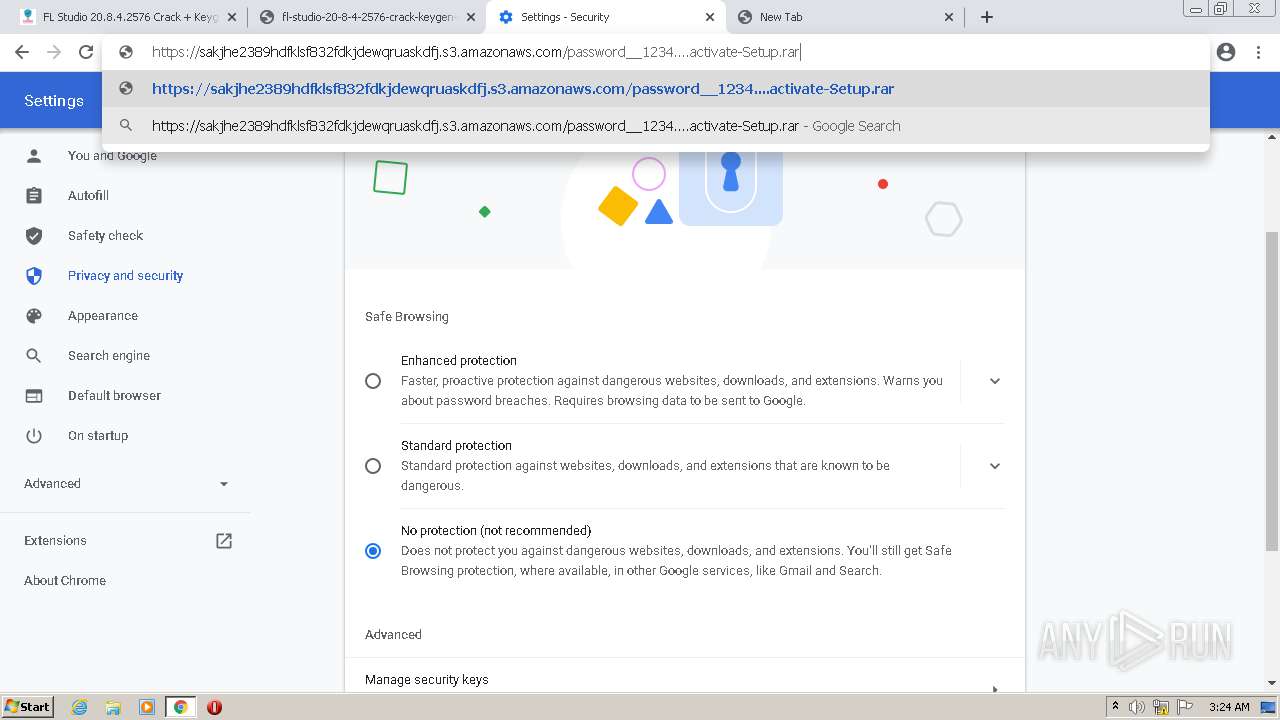
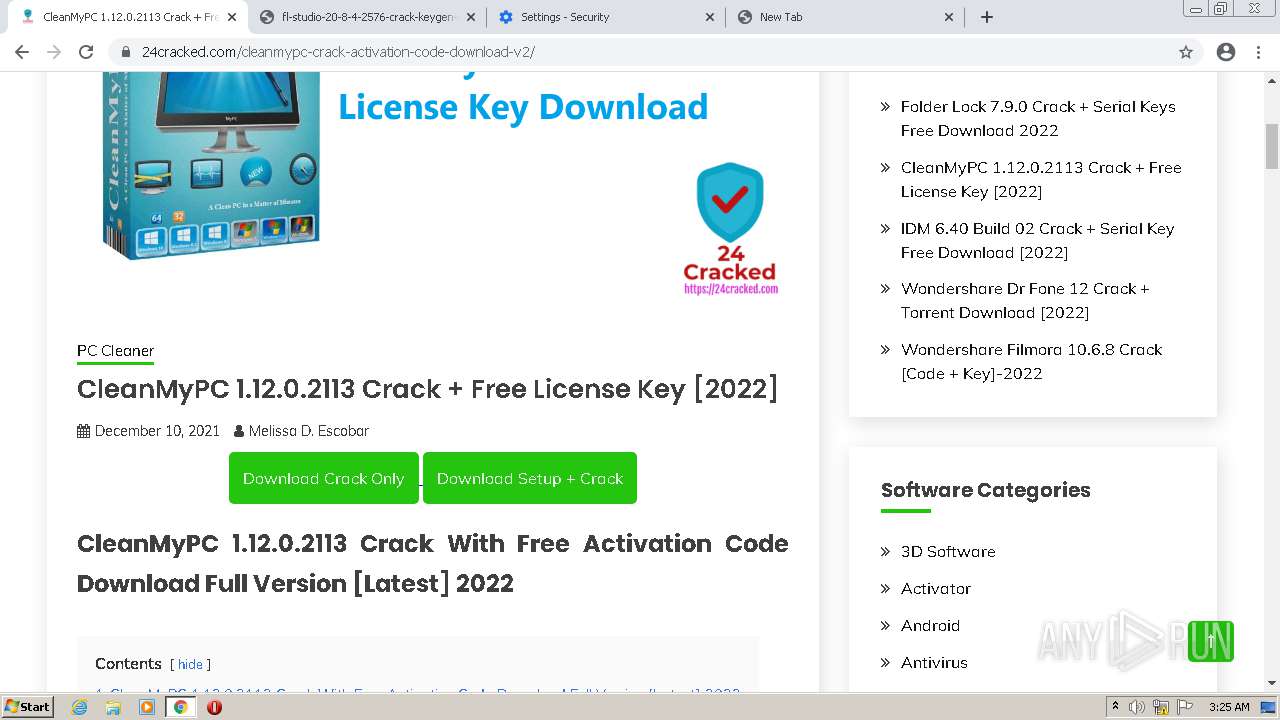
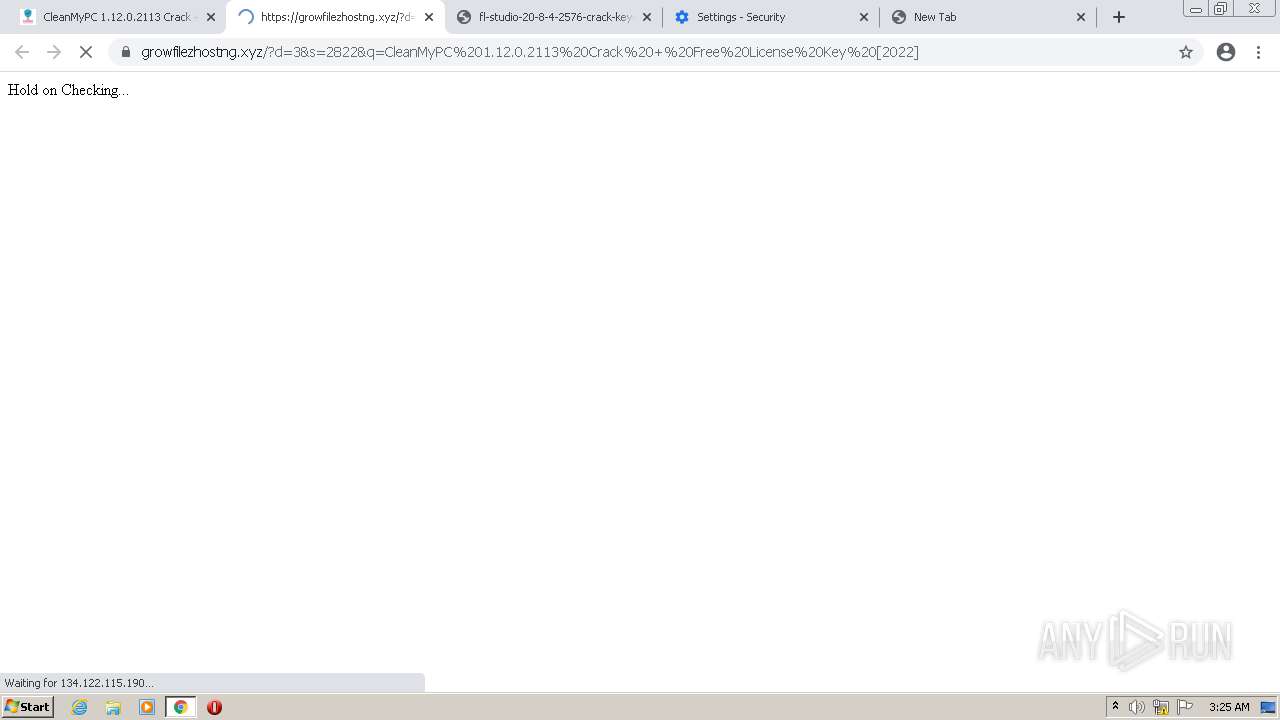
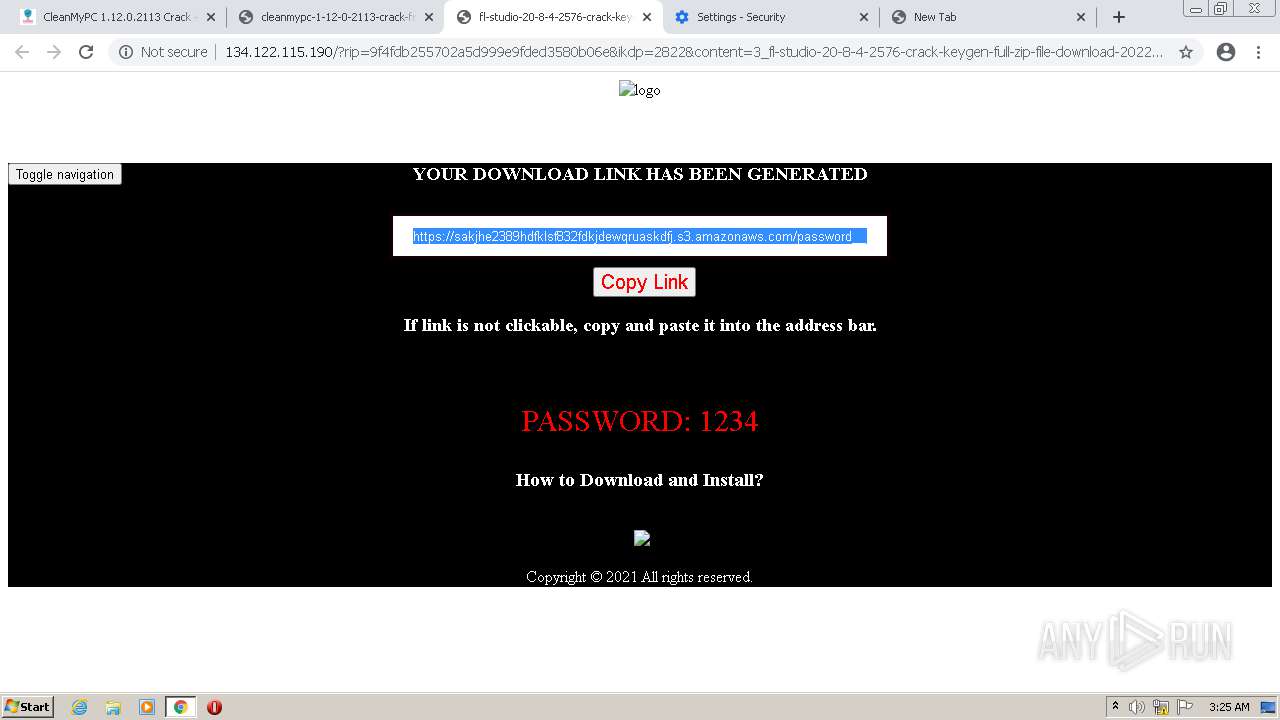
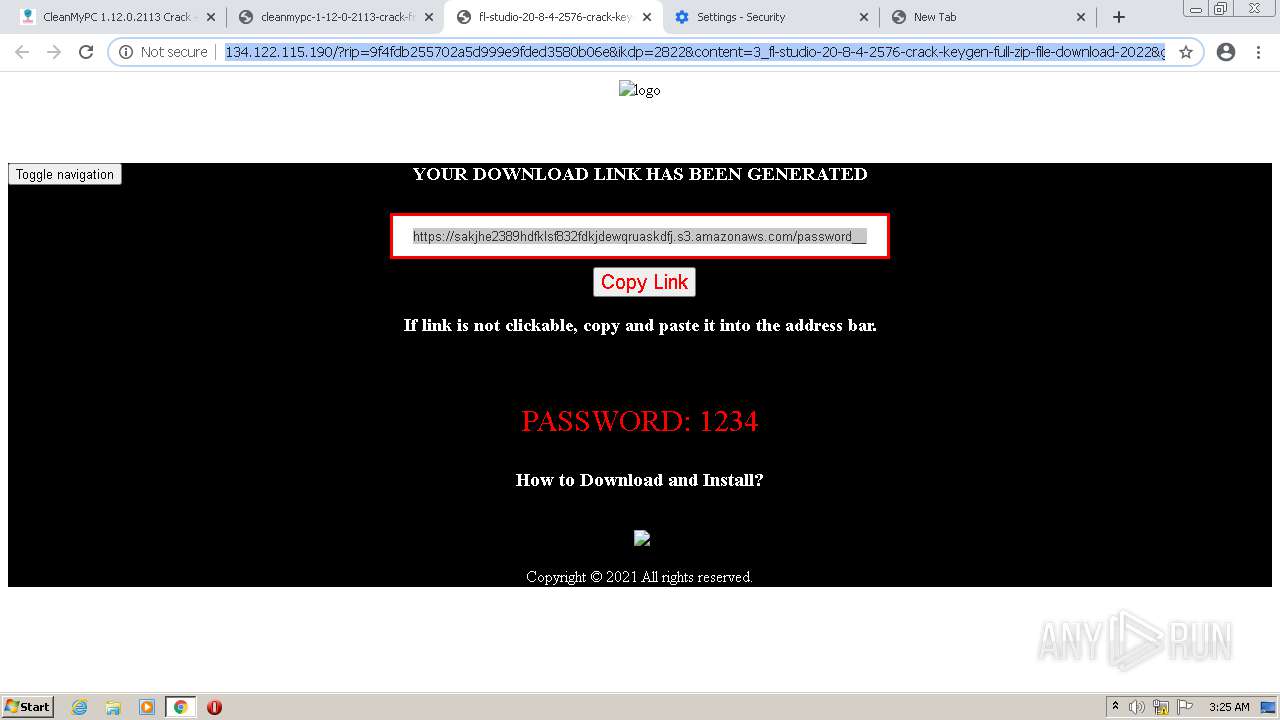
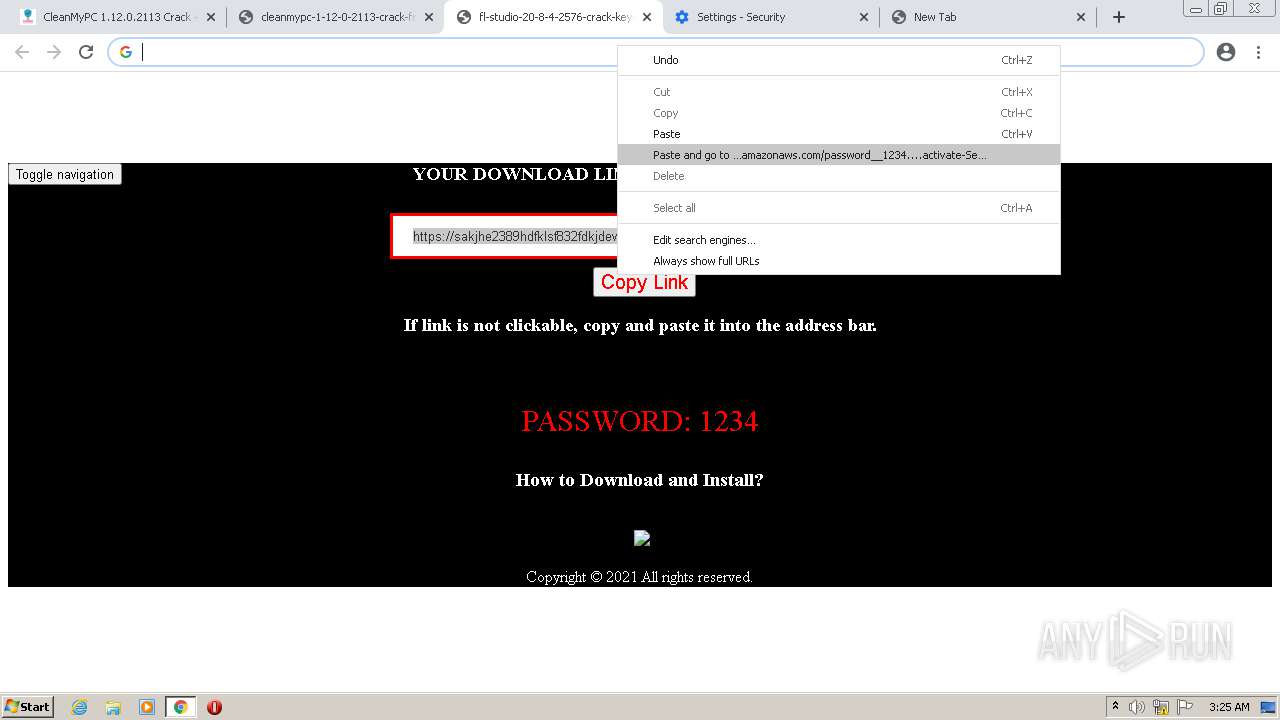
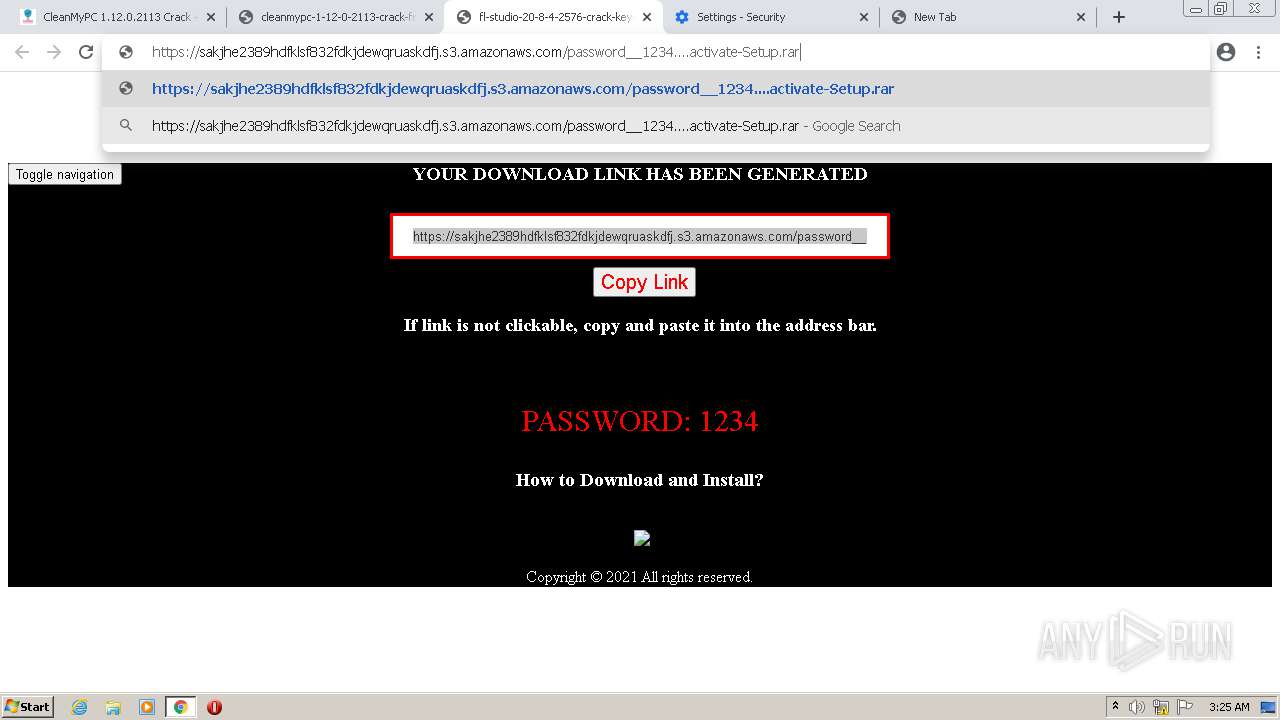
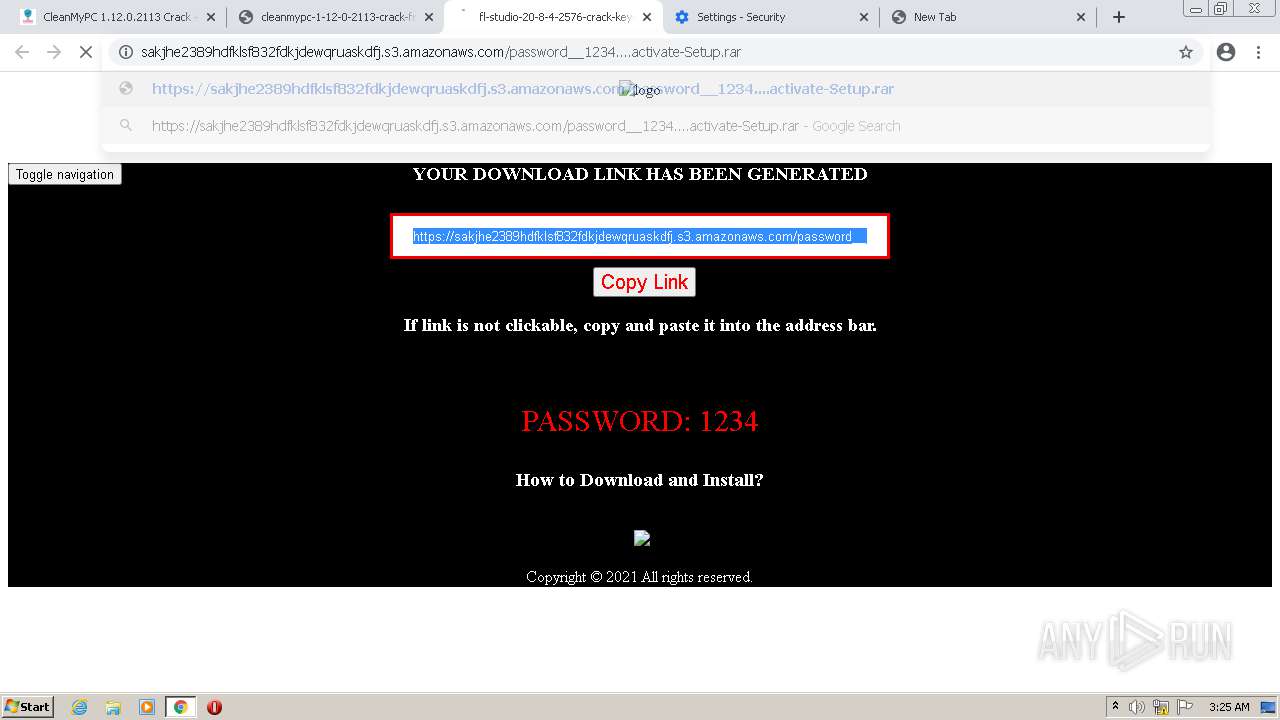
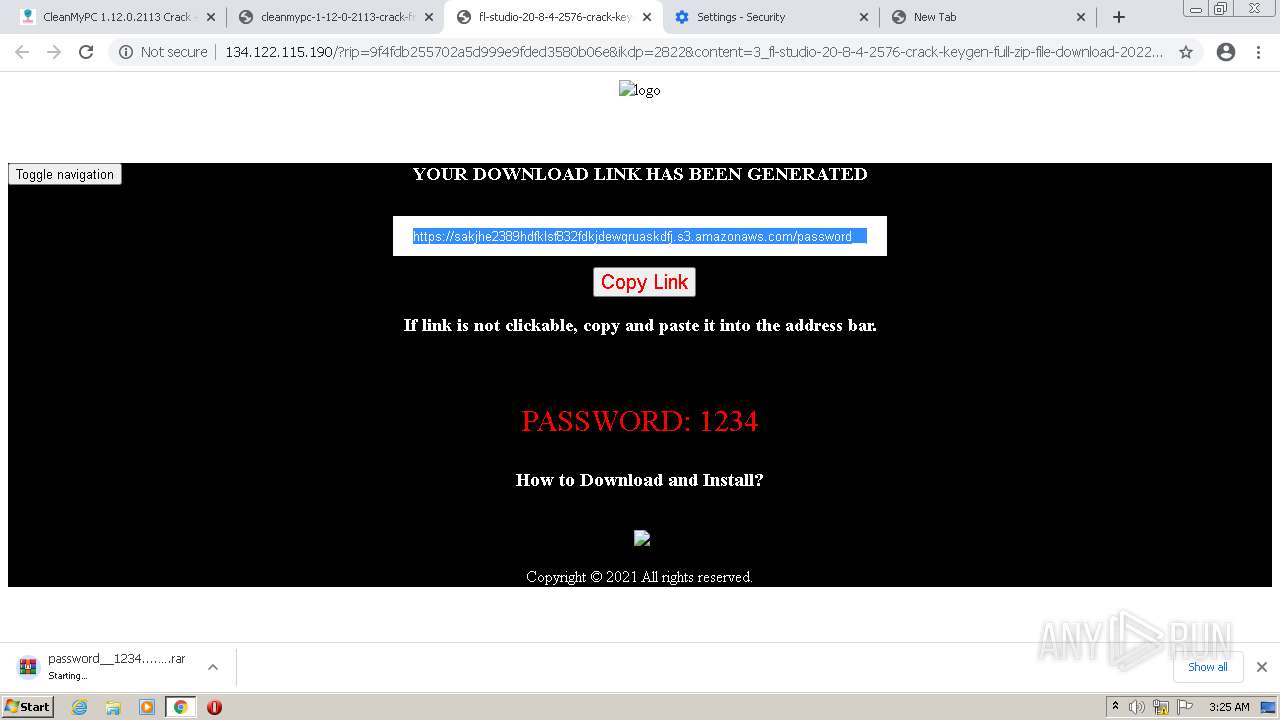
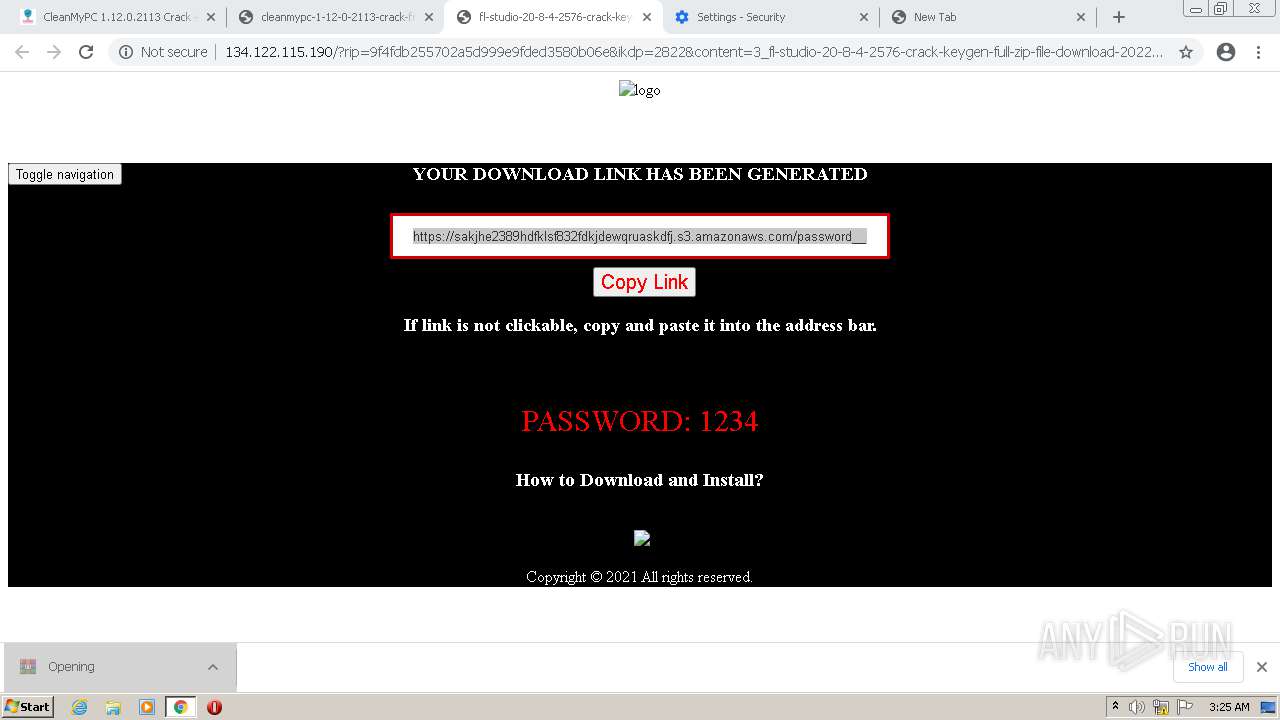
| URL: | https://24cracked.com/fl-studio-crack-keygen-full-zip-file-download/ |
| Full analysis: | https://app.any.run/tasks/13181c80-231c-4f85-bb74-90b21c668032 |
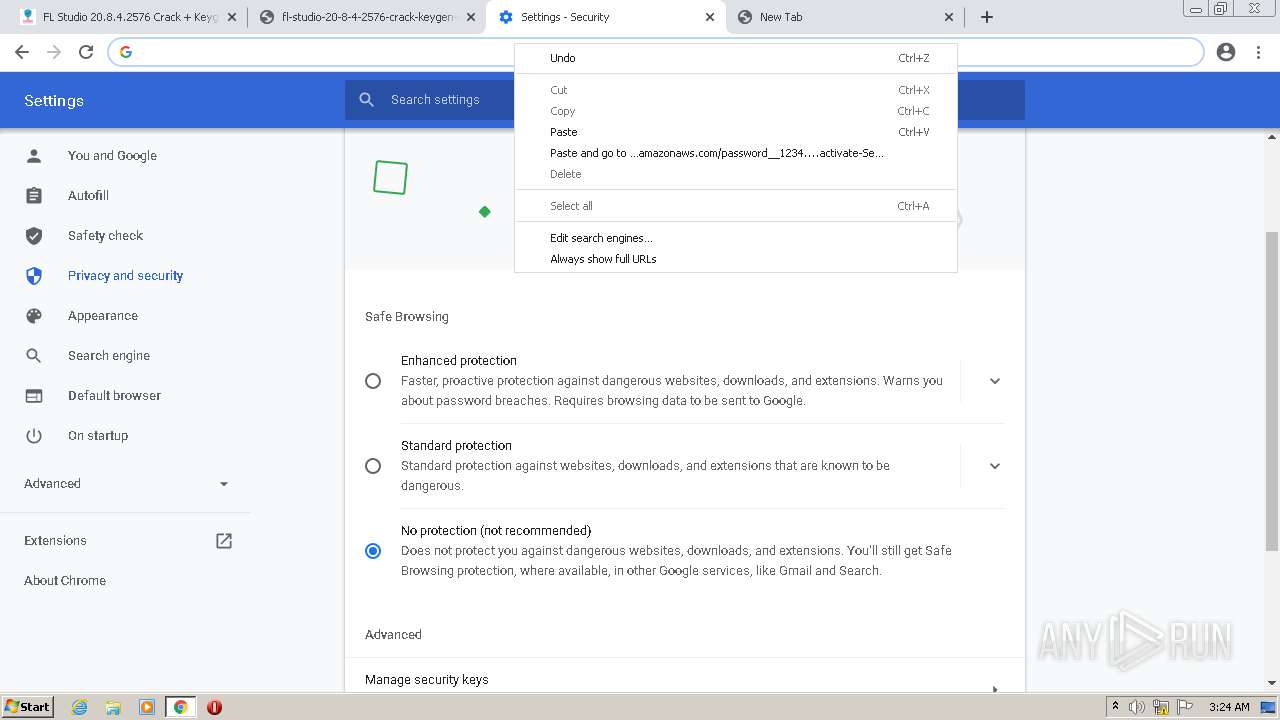
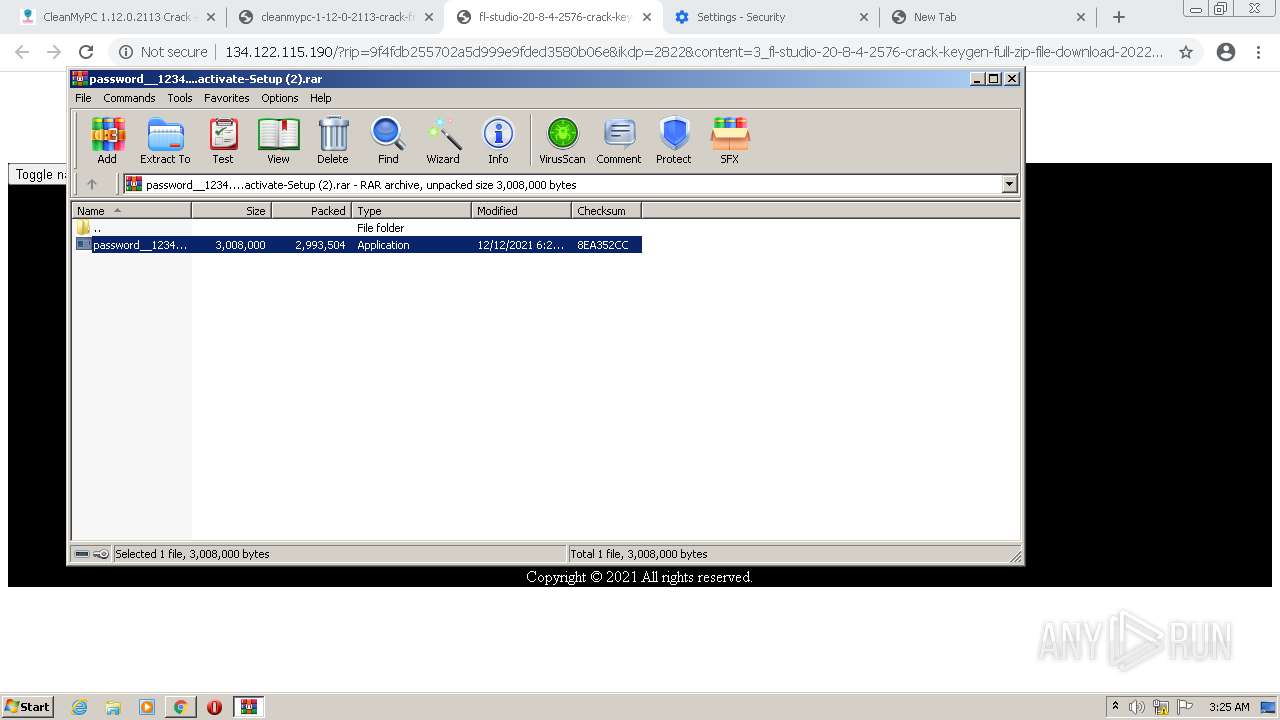
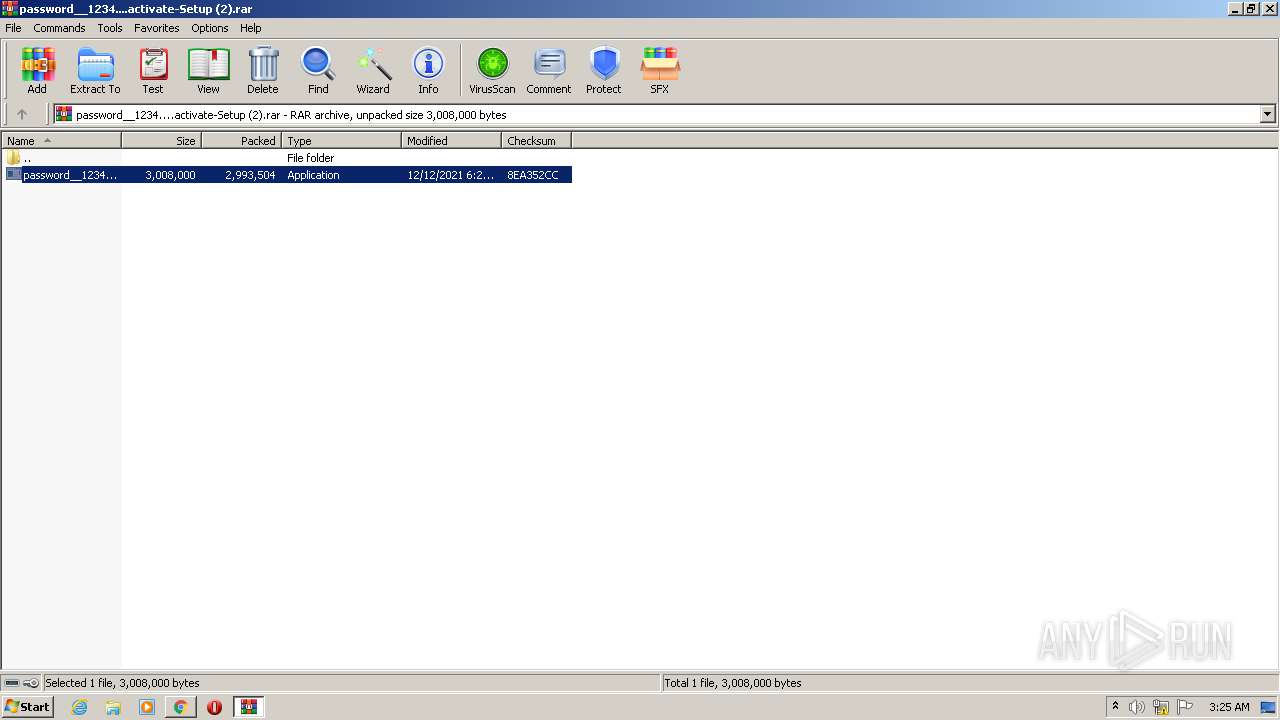
| Verdict: | Malicious activity |
| Threats: | Stealers are a group of malicious software that are intended for gaining unauthorized access to users’ information and transferring it to the attacker. The stealer malware category includes various types of programs that focus on their particular kind of data, including files, passwords, and cryptocurrency. Stealers are capable of spying on their targets by recording their keystrokes and taking screenshots. This type of malware is primarily distributed as part of phishing campaigns. |
| Analysis date: | December 13, 2021, 03:22:04 |
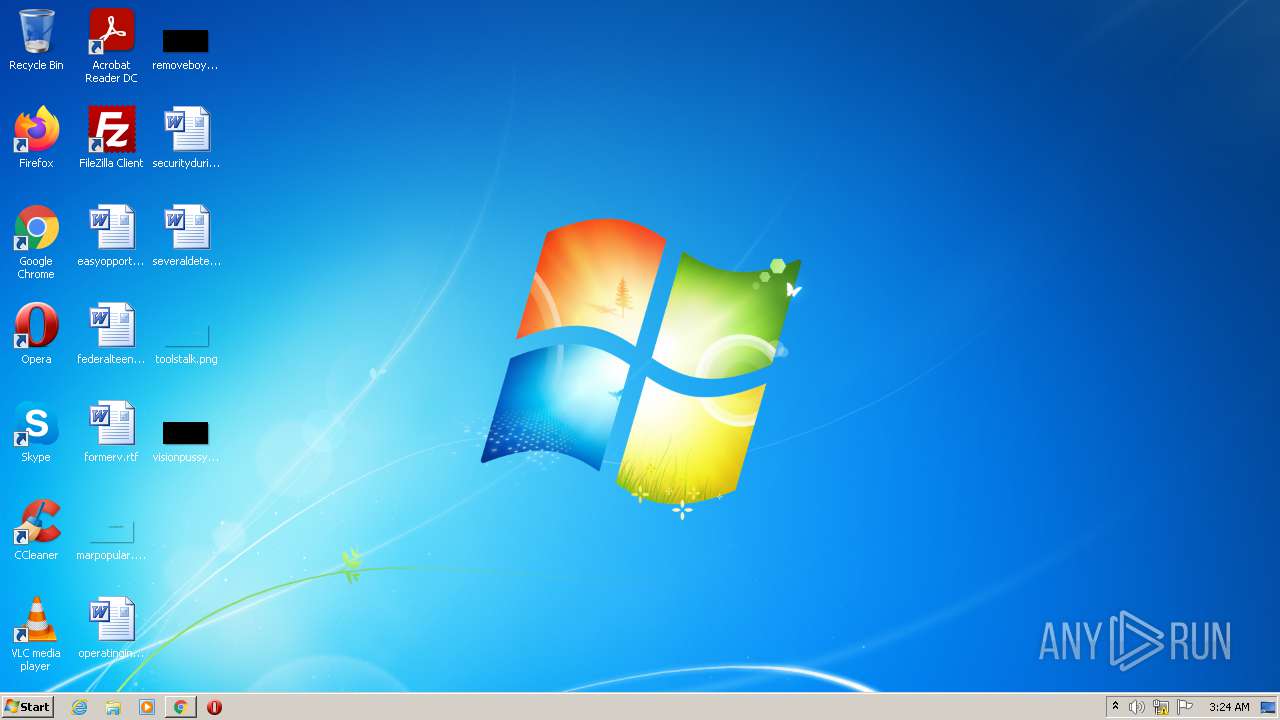
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 81494604BA33C210DA713885AC72775D |
| SHA1: | 597CCC701EFAE8BD4C4E1AF148EC3B30DF276275 |
| SHA256: | B57C94FEB764FC010FA19A0A7F6F6A6EE8B32070937F63D1A68ED002016F23C9 |
| SSDEEP: | 3:N8ZZkyTK1RQeAEOALIDWiQ84mn:25TK1hTID7Q8L |
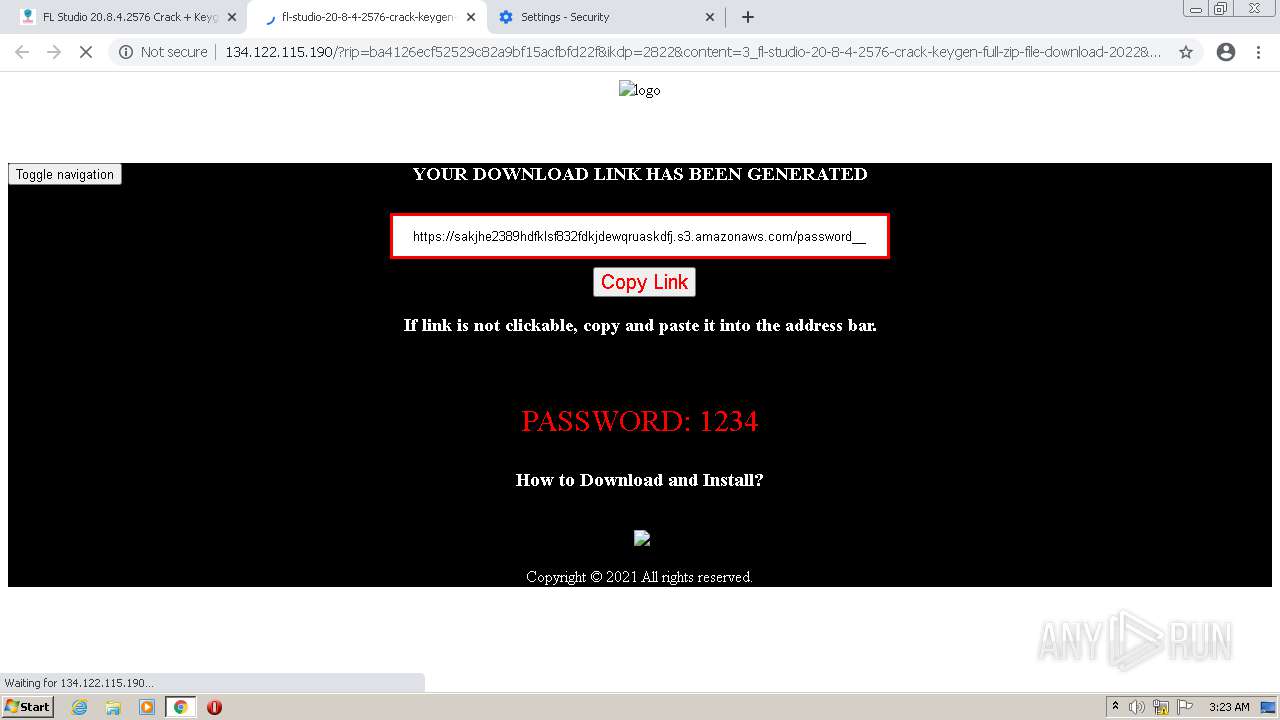
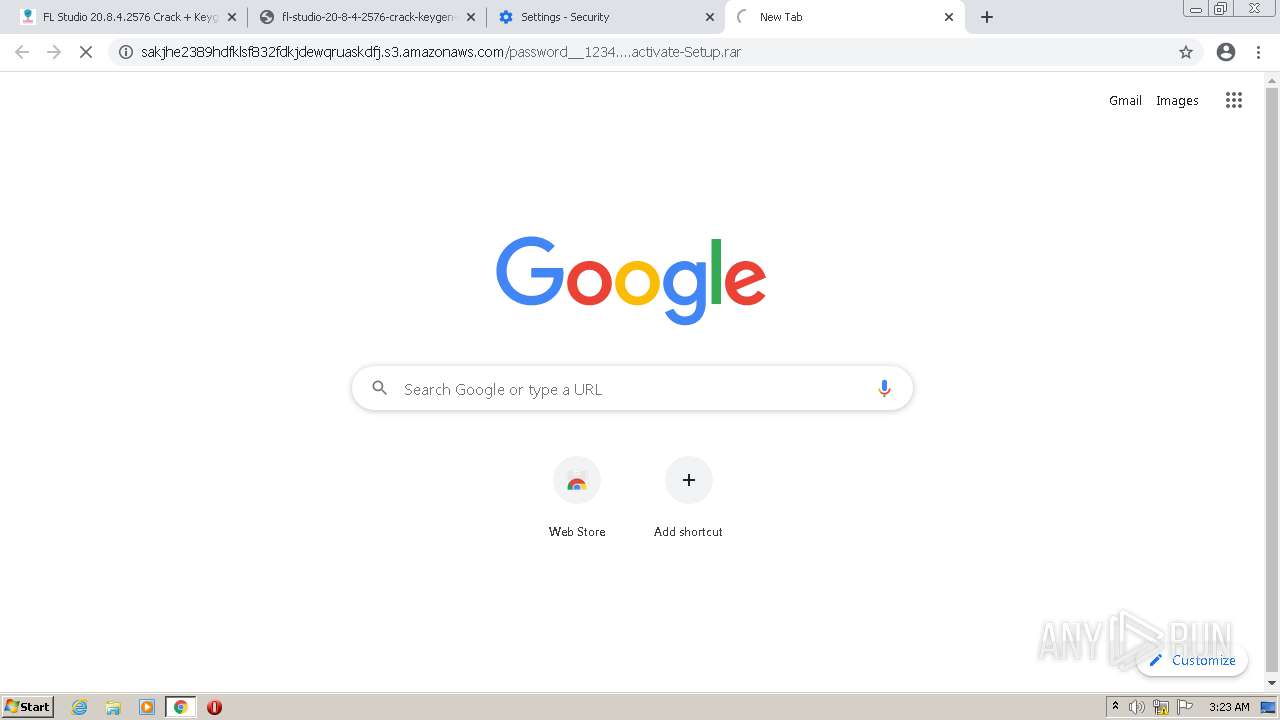
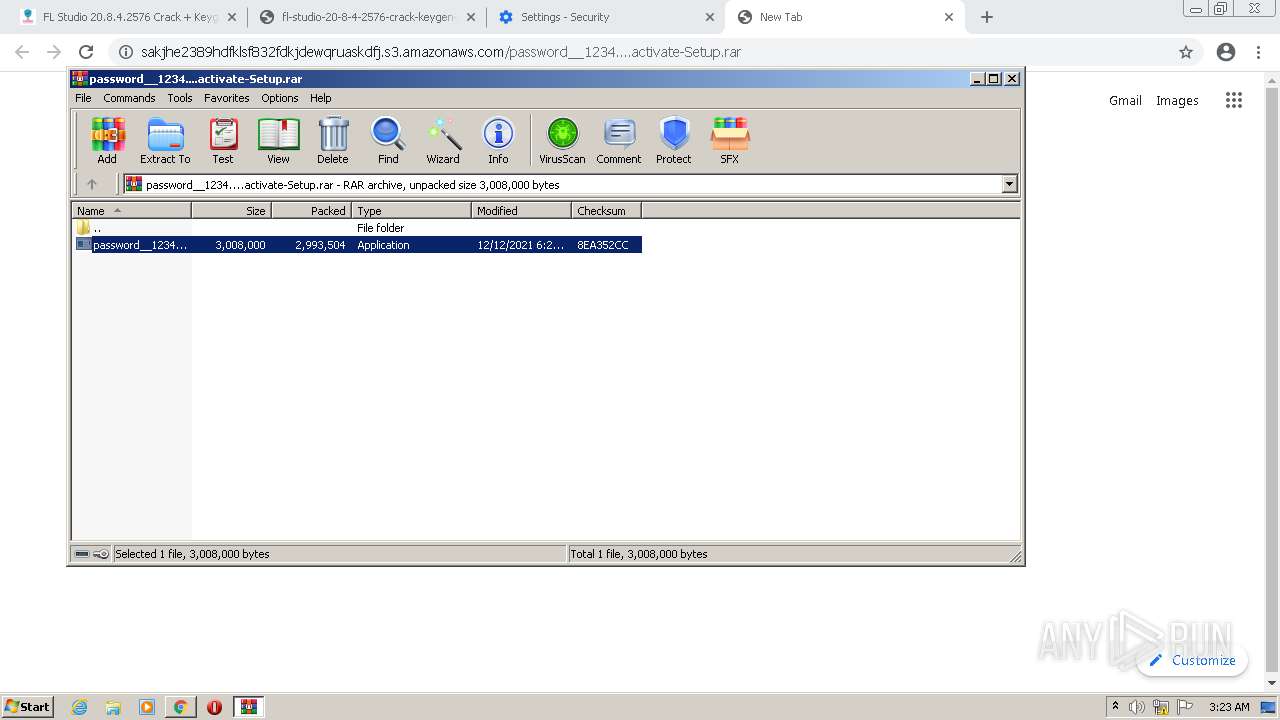
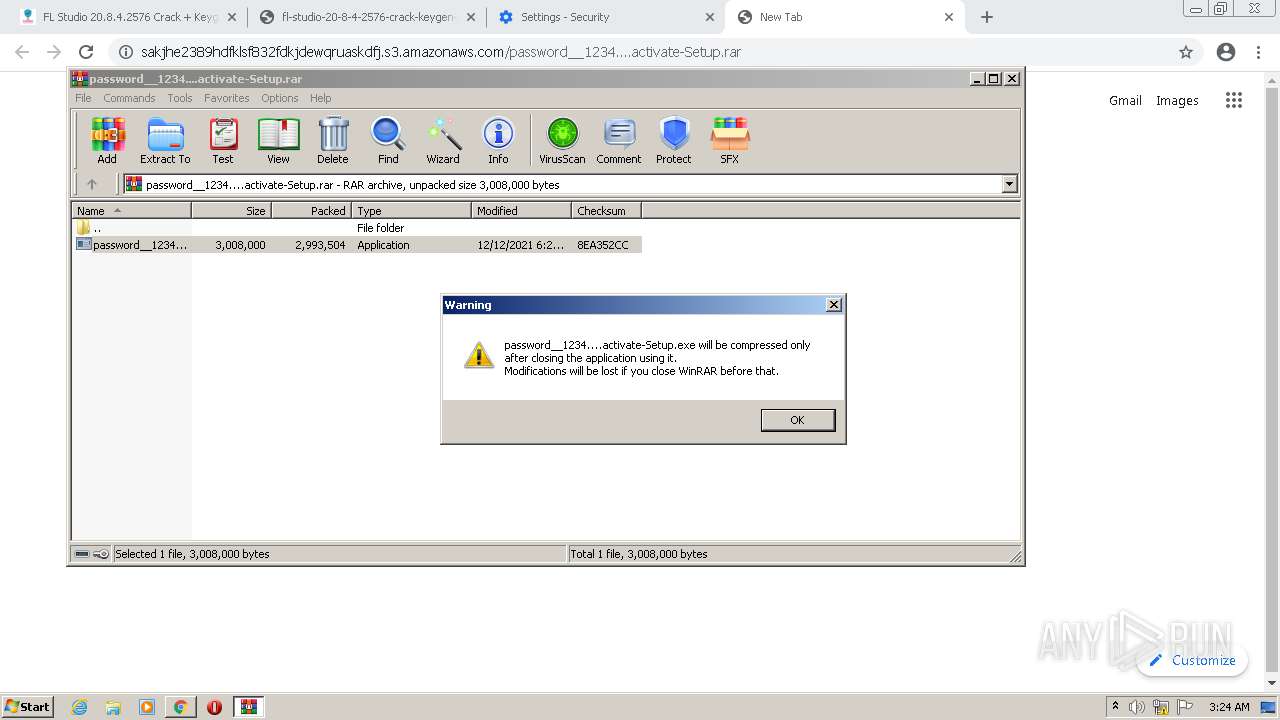
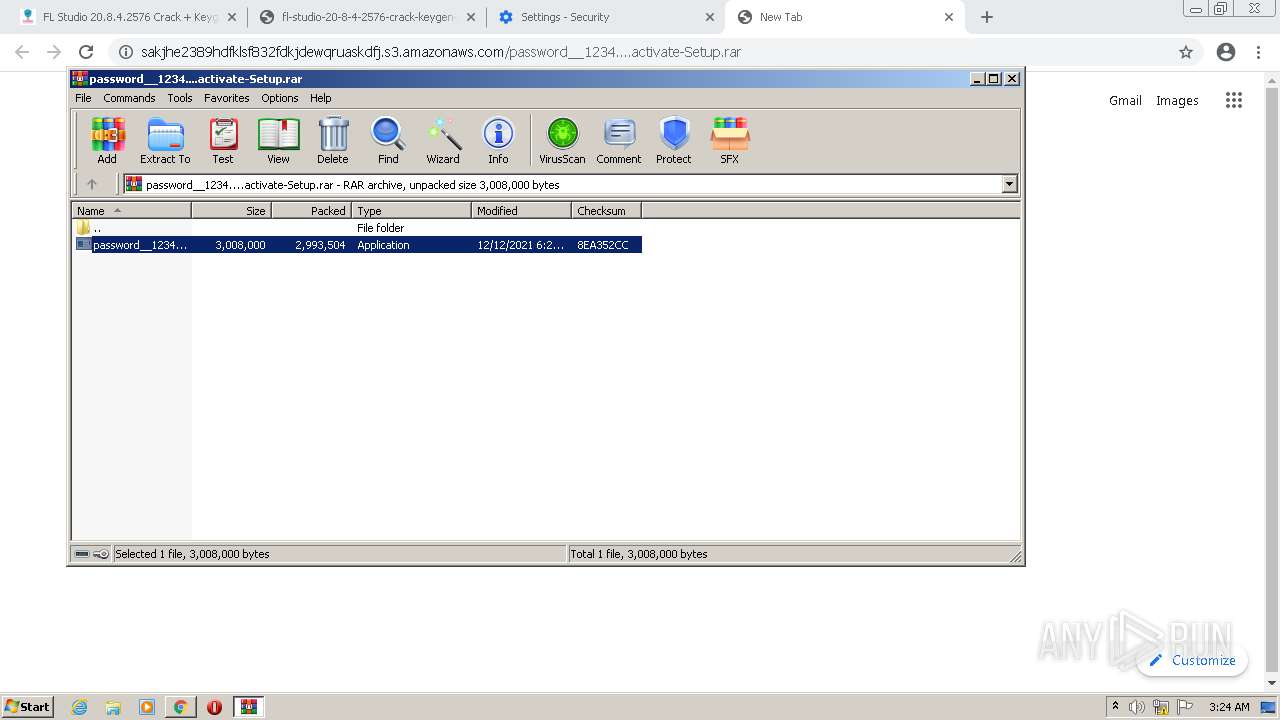
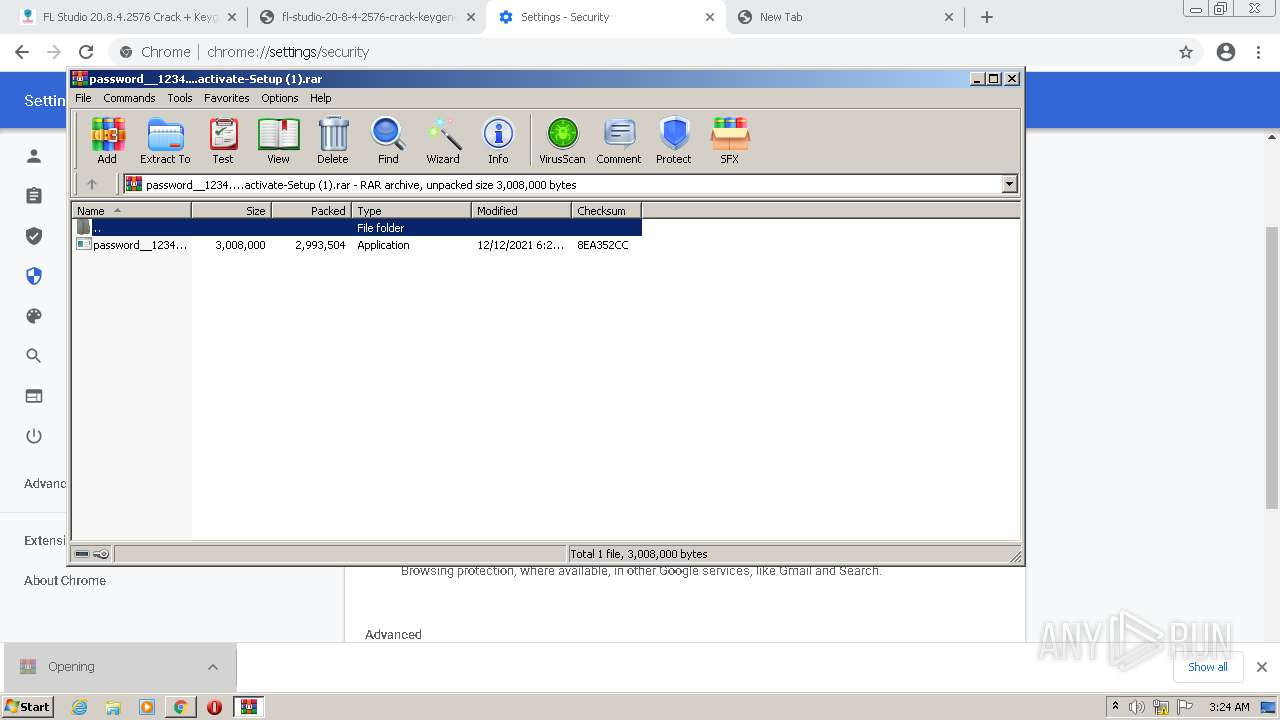
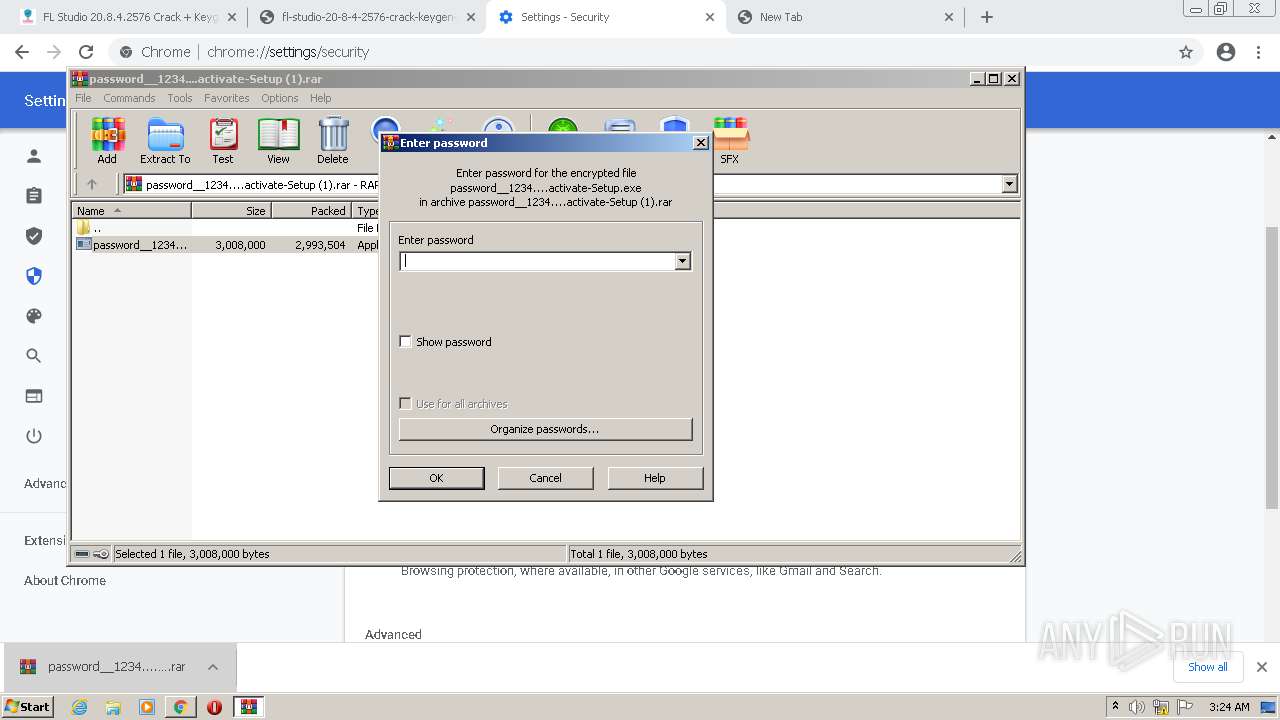
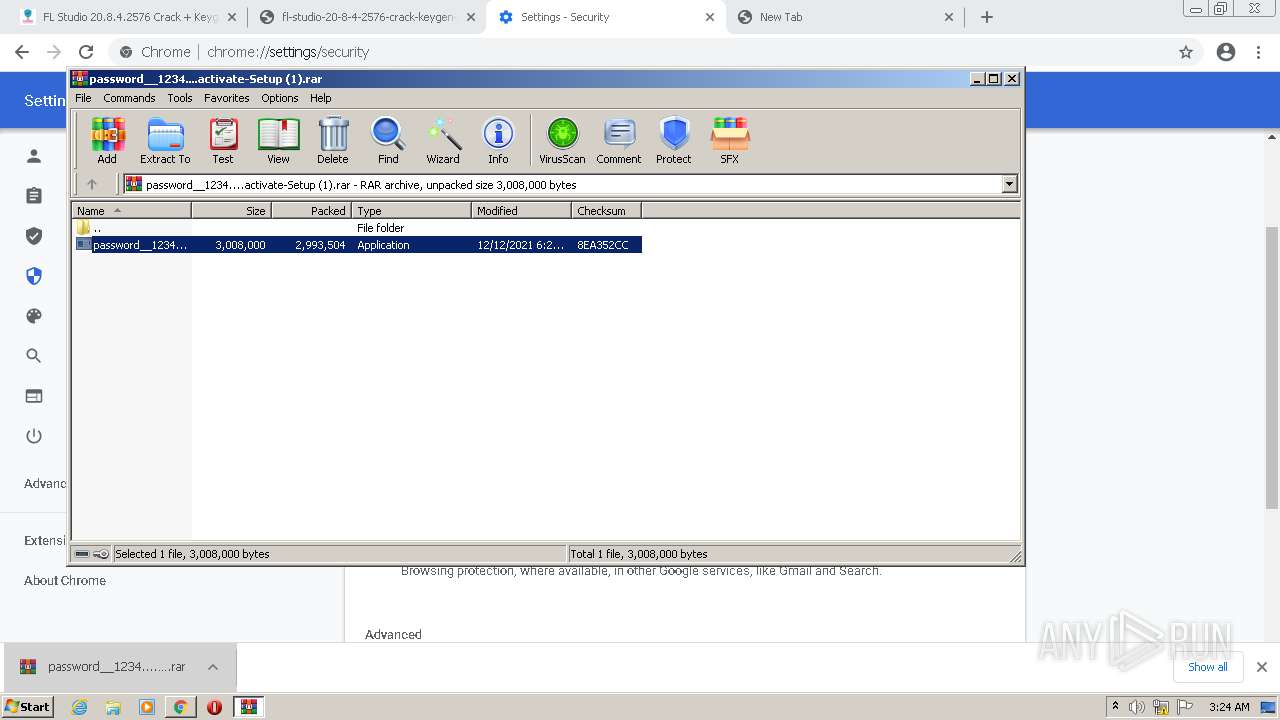
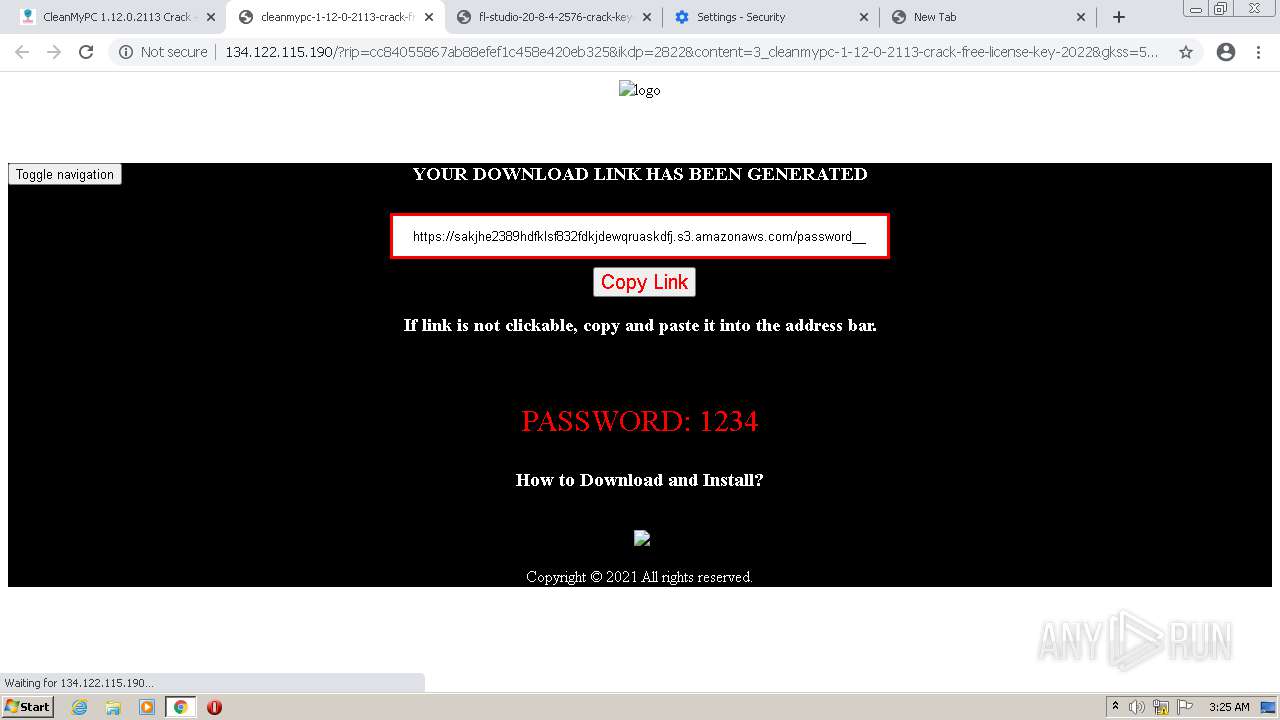
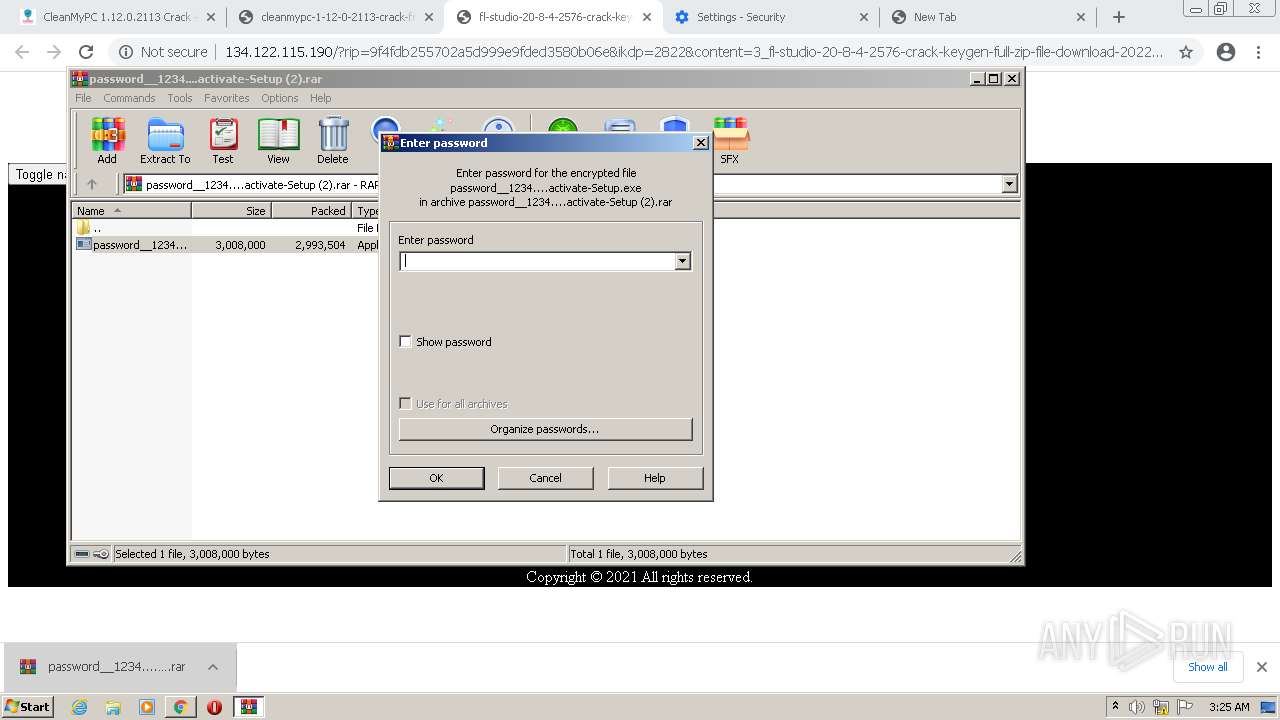
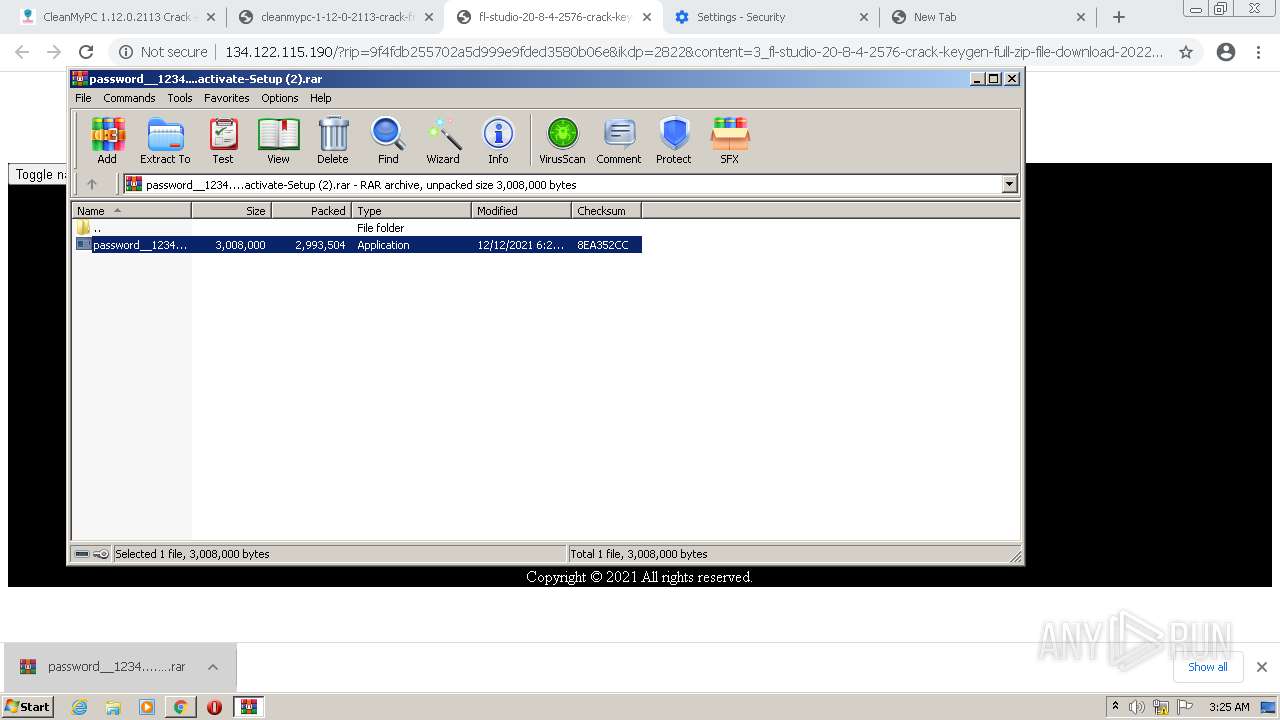
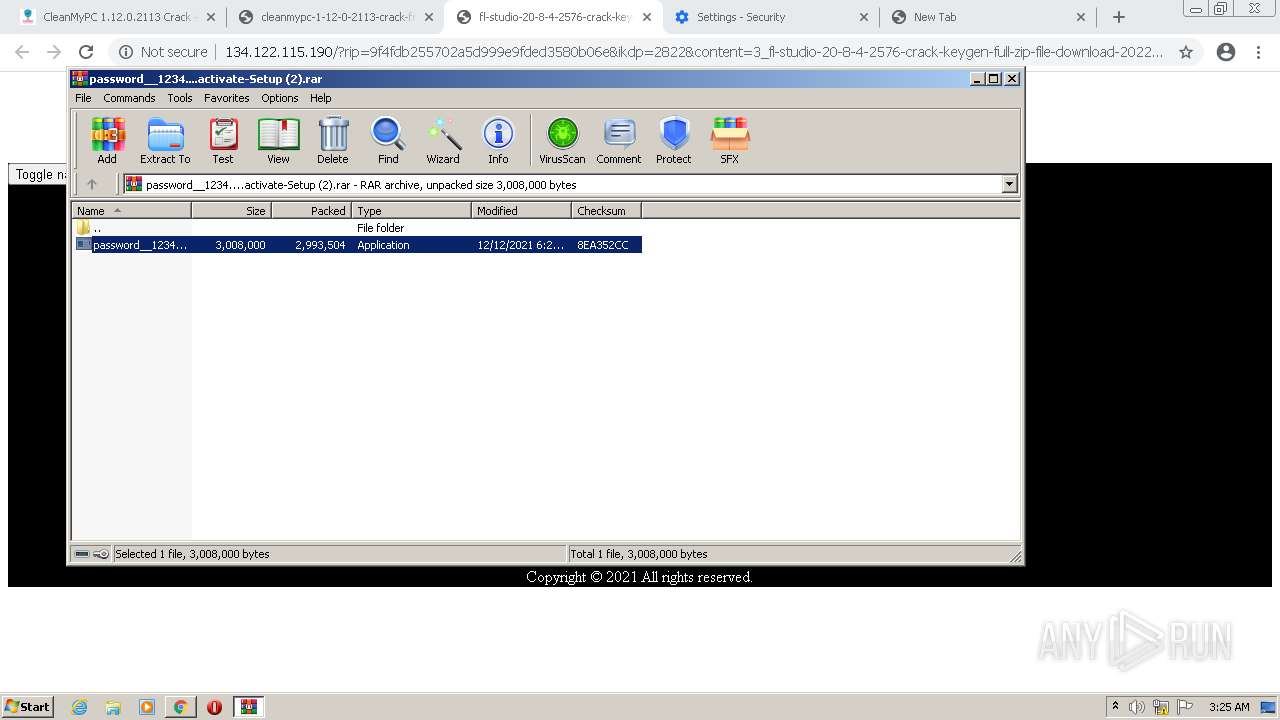
MALICIOUS
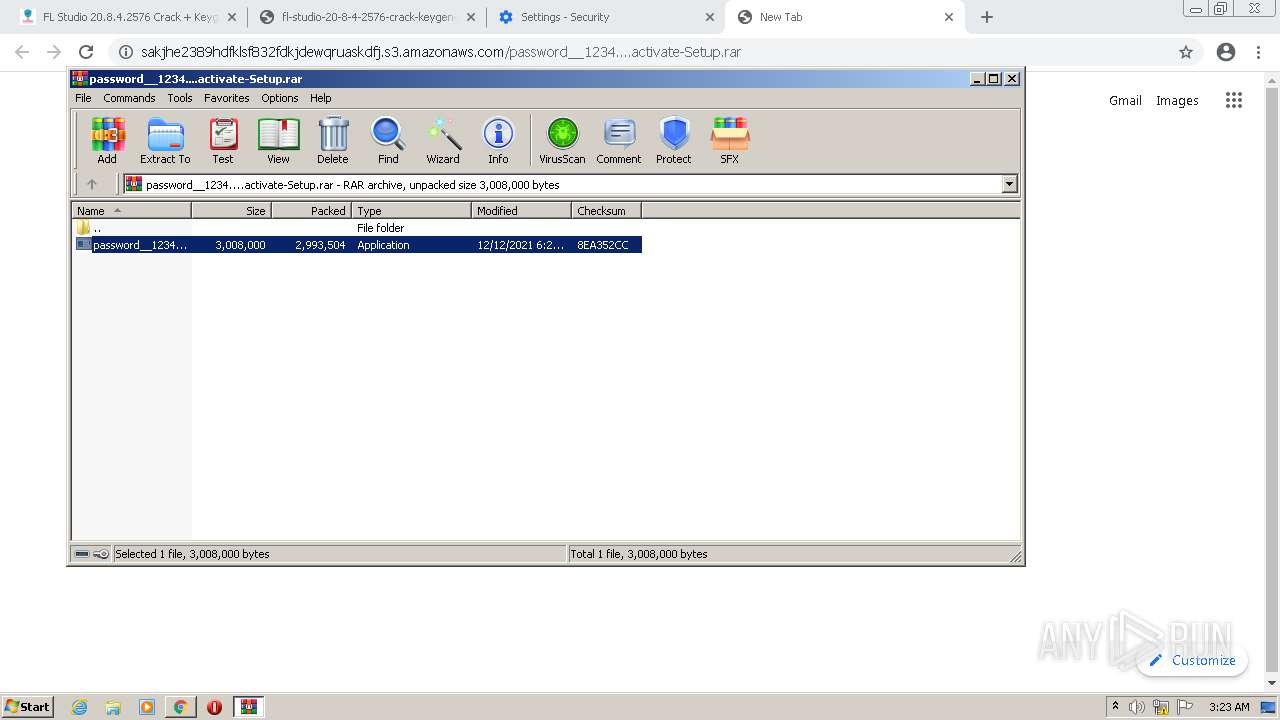
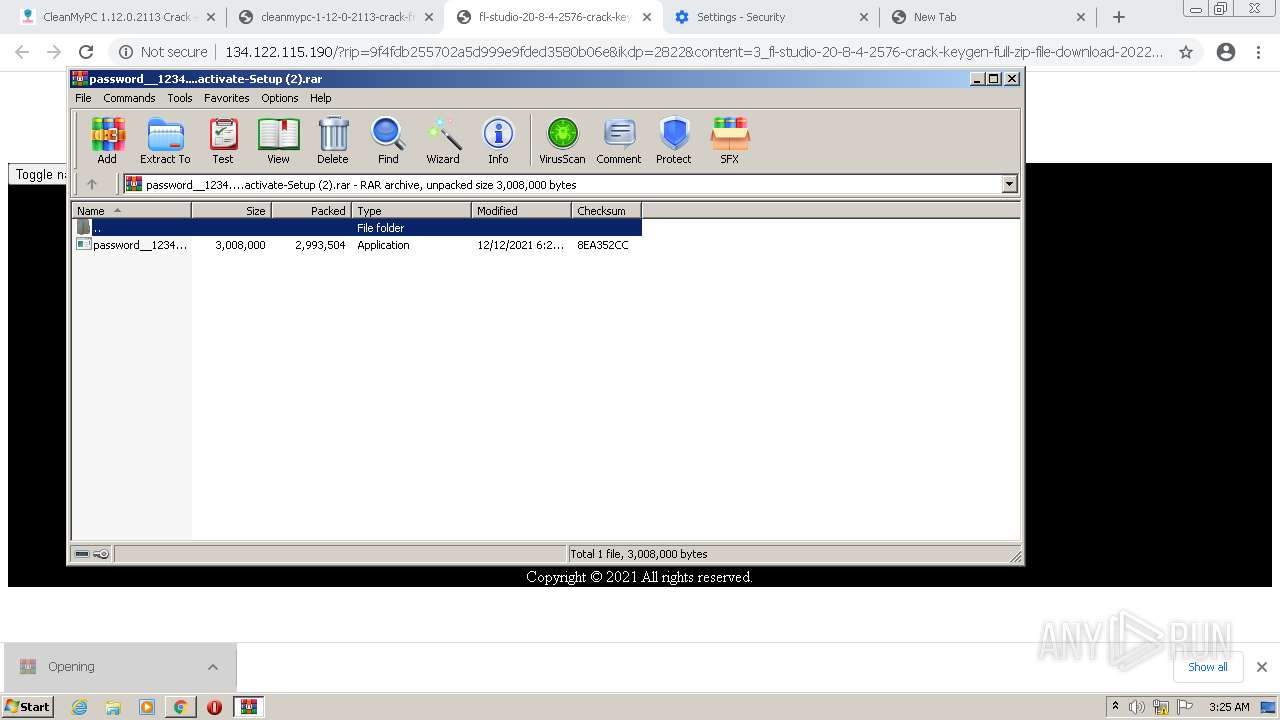
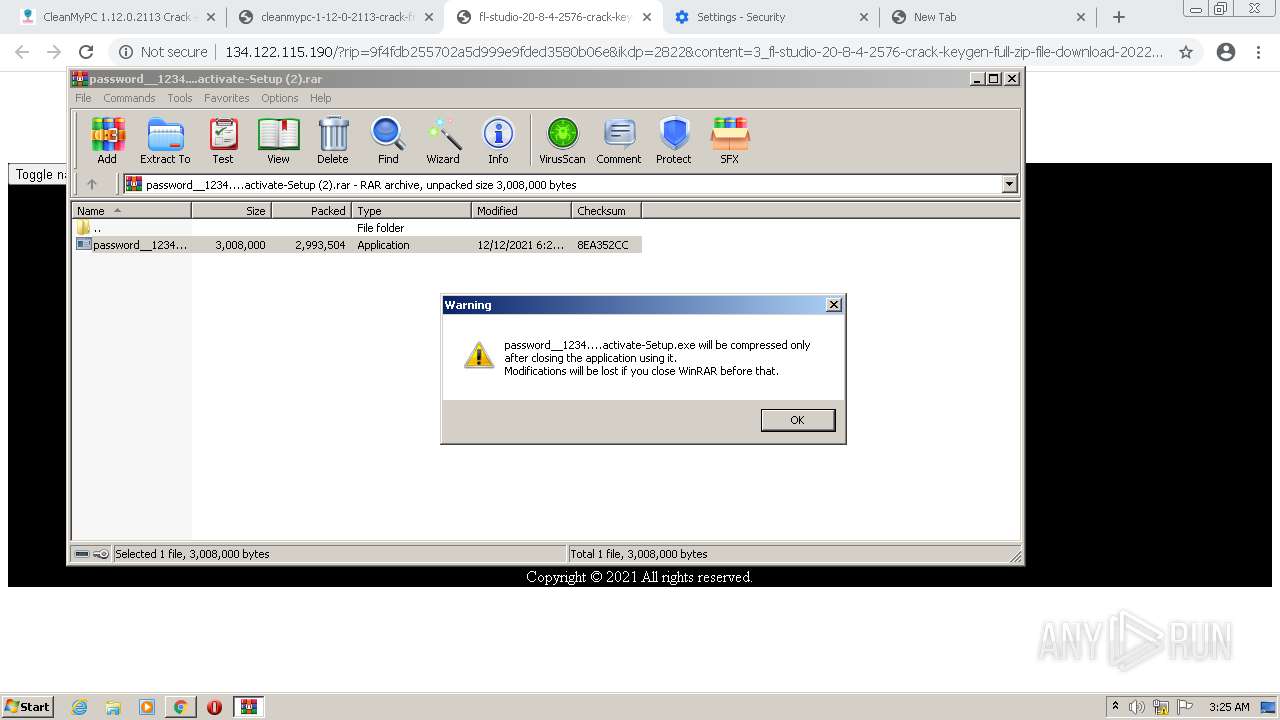
Application was dropped or rewritten from another process
- password__1234....activate-Setup.exe (PID: 3700)
- password__1234....activate-Setup.exe (PID: 1596)
- password__1234....activate-Setup.exe (PID: 3680)
- password__1234....activate-Setup.exe (PID: 3228)
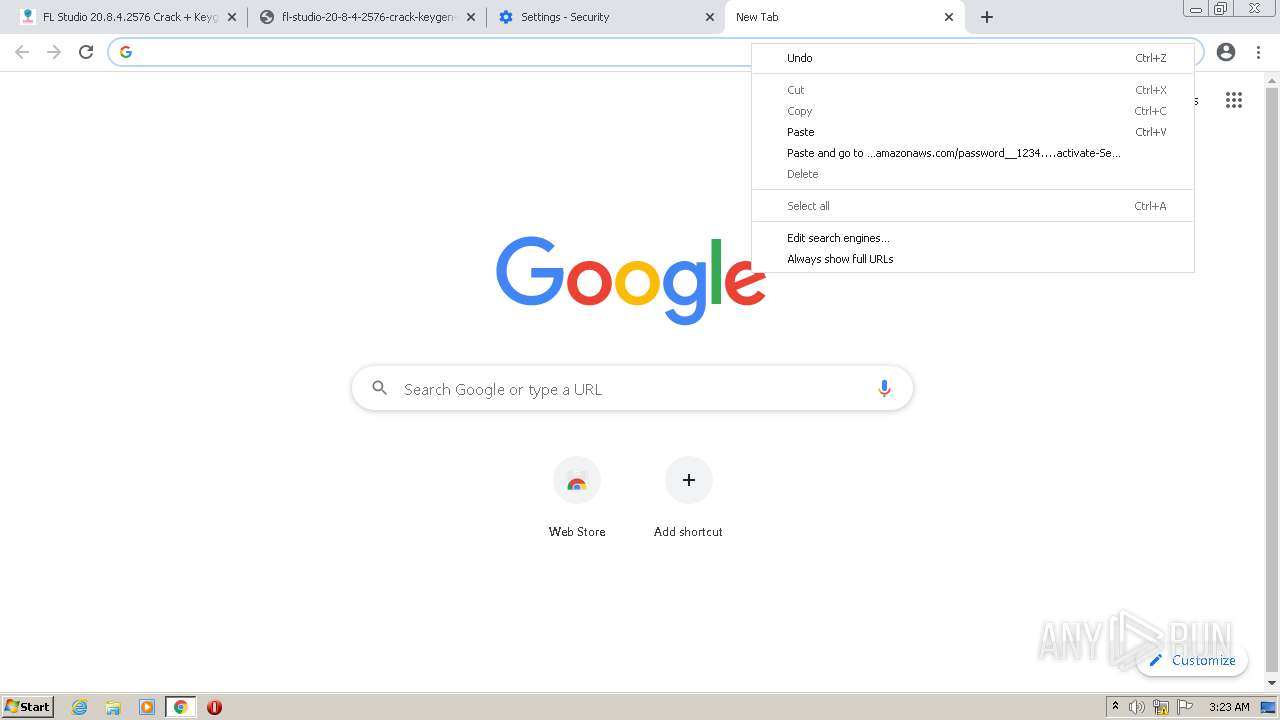
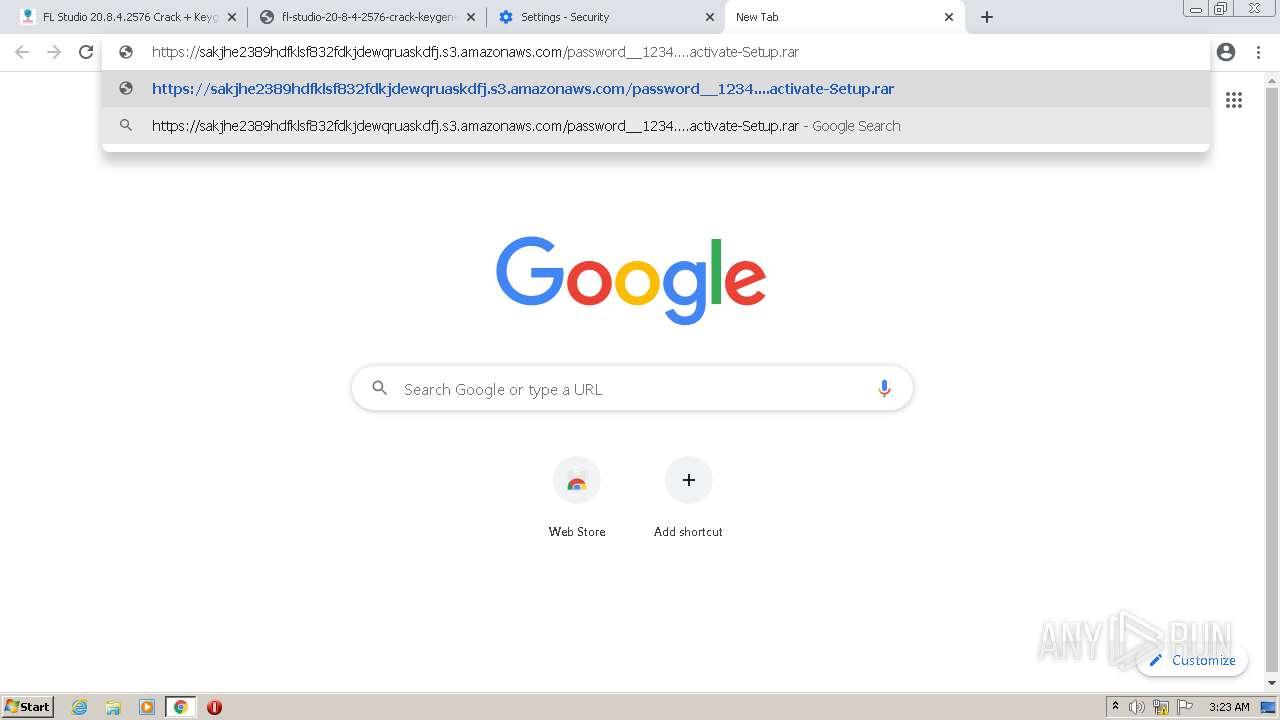
Actions looks like stealing of personal data
- password__1234....activate-Setup.exe (PID: 3700)
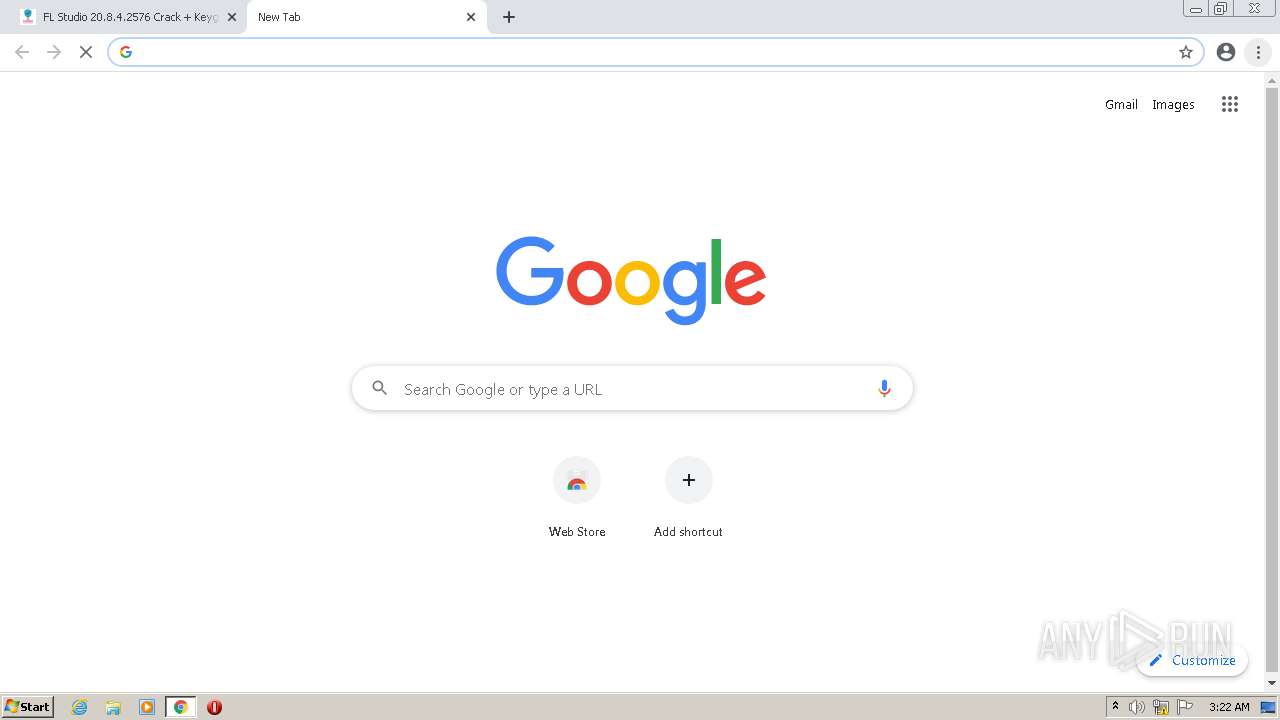
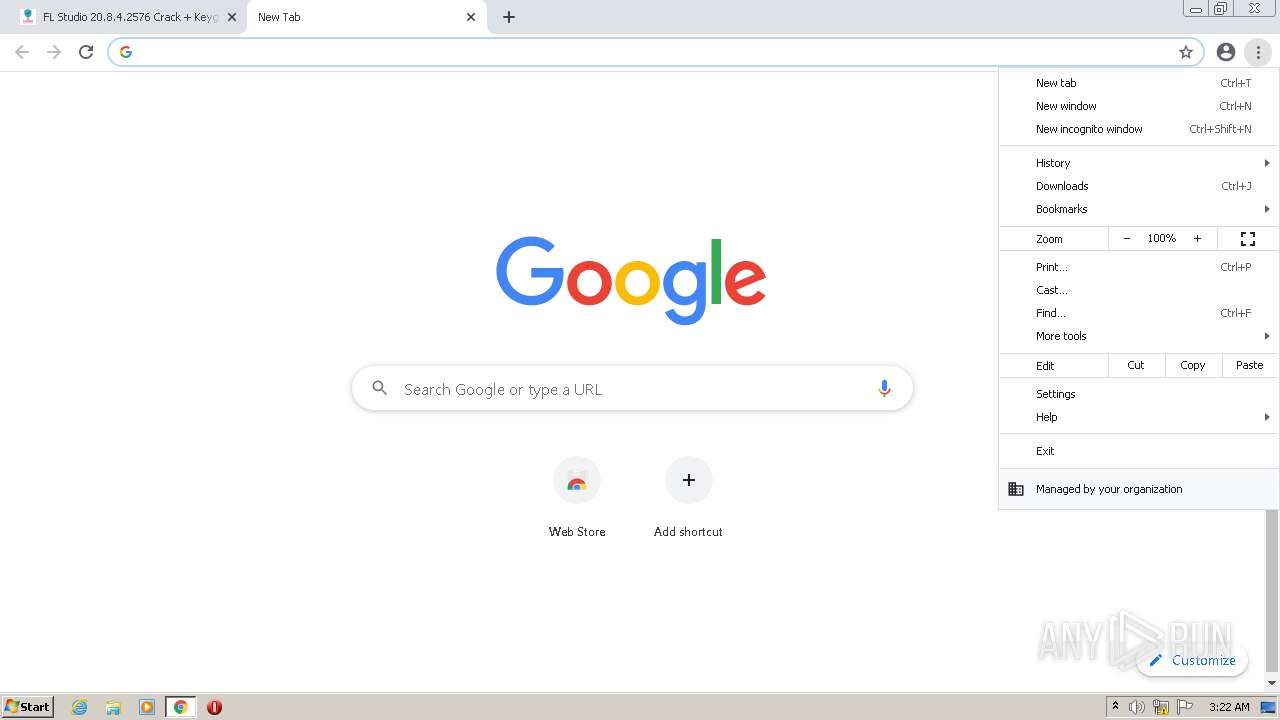
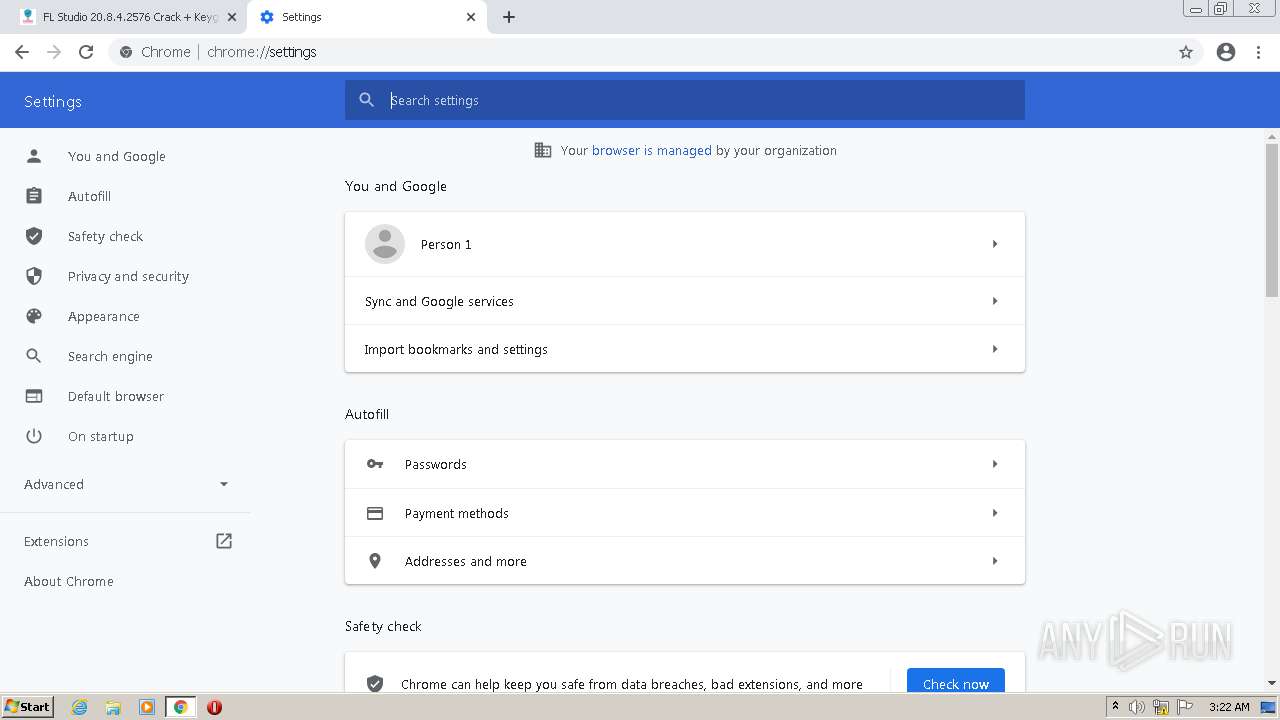
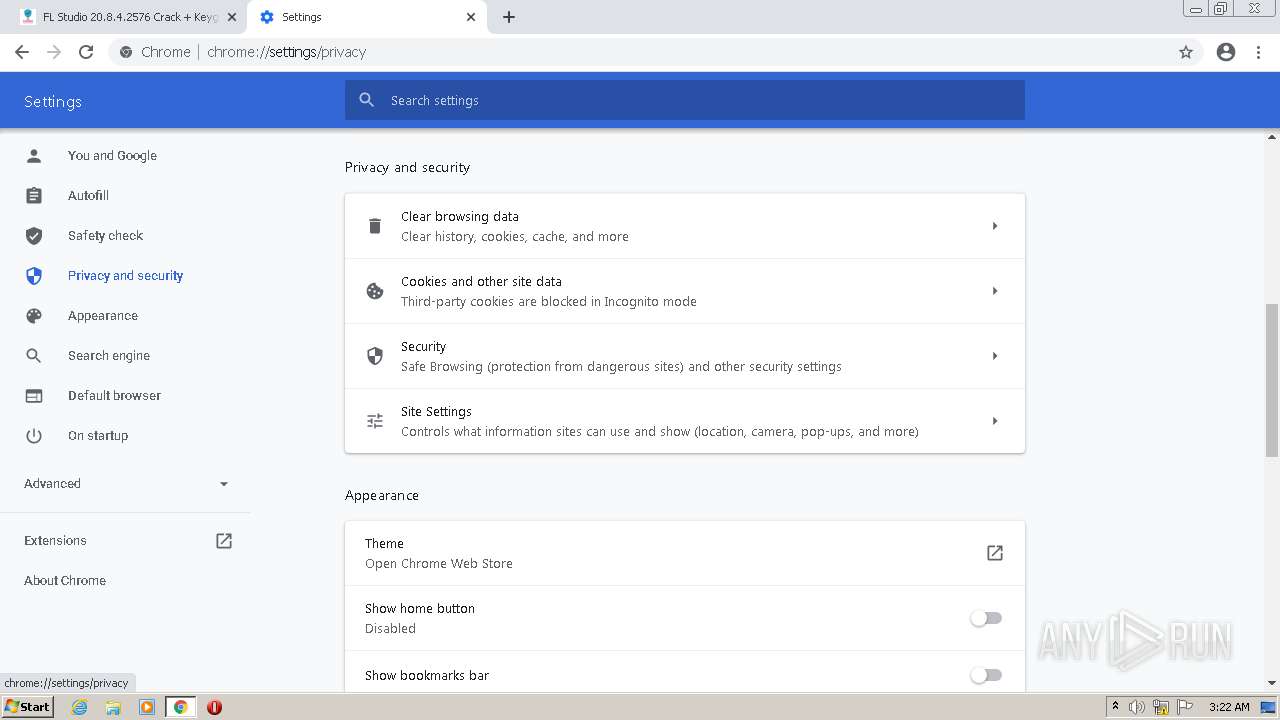
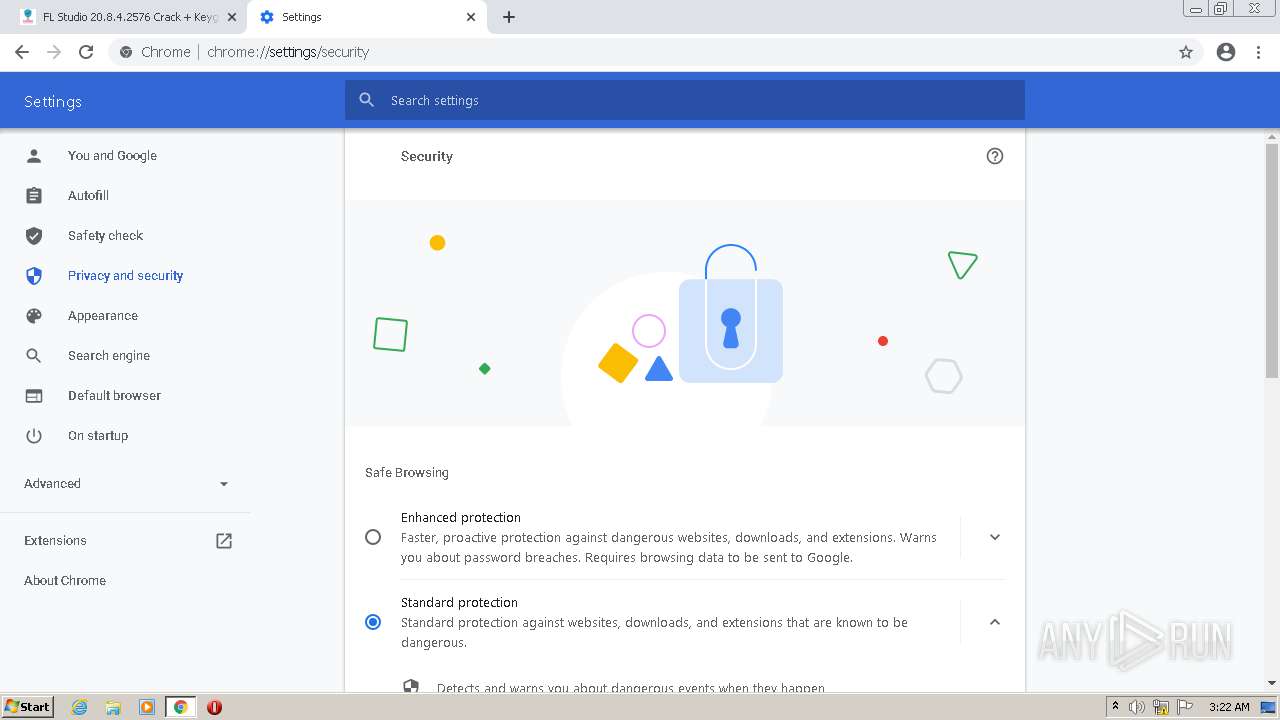
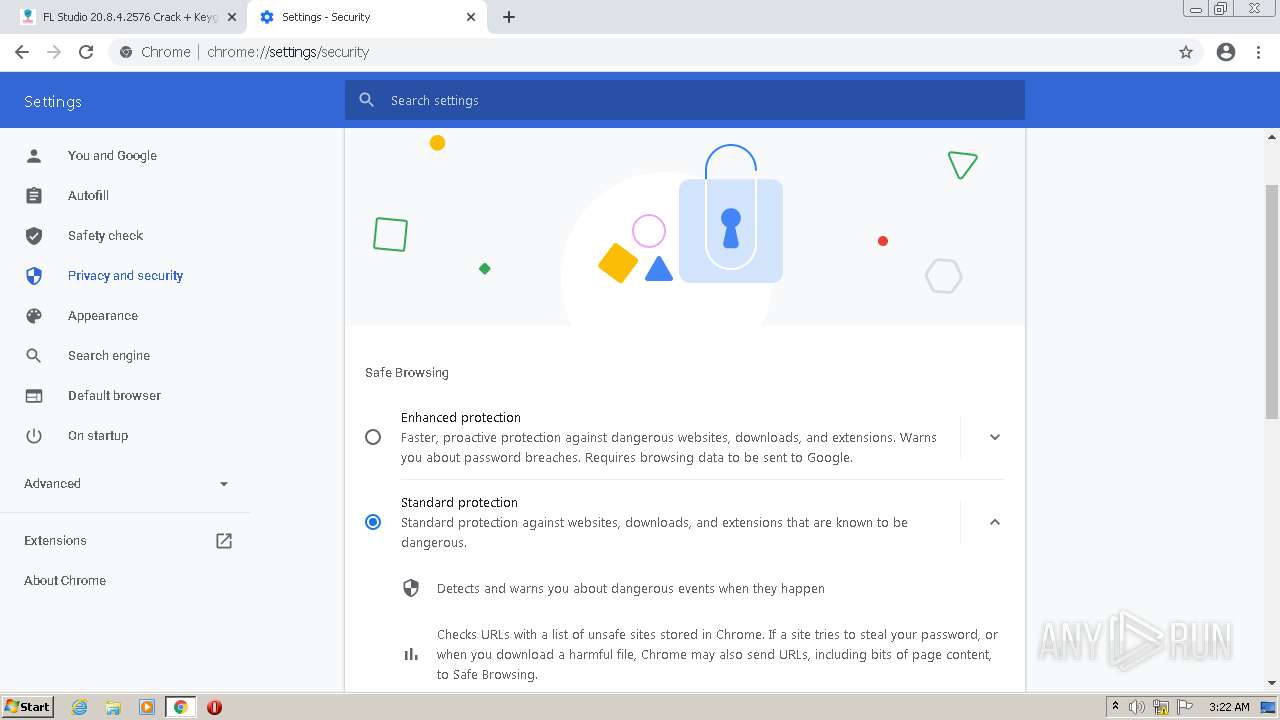
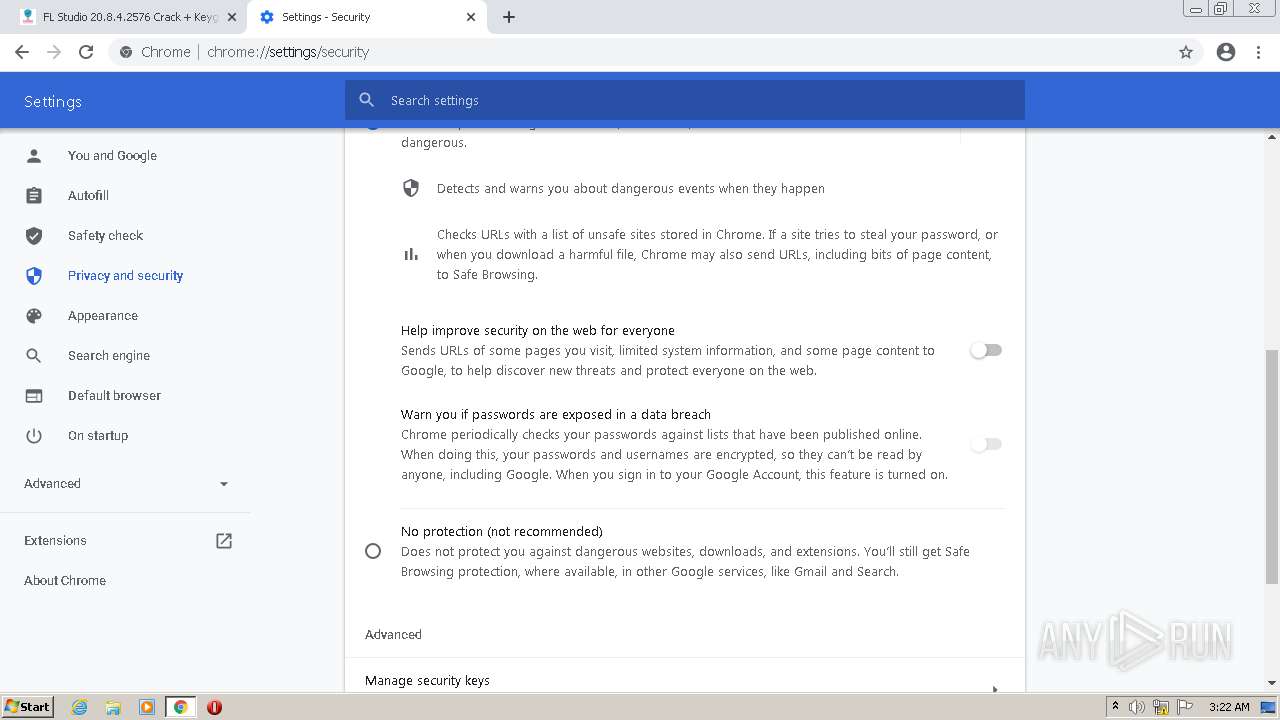
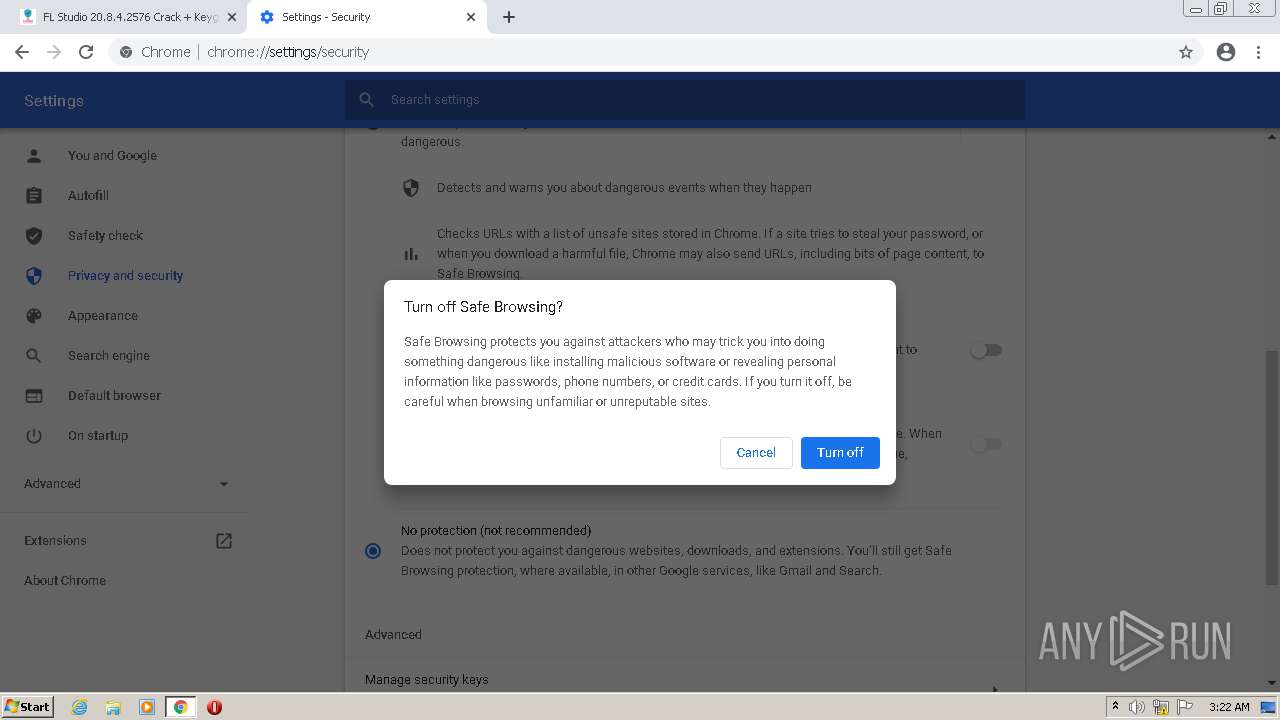
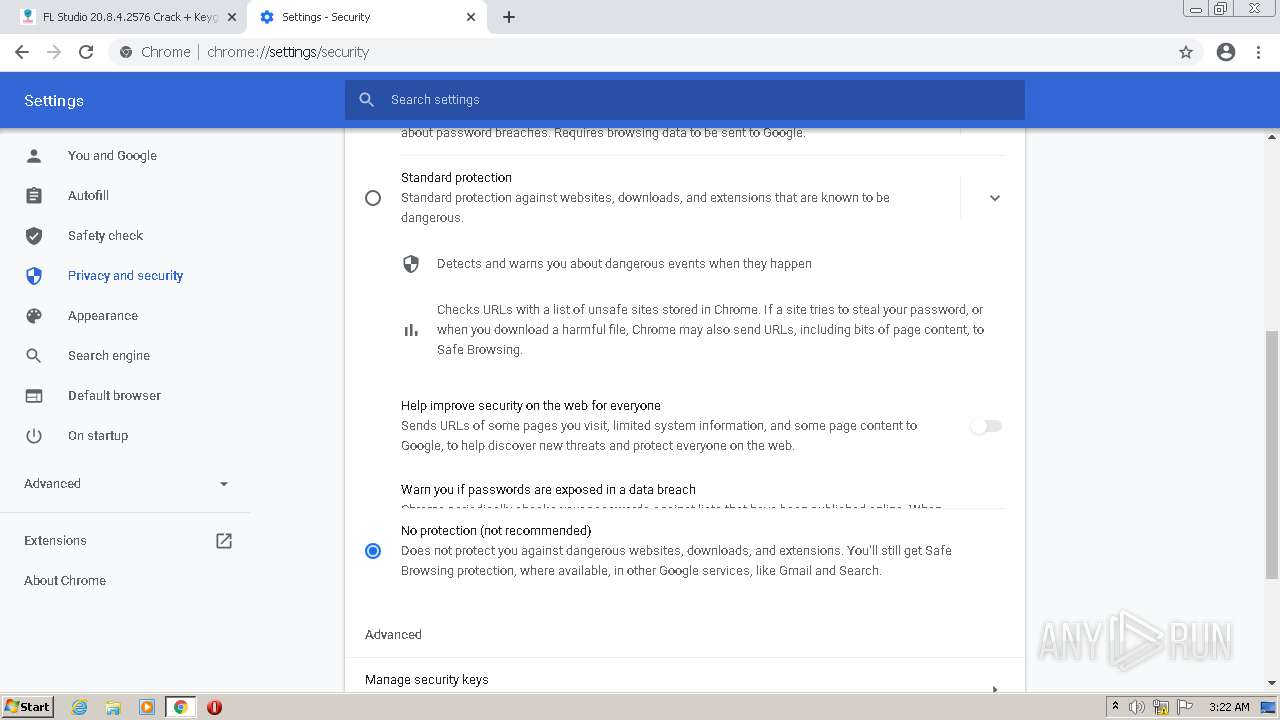
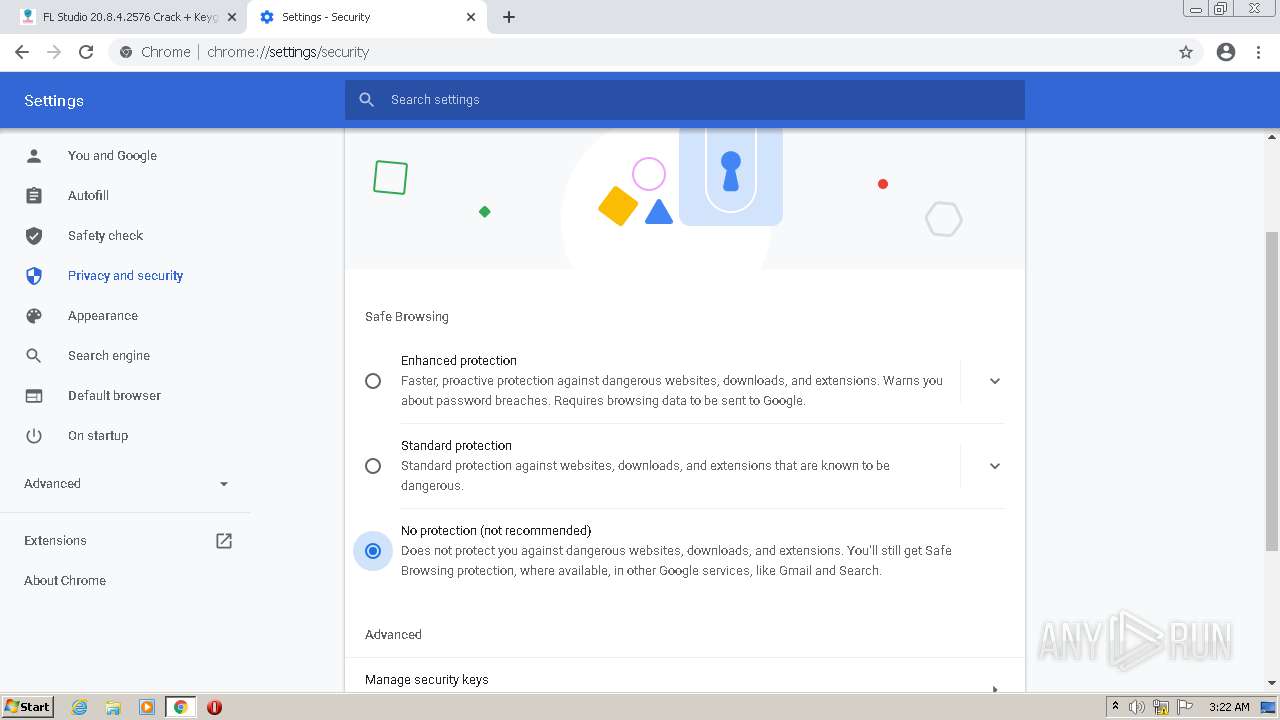
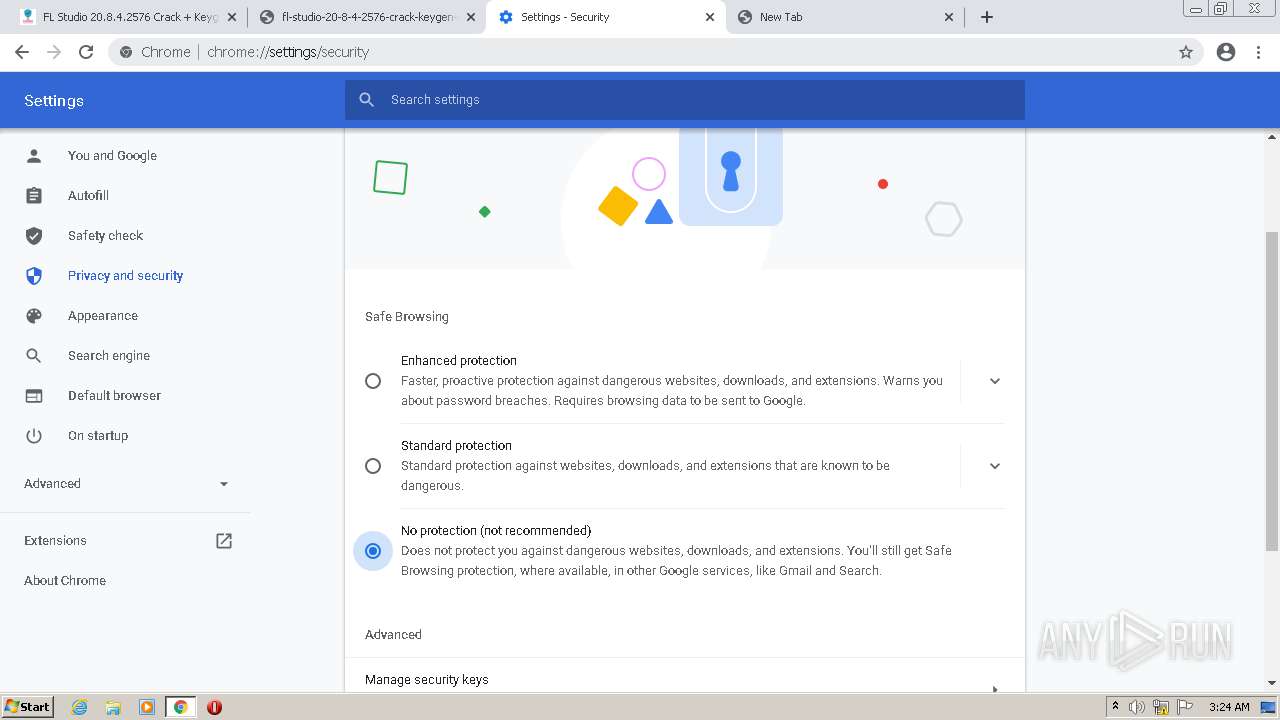
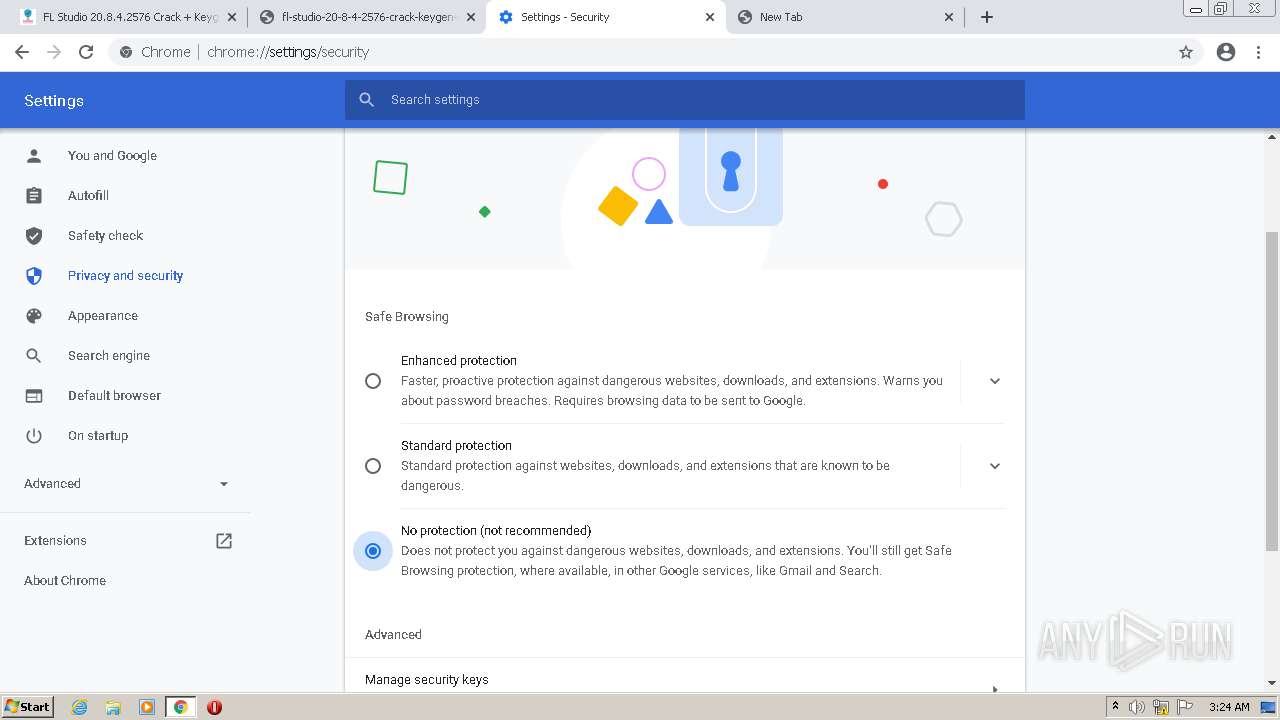
Steals credentials from Web Browsers
- password__1234....activate-Setup.exe (PID: 3700)
Stealing of credential data
- password__1234....activate-Setup.exe (PID: 3700)
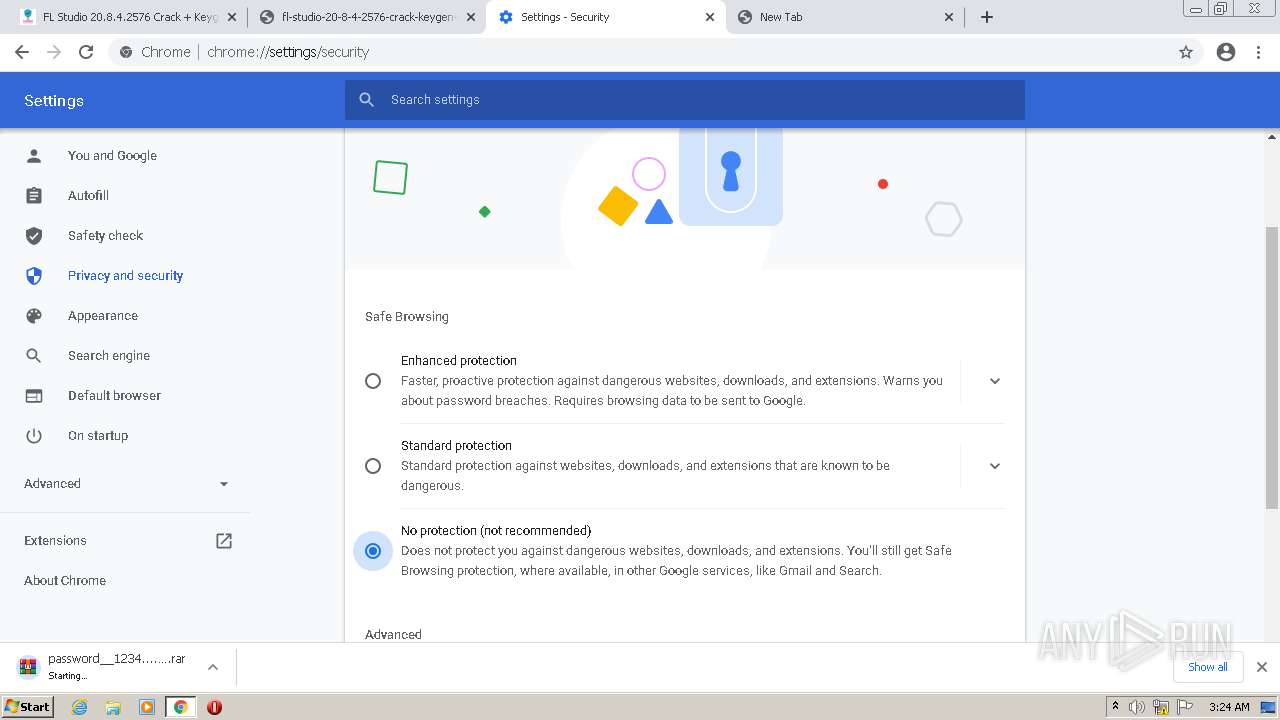
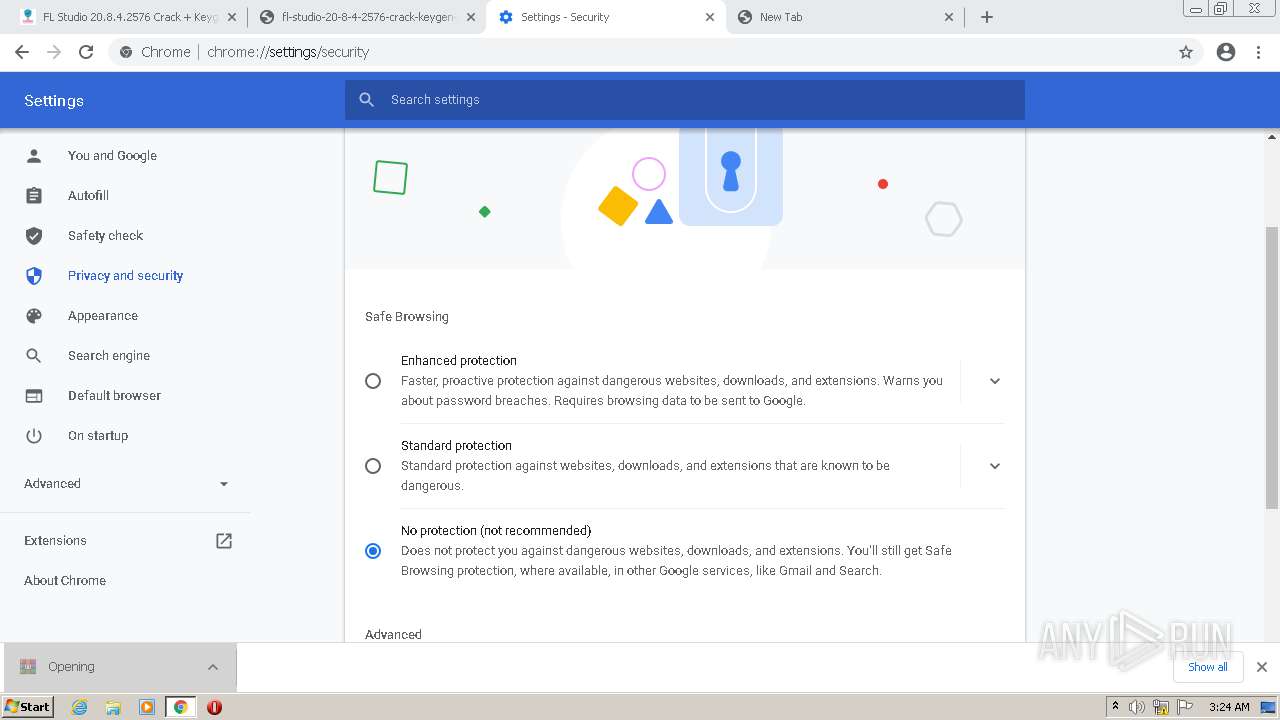
SUSPICIOUS
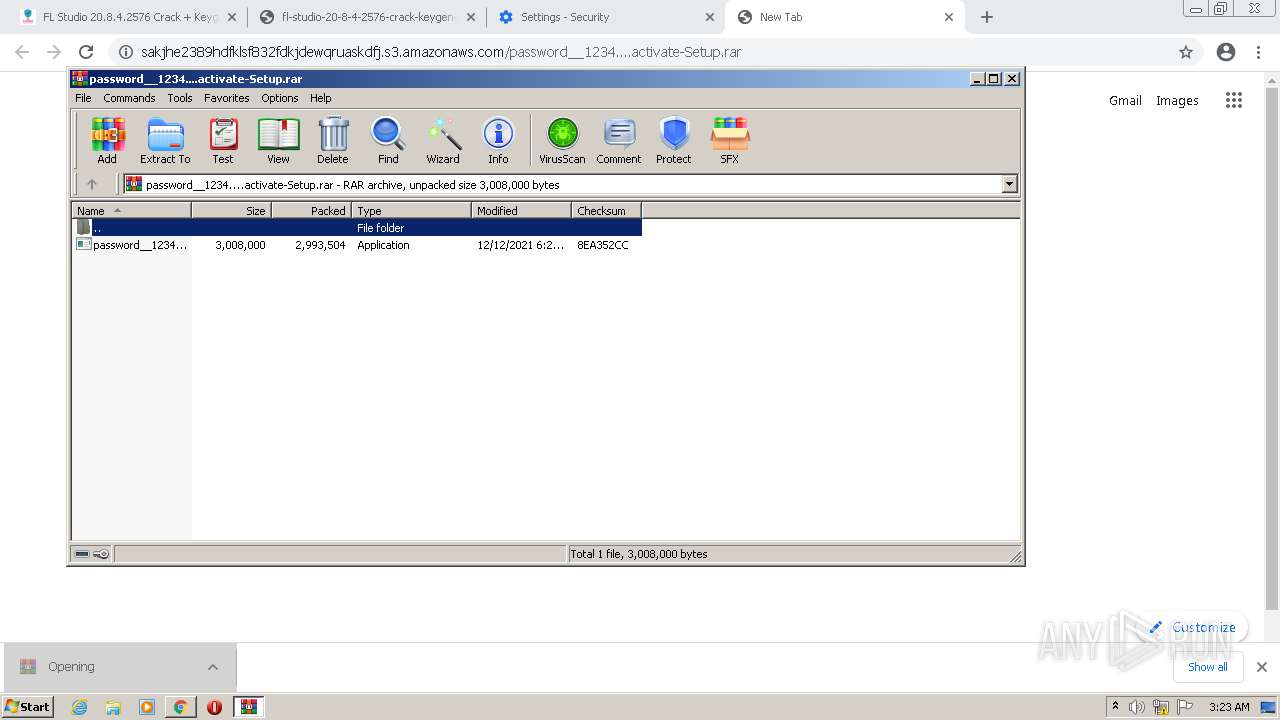
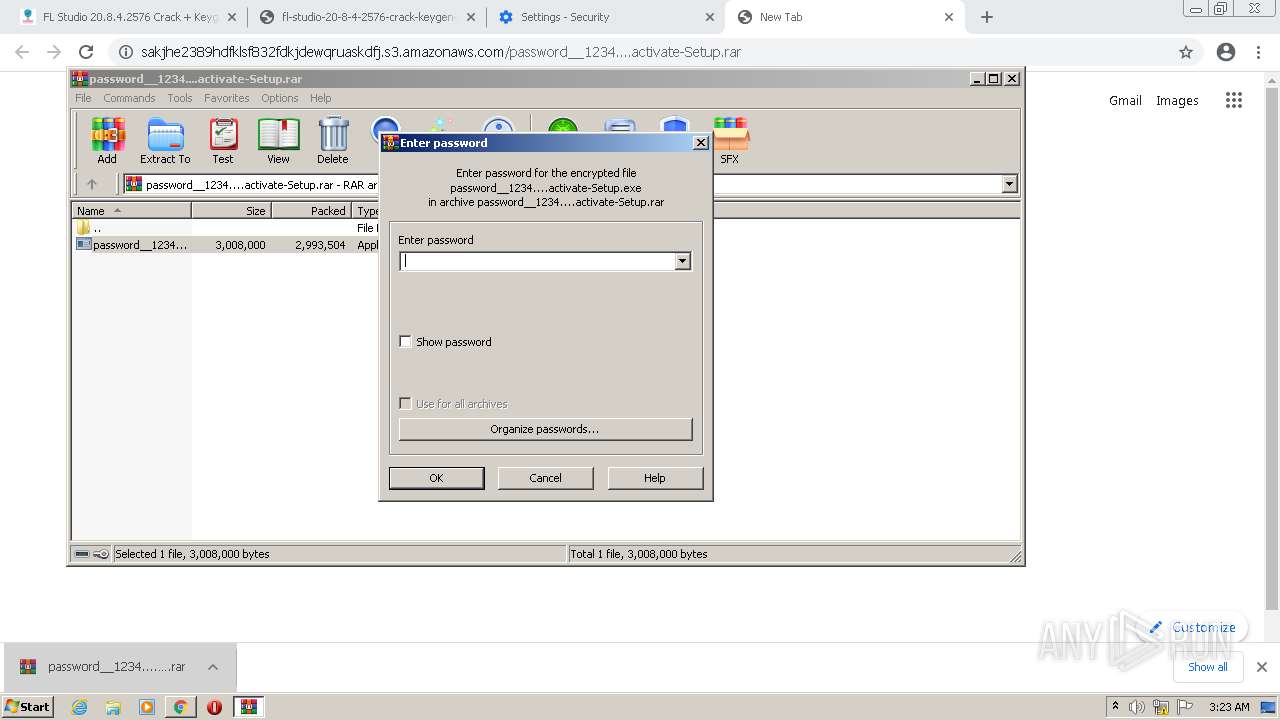
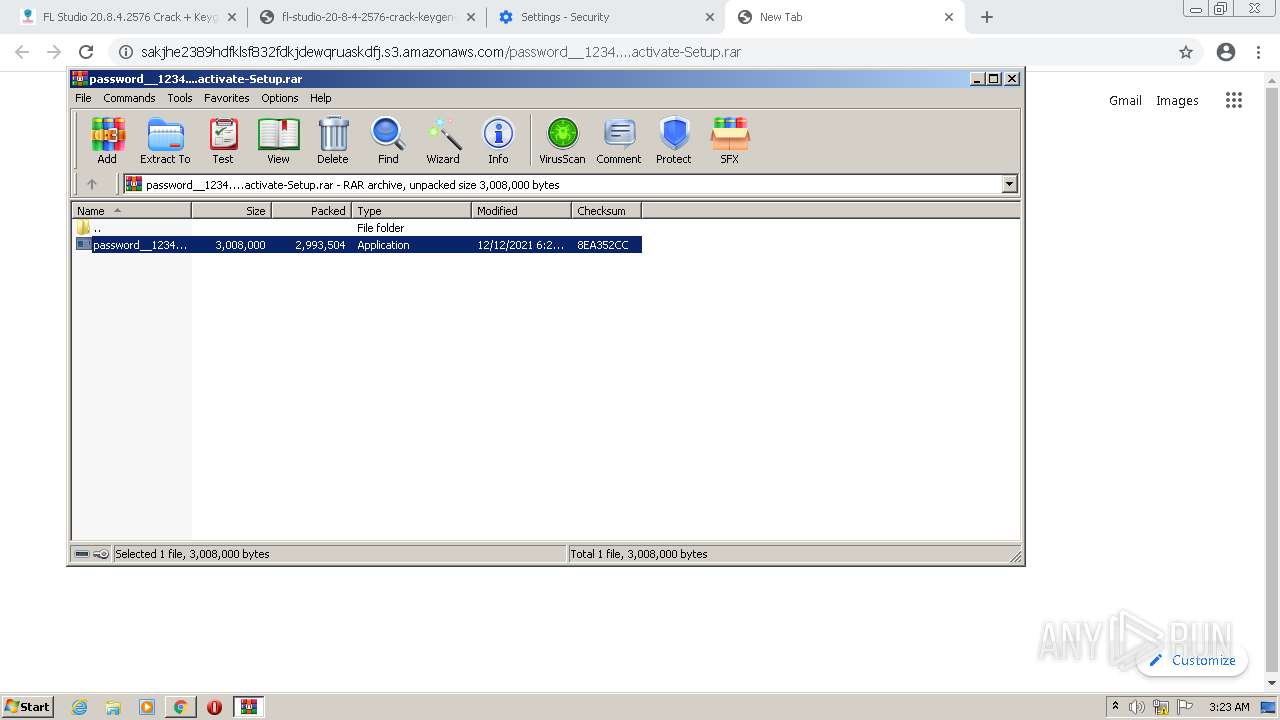
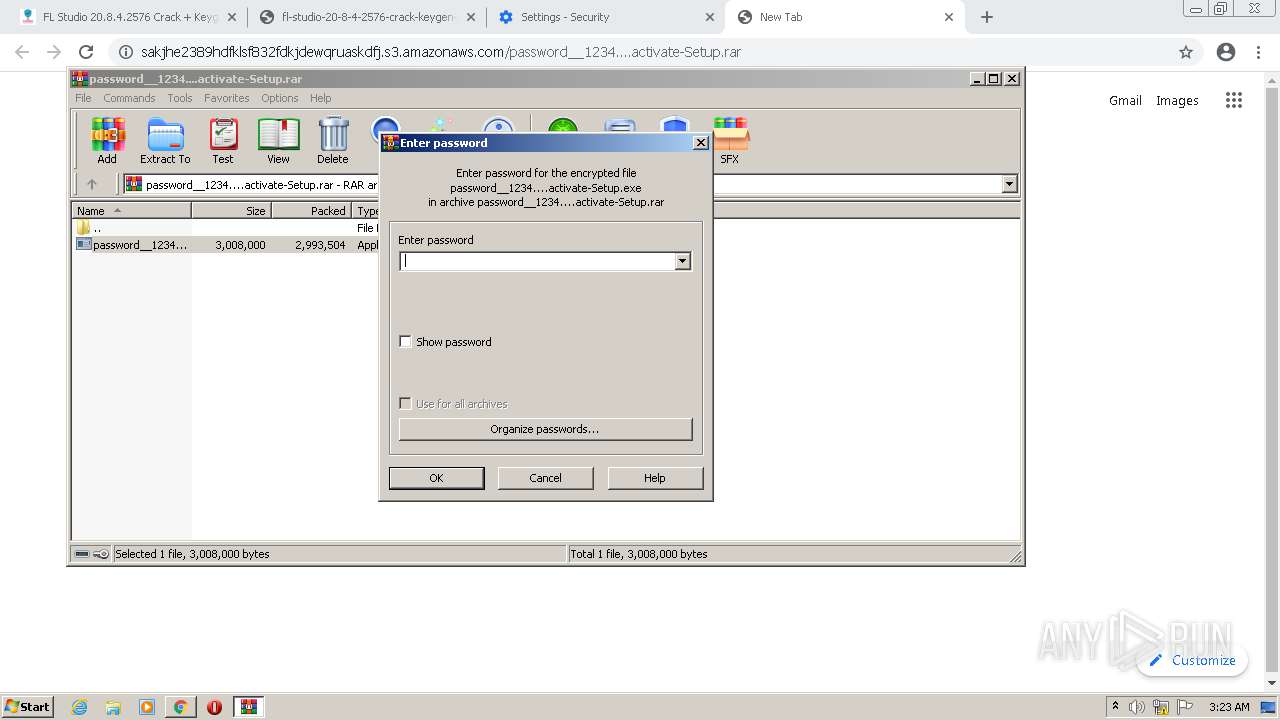
Drops a file with a compile date too recent
- WinRAR.exe (PID: 2720)
- WinRAR.exe (PID: 3372)
- WinRAR.exe (PID: 2564)
Checks supported languages
- WinRAR.exe (PID: 2720)
- password__1234....activate-Setup.exe (PID: 3700)
- password__1234....activate-Setup.exe (PID: 1596)
- WinRAR.exe (PID: 3372)
- cmd.exe (PID: 1220)
- password__1234....activate-Setup.exe (PID: 3680)
- cmd.exe (PID: 1564)
- WinRAR.exe (PID: 2564)
- password__1234....activate-Setup.exe (PID: 3228)
- cmd.exe (PID: 3300)
Reads the computer name
- password__1234....activate-Setup.exe (PID: 3700)
- WinRAR.exe (PID: 2720)
- password__1234....activate-Setup.exe (PID: 1596)
- WinRAR.exe (PID: 3372)
- password__1234....activate-Setup.exe (PID: 3680)
- WinRAR.exe (PID: 2564)
- password__1234....activate-Setup.exe (PID: 3228)
Reads Environment values
- password__1234....activate-Setup.exe (PID: 3700)
- password__1234....activate-Setup.exe (PID: 1596)
- password__1234....activate-Setup.exe (PID: 3680)
- password__1234....activate-Setup.exe (PID: 3228)
Reads the cookies of Mozilla Firefox
- password__1234....activate-Setup.exe (PID: 3700)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2720)
- WinRAR.exe (PID: 3372)
- WinRAR.exe (PID: 2564)
Reads CPU info
- password__1234....activate-Setup.exe (PID: 3700)
- password__1234....activate-Setup.exe (PID: 1596)
- password__1234....activate-Setup.exe (PID: 3680)
- password__1234....activate-Setup.exe (PID: 3228)
Starts CMD.EXE for commands execution
- password__1234....activate-Setup.exe (PID: 1596)
- password__1234....activate-Setup.exe (PID: 3680)
- password__1234....activate-Setup.exe (PID: 3228)
Starts CMD.EXE for self-deleting
- password__1234....activate-Setup.exe (PID: 1596)
- password__1234....activate-Setup.exe (PID: 3680)
- password__1234....activate-Setup.exe (PID: 3228)
Searches for installed software
- password__1234....activate-Setup.exe (PID: 3700)
INFO
Reads the computer name
- chrome.exe (PID: 2368)
- chrome.exe (PID: 2408)
- chrome.exe (PID: 3508)
- chrome.exe (PID: 3220)
- chrome.exe (PID: 3728)
- chrome.exe (PID: 2856)
- chrome.exe (PID: 1388)
- chrome.exe (PID: 600)
- chrome.exe (PID: 3392)
- chrome.exe (PID: 3052)
- chrome.exe (PID: 2932)
Application launched itself
- chrome.exe (PID: 2368)
Checks supported languages
- chrome.exe (PID: 2368)
- chrome.exe (PID: 2160)
- chrome.exe (PID: 3508)
- chrome.exe (PID: 2408)
- chrome.exe (PID: 3060)
- chrome.exe (PID: 1024)
- chrome.exe (PID: 3220)
- chrome.exe (PID: 3128)
- chrome.exe (PID: 3432)
- chrome.exe (PID: 2808)
- chrome.exe (PID: 1272)
- chrome.exe (PID: 3524)
- chrome.exe (PID: 3860)
- chrome.exe (PID: 956)
- chrome.exe (PID: 2836)
- chrome.exe (PID: 3728)
- chrome.exe (PID: 2856)
- chrome.exe (PID: 3812)
- chrome.exe (PID: 572)
- chrome.exe (PID: 2712)
- chrome.exe (PID: 2732)
- chrome.exe (PID: 1388)
- chrome.exe (PID: 1368)
- chrome.exe (PID: 600)
- chrome.exe (PID: 3392)
- chrome.exe (PID: 612)
- chrome.exe (PID: 3764)
- chrome.exe (PID: 3912)
- timeout.exe (PID: 2632)
- chrome.exe (PID: 3052)
- chrome.exe (PID: 3832)
- chrome.exe (PID: 2132)
- chrome.exe (PID: 3008)
- chrome.exe (PID: 1596)
- chrome.exe (PID: 2204)
- chrome.exe (PID: 872)
- timeout.exe (PID: 3992)
- chrome.exe (PID: 2208)
- chrome.exe (PID: 2540)
- chrome.exe (PID: 2932)
- timeout.exe (PID: 2780)
Reads the hosts file
- chrome.exe (PID: 2368)
- chrome.exe (PID: 2408)
Reads settings of System Certificates
- chrome.exe (PID: 2408)
Changes default file association
- chrome.exe (PID: 2368)
Reads the date of Windows installation
- chrome.exe (PID: 1388)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
92
Monitored processes
51
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 572 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,11373123984495570394,12710461487532574670,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --disable-client-side-phishing-detection --instant-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=19 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=992 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 600 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1000,11373123984495570394,12710461487532574670,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3536 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 612 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1000,11373123984495570394,12710461487532574670,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3788 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 872 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1000,11373123984495570394,12710461487532574670,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2964 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 956 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1000,11373123984495570394,12710461487532574670,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3692 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1024 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,11373123984495570394,12710461487532574670,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1836 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1220 | "C:\Windows\system32\cmd.exe" /c rd /s /q C:\Users\admin\AppData\Local\Temp\CBLHcEVYuuMCI & timeout 4 & del /f /q "C:\Users\admin\AppData\Local\Temp\Rar$EXb2720.48780\password__1234....activate-Setup.exe" | C:\Windows\system32\cmd.exe | — | password__1234....activate-Setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1272 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,11373123984495570394,12710461487532574670,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2752 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1368 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,11373123984495570394,12710461487532574670,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --disable-client-side-phishing-detection --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=22 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3552 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1388 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1000,11373123984495570394,12710461487532574670,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3828 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
23 683
Read events
23 359
Write events
312
Delete events
12
Modification events
| (PID) Process: | (2368) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2368) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2368) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2368) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2368) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2368) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2368) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2368) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2368) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (2368) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
4
Suspicious files
41
Text files
153
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2368 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-61B6BC6D-940.pma | — | |
MD5:— | SHA256:— | |||
| 2368 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\e2d2de96-2030-402d-ba2b-4b080ae9c664.tmp | text | |
MD5:— | SHA256:— | |||
| 2368 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 2368 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 2368 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:7721CDA9F5B73CE8A135471EB53B4E0E | SHA256:DD730C576766A46FFC84E682123248ECE1FF1887EC0ACAB22A5CE93A450F4500 | |||
| 2368 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RF13fa42.TMP | text | |
MD5:81F483F77EE490F35306A4F94DB2286B | SHA256:82434CE3C9D13F509EBEEBE3A7A1A1DE9AB4557629D9FC855761E0CFA45E8BCE | |||
| 2368 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:995C92837E4775CAFFE387D51ADBA520 | SHA256:51247C3464FD988B72670002D01A57FBFF1348704D325DC8FF8817ED2459D0D9 | |||
| 2368 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF13fa03.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
| 2368 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:8FF312A95D60ED89857FEB720D80D4E1 | SHA256:946A57FAFDD28C3164D5AB8AB4971B21BD5EC5BFFF7554DBF832CB58CC37700B | |||
| 2368 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\23173947-a343-4a0e-b0b0-948b24c6c42f.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
83
TCP/UDP connections
78
DNS requests
47
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
924 | svchost.exe | HEAD | 200 | 173.194.150.199:80 | http://r1---sn-5goeen7k.gvt1.com/edgedl/release2/chrome_component/czka5fc33qq67ao7g67evi5jte_9.32.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.32.0_all_hkbbg5yepfmg4tn57zz6rpfdiy.crx3?cms_redirect=yes&mh=1f&mip=157.97.120.205&mm=28&mn=sn-5goeen7k&ms=nvh&mt=1639365554&mv=u&mvi=1&pl=25&rmhost=r4---sn-5goeen7k.gvt1.com&shardbypass=yes&smhost=r4---sn-5goeen7r.gvt1.com | US | — | — | whitelisted |
924 | svchost.exe | HEAD | 302 | 216.58.212.142:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/czka5fc33qq67ao7g67evi5jte_9.32.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.32.0_all_hkbbg5yepfmg4tn57zz6rpfdiy.crx3 | US | — | — | whitelisted |
2408 | chrome.exe | GET | 404 | 134.122.115.190:80 | http://134.122.115.190/css/main.css | US | html | 277 b | unknown |
2408 | chrome.exe | GET | 404 | 134.122.115.190:80 | http://134.122.115.190/images/logo.png | US | html | 277 b | unknown |
2408 | chrome.exe | GET | 200 | 134.122.115.190:80 | http://134.122.115.190/?rip=ba4126ecf52529c82a9bf15acfbfd22f&ikdp=2822&content=3_fl-studio-20-8-4-2576-crack-keygen-full-zip-file-download-2022&gkss=467598 | US | html | 1.51 Kb | unknown |
2408 | chrome.exe | GET | 404 | 134.122.115.190:80 | http://134.122.115.190/js/bootstrap.min.js | US | html | 277 b | unknown |
2408 | chrome.exe | GET | 404 | 134.122.115.190:80 | http://134.122.115.190/js/slider/owl.carousel.min.js | US | html | 277 b | unknown |
2408 | chrome.exe | GET | 404 | 134.122.115.190:80 | http://134.122.115.190/js/jquery-2.1.1.min.js | US | html | 277 b | unknown |
2408 | chrome.exe | GET | 404 | 134.122.115.190:80 | http://134.122.115.190/js/wow.min.js | US | html | 277 b | unknown |
2408 | chrome.exe | GET | 404 | 134.122.115.190:80 | http://134.122.115.190/js/bootstrap.offcanvas.js | US | html | 277 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2408 | chrome.exe | 172.67.160.112:443 | 24cracked.com | — | US | unknown |
2408 | chrome.exe | 142.250.184.206:443 | clients2.google.com | Google Inc. | US | whitelisted |
2408 | chrome.exe | 67.27.158.254:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | malicious |
2408 | chrome.exe | 192.0.77.37:443 | c0.wp.com | Automattic, Inc | US | suspicious |
2408 | chrome.exe | 216.58.212.138:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2408 | chrome.exe | 142.250.185.163:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2408 | chrome.exe | 192.0.76.3:443 | stats.wp.com | Automattic, Inc | US | suspicious |
2408 | chrome.exe | 192.0.78.33:443 | jetpack.wordpress.com | Automattic, Inc | US | unknown |
2408 | chrome.exe | 192.0.77.32:443 | s0.wp.com | Automattic, Inc | US | suspicious |
2408 | chrome.exe | 157.240.27.18:443 | graph.facebook.com | Facebook, Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
24cracked.com |
| unknown |
accounts.google.com |
| shared |
clients2.google.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
c0.wp.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
0.gravatar.com |
| whitelisted |
2.gravatar.com |
| whitelisted |
1.gravatar.com |
| whitelisted |
i0.wp.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
3700 | password__1234....activate-Setup.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.top domain |
3700 | password__1234....activate-Setup.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.top domain |
3700 | password__1234....activate-Setup.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.top domain |
3700 | password__1234....activate-Setup.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.top domain |
3700 | password__1234....activate-Setup.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.top domain |
4 ETPRO signatures available at the full report