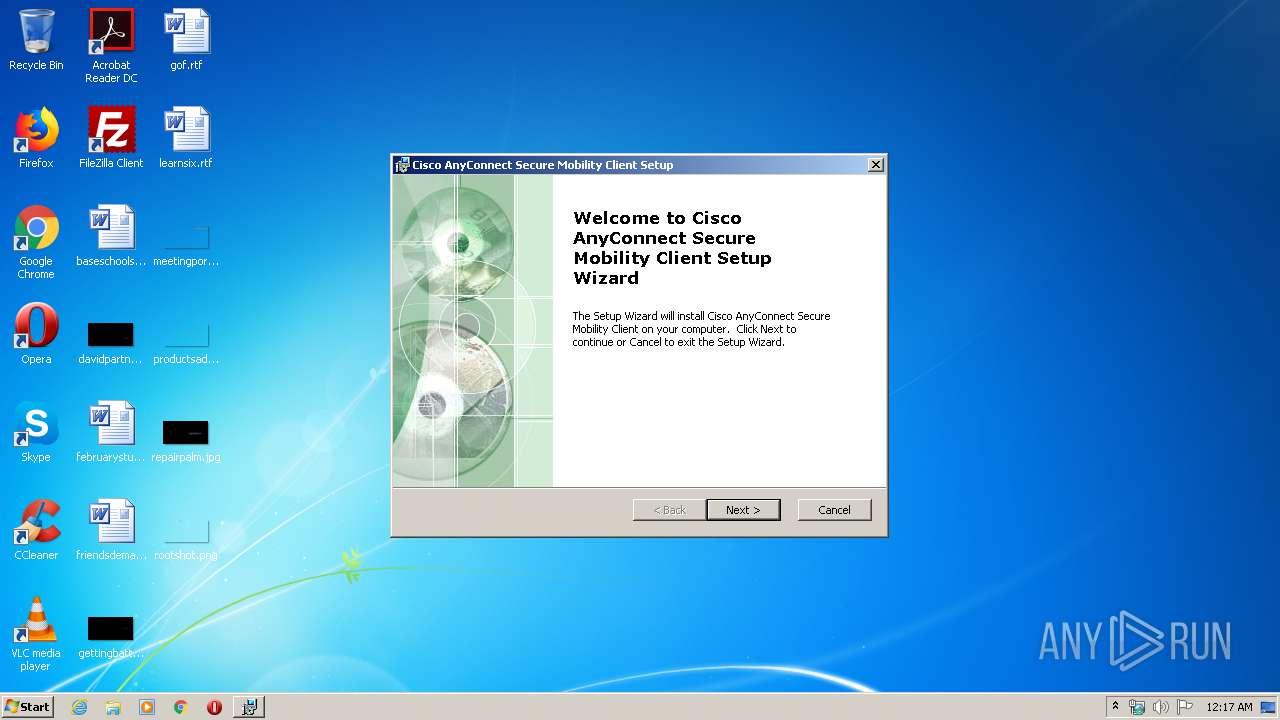
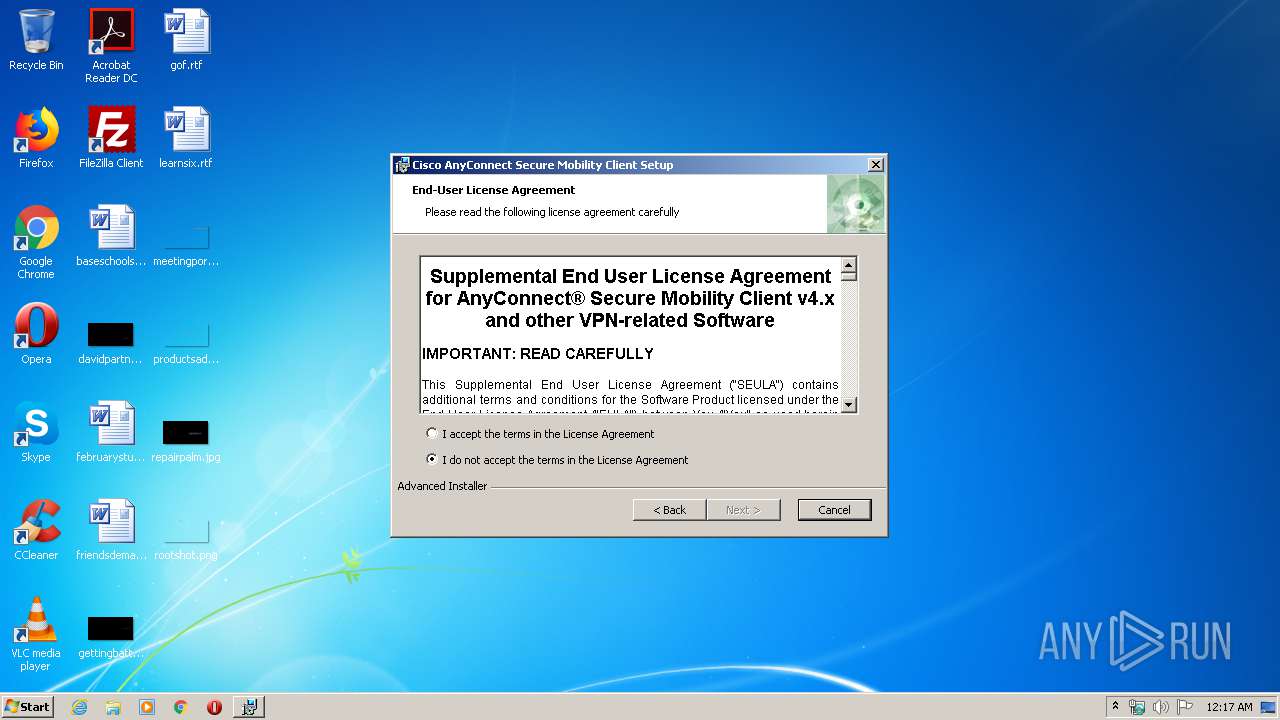
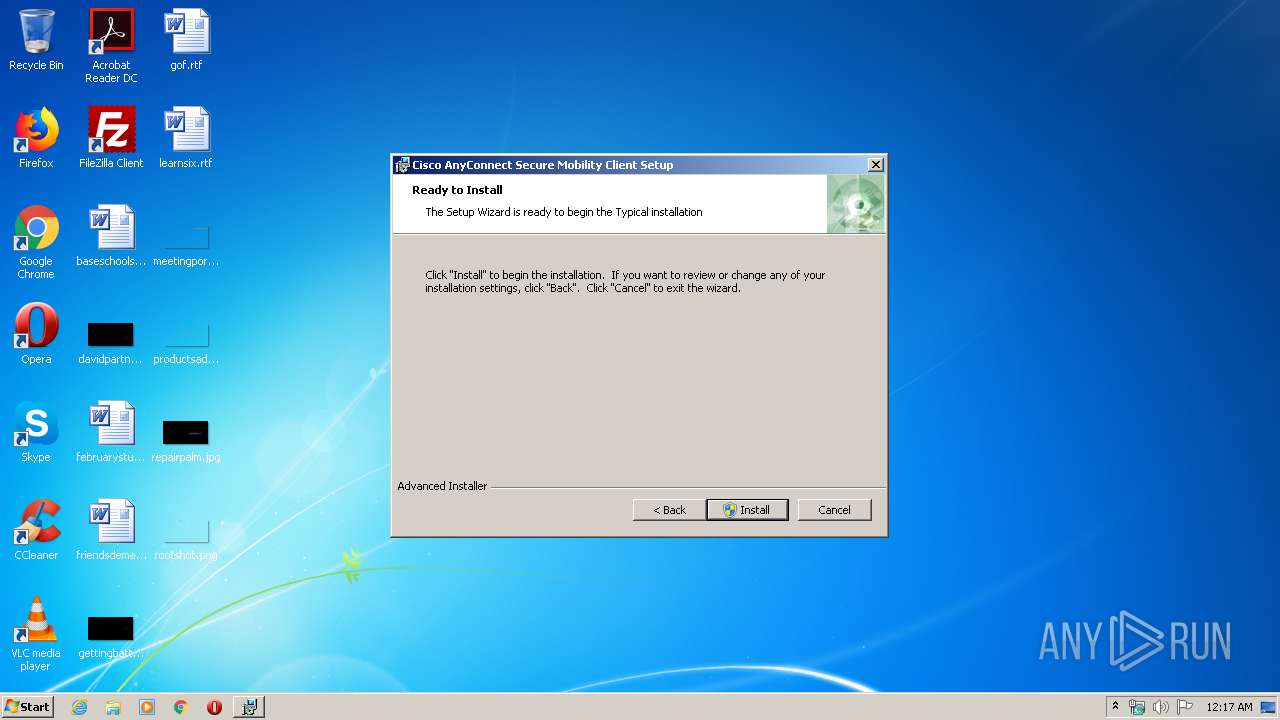
| File name: | anyconnect-win-4.7.04056-core-vpn-webdeploy-k9.exe |
| Full analysis: | https://app.any.run/tasks/be689ed1-41ae-47f1-b6cb-cfcb1eec0407 |
| Verdict: | Malicious activity |
| Analysis date: | March 31, 2020, 23:17:30 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 2BE2690D30E924A67E4C17F1F4F2FF37 |
| SHA1: | 61286F38913CE70572B8EB836E40CCBB1D515FC9 |
| SHA256: | B574392D4112CB7326DC1FBF255B7418D8CCFCD45AEC0A2586237B97DF92F0ED |
| SSDEEP: | 98304:KcJCfV+vKe/Od/Bd0TnudmXvfsIJaa09/Xp8UG/US/rjul2sIlgEdva11UXk:KcY+D2beKd0vfMIUG/UuEg/hiU0 |
MALICIOUS
Loads dropped or rewritten executable
- anyconnect-win-4.7.04056-core-vpn-webdeploy-k9.exe (PID: 540)
- InstallHelper.exe (PID: 3844)
- InstallHelper.exe (PID: 2760)
- InstallHelper.exe (PID: 3852)
- InstallHelper.exe (PID: 3452)
- InstallHelper.exe (PID: 2404)
- InstallHelper.exe (PID: 2792)
- InstallHelper.exe (PID: 1944)
- InstallHelper.exe (PID: 2500)
- InstallHelper.exe (PID: 2936)
- InstallHelper.exe (PID: 3508)
- InstallHelper.exe (PID: 1412)
- vpnagent.exe (PID: 256)
- vpnui.exe (PID: 1632)
Application was dropped or rewritten from another process
- InstallHelper.exe (PID: 3844)
- InstallHelper.exe (PID: 2792)
- InstallHelper.exe (PID: 2760)
- InstallHelper.exe (PID: 3852)
- InstallHelper.exe (PID: 2404)
- VACon.exe (PID: 604)
- VACon.exe (PID: 2452)
- InstallHelper.exe (PID: 2500)
- InstallHelper.exe (PID: 1944)
- InstallHelper.exe (PID: 2936)
- InstallHelper.exe (PID: 1412)
- InstallHelper.exe (PID: 3508)
- vpnagent.exe (PID: 256)
- ManifestTool.exe (PID: 2760)
- vpnui.exe (PID: 1632)
- InstallHelper.exe (PID: 3452)
Changes the autorun value in the registry
- VACon.exe (PID: 604)
- vpnagent.exe (PID: 256)
Changes settings of System certificates
- vpnagent.exe (PID: 256)
- VACon.exe (PID: 2452)
Tries to delete the host file
- vpnagent.exe (PID: 256)
Loads the Task Scheduler DLL interface
- anyconnect-win-4.7.04056-core-vpn-webdeploy-k9.exe (PID: 540)
SUSPICIOUS
Executable content was dropped or overwritten
- anyconnect-win-4.7.04056-core-vpn-webdeploy-k9.exe (PID: 540)
- msiexec.exe (PID: 3480)
- VACon.exe (PID: 604)
- DrvInst.exe (PID: 3340)
Executed as Windows Service
- vssvc.exe (PID: 956)
- vpnagent.exe (PID: 256)
Starts CMD.EXE for commands execution
- MsiExec.exe (PID: 2756)
Creates files in the Windows directory
- msiexec.exe (PID: 3480)
- VACon.exe (PID: 604)
- DrvInst.exe (PID: 2376)
- DrvInst.exe (PID: 3340)
- vpnagent.exe (PID: 256)
Changes the autorun value in the registry
- msiexec.exe (PID: 3480)
Changes IE settings (feature browser emulation)
- msiexec.exe (PID: 3480)
Creates files in the driver directory
- VACon.exe (PID: 604)
- DrvInst.exe (PID: 2376)
- DrvInst.exe (PID: 3340)
- vpnagent.exe (PID: 256)
Removes files from Windows directory
- VACon.exe (PID: 604)
- DrvInst.exe (PID: 2376)
- DrvInst.exe (PID: 3340)
- vpnagent.exe (PID: 256)
Executed via COM
- DrvInst.exe (PID: 2376)
- DrvInst.exe (PID: 3340)
- rundll32.exe (PID: 3492)
Creates COM task schedule object
- InstallHelper.exe (PID: 2404)
Creates files in the program directory
- InstallHelper.exe (PID: 1944)
- ManifestTool.exe (PID: 2760)
Adds / modifies Windows certificates
- vpnagent.exe (PID: 256)
- VACon.exe (PID: 2452)
Reads internet explorer settings
- vpnui.exe (PID: 1632)
Reads Internet Cache Settings
- vpnui.exe (PID: 1632)
INFO
Loads dropped or rewritten executable
- MsiExec.exe (PID: 2992)
- MsiExec.exe (PID: 3960)
- MsiExec.exe (PID: 2756)
Reads settings of System Certificates
- msiexec.exe (PID: 3480)
Low-level read access rights to disk partition
- vssvc.exe (PID: 956)
Searches for installed software
- msiexec.exe (PID: 3480)
Application launched itself
- msiexec.exe (PID: 3480)
Dropped object may contain Bitcoin addresses
- anyconnect-win-4.7.04056-core-vpn-webdeploy-k9.exe (PID: 540)
- msiexec.exe (PID: 3480)
Creates a software uninstall entry
- msiexec.exe (PID: 3480)
Creates or modifies windows services
- msiexec.exe (PID: 3480)
Creates files in the program directory
- msiexec.exe (PID: 3480)
Reads the hosts file
- vpnagent.exe (PID: 256)
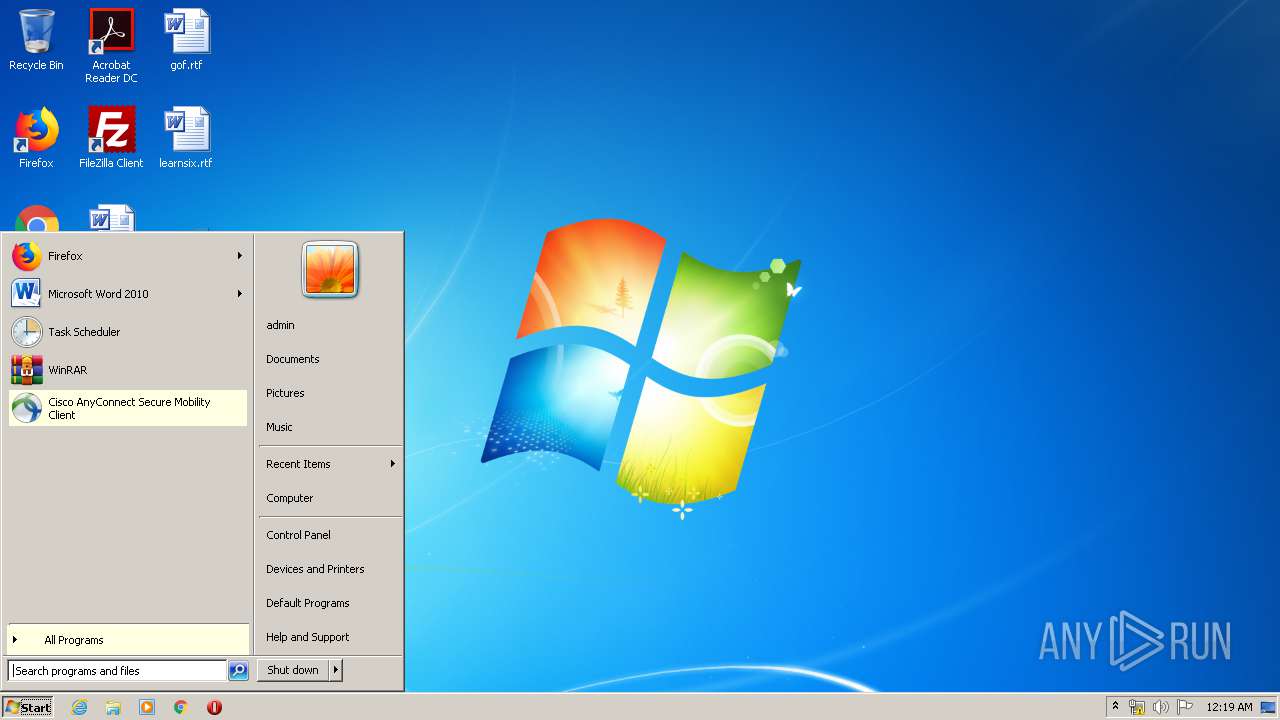
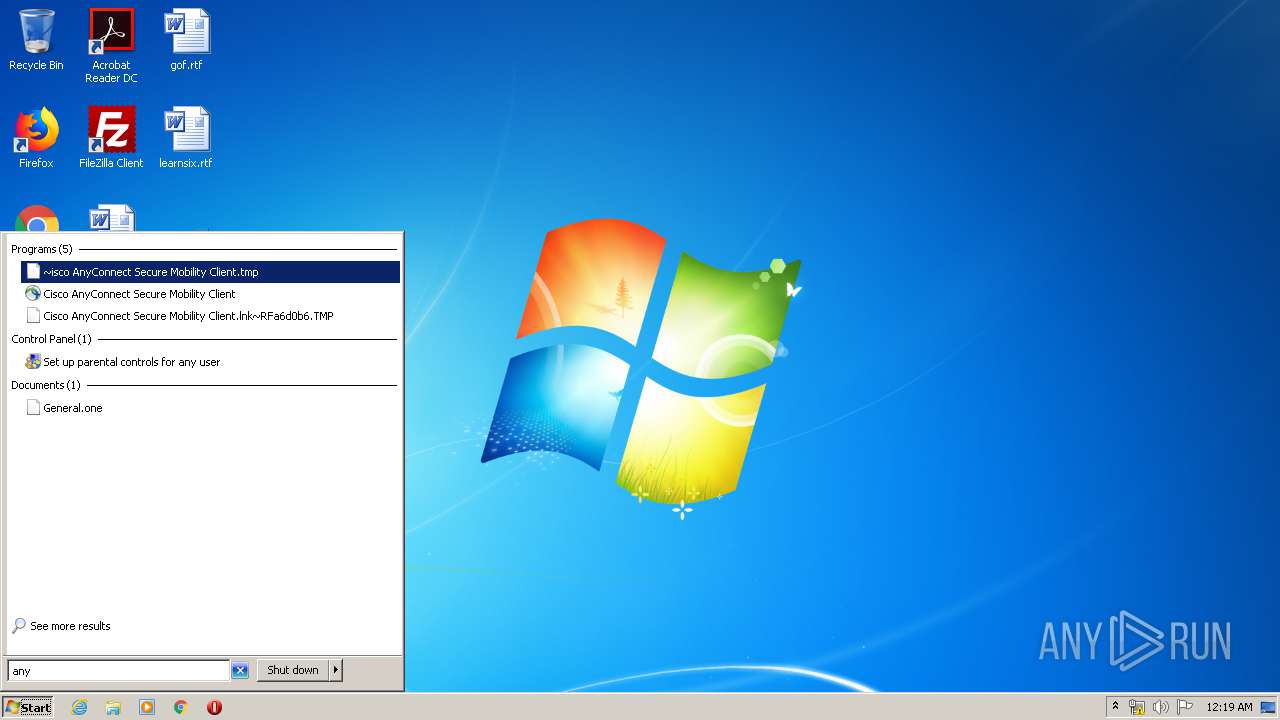
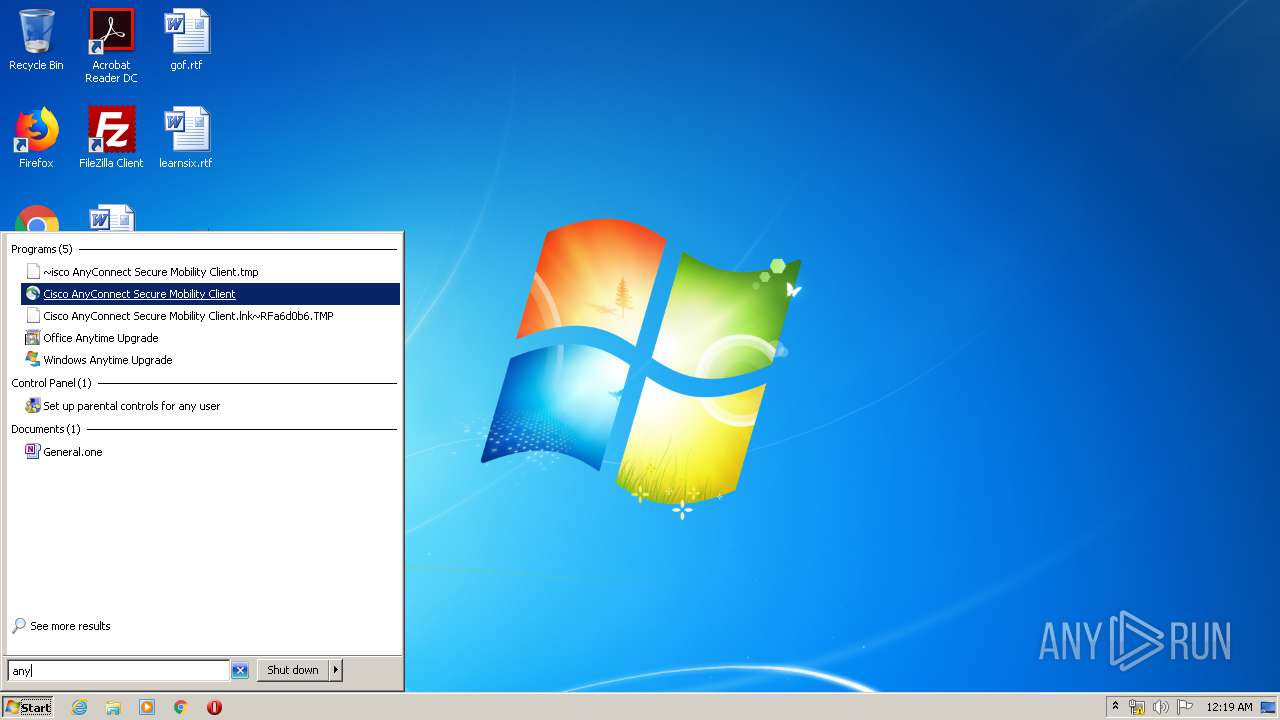
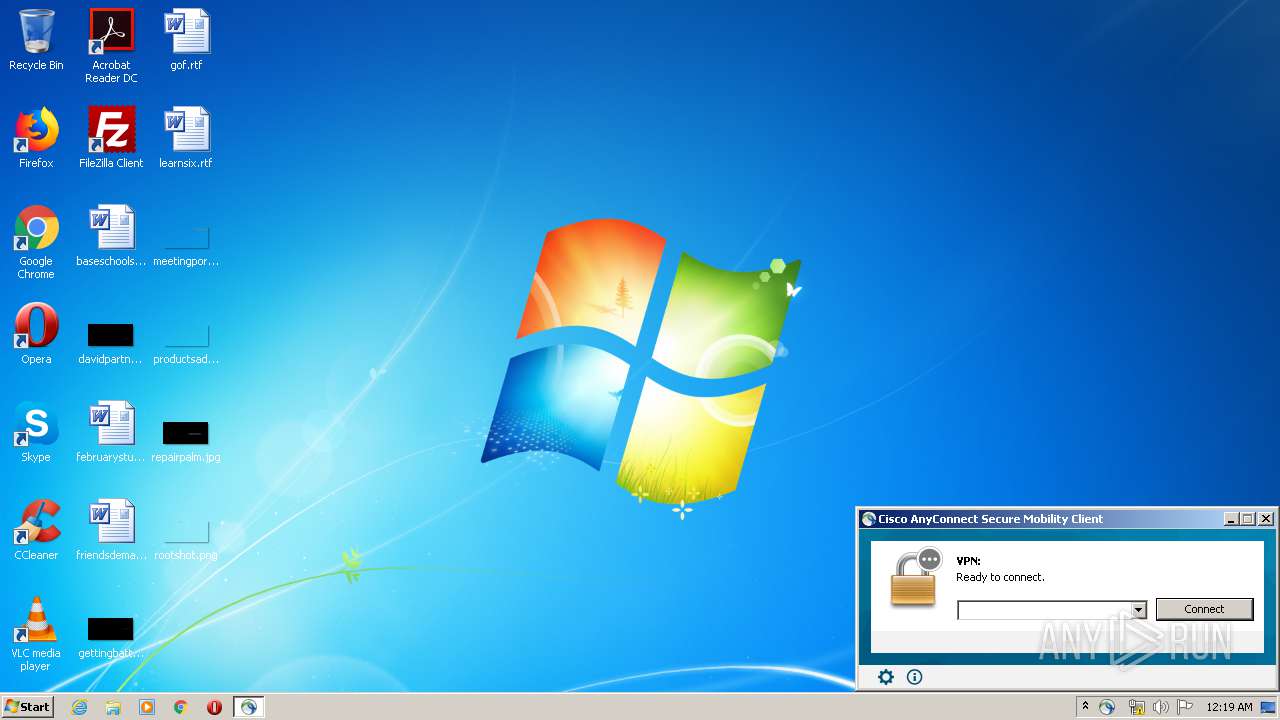
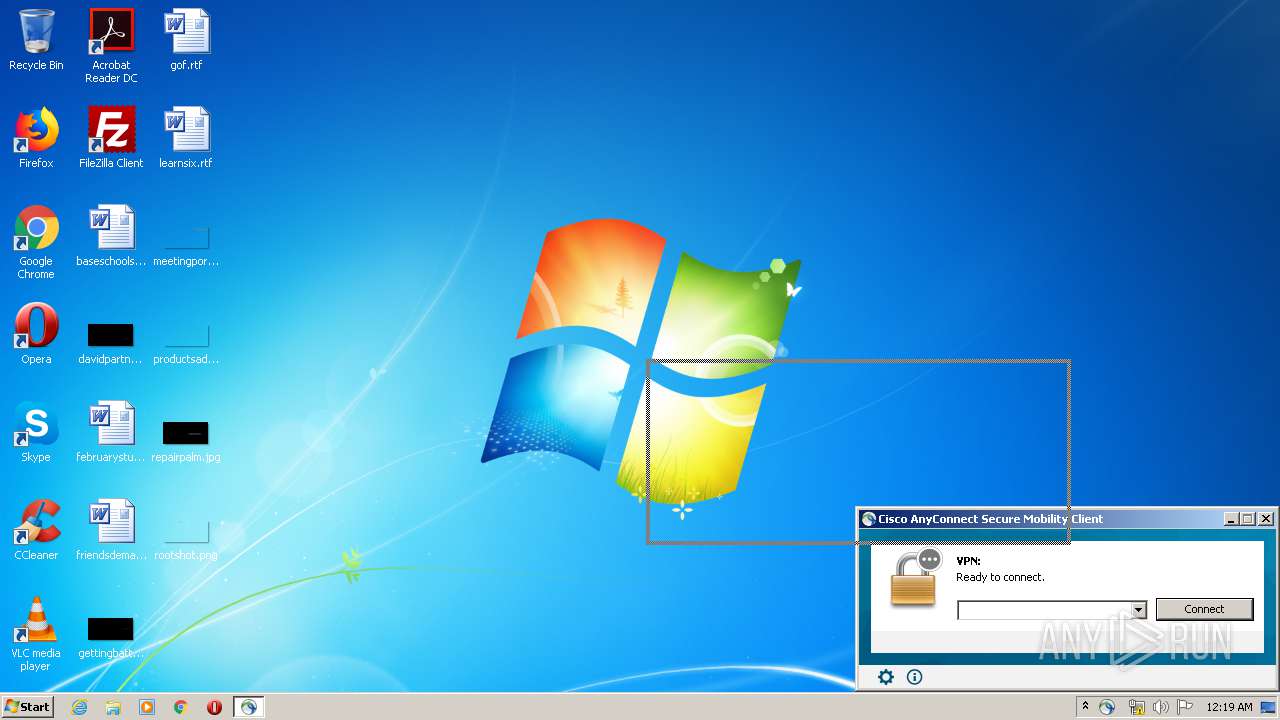
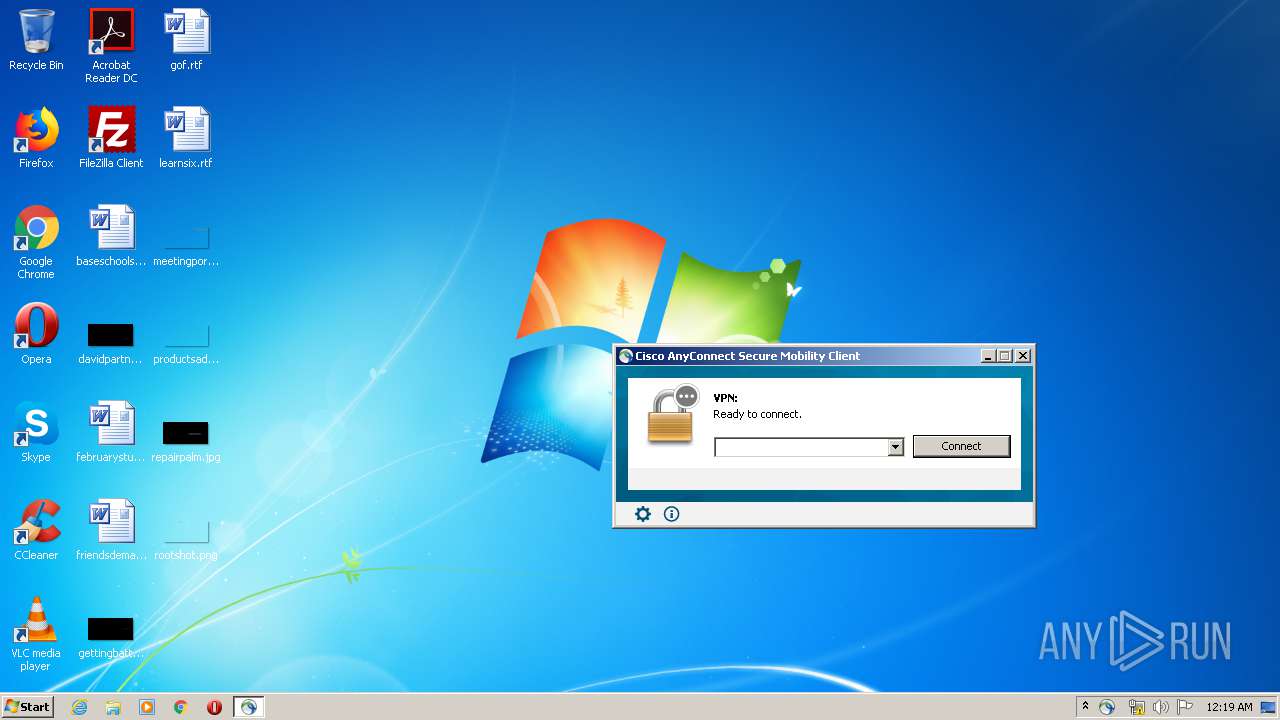
Manual execution by user
- vpnui.exe (PID: 1632)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:11:15 17:17:16+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 256000 |
| InitializedDataSize: | 155648 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x272c9 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.7.4056.0 |
| ProductVersionNumber: | 4.7.4056.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Debug |
| FileOS: | Win32 |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Cisco Systems, Inc. |
| FileDescription: | A SmartNET contract is required for support - Cisco AnyConnect Secure Mobility Client. |
| FileVersion: | 4.7.04056 |
| InternalName: | WinSetup-Release-web-deploy |
| LegalCopyright: | Copyright (C) 2019 Cisco Systems, Inc. |
| OriginalFileName: | WinSetup-Release-web-deploy.exe |
| ProductName: | Cisco AnyConnect Secure Mobility Client |
| ProductVersion: | 4.7.04056 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 15-Nov-2016 16:17:16 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Cisco Systems, Inc. |
| FileDescription: | A SmartNET contract is required for support - Cisco AnyConnect Secure Mobility Client. |
| FileVersion: | 4.7.04056 |
| InternalName: | WinSetup-Release-web-deploy |
| LegalCopyright: | Copyright (C) 2019 Cisco Systems, Inc. |
| OriginalFileName: | WinSetup-Release-web-deploy.exe |
| ProductName: | Cisco AnyConnect Secure Mobility Client |
| ProductVersion: | 4.7.04056 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000120 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 7 |
| Time date stamp: | 15-Nov-2016 16:17:16 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0003E720 | 0x0003E800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.62814 |
.rdata | 0x00040000 | 0x00012294 | 0x00012400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.67103 |
.data | 0x00053000 | 0x000022A4 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.31769 |
.gfids | 0x00056000 | 0x00000108 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.16534 |
.tls | 0x00057000 | 0x00000009 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.0203931 |
.rsrc | 0x00058000 | 0x0000EB9C | 0x0000EC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.05777 |
.reloc | 0x00067000 | 0x00003C0C | 0x00003E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.60409 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.221 | 1915 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.1591 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 3.46873 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 3.54157 | 2440 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 4.01317 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 3.37783 | 1116 | Latin 1 / Western European | English - United States | RT_STRING |
10 | 3.35254 | 1888 | Latin 1 / Western European | English - United States | RT_STRING |
11 | 3.31743 | 760 | Latin 1 / Western European | English - United States | RT_STRING |
12 | 3.23118 | 1432 | Latin 1 / Western European | English - United States | RT_STRING |
13 | 3.34109 | 1000 | Latin 1 / Western European | English - United States | RT_STRING |
Imports
KERNEL32.dll |
msi.dll (delay-loaded) |
Total processes
72
Monitored processes
31
Malicious processes
18
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 256 | "C:\Program Files\Cisco\Cisco AnyConnect Secure Mobility Client\vpnagent.exe" | C:\Program Files\Cisco\Cisco AnyConnect Secure Mobility Client\vpnagent.exe | services.exe | ||||||||||||
User: SYSTEM Company: Cisco Systems, Inc. Integrity Level: SYSTEM Description: VPN Agent Service Exit code: 0 Version: 4, 7, 04056 Modules
| |||||||||||||||
| 540 | "C:\Users\admin\AppData\Local\Temp\anyconnect-win-4.7.04056-core-vpn-webdeploy-k9.exe" | C:\Users\admin\AppData\Local\Temp\anyconnect-win-4.7.04056-core-vpn-webdeploy-k9.exe | explorer.exe | ||||||||||||
User: admin Company: Cisco Systems, Inc. Integrity Level: MEDIUM Description: A SmartNET contract is required for support - Cisco AnyConnect Secure Mobility Client. Exit code: 0 Version: 4.7.04056 Modules
| |||||||||||||||
| 604 | "C:\Program Files\Cisco\Cisco AnyConnect Secure Mobility Client\VACon.exe" kdf -install "C:\Program Files\Cisco\Cisco AnyConnect Secure Mobility Client\\" acsock | C:\Program Files\Cisco\Cisco AnyConnect Secure Mobility Client\VACon.exe | msiexec.exe | ||||||||||||
User: admin Company: Cisco Systems, Inc. Integrity Level: MEDIUM Description: AnyConnect Secure Mobility Client Virtual Adapter Installer Exit code: 0 Version: 4, 7, 04056 Modules
| |||||||||||||||
| 956 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1412 | "C:\Program Files\Cisco\Cisco AnyConnect Secure Mobility Client\InstallHelper.exe" -createRestrictedUser | C:\Program Files\Cisco\Cisco AnyConnect Secure Mobility Client\InstallHelper.exe | — | msiexec.exe | |||||||||||
User: admin Company: Cisco Systems, Inc. Integrity Level: MEDIUM Description: AnyConnect Secure Mobility Client Install Helper Exit code: 0 Version: 4, 7, 04056 Modules
| |||||||||||||||
| 1632 | "C:\Program Files\Cisco\Cisco AnyConnect Secure Mobility Client\vpnui.exe" | C:\Program Files\Cisco\Cisco AnyConnect Secure Mobility Client\vpnui.exe | explorer.exe | ||||||||||||
User: admin Company: Cisco Systems, Inc. Integrity Level: MEDIUM Description: Cisco AnyConnect User Interface Exit code: 0 Version: 4, 7, 04056 Modules
| |||||||||||||||
| 1944 | "C:\Program Files\Cisco\Cisco AnyConnect Secure Mobility Client\InstallHelper.exe" -acpolgen bd=false fm=false rpc=false rtp=false rwl=false sct=false epf=false ewn=false emn=false efn=false upsu=true upcu=true upvp=true upmv=true upip=true upsp=true upal= ecc=false | C:\Program Files\Cisco\Cisco AnyConnect Secure Mobility Client\InstallHelper.exe | — | msiexec.exe | |||||||||||
User: admin Company: Cisco Systems, Inc. Integrity Level: MEDIUM Description: AnyConnect Secure Mobility Client Install Helper Exit code: 0 Version: 4, 7, 04056 Modules
| |||||||||||||||
| 2376 | DrvInst.exe "4" "0" "C:\Users\admin\AppData\Local\Temp\{65aac024-d618-7bdb-4a2c-f12c01574530}\vpnva-6.inf" "0" "658dd218b" "000005C8" "WinSta0\Default" "00000554" "208" "c:\program files\cisco\cisco anyconnect secure mobility client" | C:\Windows\system32\DrvInst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2404 | "C:\Program Files\Cisco\Cisco AnyConnect Secure Mobility Client\InstallHelper.exe" -registerdll "C:\Program Files\Cisco\Cisco AnyConnect Secure Mobility Client\vpnapi.dll" | C:\Program Files\Cisco\Cisco AnyConnect Secure Mobility Client\InstallHelper.exe | — | msiexec.exe | |||||||||||
User: admin Company: Cisco Systems, Inc. Integrity Level: MEDIUM Description: AnyConnect Secure Mobility Client Install Helper Exit code: 0 Version: 4, 7, 04056 Modules
| |||||||||||||||
| 2424 | "C:\Windows\System32\grpconv.exe" -o | C:\Windows\System32\grpconv.exe | — | runonce.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Progman Group Converter Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
3 142
Read events
963
Write events
2 123
Delete events
56
Modification events
| (PID) Process: | (3488) msiexec.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3480) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 40000000000000000C6DBB9DB207D601980D0000FC0E0000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3480) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 40000000000000000C6DBB9DB207D601980D0000FC0E0000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3480) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 34 | |||
| (PID) Process: | (3480) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4000000000000000F255059EB207D601980D0000FC0E0000D3070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3480) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000004CB8079EB207D601980D0000B0050000E80300000100000000000000000000002352FD9610582D4B8ECE12950F1A70030000000000000000 | |||
| (PID) Process: | (956) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000C268189EB207D601BC030000500A0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (956) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000C268189EB207D601BC030000600C0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (956) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000C268189EB207D601BC030000F00C0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (956) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000C268189EB207D601BC030000340A0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
173
Suspicious files
24
Text files
250
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 540 | anyconnect-win-4.7.04056-core-vpn-webdeploy-k9.exe | C:\Users\admin\AppData\Local\Temp\Cisco\Installer\holder0.aiph | — | |
MD5:— | SHA256:— | |||
| 3488 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI774B.tmp | — | |
MD5:— | SHA256:— | |||
| 3488 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI77BA.tmp | — | |
MD5:— | SHA256:— | |||
| 3488 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI77DA.tmp | — | |
MD5:— | SHA256:— | |||
| 3488 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI7819.tmp | — | |
MD5:— | SHA256:— | |||
| 3480 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 3480 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DF05EC1B074D221004.TMP | — | |
MD5:— | SHA256:— | |||
| 3480 | msiexec.exe | C:\Windows\Installer\MSIC5EA.tmp | — | |
MD5:— | SHA256:— | |||
| 3480 | msiexec.exe | C:\Windows\Installer\MSIC60A.tmp | — | |
MD5:— | SHA256:— | |||
| 3480 | msiexec.exe | C:\Windows\Installer\MSIC64A.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
5
DNS requests
4
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
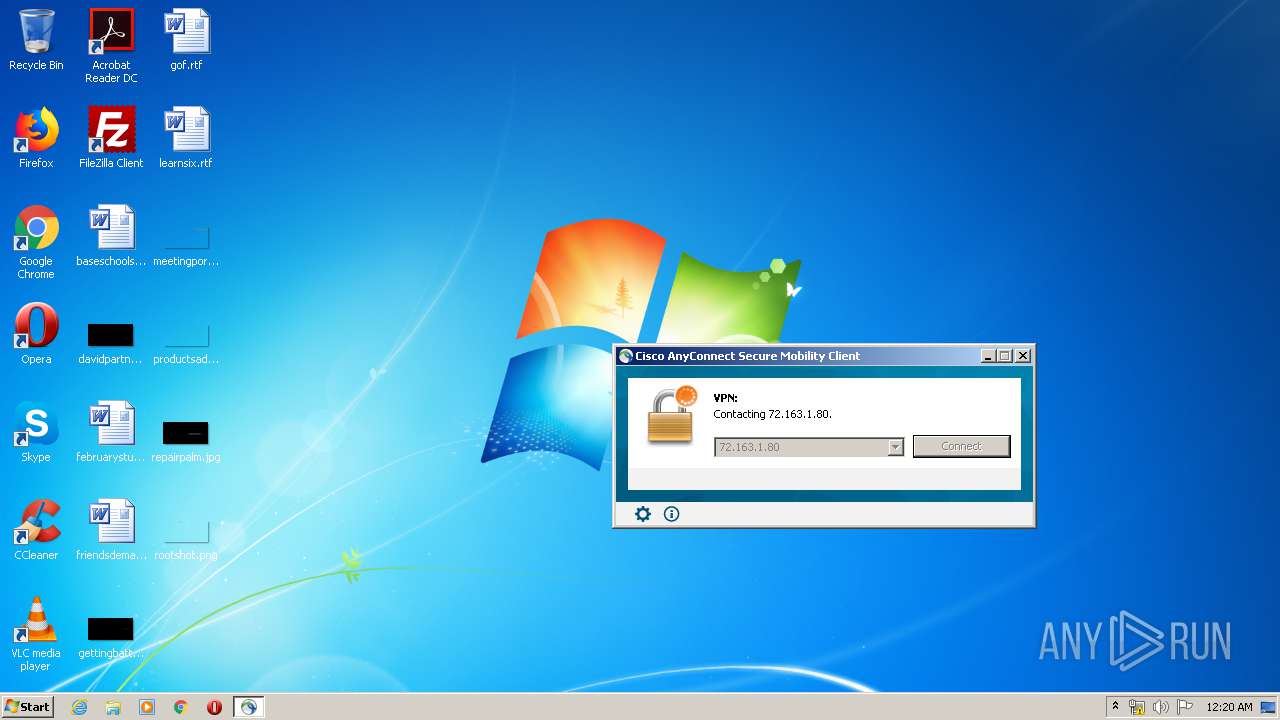
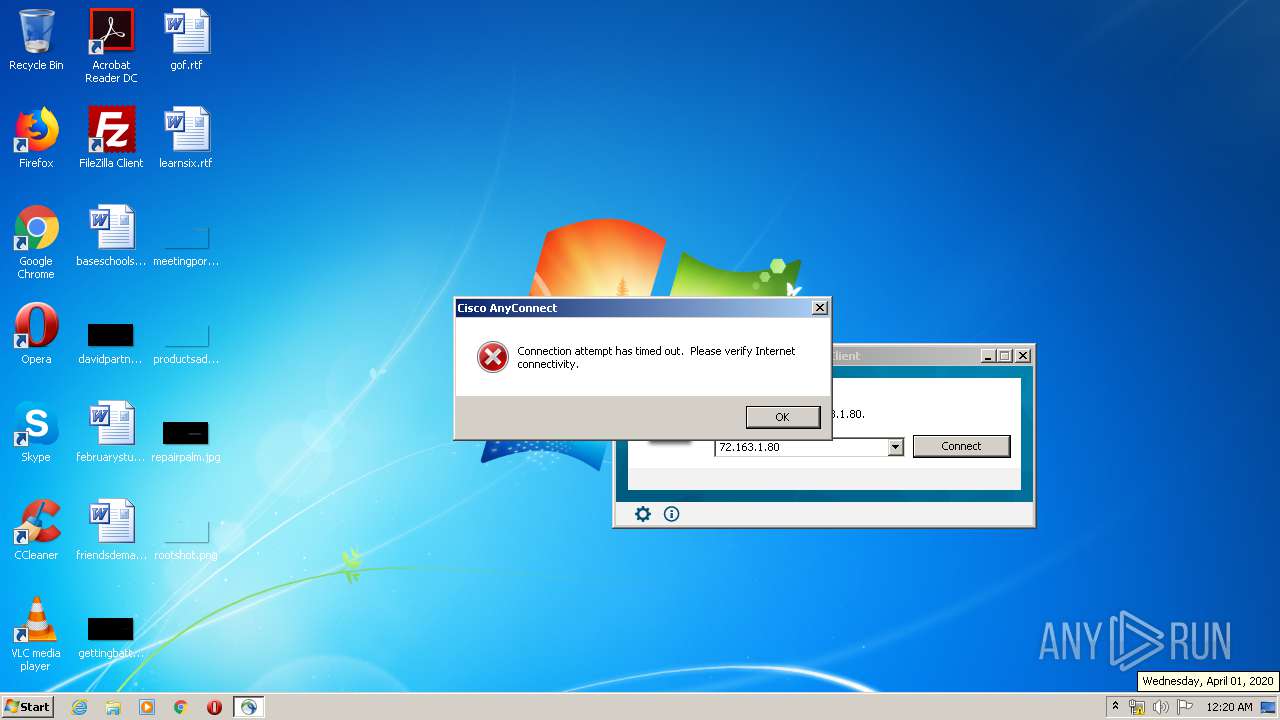
256 | vpnagent.exe | GET | — | 72.163.1.80:80 | http://72.163.1.80/ | US | — | — | whitelisted |
256 | vpnagent.exe | GET | — | 72.163.1.80:80 | http://72.163.1.80/ | US | — | — | whitelisted |
256 | vpnagent.exe | GET | — | 72.163.1.80:80 | http://72.163.1.80/ | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
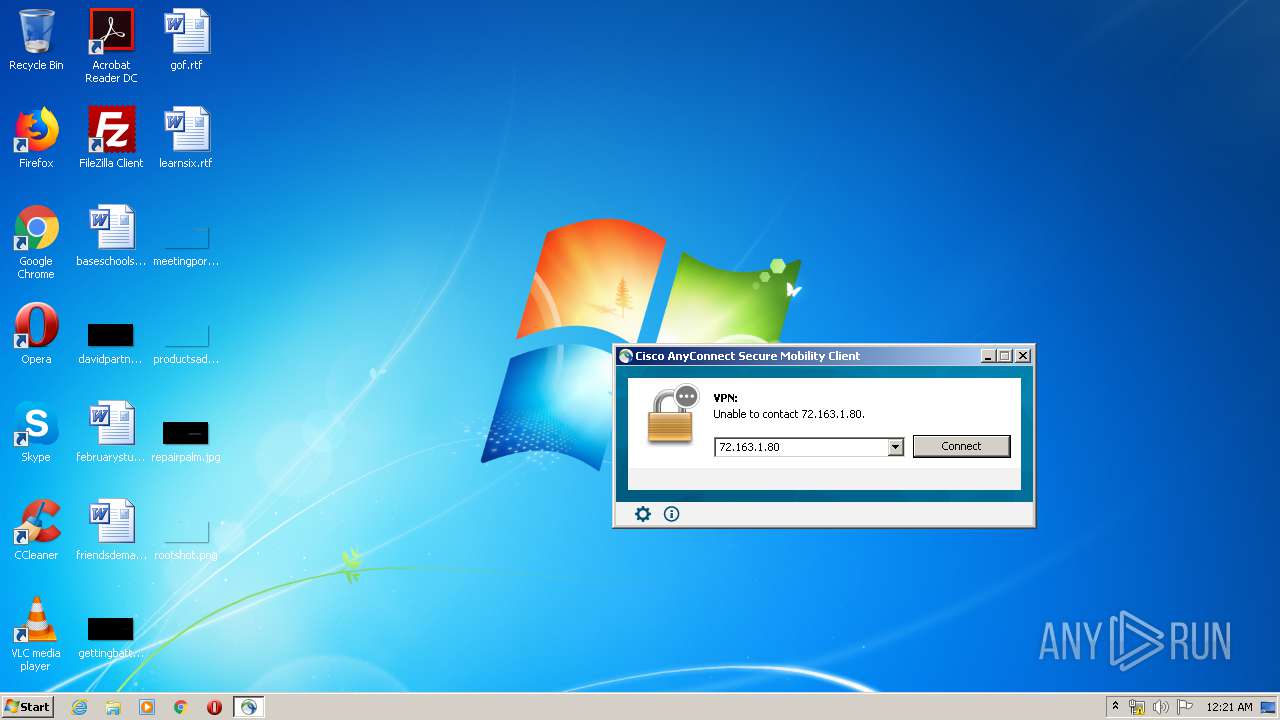
1632 | vpnui.exe | 72.163.1.80:443 | mus.cisco.com | Cisco Systems, Inc. | US | unknown |
256 | vpnagent.exe | 72.163.1.80:80 | mus.cisco.com | Cisco Systems, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
mus.cisco.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
256 | vpnagent.exe | Generic Protocol Command Decode | SURICATA STREAM CLOSEWAIT FIN out of window |
Process | Message |
|---|---|
MsiExec.exe | DBGHELP: Symbol Search Path: .
|
MsiExec.exe | DBGHELP: Symbol Search Path: C:\Windows\system32
|
MsiExec.exe | DBGHELP: SymSrv load failure: symsrv.dll
|
MsiExec.exe | DBGHELP: ntdll - export symbols
|
MsiExec.exe | DBGHELP: C:\Windows\system32\ntdll.pdb - file not found
|
MsiExec.exe | DBGHELP: C:\Windows\system32\dll\ntdll.pdb - file not found
|
MsiExec.exe | DBGHELP: C:\Windows\system32\symbols\dll\ntdll.pdb - file not found
|
MsiExec.exe | DBGHELP: ntdll.pdb - file not found
|
VACon.exe | VACON: -install
|
MsiExec.exe | DBGHELP: C:\Windows\system32\ntdll.pdb - file not found
|