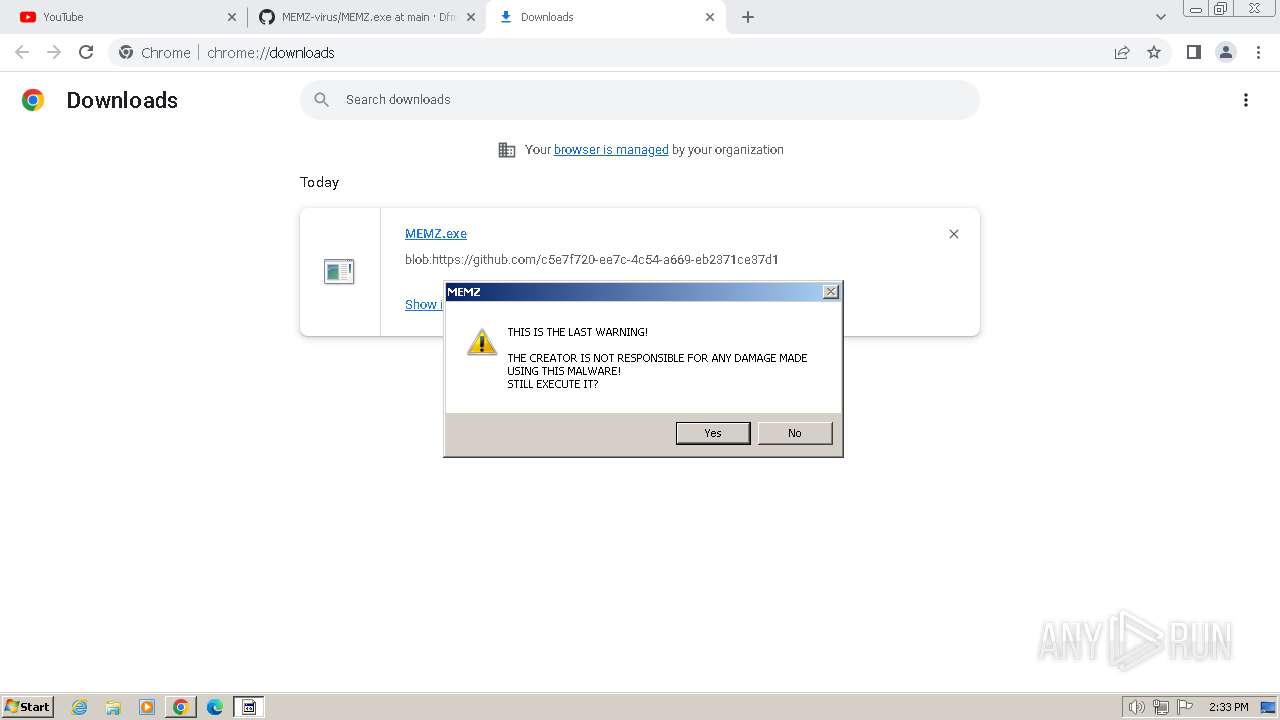
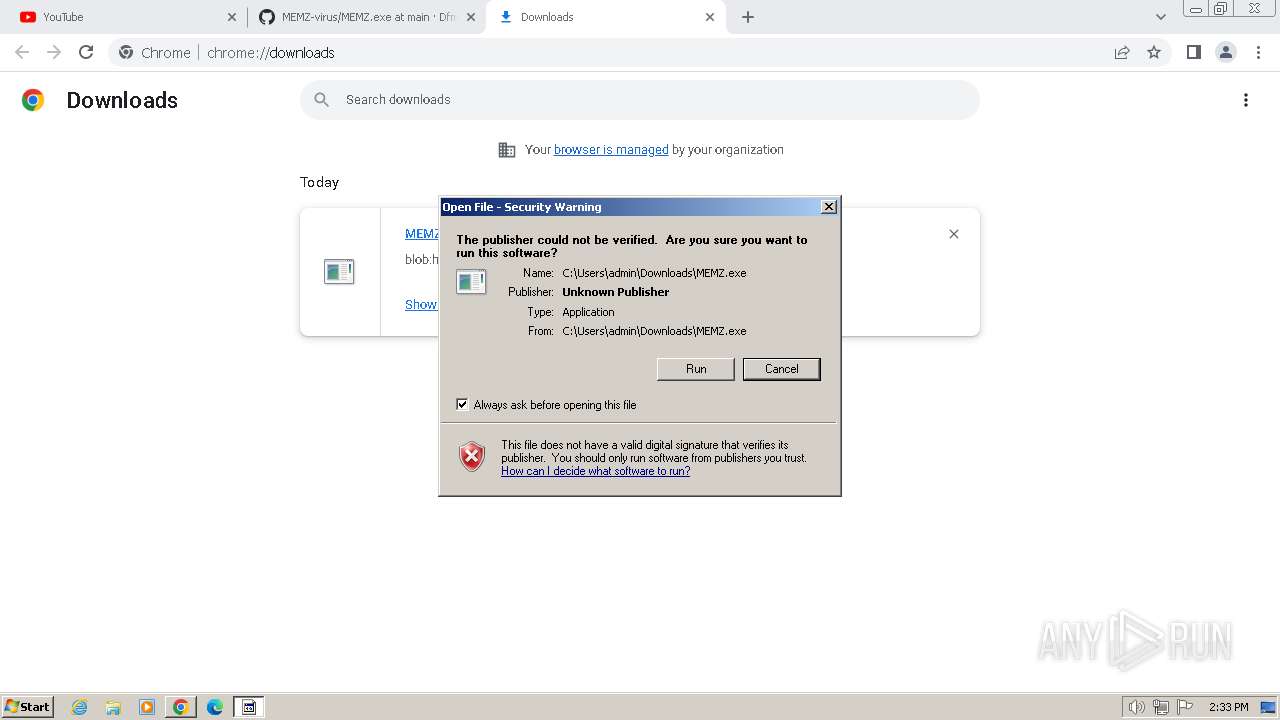
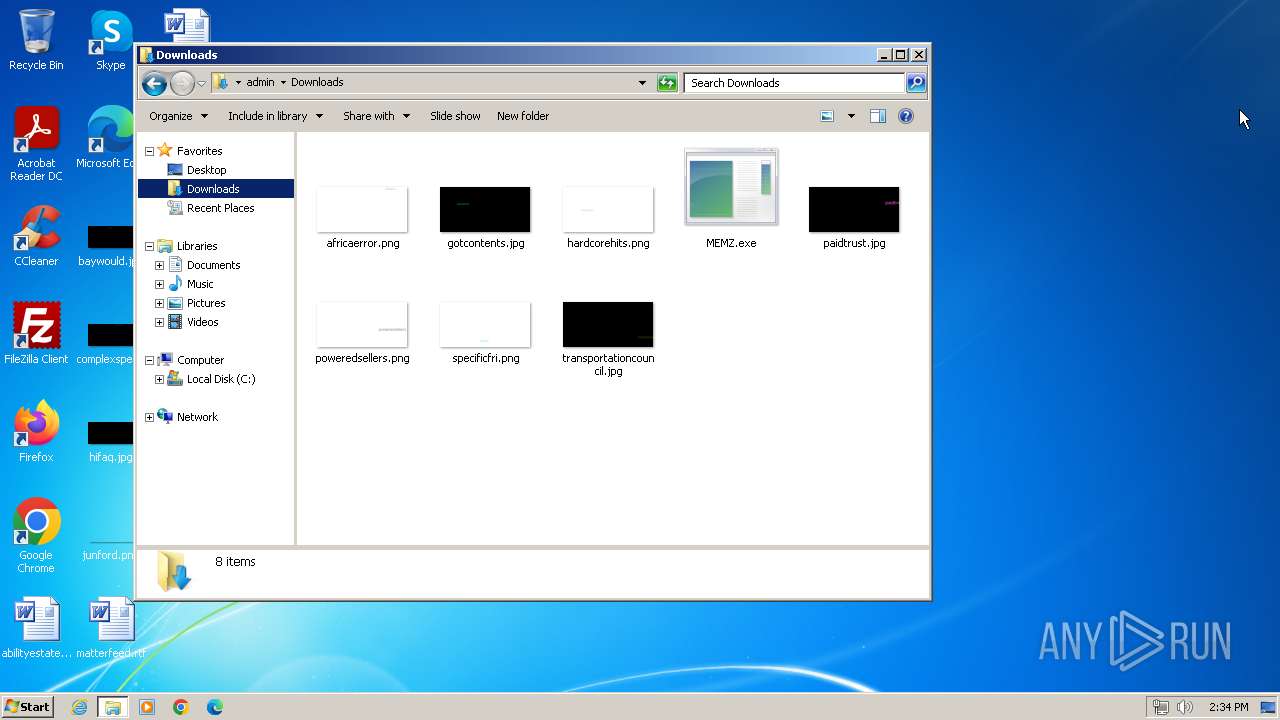
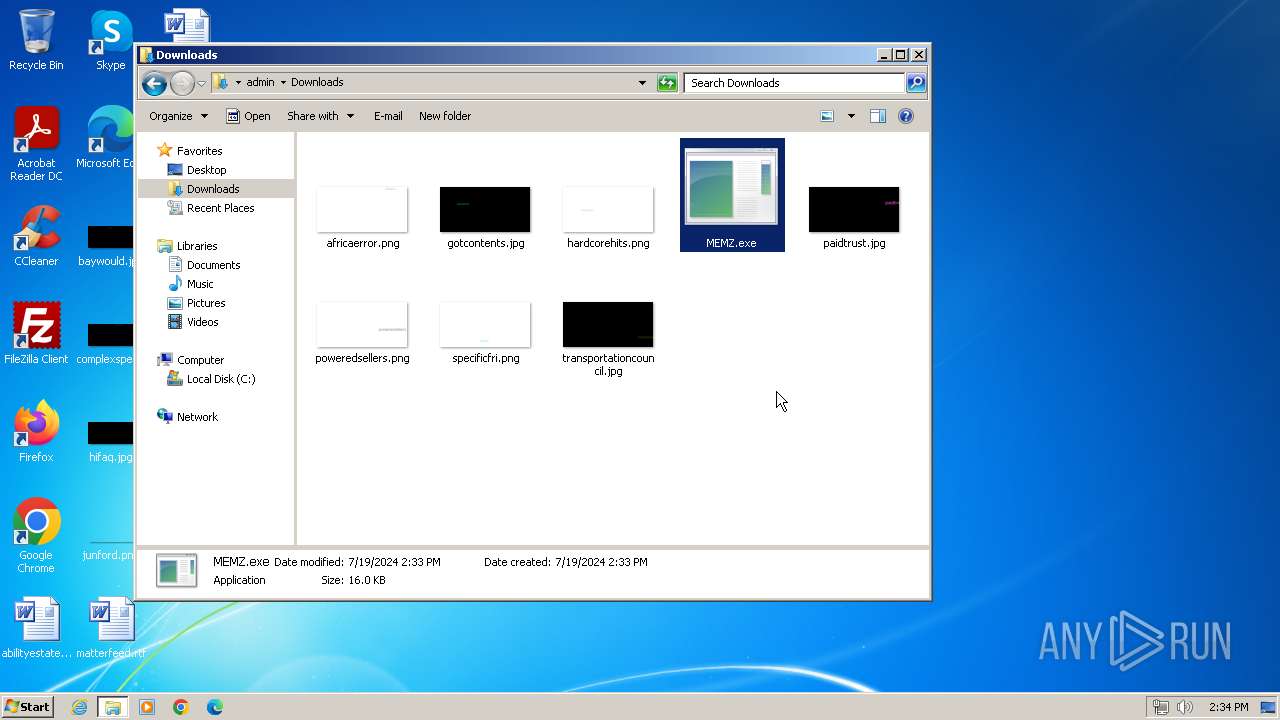
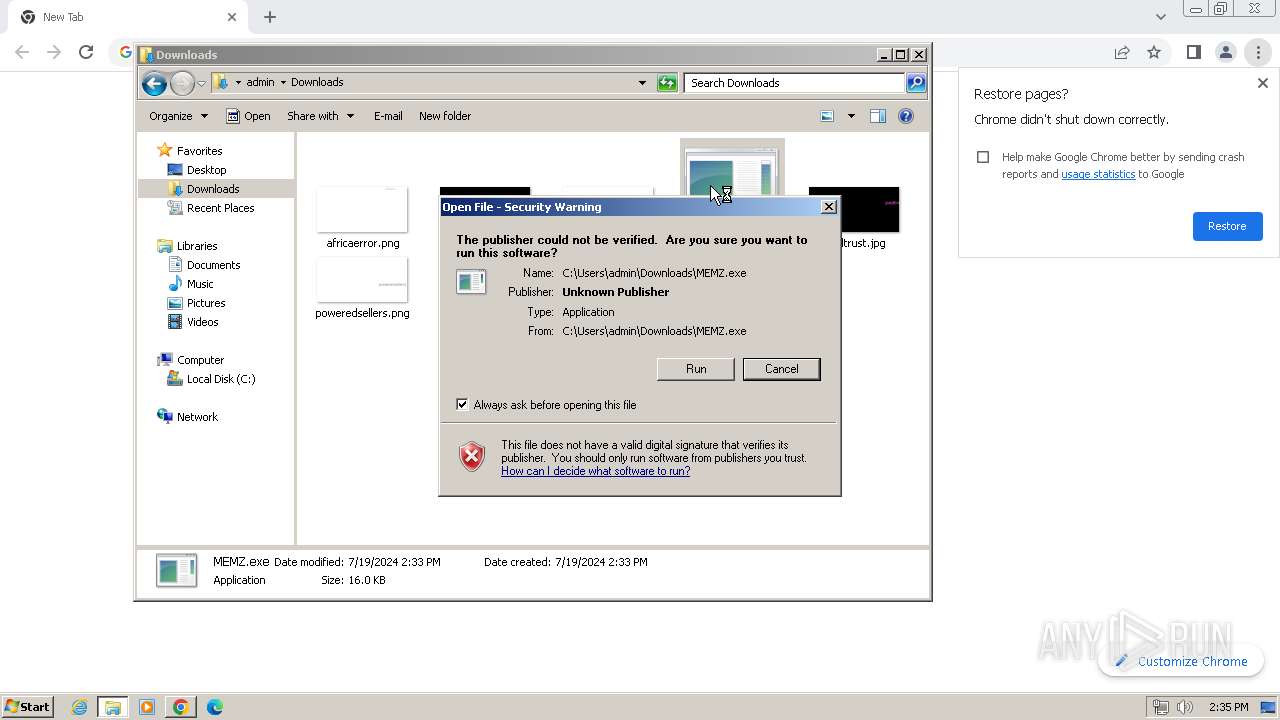
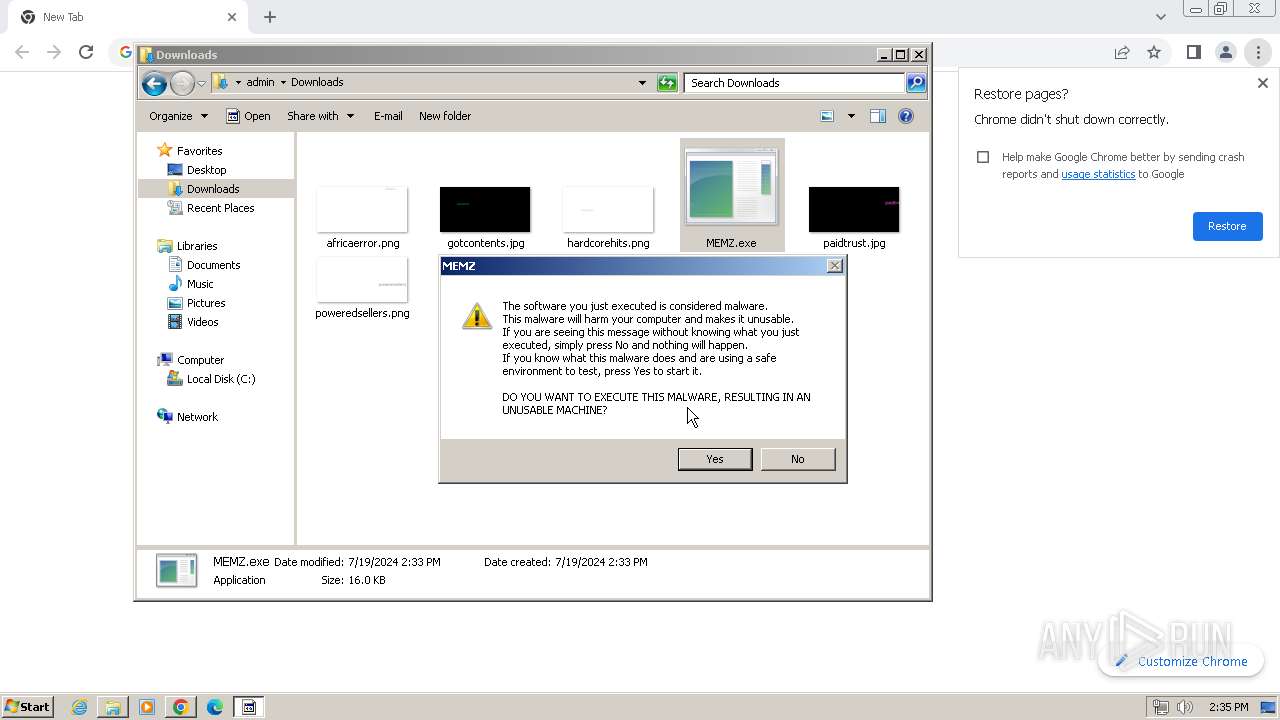
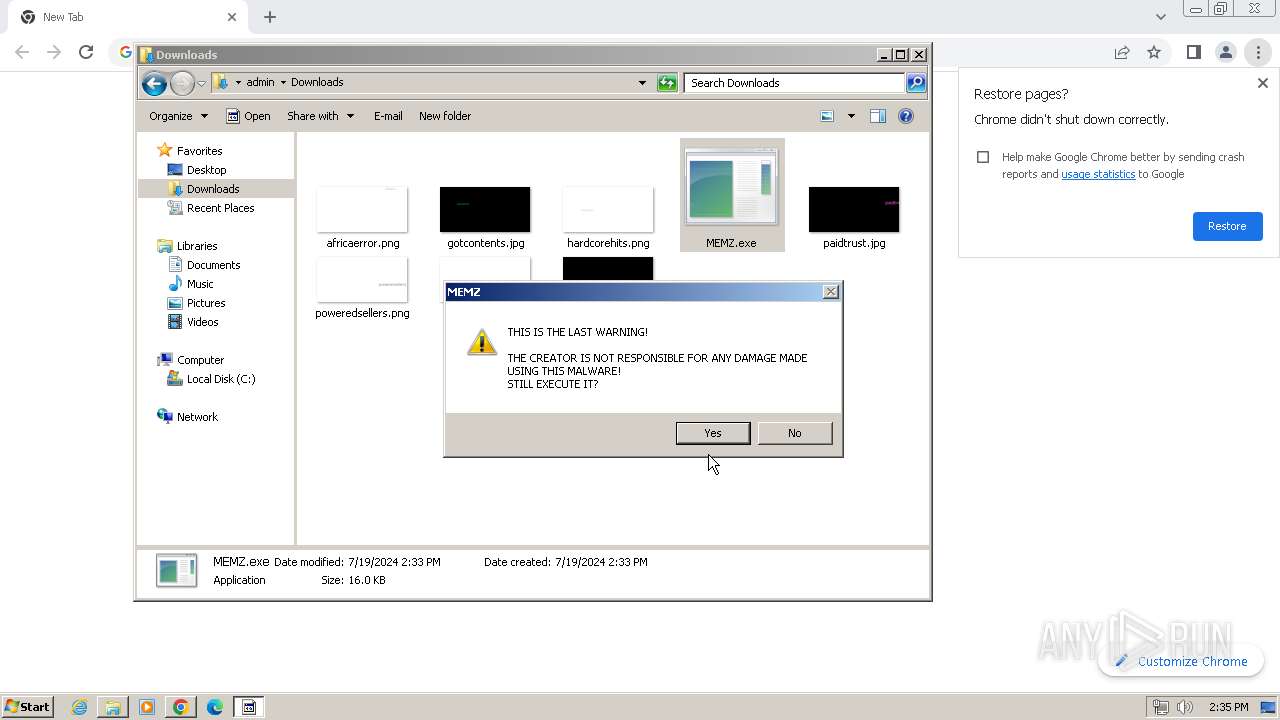
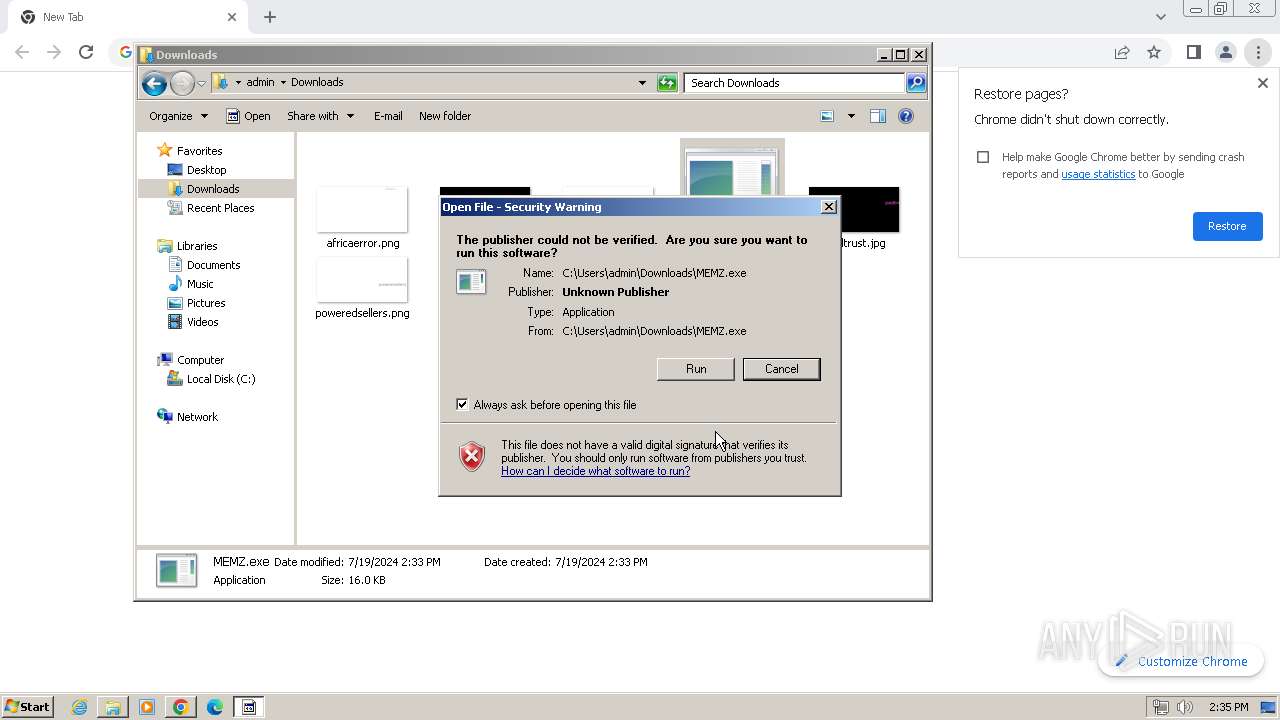
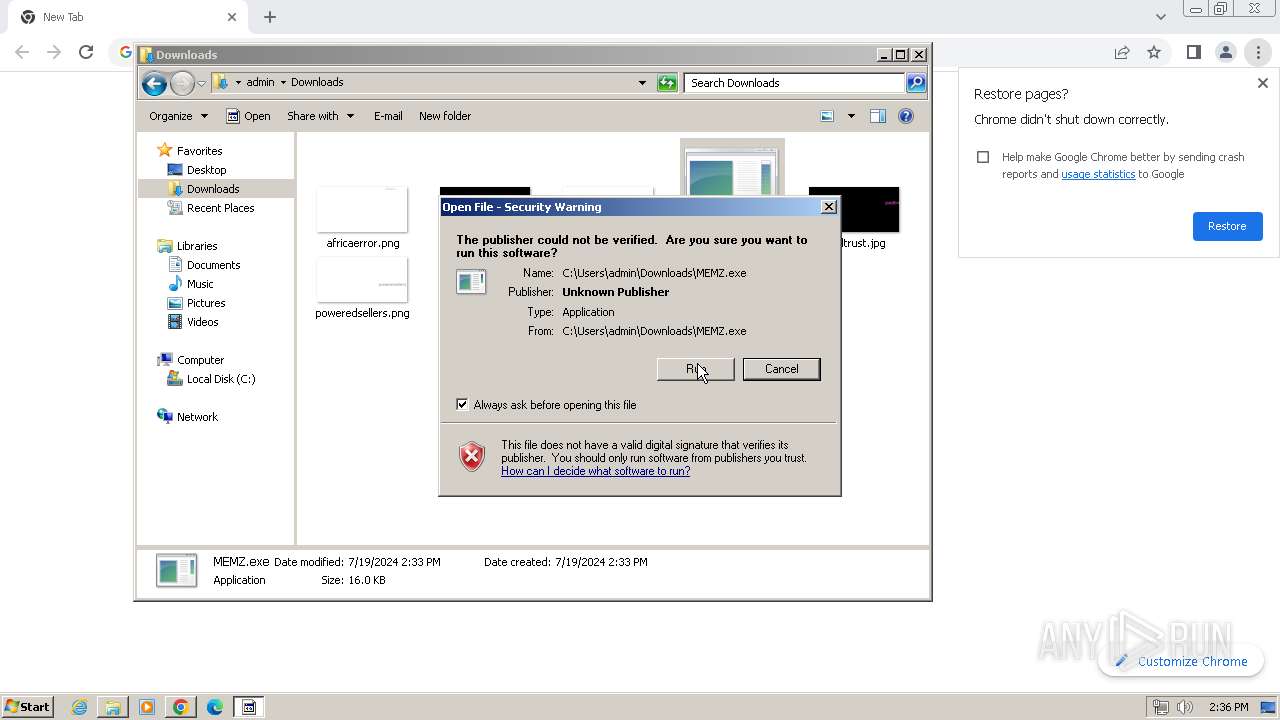
| File name: | MEMZ.exe |
| Full analysis: | https://app.any.run/tasks/f5511d62-ae41-487f-9ace-01ecff46a0e1 |
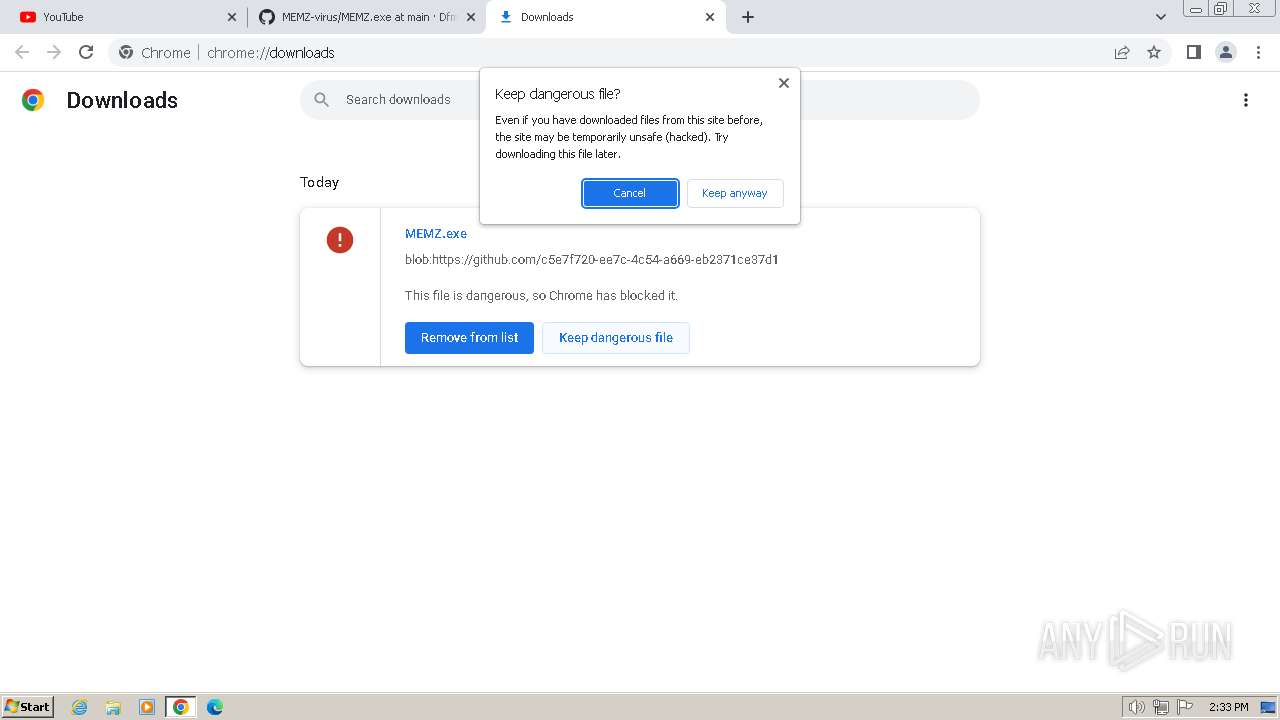
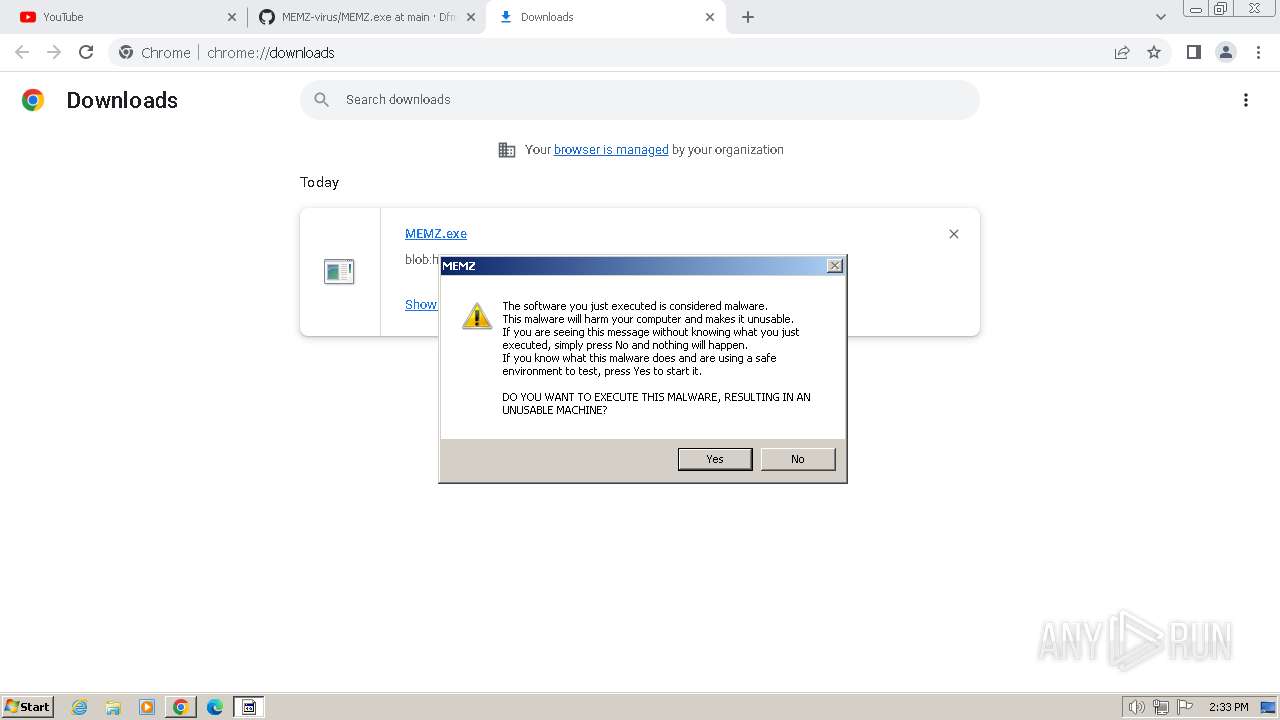
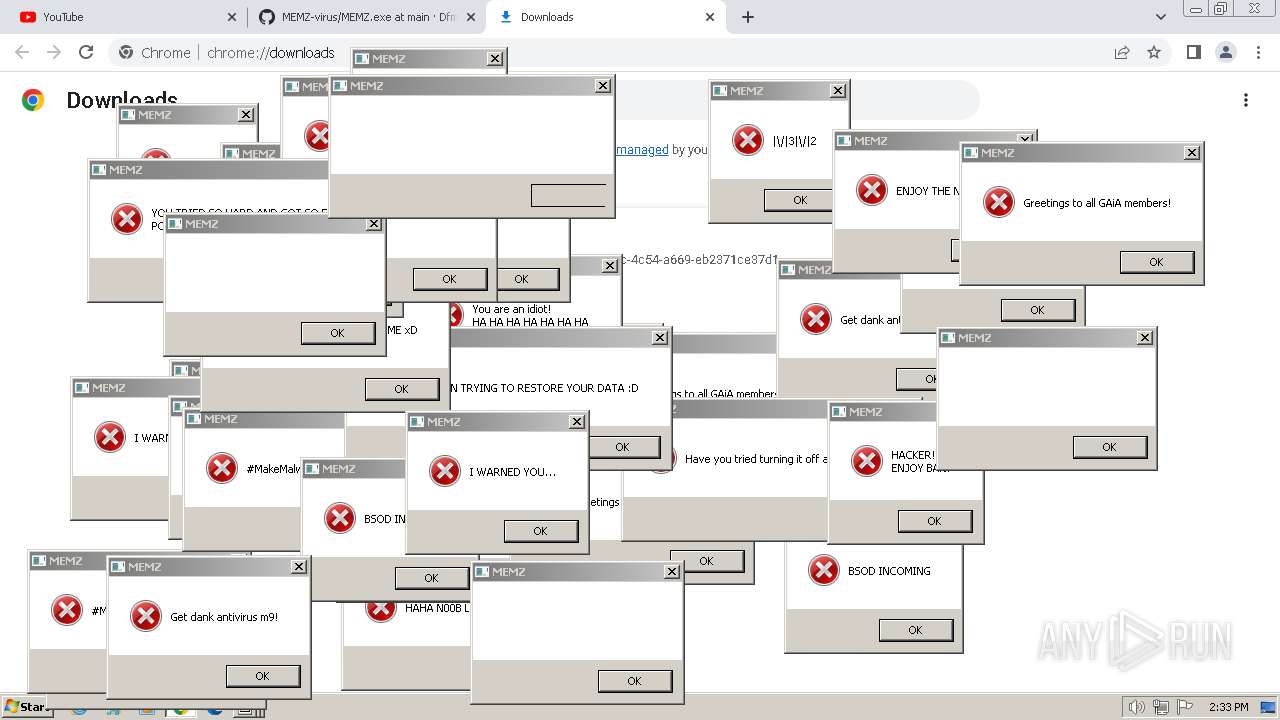
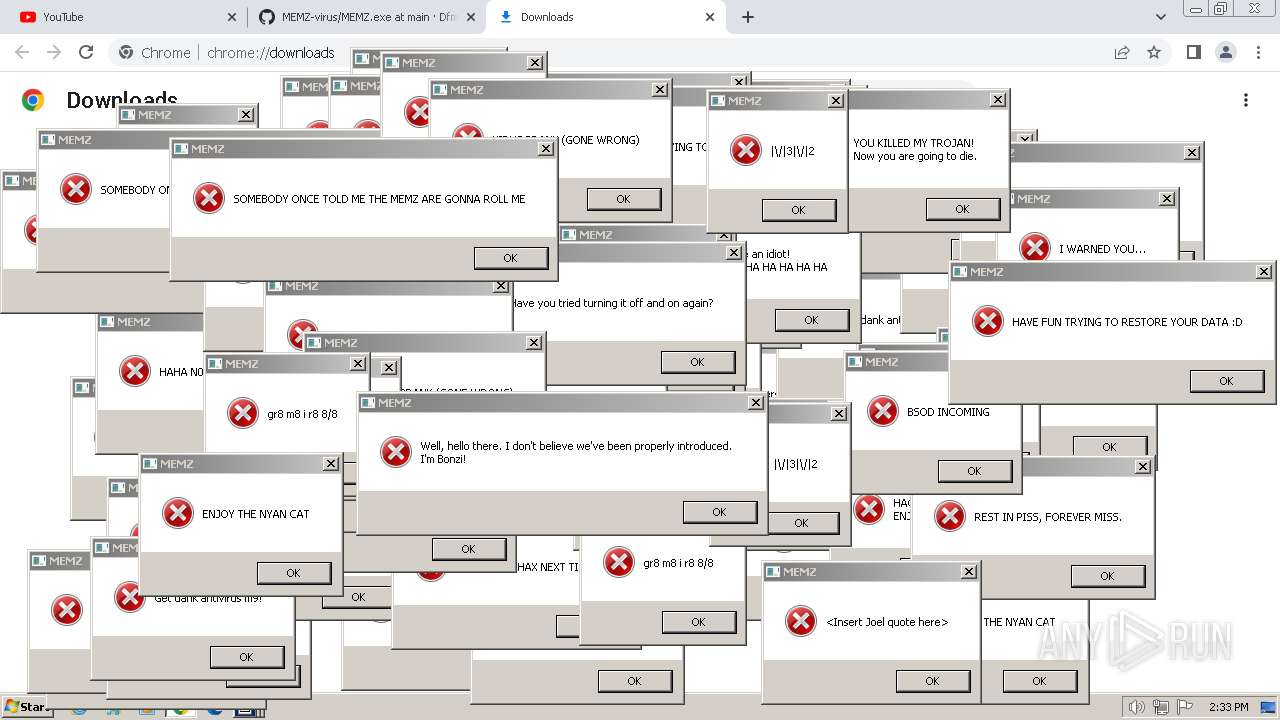
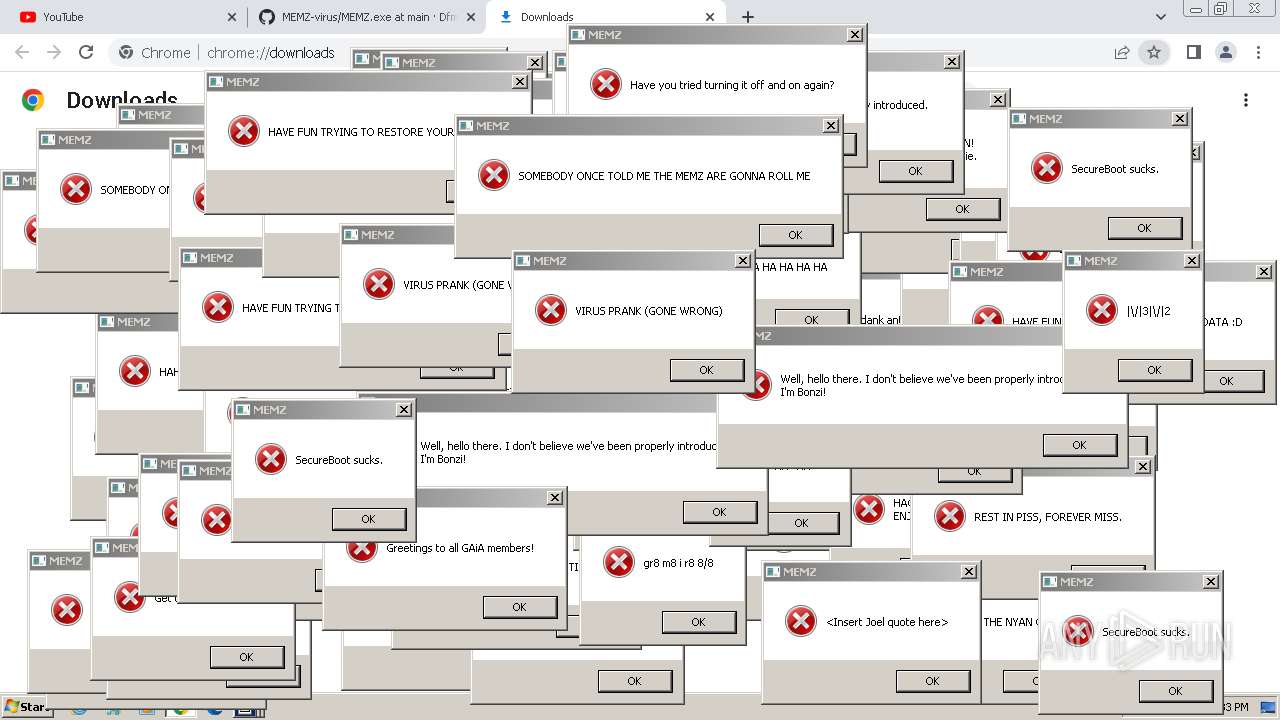
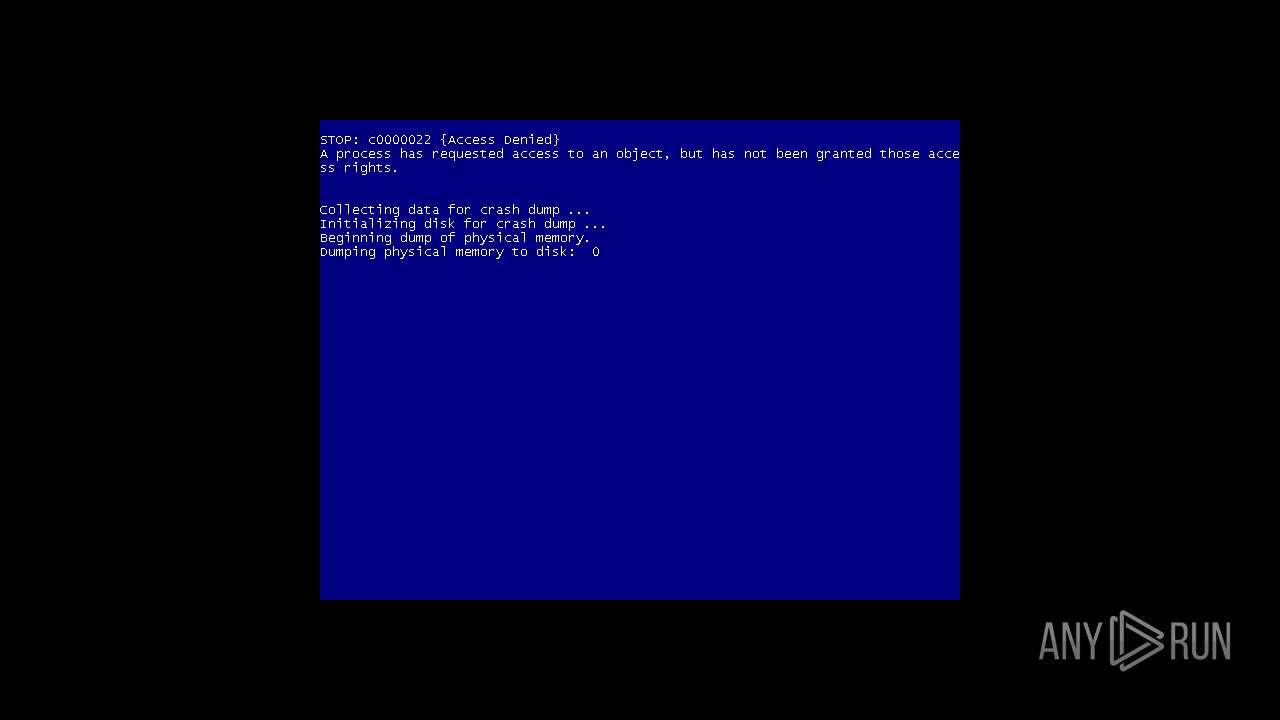
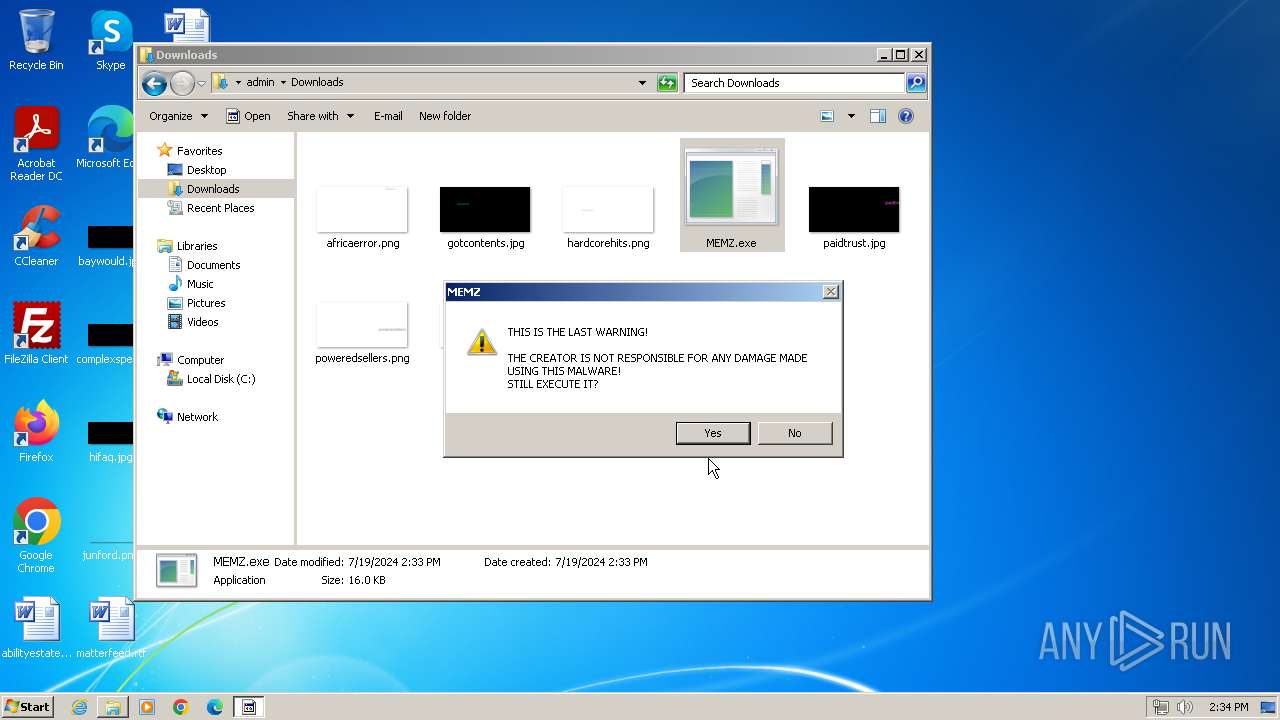
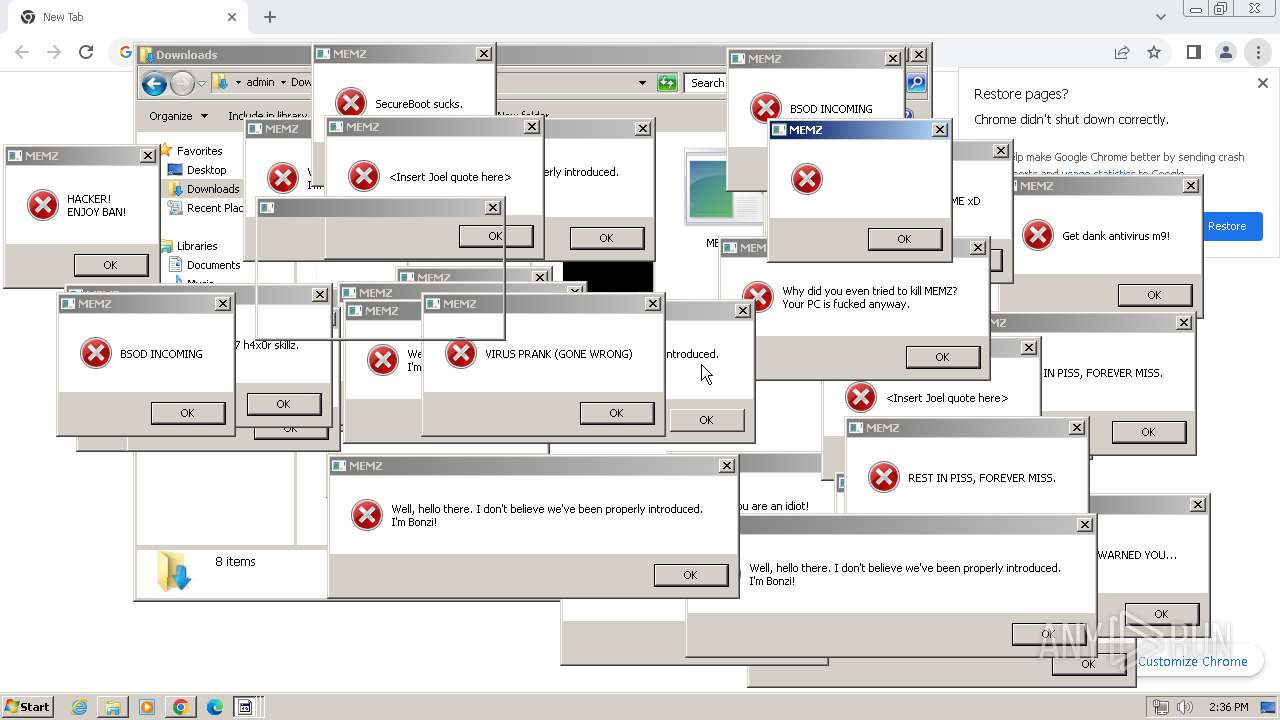
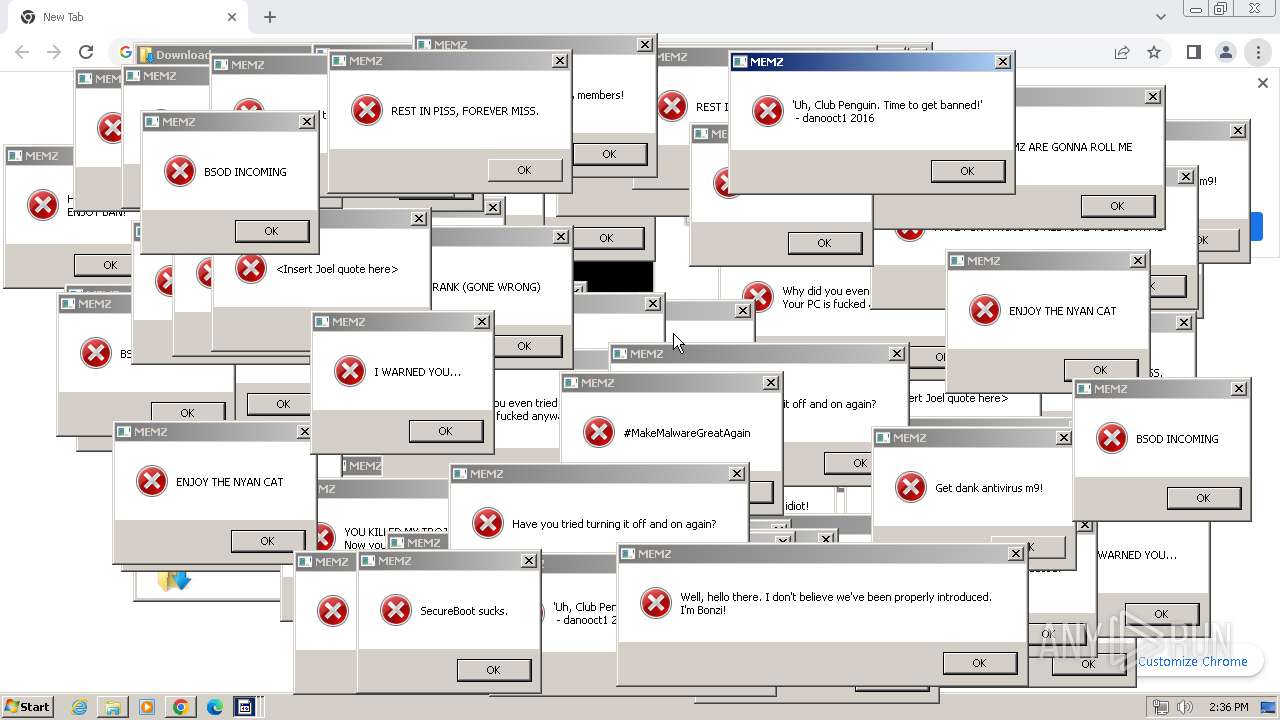
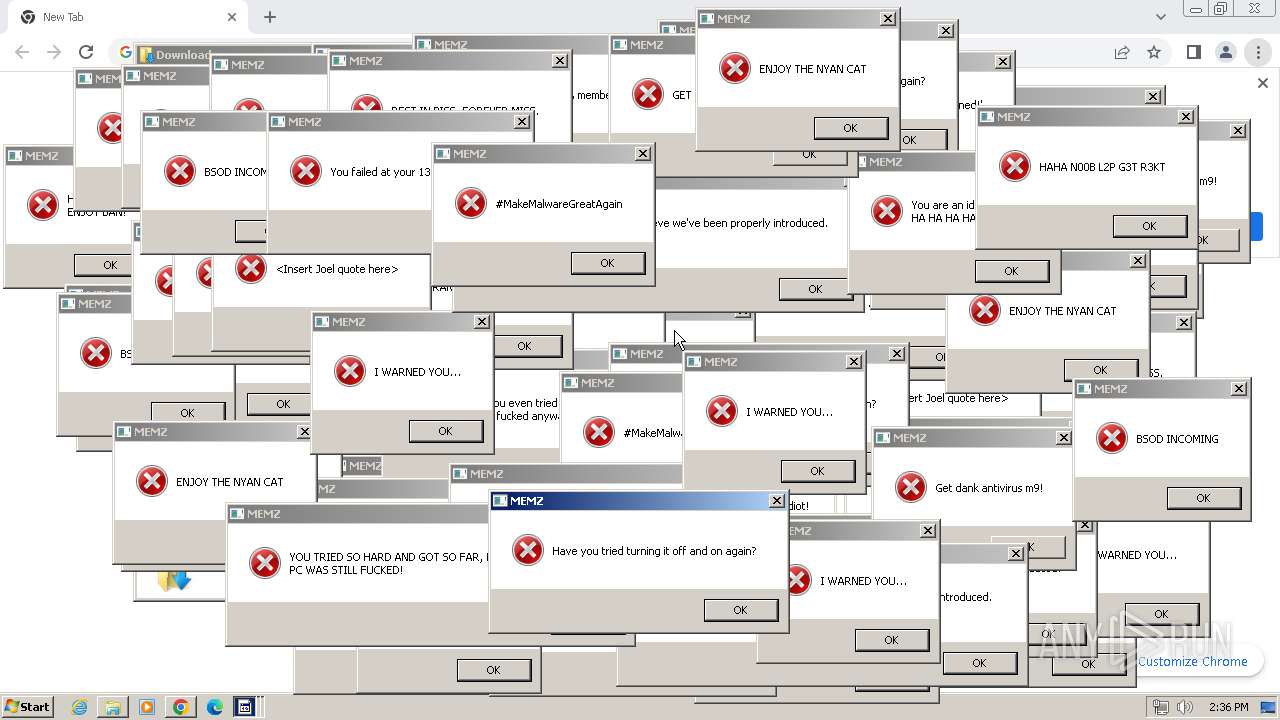
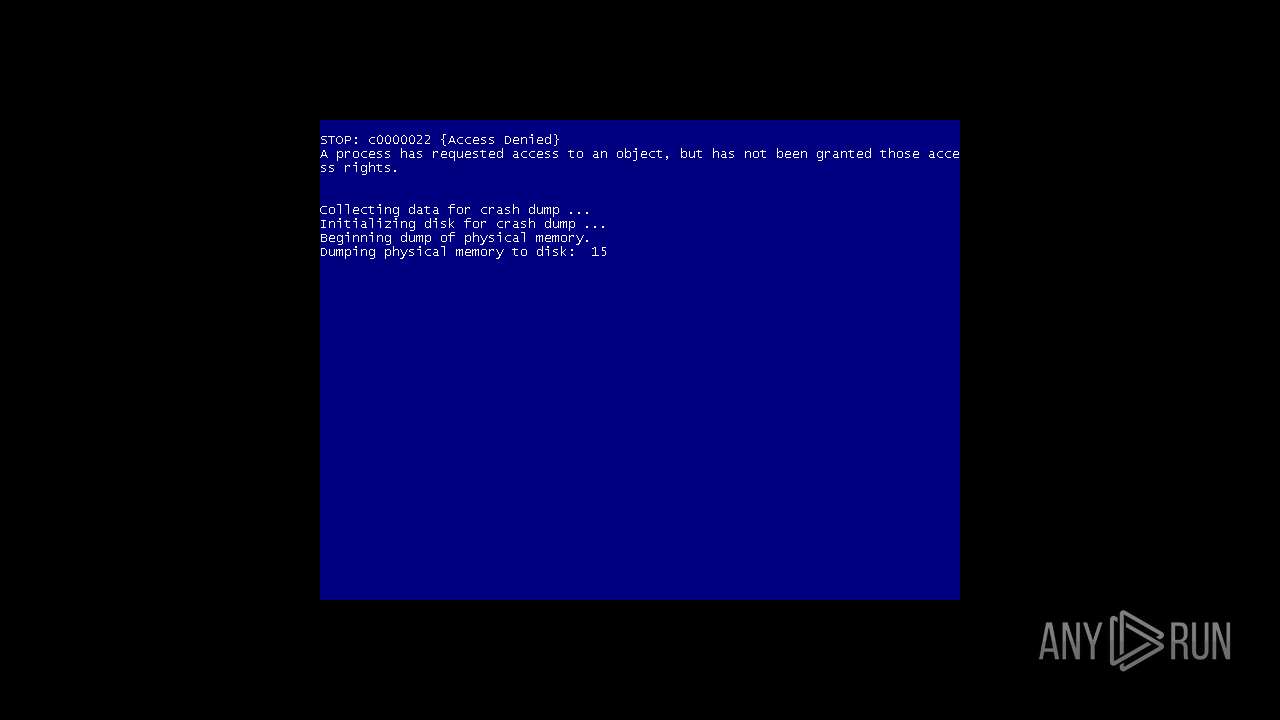
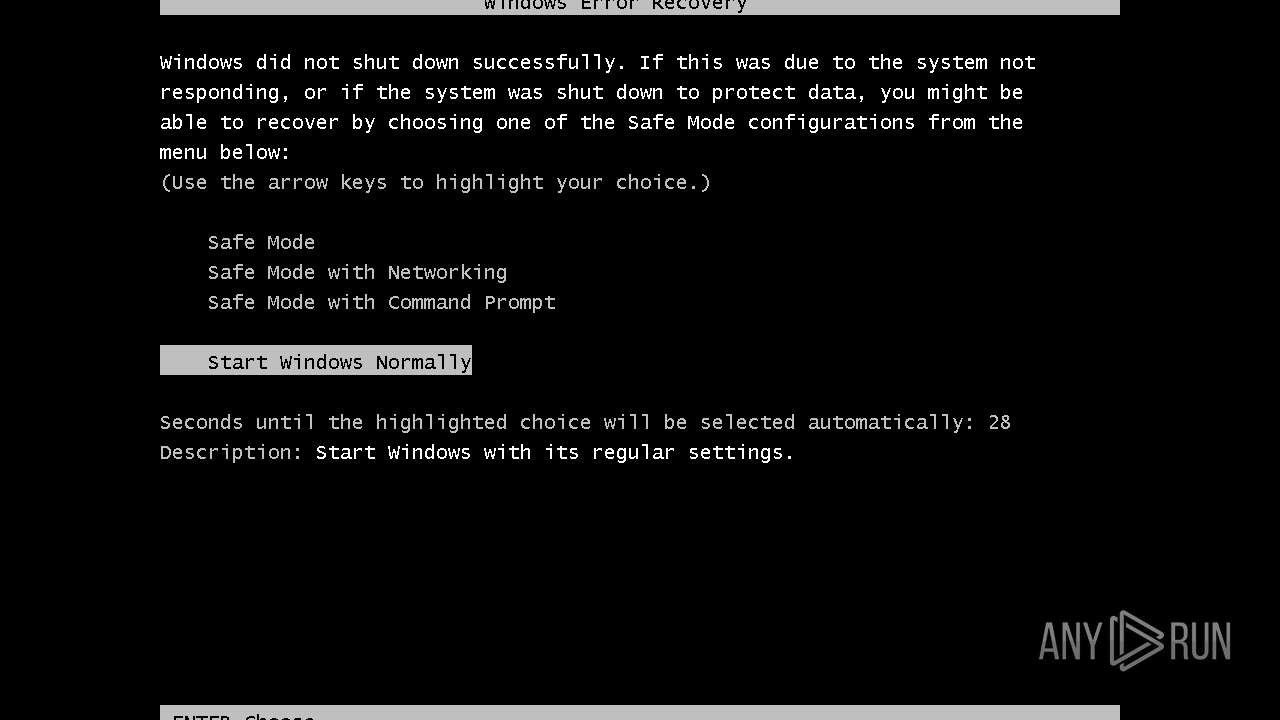
| Verdict: | Malicious activity |
| Analysis date: | July 19, 2024, 13:31:34 |
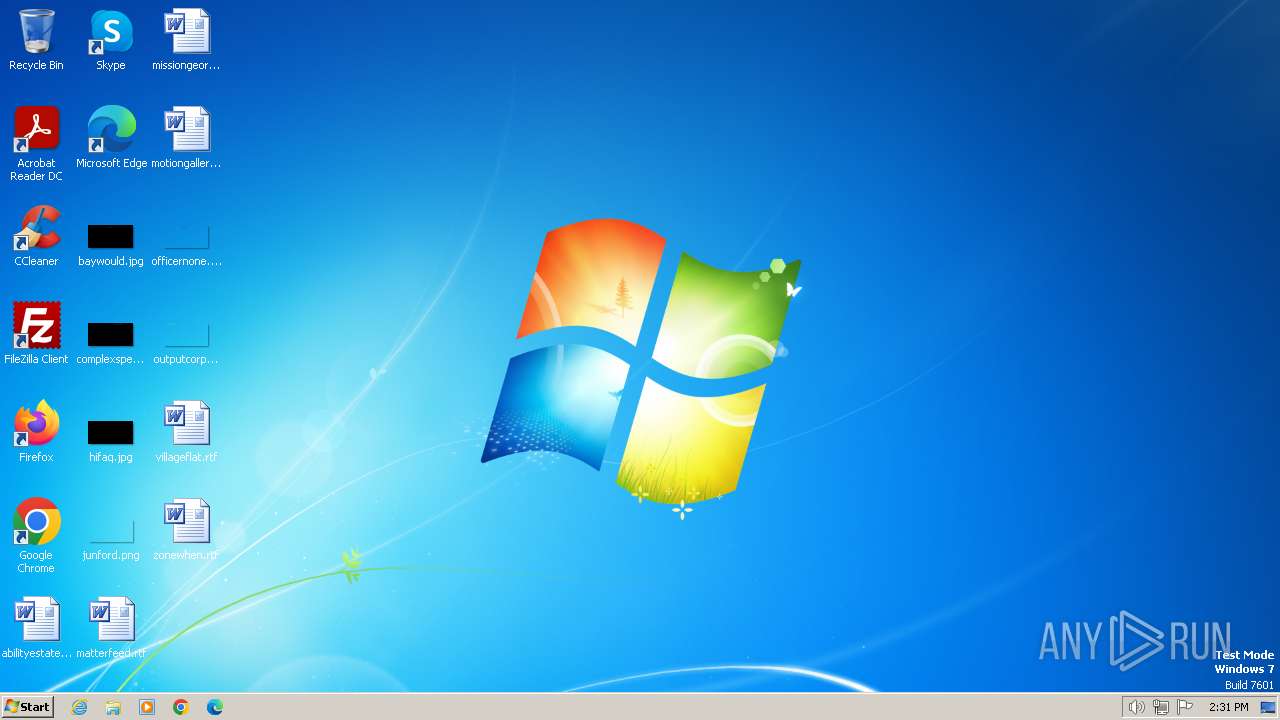
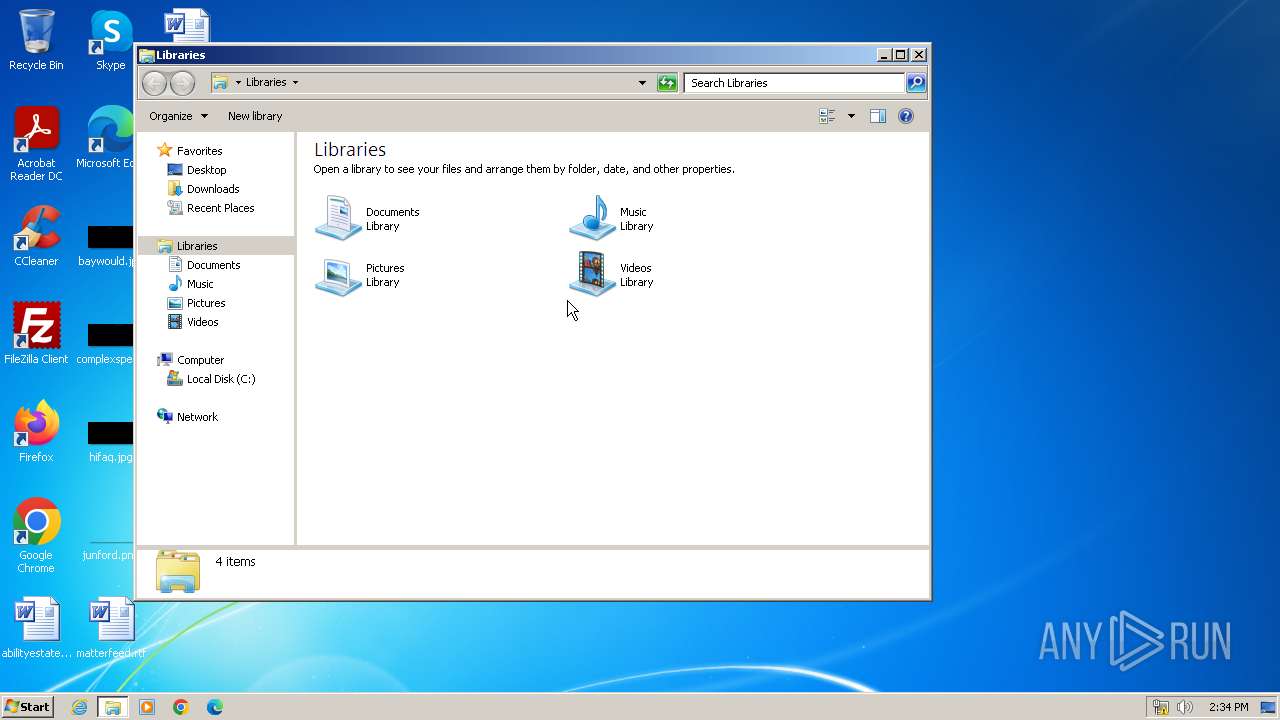
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, Unicode text, UTF-8 text, with very long lines (1531) |
| MD5: | ABBE9B37723BFF126030D2E29A276014 |
| SHA1: | 1EAFC754764C62D560738BA50112715E91F7116E |
| SHA256: | B5637244618FE0DD13BA8ED7CBC43E36C3818D237617CFCADF7549881A655A84 |
| SSDEEP: | 6144:JcWt46eOeLAJ0jRM14CJmSCvZJT3CqbMrhryf65NRPaCieMjAkvCJv1Vi0Zmzdvk:JZt46eOeLAJ0jRM14CJmSCvZJT3CqQrj |
MALICIOUS
No malicious indicators.SUSPICIOUS
Creates file in the systems drive root
- ntvdm.exe (PID: 3392)
Reads security settings of Internet Explorer
- MEMZ.exe (PID: 3596)
- MEMZ.exe (PID: 2944)
- MEMZ.exe (PID: 2376)
Reads the Internet Settings
- MEMZ.exe (PID: 3596)
- sipnotify.exe (PID: 1780)
- runonce.exe (PID: 2068)
- MEMZ.exe (PID: 2944)
- MEMZ.exe (PID: 2376)
- sipnotify.exe (PID: 2072)
- runonce.exe (PID: 2148)
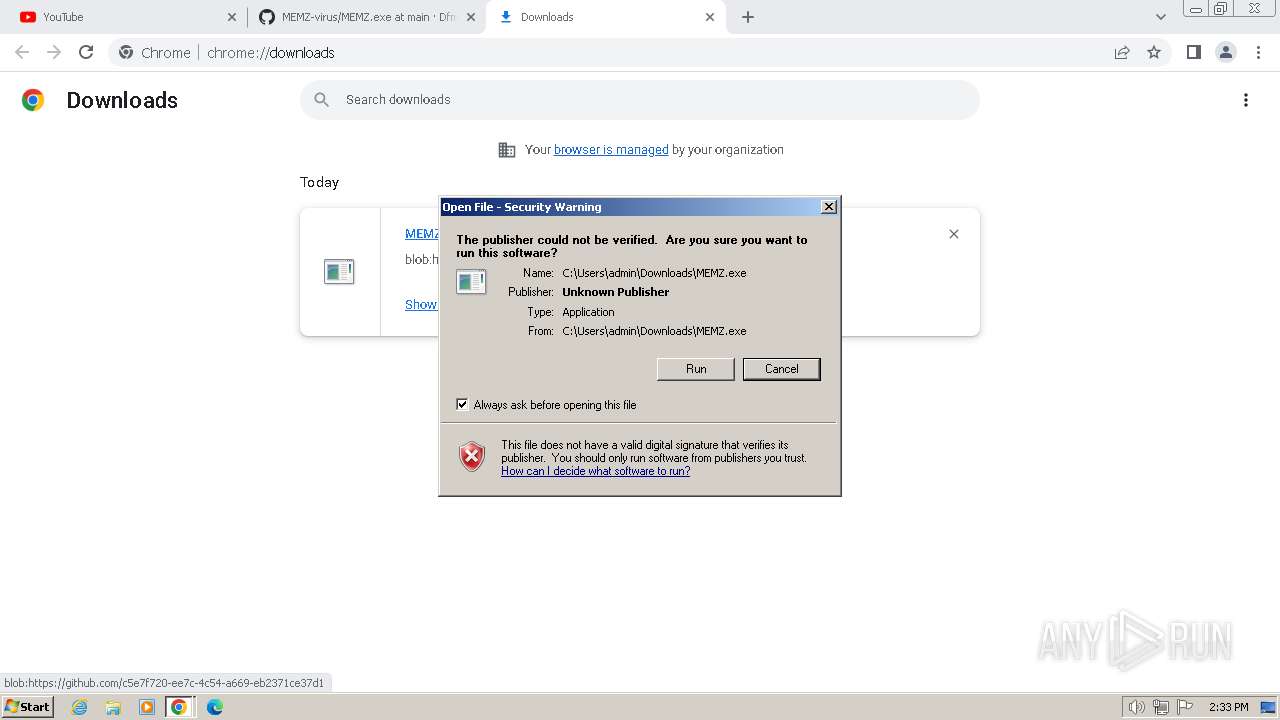
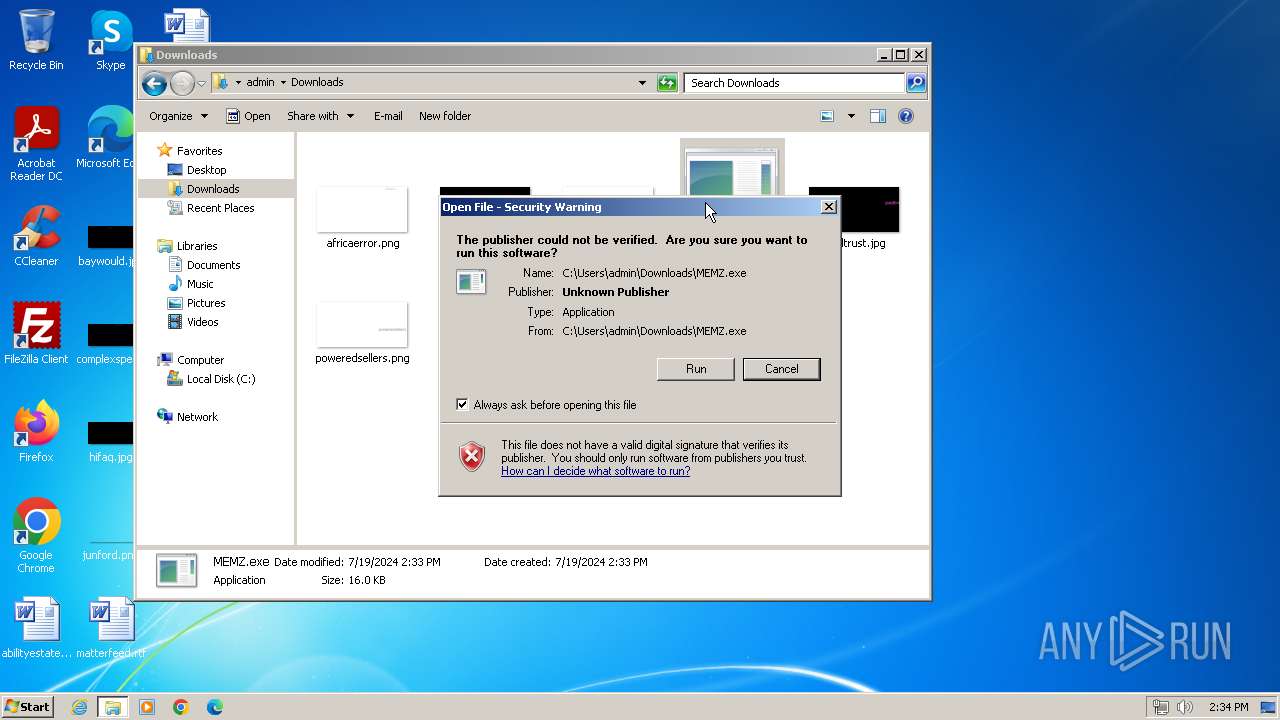
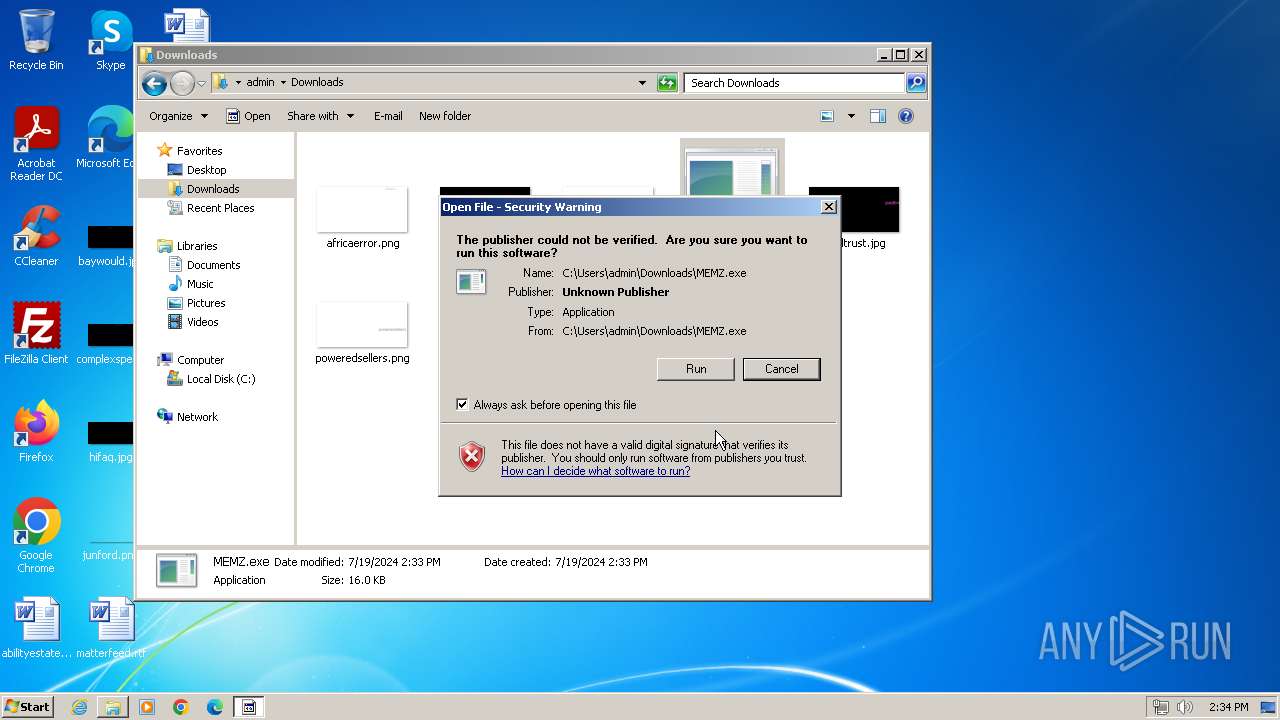
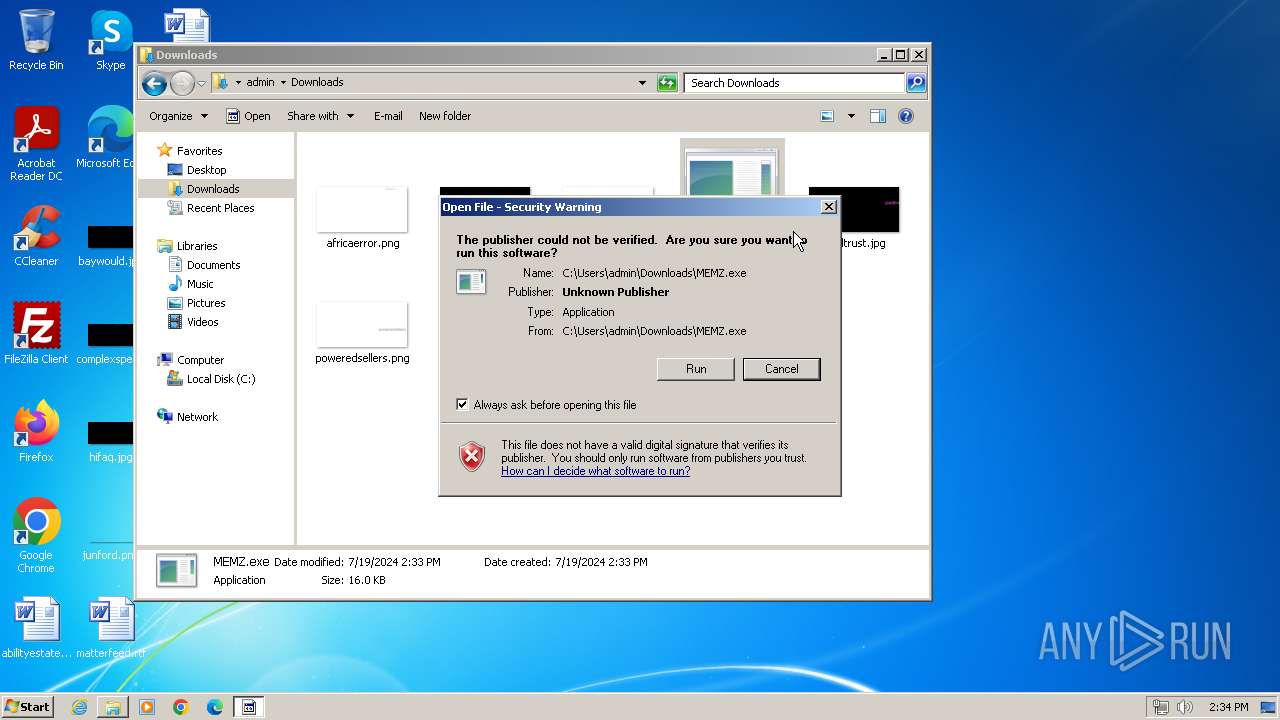
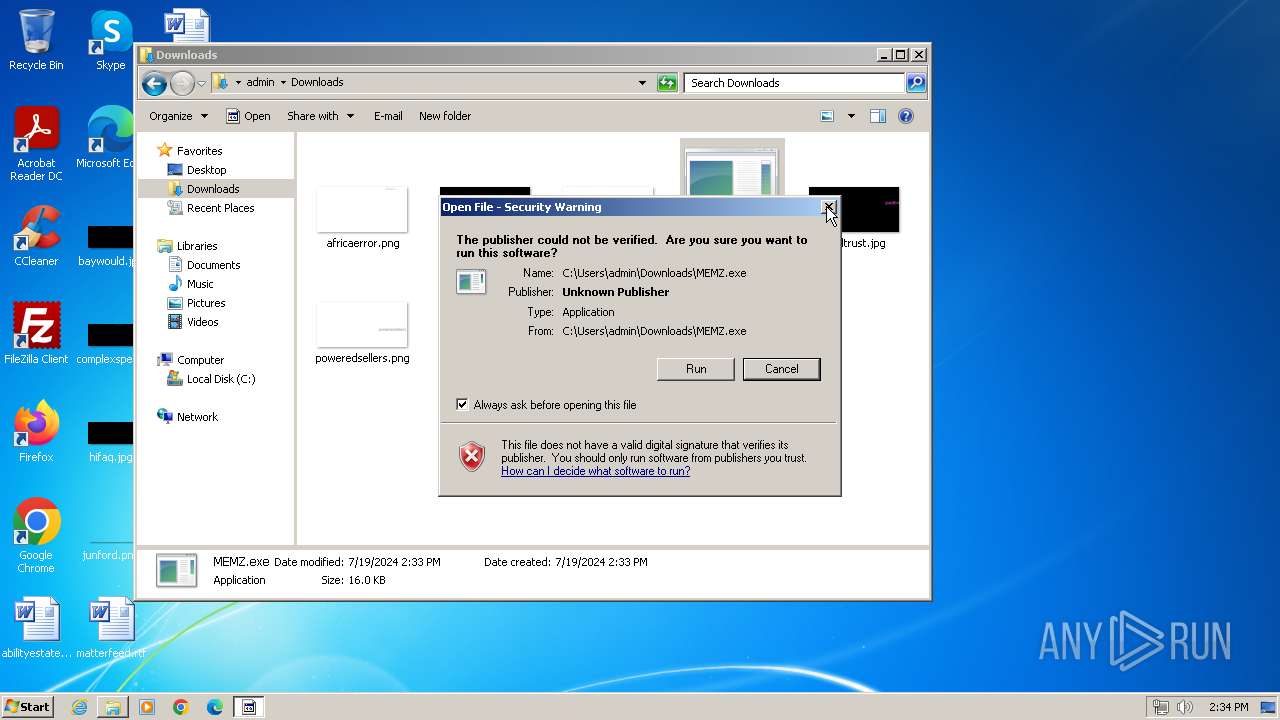
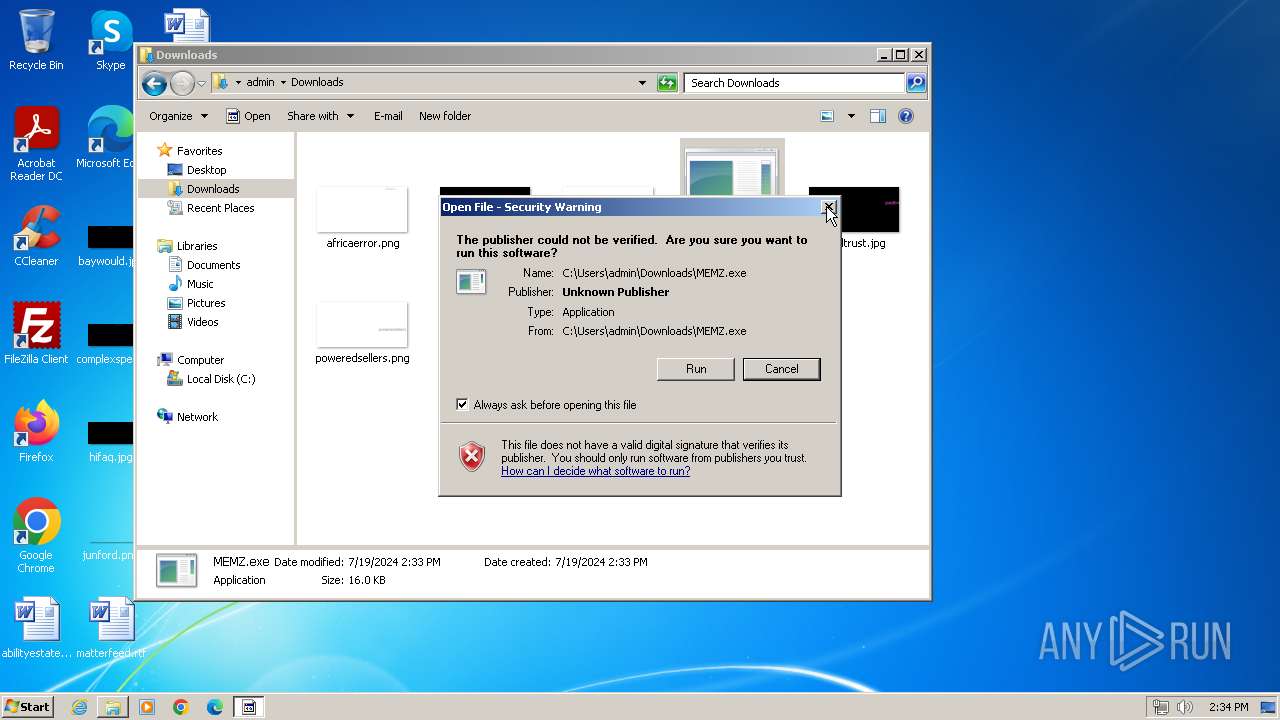
Checks Windows Trust Settings
- MEMZ.exe (PID: 3596)
- MEMZ.exe (PID: 2944)
- MEMZ.exe (PID: 2376)
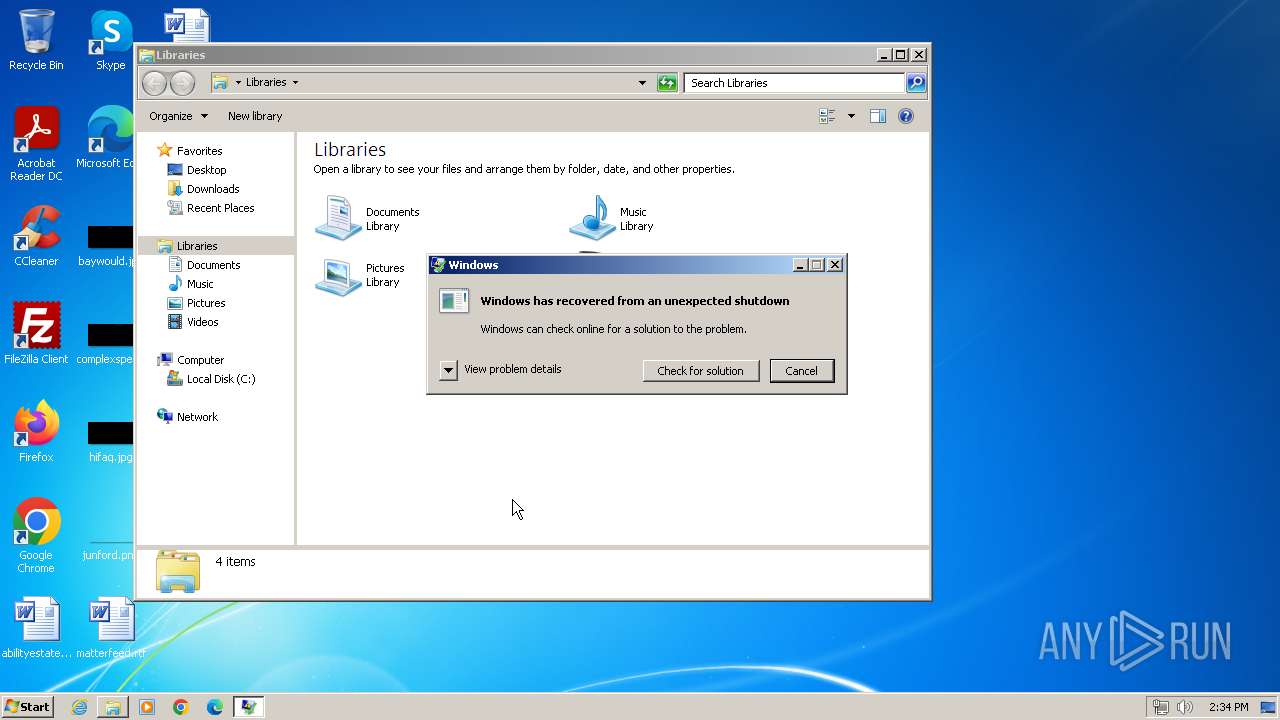
Application launched itself
- MEMZ.exe (PID: 3596)
- WerFault.exe (PID: 2100)
- MEMZ.exe (PID: 2376)
- WerFault.exe (PID: 2172)
The process executes via Task Scheduler
- ctfmon.exe (PID: 1744)
- sipnotify.exe (PID: 1780)
- ctfmon.exe (PID: 1360)
- sipnotify.exe (PID: 2072)
Reads settings of System Certificates
- sipnotify.exe (PID: 1780)
- sipnotify.exe (PID: 2072)
INFO
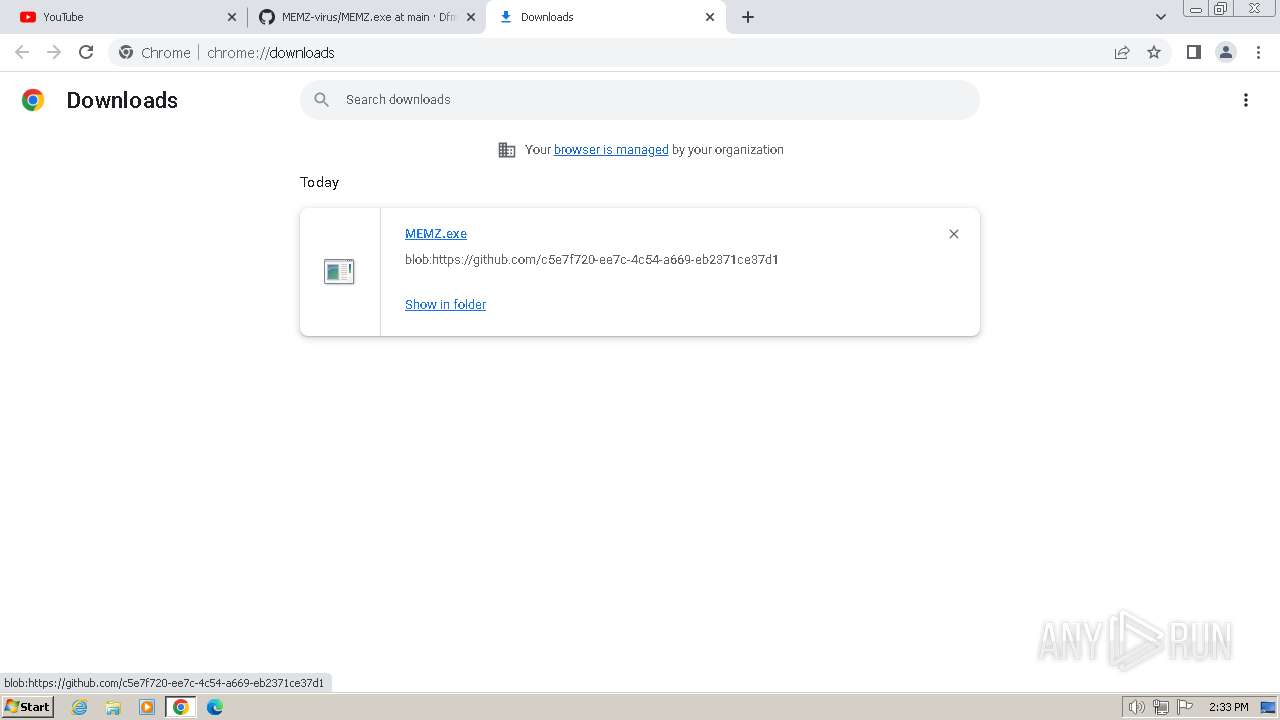
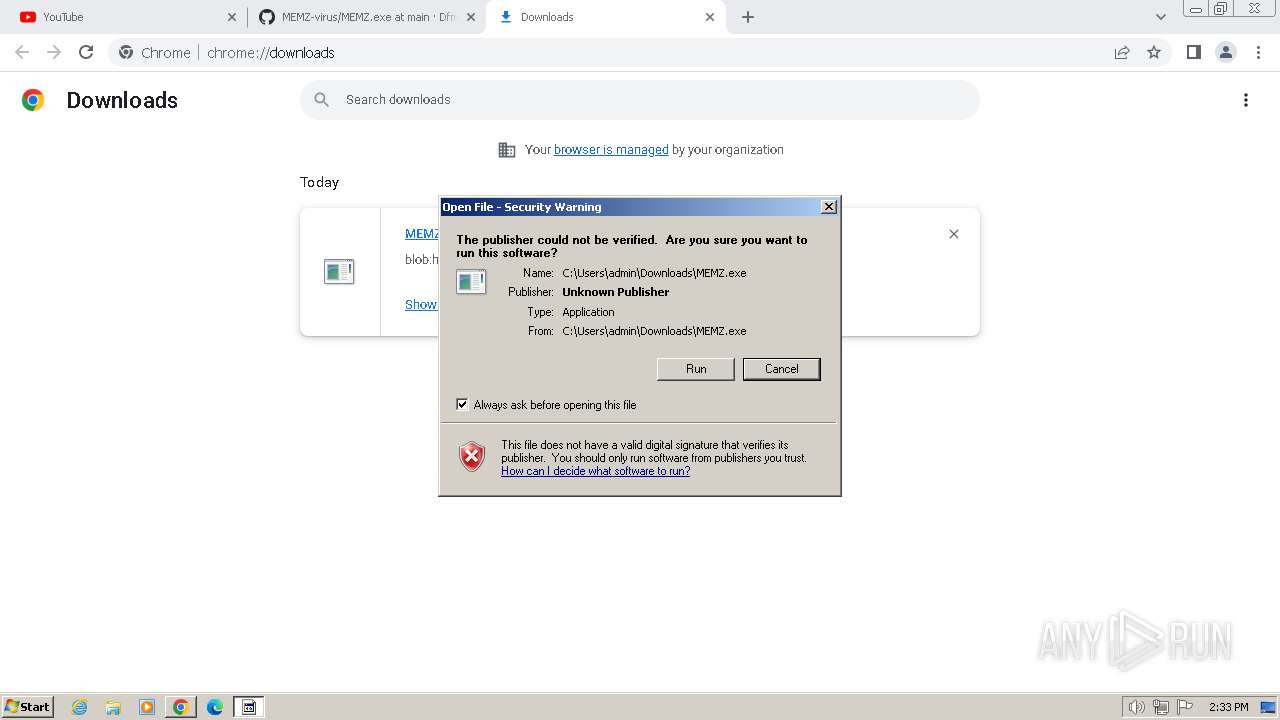
Drops the executable file immediately after the start
- chrome.exe (PID: 680)
Manual execution by a user
- chrome.exe (PID: 680)
- runonce.exe (PID: 2068)
- explorer.exe (PID: 2684)
- wmpnscfg.exe (PID: 2532)
- wmpnscfg.exe (PID: 2556)
- wmpnscfg.exe (PID: 2772)
- IMEKLMG.EXE (PID: 2200)
- IMEKLMG.EXE (PID: 2208)
- MEMZ.exe (PID: 2376)
- wmpnscfg.exe (PID: 3036)
- chrome.exe (PID: 3108)
- explorer.exe (PID: 3664)
- MEMZ.exe (PID: 2944)
- runonce.exe (PID: 2148)
- IMEKLMG.EXE (PID: 2268)
- IMEKLMG.EXE (PID: 2260)
Checks supported languages
- MEMZ.exe (PID: 3596)
- MEMZ.exe (PID: 368)
- MEMZ.exe (PID: 580)
- MEMZ.exe (PID: 1968)
- MEMZ.exe (PID: 2632)
- MEMZ.exe (PID: 3600)
- MEMZ.exe (PID: 2248)
- IMEKLMG.EXE (PID: 2208)
- wmpnscfg.exe (PID: 2532)
- wmpnscfg.exe (PID: 2556)
- IMEKLMG.EXE (PID: 2200)
- wmpnscfg.exe (PID: 2772)
- MEMZ.exe (PID: 2944)
- wmpnscfg.exe (PID: 3036)
- MEMZ.exe (PID: 2376)
- MEMZ.exe (PID: 2308)
- MEMZ.exe (PID: 2264)
- MEMZ.exe (PID: 2456)
- MEMZ.exe (PID: 2292)
- MEMZ.exe (PID: 1432)
- MEMZ.exe (PID: 2244)
- IMEKLMG.EXE (PID: 2260)
- IMEKLMG.EXE (PID: 2268)
Reads the computer name
- MEMZ.exe (PID: 3596)
- IMEKLMG.EXE (PID: 2200)
- IMEKLMG.EXE (PID: 2208)
- wmpnscfg.exe (PID: 2532)
- wmpnscfg.exe (PID: 2556)
- wmpnscfg.exe (PID: 2772)
- MEMZ.exe (PID: 2376)
- MEMZ.exe (PID: 2944)
- wmpnscfg.exe (PID: 3036)
- IMEKLMG.EXE (PID: 2268)
- IMEKLMG.EXE (PID: 2260)
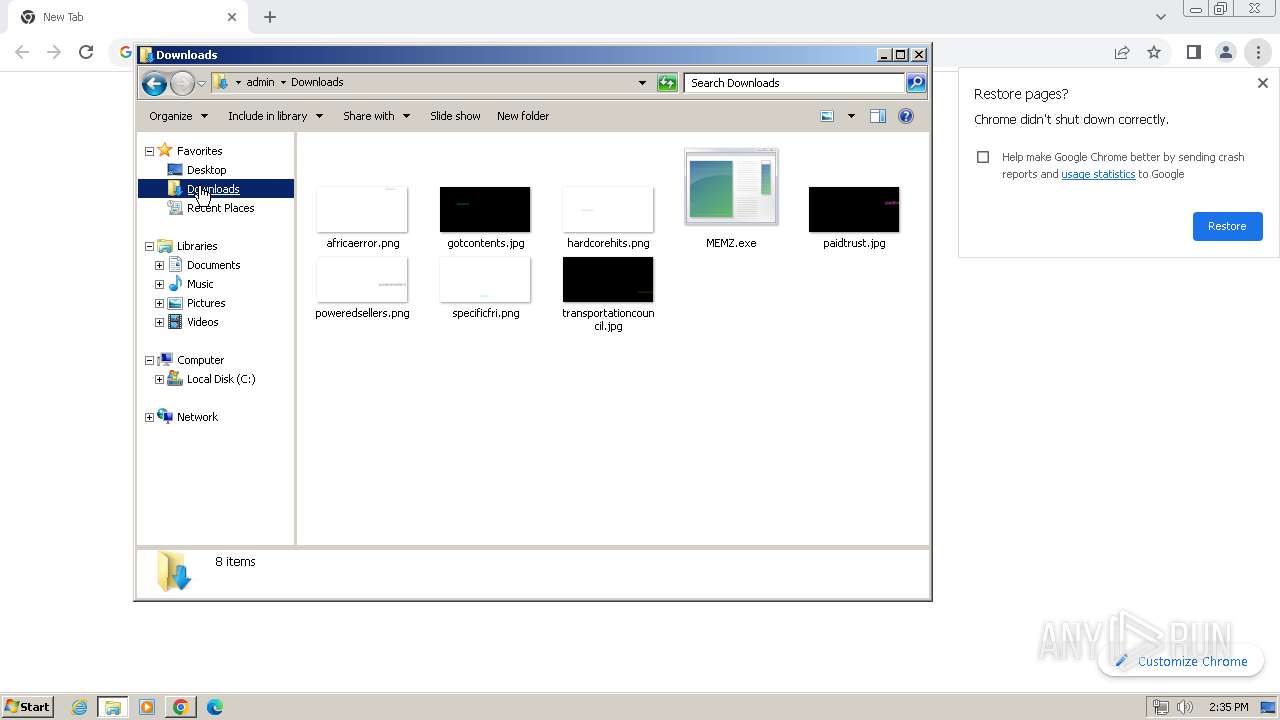
The process uses the downloaded file
- chrome.exe (PID: 1920)
- chrome.exe (PID: 680)
- MEMZ.exe (PID: 3596)
- MEMZ.exe (PID: 2944)
- MEMZ.exe (PID: 2376)
Executable content was dropped or overwritten
- chrome.exe (PID: 680)
Reads the machine GUID from the registry
- MEMZ.exe (PID: 3596)
- MEMZ.exe (PID: 580)
- MEMZ.exe (PID: 1968)
- MEMZ.exe (PID: 368)
- MEMZ.exe (PID: 3600)
- MEMZ.exe (PID: 2632)
- MEMZ.exe (PID: 2944)
- MEMZ.exe (PID: 2376)
- MEMZ.exe (PID: 2456)
- MEMZ.exe (PID: 2292)
- MEMZ.exe (PID: 2308)
- MEMZ.exe (PID: 1432)
Reads security settings of Internet Explorer
- runonce.exe (PID: 2068)
- sipnotify.exe (PID: 1780)
- runonce.exe (PID: 2148)
- sipnotify.exe (PID: 2072)
Reads the time zone
- runonce.exe (PID: 2068)
- runonce.exe (PID: 2148)
Application launched itself
- chrome.exe (PID: 680)
- chrome.exe (PID: 3108)
Process checks whether UAC notifications are on
- IMEKLMG.EXE (PID: 2200)
- IMEKLMG.EXE (PID: 2208)
- IMEKLMG.EXE (PID: 2268)
- IMEKLMG.EXE (PID: 2260)
Reads the software policy settings
- sipnotify.exe (PID: 1780)
- sipnotify.exe (PID: 2072)
Create files in a temporary directory
- WerFault.exe (PID: 2108)
- WerFault.exe (PID: 2180)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
EXIF
HTML
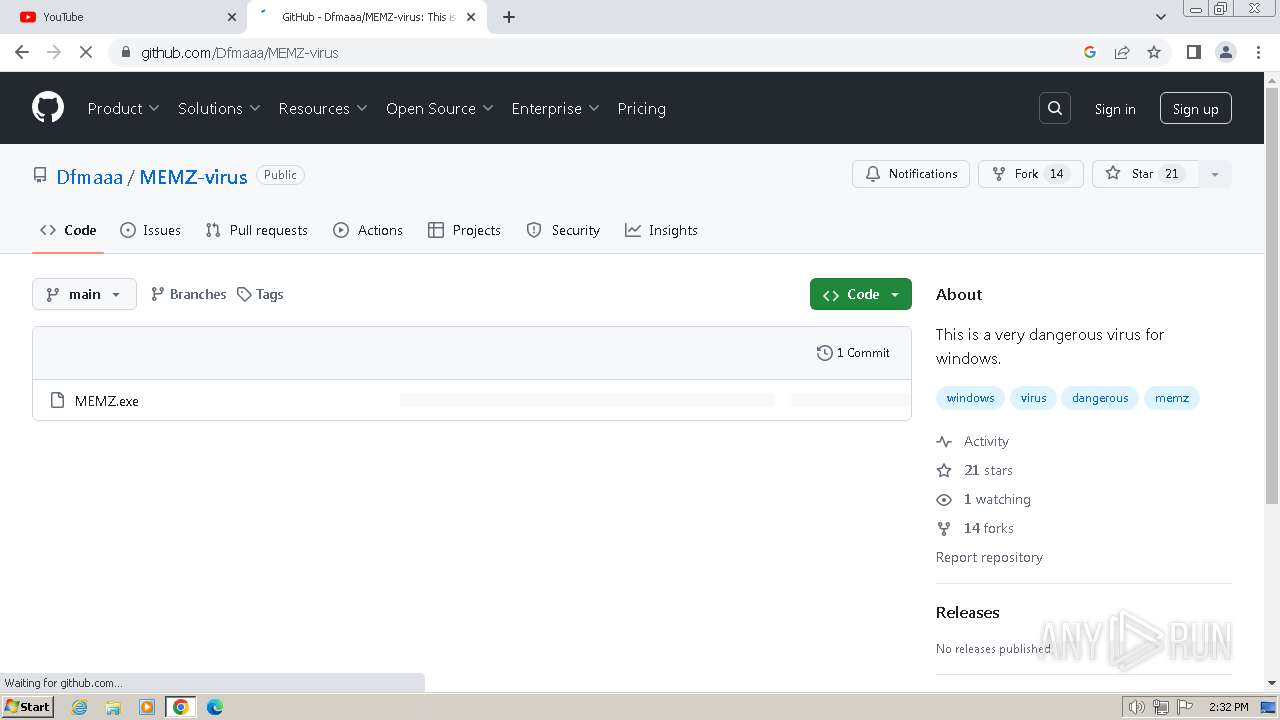
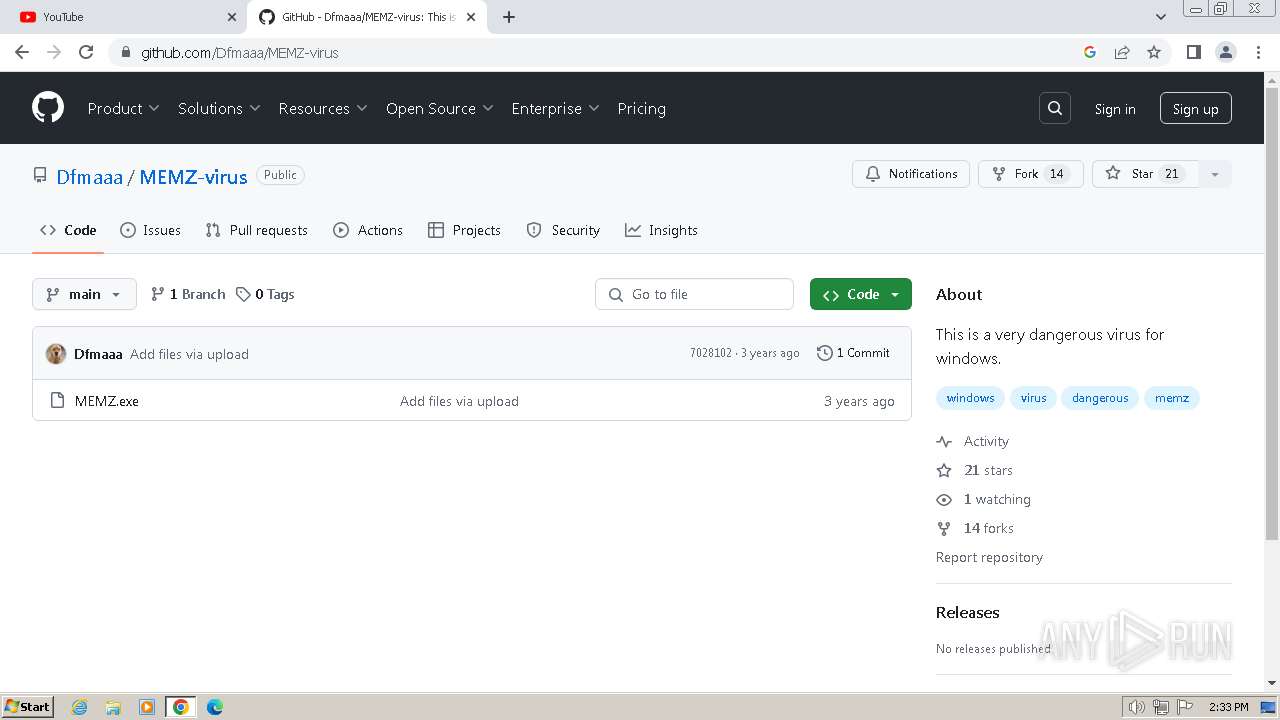
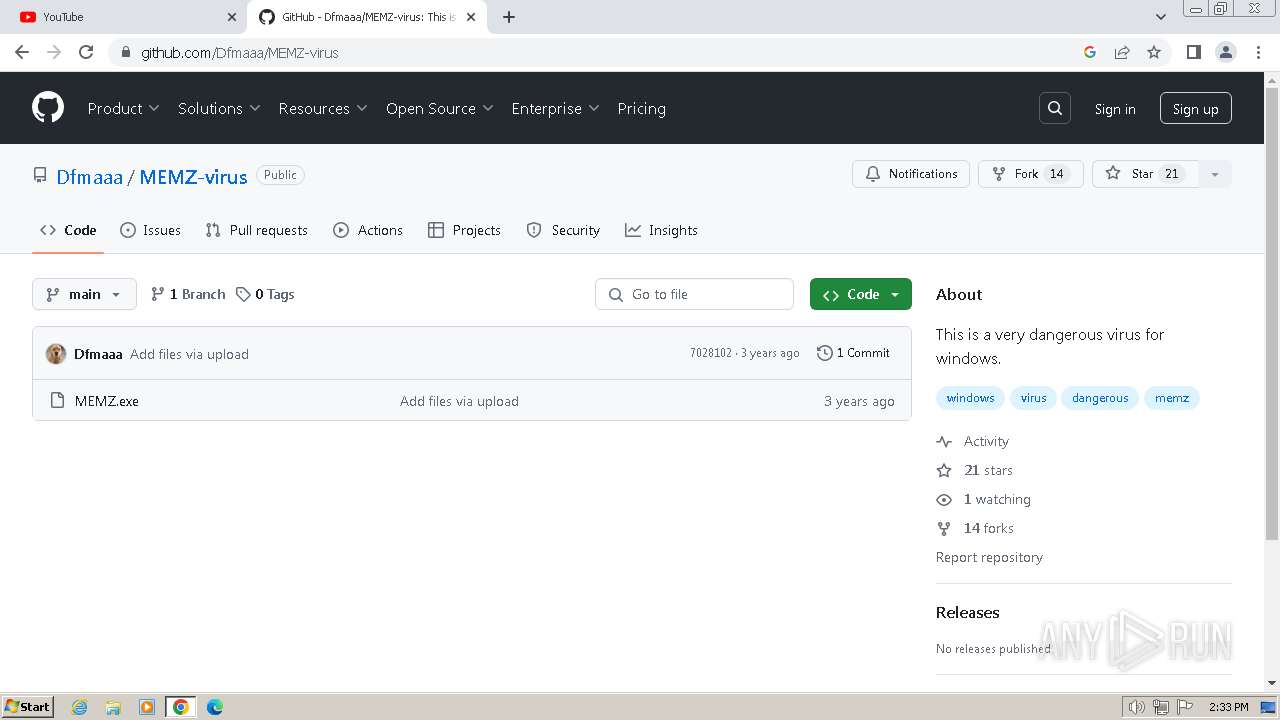
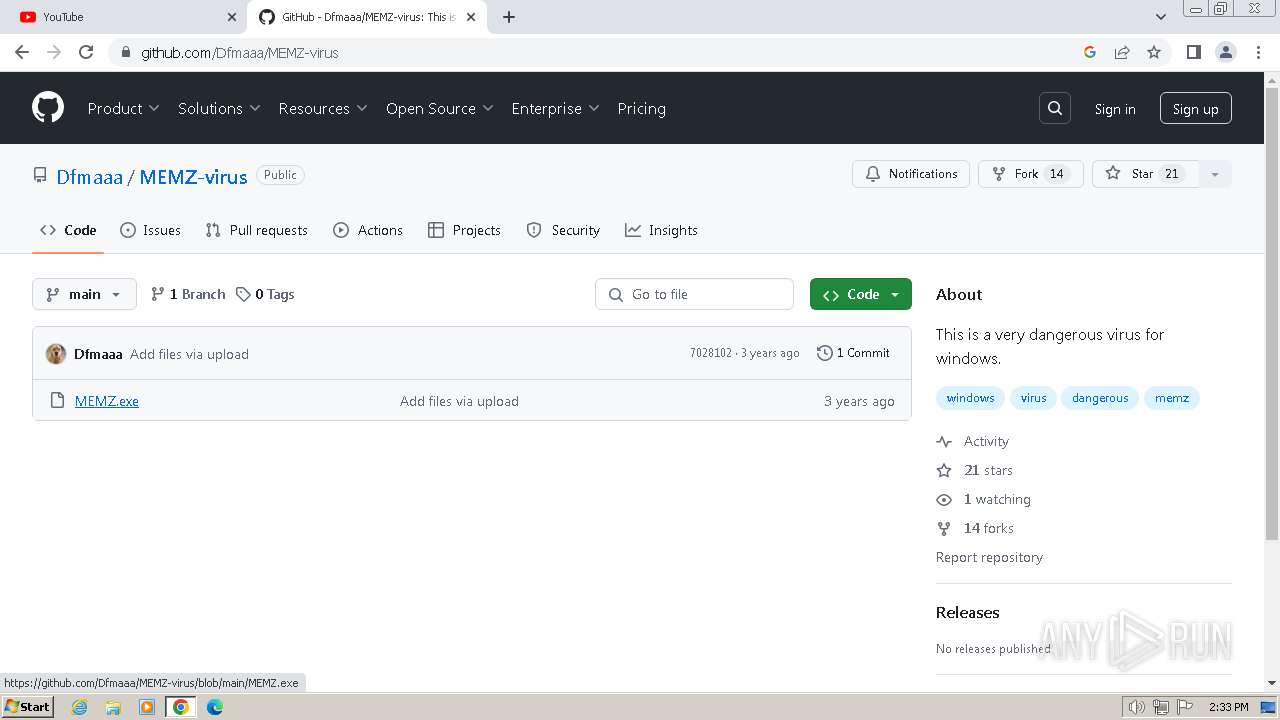
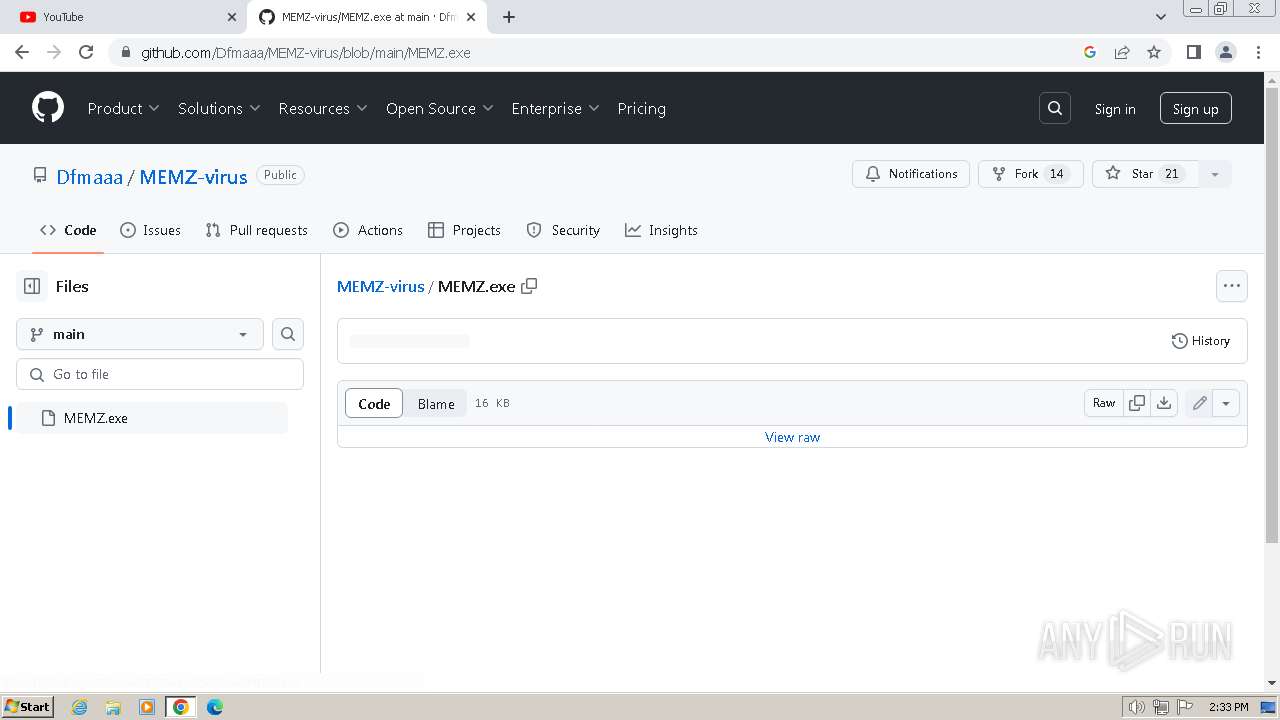
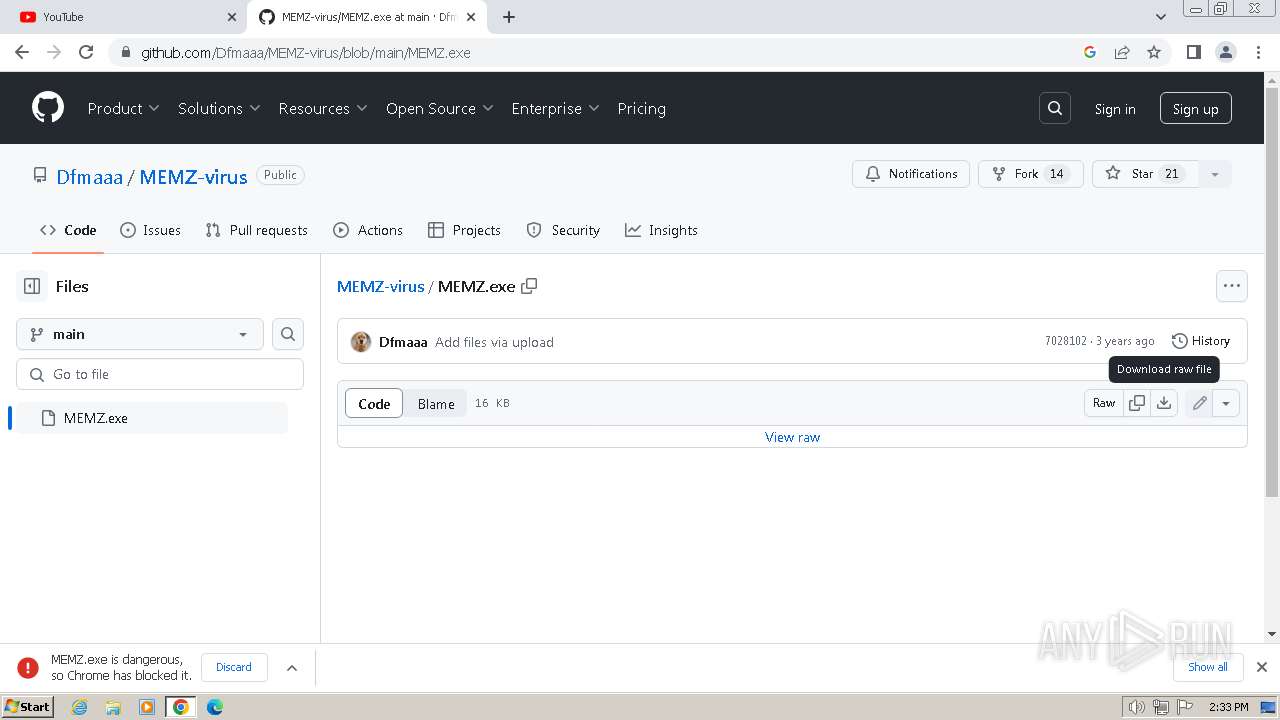
| Title: | MEMZ-virus/MEMZ.exe at main · Dfmaaa/MEMZ-virus |
|---|---|
| RoutePattern: | /:user_id/:repository/blob/*name(/*path) |
| RouteController: | blob |
| RouteAction: | show |
| CurrentCatalogServiceHash: | f3abb0cc802f3d7b95fc8762b94bdcb13bf39634c40c357301c4aa1d67a256fb |
| RequestId: | CFC6:15878:2BDF340:2CB8568:669A6A97 |
| HtmlSafeNonce: | 85e854a515cbcf397ffd9223aa5e202a1ba4a98f1a6225cc517b2f0b3c564b5c |
| VisitorPayload: | eyJyZWZlcnJlciI6Imh0dHBzOi8vZ2l0aHViLmNvbS9EZm1hYWEvTUVNWi12aXJ1cyIsInJlcXVlc3RfaWQiOiJDRkM2OjE1ODc4OjJCREYzNDA6MkNCODU2ODo2NjlBNkE5NyIsInZpc2l0b3JfaWQiOiI1NDA5MDMwNDcyMjYxMzEzOTA1IiwicmVnaW9uX2VkZ2UiOiJmcmEiLCJyZWdpb25fcmVuZGVyIjoiaWFkIn0= |
| VisitorHmac: | c73e74dbe36cd8e5fabc8c7e2a94029993e4d43dd276bacd8b23f9513da9d4a2 |
| HovercardSubjectTag: | repository:359759769 |
| GithubKeyboardShortcuts: | repository,source-code,file-tree,copilot |
| GoogleSiteVerification: | Apib7-x98H0j5cPqHWwSMm6dNU4GmODRoqxLiDzdx9I |
| OctolyticsUrl: | https://collector.github.com/github/collect |
| OctolyticsActorId: | 121751191 |
| OctolyticsActorLogin: | kaannsaydamm |
| OctolyticsActorHash: | e0485061b562edc0a78f55c44759a1b183e95cb7ed73a2330e2a20fee7e00ec0 |
| AnalyticsLocation: | /<user-name>/<repo-name>/blob/show |
| UserLogin: | kaannsaydamm |
| HTTPEquivXPjaxVersion: | e08b9b93be63bd4dff3b05d7e8468215176e199ad57060e8b6c006e4b5fc7a66 |
| HTTPEquivXPjaxCspVersion: | 479d0e4f25e10adc648c4dd302ffd147aa5c2b606f0c5424f6f6f0f4511e5753 |
| HTTPEquivXPjaxCssVersion: | 1820a7d812210e3c5936956de65fb85c4432587e0365207859b566b849146f54 |
| HTTPEquivXPjaxJsVersion: | 21ba2d3aacfc137a5c2a619c9ecf8466b4f0f4d8522e543ad9d1dfea8d6a3c84 |
| TurboCacheControl: | no-cache |
| GoImport: | github.com/Dfmaaa/MEMZ-virus git https://github.com/Dfmaaa/MEMZ-virus.git |
| OctolyticsDimensionUser_id: | 82197472 |
| OctolyticsDimensionUser_login: | Dfmaaa |
| OctolyticsDimensionRepository_id: | 359759769 |
| OctolyticsDimensionRepository_nwo: | Dfmaaa/MEMZ-virus |
| OctolyticsDimensionRepository_public: | |
| OctolyticsDimensionRepository_is_fork: | - |
| OctolyticsDimensionRepository_network_root_id: | 359759769 |
| OctolyticsDimensionRepository_network_root_nwo: | Dfmaaa/MEMZ-virus |
| TurboBodyClasses: | logged-in env-production page-responsive |
| BrowserStatsUrl: | https://api.github.com/_private/browser/stats |
| BrowserErrorsUrl: | https://api.github.com/_private/browser/errors |
| ThemeColor: | #1e2327 |
| ColorScheme: | light dark |
Total processes
204
Monitored processes
83
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 292 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --mojo-platform-channel-handle=4560 --field-trial-handle=1148,i,12596384035975212835,10865647332235617643,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 328 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=4128 --field-trial-handle=1148,i,12596384035975212835,10865647332235617643,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 348 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=audio.mojom.AudioService --lang=en-US --service-sandbox-type=audio --disable-quic --mojo-platform-channel-handle=3804 --field-trial-handle=1148,i,12596384035975212835,10865647332235617643,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 368 | "C:\Users\admin\Downloads\MEMZ.exe" /watchdog | C:\Users\admin\Downloads\MEMZ.exe | — | MEMZ.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 444 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=20 --mojo-platform-channel-handle=4552 --field-trial-handle=1148,i,12596384035975212835,10865647332235617643,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 580 | "C:\Users\admin\Downloads\MEMZ.exe" /watchdog | C:\Users\admin\Downloads\MEMZ.exe | — | MEMZ.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 596 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --first-renderer-process --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=2096 --field-trial-handle=1148,i,12596384035975212835,10865647332235617643,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 680 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "--disable-features=OptimizationGuideModelDownloading,OptimizationHintsFetching,OptimizationTargetPrediction,OptimizationHints" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 828 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=4732 --field-trial-handle=1148,i,12596384035975212835,10865647332235617643,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 940 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1104 --field-trial-handle=1148,i,12596384035975212835,10865647332235617643,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
30 556
Read events
30 280
Write events
236
Delete events
40
Modification events
| (PID) Process: | (680) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (680) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (680) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (680) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (680) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (680) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (680) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (680) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (680) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (680) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
3
Suspicious files
519
Text files
68
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 680 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF55451.TMP | — | |
MD5:— | SHA256:— | |||
| 680 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 680 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:456D3EF989973A7C218E338A6CFFAD25 | SHA256:75631D994431F254B94255C50038A3657BFC45D76FCE9D794D514E57CA678872 | |||
| 680 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF55451.TMP | text | |
MD5:ECD3386BCC950E73B86EB128A5F57622 | SHA256:C9A068EAFBC587EDFC89392F64DDD350EEB96C5CF195CDB030BAB8F6DD33833B | |||
| 3392 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\scsE339.tmp | text | |
MD5:4C361DEA398F7AEEF49953BDC0AB4A9B | SHA256:06D61C23E6CA59B9DDAD1796ECCC42C032CD8F6F424AF6CFEE5D085D36FF7DFD | |||
| 680 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:FA25AF7098FC1571F24F200A9D105D58 | SHA256:4F40C87070B7A151FB241CCF36E7027AA703C15CA0ACB0A1759DA07B2C318574 | |||
| 680 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RF55636.TMP | text | |
MD5:E53573A93829681410D5E7DBB1B61C78 | SHA256:A82D28F2C1E22A2AE0ABC5F5AF0CC8EE7AD913BAB3A0BF84CE6D8D23F67E06A3 | |||
| 680 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 680 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\metadata\LOG.old | text | |
MD5:23E954DCE0FB0ECF46A96FF4ACBE66F4 | SHA256:68F3B7AA8367C46273C296103B799A112DE3B70DE873C16F7166496CA31C3DDD | |||
| 680 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RF55599.TMP | text | |
MD5:AD0DB8476493577A67FA94A162B646C4 | SHA256:304FB5B4FD83D4A9FF1EF4CF20232A1783169C148297BFE37ED24A1D22A74F2B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
18
TCP/UDP connections
115
DNS requests
140
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1372 | svchost.exe | GET | 304 | 2.19.198.34:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?33775f6043c93e33 | DE | — | — | whitelisted |
1060 | svchost.exe | GET | 304 | 199.232.214.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?a9f83325acc8ca75 | US | — | — | whitelisted |
1372 | svchost.exe | GET | 200 | 23.32.238.171:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | whitelisted |
1372 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
844 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | US | — | — | whitelisted |
844 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | US | binary | 6.69 Kb | whitelisted |
844 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | US | binary | 10.0 Kb | whitelisted |
844 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | US | binary | 9.20 Kb | whitelisted |
844 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | US | binary | 9.96 Kb | whitelisted |
844 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | US | binary | 21.2 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1372 | svchost.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1060 | svchost.exe | 224.0.0.252:5355 | — | — | — | whitelisted |
2564 | svchost.exe | 239.255.255.250:3702 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1372 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1372 | svchost.exe | 2.19.198.34:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
1372 | svchost.exe | 23.32.238.171:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
1372 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | unknown |
2852 | chrome.exe | 142.250.186.131:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
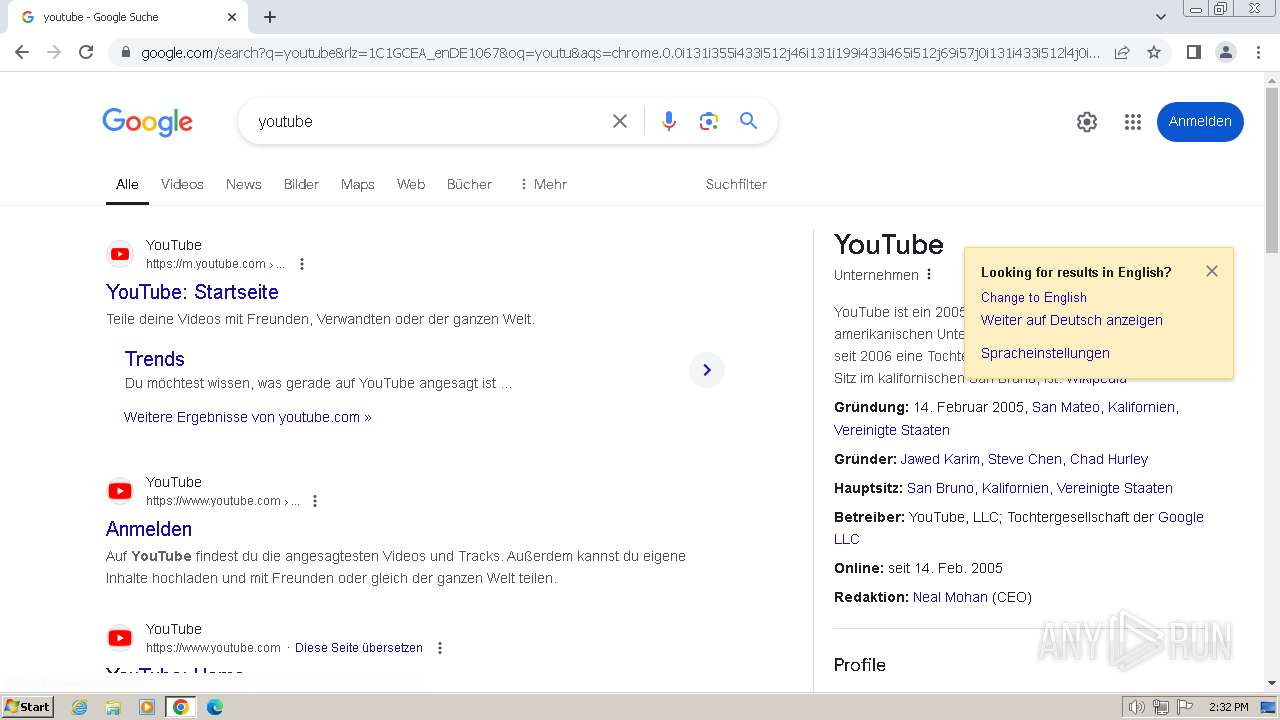
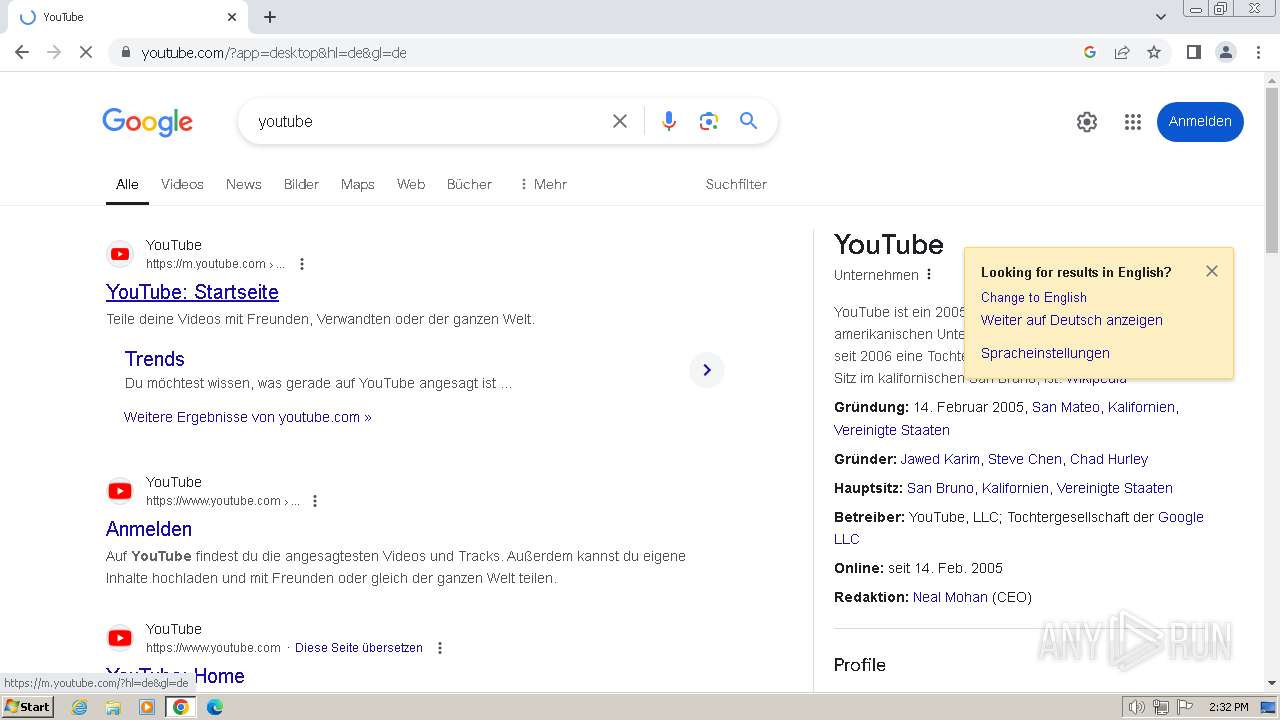
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| whitelisted |
www.google.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
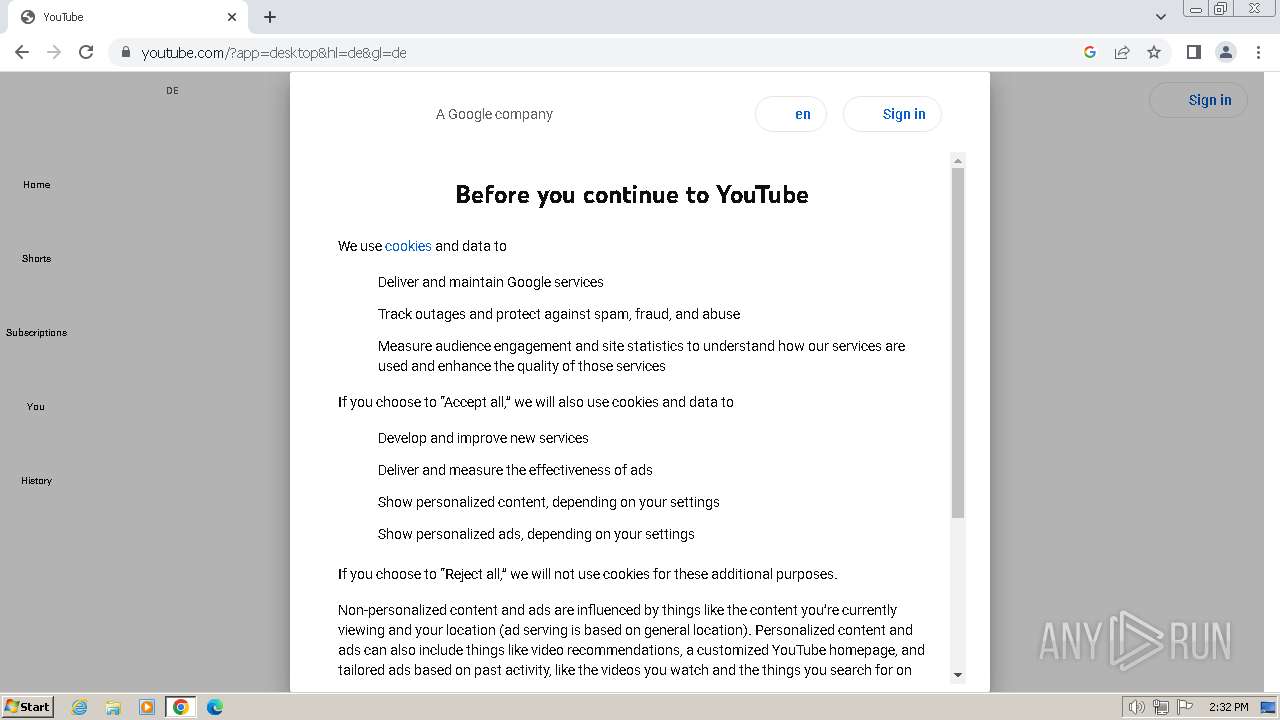
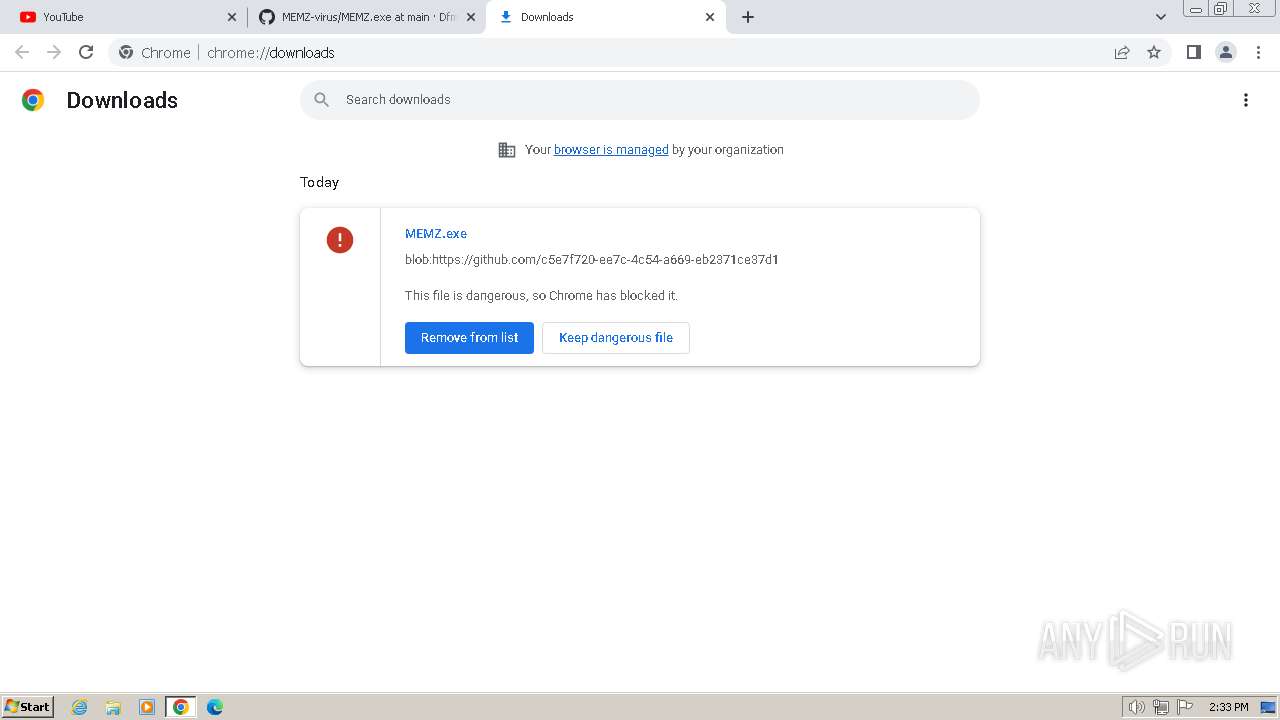
2852 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
2852 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |