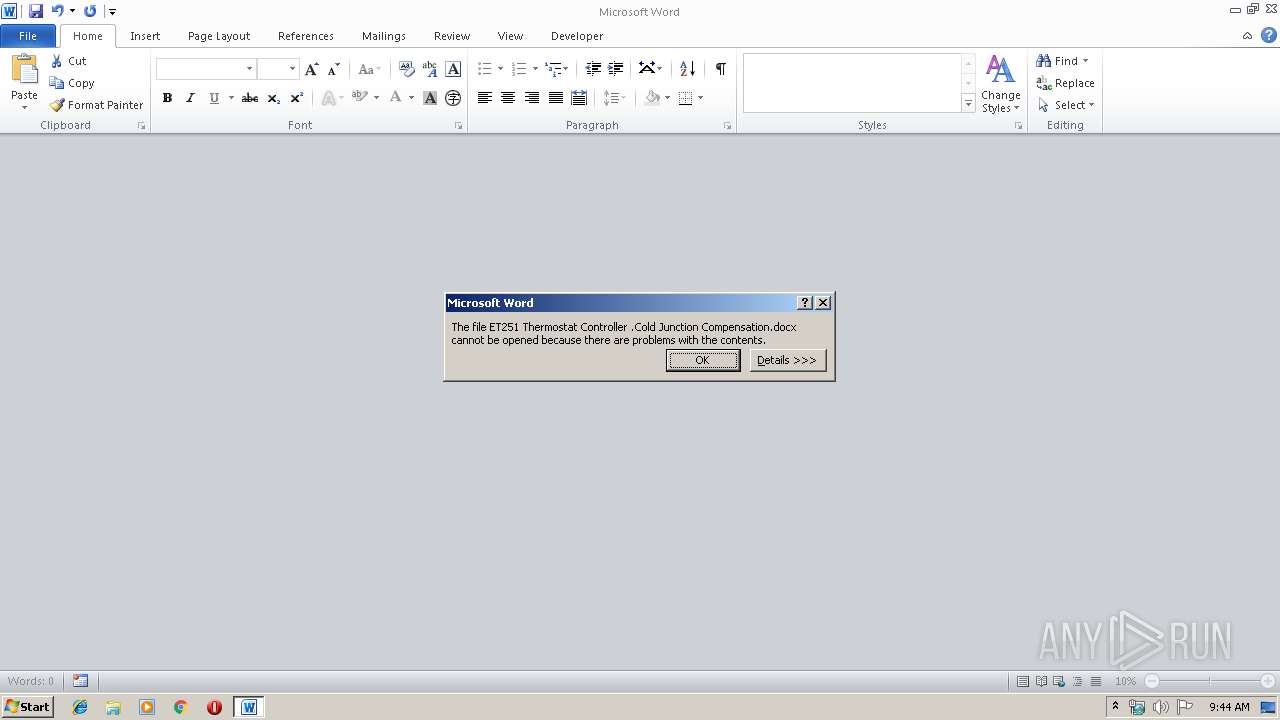
| File name: | ET251 Thermostat Controller .Cold Junction Compensation.docx |
| Full analysis: | https://app.any.run/tasks/09a92b58-d74d-477a-b4ca-09665afb3c90 |
| Verdict: | Malicious activity |
| Analysis date: | December 09, 2019, 09:44:24 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract |
| MD5: | 489648D6EB6B942CEF2B022D29330C8F |
| SHA1: | 695AA69C1EB33DFBC3480636C0CA8D5AA71628B2 |
| SHA256: | B55D518C7C4CDBA474EF2455025A2F5EB22C9DB03198882F09EFBDF4E65EA6BA |
| SSDEEP: | 192:4GT3ZWmbBR6/ufVmhf2QwPwden4c2Sd8SQD1HA37qNAiasP9sK2QVpAO:4ir6/CVmxhwoI4cqHg+NAiFuK9z |
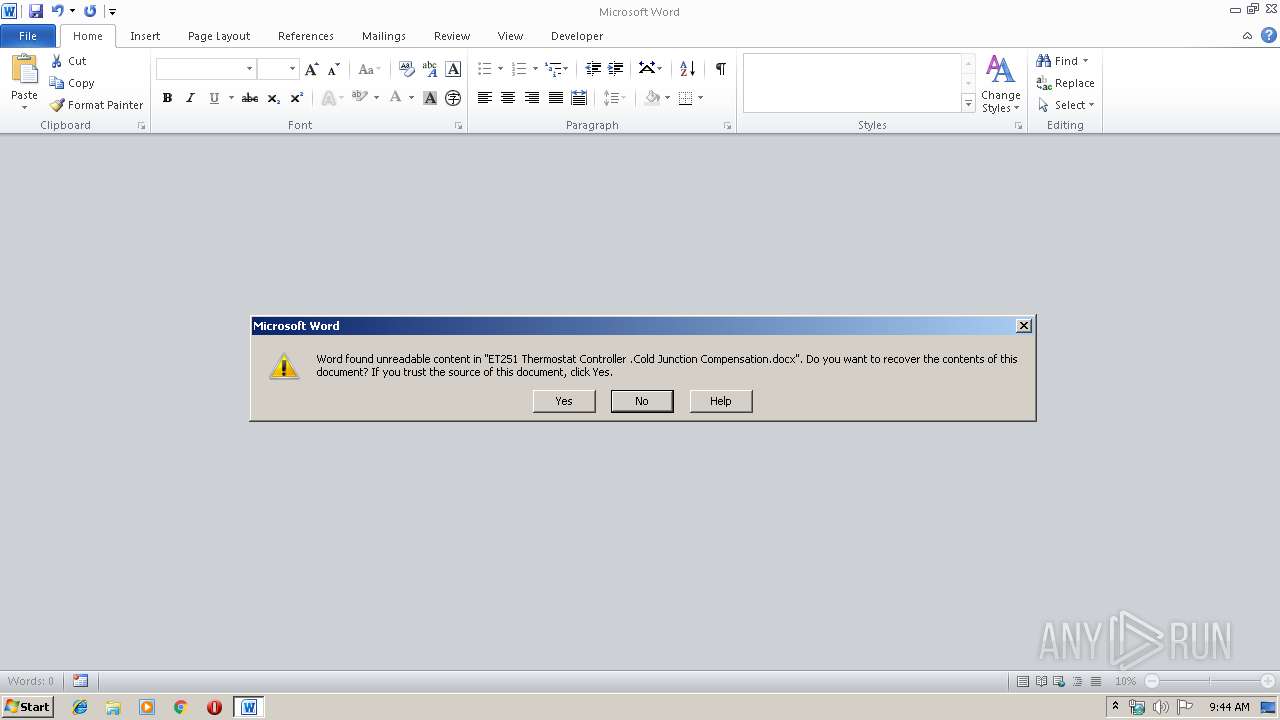
MALICIOUS
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 1324)
SUSPICIOUS
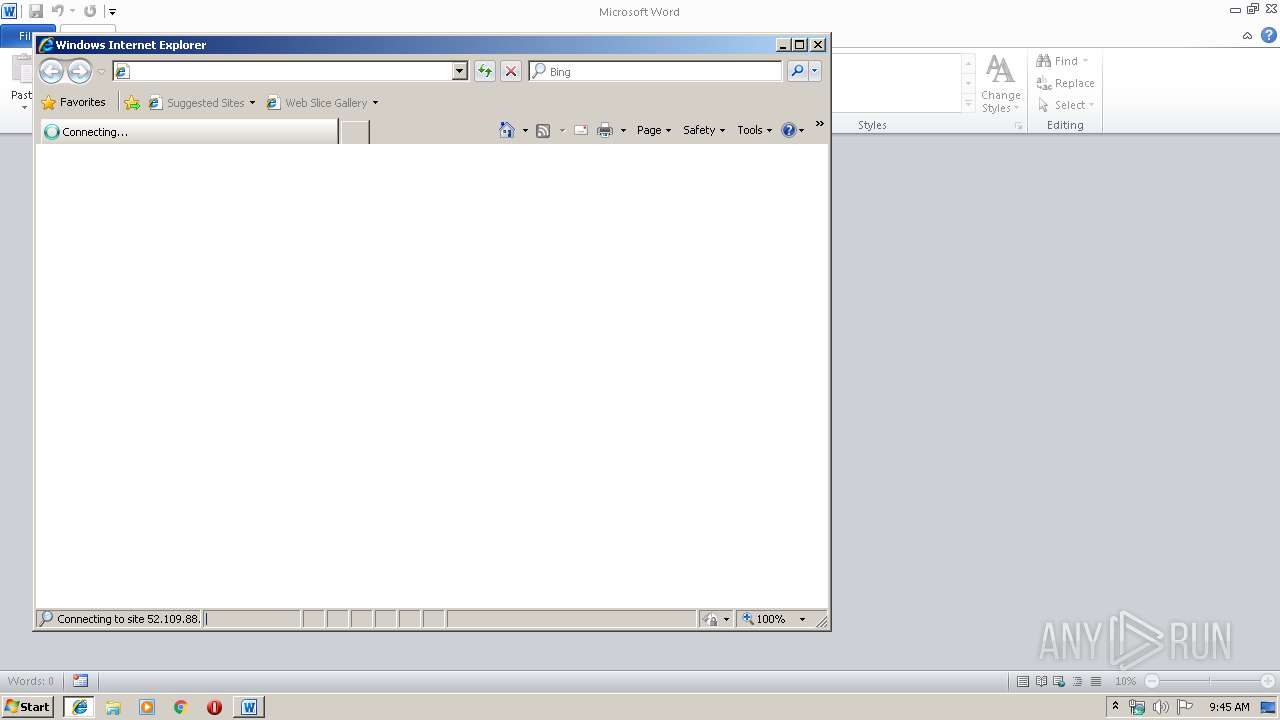
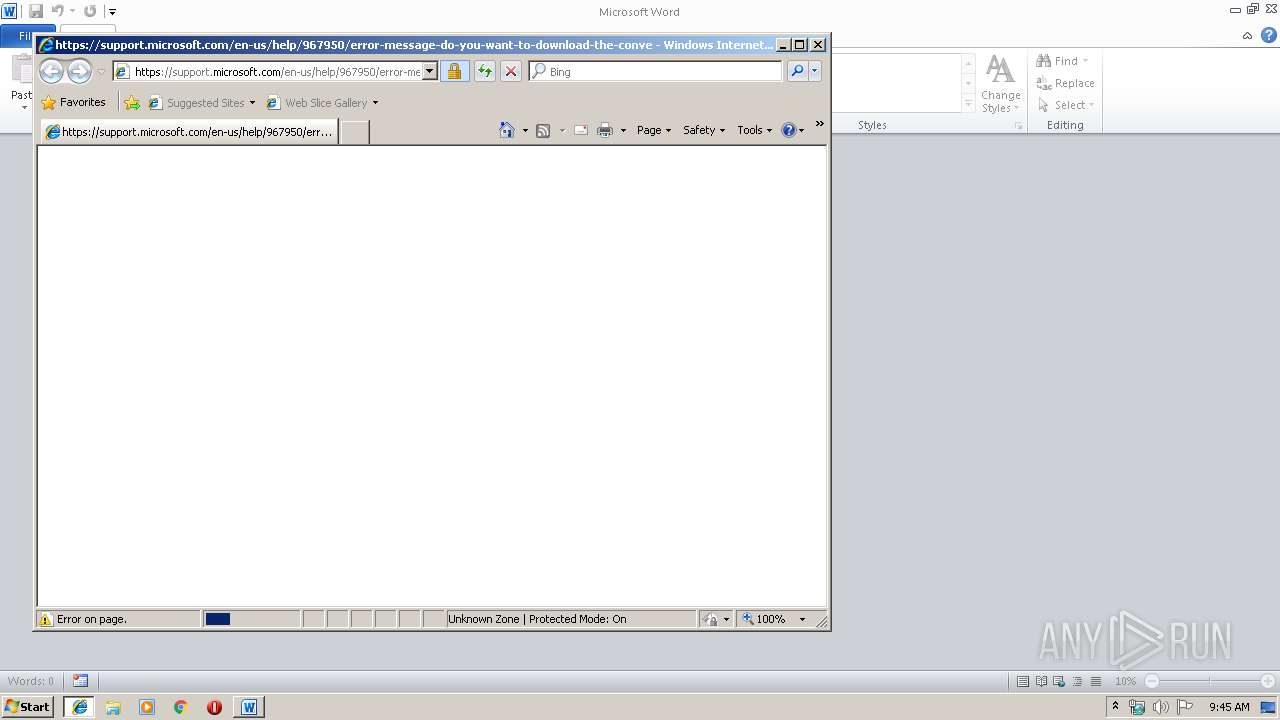
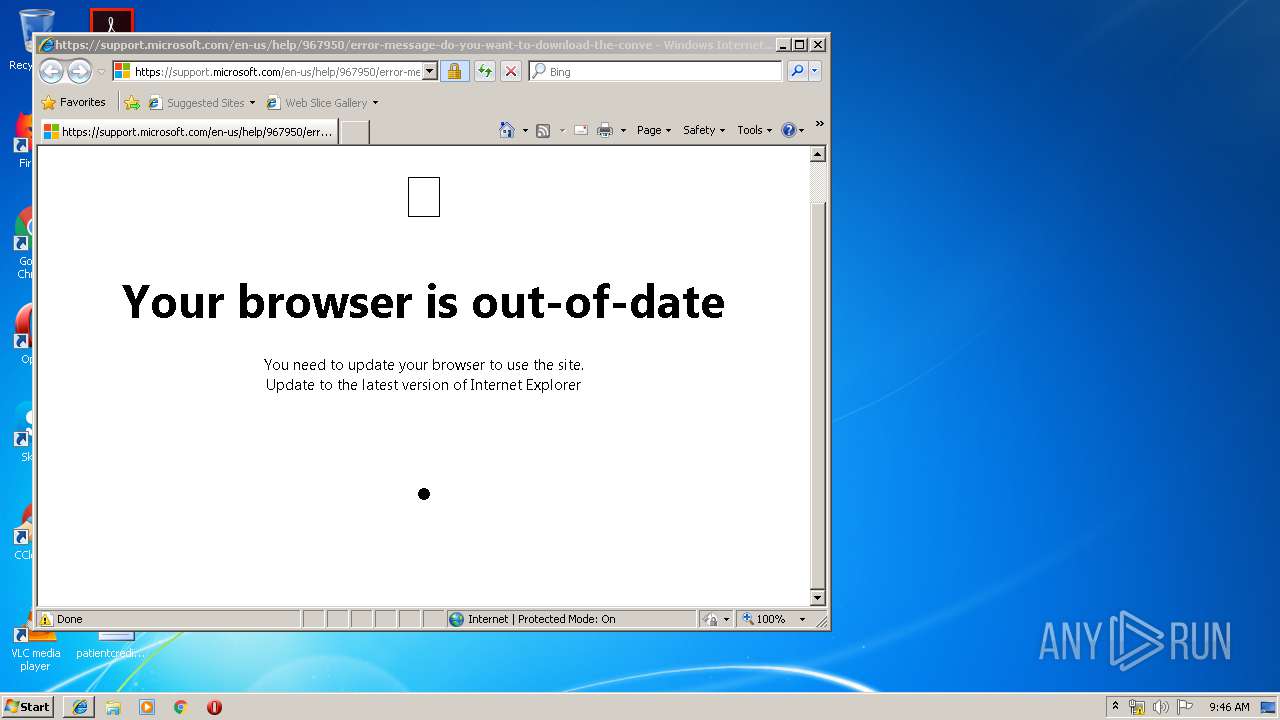
Starts Internet Explorer
- WINWORD.EXE (PID: 1324)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1324)
Creates files in the user directory
- WINWORD.EXE (PID: 1324)
- iexplore.exe (PID: 3084)
- iexplore.exe (PID: 2600)
Changes internet zones settings
- iexplore.exe (PID: 2600)
Reads Internet Cache Settings
- iexplore.exe (PID: 3084)
Application launched itself
- iexplore.exe (PID: 2600)
Reads settings of System Certificates
- iexplore.exe (PID: 2600)
Reads internet explorer settings
- iexplore.exe (PID: 3084)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2600)
Changes settings of System certificates
- iexplore.exe (PID: 2600)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .docx | | | Word Microsoft Office Open XML Format document (52.2) |
|---|---|---|
| .zip | | | Open Packaging Conventions container (38.8) |
| .zip | | | ZIP compressed archive (8.8) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2012:07:02 09:52:07 |
| ZipCRC: | 0xdaffb6d4 |
| ZipCompressedSize: | 363 |
| ZipUncompressedSize: | 1432 |
| ZipFileName: | [Content_Types].xml |
XML
| Template: | Normal.dotm |
|---|---|
| Pages: | 1 |
| Words: | - |
| Characters: | - |
| Lines: | - |
| Paragraphs: | - |
| TotalEditTime: | - |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| CharactersWithSpaces: | - |
| Application: | WPS Office_10.1.0.7400_F1E327BC-269C-435d-A152-05C5408002CA |
| DocSecurity: | None |
| CreateDate: | 2014:10:29 12:08:00Z |
| LastModifiedBy: | 杭州中创电子有限公司 |
| ModifyDate: | 2018:06:05 01:43:13Z |
| KSOProductBuildVer: | 2052-10.1.0.7400 |
XMP
| Creator: | Administrator |
|---|
Total processes
37
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1324 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\ET251 Thermostat Controller .Cold Junction Compensation.docx" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2600 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | WINWORD.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3084 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2600 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 530
Read events
690
Write events
584
Delete events
256
Modification events
| (PID) Process: | (1324) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | ?n; |
Value: 3F6E3B002C050000010000000000000000000000 | |||
| (PID) Process: | (1324) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (1324) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (1324) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (1324) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (1324) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (1324) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (1324) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (1324) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (1324) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1334378558 | |||
Executable files
0
Suspicious files
5
Text files
22
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1324 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR9630.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1324 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\mso1719.tmp | — | |
MD5:— | SHA256:— | |||
| 2600 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2600 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3084 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@microsoft[2].txt | — | |
MD5:— | SHA256:— | |||
| 3084 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\VH0222RF\error-message-do-you-want-to-download-the-converter-when-you-try-to-op[1].txt | — | |
MD5:— | SHA256:— | |||
| 1324 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 1324 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$251 Thermostat Controller .Cold Junction Compensation.docx | pgc | |
MD5:— | SHA256:— | |||
| 3084 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\JG50I4FQ\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
| 3084 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\Low\History.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
11
DNS requests
7
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2600 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2600 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3084 | iexplore.exe | 52.109.88.6:80 | officeredir.microsoft.com | Microsoft Corporation | NL | whitelisted |
3084 | iexplore.exe | 23.210.248.208:443 | support.microsoft.com | Akamai International B.V. | NL | whitelisted |
2600 | iexplore.exe | 2.18.233.62:443 | www.microsoft.com | Akamai International B.V. | — | whitelisted |
3084 | iexplore.exe | 2.18.233.62:443 | www.microsoft.com | Akamai International B.V. | — | whitelisted |
3084 | iexplore.exe | 104.109.56.54:443 | mem.gfx.ms | Akamai International B.V. | NL | whitelisted |
3084 | iexplore.exe | 2.16.186.27:443 | statics-marketingsites-neu-ms-com.akamaized.net | Akamai International B.V. | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
officeredir.microsoft.com |
| whitelisted |
support.microsoft.com |
| malicious |
www.microsoft.com |
| whitelisted |
statics-marketingsites-neu-ms-com.akamaized.net |
| whitelisted |
mem.gfx.ms |
| whitelisted |
img-prod-cms-rt-microsoft-com.akamaized.net |
| whitelisted |