| File name: | z3r0.rtf |
| Full analysis: | https://app.any.run/tasks/3d049e31-eecf-46f1-836e-5ec0153b7fee |
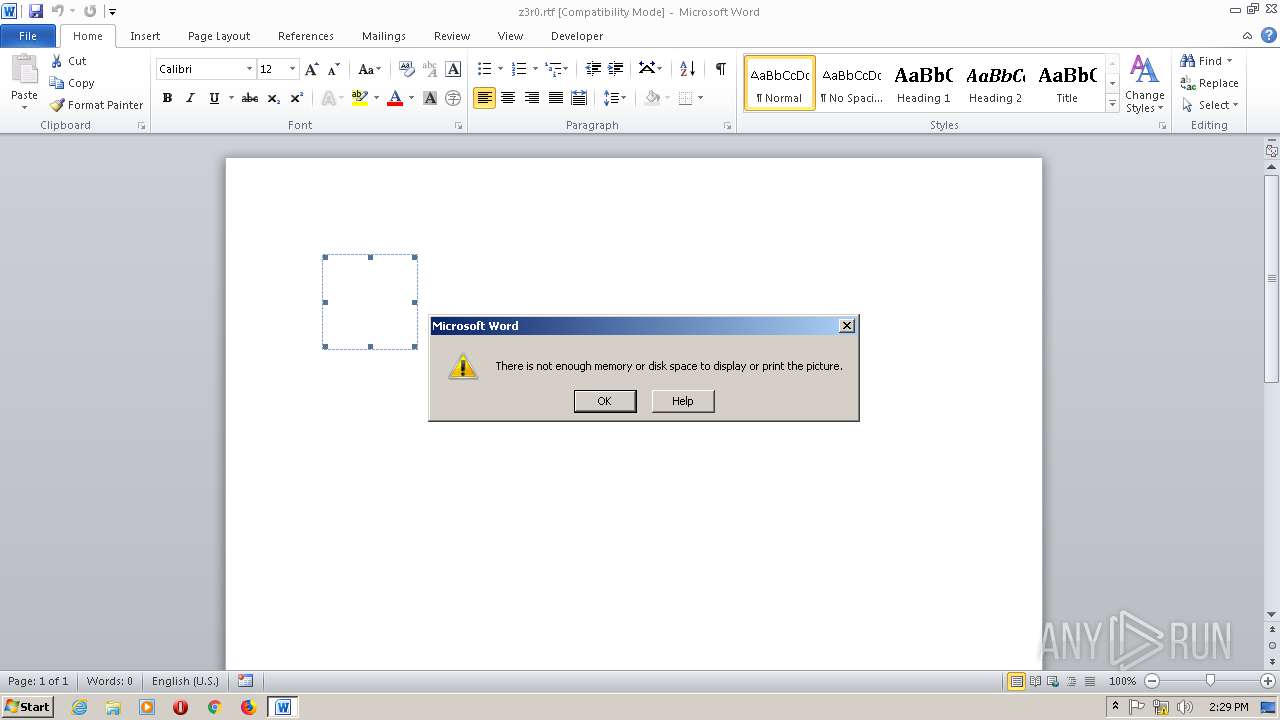
| Verdict: | Malicious activity |
| Analysis date: | November 08, 2019, 14:24:35 |
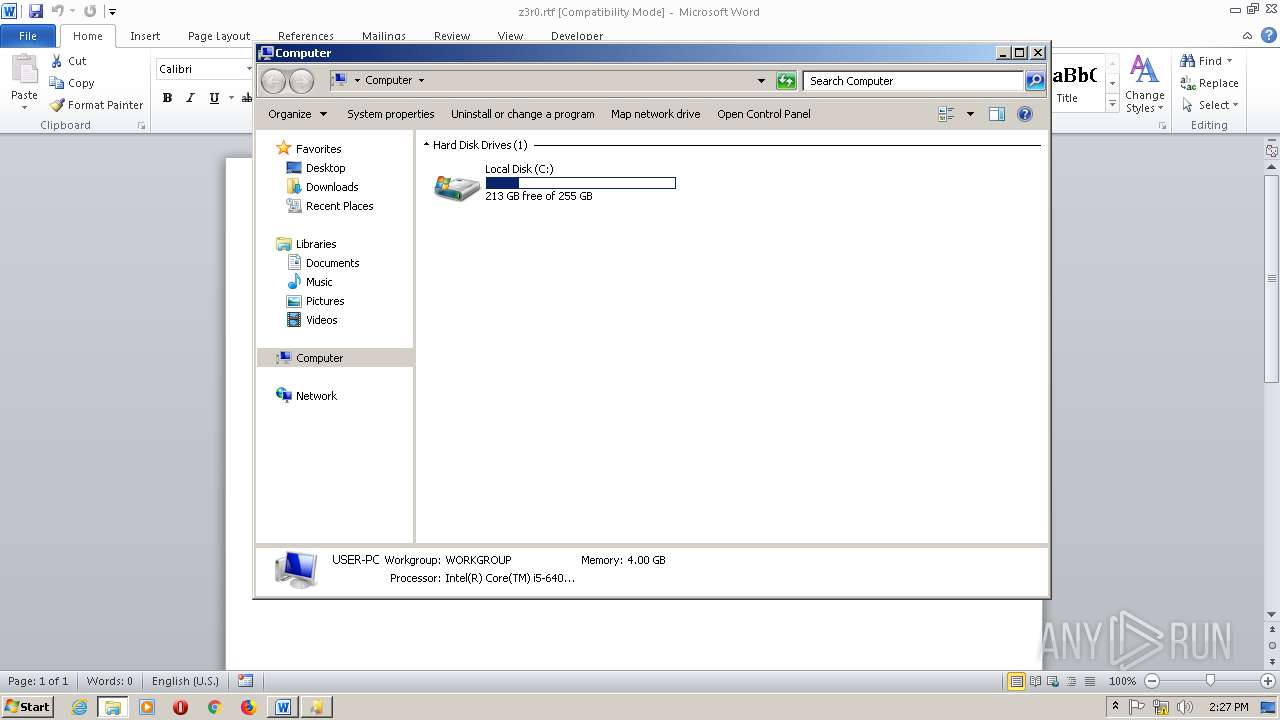
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines, with CR, LF line terminators |
| MD5: | 5858B1C68C8A91C565E875E3492EDD49 |
| SHA1: | 48B8DF7B68BA004E67AD5F4C8A0E9215F632AB04 |
| SHA256: | B5572ED87256F85CC663EDBE6884820AC35AFFECD16891F28EC6A8817D1A2F88 |
| SSDEEP: | 48:5fU5NncuBCnb5S2vw3xMa279j+J5ffRKVr9z9UyDW3SkSNmhmXmw9sv5:NaBCnLvwWxBCRKVJzuyDW3SkuOmsv5 |
MALICIOUS
Loads dropped or rewritten executable
- Setup.exe (PID: 992)
- EQNEDT32.EXE (PID: 1788)
- WerFault.exe (PID: 2456)
- WerFault.exe (PID: 2500)
- EQNEDT32.EXE (PID: 2908)
- WINWORD.EXE (PID: 2816)
- explorer.exe (PID: 1936)
- svchost.exe (PID: 904)
Application was dropped or rewritten from another process
- EQNEDT32.EXE (PID: 1788)
- EQNEDT32.EXE (PID: 2908)
- msohtmed.exe (PID: 564)
- msohtmed.exe (PID: 1012)
SUSPICIOUS
Executed via COM
- EQNEDT32.EXE (PID: 1788)
- EQNEDT32.EXE (PID: 2908)
- Setup.exe (PID: 992)
Creates files in the user directory
- explorer.exe (PID: 1936)
Reads the machine GUID from the registry
- Setup.exe (PID: 992)
- MsiExec.exe (PID: 2632)
- MsiExec.exe (PID: 1364)
- msiexec.exe (PID: 1472)
- MsiExec.exe (PID: 2784)
- MsiExec.exe (PID: 1832)
- MsiExec.exe (PID: 2288)
- MsiExec.exe (PID: 2528)
- MsiExec.exe (PID: 2944)
- MsiExec.exe (PID: 2356)
- MsiExec.exe (PID: 2660)
- MsiExec.exe (PID: 2700)
- MsiExec.exe (PID: 1928)
- MsiExec.exe (PID: 2972)
- MsiExec.exe (PID: 2768)
- MsiExec.exe (PID: 2376)
- MsiExec.exe (PID: 312)
- MsiExec.exe (PID: 1504)
- MsiExec.exe (PID: 2564)
- addinutil.exe (PID: 2672)
- addinutil.exe (PID: 2440)
- MsiExec.exe (PID: 480)
Executable content was dropped or overwritten
- Setup.exe (PID: 992)
- MsiExec.exe (PID: 1364)
- MsiExec.exe (PID: 2288)
- MsiExec.exe (PID: 1832)
- MsiExec.exe (PID: 2528)
- msiexec.exe (PID: 1472)
- MsiExec.exe (PID: 1928)
- MsiExec.exe (PID: 2972)
- MsiExec.exe (PID: 1504)
- MsiExec.exe (PID: 312)
- MsiExec.exe (PID: 2564)
Searches for installed software
- Setup.exe (PID: 992)
Creates files in the Windows directory
- msiexec.exe (PID: 1472)
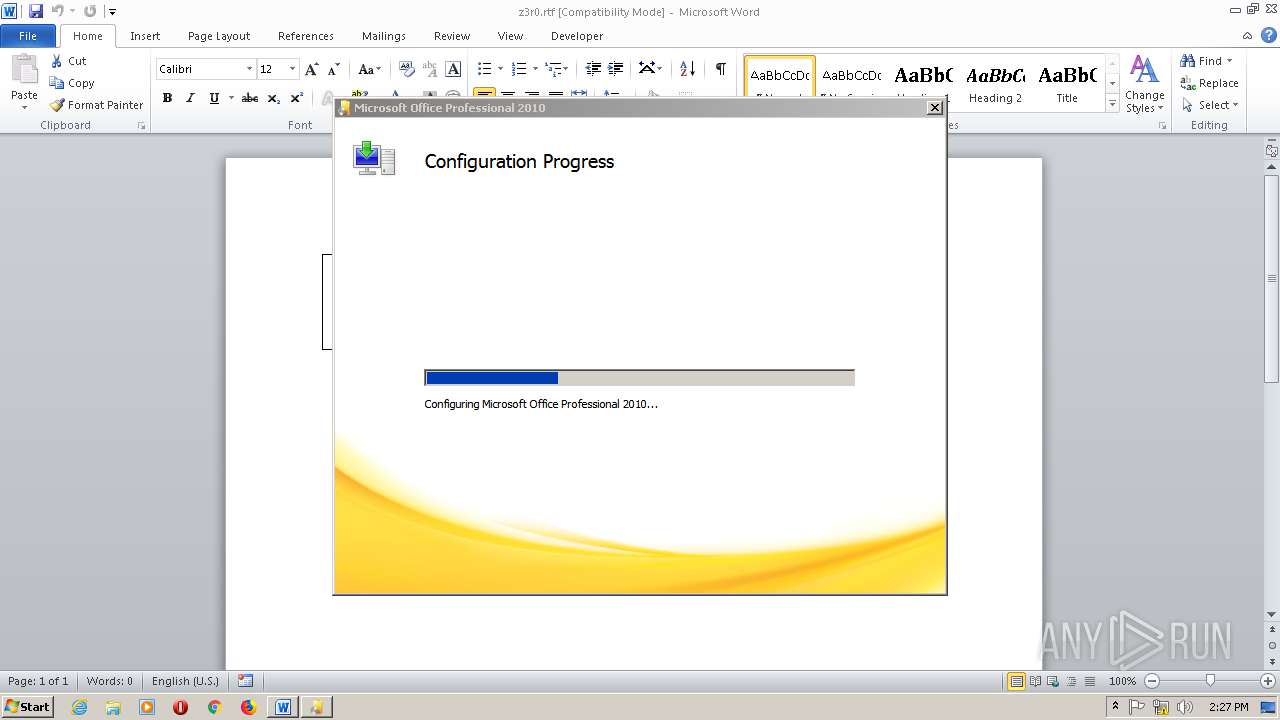
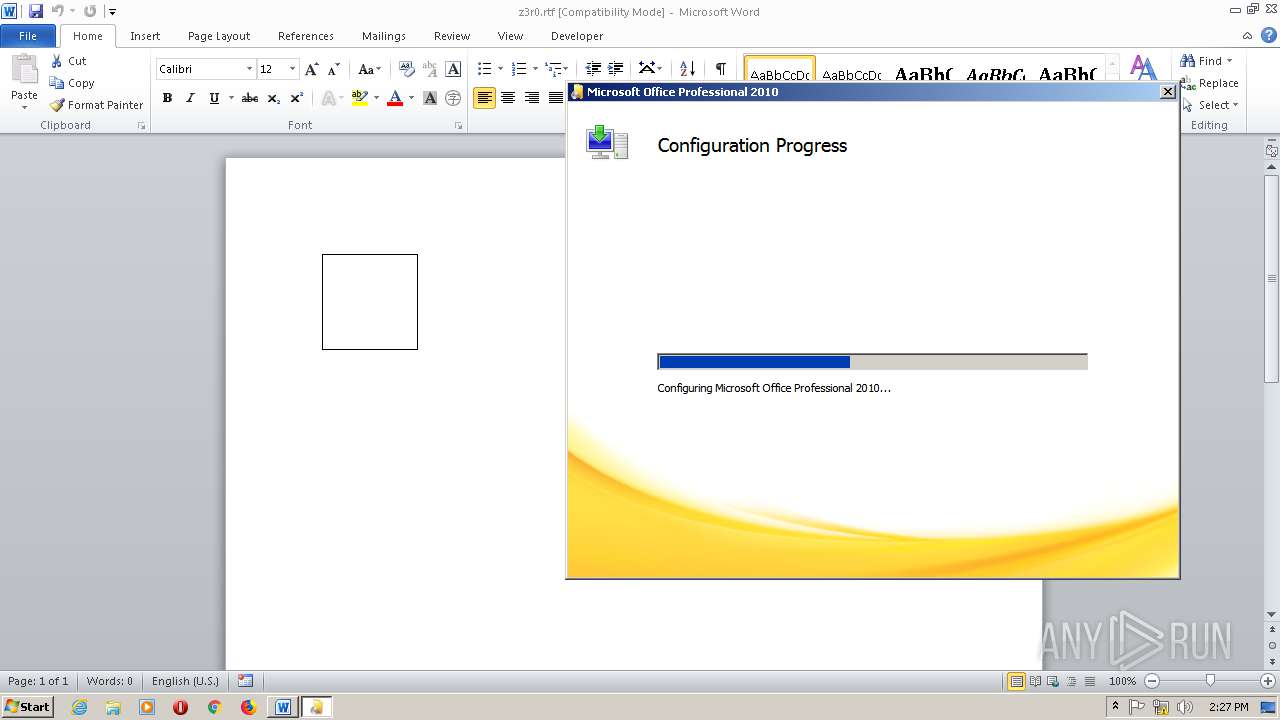
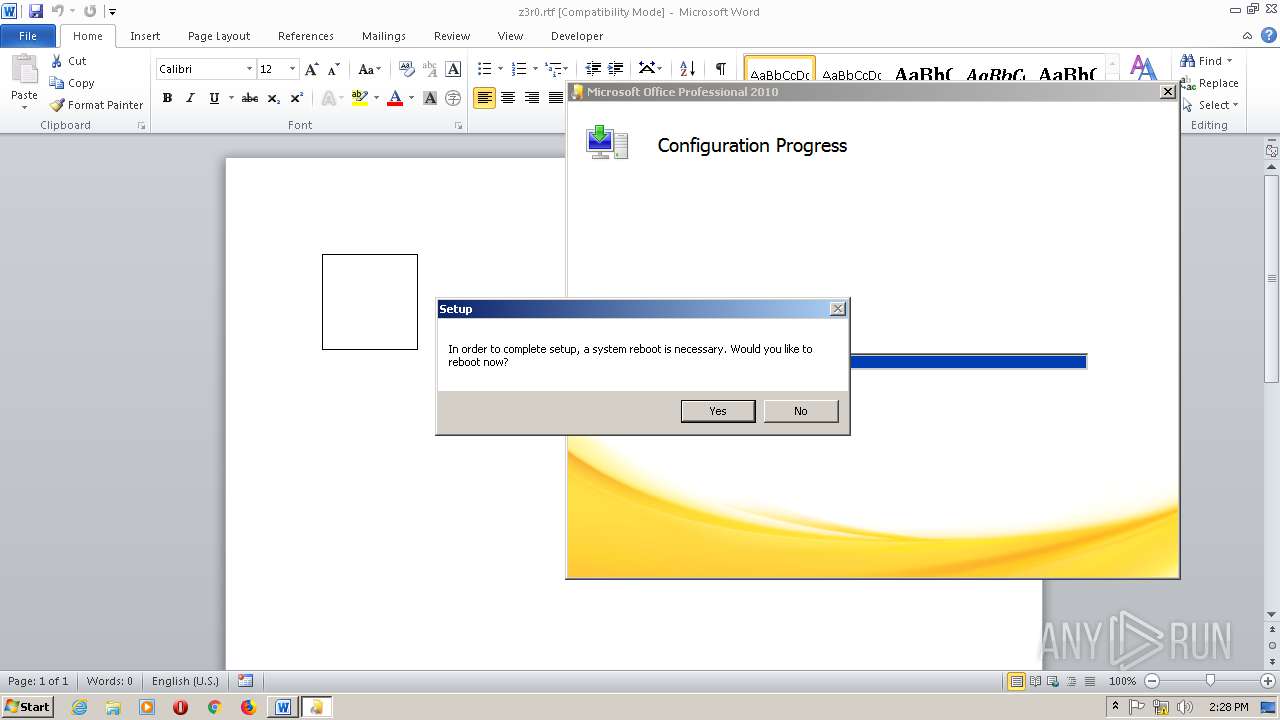
Starts Microsoft Office Application
- msiexec.exe (PID: 1472)
Creates COM task schedule object
- msohtmed.exe (PID: 1012)
- msiexec.exe (PID: 1472)
- msohtmed.exe (PID: 564)
Removes files from Windows directory
- msiexec.exe (PID: 1472)
Modifies the open verb of a shell class
- msiexec.exe (PID: 1472)
INFO
Starts Microsoft Office Application
- explorer.exe (PID: 1936)
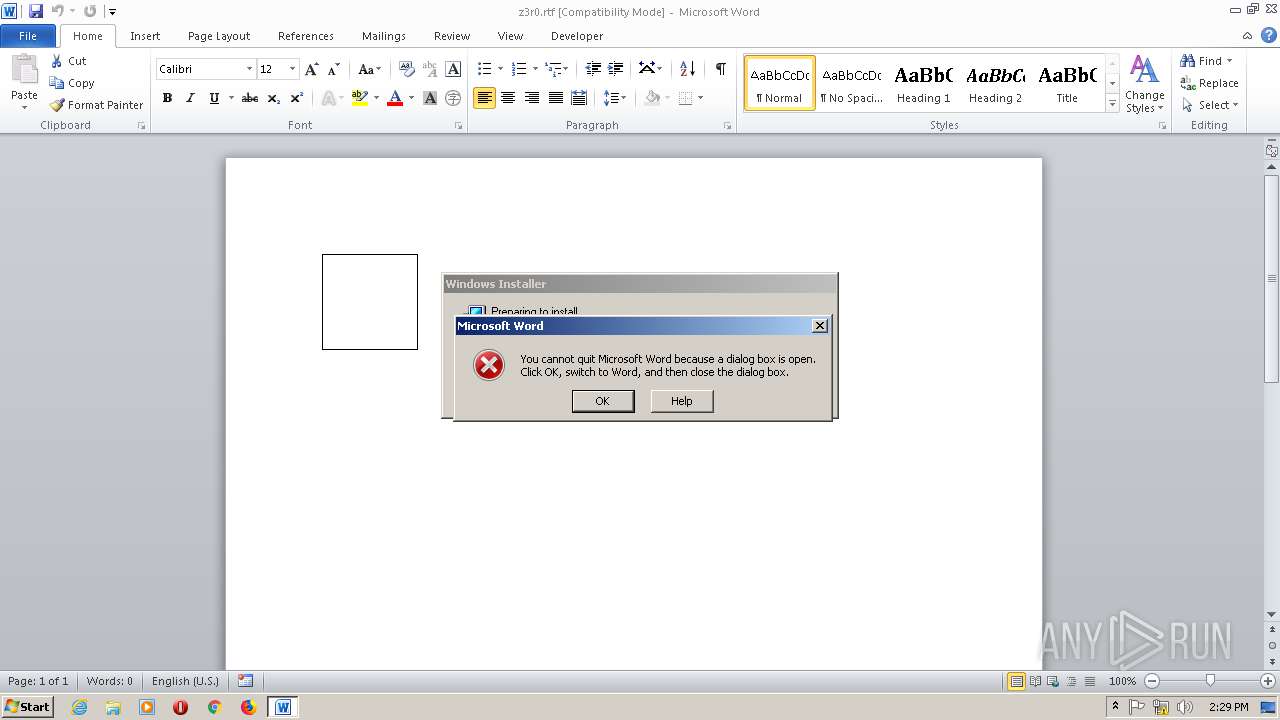
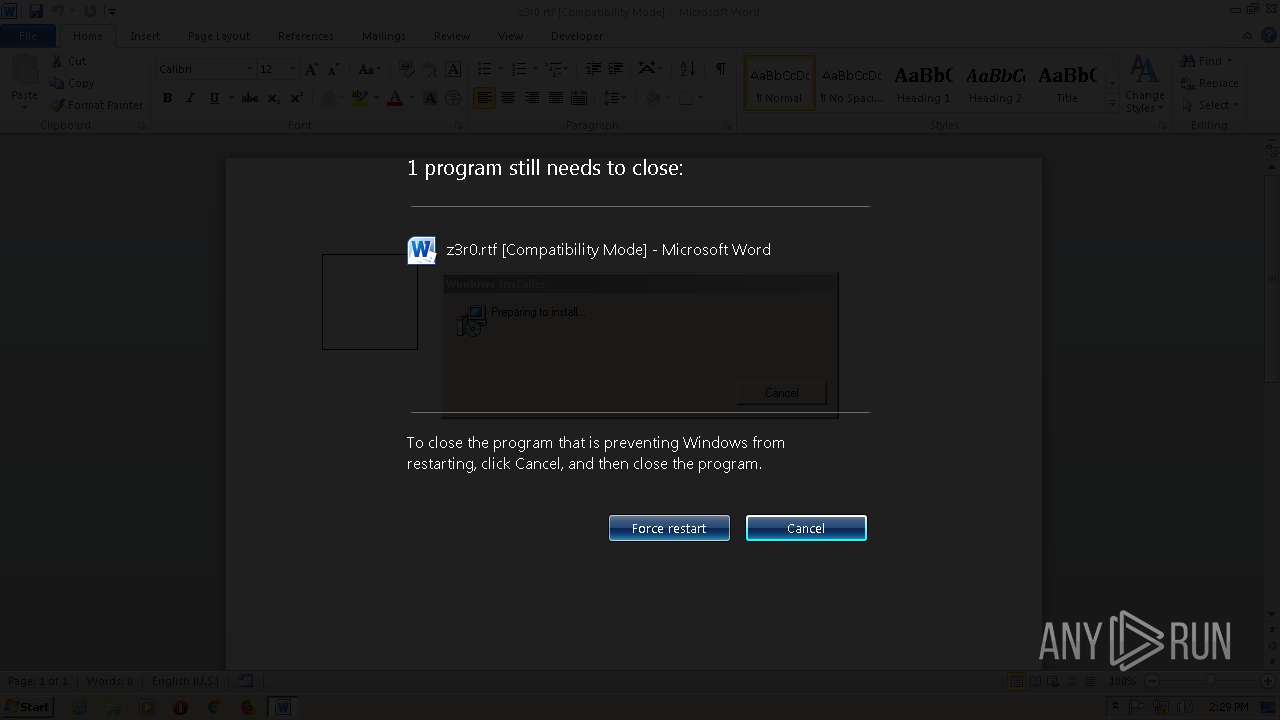
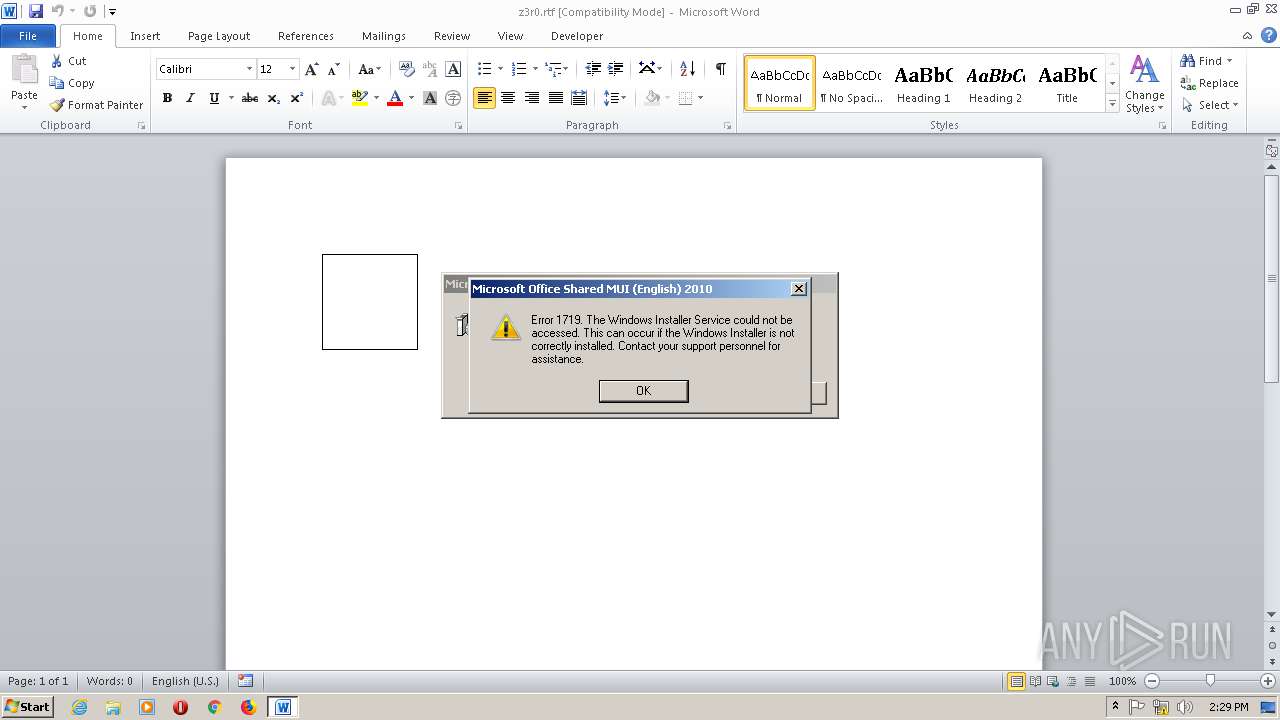
Application was crashed
- EQNEDT32.EXE (PID: 1788)
- EQNEDT32.EXE (PID: 2908)
Creates files in the user directory
- WINWORD.EXE (PID: 2816)
Reads the machine GUID from the registry
- WINWORD.EXE (PID: 2816)
Reads settings of System Certificates
- Setup.exe (PID: 992)
Creates files in the program directory
- MsiExec.exe (PID: 2632)
- MsiExec.exe (PID: 2784)
- MsiExec.exe (PID: 2356)
- msiexec.exe (PID: 1472)
- MsiExec.exe (PID: 2944)
- MsiExec.exe (PID: 2660)
- MsiExec.exe (PID: 2700)
- MsiExec.exe (PID: 2376)
- MsiExec.exe (PID: 2768)
- MsiExec.exe (PID: 480)
Writes to a desktop.ini file (may be used to cloak folders)
- msiexec.exe (PID: 1472)
Loads dropped or rewritten executable
- msiexec.exe (PID: 1472)
- MsiExec.exe (PID: 1684)
- MsiExec.exe (PID: 1364)
- MsiExec.exe (PID: 2784)
- MsiExec.exe (PID: 1832)
- MsiExec.exe (PID: 2356)
- MsiExec.exe (PID: 2288)
- MsiExec.exe (PID: 2944)
- MsiExec.exe (PID: 1092)
- MsiExec.exe (PID: 2932)
- MsiExec.exe (PID: 2260)
- MsiExec.exe (PID: 2528)
- MsiExec.exe (PID: 2660)
- MsiExec.exe (PID: 2972)
- MsiExec.exe (PID: 2608)
- MsiExec.exe (PID: 3048)
- MsiExec.exe (PID: 2700)
- MsiExec.exe (PID: 312)
- MsiExec.exe (PID: 2488)
- MsiExec.exe (PID: 1928)
- MsiExec.exe (PID: 2768)
- MsiExec.exe (PID: 2552)
- MsiExec.exe (PID: 2376)
- MsiExec.exe (PID: 1504)
- MsiExec.exe (PID: 1772)
- MsiExec.exe (PID: 480)
- MsiExec.exe (PID: 2564)
- MsiExec.exe (PID: 1836)
- MsiExec.exe (PID: 2632)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2816)
- Setup.exe (PID: 992)
- msiexec.exe (PID: 1472)
- msohtmed.exe (PID: 1012)
- MsiExec.exe (PID: 2564)
- msohtmed.exe (PID: 564)
Application launched itself
- msiexec.exe (PID: 1472)
Creates a software uninstall entry
- msiexec.exe (PID: 1472)
Dropped object may contain Bitcoin addresses
- msiexec.exe (PID: 1472)
Manual execution by user
- runonce.exe (PID: 2112)
- IMEKLMG.EXE (PID: 1376)
- IMEKLMG.EXE (PID: 2968)
Starts application with an unusual extension
- msiexec.exe (PID: 1472)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
129
Monitored processes
51
Malicious processes
7
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 124 | C:\Windows\syswow64\MsiExec.exe -Embedding 2429B2E20F24DB52ED6E71202754B6BA | C:\Windows\syswow64\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 304 | "C:\Windows\Installer\MSI809E.tmp" ms-help://Hx | C:\Windows\Installer\MSI809E.tmp | — | msiexec.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1603 Modules
| |||||||||||||||
| 312 | C:\Windows\system32\MsiExec.exe -Embedding 745873035EB6BFE33931EBDA26F8F4D5 | C:\Windows\system32\MsiExec.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 480 | C:\Windows\system32\MsiExec.exe -Embedding 1F4532C322A821B3522C4CDC2DA03BC0 E Global\MSI0000 | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 564 | "C:\Program Files\Microsoft Office\Office14\msohtmed.exe" /regserverfp | C:\Program Files\Microsoft Office\Office14\msohtmed.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Office 2010 component Exit code: 0 Version: 14.0.4730.1010 Modules
| |||||||||||||||
| 904 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 992 | "C:\Program Files\Common Files\Microsoft Shared\OFFICE14\Office Setup Controller\Setup.exe" -Embedding | C:\Program Files\Common Files\Microsoft Shared\OFFICE14\Office Setup Controller\Setup.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Setup Bootstrapper Exit code: 1073807364 Version: 14.0.4755.1000 Modules
| |||||||||||||||
| 1012 | "C:\Program Files\Microsoft Office\Office14\msohtmed.exe" /regserverfp | C:\Program Files\Microsoft Office\Office14\msohtmed.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Office 2010 component Exit code: 0 Version: 14.0.4730.1010 Modules
| |||||||||||||||
| 1092 | C:\Windows\system32\MsiExec.exe -Embedding 7167DCF4CEF80C868EDD12F9192058F1 | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1364 | C:\Windows\system32\MsiExec.exe -Embedding 9FC01BC9E90E1CD9A7A08127AD00BBCF | C:\Windows\system32\MsiExec.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
35 846
Read events
22 818
Write events
12 062
Delete events
966
Modification events
| (PID) Process: | (2816) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | !8< |
Value: 21383C00000B0000010000000000000000000000 | |||
| (PID) Process: | (2816) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2816) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2816) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (2816) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2816) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2816) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2816) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2816) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2816) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
Executable files
402
Suspicious files
47
Text files
75
Unknown types
159
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2816 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR5011.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2500 | WerFault.exe | C:\Users\admin\AppData\Local\Temp\WER6CB3.tmp.hdmp | — | |
MD5:— | SHA256:— | |||
| 2500 | WerFault.exe | C:\Users\admin\AppData\Local\Temp\WER6D8F.tmp.mdmp | — | |
MD5:— | SHA256:— | |||
| 2456 | WerFault.exe | C:\Users\admin\AppData\Local\Temp\WERFB58.tmp.mdmp | — | |
MD5:— | SHA256:— | |||
| 2816 | WINWORD.EXE | C:\Users\admin\Desktop\~$z3r0.rtf | pgc | |
MD5:— | SHA256:— | |||
| 2500 | WerFault.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\WER\ReportQueue\AppCrash_EQNEDT32.EXE_67557343b893ec8761487d58d5a5eebb314b7_cab_09d56dda\Report.wer | binary | |
MD5:— | SHA256:— | |||
| 2500 | WerFault.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\WER\ReportQueue\AppCrash_EQNEDT32.EXE_67557343b893ec8761487d58d5a5eebb314b7_cab_09d56dda\WER6CB3.tmp.hdmp | dmp | |
MD5:— | SHA256:— | |||
| 2500 | WerFault.exe | C:\Users\admin\AppData\Local\Temp\WER6CA2.tmp.WERInternalMetadata.xml | xml | |
MD5:— | SHA256:— | |||
| 2500 | WerFault.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\WER\ReportQueue\AppCrash_EQNEDT32.EXE_67557343b893ec8761487d58d5a5eebb314b7_cab_09d56dda\WER6CA2.tmp.WERInternalMetadata.xml | xml | |
MD5:— | SHA256:— | |||
| 2500 | WerFault.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\WER\ReportQueue\AppCrash_EQNEDT32.EXE_67557343b893ec8761487d58d5a5eebb314b7_cab_09d56dda\WER6D8F.tmp.mdmp | dmp | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Domain | IP | Reputation |
|---|---|---|
teredo.ipv6.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
msiexec.exe | Failed to release Service
|
msiexec.exe | Failed to release Service
|
addinutil.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\amd64fre\base\isolation\com\copyout.cpp, line 1302
|
addinutil.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\amd64fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
addinutil.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\amd64fre\base\isolation\com\copyout.cpp, line 1302
|
addinutil.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\amd64fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
addinutil.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\amd64fre\base\isolation\com\copyout.cpp, line 1302
|
addinutil.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\amd64fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
addinutil.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\amd64fre\base\isolation\com\copyout.cpp, line 1302
|
addinutil.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\amd64fre\base\isolation\com\enumidentityattribute.cpp, line 144
|