| File name: | DiagnosticoItau.exe |
| Full analysis: | https://app.any.run/tasks/b8e776fa-bb6b-4916-bd74-8f68fbece7fc |
| Verdict: | Malicious activity |
| Analysis date: | November 22, 2019, 16:23:58 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | E62445423F3C0F78EC4835058FFB926B |
| SHA1: | B2C7D4D7DF2C9C52BC3B7DE335AEB3720A9ED639 |
| SHA256: | B552D60C7F66593FB6A33367EAD28FD15E2837291B223309F5E69ACAF0422175 |
| SSDEEP: | 98304:h8Zd2+CuZw/kIVEPolHpo30DCaZZk8ymjcvnvXUU7uSmnhRa:X+CuUJlXGaZulnvXtDOhRa |
MALICIOUS
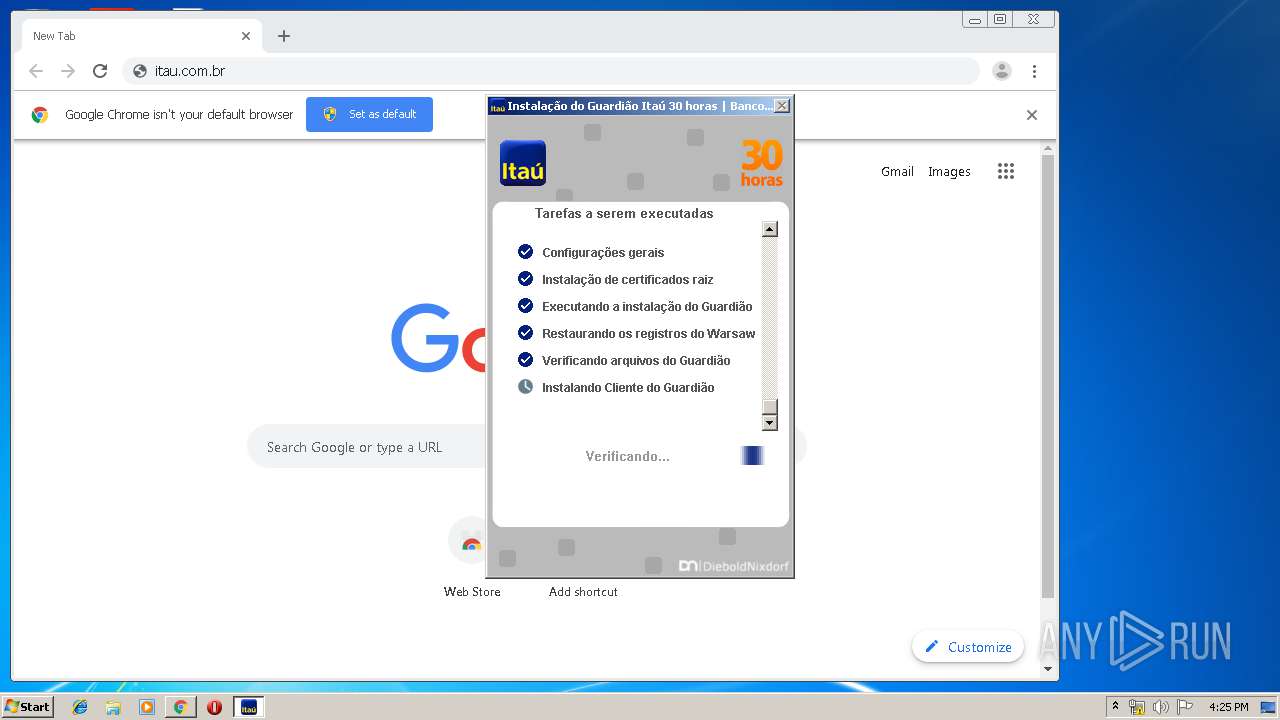
Changes settings of System certificates
- DiagnosticoItau.exe (PID: 2440)
- core.exe (PID: 516)
Application was dropped or rewritten from another process
- warsaw_setup_32.tmp (PID: 1908)
- warsaw_setup_32.exe (PID: 2448)
- get_version.exe (PID: 1852)
- get_version.exe (PID: 3404)
- impersonate.exe (PID: 3452)
- corefixer.exe (PID: 3092)
- core.exe (PID: 3840)
- core.exe (PID: 516)
- core.exe (PID: 3756)
- ffcu.dat (PID: 3576)
- wsffcmgr.exe (PID: 3284)
- warsaw2.tt (PID: 624)
Loads the Task Scheduler COM API
- corefixer.exe (PID: 3092)
Loads dropped or rewritten executable
- core.exe (PID: 516)
- core.exe (PID: 3756)
- rundll32.exe (PID: 4048)
- rundll32.exe (PID: 1884)
- chrome.exe (PID: 932)
- chrome.exe (PID: 3936)
- chrome.exe (PID: 2712)
- chrome.exe (PID: 1536)
- rundll32.exe (PID: 2728)
- core.exe (PID: 3840)
- chrome.exe (PID: 2308)
- chrome.exe (PID: 2356)
- DiagnosticoItau.exe (PID: 2372)
- chrome.exe (PID: 2156)
- chrome.exe (PID: 2504)
- chrome.exe (PID: 1788)
- iexplore.exe (PID: 1956)
- iexplore.exe (PID: 1364)
- warsaw2.tt (PID: 624)
- chrome.exe (PID: 1648)
SUSPICIOUS
Application launched itself
- DiagnosticoItau.exe (PID: 2372)
- core.exe (PID: 516)
Executed as Windows Service
- DiagnosticoItau.exe (PID: 2440)
- core.exe (PID: 516)
- vssvc.exe (PID: 3996)
Creates files in the program directory
- DiagnosticoItau.exe (PID: 2372)
- DiagnosticoItau.exe (PID: 2440)
- warsaw_setup_32.tmp (PID: 1908)
- core.exe (PID: 516)
Reads Internet Cache Settings
- DiagnosticoItau.exe (PID: 2372)
Creates files in the user directory
- DiagnosticoItau.exe (PID: 2372)
- wsffcmgr.exe (PID: 3284)
- ffcu.dat (PID: 3576)
Executable content was dropped or overwritten
- DiagnosticoItau.exe (PID: 2372)
- warsaw_setup_32.exe (PID: 2448)
- warsaw_setup_32.tmp (PID: 1908)
- core.exe (PID: 516)
- DrvInst.exe (PID: 3132)
- DiagnosticoItau.exe (PID: 2440)
Creates files in the Windows directory
- warsaw_setup_32.exe (PID: 2448)
- warsaw_setup_32.tmp (PID: 1908)
- get_version.exe (PID: 1852)
- cmd.exe (PID: 2760)
- core.exe (PID: 516)
- DrvInst.exe (PID: 3132)
- core.exe (PID: 3756)
- warsaw2.tt (PID: 624)
Reads Windows owner or organization settings
- warsaw_setup_32.tmp (PID: 1908)
Reads the Windows organization settings
- warsaw_setup_32.tmp (PID: 1908)
Starts SC.EXE for service management
- warsaw_setup_32.tmp (PID: 1908)
Creates files in the driver directory
- warsaw_setup_32.tmp (PID: 1908)
- DrvInst.exe (PID: 3132)
- core.exe (PID: 516)
Removes files from Windows directory
- warsaw_setup_32.tmp (PID: 1908)
- warsaw_setup_32.exe (PID: 2448)
- core.exe (PID: 516)
- DrvInst.exe (PID: 3132)
Creates a software uninstall entry
- warsaw_setup_32.tmp (PID: 1908)
Uses RUNDLL32.EXE to load library
- impersonate.exe (PID: 3452)
- warsaw_setup_32.tmp (PID: 1908)
Creates or modifies windows services
- core.exe (PID: 516)
Starts CMD.EXE for commands execution
- warsaw_setup_32.tmp (PID: 1908)
- cmd.exe (PID: 2760)
Uses TASKLIST.EXE to query information about running processes
- cmd.exe (PID: 3540)
- cmd.exe (PID: 2760)
Modifies files in Chrome extension folder
- chrome.exe (PID: 932)
Executed via COM
- DrvInst.exe (PID: 3132)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 3084)
Loads DLL from Mozilla Firefox
- wsffcmgr.exe (PID: 3284)
- ffcu.dat (PID: 3576)
Starts application with an unusual extension
- DiagnosticoItau.exe (PID: 2440)
- core.exe (PID: 516)
Reads the BIOS version
- DiagnosticoItau.exe (PID: 2372)
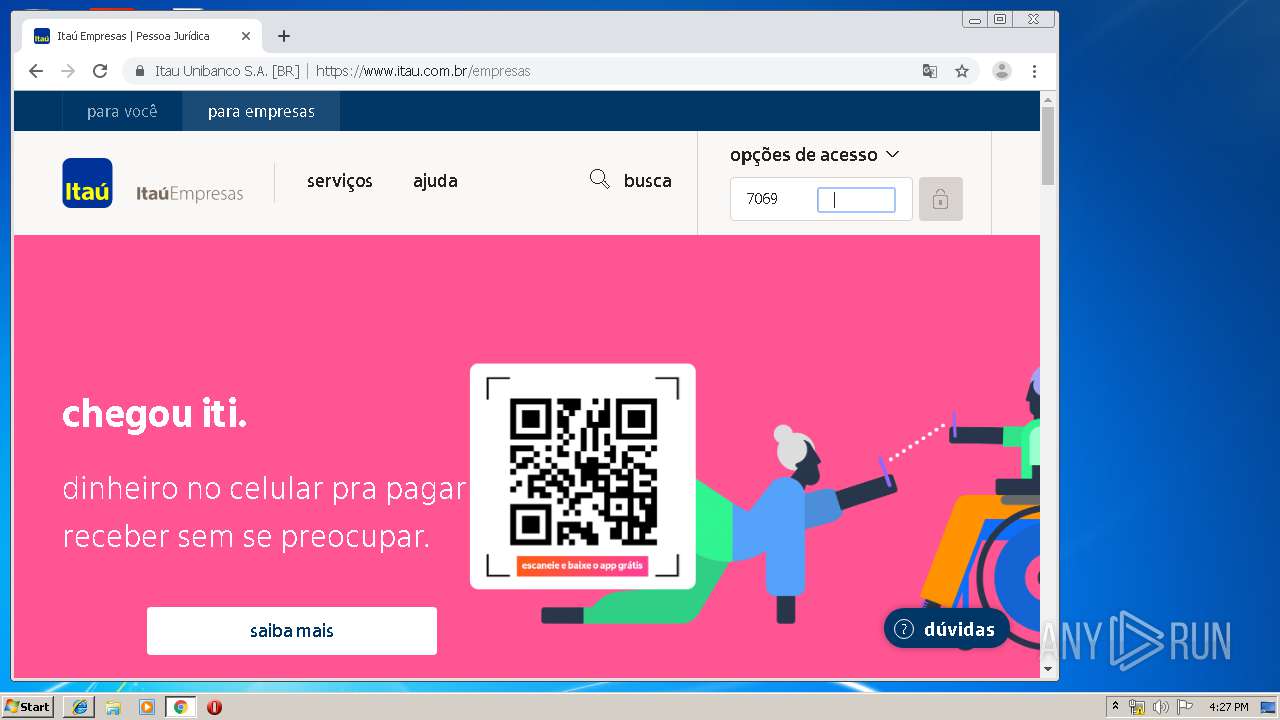
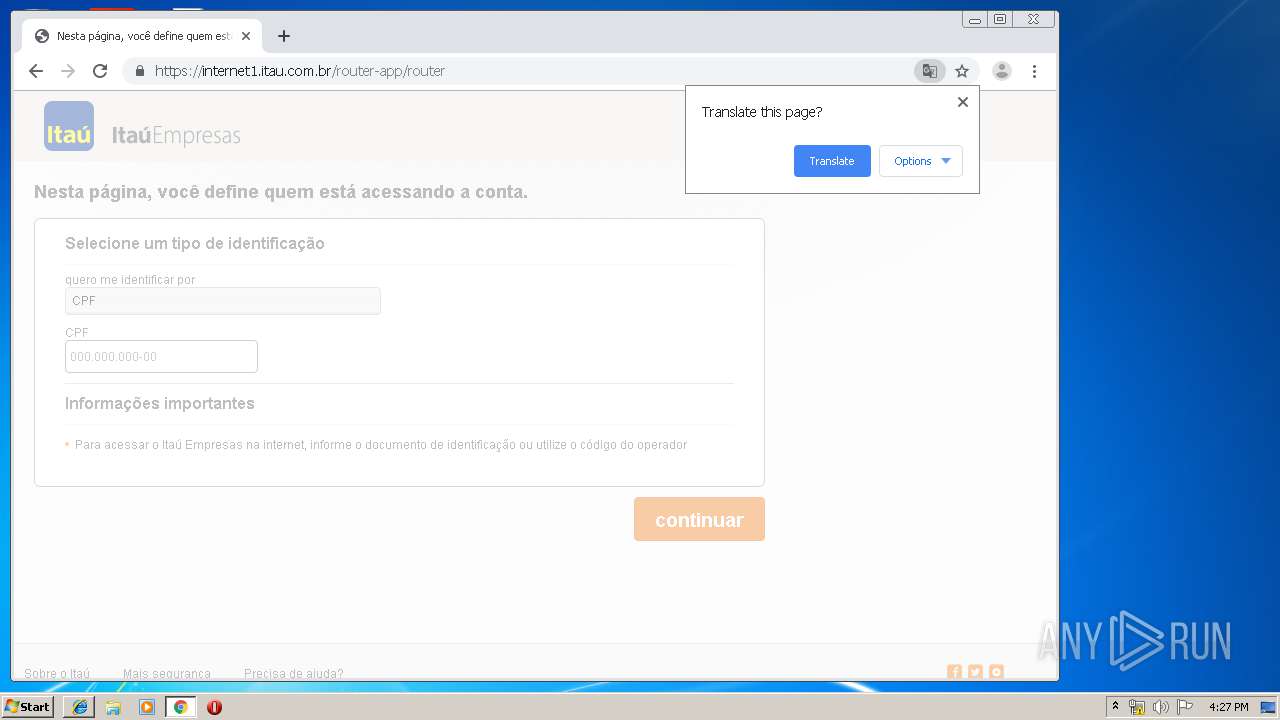
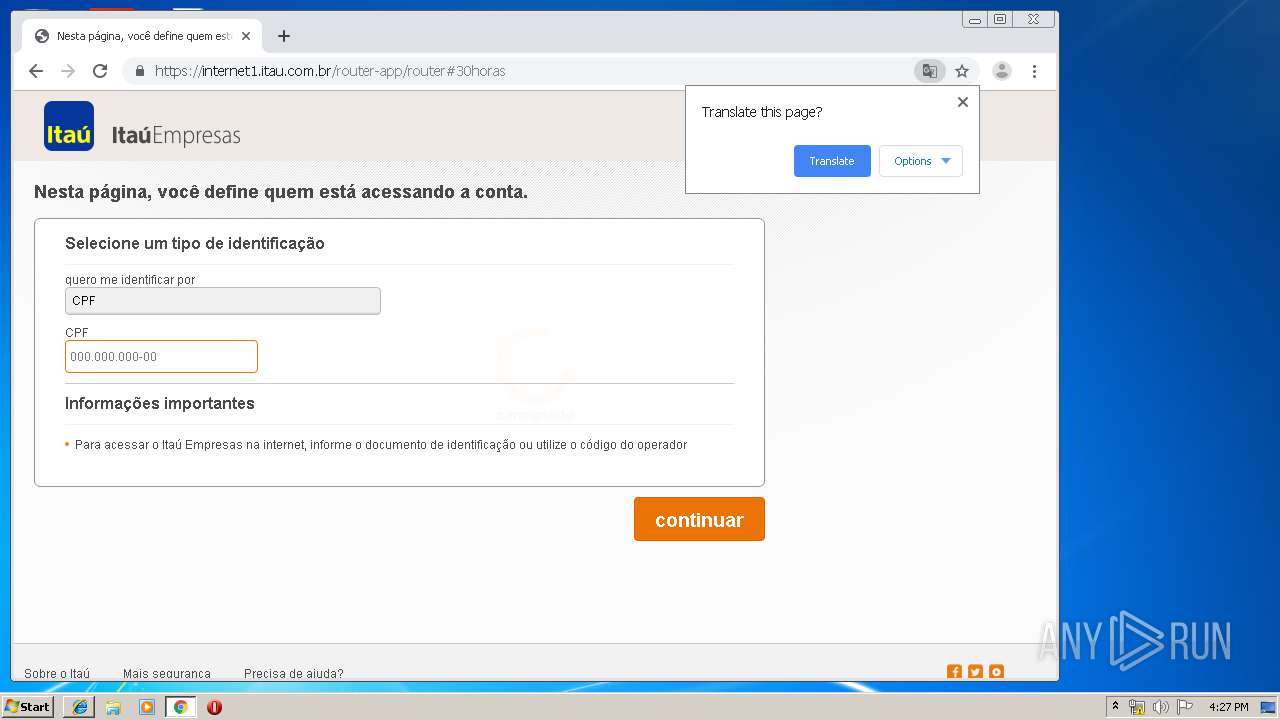
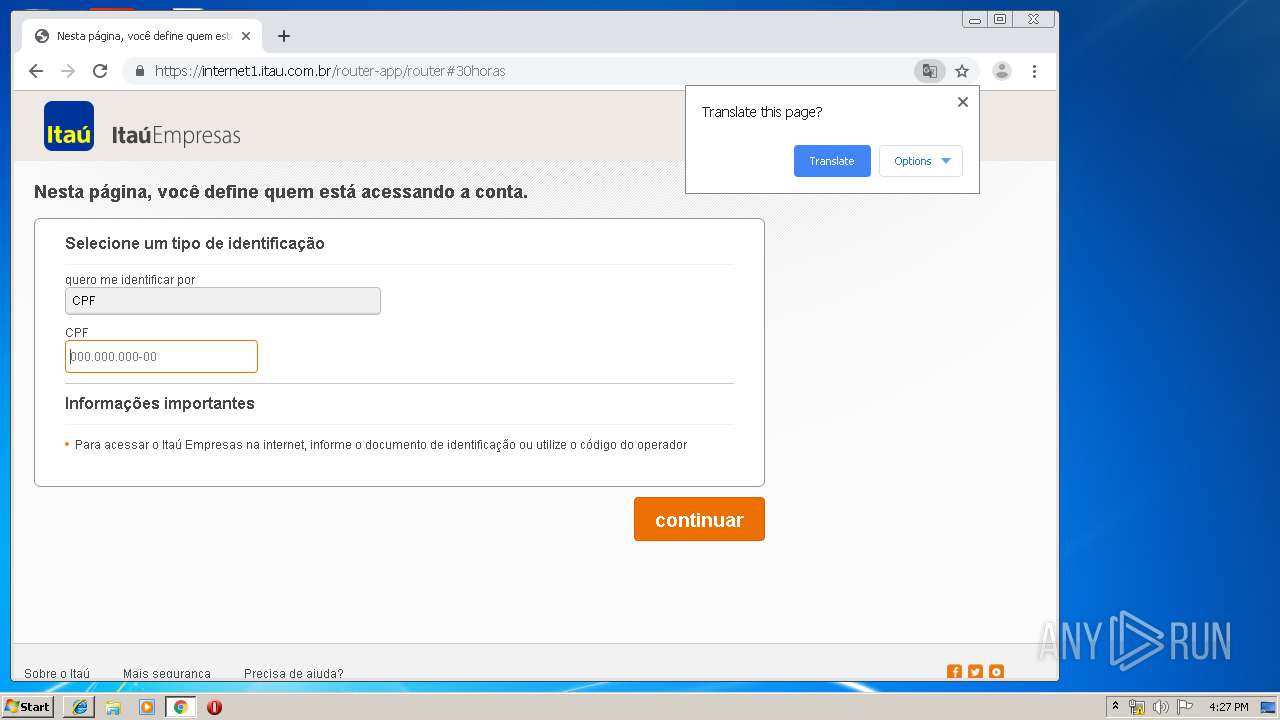
Starts Internet Explorer
- DiagnosticoItau.exe (PID: 2372)
Creates COM task schedule object
- core.exe (PID: 516)
INFO
Reads the hosts file
- DiagnosticoItau.exe (PID: 2440)
- chrome.exe (PID: 932)
- chrome.exe (PID: 2308)
- core.exe (PID: 516)
Manual execution by user
- chrome.exe (PID: 932)
Application launched itself
- chrome.exe (PID: 932)
- iexplore.exe (PID: 1956)
Reads settings of System Certificates
- DiagnosticoItau.exe (PID: 2440)
- core.exe (PID: 516)
- iexplore.exe (PID: 1956)
Changes settings of System certificates
- DrvInst.exe (PID: 3132)
- chrome.exe (PID: 2308)
Searches for installed software
- DrvInst.exe (PID: 3132)
Low-level read access rights to disk partition
- vssvc.exe (PID: 3996)
Reads internet explorer settings
- iexplore.exe (PID: 1364)
Changes internet zones settings
- iexplore.exe (PID: 1956)
Creates files in the user directory
- iexplore.exe (PID: 1364)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 3084)
Reads Internet Cache Settings
- iexplore.exe (PID: 1364)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:06:18 23:35:37+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 2442752 |
| InitializedDataSize: | 3443712 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1d047c |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.4.0.21 |
| ProductVersionNumber: | 2.4.0.21 |
| FileFlagsMask: | 0x001f |
| FileFlags: | Private build |
| FileOS: | Win32 |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | Unknown (0016) |
| CharacterSet: | Unicode |
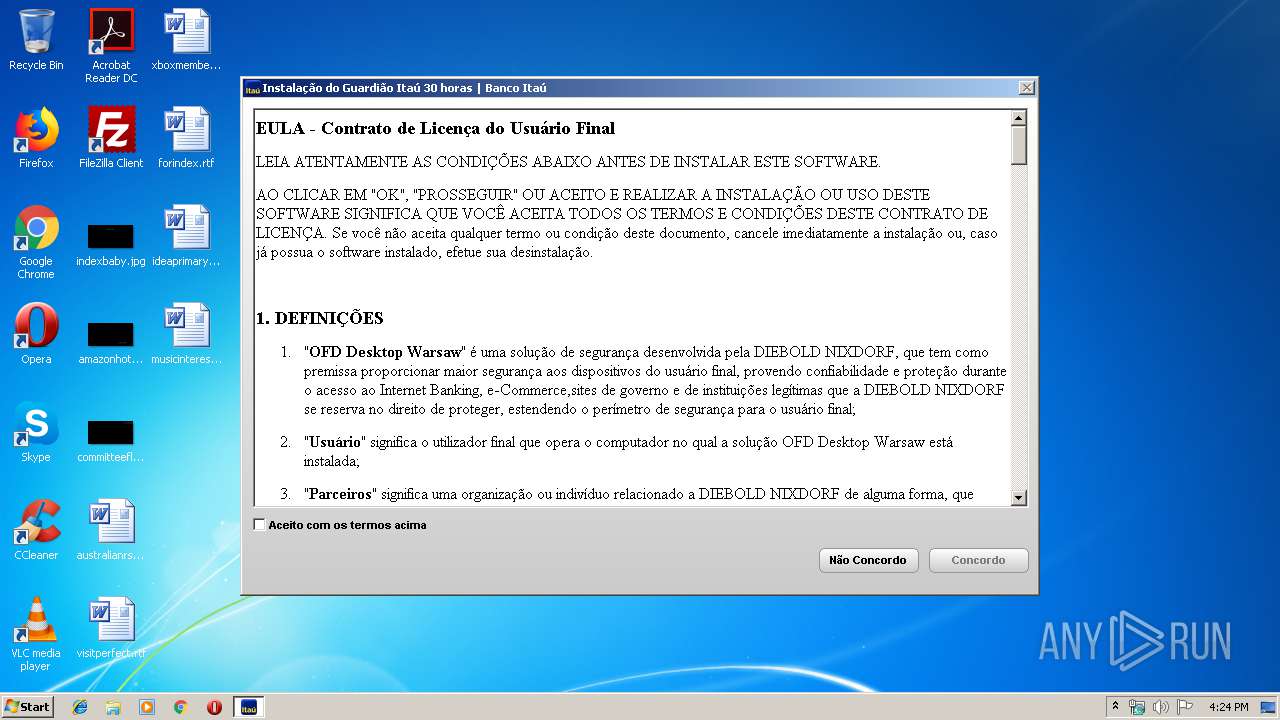
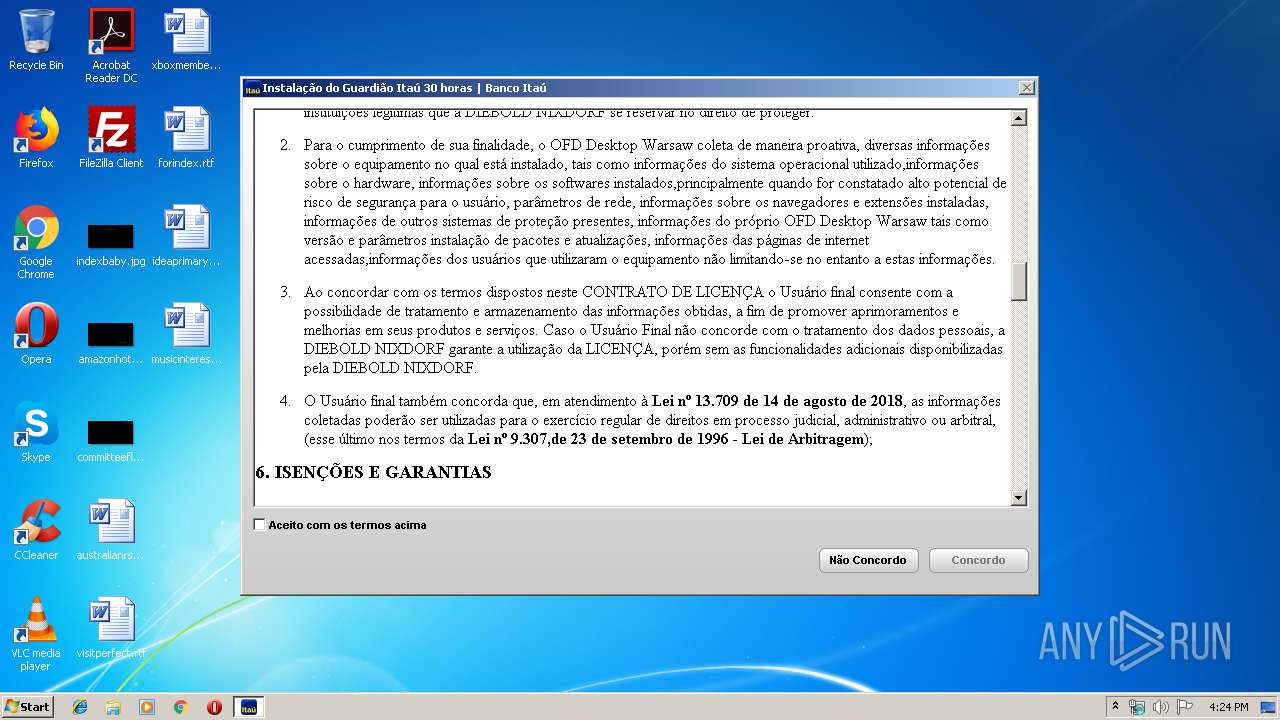
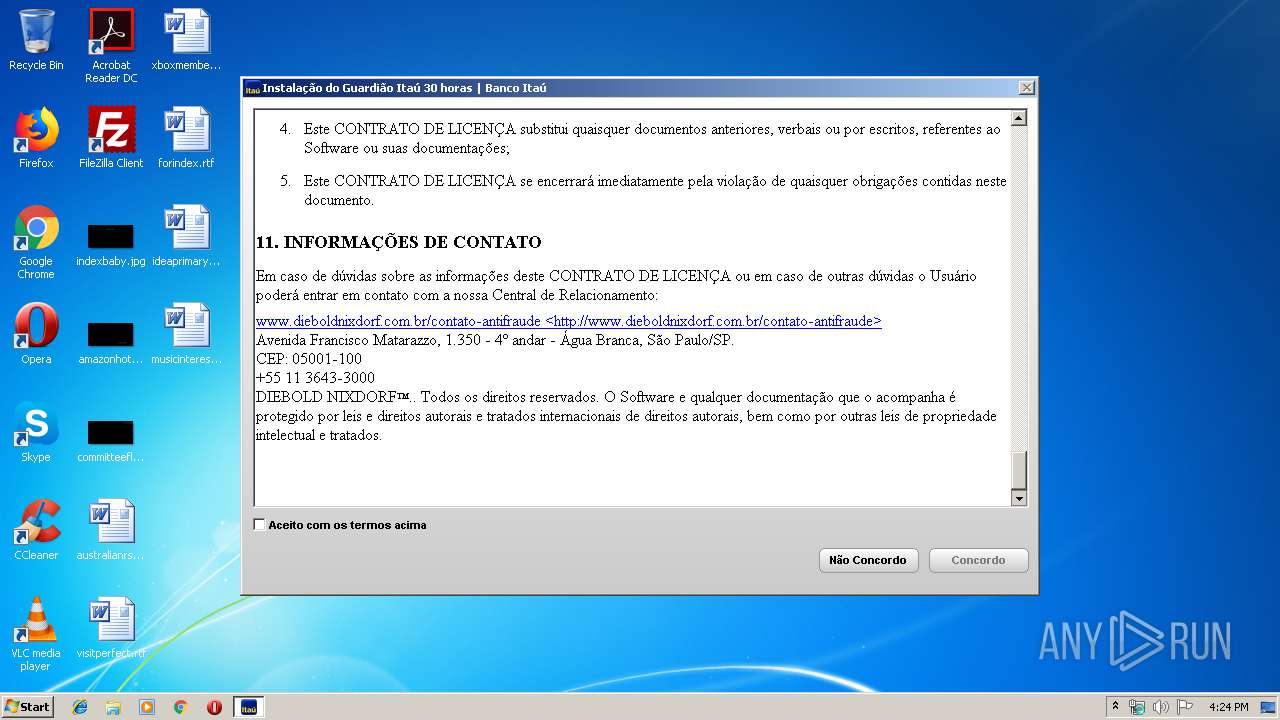
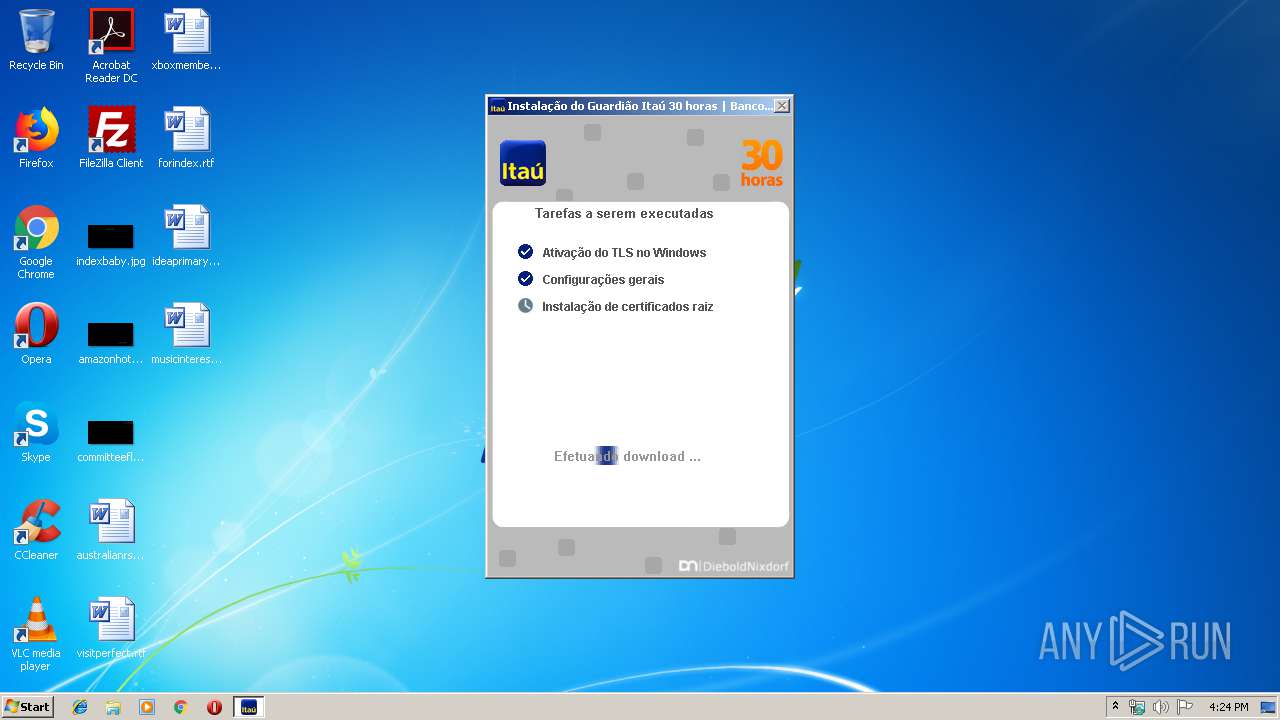
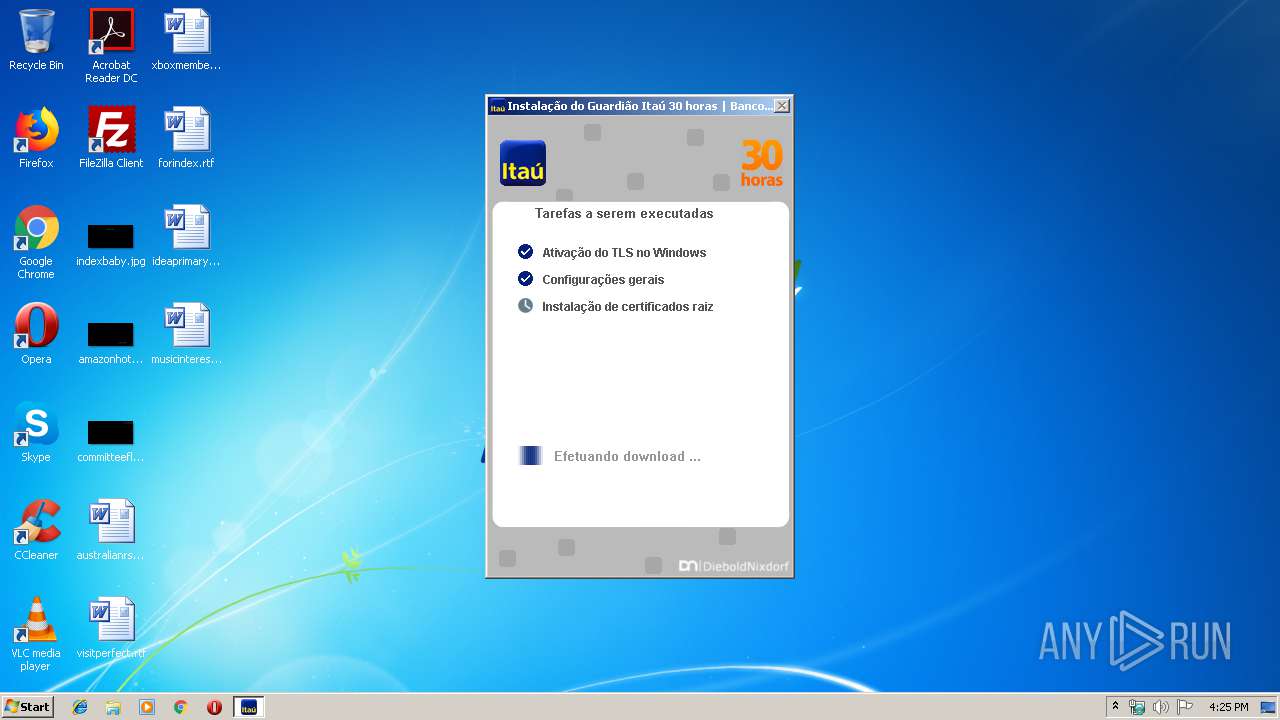
| CompanyName: | Banco Itaú |
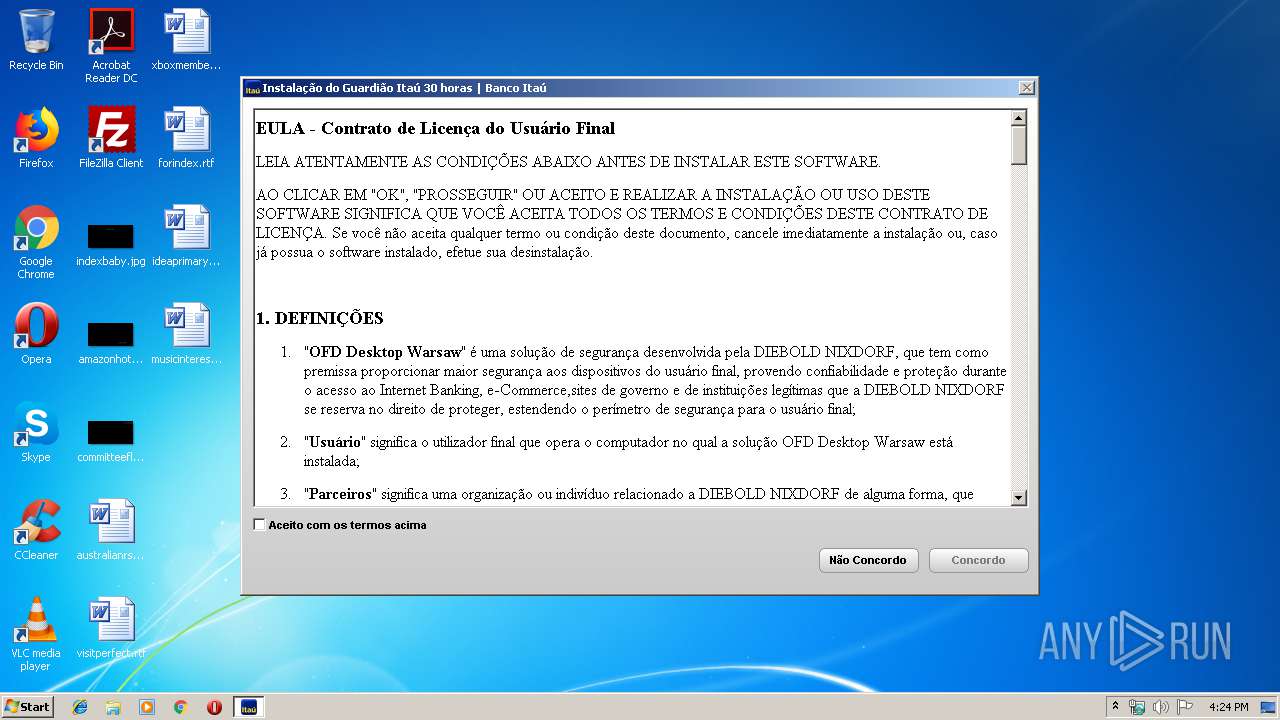
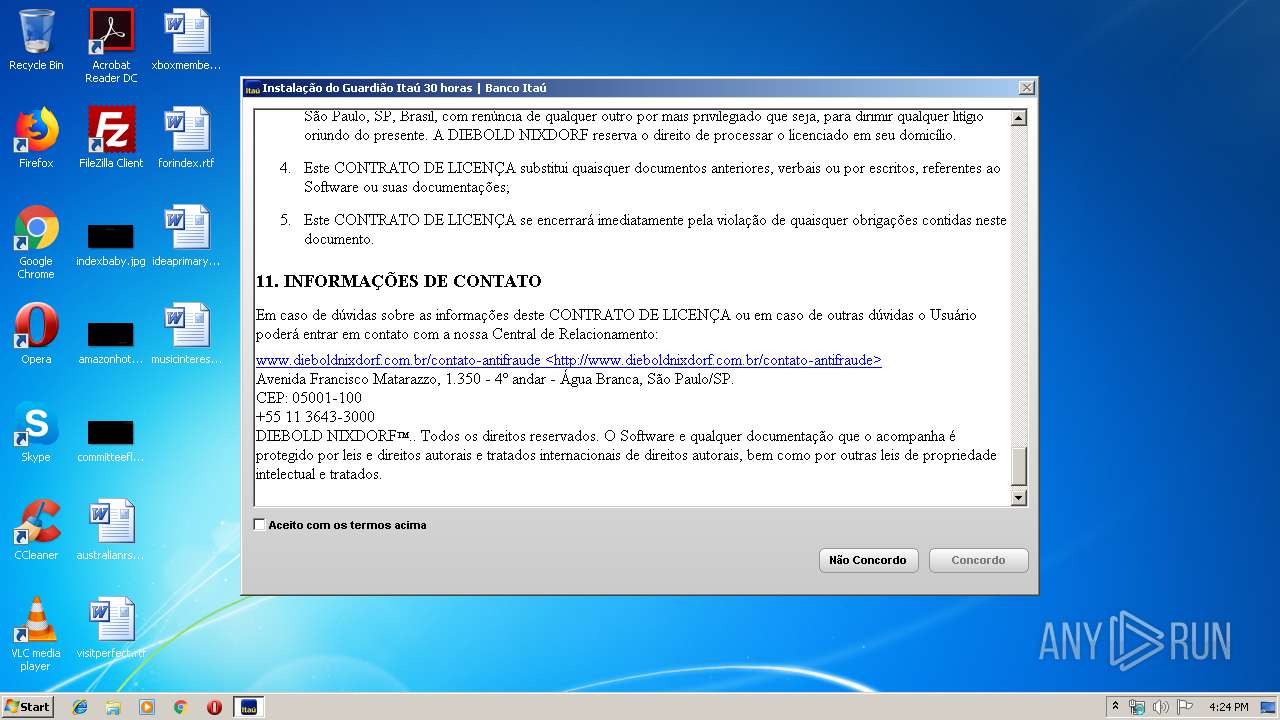
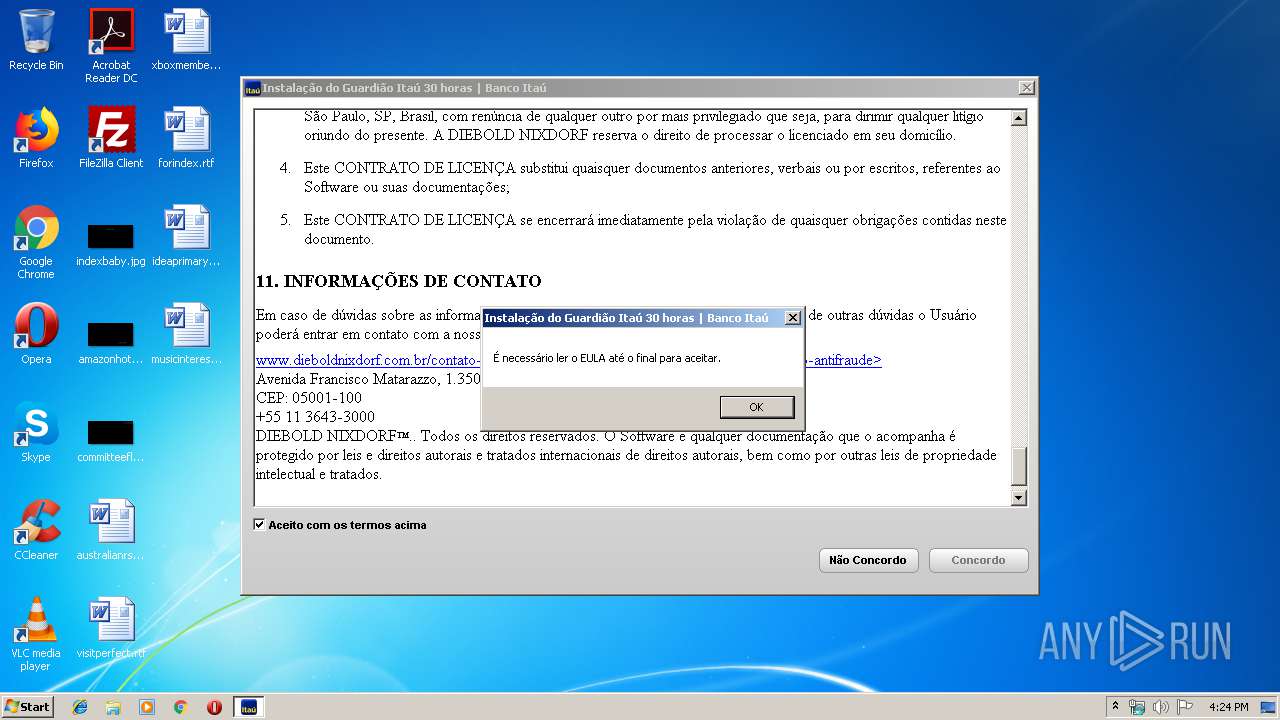
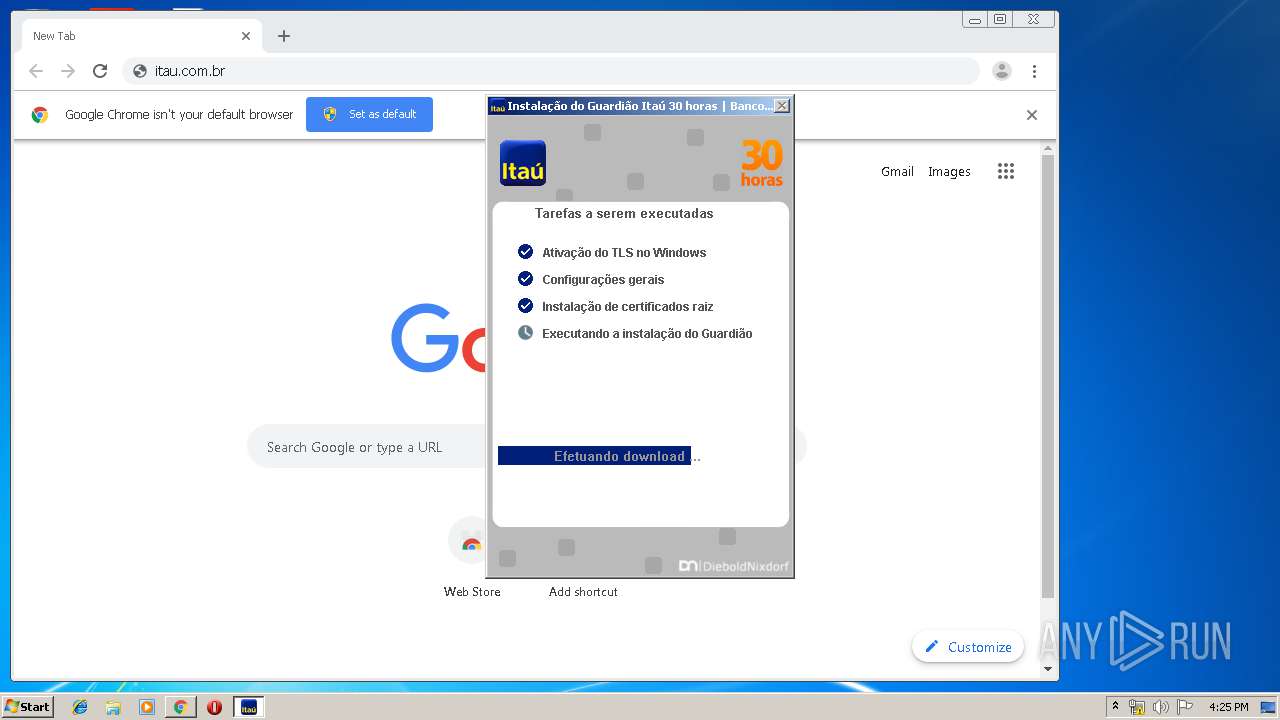
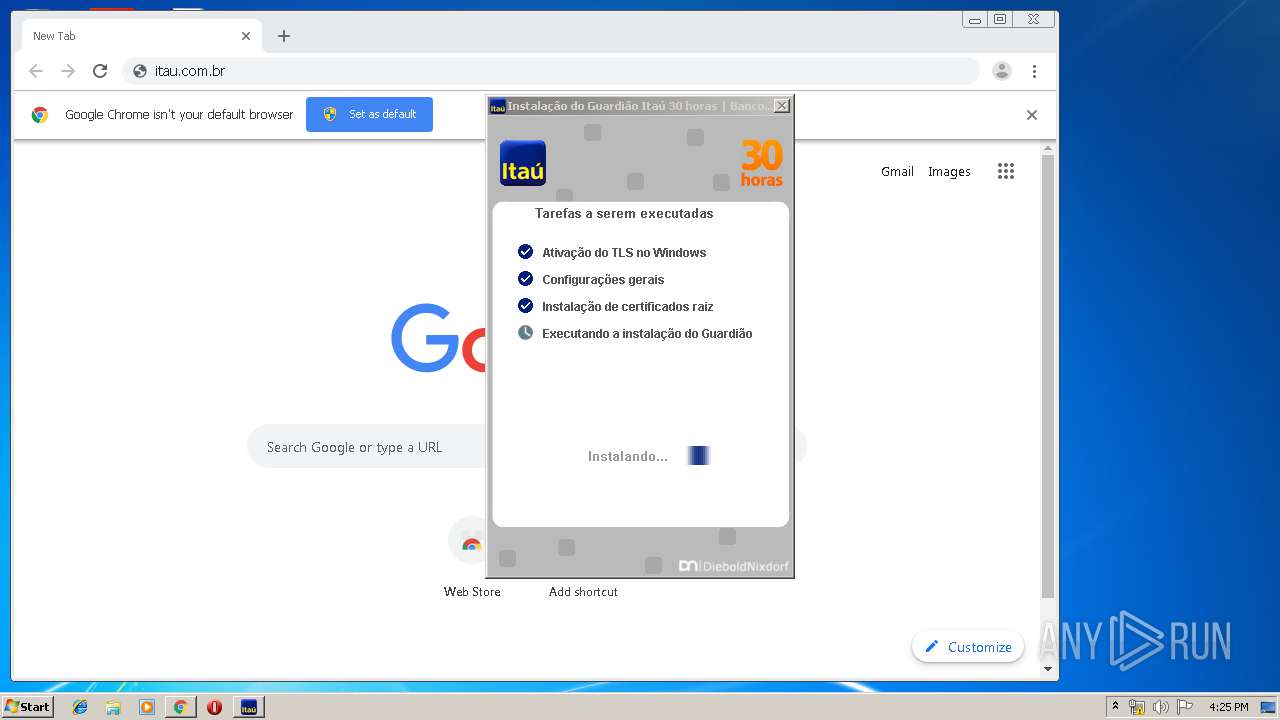
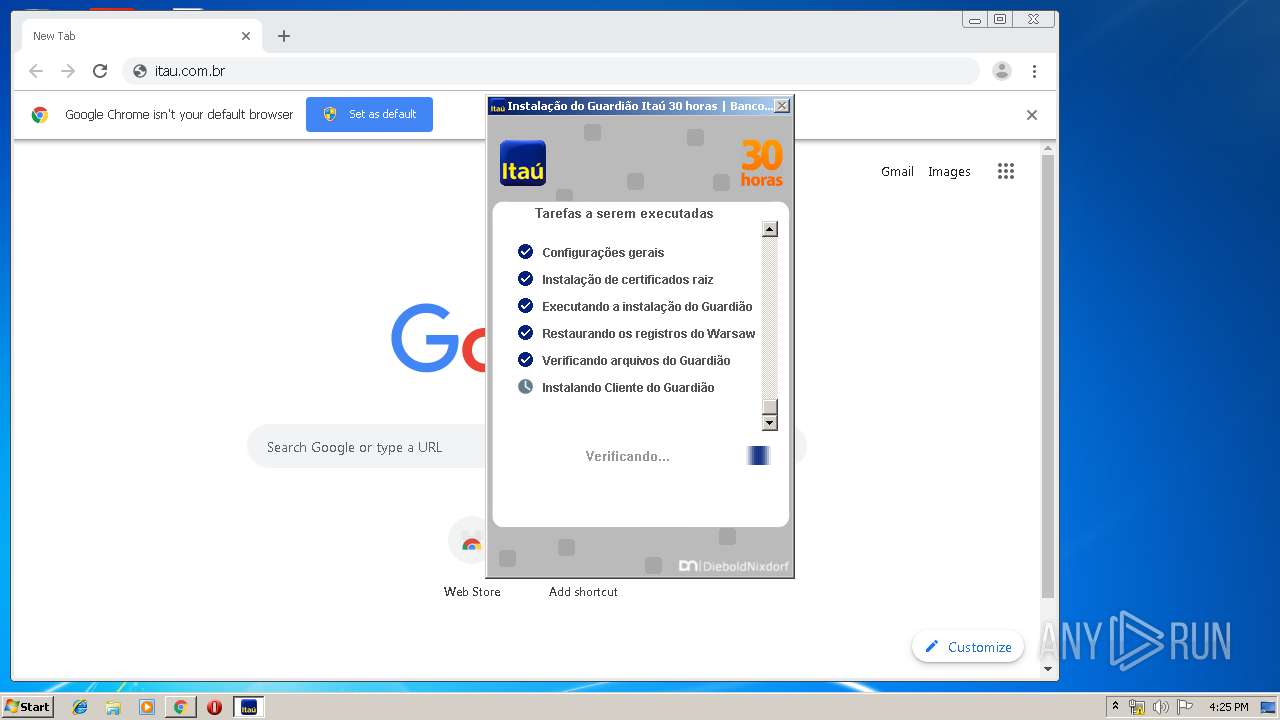
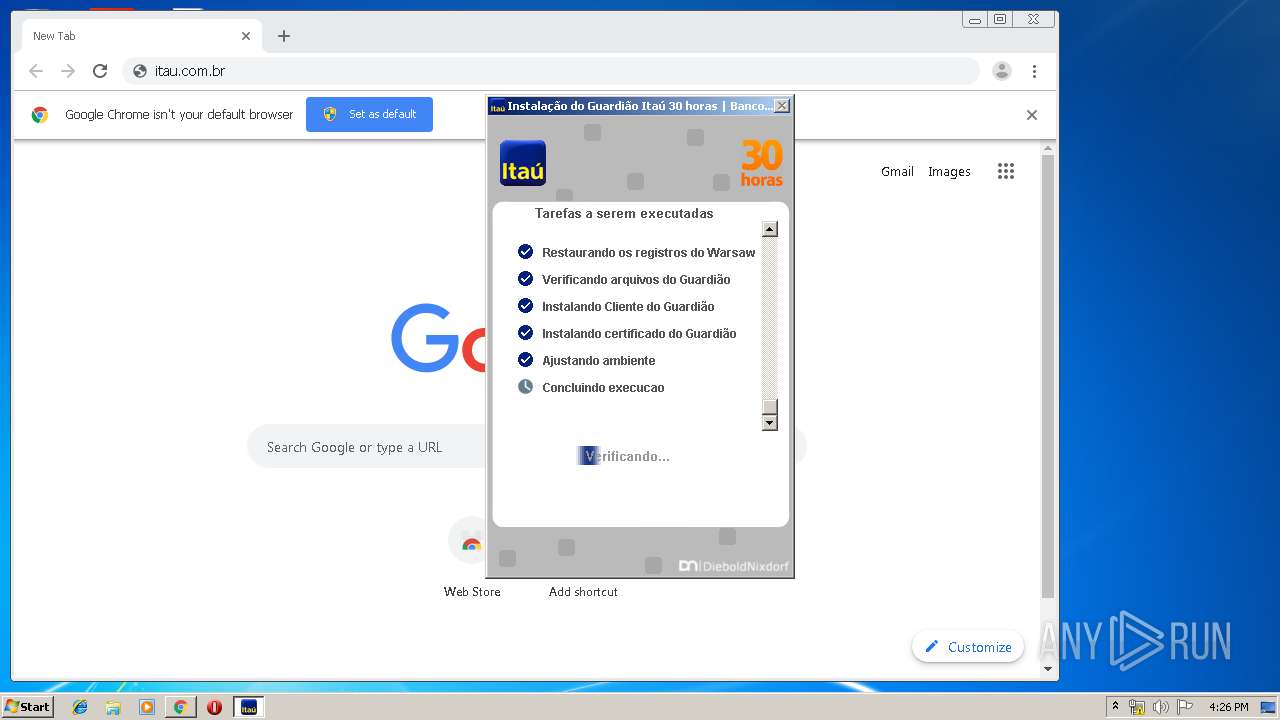
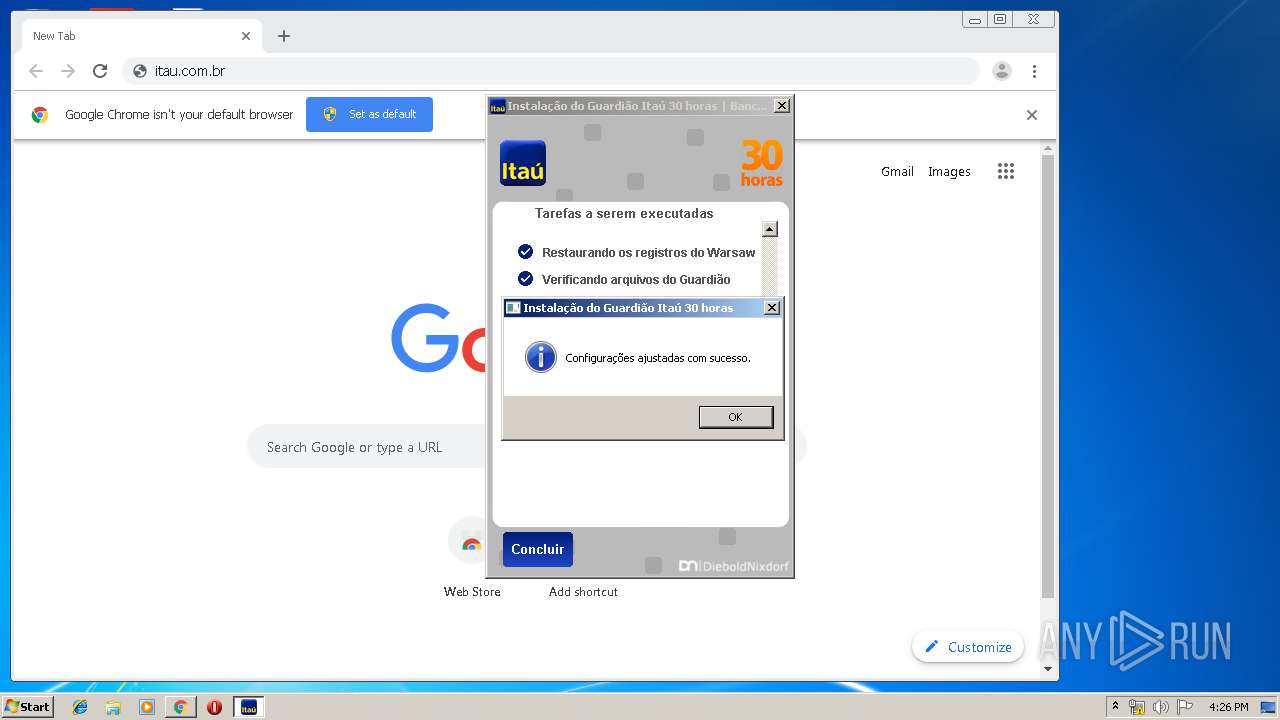
| FileDescription: | Instalação do Guardião Itaú 30 horas |
| FileVersion: | 2,4,0,21 |
| InternalName: | HDA |
| LegalCopyright: | Copyright © 2019, Banco Itaú |
| OriginalFileName: | DiagnosticoItau_PROD |
| PrivateBuild: | 2,4,0,21 |
| ProductName: | Instalação do Guardião Itaú 30 horas |
| ProductVersion: | 2,4,0,21 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 18-Jun-2019 21:35:37 |
| Detected languages: |
|
| TLS Callbacks: | 1 callback(s) detected. |
| Debug artifacts: |
|
| CompanyName: | Banco Itaú |
| FileDescription: | Instalação do Guardião Itaú 30 horas |
| FileVersion: | 2,4,0,21 |
| InternalName: | HDA |
| LegalCopyright: | Copyright © 2019, Banco Itaú |
| OriginalFilename: | DiagnosticoItau_PROD |
| PrivateBuild: | 2,4,0,21 |
| ProductName: | Instalação do Guardião Itaú 30 horas |
| ProductVersion: | 2,4,0,21 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 9 |
| Time date stamp: | 18-Jun-2019 21:35:37 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x002337DA | 0x00233800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.66262 |
CODE | 0x00235000 | 0x00020DA0 | 0x00020E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.59112 |
.rdata | 0x00256000 | 0x0004A64A | 0x0004A800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.44226 |
.data | 0x002A1000 | 0x000100E8 | 0x00009600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.16963 |
DATA | 0x002B2000 | 0x000014E0 | 0x00001600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.98456 |
BSS | 0x002B4000 | 0x00000761 | 0x00000800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.tls | 0x002B5000 | 0x00000002 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x002B6000 | 0x002C6B3C | 0x002C6C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.68171 |
.reloc | 0x0057D000 | 0x0002C09E | 0x0002C200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 5.13423 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.8253 | 872 | Latin 1 / Western European | Portuguese - Brazil | RT_MANIFEST |
2 | 6.32263 | 4264 | Latin 1 / Western European | Portuguese - Brazil | RT_ICON |
3 | 6.40717 | 1128 | Latin 1 / Western European | Portuguese - Brazil | RT_ICON |
101 | 7.55403 | 1283 | Latin 1 / Western European | Portuguese - Brazil | FILE |
104 | 7.88025 | 14083 | Latin 1 / Western European | Portuguese - Brazil | IMG |
105 | 6.62894 | 148 | Latin 1 / Western European | Portuguese - Brazil | IMG |
106 | 7.36799 | 454 | Latin 1 / Western European | Portuguese - Brazil | IMG |
107 | 7.62796 | 563 | Latin 1 / Western European | Portuguese - Brazil | IMG |
108 | 7.30965 | 465 | Latin 1 / Western European | Portuguese - Brazil | IMG |
112 | 7.87407 | 3199 | Latin 1 / Western European | Portuguese - Brazil | FILE |
Imports
ADVAPI32.dll |
COMCTL32.dll |
CRYPT32.dll |
GDI32.dll |
IPHLPAPI.DLL |
KERNEL32.dll |
MSIMG32.dll |
NETAPI32.dll |
OLEAUT32.dll |
PSAPI.DLL |
Total processes
112
Monitored processes
64
Malicious processes
12
Suspicious processes
8
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 392 | "sc" stop wsddfac | C:\Windows\system32\sc.exe | — | warsaw_setup_32.tmp | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: A tool to aid in developing services for WindowsNT Exit code: 1060 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 516 | "C:\Program Files\Diebold\Warsaw\core.exe" | C:\Program Files\Diebold\Warsaw\core.exe | services.exe | ||||||||||||
User: SYSTEM Company: GAS Tecnologia LTDA Integrity Level: SYSTEM Description: GAS Tecnologia - Core Exit code: 0 Version: 2.8.5.0 Modules
| |||||||||||||||
| 564 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,11779532103623131912,7251693750692203888,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7655119777194772734 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2488 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 624 | warsaw2.tt | C:\Program Files\Diebold\Warsaw\warsaw2.tt | — | core.exe | |||||||||||
User: SYSTEM Company: GAS Tecnologia LTDA Integrity Level: SYSTEM Description: GAS Tecnologia - Warsaw Tool Exit code: 0 Version: 1.0.3.1 Modules
| |||||||||||||||
| 716 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,11779532103623131912,7251693750692203888,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7756040732444848078 --mojo-platform-channel-handle=3708 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 788 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,11779532103623131912,7251693750692203888,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17443089539208595977 --mojo-platform-channel-handle=4288 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 836 | tasklist /FI "imagename eq core.exe" | C:\Windows\system32\tasklist.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Lists the current running tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 932 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1012 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,11779532103623131912,7251693750692203888,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11806695272639163930 --mojo-platform-channel-handle=3816 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1292 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,11779532103623131912,7251693750692203888,131072 --enable-features=PasswordImport --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11453408185112931582 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2232 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 550
Read events
1 672
Write events
868
Delete events
10
Modification events
| (PID) Process: | (2372) DiagnosticoItau.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2372) DiagnosticoItau.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2440) DiagnosticoItau.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | SecureProtocols |
Value: 512 | |||
| (PID) Process: | (2440) DiagnosticoItau.exe | Key: | HKEY_USERS\S-1-5-19\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | SecureProtocols |
Value: 512 | |||
| (PID) Process: | (2440) DiagnosticoItau.exe | Key: | HKEY_USERS\S-1-5-20\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | SecureProtocols |
Value: 512 | |||
| (PID) Process: | (2440) DiagnosticoItau.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | SecureProtocols |
Value: 672 | |||
| (PID) Process: | (2440) DiagnosticoItau.exe | Key: | HKEY_USERS\NTUSER.DAT\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | SecureProtocols |
Value: 512 | |||
| (PID) Process: | (2440) DiagnosticoItau.exe | Key: | HKEY_USERS\NTUSER.DAT\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | SecureProtocols |
Value: 672 | |||
| (PID) Process: | (2372) DiagnosticoItau.exe | Key: | HKEY_CURRENT_USER\Software\AutoHelpDesk |
| Operation: | write | Name: | RebootTasks |
Value: 9pq5gcGNUpw1o72MZjcjNA== | |||
| (PID) Process: | (2372) DiagnosticoItau.exe | Key: | HKEY_CURRENT_USER\Software\AutoHelpDesk |
| Operation: | write | Name: | RebootTasks |
Value: g8ExBMyKNCKVgy+Mq0M/71EgkjYteBIJoN8IpsDM4q8= | |||
Executable files
65
Suspicious files
191
Text files
516
Unknown types
65
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 932 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | — | |
MD5:— | SHA256:— | |||
| 932 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 932 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\c3df5b99-0762-4f17-b39b-f62dc954beba.tmp | — | |
MD5:— | SHA256:— | |||
| 932 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 932 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT | — | |
MD5:— | SHA256:— | |||
| 932 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT~RF3a5346.TMP | — | |
MD5:— | SHA256:— | |||
| 932 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 932 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 932 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF3a526b.TMP | text | |
MD5:— | SHA256:— | |||
| 932 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF3a526b.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
148
DNS requests
65
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
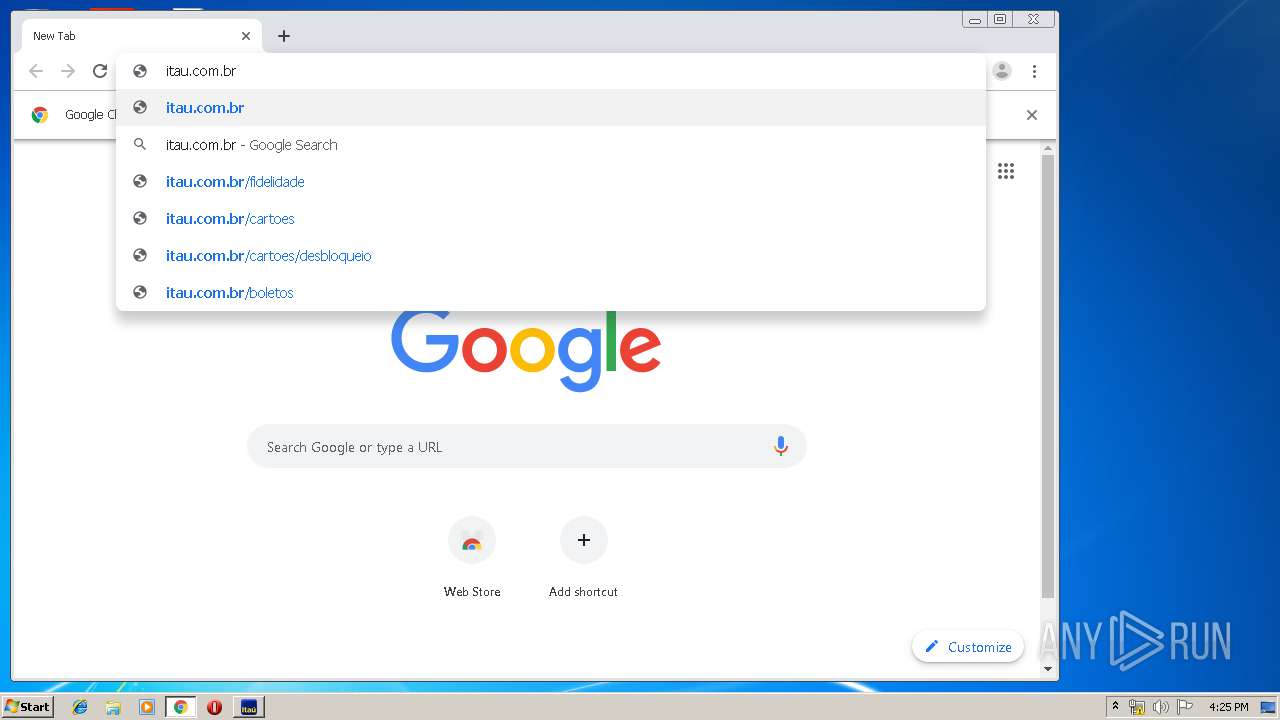
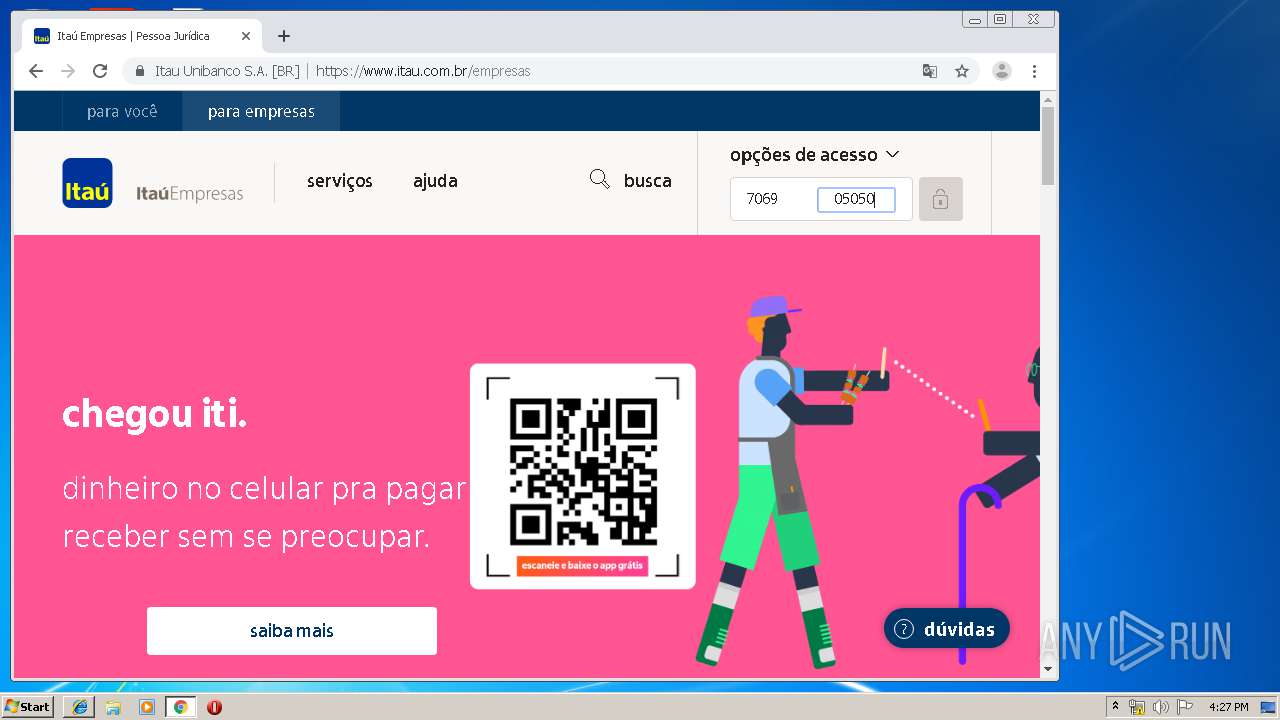
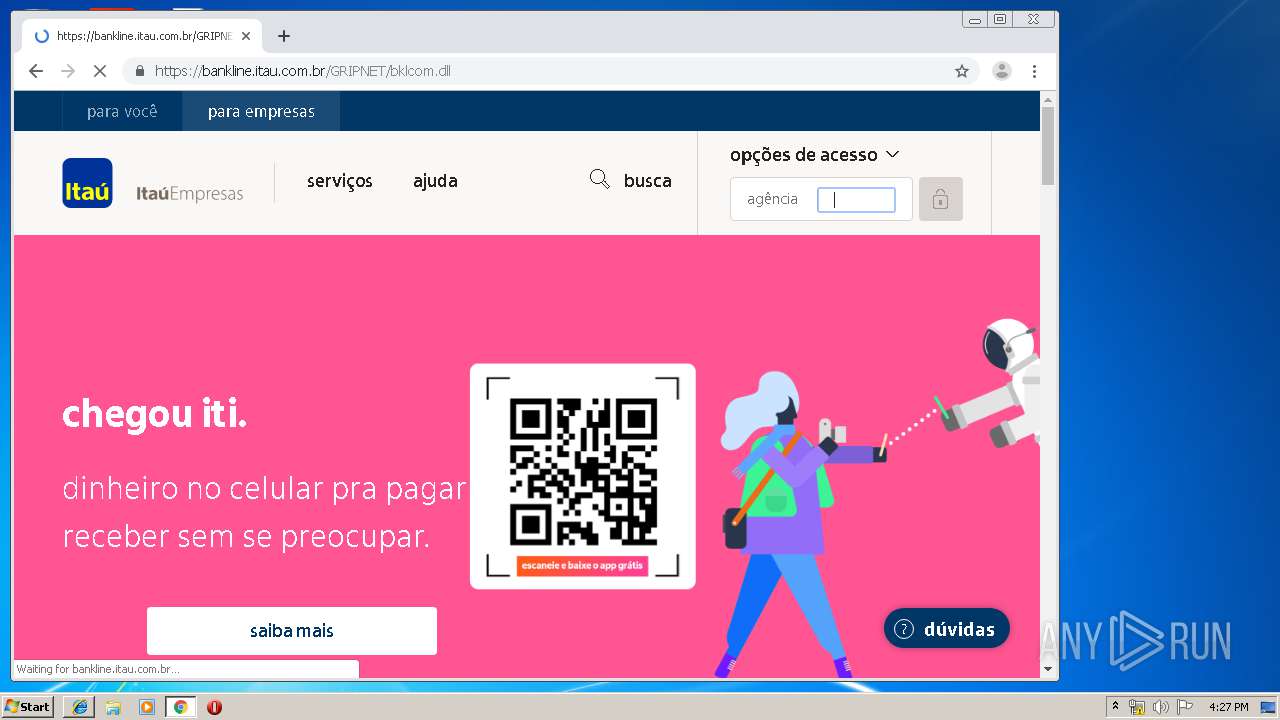
2308 | chrome.exe | GET | 301 | 23.4.252.20:80 | http://itau.com.br/ | NL | — | — | whitelisted |
2308 | chrome.exe | GET | 200 | 91.199.212.52:80 | http://crt.usertrust.com/USERTrustRSAAddTrustCA.crt | GB | der | 1.37 Kb | whitelisted |
2308 | chrome.exe | GET | 302 | 172.217.22.46:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 510 b | whitelisted |
2308 | chrome.exe | GET | 302 | 172.217.22.46:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 515 b | whitelisted |
2308 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAx5qUSwjBGVIJJhX%2BJrHYM%3D | US | der | 471 b | whitelisted |
2308 | chrome.exe | GET | 200 | 173.194.160.218:80 | http://r4---sn-hpa7zn7d.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=37.120.135.140&mm=28&mn=sn-hpa7zn7d&ms=nvh&mt=1574439807&mv=m&mvi=3&pl=24&shardbypass=yes | US | crx | 862 Kb | whitelisted |
3756 | core.exe | GET | 200 | 205.185.216.42:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.4 Kb | whitelisted |
3756 | core.exe | GET | 200 | 13.225.84.115:80 | http://x.ss2.us/x.cer | US | der | 1.27 Kb | whitelisted |
2308 | chrome.exe | GET | 200 | 74.125.153.7:80 | http://r1---sn-hpa7zne6.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mip=37.120.135.140&mm=28&mn=sn-hpa7zne6&ms=nvh&mt=1574439807&mv=m&mvi=0&pl=24&shardbypass=yes | US | crx | 293 Kb | whitelisted |
2372 | DiagnosticoItau.exe | GET | 200 | 150.162.159.4:80 | http://acraiz.icpbrasil.gov.br/ICP-Brasilv5.crt | BR | text | 2.30 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2372 | DiagnosticoItau.exe | 45.60.123.229:443 | www.digicert.com | — | US | suspicious |
2372 | DiagnosticoItau.exe | 104.109.54.101:443 | www.symantec.com | Akamai International B.V. | NL | whitelisted |
2372 | DiagnosticoItau.exe | 150.162.159.4:80 | acraiz.icpbrasil.gov.br | Universidade Federal de Santa Catarina | BR | unknown |
2308 | chrome.exe | 216.58.207.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2308 | chrome.exe | 216.58.208.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
2308 | chrome.exe | 216.58.205.227:443 | www.google.com.ua | Google Inc. | US | whitelisted |
2372 | DiagnosticoItau.exe | 2.18.234.32:443 | guardiao.itau.com.br | Akamai International B.V. | — | whitelisted |
2308 | chrome.exe | 172.217.22.106:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2308 | chrome.exe | 172.217.21.238:443 | ogs.google.com | Google Inc. | US | whitelisted |
2308 | chrome.exe | 216.58.206.14:443 | apis.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.digicert.com |
| whitelisted |
www.symantec.com |
| whitelisted |
acraiz.icpbrasil.gov.br |
| unknown |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
guardiao.itau.com.br |
| suspicious |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |