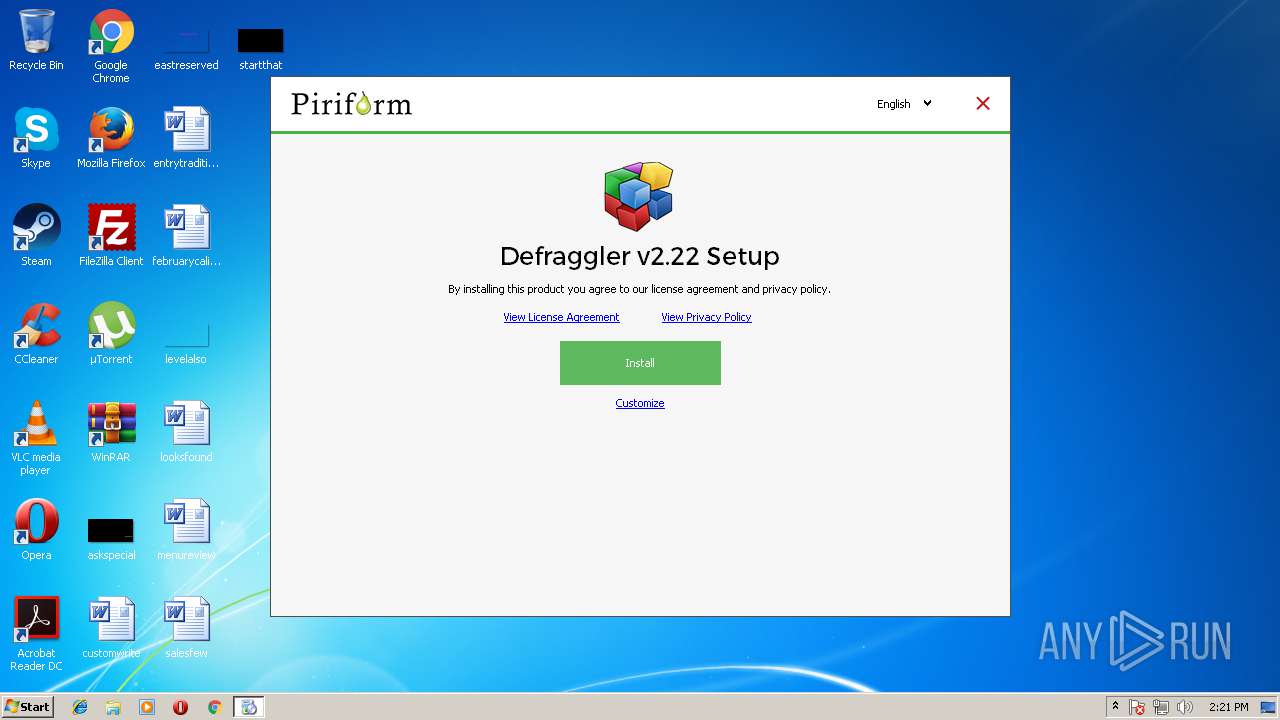
| download: | dfsetup222.exe |
| Full analysis: | https://app.any.run/tasks/3f04c4bf-074f-47ae-902c-94aaa5a9c9a1 |
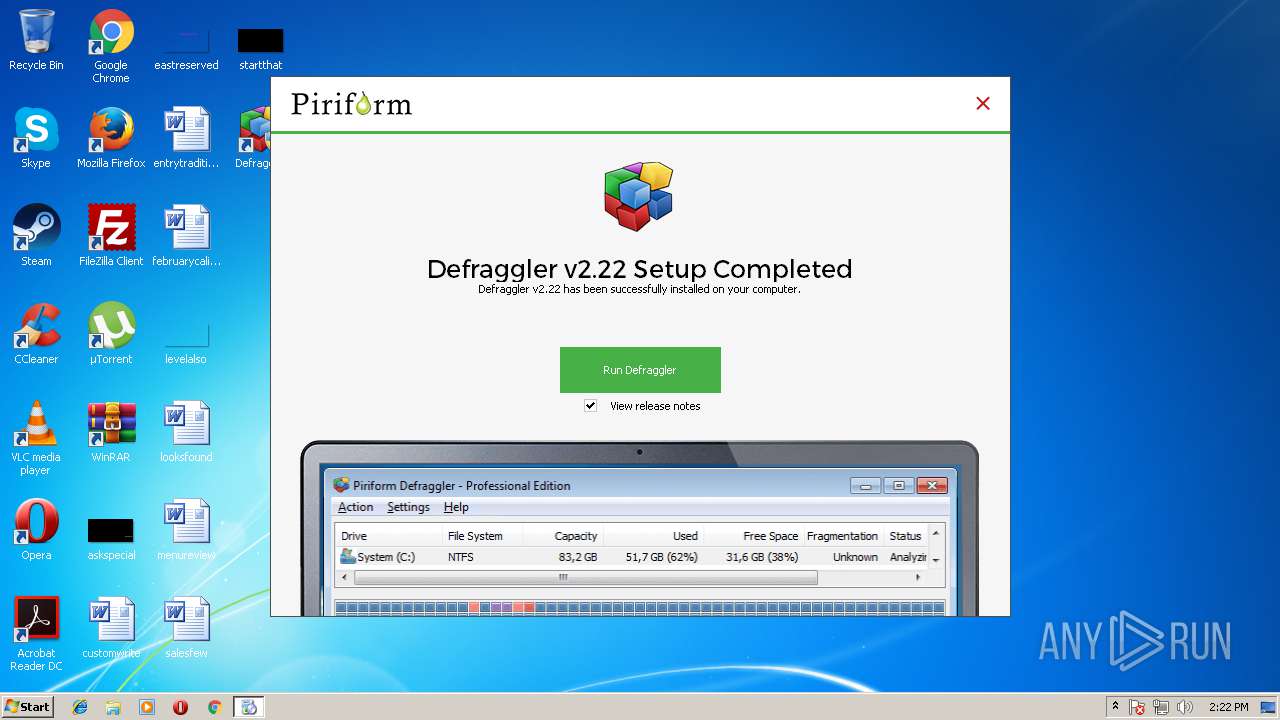
| Verdict: | Malicious activity |
| Analysis date: | July 31, 2018, 13:21:13 |
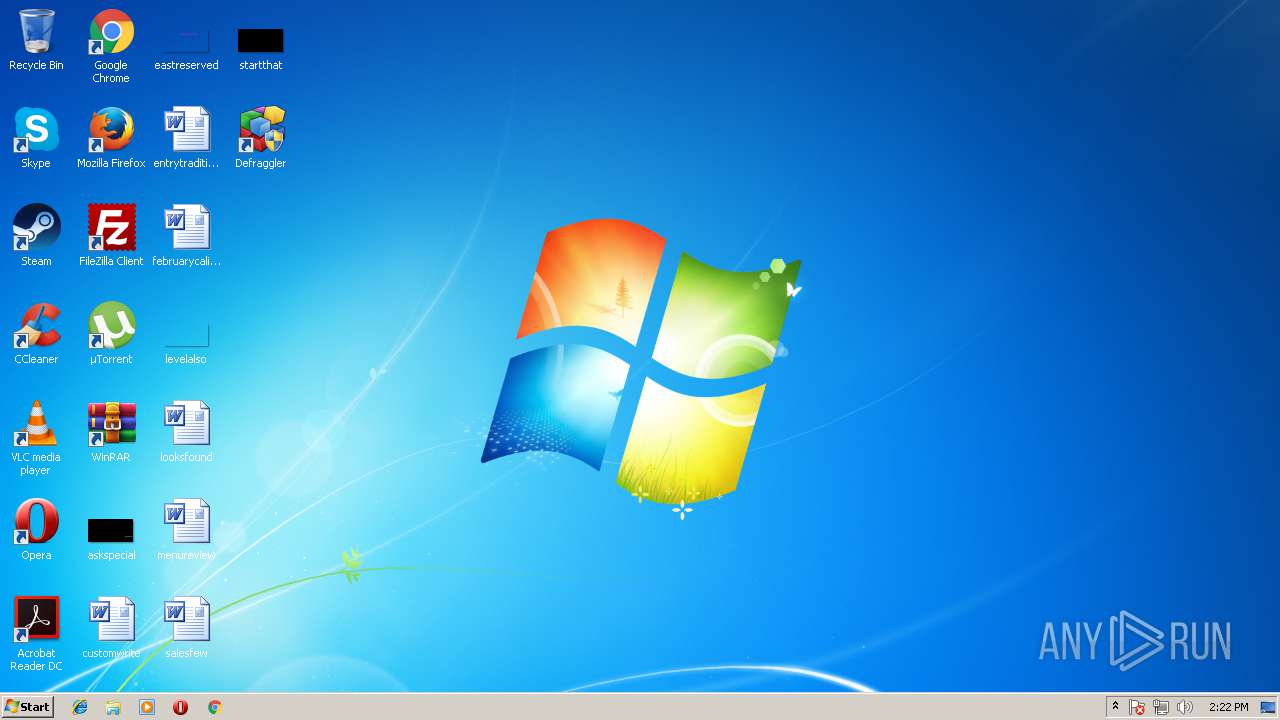
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | C39FB9E300ABC7D158473BD516BE3858 |
| SHA1: | B0E0F327809A767D6B524E2FA325DD35B678AF44 |
| SHA256: | B53EB82D6A46C812171CA878B7342E1939A0AFECC277B0B57C708EEF8FC700DE |
| SSDEEP: | 196608:9RkDrtDK+KeWN3v7EO/6EkC2XM4kCY76x/:9RkDJDEp79/69E4rYg/ |
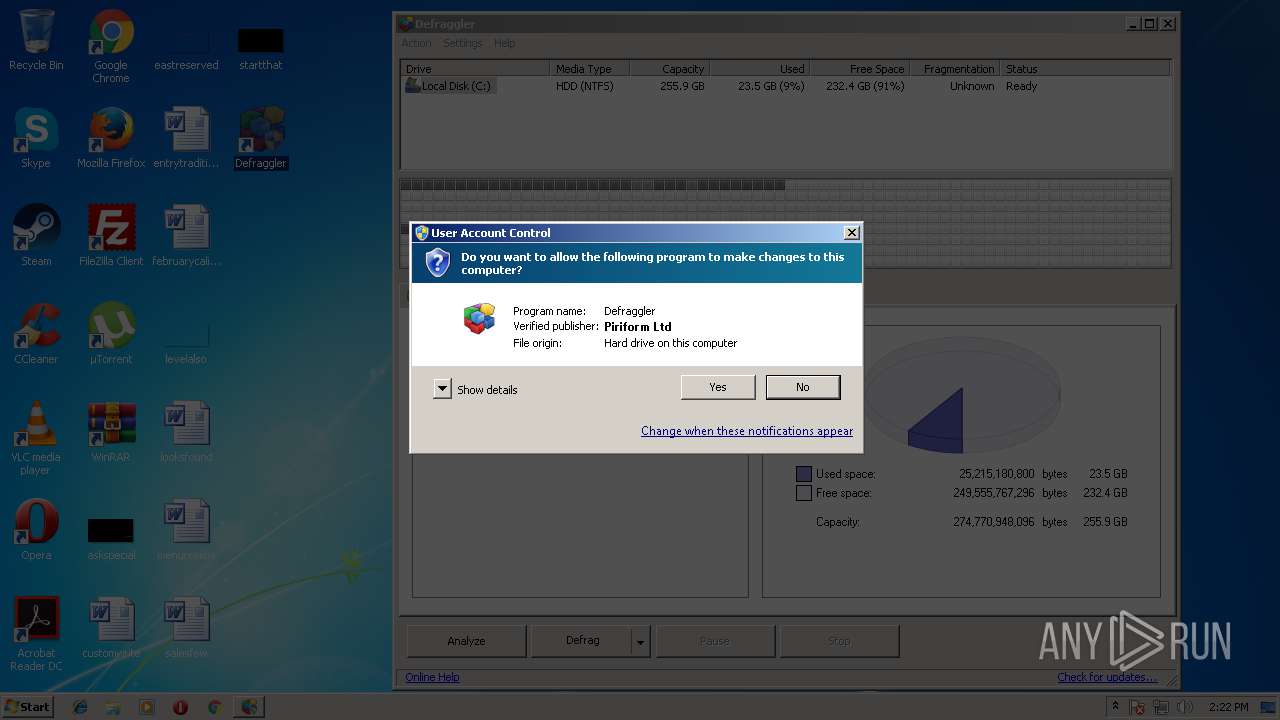
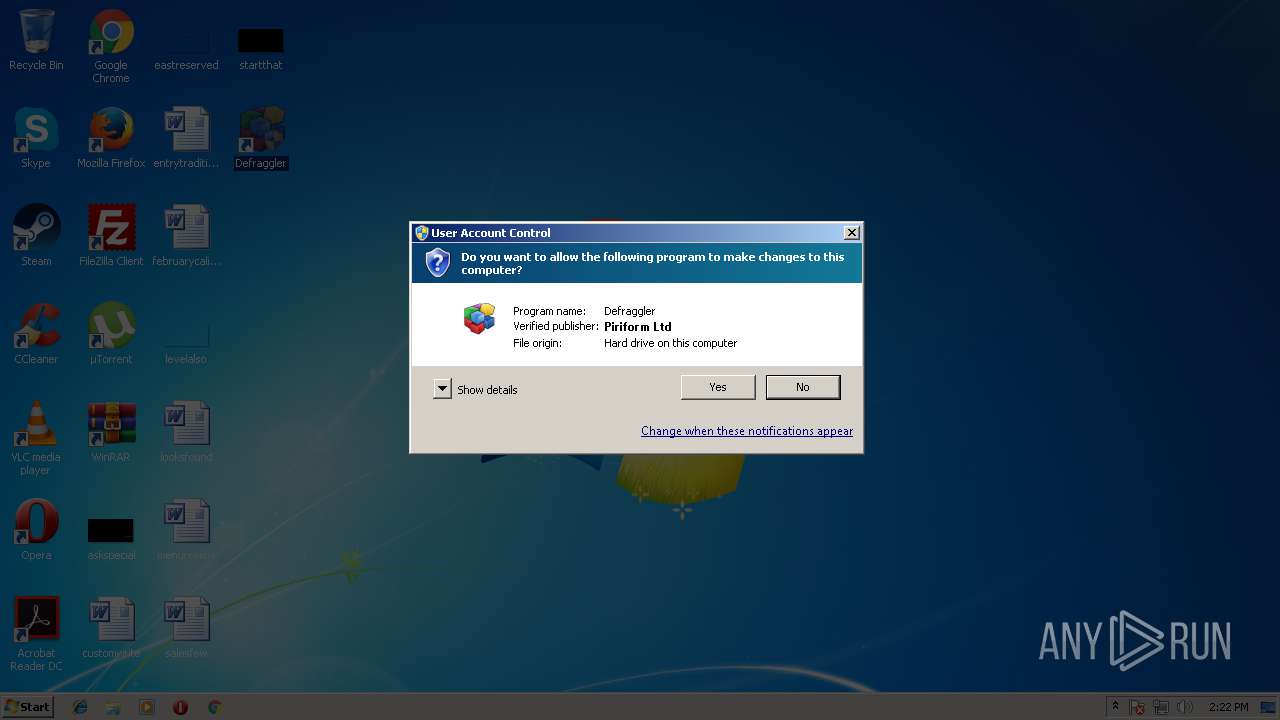
MALICIOUS
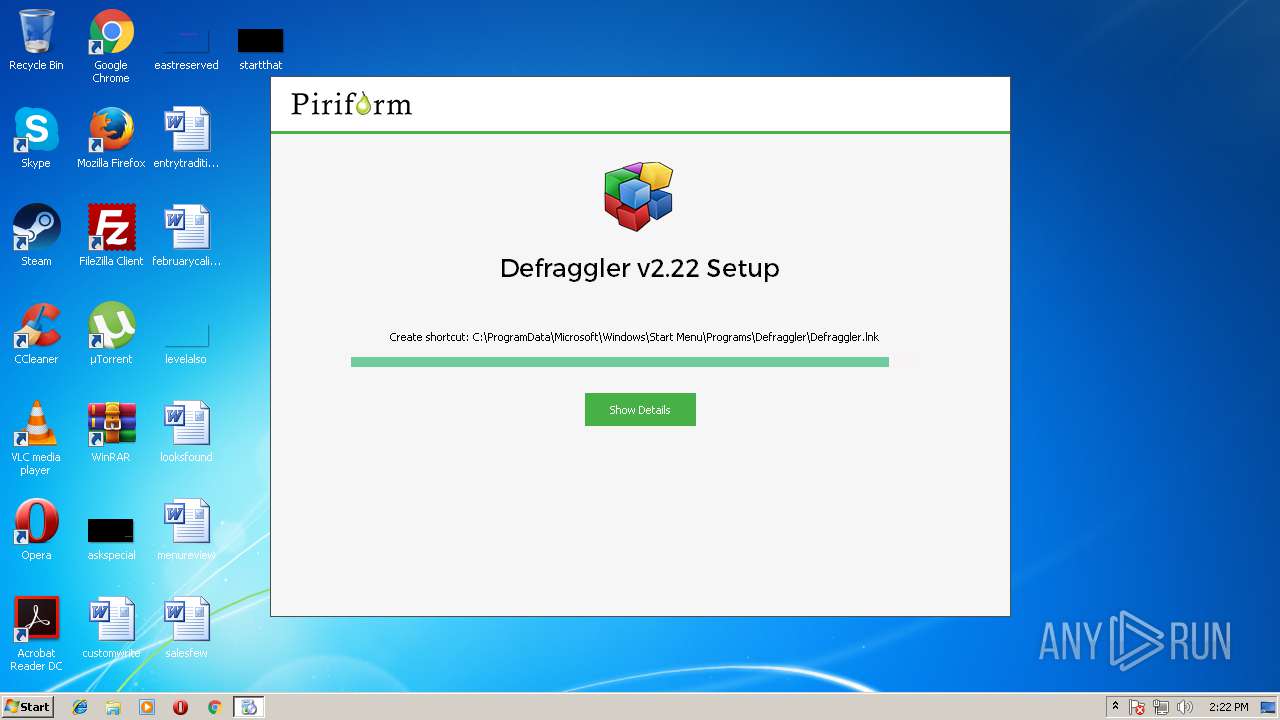
Loads dropped or rewritten executable
- dfsetup222.exe (PID: 3348)
- regsvr32.exe (PID: 1460)
- Defraggler.exe (PID: 3404)
- Defraggler.exe (PID: 3440)
Actions looks like stealing of personal data
- dfsetup222.exe (PID: 3348)
Registers / Runs the DLL via REGSVR32.EXE
- dfsetup222.exe (PID: 3348)
Application was dropped or rewritten from another process
- Defraggler.exe (PID: 3404)
- Defraggler.exe (PID: 3728)
- Defraggler.exe (PID: 1712)
- Defraggler.exe (PID: 3440)
Changes settings of System certificates
- dfsetup222.exe (PID: 3348)
SUSPICIOUS
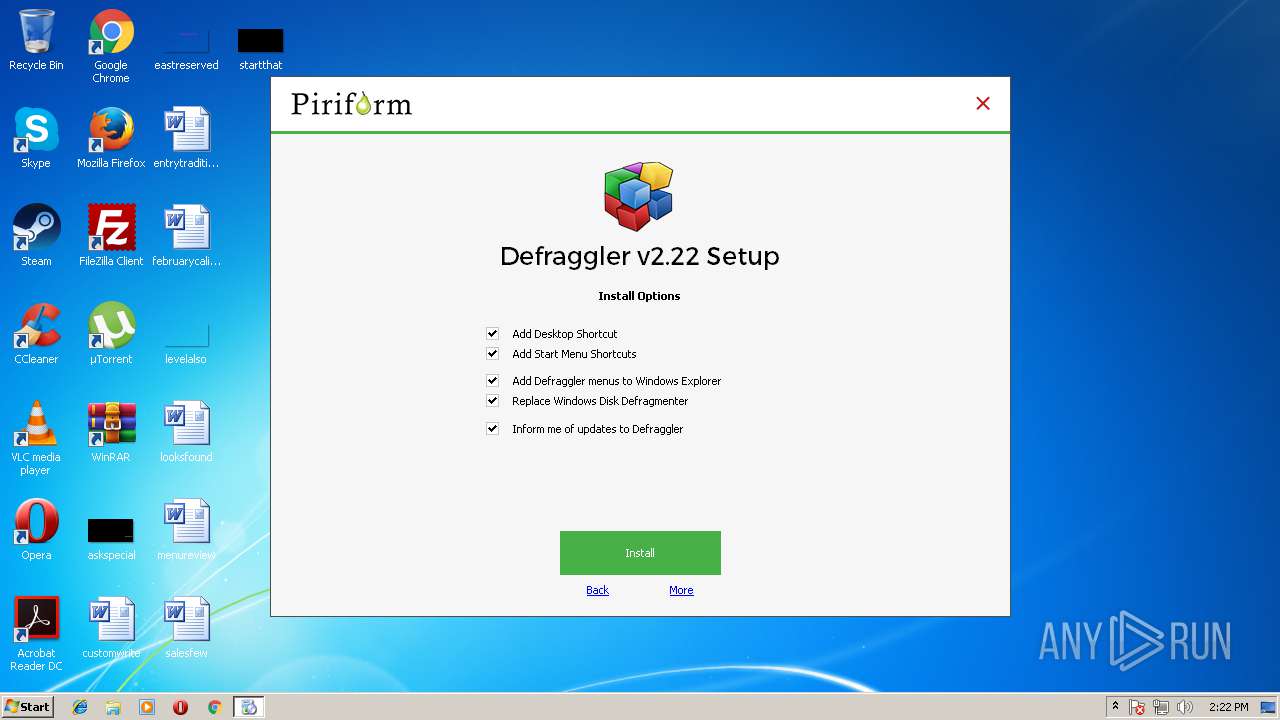
Searches for installed software
- dfsetup222.exe (PID: 3348)
Executable content was dropped or overwritten
- dfsetup222.exe (PID: 3348)
Starts application with an unusual extension
- dfsetup222.exe (PID: 3348)
Adds / modifies Windows certificates
- dfsetup222.exe (PID: 3348)
Reads internet explorer settings
- dfsetup222.exe (PID: 3348)
- Defraggler.exe (PID: 3404)
- Defraggler.exe (PID: 3440)
Creates files in the program directory
- dfsetup222.exe (PID: 3348)
- Defraggler.exe (PID: 3404)
Creates a software uninstall entry
- dfsetup222.exe (PID: 3348)
Creates files in the user directory
- dfsetup222.exe (PID: 3348)
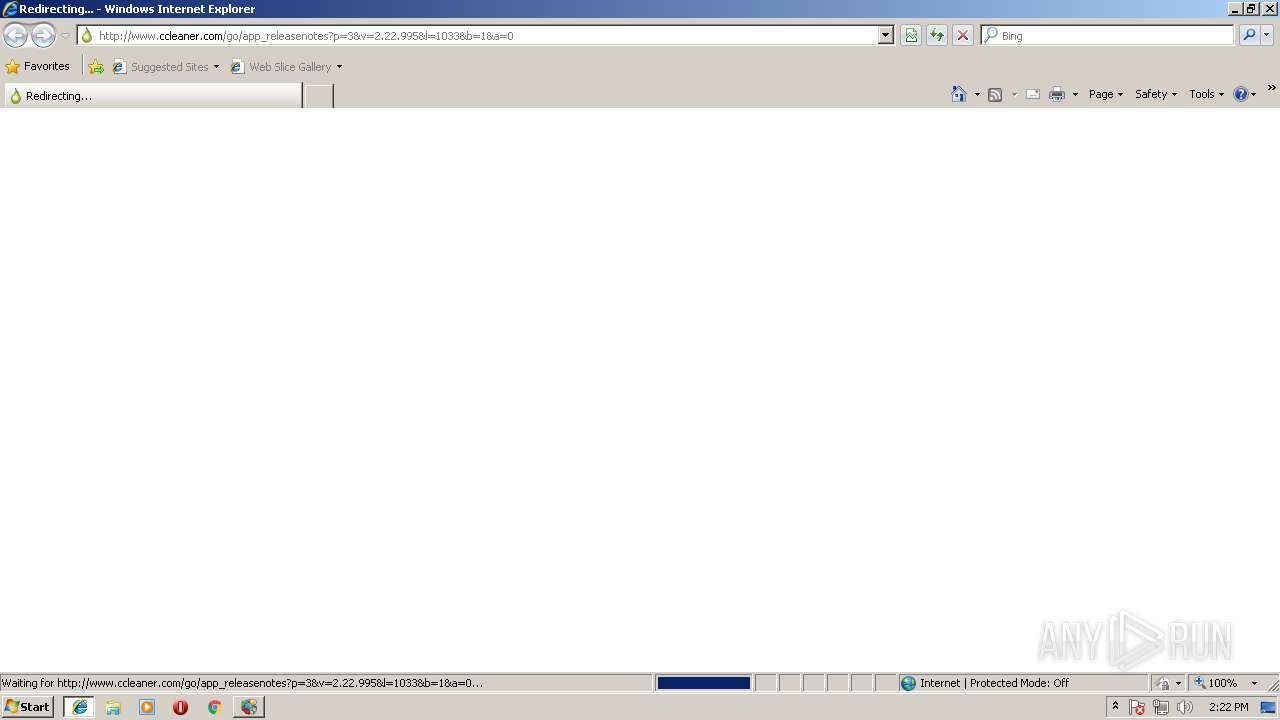
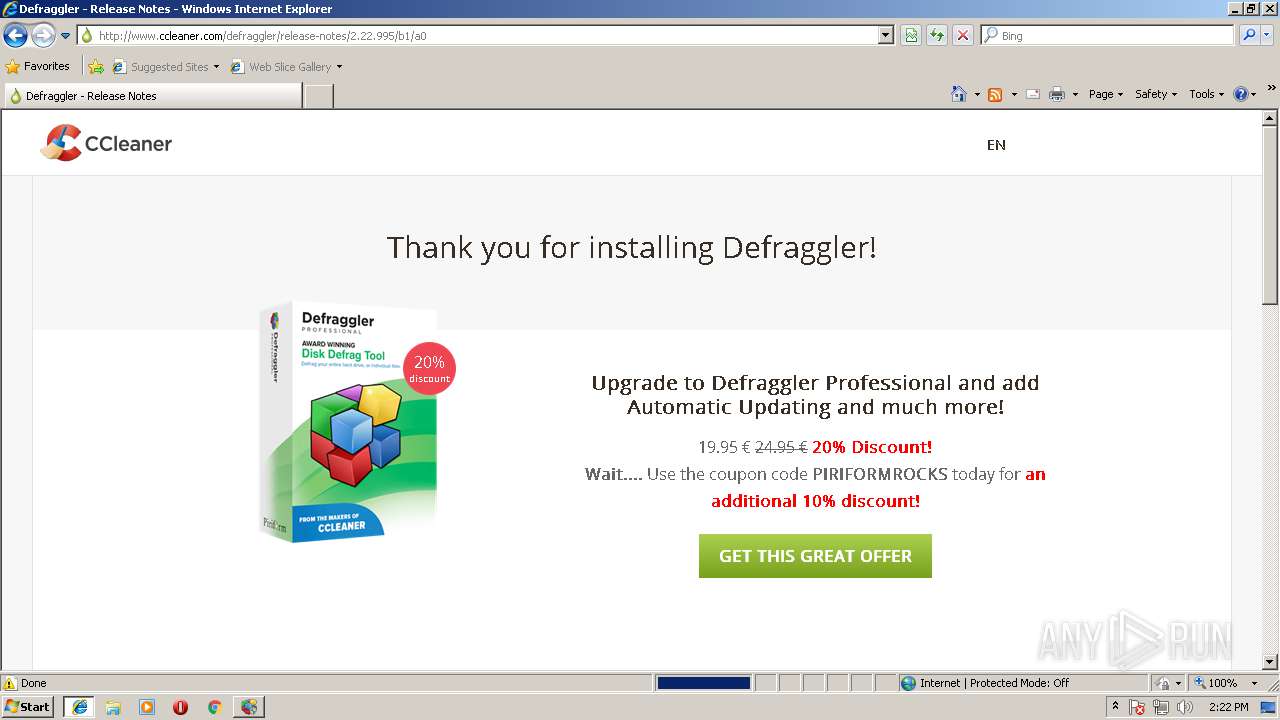
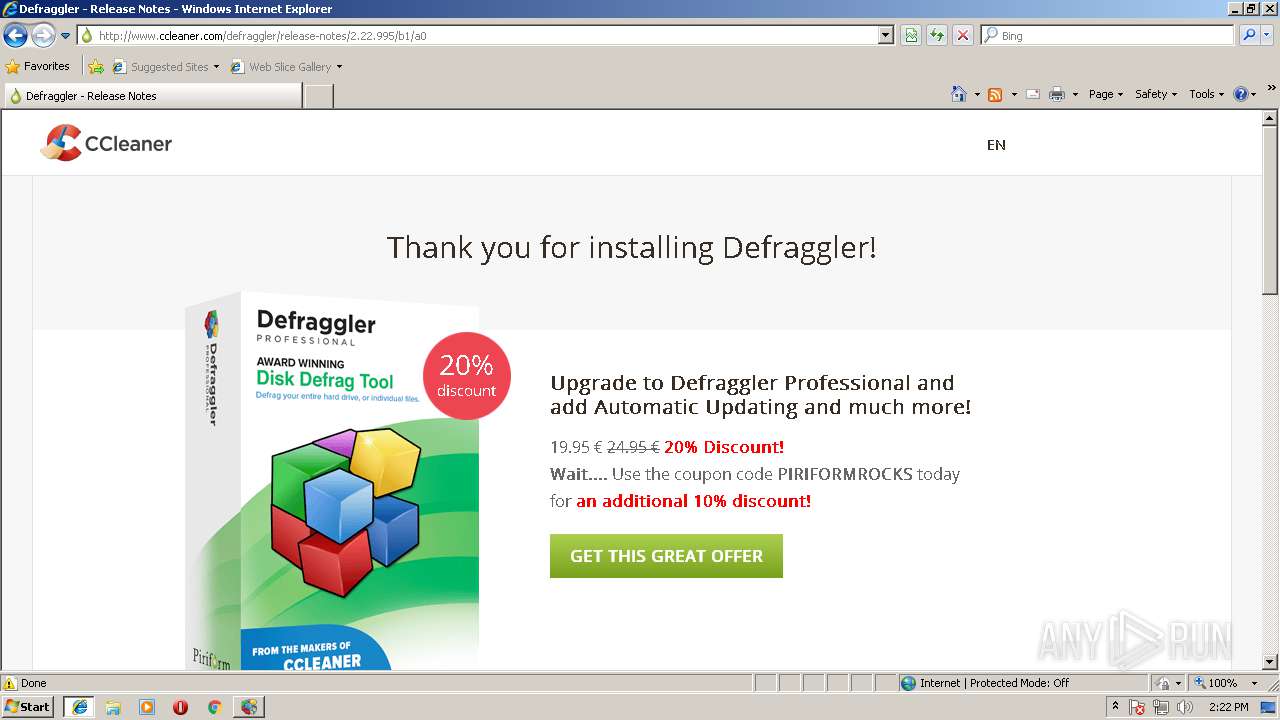
Starts Internet Explorer
- dfsetup222.exe (PID: 3348)
Creates COM task schedule object
- regsvr32.exe (PID: 1460)
INFO
Application launched itself
- iexplore.exe (PID: 2368)
Changes internet zones settings
- iexplore.exe (PID: 2368)
Reads internet explorer settings
- iexplore.exe (PID: 2196)
Reads Internet Cache Settings
- iexplore.exe (PID: 2196)
Creates files in the user directory
- iexplore.exe (PID: 2196)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2196)
Changes settings of System certificates
- iexplore.exe (PID: 2196)
Dropped object may contain URL's
- iexplore.exe (PID: 2368)
- iexplore.exe (PID: 2196)
- dfsetup222.exe (PID: 3348)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2015:12:29 22:34:49+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 29696 |
| InitializedDataSize: | 441856 |
| UninitializedDataSize: | 16896 |
| EntryPoint: | 0x3a1c |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.22.33.995 |
| ProductVersionNumber: | 2.22.33.995 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
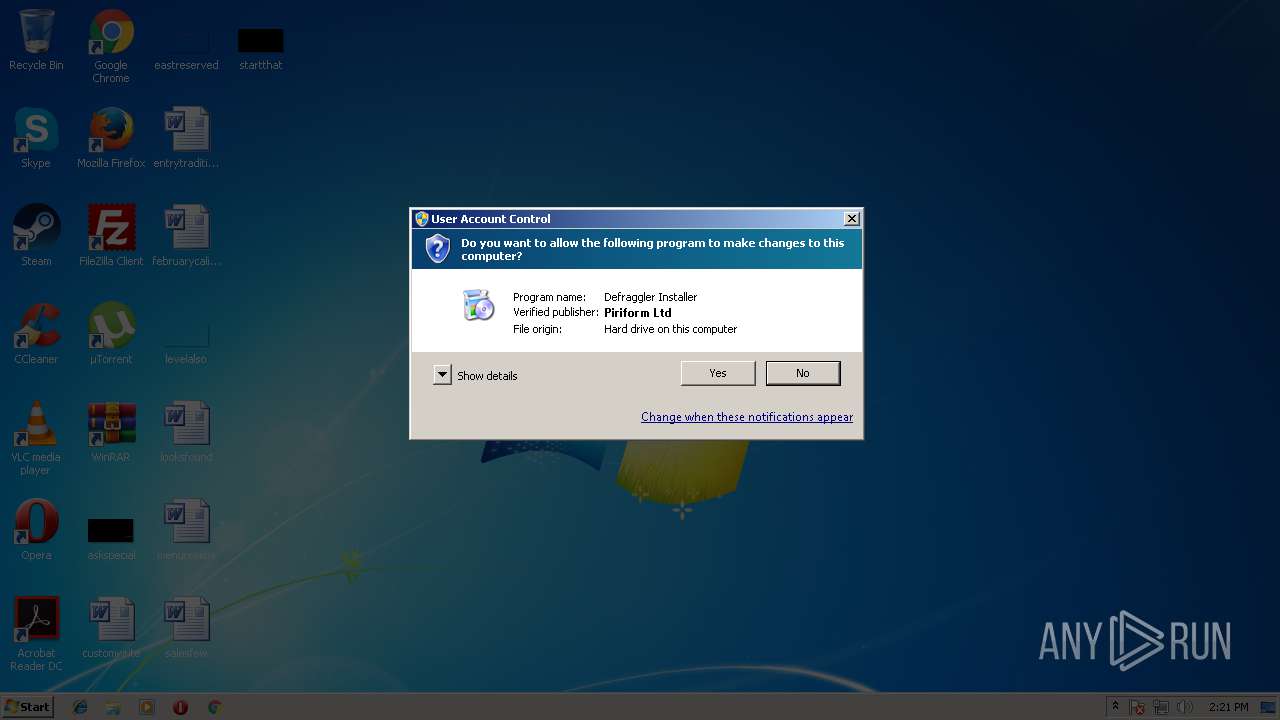
| CompanyName: | Piriform Ltd |
| FileDescription: | Defraggler Installer |
| FileVersion: | 2.22.33.995 |
| LegalCopyright: | Copyright © 2006-2018 Piriform Ltd |
| ProductName: | Defraggler |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 29-Dec-2015 21:34:49 |
| Detected languages: |
|
| CompanyName: | Piriform Ltd |
| FileDescription: | Defraggler Installer |
| FileVersion: | 2.22.33.995 |
| LegalCopyright: | Copyright © 2006-2018 Piriform Ltd |
| ProductName: | Defraggler |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 29-Dec-2015 21:34:49 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00007250 | 0x00007400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.46491 |
.rdata | 0x00009000 | 0x00002B38 | 0x00002C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.41939 |
.data | 0x0000C000 | 0x00067EDC | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.89689 |
.ndata | 0x00074000 | 0x00331000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x003A5000 | 0x00008008 | 0x00008200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.9565 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.21562 | 968 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.62687 | 4264 | UNKNOWN | English - United States | RT_ICON |
3 | 4.7389 | 2216 | UNKNOWN | English - United States | RT_ICON |
4 | 3.91559 | 1384 | UNKNOWN | English - United States | RT_ICON |
5 | 5.97397 | 1128 | UNKNOWN | English - United States | RT_ICON |
6 | 3.89369 | 744 | UNKNOWN | English - United States | RT_ICON |
103 | 2.72033 | 90 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.704 | 688 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.92897 | 344 | UNKNOWN | English - United States | RT_DIALOG |
111 | 2.92787 | 238 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
57
Monitored processes
13
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1460 | regsvr32.exe /I "C:\Program Files\Defraggler\DefragglerShell.dll" /s | C:\Windows\system32\regsvr32.exe | — | dfsetup222.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 4 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
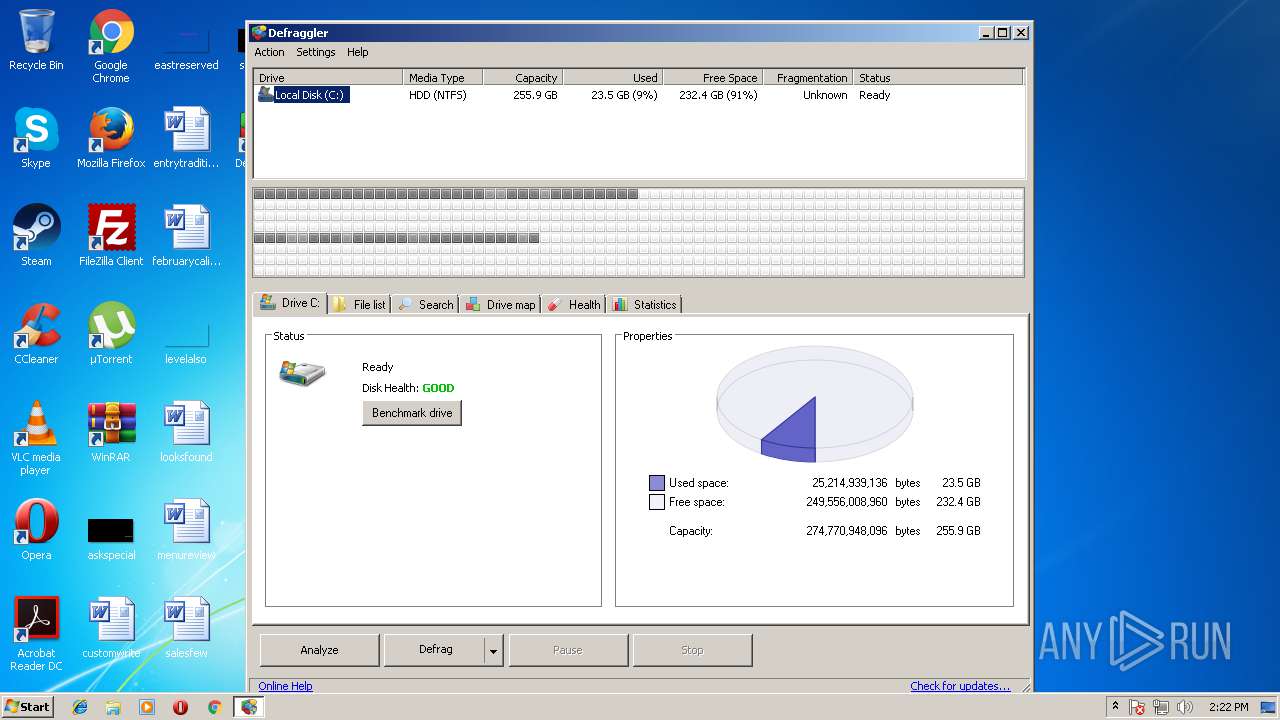
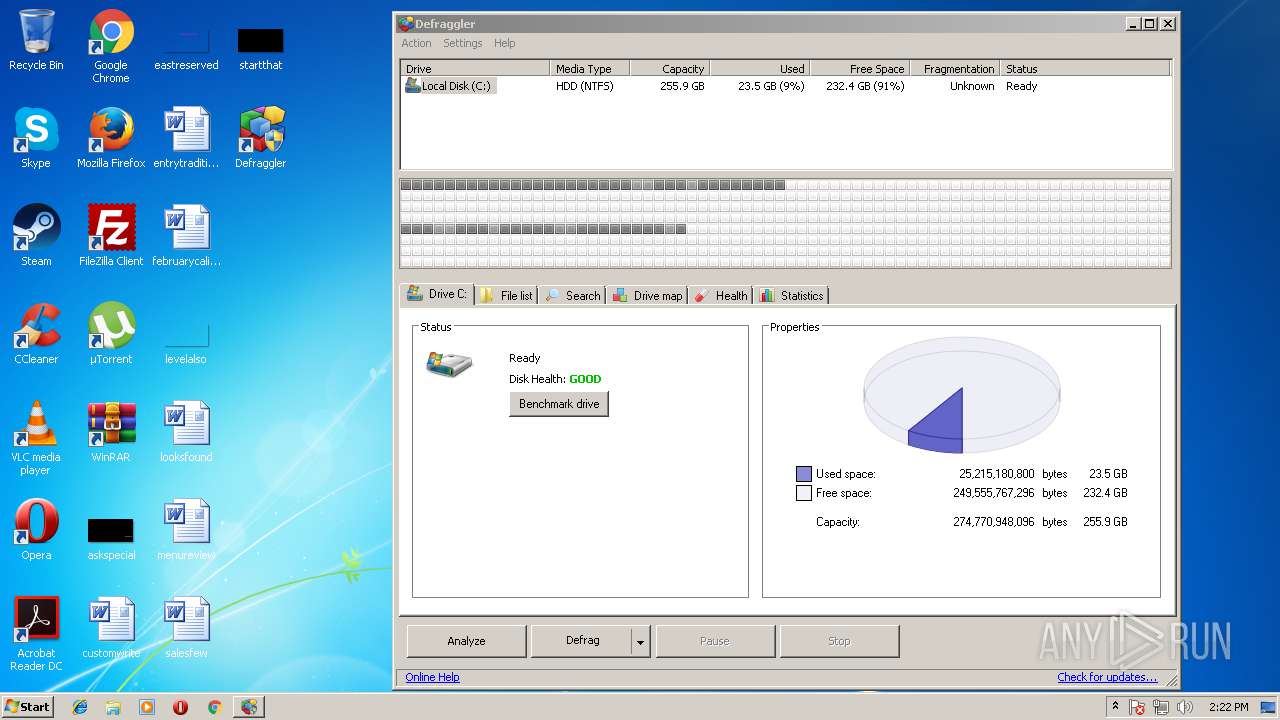
| 1712 | "C:\Program Files\Defraggler\Defraggler.exe" | C:\Program Files\Defraggler\Defraggler.exe | — | explorer.exe | |||||||||||
User: admin Company: Piriform Ltd Integrity Level: MEDIUM Description: Defraggler Exit code: 3221226540 Version: 2.22.33.995 Modules
| |||||||||||||||
| 2196 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2368 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 3221225547 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2368 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | dfsetup222.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2424 | "C:\Users\admin\AppData\Local\Temp\nsk6400.tmp\ns674D.tmp" ping -n 1 -w 1000 www.ccleaner.com | C:\Users\admin\AppData\Local\Temp\nsk6400.tmp\ns674D.tmp | — | dfsetup222.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3136 | ping -n 1 -w 5000 www.ccleaner.com | C:\Windows\system32\ping.exe | — | ns9E3D.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3348 | "C:\Users\admin\AppData\Local\Temp\dfsetup222.exe" | C:\Users\admin\AppData\Local\Temp\dfsetup222.exe | explorer.exe | ||||||||||||
User: admin Company: Piriform Ltd Integrity Level: HIGH Description: Defraggler Installer Exit code: 0 Version: 2.22.33.995 Modules
| |||||||||||||||
| 3404 | "C:\Program Files\Defraggler\Defraggler.exe" | C:\Program Files\Defraggler\Defraggler.exe | dfsetup222.exe | ||||||||||||
User: admin Company: Piriform Ltd Integrity Level: HIGH Description: Defraggler Exit code: 1 Version: 2.22.33.995 Modules
| |||||||||||||||
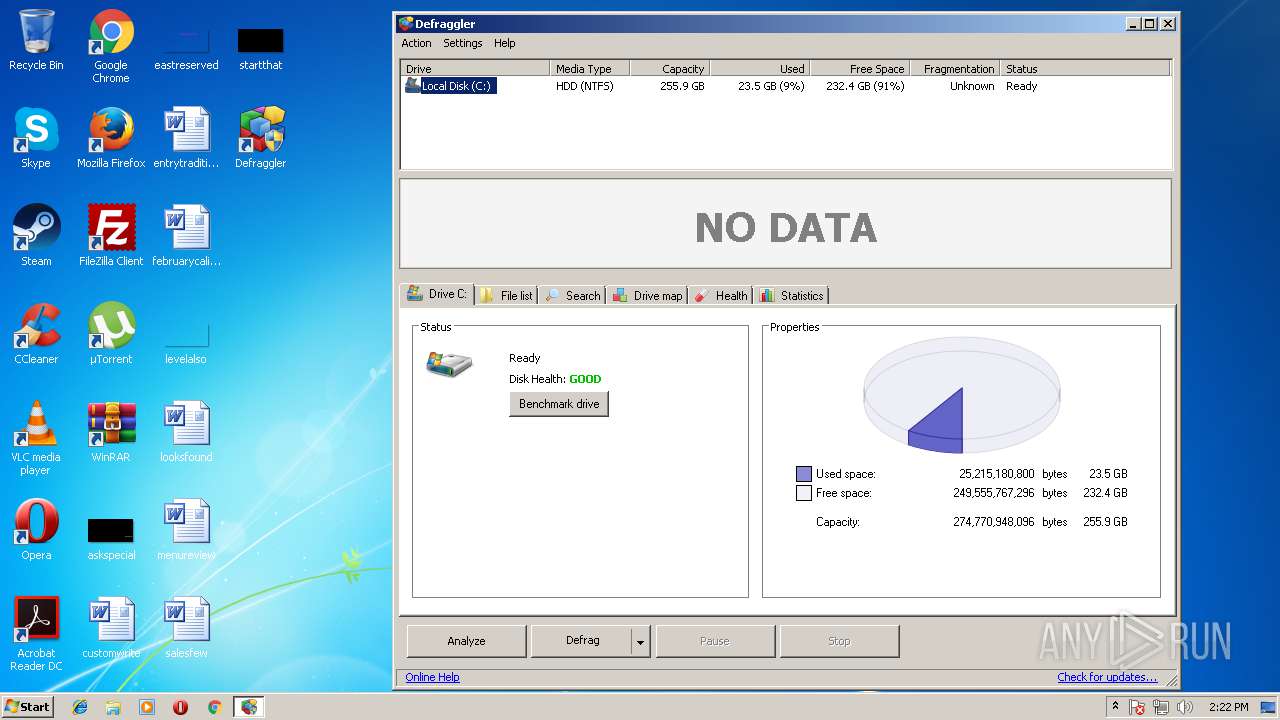
| 3440 | "C:\Program Files\Defraggler\Defraggler.exe" | C:\Program Files\Defraggler\Defraggler.exe | explorer.exe | ||||||||||||
User: admin Company: Piriform Ltd Integrity Level: HIGH Description: Defraggler Exit code: 0 Version: 2.22.33.995 Modules
| |||||||||||||||
| 3452 | ping -n 1 -w 1000 www.ccleaner.com | C:\Windows\system32\ping.exe | — | ns674D.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 213
Read events
950
Write events
257
Delete events
6
Modification events
| (PID) Process: | (3348) dfsetup222.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Google Toolbar |
| Operation: | write | Name: | test |
Value: test | |||
| (PID) Process: | (3348) dfsetup222.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Google Toolbar |
| Operation: | delete value | Name: | test |
Value: test | |||
| (PID) Process: | (3348) dfsetup222.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Google Toolbar |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (3348) dfsetup222.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\59\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3348) dfsetup222.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\B1BC968BD4F49D622AA89A81F2150152A41D829C |
| Operation: | write | Name: | Blob |
Value: 0400000001000000100000003E455215095192E1B75D379FB187298A0B000000010000003000000047006C006F00620061006C005300690067006E00200052006F006F00740020004300410020002D0020005200310000000F00000001000000140000005A6D07B6371D966A2FB6BA92828CE5512A49513D090000000100000068000000306606082B0601050507030106082B0601050507030206082B0601050507030306082B0601050507030406082B0601050507030806082B06010505070309060A2B0601040182370A030406082B0601050507030606082B0601050507030706082B060105050802025300000001000000230000003021301F06092B06010401A032010130123010060A2B0601040182373C0101030200C0140000000100000014000000607B661A450D97CA89502F7D04CD34A8FFFCFD4B1D00000001000000100000006EE7F3B060D10E90A31BA3471B999236030000000100000014000000B1BC968BD4F49D622AA89A81F2150152A41D829C190000000100000010000000A823B4A20180BEB460CAB955C24D7E21620000000100000020000000EBD41040E4BB3EC742C9E381D31EF2A41A48B6685C96E7CEF3C1DF6CD4331C99200000000100000079030000308203753082025DA003020102020B040000000001154B5AC394300D06092A864886F70D01010505003057310B300906035504061302424531193017060355040A1310476C6F62616C5369676E206E762D73613110300E060355040B1307526F6F74204341311B301906035504031312476C6F62616C5369676E20526F6F74204341301E170D3938303930313132303030305A170D3238303132383132303030305A3057310B300906035504061302424531193017060355040A1310476C6F62616C5369676E206E762D73613110300E060355040B1307526F6F74204341311B301906035504031312476C6F62616C5369676E20526F6F7420434130820122300D06092A864886F70D01010105000382010F003082010A0282010100DA0EE6998DCEA3E34F8A7EFBF18B83256BEA481FF12AB0B9951104BDF063D1E26766CF1CDDCF1B482BEE8D898E9AAF298065ABE9C72D12CBAB1C4C7007A13D0A30CD158D4FF8DDD48C50151CEF50EEC42EF7FCE952F2917DE06DD535308E5E4373F241E9D56AE3B2893A5639386F063C88695B2A4DC5A754B86C89CC9BF93CCAE5FD89F5123C927896D6DC746E934461D18DC746B2750E86E8198AD56D6CD5781695A2E9C80A38EBF224134F73549313853A1BBC1E34B58B058CB9778BB1DB1F2091AB09536E90CE7B3774B97047912251631679AEB1AE412608C8192BD146AA48D6642AD78334FF2C2AC16C19434A0785E7D37CF62168EFEAF2529F7F9390CF0203010001A3423040300E0603551D0F0101FF040403020106300F0603551D130101FF040530030101FF301D0603551D0E04160414607B661A450D97CA89502F7D04CD34A8FFFCFD4B300D06092A864886F70D01010505000382010100D673E77C4F76D08DBFECBAA2BE34C52832B57CFC6C9C2C2BBD099E53BF6B5EAA1148B6E508A3B3CA3D614DD34609B33EC3A0E363551BF2BAEFAD39E143B938A3E62F8A263BEFA05056F9C60AFD38CDC40B705194979804DFC35F94D515C914419CC45D7564150DFF5530EC868FFF0DEF2CB96346F6AAFCDFBC69FD2E1248649AE095F0A6EF298F01B115B50C1DA5FE692C6924781EB3A71C7162EECAC897AC175D8AC2F847866E2AC4563195D06789852BF96CA65D469D0CAA82E49951DD70B7DB563D61E46AE15CD6F6FE3DDE41CC07AE6352BF5353F42BE9C7FDB6F7825F85D24118DB81B3041CC51FA4806F1520C9DE0C880A1DD66655E2FC48C9292669E0 | |||
| (PID) Process: | (3348) dfsetup222.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\dfsetup222_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3348) dfsetup222.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\dfsetup222_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3348) dfsetup222.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\dfsetup222_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3348) dfsetup222.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\dfsetup222_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3348) dfsetup222.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\dfsetup222_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
Executable files
99
Suspicious files
2
Text files
76
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3348 | dfsetup222.exe | C:\Users\admin\AppData\Local\Temp\nsk6400.tmp\ns674D.tmp | — | |
MD5:— | SHA256:— | |||
| 3348 | dfsetup222.exe | C:\Users\admin\AppData\Local\Temp\nsk6400.tmp\System.dll | executable | |
MD5:41A3C964232EDD2D7D5EDEA53E8245CD | SHA256:8B65FEC615C7B371C23F8F7F344B12DC5085E40A556F96DB318ED757494D62D5 | |||
| 3348 | dfsetup222.exe | C:\Users\admin\AppData\Local\Temp\nsk6400.tmp\ui\res\Defraggler_Logo_72px.png | image | |
MD5:6FF9FCEE38D74372A5851B2E725C8912 | SHA256:41364C1FA2CA18FA9B56FDBA5C04CEE3AF3767AAA6962F90545FCA3A40CC8901 | |||
| 3348 | dfsetup222.exe | C:\Users\admin\AppData\Local\Temp\nsk6400.tmp\nsExec.dll | executable | |
MD5:5ED60250F74FA36A5A247A715BCD026E | SHA256:EA8026766ADC2D7CC26E2206CFDF5F0865B1426BFE3BC2AEC8F43D3FC9A072EF | |||
| 3348 | dfsetup222.exe | C:\Users\admin\AppData\Local\Temp\nsk6400.tmp\ui\res\DF_computer.png | image | |
MD5:8CFC0CAA56CFD01F0B273FEF239BC025 | SHA256:7790CC5E6105B9A35A6FB79618CCEF6E035E96B5839DB34EA0A15C7A1D4E56C7 | |||
| 3348 | dfsetup222.exe | C:\Users\admin\AppData\Local\Temp\nsk6400.tmp\g\gcapi_dll.dll | executable | |
MD5:2973AF8515EFFD0A3BFC7A43B03B3FCC | SHA256:D0E4581210A22135CE5DEB47D9DF4D636A94B3813E0649AAB84822C9F08AF2A0 | |||
| 3348 | dfsetup222.exe | C:\Users\admin\AppData\Local\Temp\nsk6400.tmp\ui\res\lang-1049.dll | executable | |
MD5:FAA0ABD5AC8CD66C58DA48C8F821AC65 | SHA256:CBCC1F7A3D71AEAD48411D98261A28886566968FF1BC3EFF820A4689C41811A4 | |||
| 3348 | dfsetup222.exe | C:\Users\admin\AppData\Local\Temp\nsk6400.tmp\ui\res\PF_logo.png | image | |
MD5:079CCA30760CCA3C01863B6B96E87848 | SHA256:8DD37D3721E25C32C5BF878B6DBA9E61D04B7CE8AEC45BDF703A41BC41802DFA | |||
| 3348 | dfsetup222.exe | C:\Users\admin\AppData\Local\Temp\nsk6400.tmp\p\pfAP.dll | executable | |
MD5:02C1D0D54B22601352681B39C44C6893 | SHA256:43B2C088A34C2115A33661BA6A9526AA6FA49040B314016257F93EA4F8E2C8CA | |||
| 3348 | dfsetup222.exe | C:\Users\admin\AppData\Local\Temp\nsk6400.tmp\ui\res\lang-1053.dll | executable | |
MD5:F4ACFDA9B2062F741F4789DA38234DBA | SHA256:7F2207C27FB2D59C083CED636595C9B48EEDFB3F7A71749B80F1FD7507D2CDBA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
50
TCP/UDP connections
41
DNS requests
26
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2196 | iexplore.exe | GET | 200 | 172.217.168.72:80 | http://www.googletagmanager.com/gtm.js?id=GTM-KFXRTR | US | text | 31.3 Kb | whitelisted |
2196 | iexplore.exe | GET | 200 | 151.101.2.202:80 | http://www.ccleaner.com/go/app_releasenotes?p=3&v=2.22.995&l=1033&b=1&a=0 | US | html | 1.81 Kb | whitelisted |
2196 | iexplore.exe | GET | 200 | 151.101.2.202:80 | http://www.ccleaner.com/favicon.ico | US | image | 2.65 Kb | whitelisted |
2196 | iexplore.exe | GET | 200 | 151.101.2.202:80 | http://www.ccleaner.com/css/global--blessed.1.css?v=CQYDAwIPDQs | US | text | 62.1 Kb | whitelisted |
2196 | iexplore.exe | GET | 200 | 130.211.5.208:80 | http://cdn.mxpnl.com/libs/mixpanel-2-latest.min.js | US | text | 20.4 Kb | whitelisted |
3404 | Defraggler.exe | GET | 200 | 151.101.2.202:80 | http://www.ccleaner.com/auto?p=df&v=2.22.995&l=1033&o=6.1W3&lk=&mk=BGKP-I9IF-8RSW-23YZ-UVRG-BSB9-I2HQ-F69D-78KP | US | text | 18 b | whitelisted |
2196 | iexplore.exe | GET | 200 | 151.101.2.202:80 | http://www.ccleaner.com/scripts/modernizr-custom.js | US | text | 4.72 Kb | whitelisted |
2196 | iexplore.exe | GET | 200 | 151.101.2.202:80 | http://www.ccleaner.com/css/global--blessed.css?v=CQYDAwIPDQs | US | text | 24.5 Kb | whitelisted |
2196 | iexplore.exe | GET | 200 | 52.222.149.245:80 | http://dnn506yrbagrg.cloudfront.net/pages/scripts/0067/8402.js?425845 | US | text | 81 b | whitelisted |
2196 | iexplore.exe | GET | 200 | 151.101.2.202:80 | http://www.ccleaner.com/css/hide-page-furniture.css | US | text | 421 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3348 | dfsetup222.exe | 151.101.2.202:443 | www.ccleaner.com | Fastly | US | suspicious |
3348 | dfsetup222.exe | 151.101.0.64:80 | service.piriform.com | Fastly | US | whitelisted |
2368 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2196 | iexplore.exe | 130.211.5.208:80 | cdn.mxpnl.com | Google Inc. | US | whitelisted |
2196 | iexplore.exe | 172.217.168.72:80 | www.googletagmanager.com | Google Inc. | US | whitelisted |
2196 | iexplore.exe | 159.122.19.153:443 | api.mixpanel.com | SoftLayer Technologies Inc. | US | unknown |
2196 | iexplore.exe | 208.118.62.70:443 | www.upsellit.com | Alchemy Communications, Inc. | US | unknown |
2196 | iexplore.exe | 216.58.215.238:80 | www.google-analytics.com | Google Inc. | US | whitelisted |
3404 | Defraggler.exe | 151.101.2.202:80 | www.ccleaner.com | Fastly | US | suspicious |
2196 | iexplore.exe | 172.217.168.74:80 | ajax.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.ccleaner.com |
| whitelisted |
service.piriform.com |
| whitelisted |
www.bing.com |
| whitelisted |
cdn.mxpnl.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
api.mixpanel.com |
| whitelisted |
dnn506yrbagrg.cloudfront.net |
| whitelisted |
www.upsellit.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
stats.g.doubleclick.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3404 | Defraggler.exe | Misc activity | SUSPICIOUS [PTsecurity] Bundled.Toolbar.Google potentially unsafe |