| File name: | kprm_2.8.exe |
| Full analysis: | https://app.any.run/tasks/85fdd998-cc9a-4c54-9b1f-df374a5548f2 |
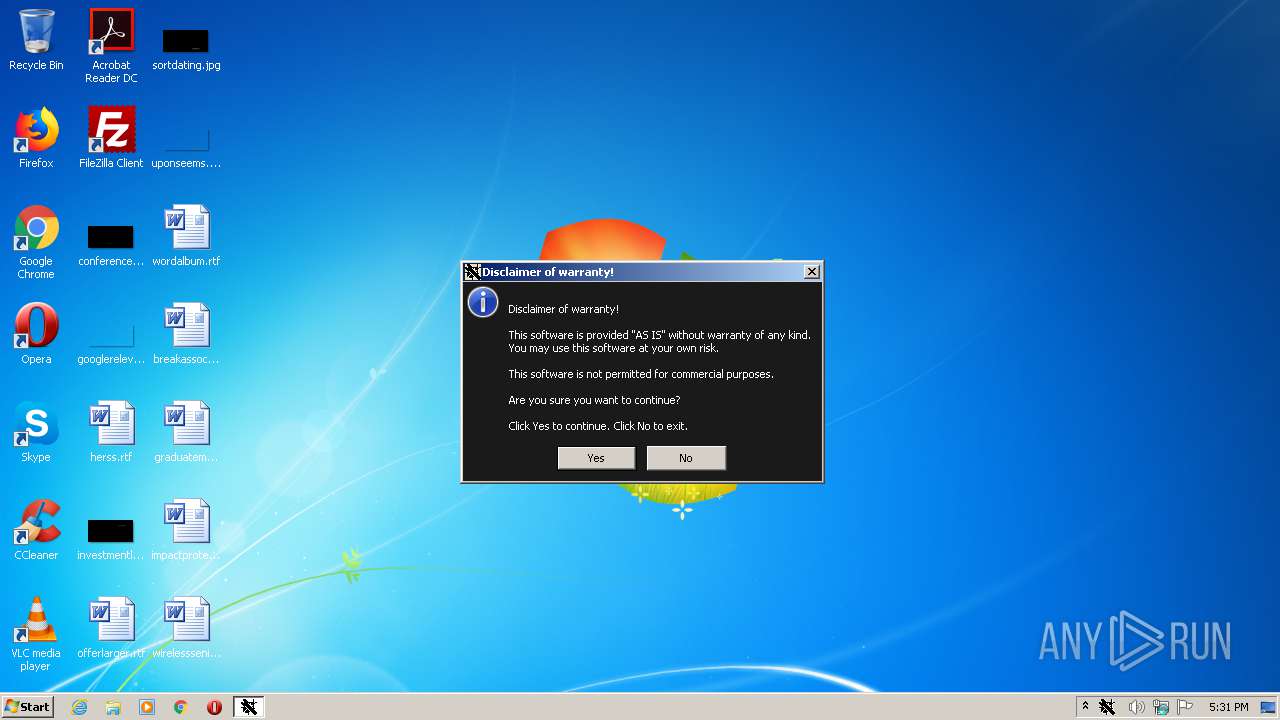
| Verdict: | Malicious activity |
| Analysis date: | August 01, 2020, 16:30:57 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | B4EA00DBD84DCF35C30F6B9702506CFE |
| SHA1: | 21A835964D760E805DD8B8C573D6DCC78A4AB059 |
| SHA256: | B534007B35CE2564E07CD65B4797B8A4F1BCE5740AF447B513305744611A15ED |
| SSDEEP: | 49152:Hh+ZkldoPK8YaNV4HjN3Xyf4m3UJBNqwqeMh1CtTTCf9sycP0prhe//jVyBO:w2cPK8d4DN3ictKeqJ8MI//jV4O |
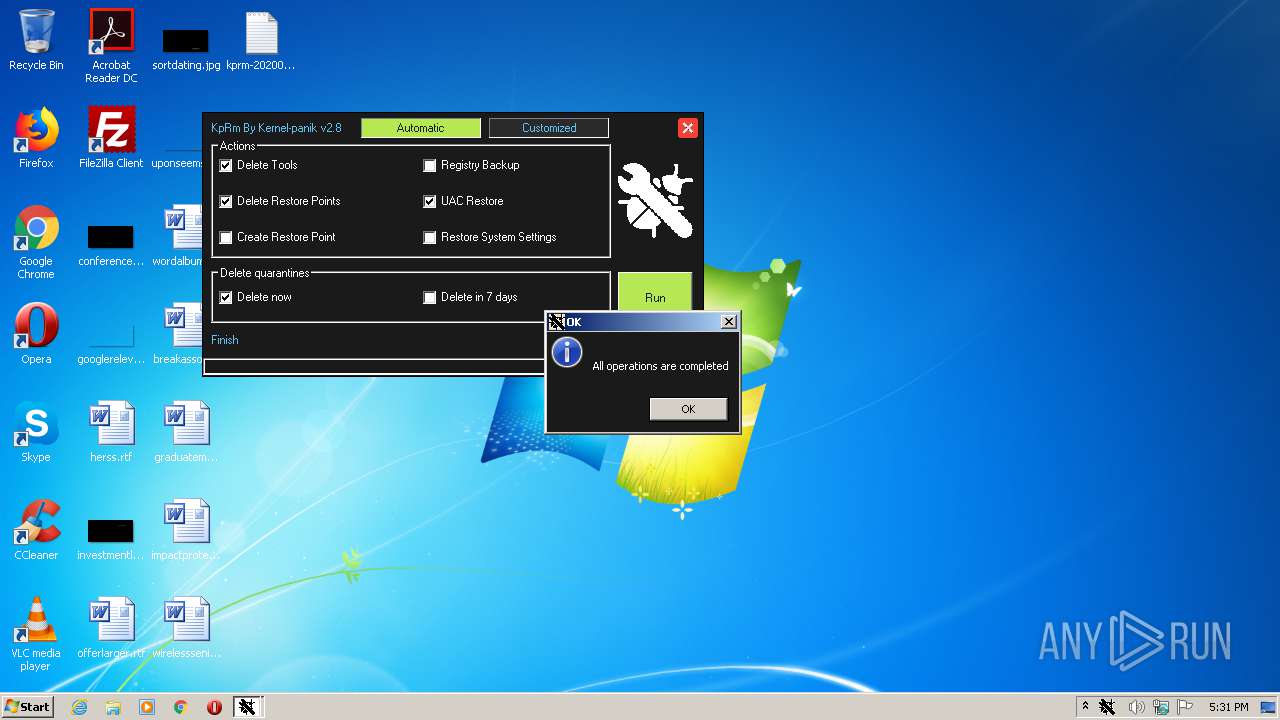
MALICIOUS
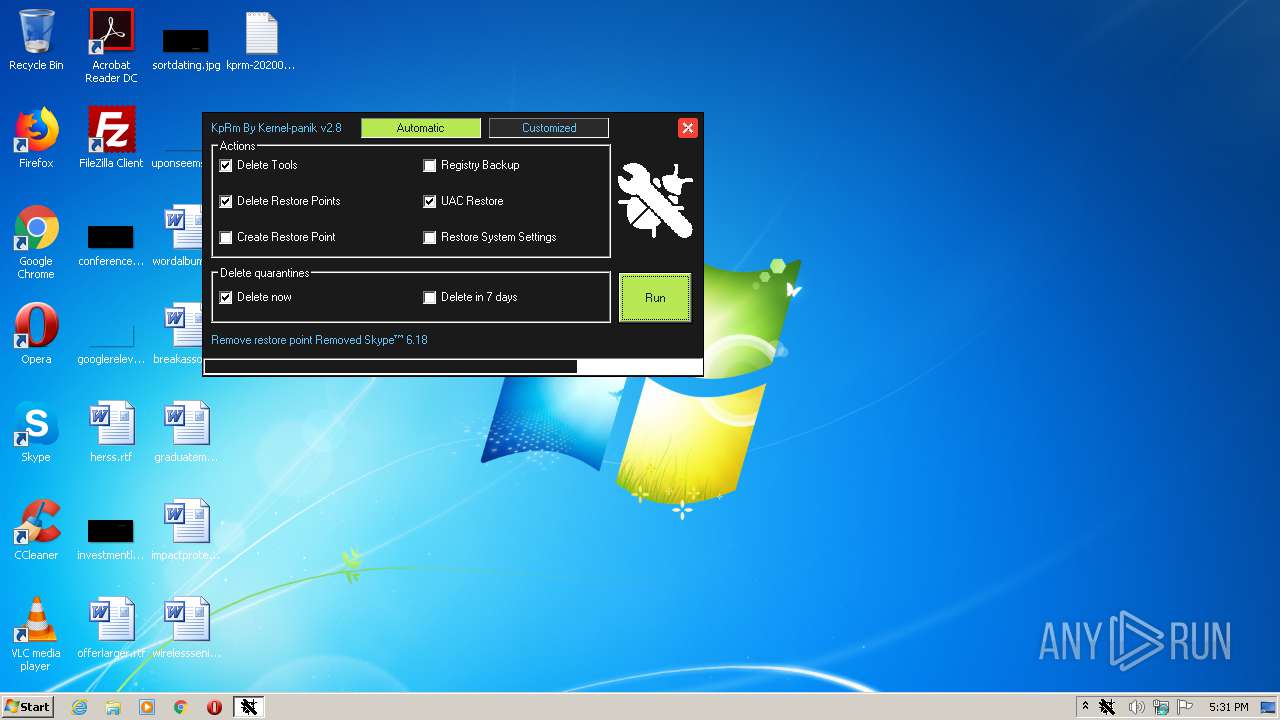
UAC/LUA settings modification
- kprm_2.8.exe (PID: 3756)
SUSPICIOUS
Executed via COM
- DllHost.exe (PID: 2720)
Starts CMD.EXE for self-deleting
- kprm_2.8.exe (PID: 3756)
Starts CMD.EXE for commands execution
- kprm_2.8.exe (PID: 3756)
Executed as Windows Service
- vssvc.exe (PID: 3896)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:02:27 15:56:53+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 12 |
| CodeSize: | 581632 |
| InitializedDataSize: | 2226176 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2800a |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.0.0.8 |
| ProductVersionNumber: | 2.8.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | English (British) |
| CharacterSet: | Unicode |
| FileVersion: | 2.0.0.8 |
| Comments: | Delete all removal tools |
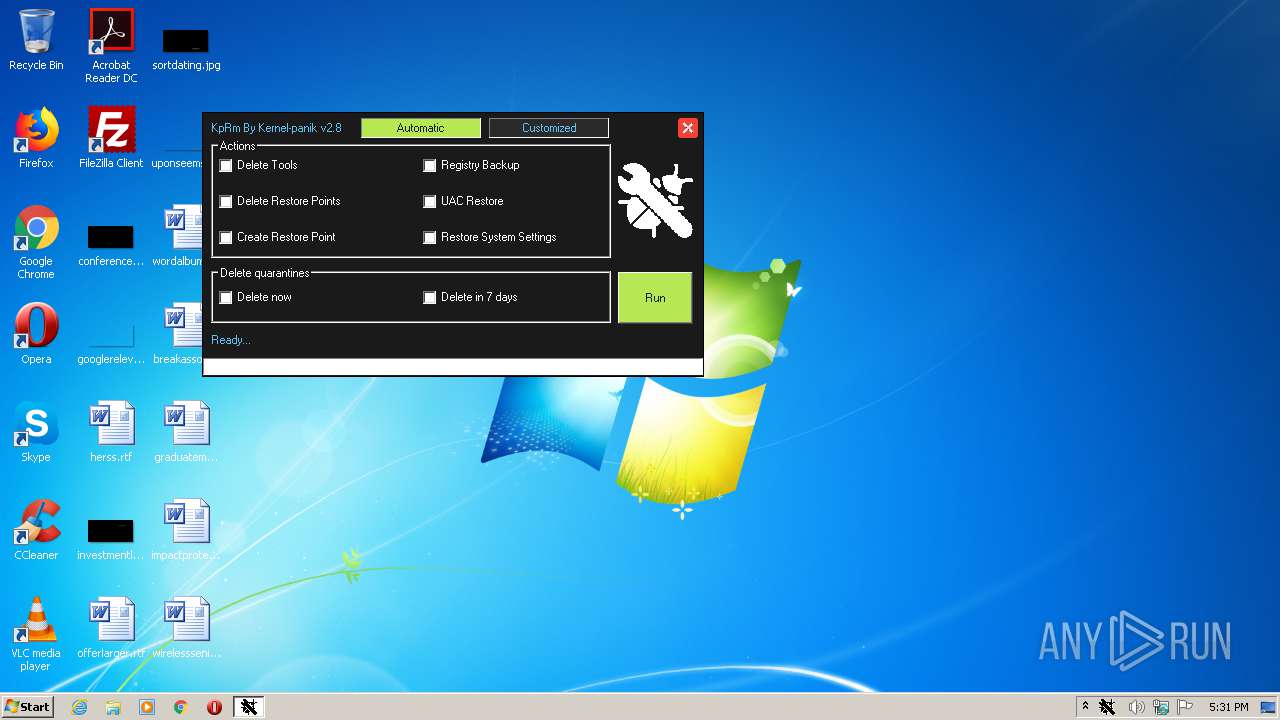
| FileDescription: | KpRm By Kernel-Panik |
| ProductName: | KpRm |
| ProductVersion: | 2.8 |
| CompanyName: | kernel-panik |
| LegalCopyright: | kernel-panik |
| LegalTradeMarks: | kernel-panik |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 27-Feb-2020 14:56:53 |
| Detected languages: |
|
| FileVersion: | 2.0.0.8 |
| Comments: | Delete all removal tools |
| FileDescription: | KpRm By Kernel-Panik |
| ProductName: | KpRm |
| ProductVersion: | 2.8 |
| CompanyName: | kernel-panik |
| LegalCopyright: | kernel-panik |
| LegalTradeMarks: | kernel-panik |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000110 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 27-Feb-2020 14:56:53 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0008DFDD | 0x0008E000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.67525 |
.rdata | 0x0008F000 | 0x0002FD8E | 0x0002FE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.76324 |
.data | 0x000BF000 | 0x00008F74 | 0x00005200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.19638 |
.rsrc | 0x000C8000 | 0x001E34F0 | 0x001E3600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.99109 |
.reloc | 0x002AC000 | 0x00007134 | 0x00007200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.78396 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.33385 | 1629 | Latin 1 / Western European | English - United Kingdom | RT_MANIFEST |
2 | 2.05883 | 296 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
3 | 2.25499 | 296 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
4 | 1.81896 | 17384 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
7 | 3.34702 | 1428 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
8 | 3.2817 | 1674 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
9 | 3.28849 | 1168 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
10 | 3.28373 | 1532 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
11 | 3.26322 | 1628 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
12 | 3.25812 | 1126 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
GDI32.dll |
IPHLPAPI.DLL |
KERNEL32.dll |
MPR.dll |
OLEAUT32.dll |
PSAPI.DLL |
SHELL32.dll |
Total processes
47
Monitored processes
7
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1492 | notepad.exe C:\KPRM\kprm-20200801173144.txt | C:\Windows\system32\notepad.exe | — | kprm_2.8.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1996 | "C:\Users\admin\AppData\Local\Temp\kprm_2.8.exe" | C:\Users\admin\AppData\Local\Temp\kprm_2.8.exe | — | explorer.exe | |||||||||||
User: admin Company: kernel-panik Integrity Level: MEDIUM Description: KpRm By Kernel-Panik Exit code: 3221226540 Version: 2.0.0.8 Modules
| |||||||||||||||
| 2320 | C:\Windows\system32\cmd.exe /c timeout 5 && del /F /Q "C:\Users\admin\AppData\Local\Temp\kprm_2.8.exe" | C:\Windows\system32\cmd.exe | — | kprm_2.8.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2720 | C:\Windows\system32\DllHost.exe /Processid:{F32D97DF-E3E5-4CB9-9E3E-0EB5B4E49801} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3416 | timeout 5 | C:\Windows\system32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: timeout - pauses command processing Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3756 | "C:\Users\admin\AppData\Local\Temp\kprm_2.8.exe" | C:\Users\admin\AppData\Local\Temp\kprm_2.8.exe | explorer.exe | ||||||||||||
User: admin Company: kernel-panik Integrity Level: HIGH Description: KpRm By Kernel-Panik Exit code: 0 Version: 2.0.0.8 Modules
| |||||||||||||||
| 3896 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
234
Read events
136
Write events
98
Delete events
0
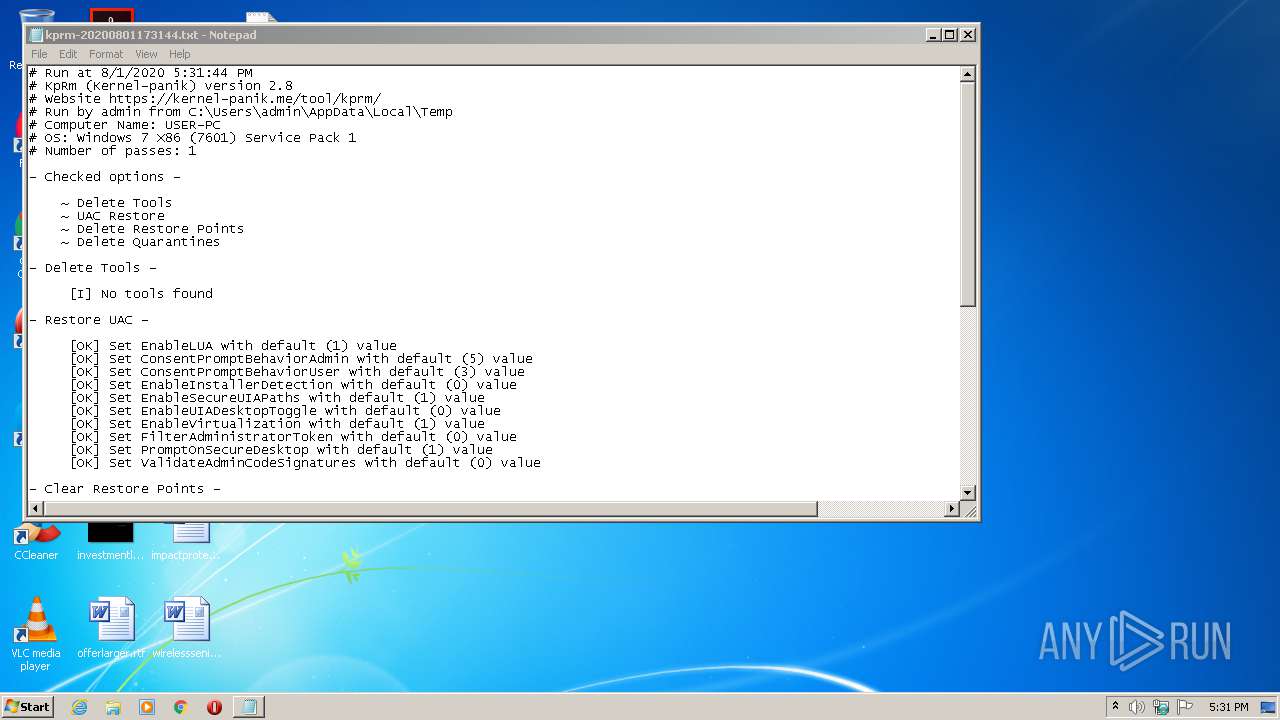
Modification events
| (PID) Process: | (2720) DllHost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 400000000000000052A1B63F2168D601A00A0000B40B0000D2070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3756) kprm_2.8.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | EnableLUA |
Value: 1 | |||
| (PID) Process: | (3756) kprm_2.8.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | ConsentPromptBehaviorAdmin |
Value: 5 | |||
| (PID) Process: | (3756) kprm_2.8.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | ConsentPromptBehaviorUser |
Value: 3 | |||
| (PID) Process: | (3756) kprm_2.8.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | EnableInstallerDetection |
Value: 0 | |||
| (PID) Process: | (3756) kprm_2.8.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | EnableSecureUIAPaths |
Value: 1 | |||
| (PID) Process: | (3756) kprm_2.8.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | EnableUIADesktopToggle |
Value: 0 | |||
| (PID) Process: | (3756) kprm_2.8.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | EnableVirtualization |
Value: 1 | |||
| (PID) Process: | (3756) kprm_2.8.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | FilterAdministratorToken |
Value: 0 | |||
| (PID) Process: | (3756) kprm_2.8.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | PromptOnSecureDesktop |
Value: 1 | |||
Executable files
0
Suspicious files
0
Text files
100
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3756 | kprm_2.8.exe | C:\Users\admin\AppData\Local\Temp\aut7744.tmp | — | |
MD5:— | SHA256:— | |||
| 3756 | kprm_2.8.exe | C:\Users\admin\AppData\Local\Temp\aut7745.tmp | — | |
MD5:— | SHA256:— | |||
| 3756 | kprm_2.8.exe | C:\Users\admin\AppData\Local\Temp\aut7746.tmp | — | |
MD5:— | SHA256:— | |||
| 3756 | kprm_2.8.exe | C:\Users\admin\AppData\Local\Temp\aut7747.tmp | — | |
MD5:— | SHA256:— | |||
| 3756 | kprm_2.8.exe | C:\Users\admin\AppData\Local\Temp\~DF89EA94B9F6924587.TMP | — | |
MD5:— | SHA256:— | |||
| 3756 | kprm_2.8.exe | C:\Users\admin\AppData\Local\Temp\KPRM\kprm-tools.xml | text | |
MD5:— | SHA256:— | |||
| 3756 | kprm_2.8.exe | C:\Users\admin\Desktop\kprm-20200801173144.txt | text | |
MD5:— | SHA256:— | |||
| 3756 | kprm_2.8.exe | C:\KPRM\kprm-20200801173144.txt | text | |
MD5:— | SHA256:— | |||
| 3756 | kprm_2.8.exe | C:\Users\admin\AppData\Local\Temp\KPRM\kprm-close.gif | image | |
MD5:B940F9839161F936B596C6AAC7795B63 | SHA256:33BE3877539E6A83AACDBBDC7A7A9FE28F495F108B3DBE624237CF95543DFA04 | |||
| 3756 | kprm_2.8.exe | C:\Users\admin\AppData\Local\Temp\KPRM\kprm-logo.gif | image | |
MD5:586108678B48474BC7745018F7B7A95E | SHA256:D64E2562DC0E6C994694706CA318553C7D90090092EE8A8802756D174CF69493 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report