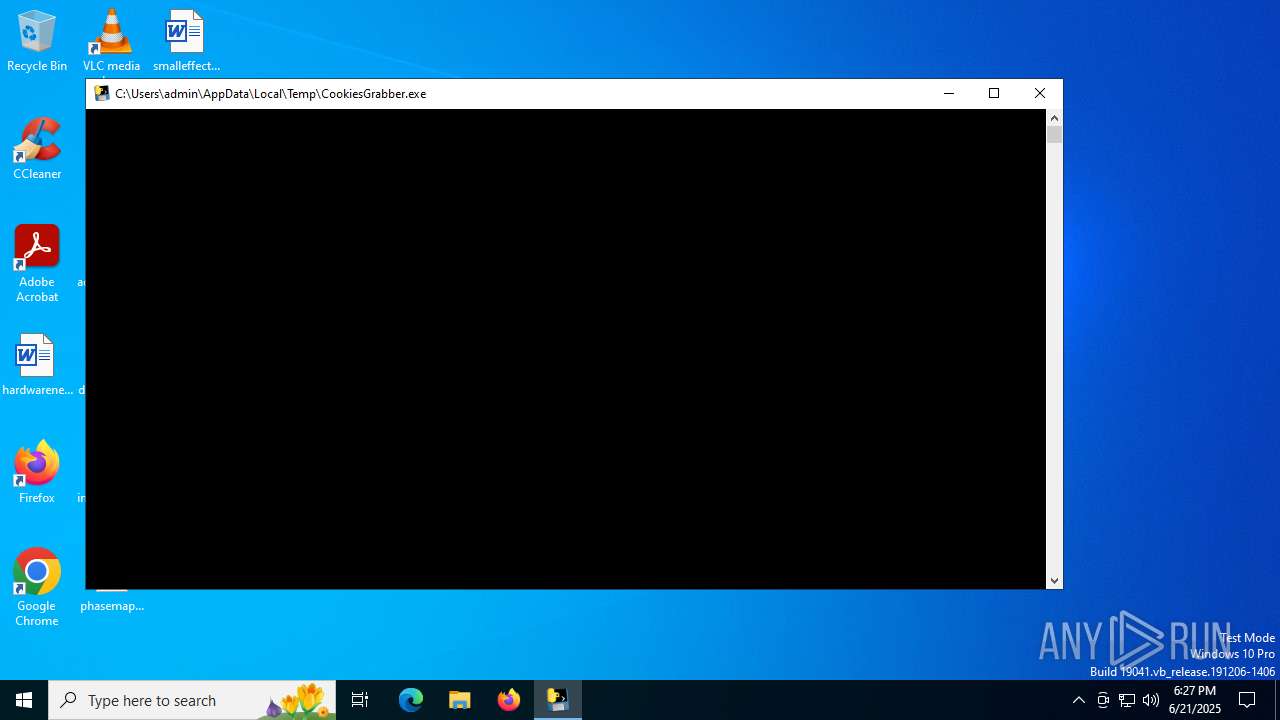
| File name: | CookiesGrabber.exe |
| Full analysis: | https://app.any.run/tasks/8d477ec6-bd8e-496d-a8c3-981c48862b4f |
| Verdict: | Malicious activity |
| Analysis date: | June 21, 2025, 18:26:57 |
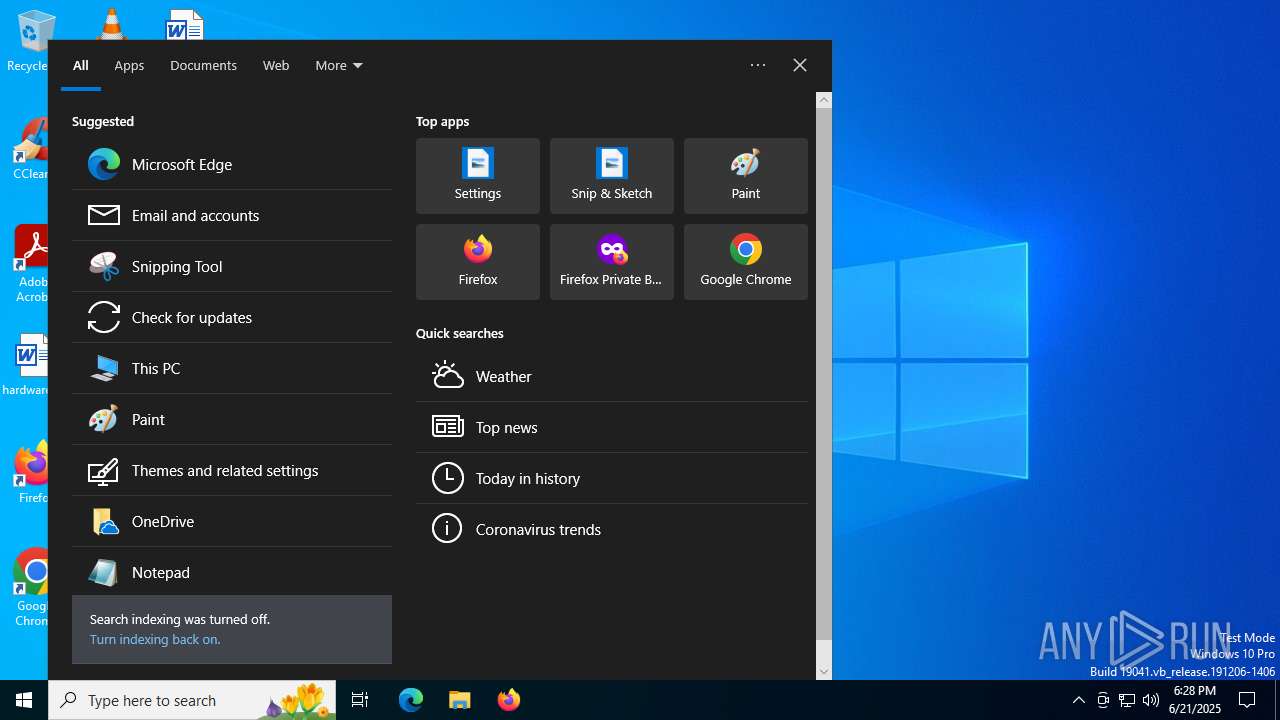
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (console) x86-64, for MS Windows, 7 sections |
| MD5: | 1099BAA9E7504DFFE917EEB846C16943 |
| SHA1: | F69FDF685BC0A2F51ACEAFE516579C50BC830330 |
| SHA256: | B513572FBC4154717C723D52DD793C413D98EF370EFB050FF800A89C8DCD15C4 |
| SSDEEP: | 98304:zD/lCFXRRdopaZOl/QOsIgMb1mB75kzlUzUjGNgLN71bxelLb/ncfNAnYRO4Y6Zd:GJG93881mwe/kiPNAnQBI1G |
MALICIOUS
No malicious indicators.SUSPICIOUS
Process drops python dynamic module
- CookiesGrabber.exe (PID: 7100)
Executable content was dropped or overwritten
- CookiesGrabber.exe (PID: 7100)
Application launched itself
- CookiesGrabber.exe (PID: 7100)
Process drops legitimate windows executable
- CookiesGrabber.exe (PID: 7100)
The process drops C-runtime libraries
- CookiesGrabber.exe (PID: 7100)
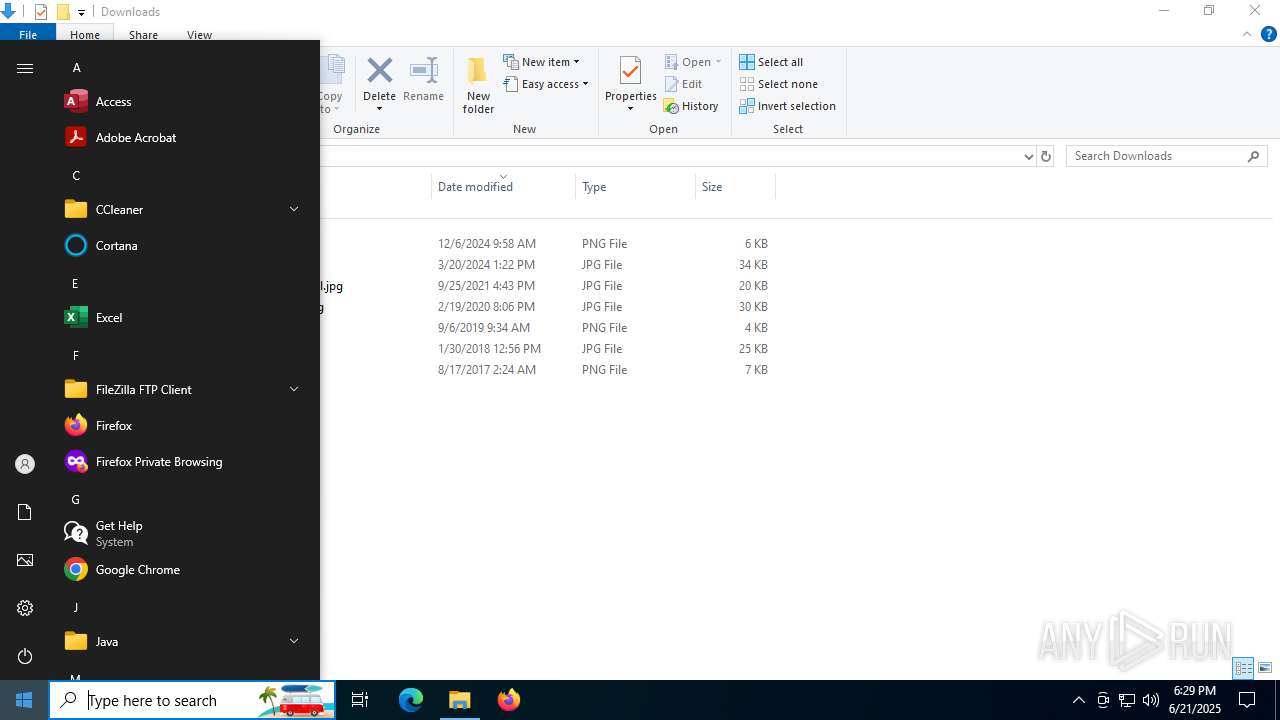
Loads Python modules
- CookiesGrabber.exe (PID: 4500)
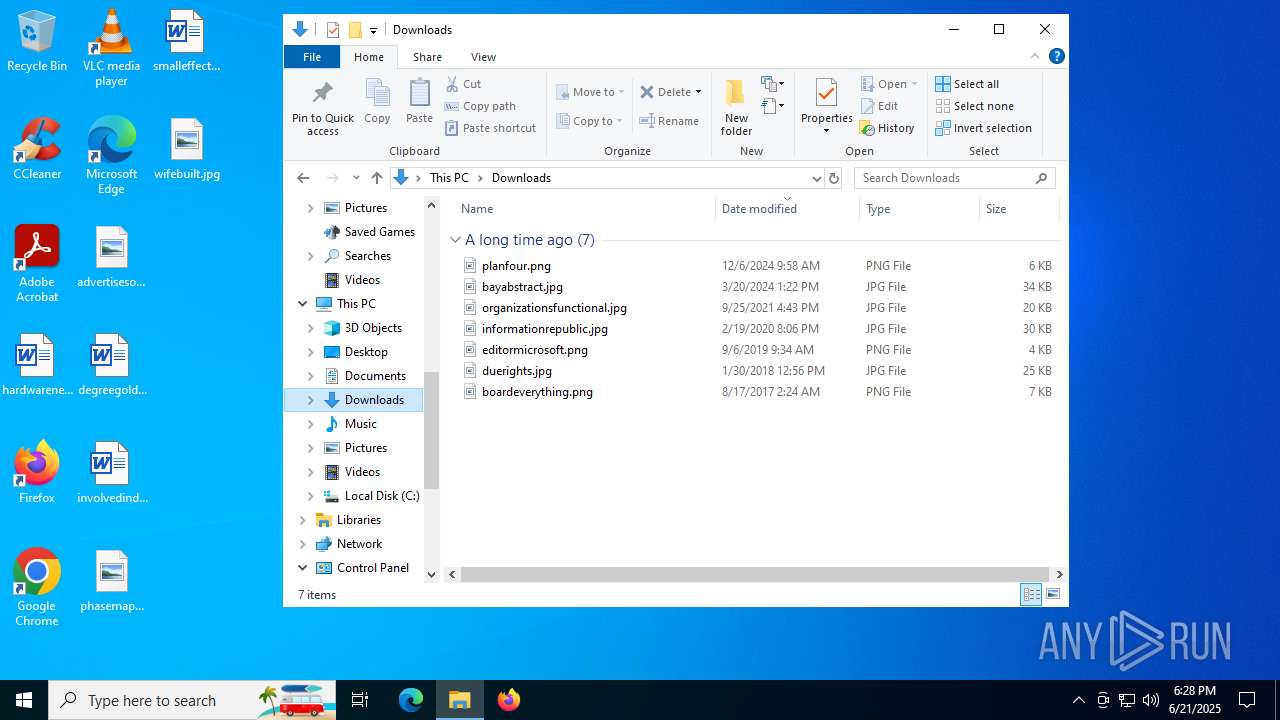
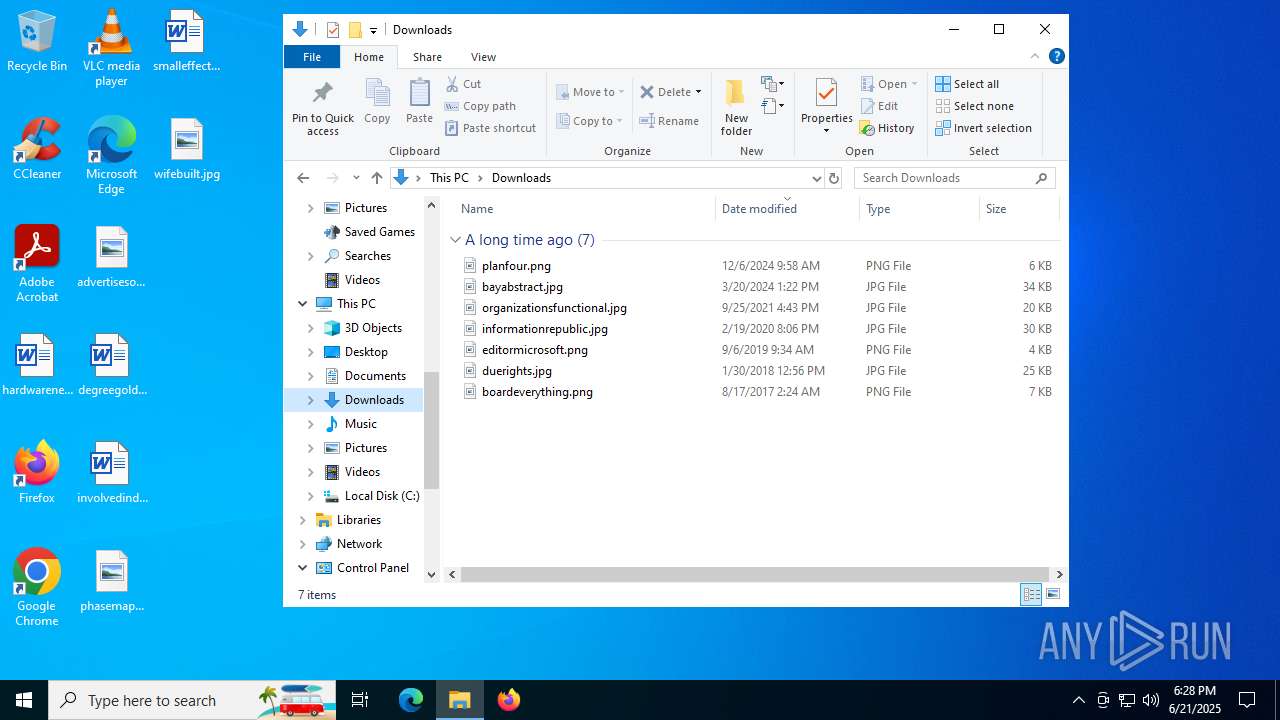
Reads browser cookies
- CookiesGrabber.exe (PID: 4500)
INFO
Reads the computer name
- CookiesGrabber.exe (PID: 7100)
- CookiesGrabber.exe (PID: 4500)
Checks supported languages
- CookiesGrabber.exe (PID: 7100)
- CookiesGrabber.exe (PID: 4500)
- SearchApp.exe (PID: 5328)
The sample compiled with english language support
- CookiesGrabber.exe (PID: 7100)
Create files in a temporary directory
- CookiesGrabber.exe (PID: 7100)
Creates files or folders in the user directory
- CookiesGrabber.exe (PID: 4500)
Reads the software policy settings
- slui.exe (PID: 5168)
- SearchApp.exe (PID: 5328)
Process checks computer location settings
- SearchApp.exe (PID: 5328)
Reads the machine GUID from the registry
- SearchApp.exe (PID: 5328)
Checks proxy server information
- slui.exe (PID: 5168)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:06:21 18:25:10+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.43 |
| CodeSize: | 179712 |
| InitializedDataSize: | 155136 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xc650 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
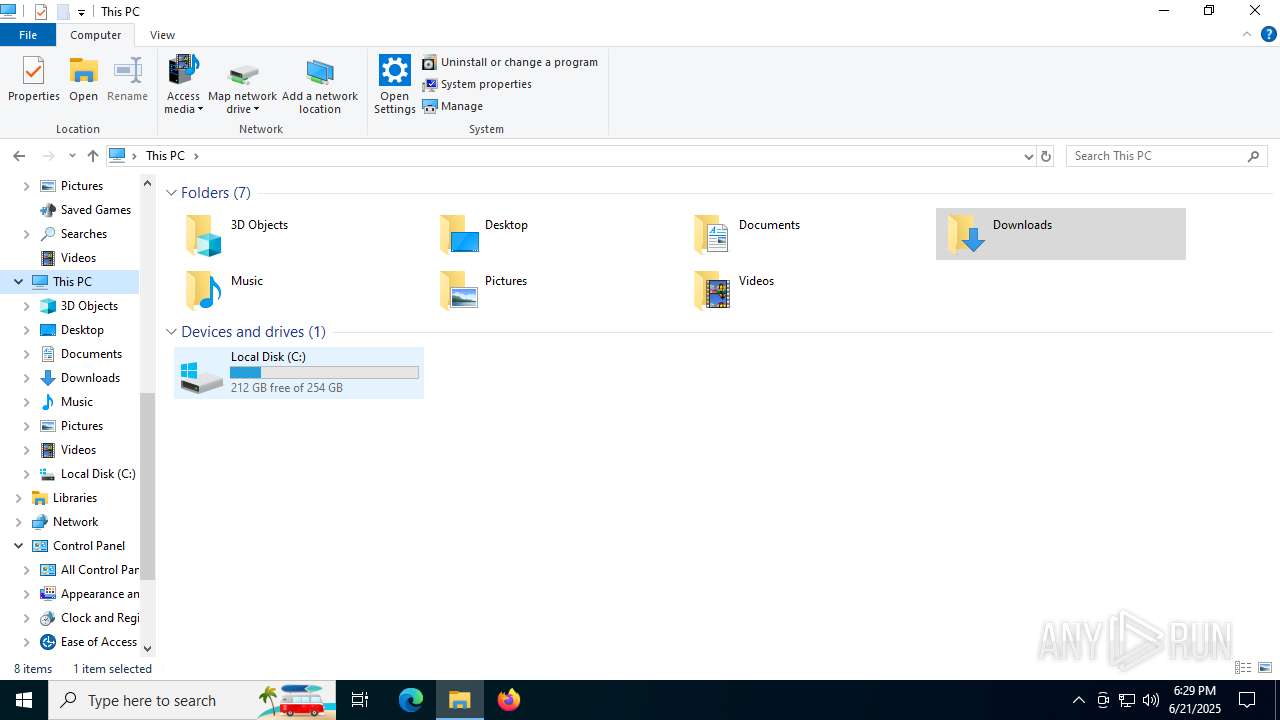
Total processes
150
Monitored processes
6
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3756 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | CookiesGrabber.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4500 | "C:\Users\admin\AppData\Local\Temp\CookiesGrabber.exe" | C:\Users\admin\AppData\Local\Temp\CookiesGrabber.exe | — | CookiesGrabber.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 5168 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5328 | "C:\WINDOWS\SystemApps\Microsoft.Windows.Search_cw5n1h2txyewy\SearchApp.exe" -ServerName:CortanaUI.AppX8z9r6jm96hw4bsbneegw0kyxx296wr9t.mca | C:\Windows\SystemApps\Microsoft.Windows.Search_cw5n1h2txyewy\SearchApp.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Search application Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6260 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7100 | "C:\Users\admin\AppData\Local\Temp\CookiesGrabber.exe" | C:\Users\admin\AppData\Local\Temp\CookiesGrabber.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
7 036
Read events
6 931
Write events
98
Delete events
7
Modification events
| (PID) Process: | (5328) SearchApp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Search\Flighting |
| Operation: | delete value | Name: | CachedFeatureString |
Value: | |||
| (PID) Process: | (5328) SearchApp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\SearchSettings |
| Operation: | write | Name: | IsMSACloudSearchEnabled |
Value: 0 | |||
| (PID) Process: | (5328) SearchApp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\SearchSettings |
| Operation: | write | Name: | IsAADCloudSearchEnabled |
Value: 0 | |||
| (PID) Process: | (5328) SearchApp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Search |
| Operation: | write | Name: | CortanaStateLastRun |
Value: 9AF9566800000000 | |||
| (PID) Process: | (5328) SearchApp.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.search_cw5n1h2txyewy\SOFTWARE\Microsoft\Speech_OneCore\Isolated\A1hdl50UVDh2ZbG324Nx-6fZgntcGnHOs5kHLdmaJYE\HKEY_CURRENT_USER\SOFTWARE\Microsoft\Speech_OneCore\Recognizers |
| Operation: | write | Name: | DefaultTokenId |
Value: HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Speech_OneCore\Recognizers\Tokens\MS-1033-110-WINMO-DNN | |||
| (PID) Process: | (5328) SearchApp.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.search_cw5n1h2txyewy\Internet Explorer\DOMStorage\bing.com |
| Operation: | write | Name: | Total |
Value: 1517 | |||
| (PID) Process: | (5328) SearchApp.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.search_cw5n1h2txyewy\Internet Explorer\DOMStorage\bing.com |
| Operation: | write | Name: | Total |
Value: 2244 | |||
| (PID) Process: | (5328) SearchApp.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.search_cw5n1h2txyewy\Internet Explorer\DOMStorage\bing.com |
| Operation: | write | Name: | Total |
Value: 949 | |||
| (PID) Process: | (5328) SearchApp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\SearchSettings |
| Operation: | write | Name: | SafeSearchMode |
Value: 1 | |||
| (PID) Process: | (5328) SearchApp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Search\Flighting |
| Operation: | write | Name: | CachedFeatureString |
Value: | |||
Executable files
71
Suspicious files
88
Text files
184
Unknown types
0
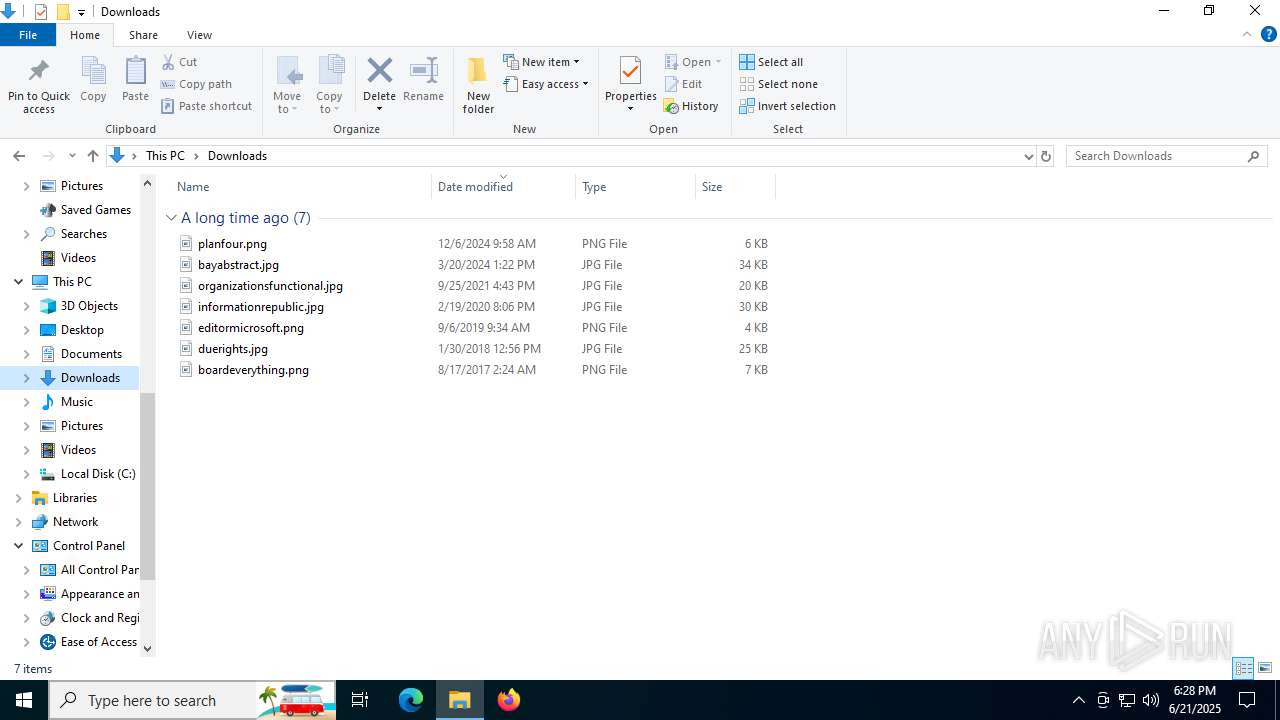
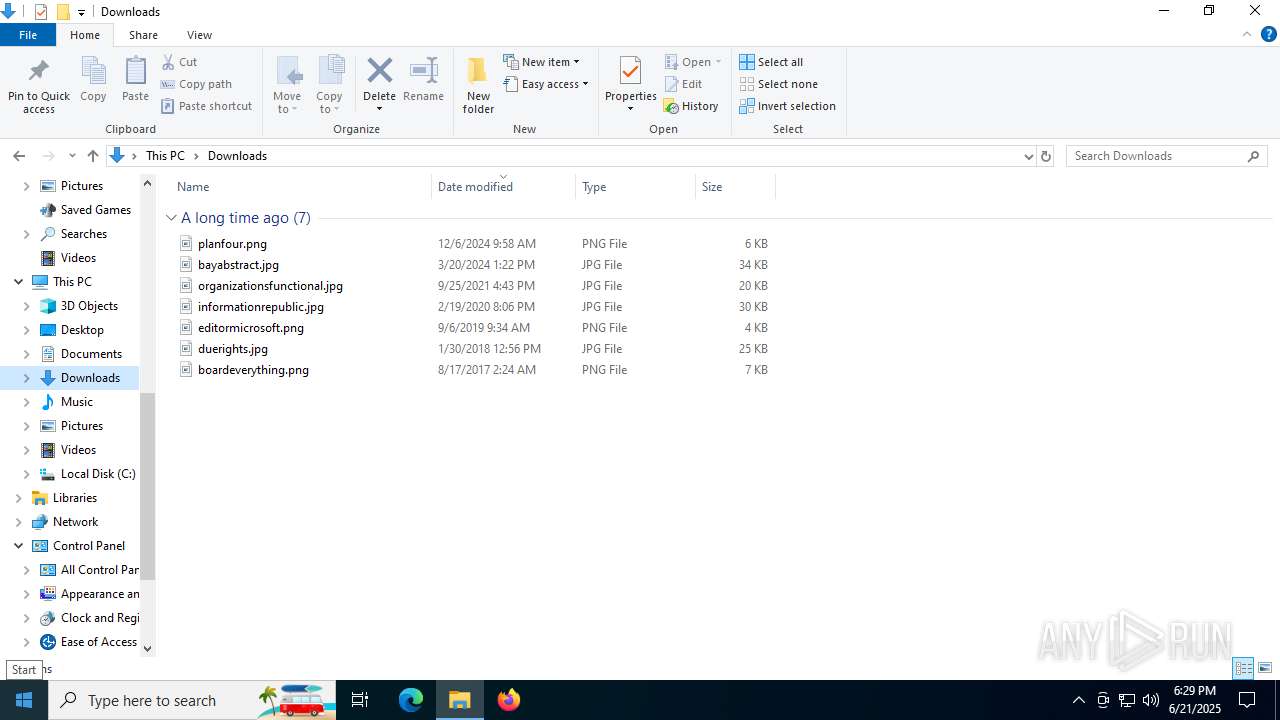
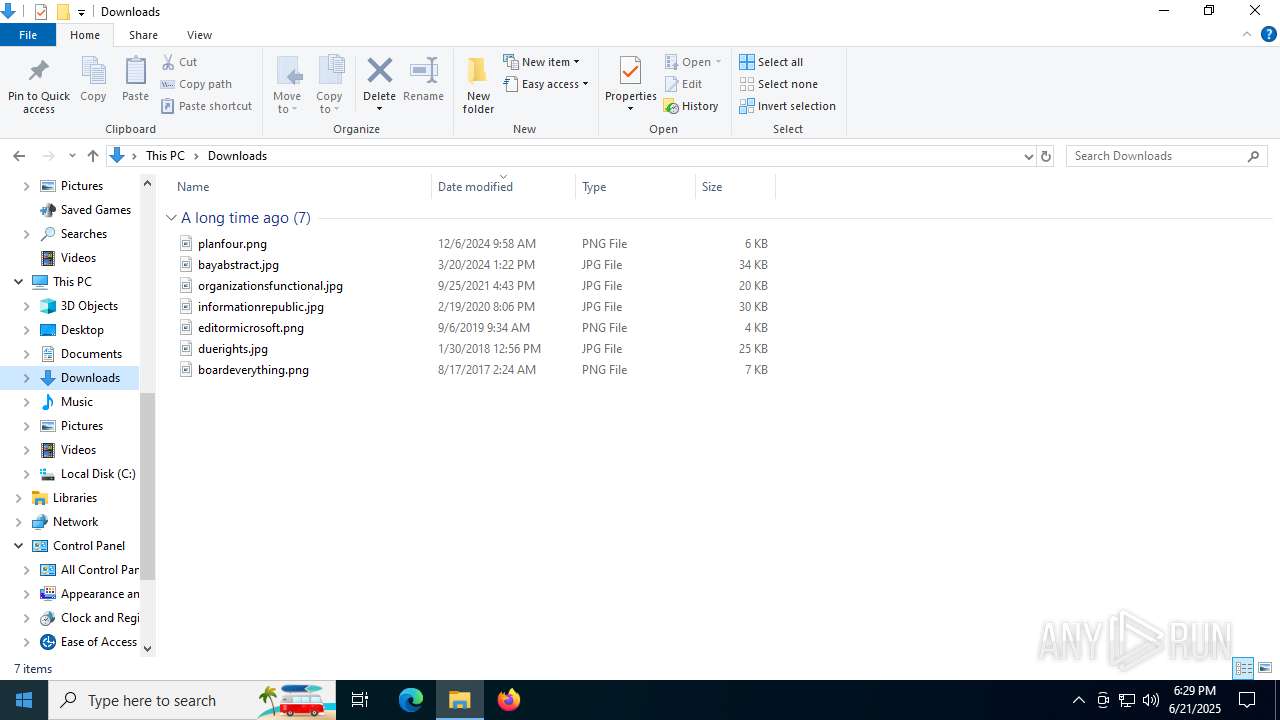
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7100 | CookiesGrabber.exe | C:\Users\admin\AppData\Local\Temp\_MEI71002\Crypto\Cipher\_raw_aes.pyd | executable | |
MD5:61CB04BF8E8C111AB4B6FED3BE0E8FA9 | SHA256:DD5A327AF8913D4B772E37ABB1FB7E0F74D4CE0E5850EB06A4329720FC159175 | |||
| 7100 | CookiesGrabber.exe | C:\Users\admin\AppData\Local\Temp\_MEI71002\Crypto\Cipher\_chacha20.pyd | executable | |
MD5:709BE56D3AE0CB50807A6B54A762C875 | SHA256:612B4DA235E04CB9CE0106A13AA31AB7D5F651A0685653EDC9A57E1F93BE5670 | |||
| 7100 | CookiesGrabber.exe | C:\Users\admin\AppData\Local\Temp\_MEI71002\Crypto\Cipher\_raw_ocb.pyd | executable | |
MD5:35B044D9ECD823161EF267517BA88509 | SHA256:3B236F9148645B4CE4375D2BEE7844F4F5D381746F4A33492A3C35C2B156DE4D | |||
| 7100 | CookiesGrabber.exe | C:\Users\admin\AppData\Local\Temp\_MEI71002\Crypto\Cipher\_raw_blowfish.pyd | executable | |
MD5:403A4F70938F58C15DAEB4A63D7ECADB | SHA256:FB407812E3E4D17B2CA981C8B95C716FF1B288A5E4658A831CD067A2837A753B | |||
| 7100 | CookiesGrabber.exe | C:\Users\admin\AppData\Local\Temp\_MEI71002\Crypto\Cipher\_raw_ofb.pyd | executable | |
MD5:A2B9F1DB81EE431F07A848F44153518F | SHA256:CD11346BDC23F15D68701C3F602B621BB7C93CF1AAA193FF079225603514122D | |||
| 7100 | CookiesGrabber.exe | C:\Users\admin\AppData\Local\Temp\_MEI71002\Crypto\Hash\_BLAKE2b.pyd | executable | |
MD5:7FCAD6D233F8F41636258C970390284C | SHA256:E0D97FD22D02BE38357905F8D833E1CD78839EDF986692EDE944F9EE0CEE8B40 | |||
| 7100 | CookiesGrabber.exe | C:\Users\admin\AppData\Local\Temp\_MEI71002\Crypto\Cipher\_raw_cfb.pyd | executable | |
MD5:BF18D19EB79557E767A8E8E1EDA6C060 | SHA256:6DE05E3507157C94F20825196677E12964780502D5A3DD04424B05C3E4AEF186 | |||
| 7100 | CookiesGrabber.exe | C:\Users\admin\AppData\Local\Temp\_MEI71002\Crypto\Cipher\_raw_aesni.pyd | executable | |
MD5:133B156E060C77AF41B38841A32DA4B6 | SHA256:20005B988FE848983A65F7F4727EC27148E4D0ABEAB9CFD0E58778F812BF7595 | |||
| 7100 | CookiesGrabber.exe | C:\Users\admin\AppData\Local\Temp\_MEI71002\Crypto\Cipher\_raw_ctr.pyd | executable | |
MD5:3D0FB2250C76B501ABF008D8E6180594 | SHA256:E5E2B54591D4CA2DC43F6D0FFDBFF45393D092E9E37C072FFE7B8769EEC3B82E | |||
| 7100 | CookiesGrabber.exe | C:\Users\admin\AppData\Local\Temp\_MEI71002\Crypto\Cipher\_raw_des3.pyd | executable | |
MD5:494239F9453679D80511BECC23C6B621 | SHA256:9C849A1DD641A3143C25B261E18D8F1453B00BB975E324384F15311C1B544F3D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
50
DNS requests
34
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1148 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5328 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
1148 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5328 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
2940 | svchost.exe | GET | 200 | 23.209.209.135:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
3620 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
5328 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
892 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2228 | RUXIMICS.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1268 | svchost.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2336 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
892 | svchost.exe | 20.190.159.128:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
892 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
1268 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 23.53.40.176:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5328 | SearchApp.exe | Not Suspicious Traffic | INFO [ANY.RUN] Azure Front Door domain observed in TLS SNI ( .azurefd .net) |