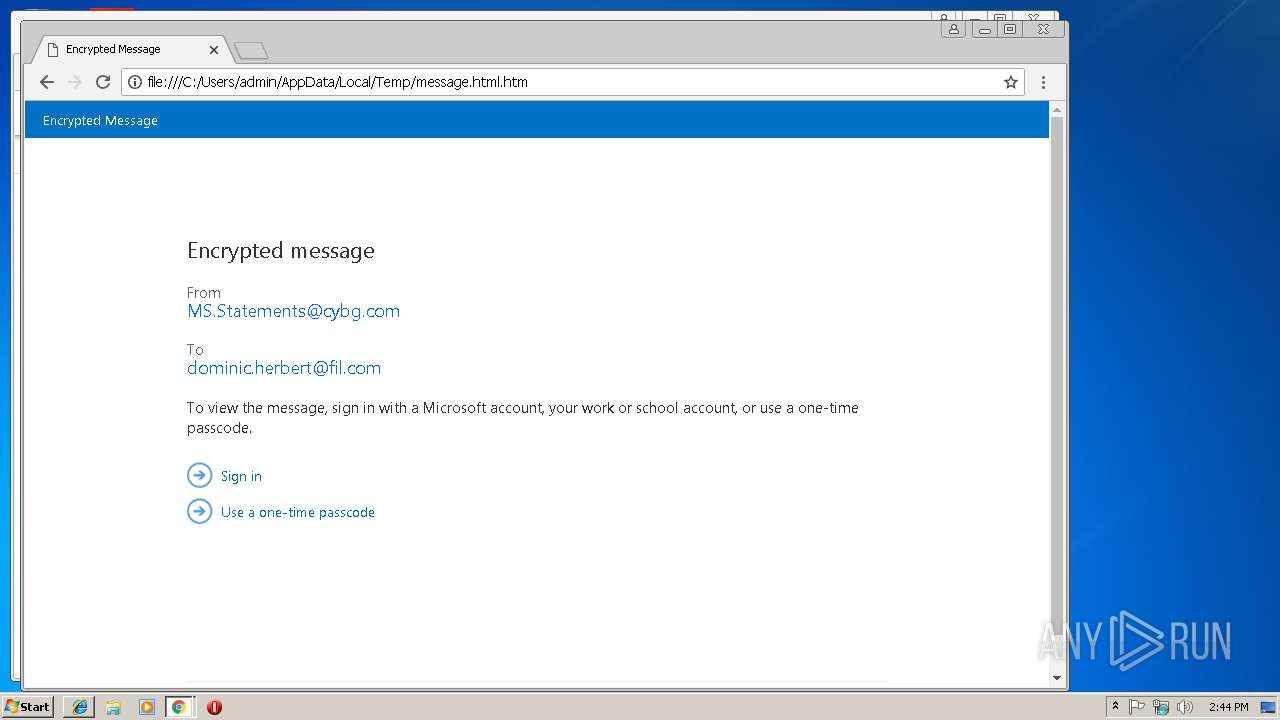
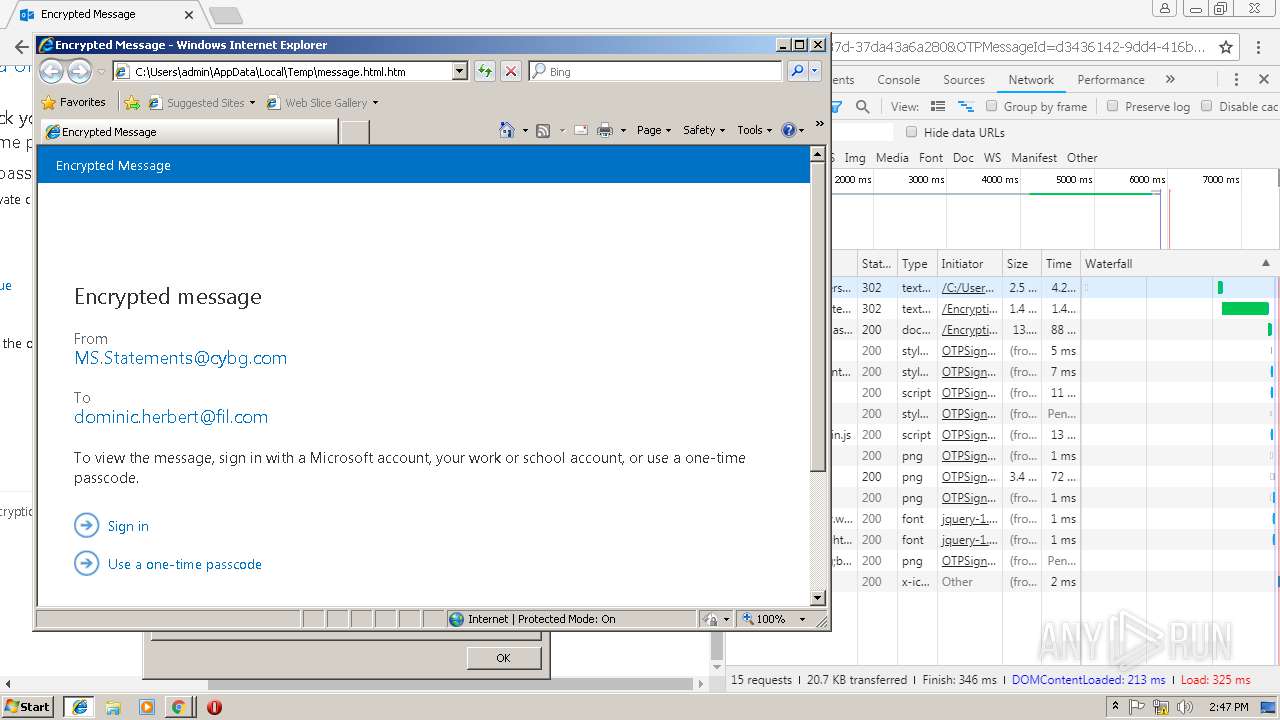
| File name: | message.html |
| Full analysis: | https://app.any.run/tasks/d5516951-28f7-4da5-8c39-55695eb76c62 |
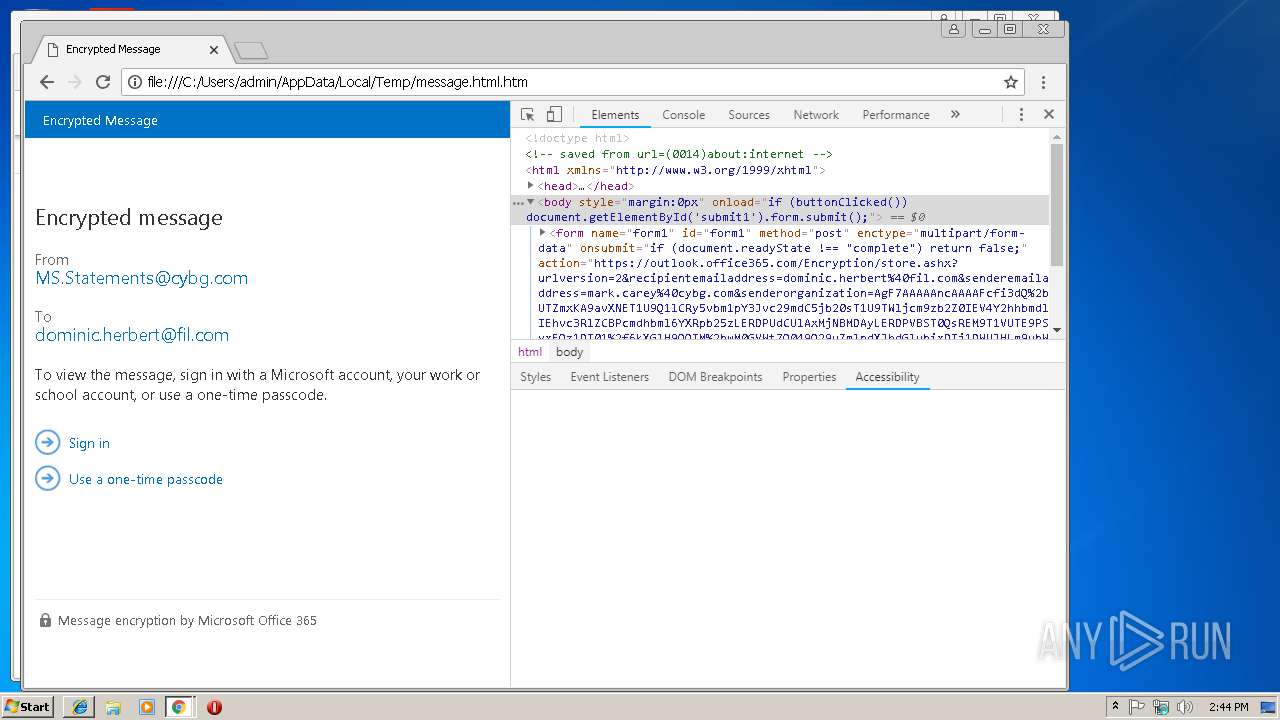
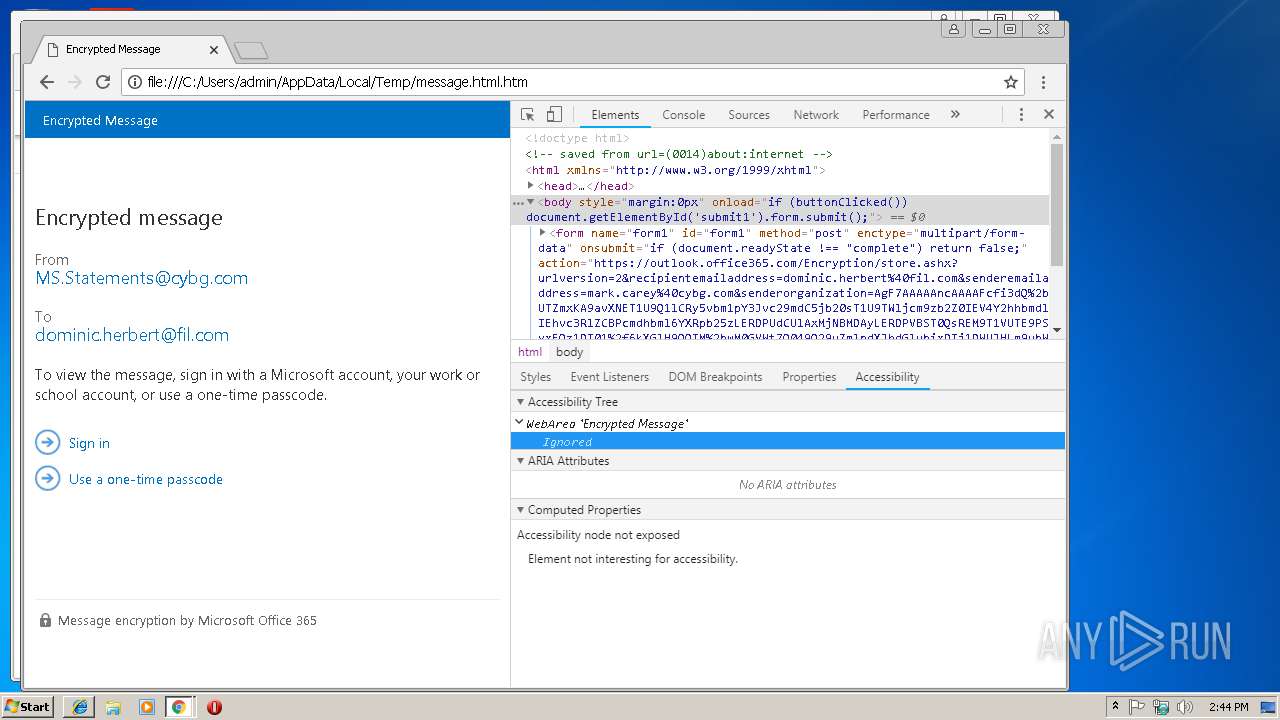
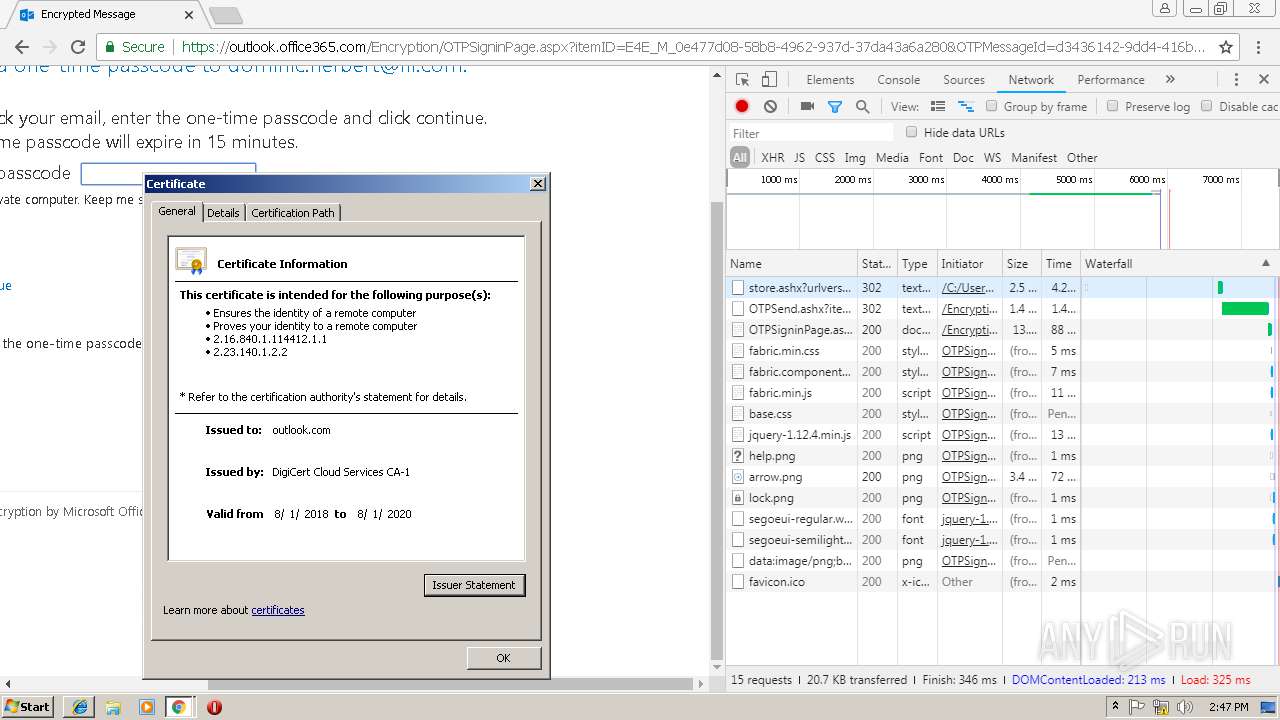
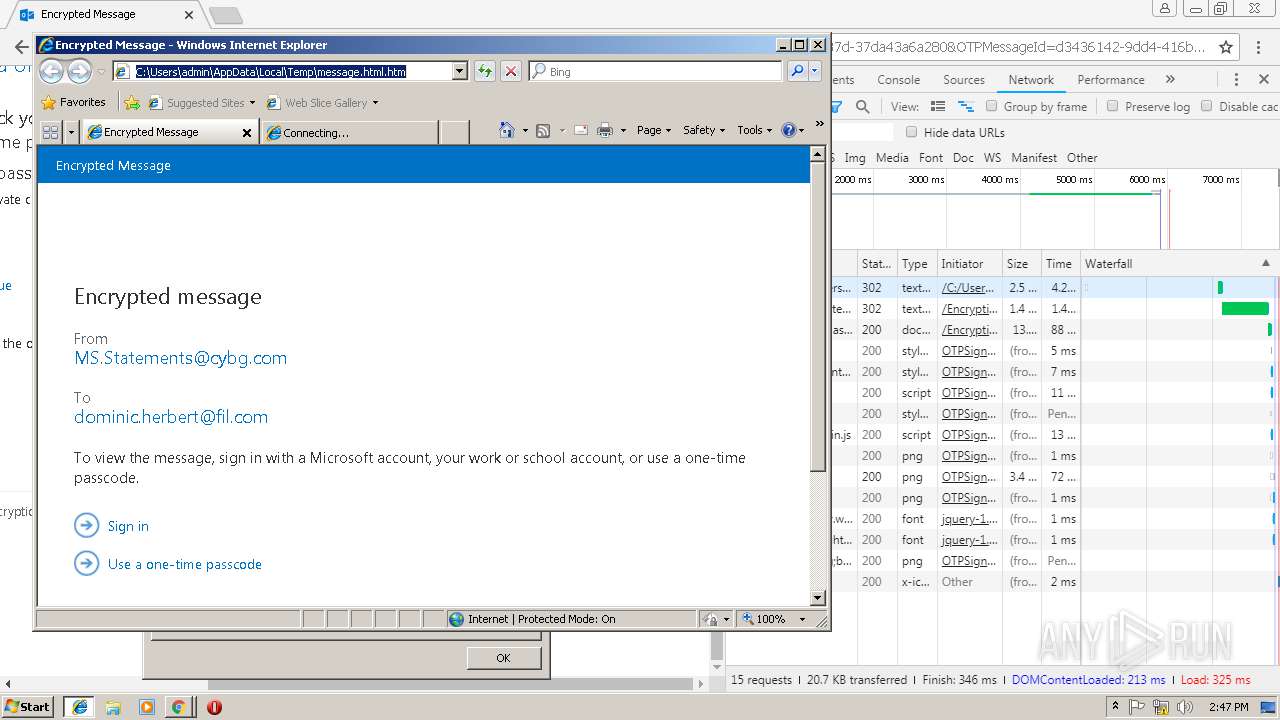
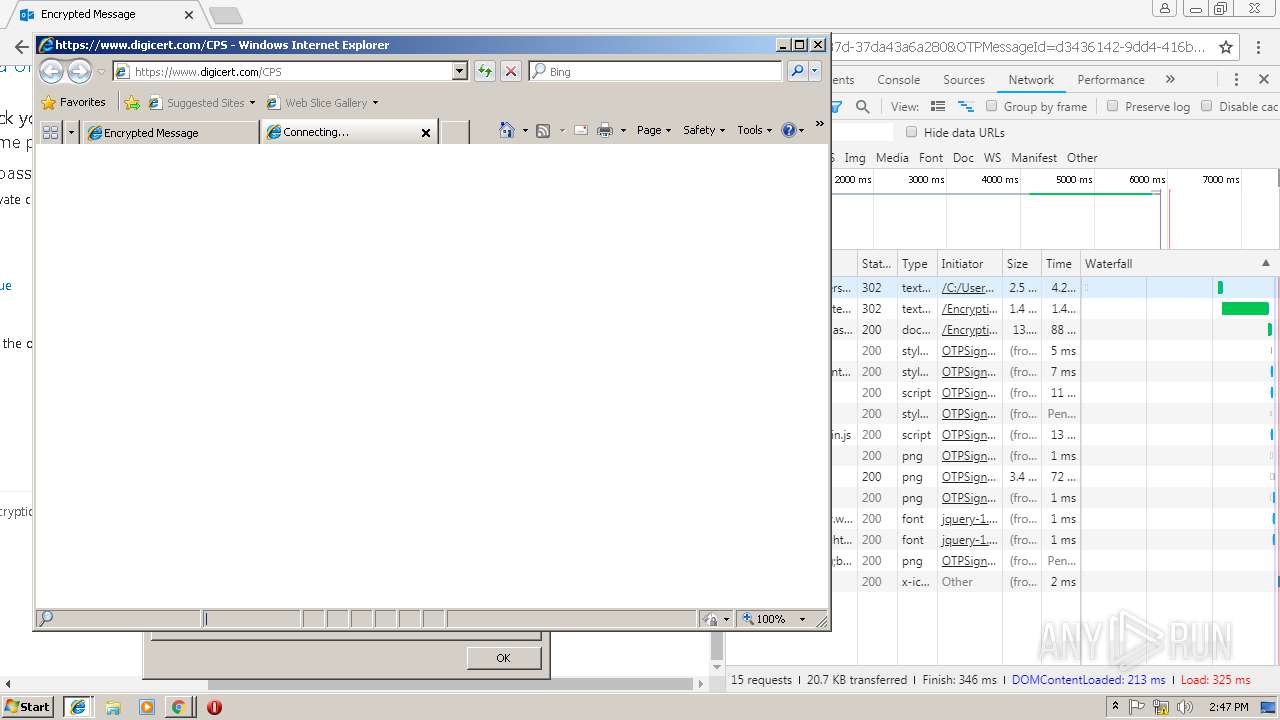
| Verdict: | Malicious activity |
| Analysis date: | January 10, 2019, 14:43:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, ASCII text, with very long lines, with CRLF line terminators |
| MD5: | 5F79D72546FEEE89DFA2D3AB43E3E9F6 |
| SHA1: | 85DEF7BDDE099BF09B2C8B30881298A69D8A3E87 |
| SHA256: | B51197A30F56EDF2B78E64DACCE2CA394E223A114FCD314E8AF3C04C8C9A9C56 |
| SSDEEP: | 12288:pciskNPC1d2W9xRbmc4vNrSFlYLi+cZBmS41N7FCMcXC4OWMbr9l:phskZkvxRbmnNrSoGnsKMcS/Wul |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Changes internet zones settings
- iexplore.exe (PID: 2984)
Reads internet explorer settings
- iexplore.exe (PID: 3632)
- iexplore.exe (PID: 2888)
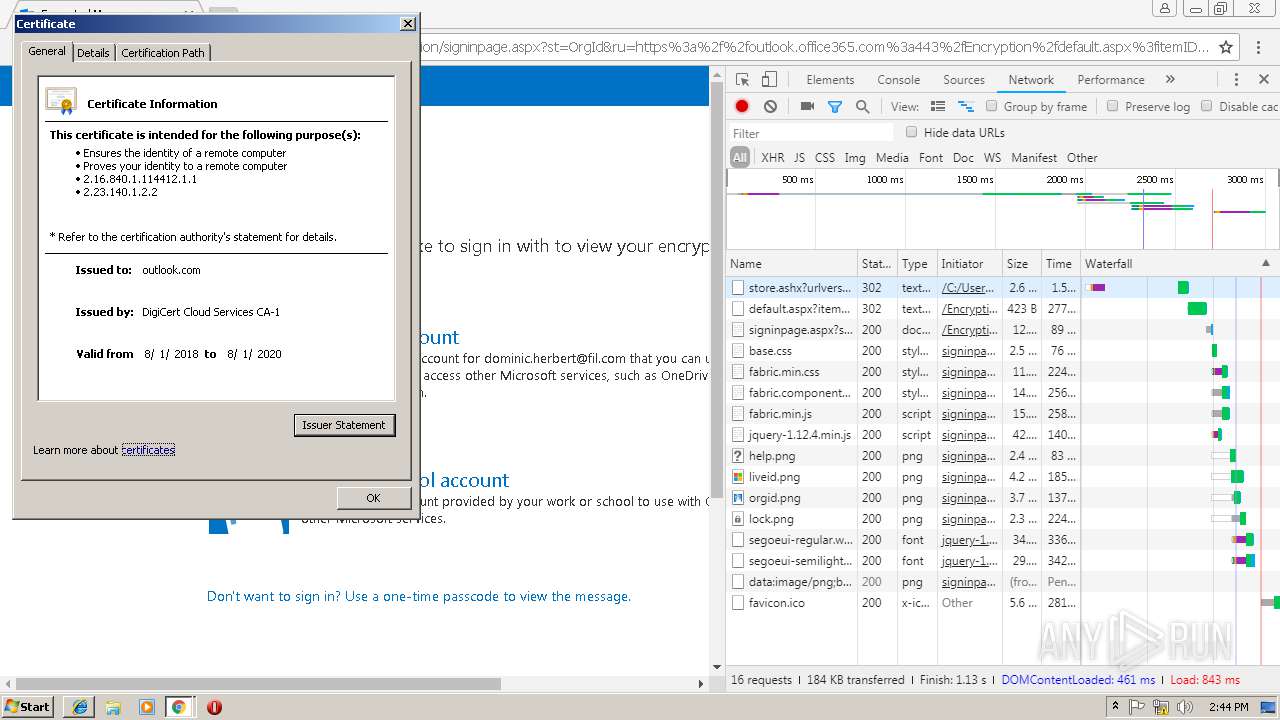
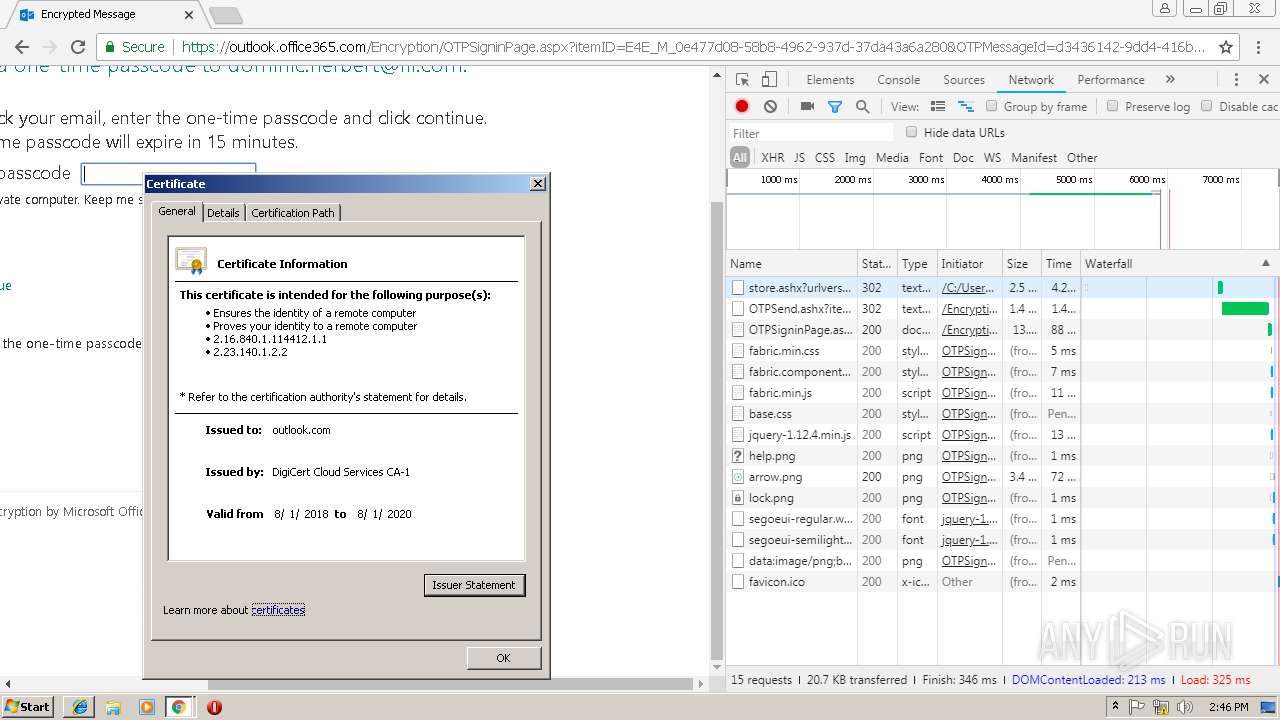
Reads settings of System Certificates
- chrome.exe (PID: 792)
Reads Internet Cache Settings
- iexplore.exe (PID: 3632)
- iexplore.exe (PID: 2984)
- iexplore.exe (PID: 2888)
Application launched itself
- chrome.exe (PID: 3116)
- iexplore.exe (PID: 2984)
- chrome.exe (PID: 792)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .htm/html | | | HyperText Markup Language with DOCTYPE (80.6) |
|---|---|---|
| .html | | | HyperText Markup Language (19.3) |
EXIF
HTML
| ContentType: | text/html;charset=UTF-8 |
|---|---|
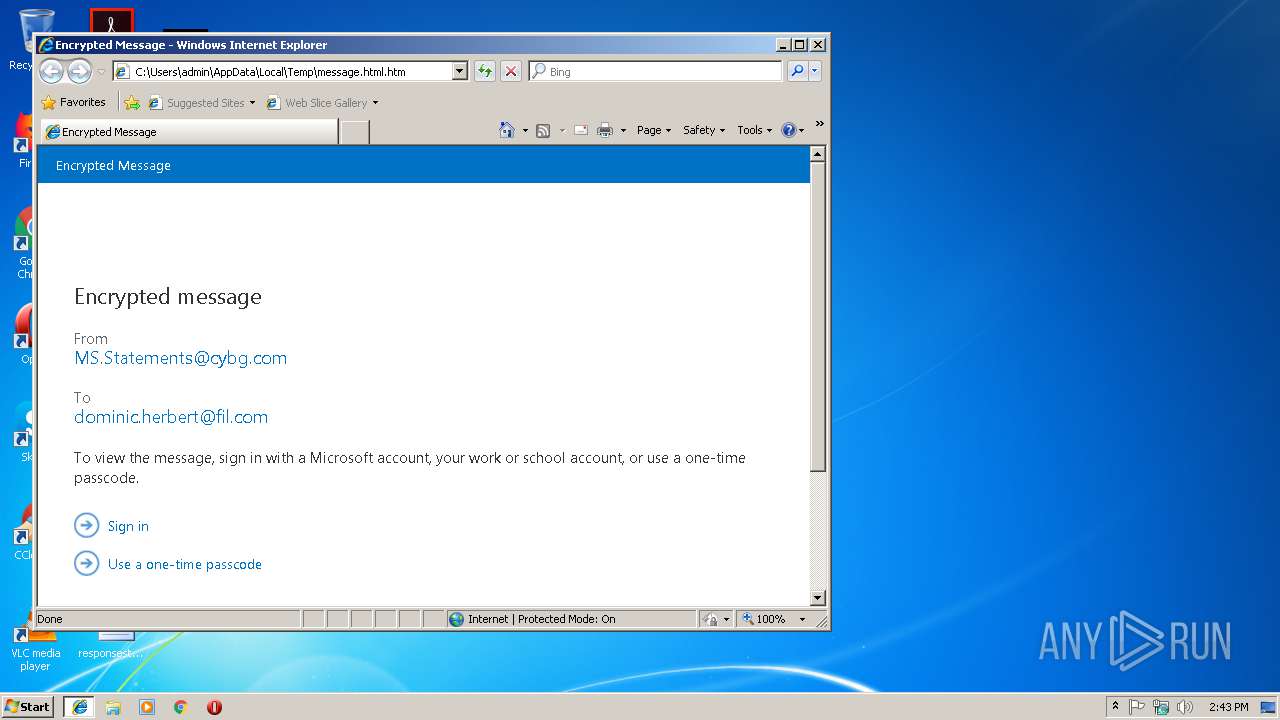
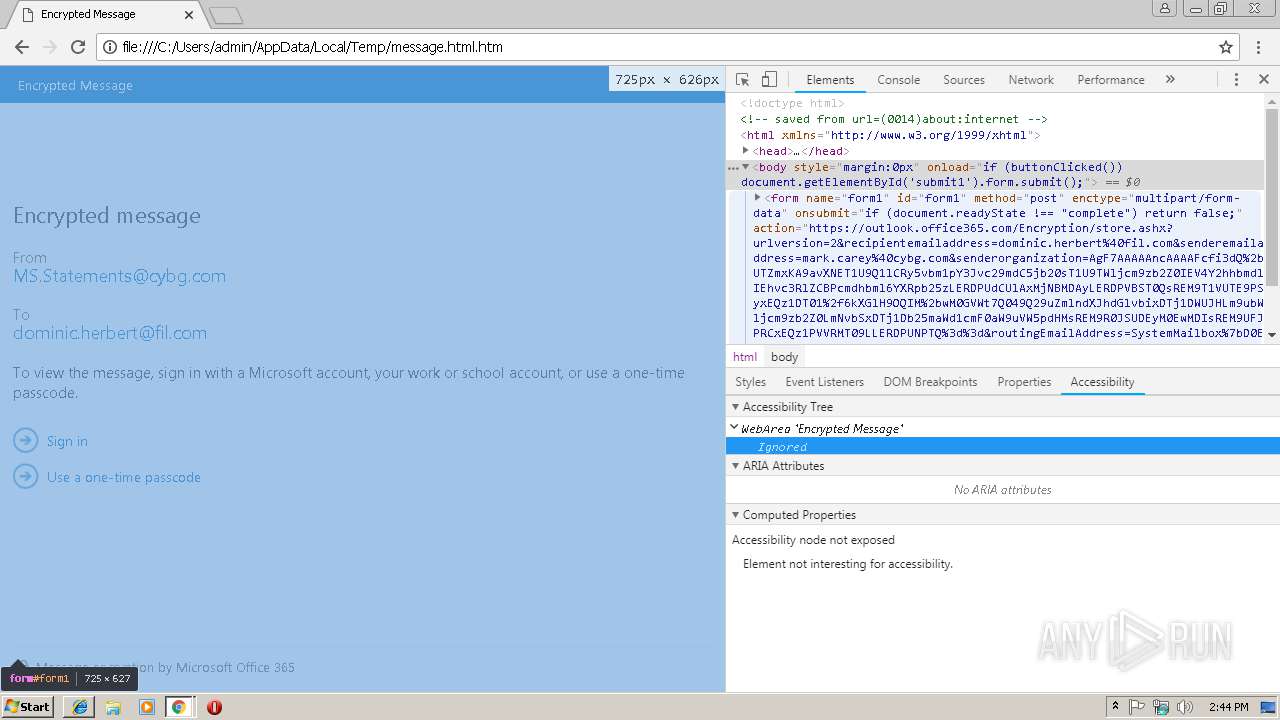
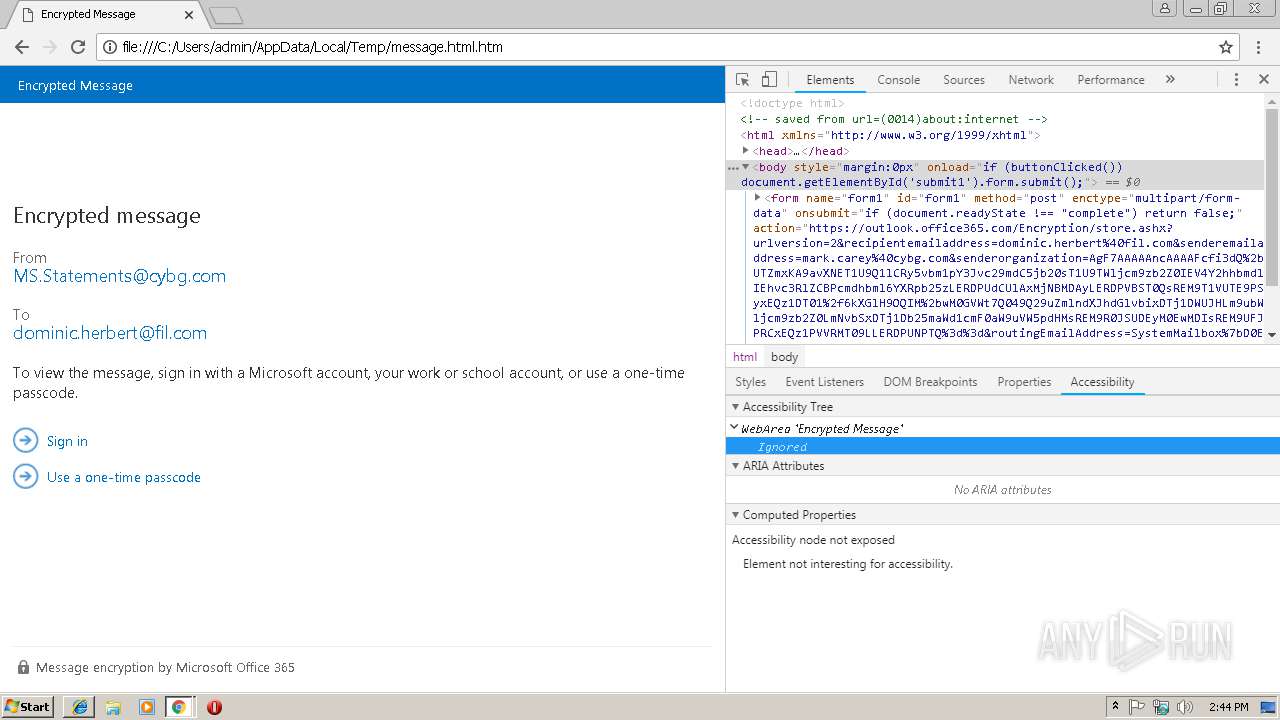
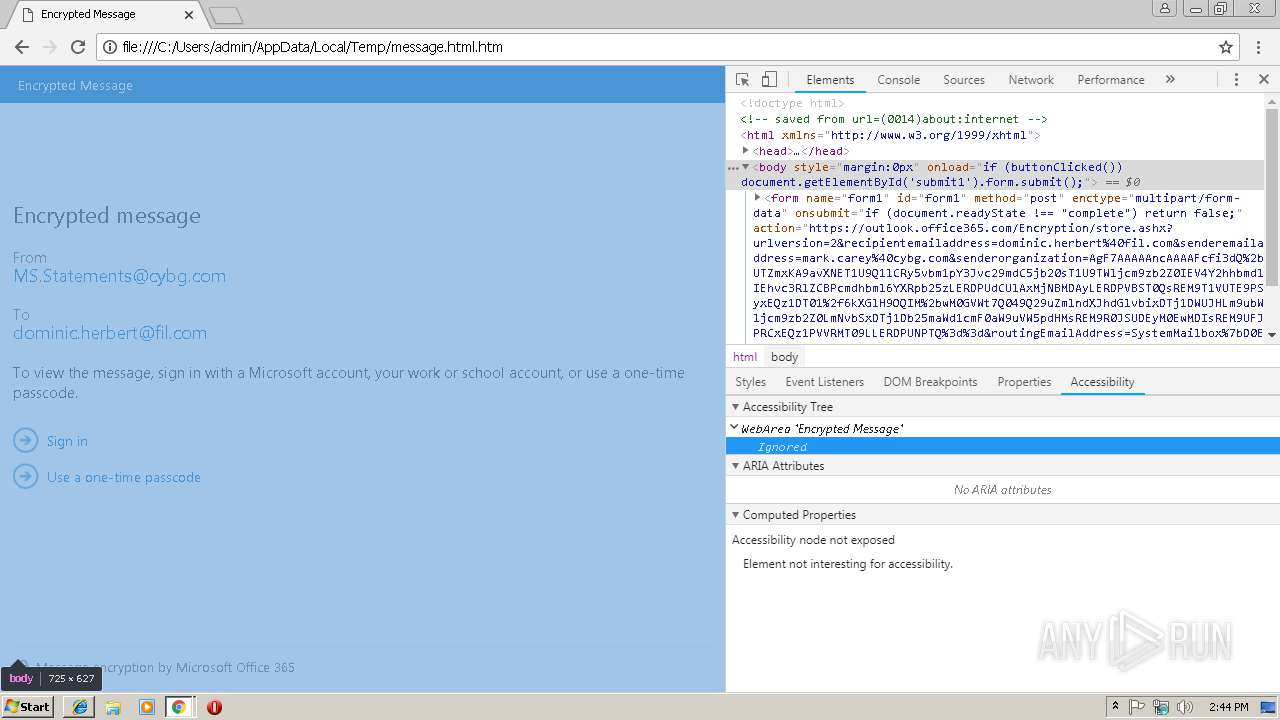
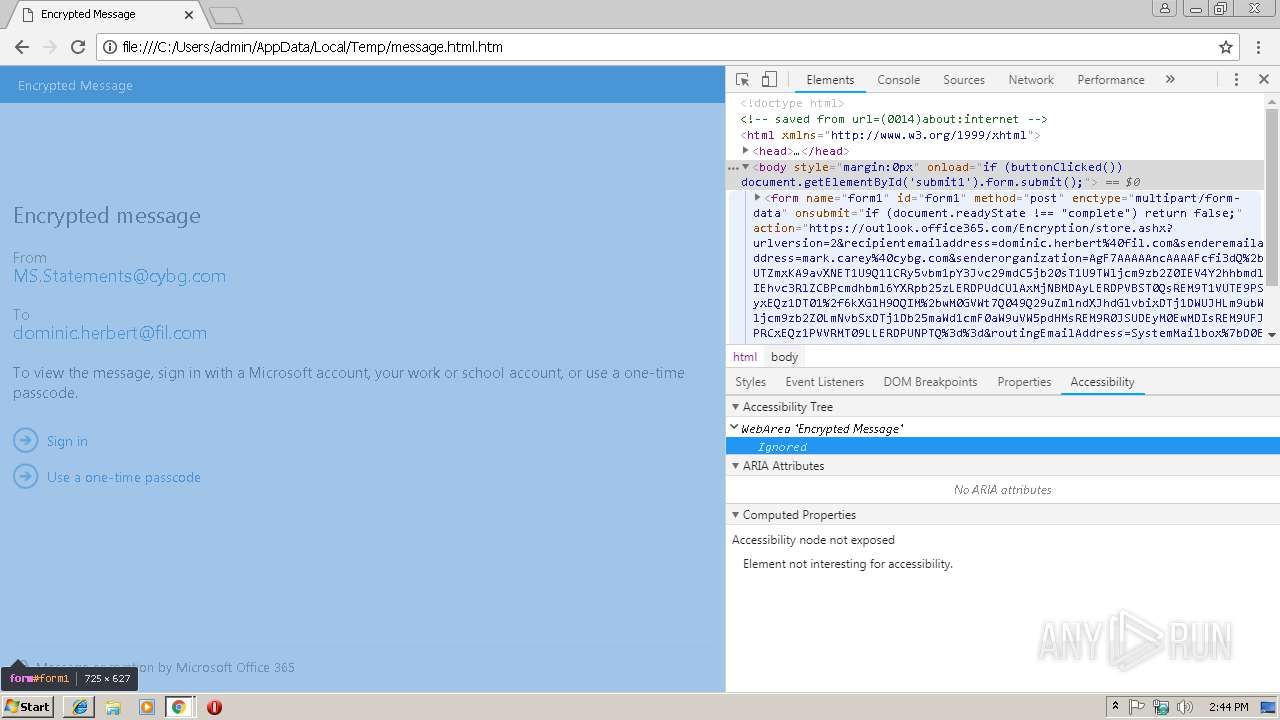
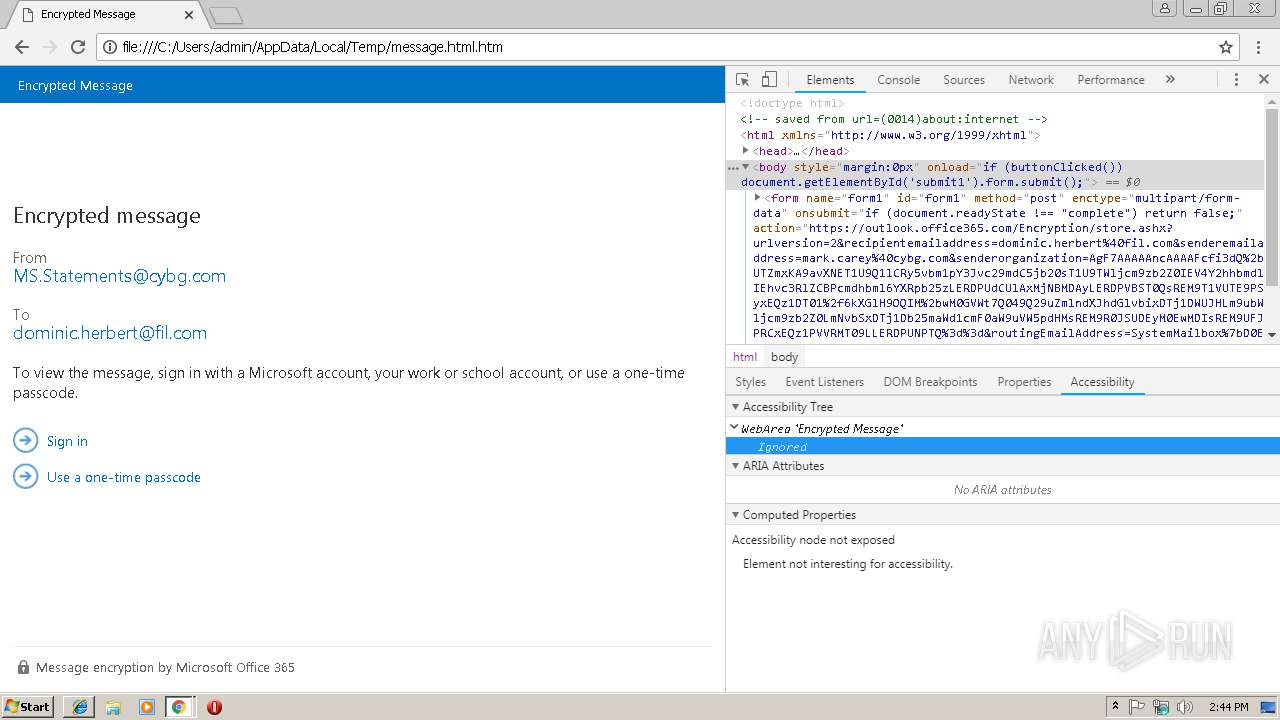
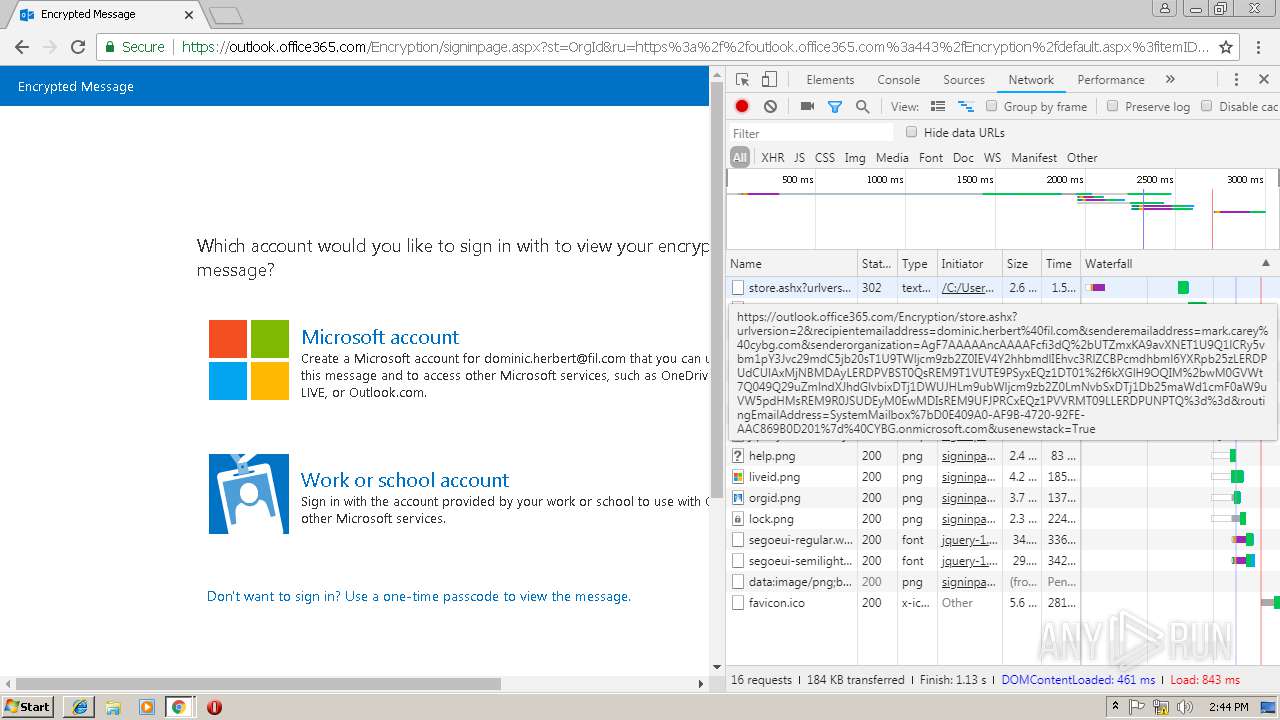
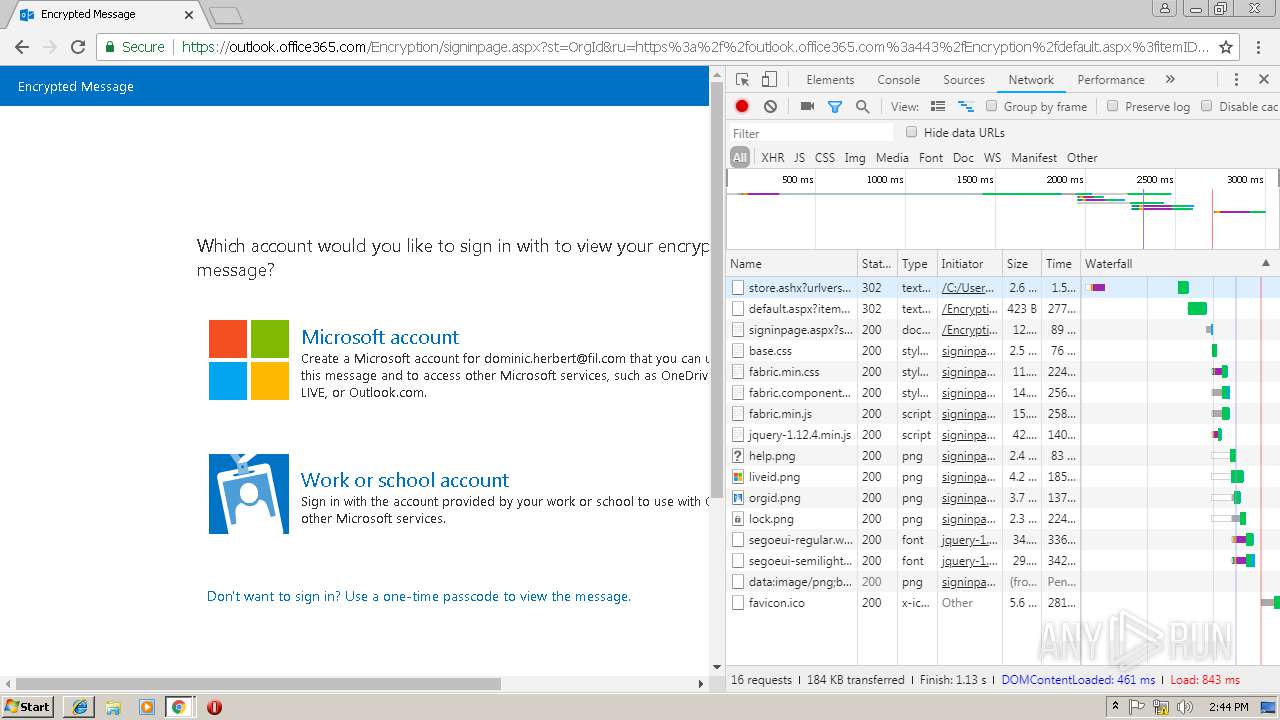
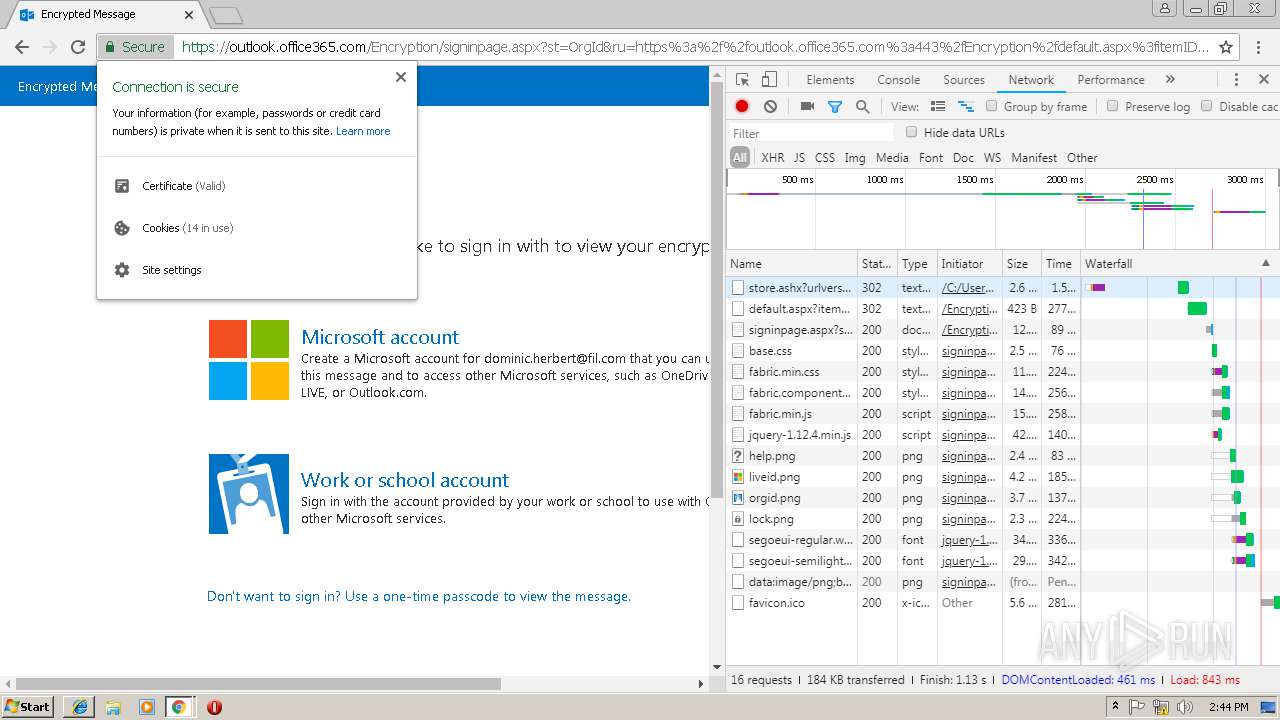
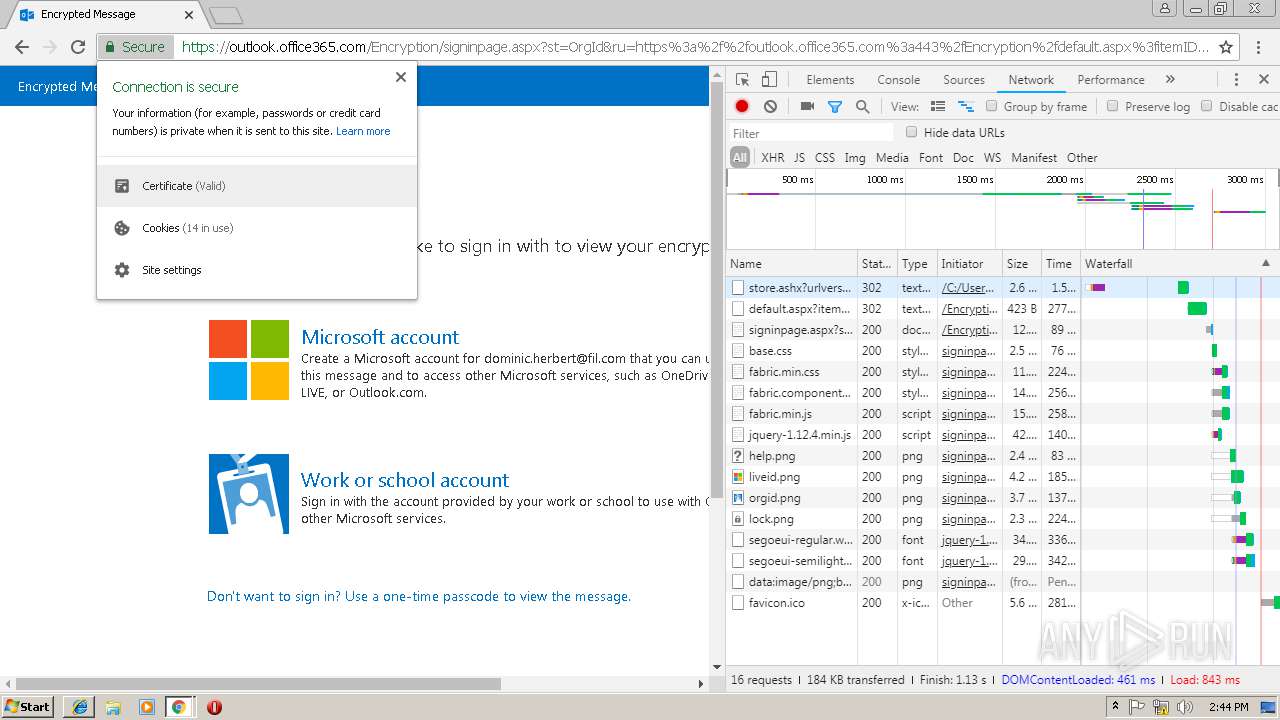
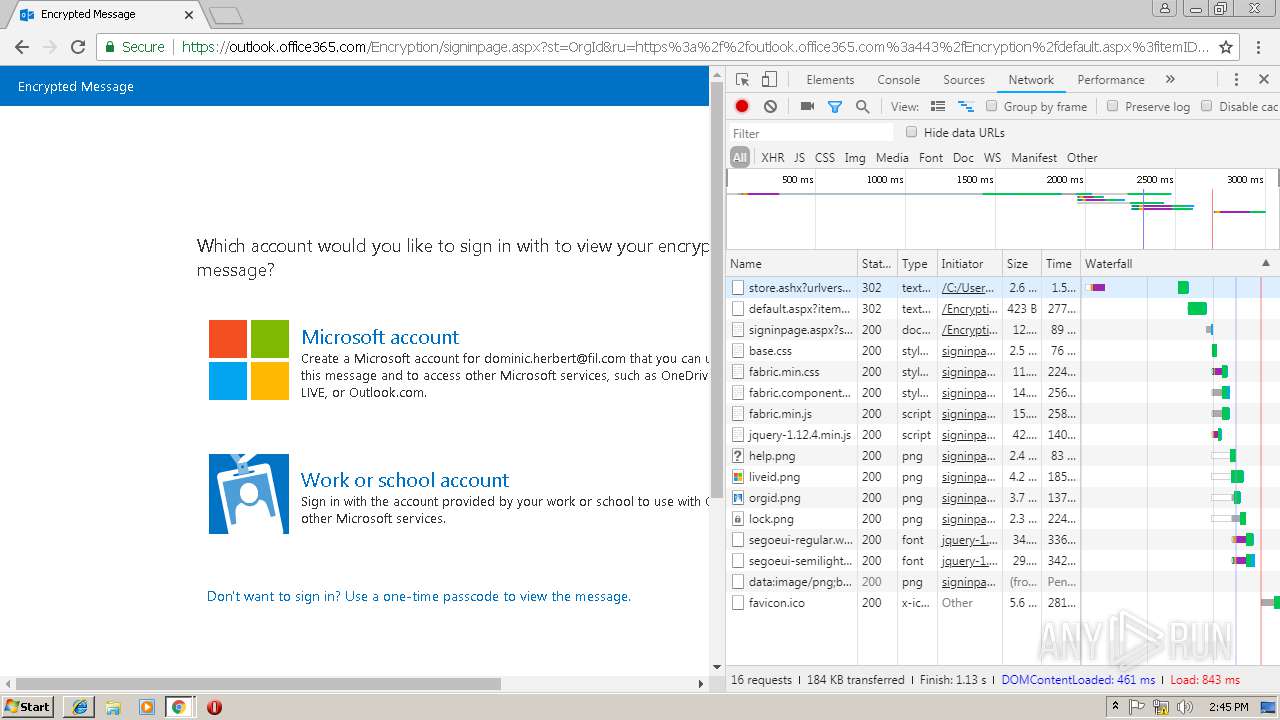
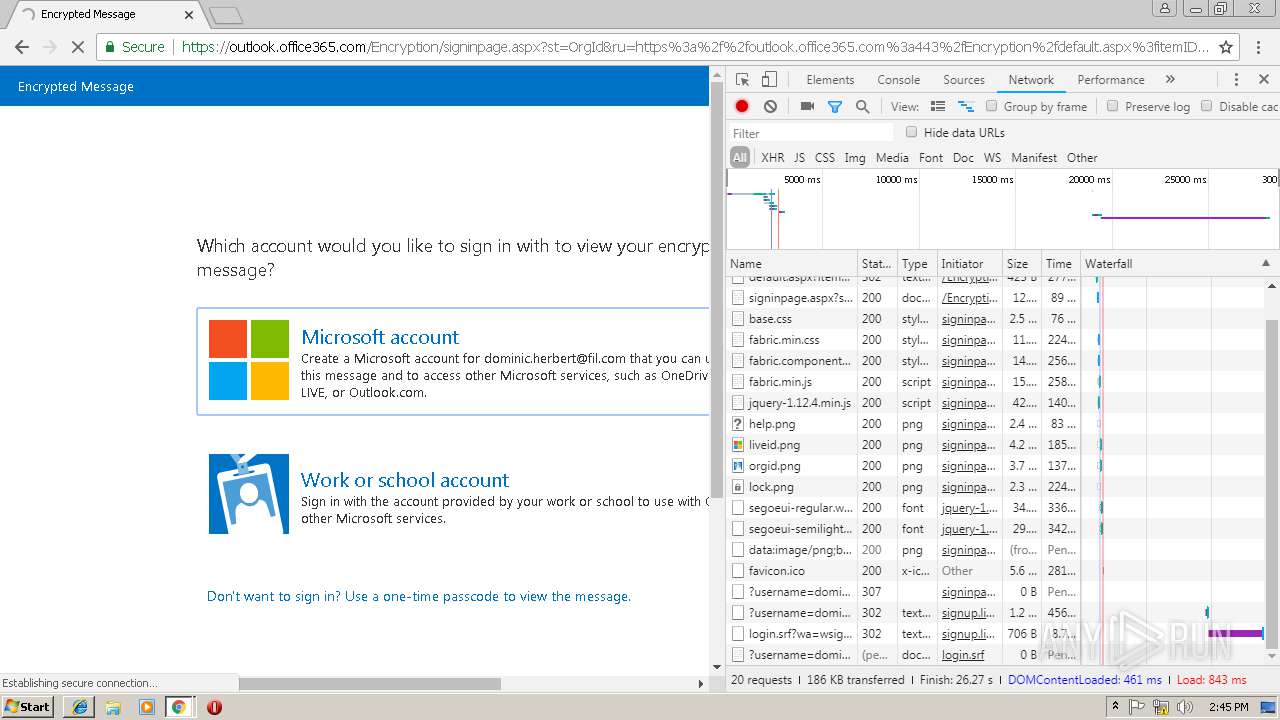
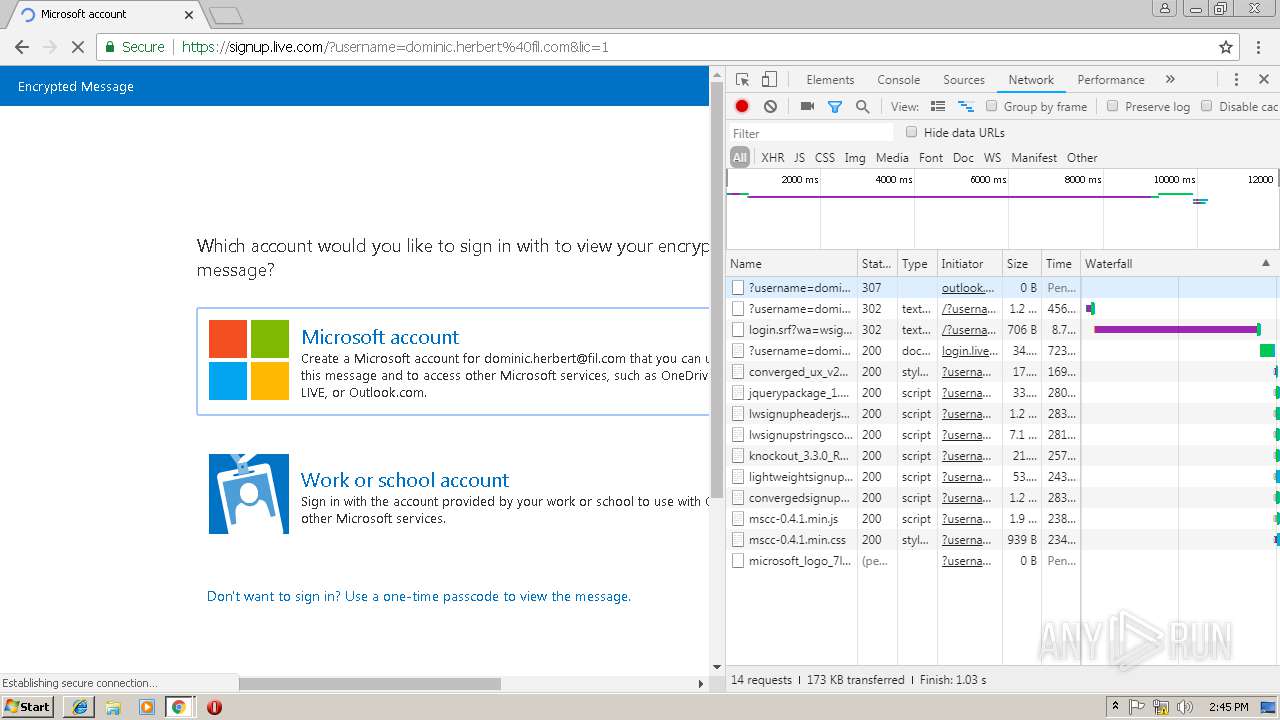
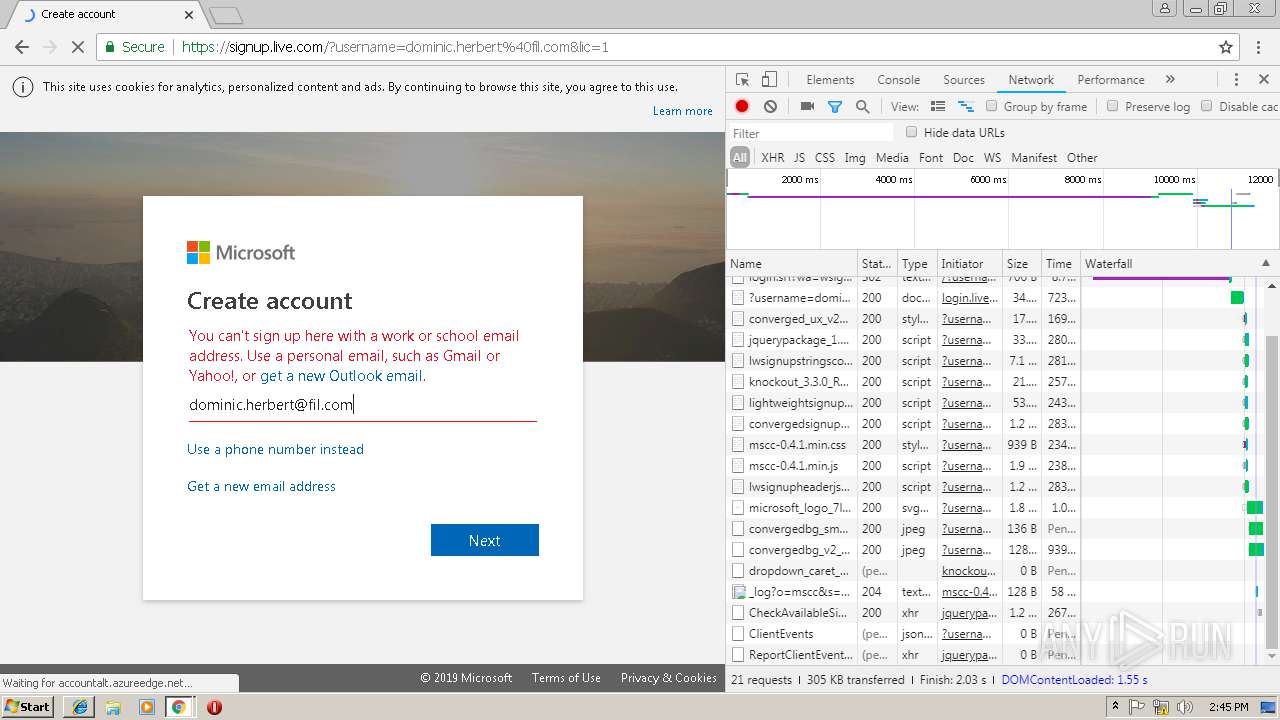
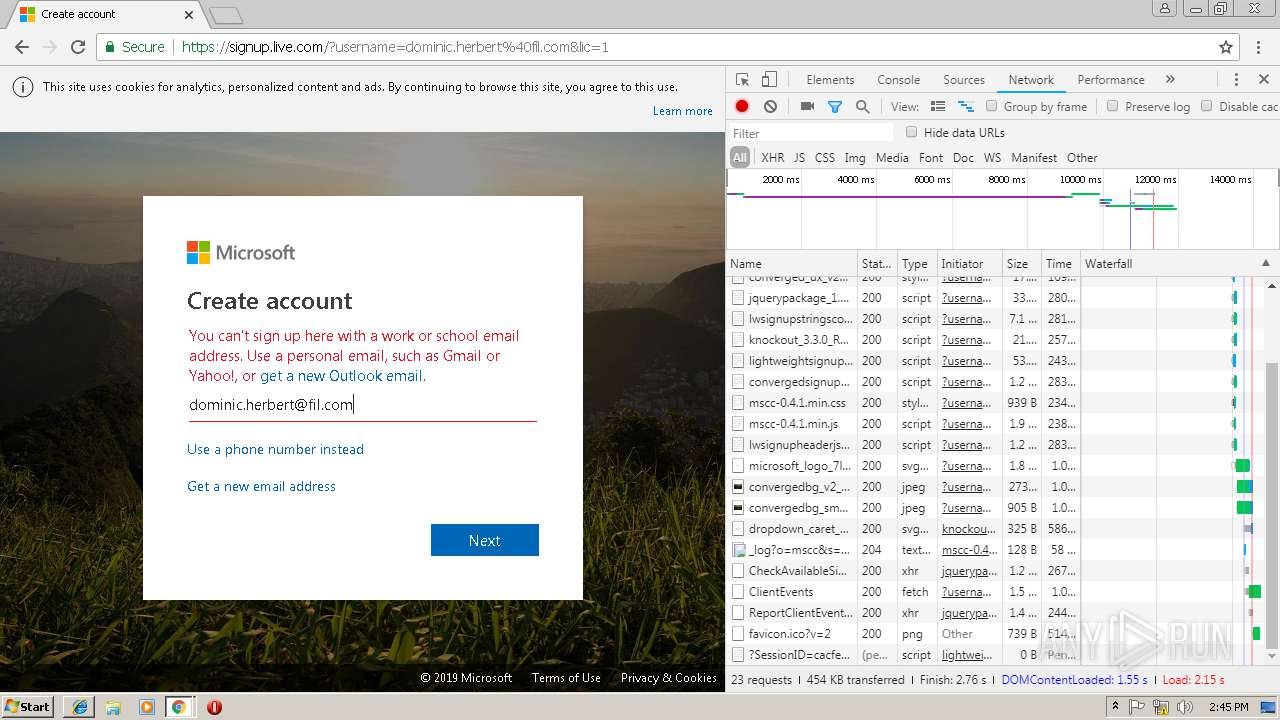
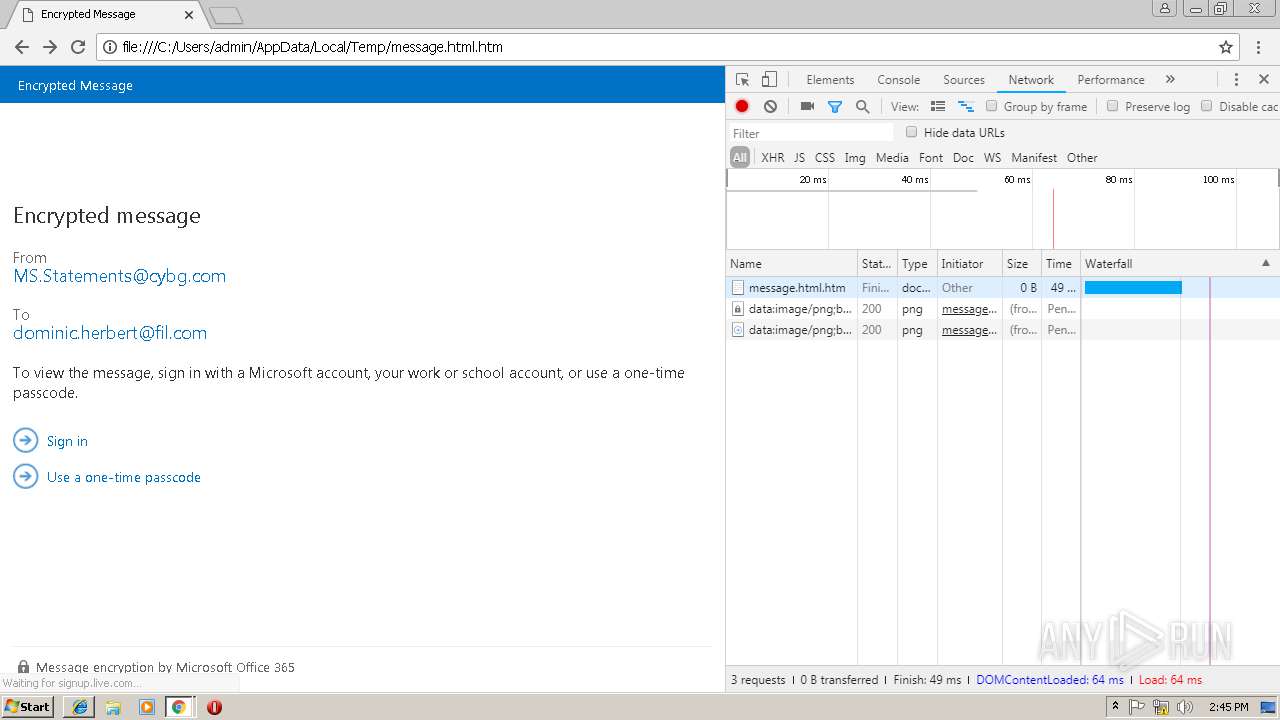
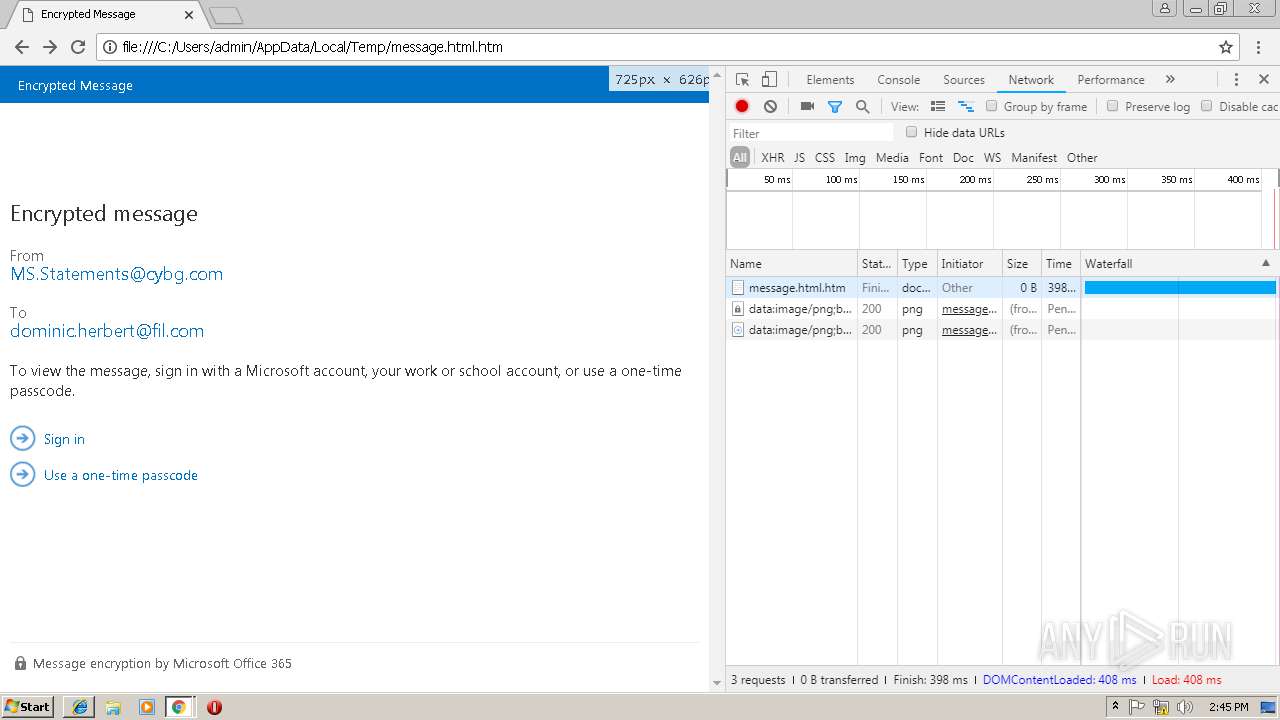
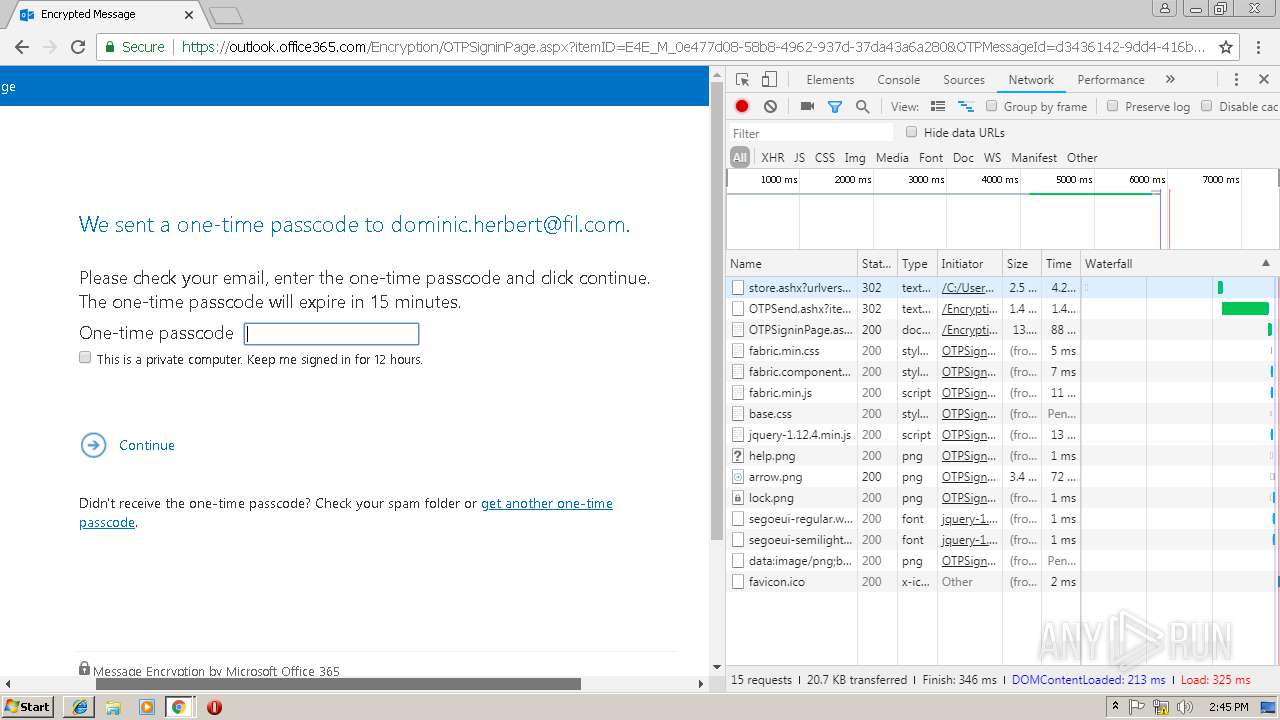
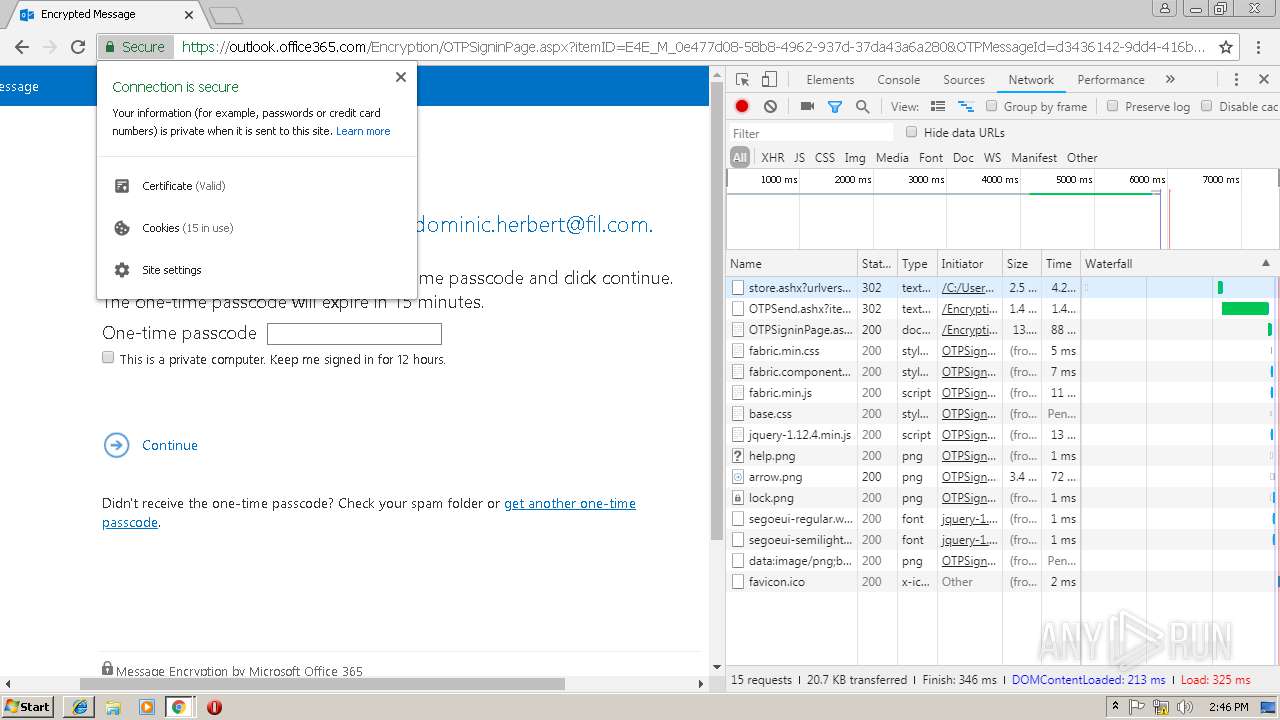
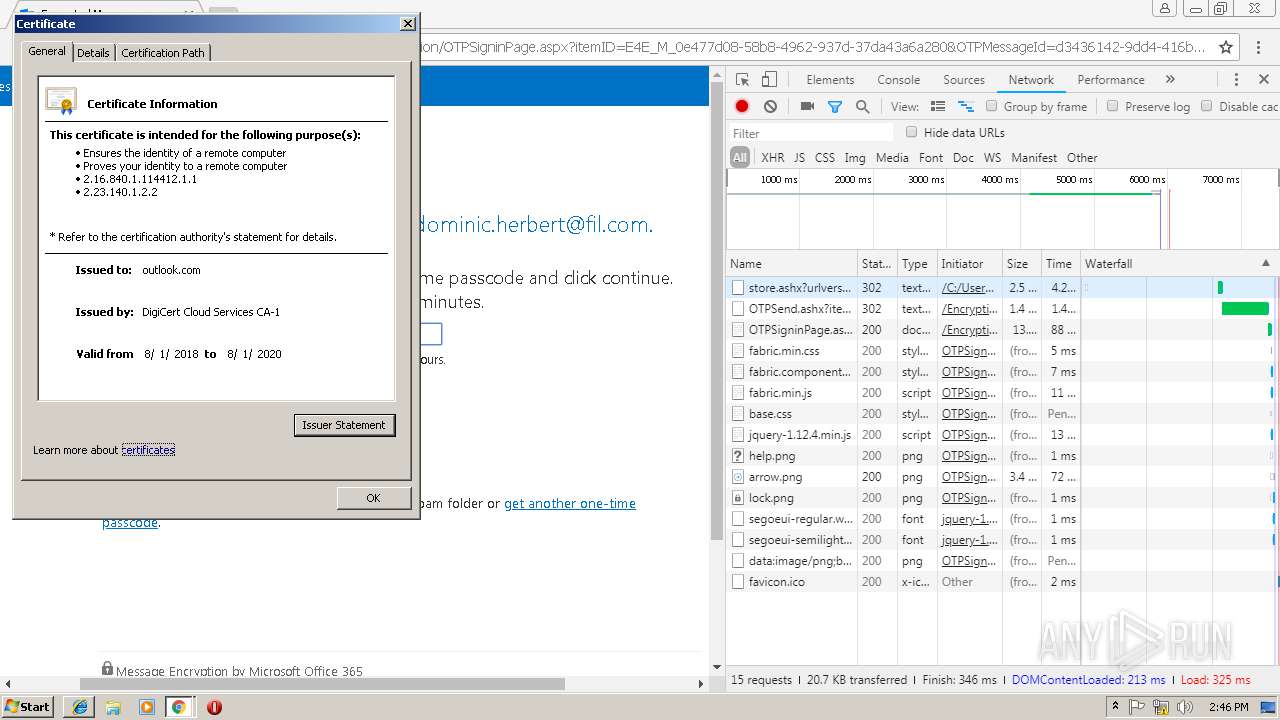
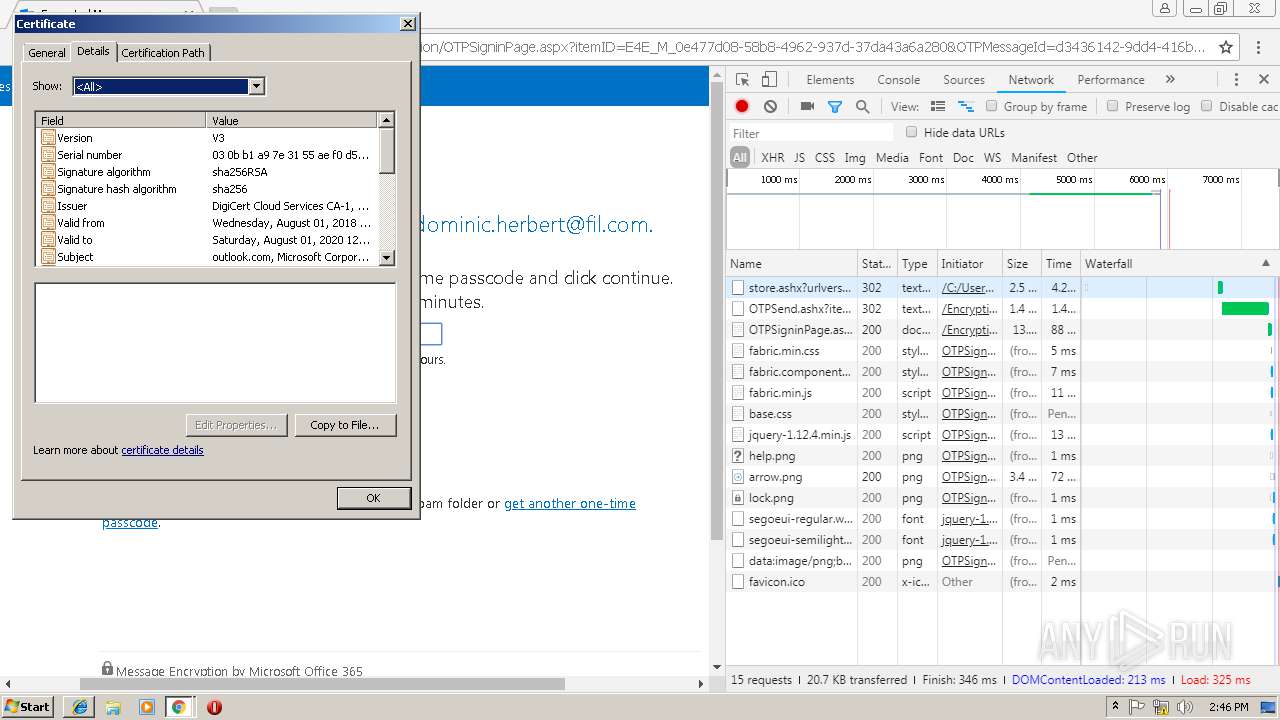
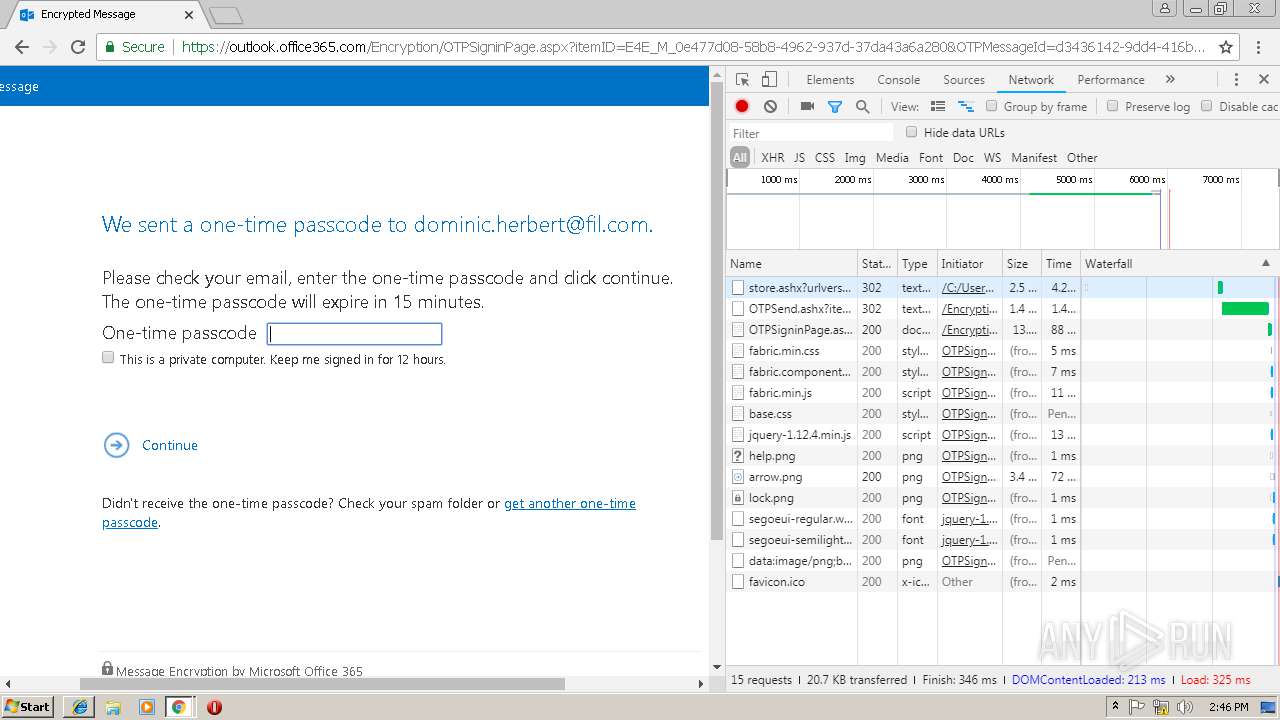
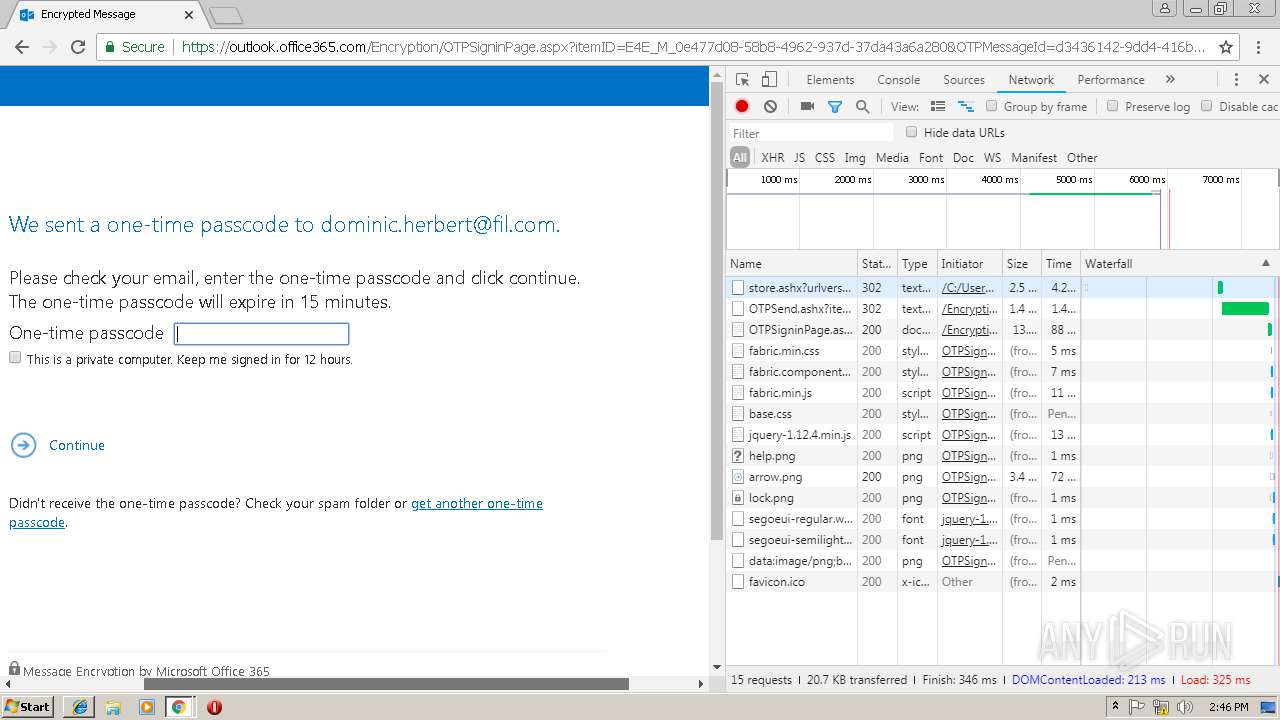
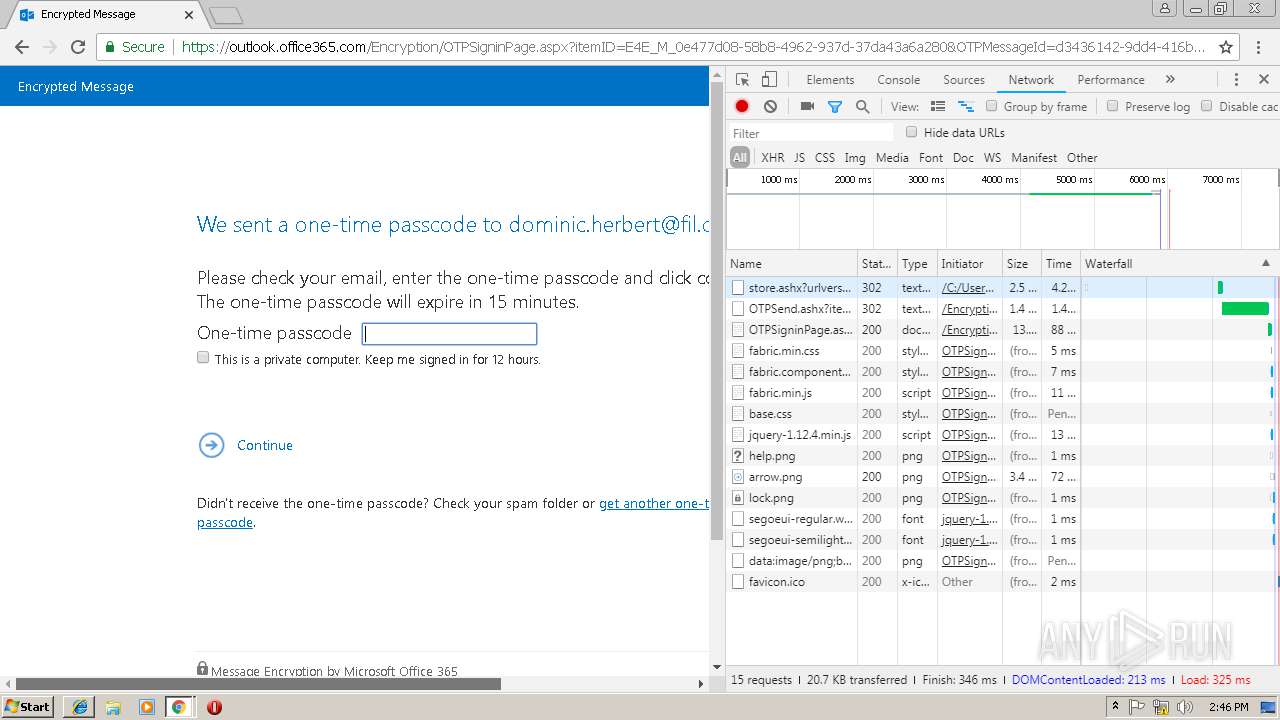
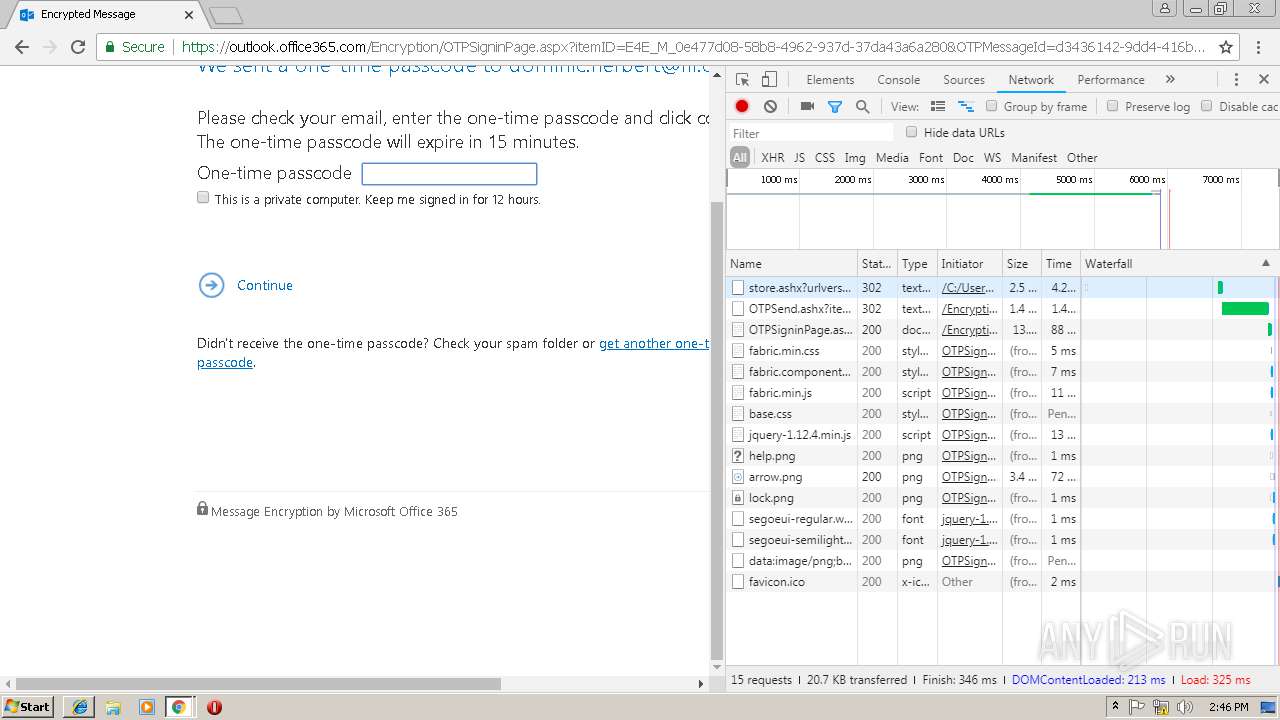
| Title: | Encrypted Message |
| restUploadUrl: | https://outlook.office365.com/Encryption/api.svc/mail/upload?urlversion=2&recipientemailaddress=dominic.herbert%40fil.com&senderemailaddress=mark.carey%40cybg.com&senderorganization=AgF7AAAAAncAAAAFcfi3dQ%2bUTZmxKA9avXNET1U9Q1lCRy5vbm1pY3Jvc29mdC5jb20sT1U9TWljcm9zb2Z0IEV4Y2hhbmdlIEhvc3RlZCBPcmdhbml6YXRpb25zLERDPUdCUlAxMjNBMDAyLERDPVBST0QsREM9T1VUTE9PSyxEQz1DT01%2f6kXGlH9OQIM%2bwM0GVWt7Q049Q29uZmlndXJhdGlvbixDTj1DWUJHLm9ubWljcm9zb2Z0LmNvbSxDTj1Db25maWd1cmF0aW9uVW5pdHMsREM9R0JSUDEyM0EwMDIsREM9UFJPRCxEQz1PVVRMT09LLERDPUNPTQ%3d%3d&routingEmailAddress=SystemMailbox%7bD0E409A0-AF9B-4720-92FE-AAC869B0D201%7d%40CYBG.onmicrosoft.com |
| signatureMeta: | VNG8EbdTvnTakBaEEaeyTYgcEbw/ngWRCnPA8Kr/nBerqv5lM6YRNvbWHBwJQCXqC50+4CuMOyhWPyfD0ntrUPWgEOm/wmudNeOqLP8urwgQZQRJXymioYgAewB8+brIfGoDdkURycWRN/TbzBoU7Oj98DcTfuPLHvPDL8+rj7iOp/o+CUAEU+Uxh7hItOACRYhxTdqTjZ4OqV7o3br97xeo80WgxlgpaW/BQw2XhLGMOo5NdCDqW1n8LCZFzLfCXrf6TYqjNn06rPl2QvSJsthM+g7l6n1fuILwnr8bqSb/ch6T+6RNkxKABiP78DCteRPUqPyn5AQj/ZKi4AVt2g== |
| viewport: | user-scalable=0, width=device-width, initial-scale=1.0, maximum-scale=1.0 |
Total processes
52
Monitored processes
22
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
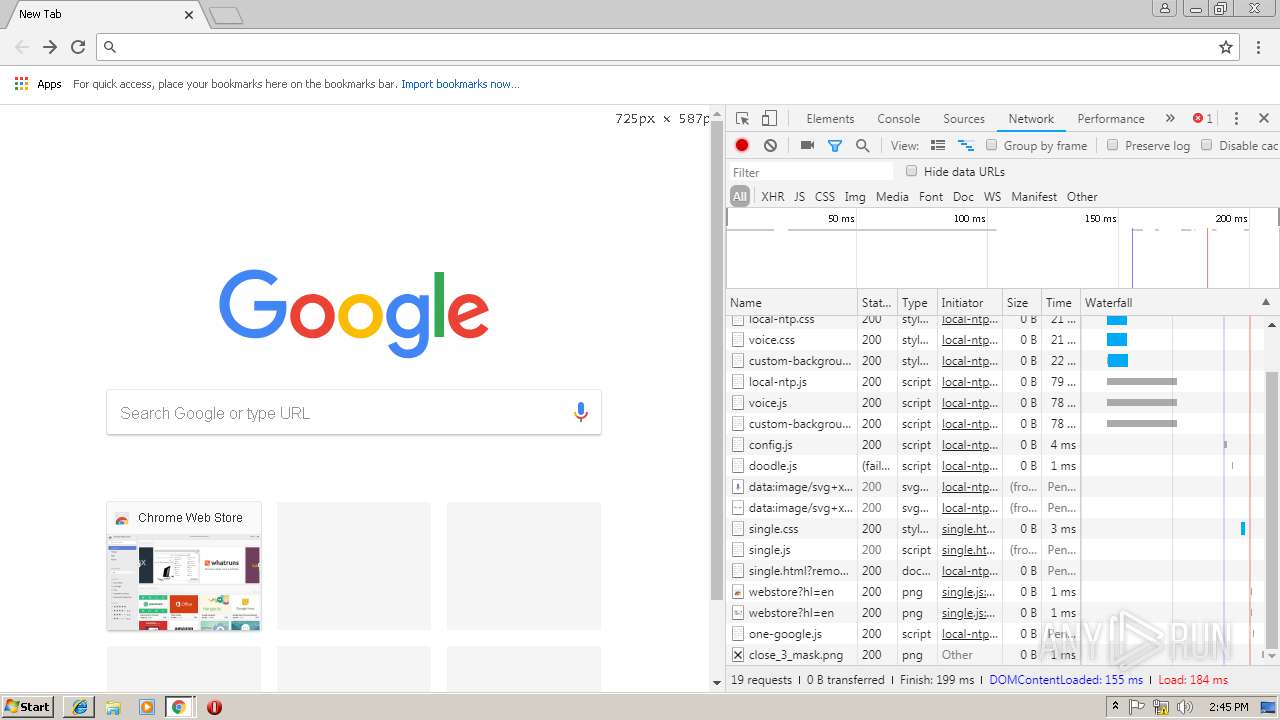
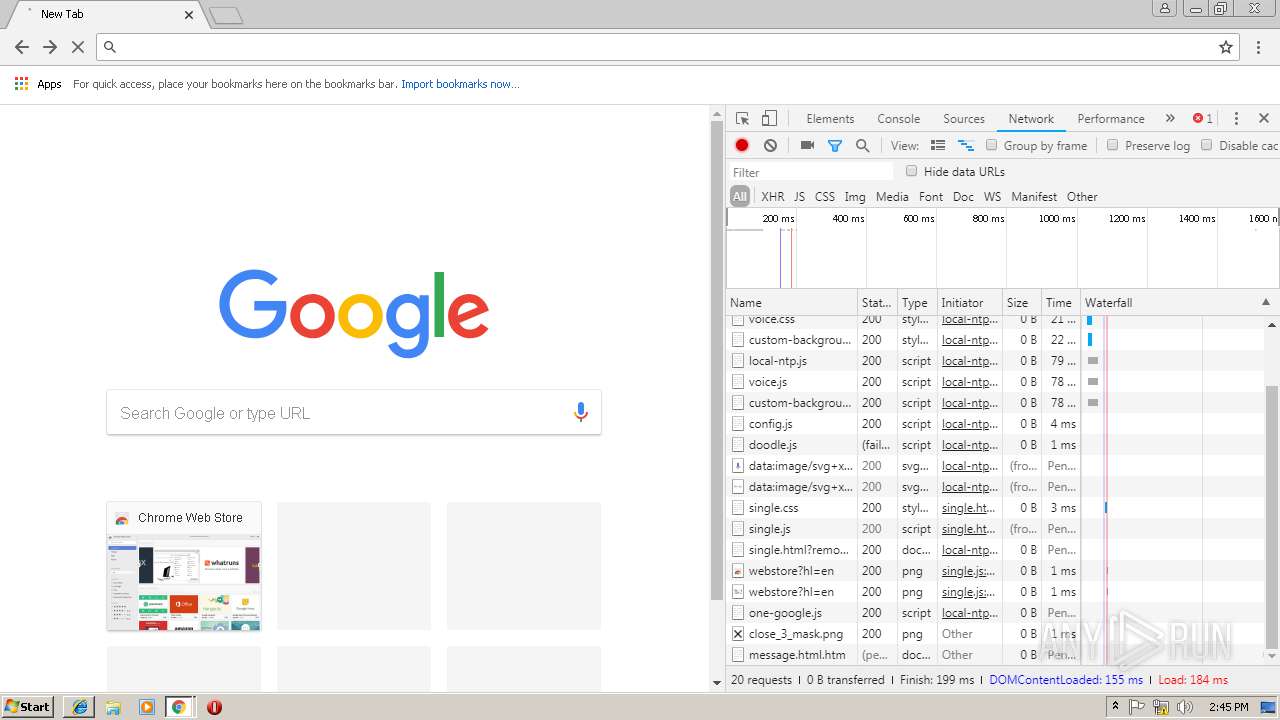
| 792 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1344 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,8270002235950365715,1702451880469036609,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=AF0F1B80F666F1B3B1209E0BD890C3C2 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=AF0F1B80F666F1B3B1209E0BD890C3C2 --renderer-client-id=16 --mojo-platform-channel-handle=4060 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2144 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,8270002235950365715,1702451880469036609,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=10D1240486AE564D6B6BBB3455CA6772 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10D1240486AE564D6B6BBB3455CA6772 --renderer-client-id=9 --mojo-platform-channel-handle=4016 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2308 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,8270002235950365715,1702451880469036609,131072 --enable-features=PasswordImport --service-pipe-token=FA6ED293981700BABC0A7C67C60EA00F --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=FA6ED293981700BABC0A7C67C60EA00F --renderer-client-id=3 --mojo-platform-channel-handle=2076 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2340 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=984,8270002235950365715,1702451880469036609,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=44B96B91684CC77BF36ACB0D8E009D4E --mojo-platform-channel-handle=3788 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2468 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2168 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2528 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,8270002235950365715,1702451880469036609,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=23BB33B2579914B2355FD3935BF77CA5 --mojo-platform-channel-handle=3124 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2708 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=68.0.3440.106 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x6f4000b0,0x6f4000c0,0x6f4000cc | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2888 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2984 CREDAT:6405 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2984 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\AppData\Local\Temp\message.html.htm | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 151
Read events
1 002
Write events
142
Delete events
7
Modification events
| (PID) Process: | (2984) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2984) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2984) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2984) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2984) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2984) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000069000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2984) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {270CBA93-14E6-11E9-AA93-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (2984) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2984) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 3 | |||
| (PID) Process: | (2984) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E307010004000A000E002B003700E101 | |||
Executable files
0
Suspicious files
75
Text files
117
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2984 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2984 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 792 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\dd306c7f-c90f-4c0b-b512-ca25dc2799b7.tmp | — | |
MD5:— | SHA256:— | |||
| 792 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 792 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3632 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\Low\History.IE5\MSHist012019011020190111\index.dat | dat | |
MD5:— | SHA256:— | |||
| 792 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old~RF212df5.TMP | text | |
MD5:— | SHA256:— | |||
| 792 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
| 792 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\a17b9bb8-4475-472e-89e1-941f0d8eb370.tmp | — | |
MD5:— | SHA256:— | |||
| 792 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Thumbnails\LOG.old~RF212e72.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
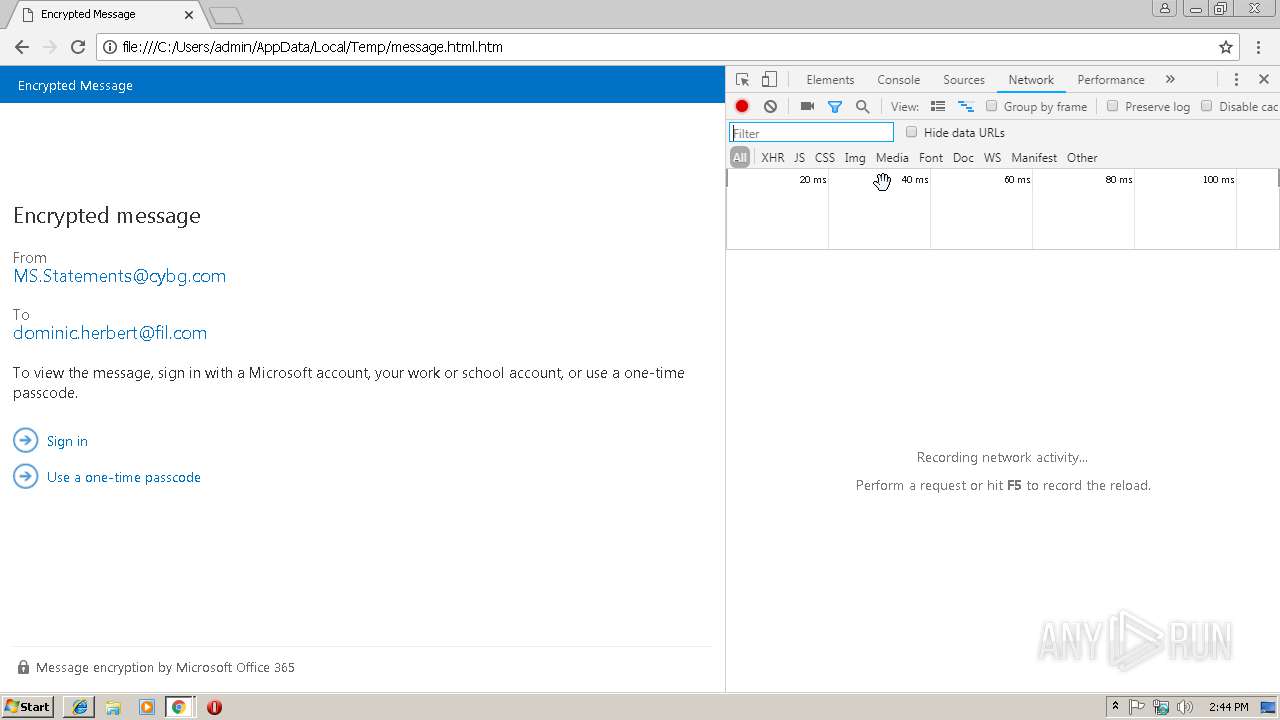
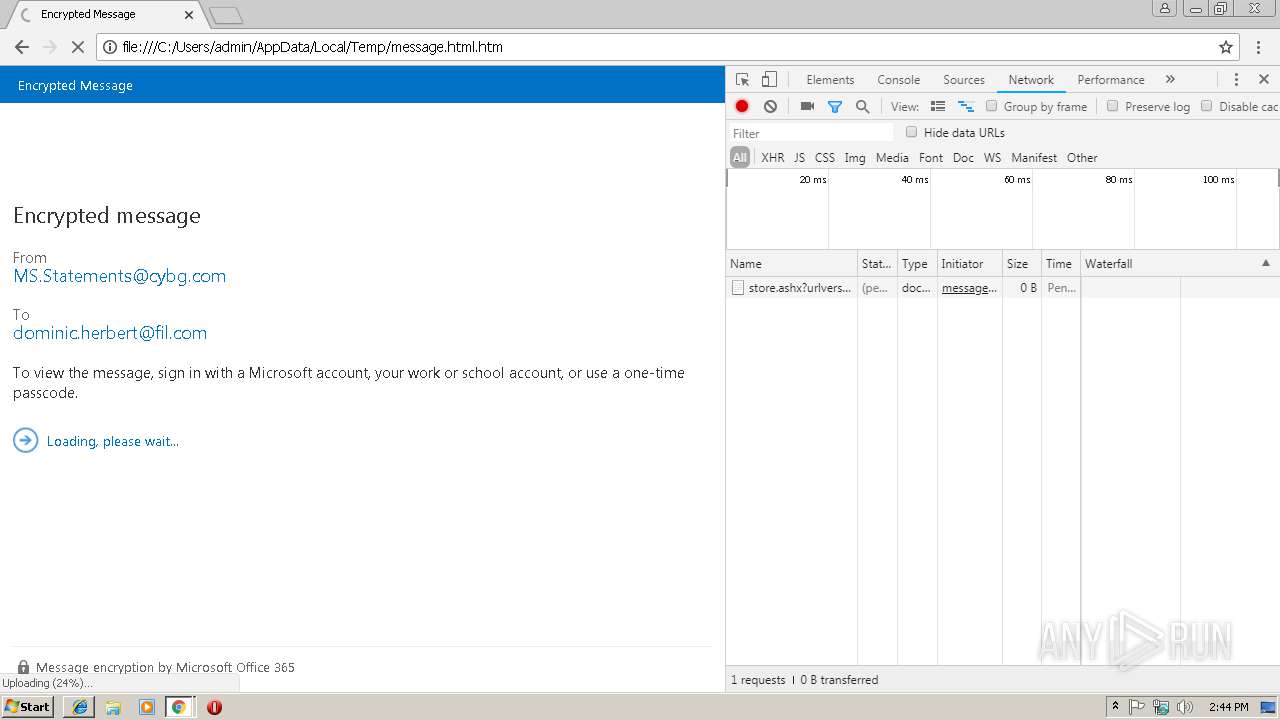
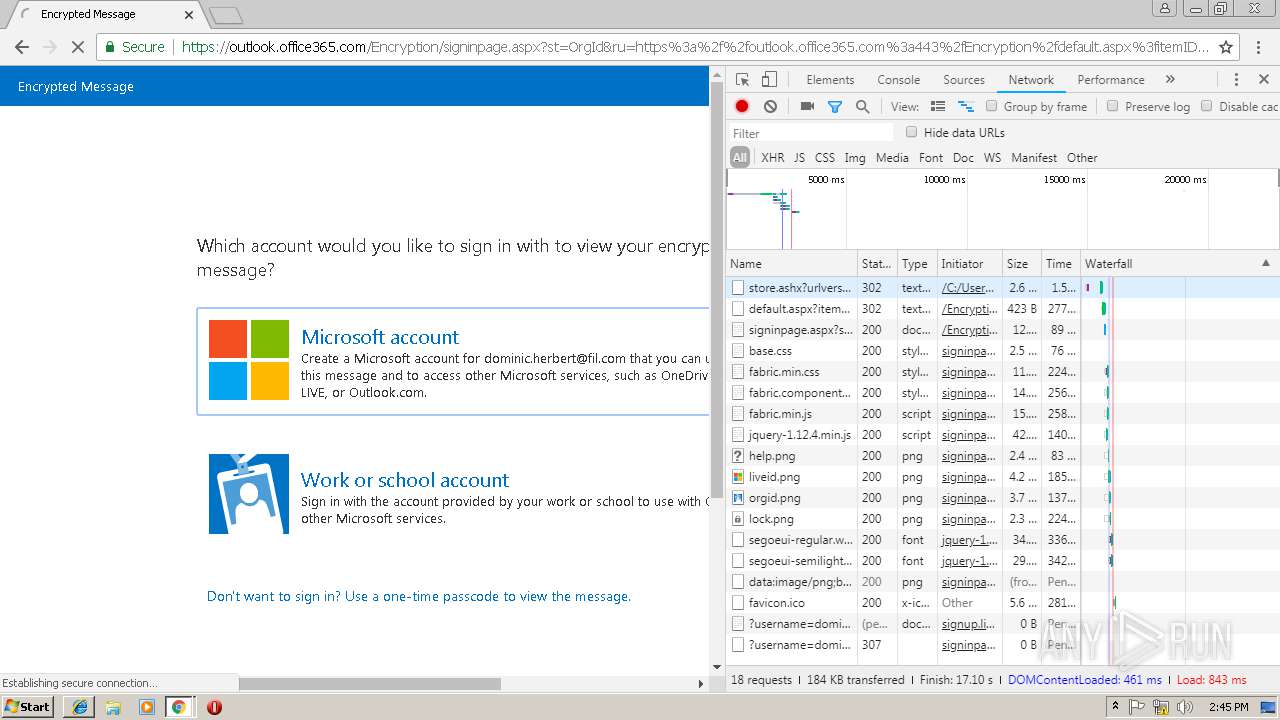
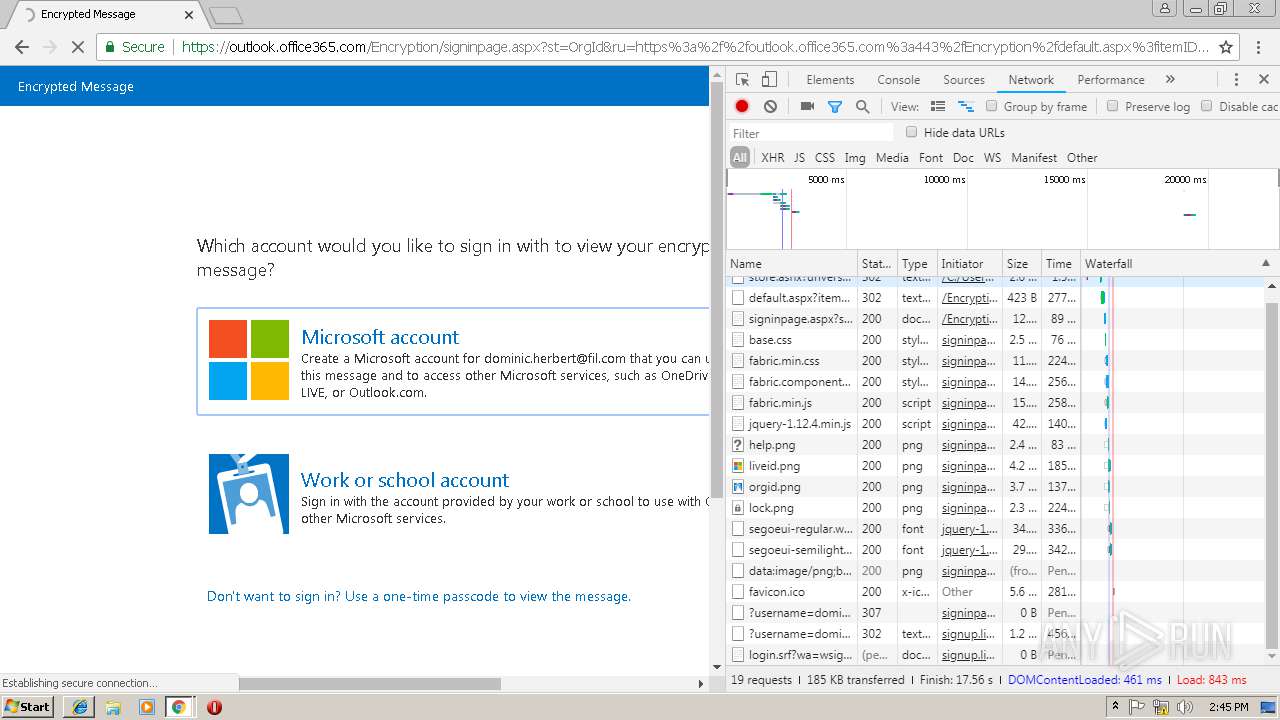
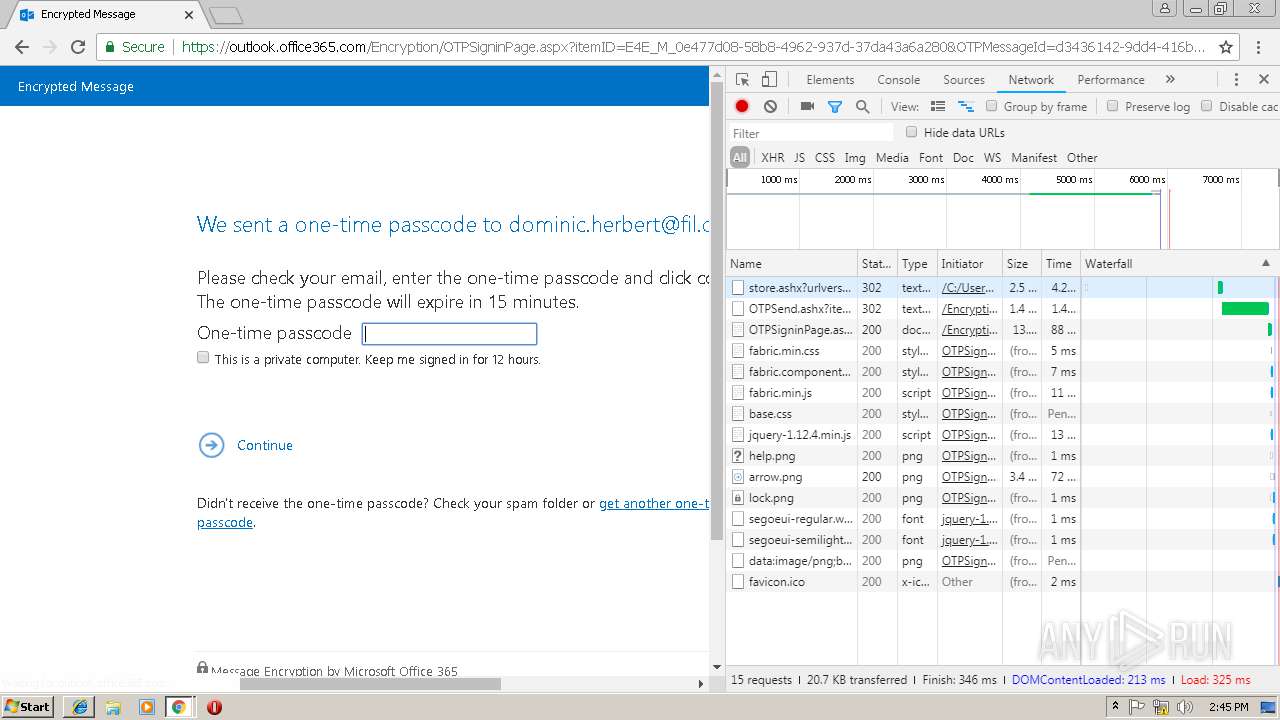
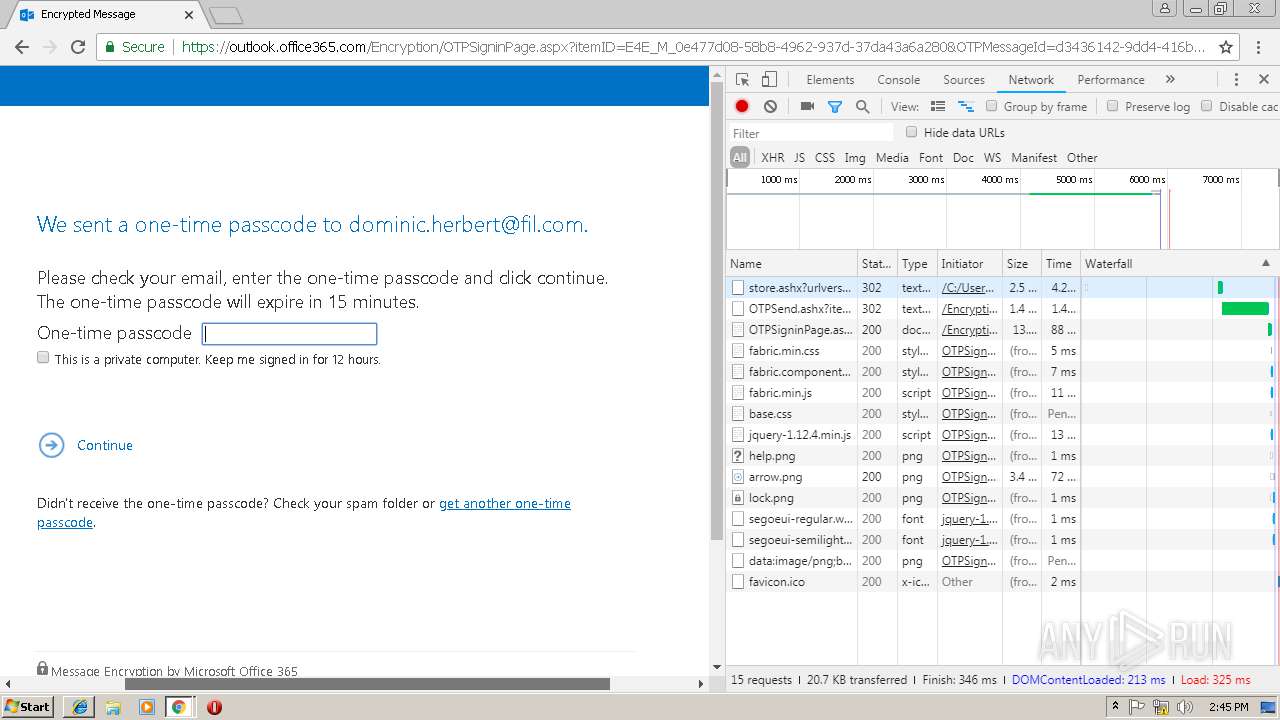
HTTP(S) requests
1
TCP/UDP connections
50
DNS requests
30
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2984 | iexplore.exe | GET | 200 | 13.107.21.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
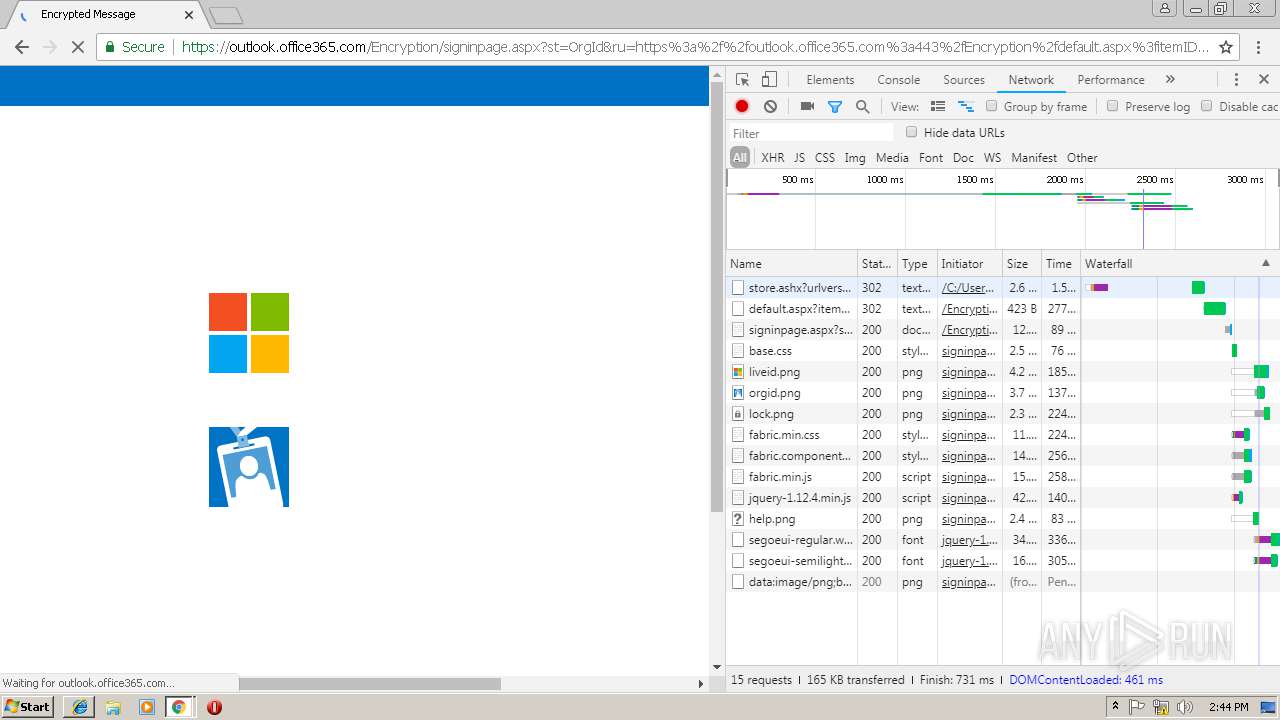
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
792 | chrome.exe | 216.58.206.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2984 | iexplore.exe | 13.107.21.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
792 | chrome.exe | 216.58.208.35:443 | www.gstatic.com | Google Inc. | US | whitelisted |
792 | chrome.exe | 216.58.207.42:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
792 | chrome.exe | 172.217.21.238:443 | apis.google.com | Google Inc. | US | whitelisted |
792 | chrome.exe | 172.217.22.100:443 | www.google.com | Google Inc. | US | whitelisted |
792 | chrome.exe | 172.217.18.99:443 | www.google.no | Google Inc. | US | whitelisted |
792 | chrome.exe | 172.217.22.106:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
792 | chrome.exe | 172.217.22.20:443 | chrome-devtools-frontend.appspot.com | Google Inc. | US | whitelisted |
792 | chrome.exe | 216.58.210.14:443 | ogs.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
www.google.de |
| whitelisted |
www.gstatic.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
apis.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
www.google.com |
| malicious |
www.google.no |
| whitelisted |