| File name: | String-Buddy.ps1 |
| Full analysis: | https://app.any.run/tasks/c7ea8c63-0679-433e-a0c7-6f854b292989 |
| Verdict: | Malicious activity |
| Analysis date: | December 18, 2018, 11:11:56 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | UTF-8 Unicode (with BOM) text, with CRLF line terminators |
| MD5: | 9ED25030F5B673BD9F2380647BE0EA92 |
| SHA1: | 3E071033F58693E8741A9051F5BBDE3EE4EB2CC5 |
| SHA256: | B50D6465B90EAD5365C6FD13B4B28046830B33CCE6D1F35FD7B31014EEFBA920 |
| SSDEEP: | 96:ik8OHOl09jWVvW2bseJW2buK35bK3kw/+Xvwuk:s6EW2bdW2bF2/+Xvwuk |
MALICIOUS
No malicious indicators.SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 2988)
INFO
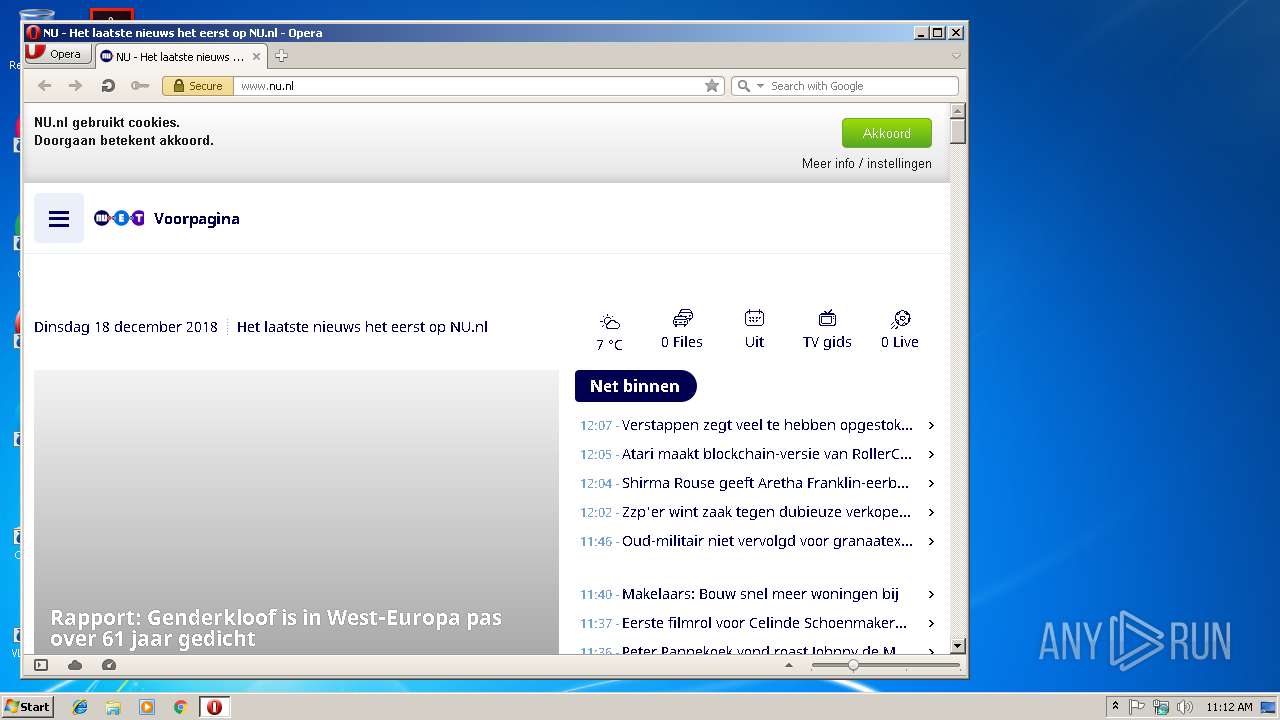
Dropped object may contain Bitcoin addresses
- opera.exe (PID: 3624)
Creates files in the user directory
- opera.exe (PID: 3624)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .txt | | | Text - UTF-8 encoded (100) |
|---|
Total processes
32
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
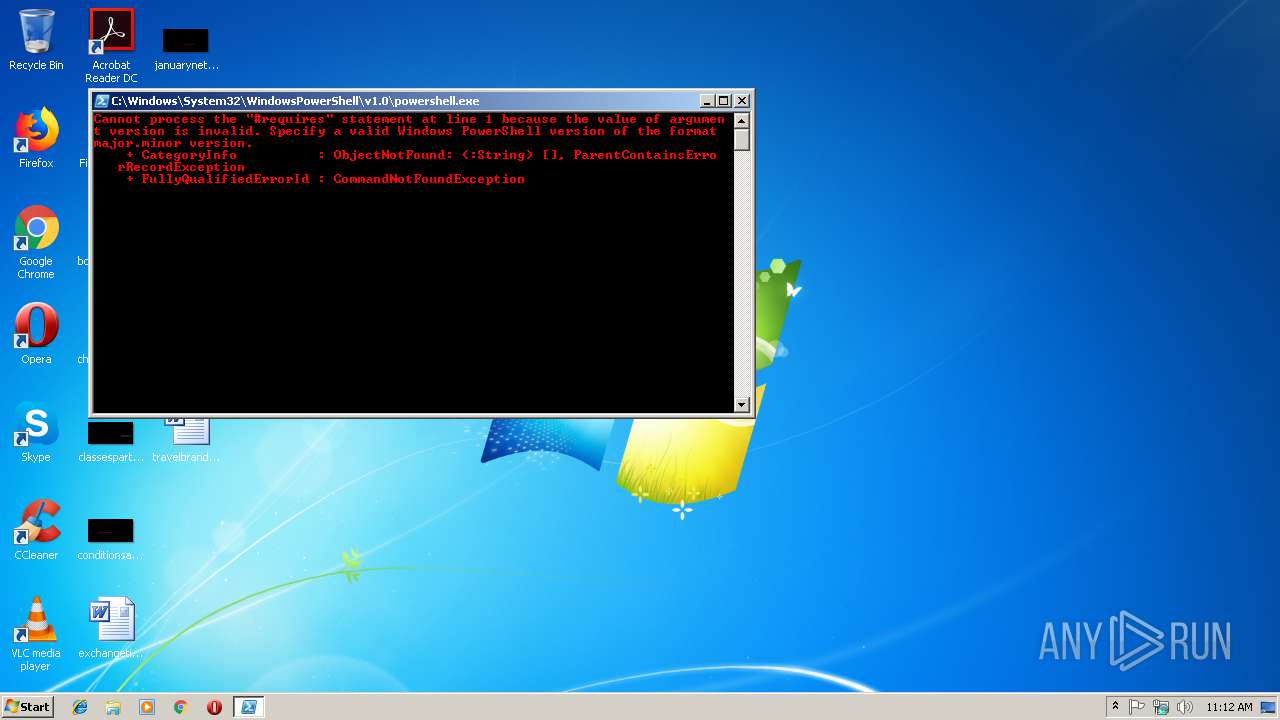
| 2988 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" "-file" "C:\Users\admin\AppData\Local\Temp\String-Buddy.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3624 | "C:\Program Files\Opera\opera.exe" | C:\Program Files\Opera\opera.exe | explorer.exe | ||||||||||||
User: admin Company: Opera Software Integrity Level: MEDIUM Description: Opera Internet Browser Exit code: 0 Version: 1748 Modules
| |||||||||||||||
Total events
494
Read events
323
Write events
171
Delete events
0
Modification events
| (PID) Process: | (2988) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2988) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2988) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3624) opera.exe | Key: | HKEY_CURRENT_USER\Software\Opera Software |
| Operation: | write | Name: | Last CommandLine v2 |
Value: C:\Program Files\Opera\opera.exe | |||
| (PID) Process: | (3624) opera.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
0
Suspicious files
84
Text files
77
Unknown types
19
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2988 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\NSJTZYTCTPOCNIT492GO.temp | — | |
MD5:— | SHA256:— | |||
| 3624 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\oprCB07.tmp | — | |
MD5:— | SHA256:— | |||
| 3624 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\oprCB56.tmp | — | |
MD5:— | SHA256:— | |||
| 3624 | opera.exe | C:\Users\admin\AppData\Local\Opera\Opera\cache\sesn\opr0000V.tmp | — | |
MD5:— | SHA256:— | |||
| 3624 | opera.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\V20OK83HL2YEWIQ3OAPF.temp | — | |
MD5:— | SHA256:— | |||
| 3624 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\sessions\oprE799.tmp | — | |
MD5:— | SHA256:— | |||
| 3624 | opera.exe | C:\Users\admin\AppData\Local\Opera\Opera\icons\https%3A%2F%2Fwww.nu.nl%2Fstatic%2Fimg%2Fatoms%2Fimages%2Ffavicon%2Ffavicon-32x32.png | — | |
MD5:— | SHA256:— | |||
| 3624 | opera.exe | C:\Users\admin\AppData\Local\Opera\Opera\icons\https%3A%2F%2Fwww.nu.nl%2Fstatic%2Fimg%2Fatoms%2Fimages%2Ffavicon%2Ffavicon.png | — | |
MD5:— | SHA256:— | |||
| 3624 | opera.exe | C:\Users\admin\AppData\Local\Opera\Opera\icons\https%3A%2F%2Fwww.nu.nl%2Fstatic%2Fimg%2Fatoms%2Fimages%2Ffavicon%2Ffavicon-96x96.png | — | |
MD5:— | SHA256:— | |||
| 3624 | opera.exe | C:\Users\admin\AppData\Local\Opera\Opera\icons\https%3A%2F%2Fwww.nu.nl%2Fstatic%2Fimg%2Fatoms%2Fimages%2Ffavicon%2Fandroid-chrome-192x192.png | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
22
TCP/UDP connections
67
DNS requests
37
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
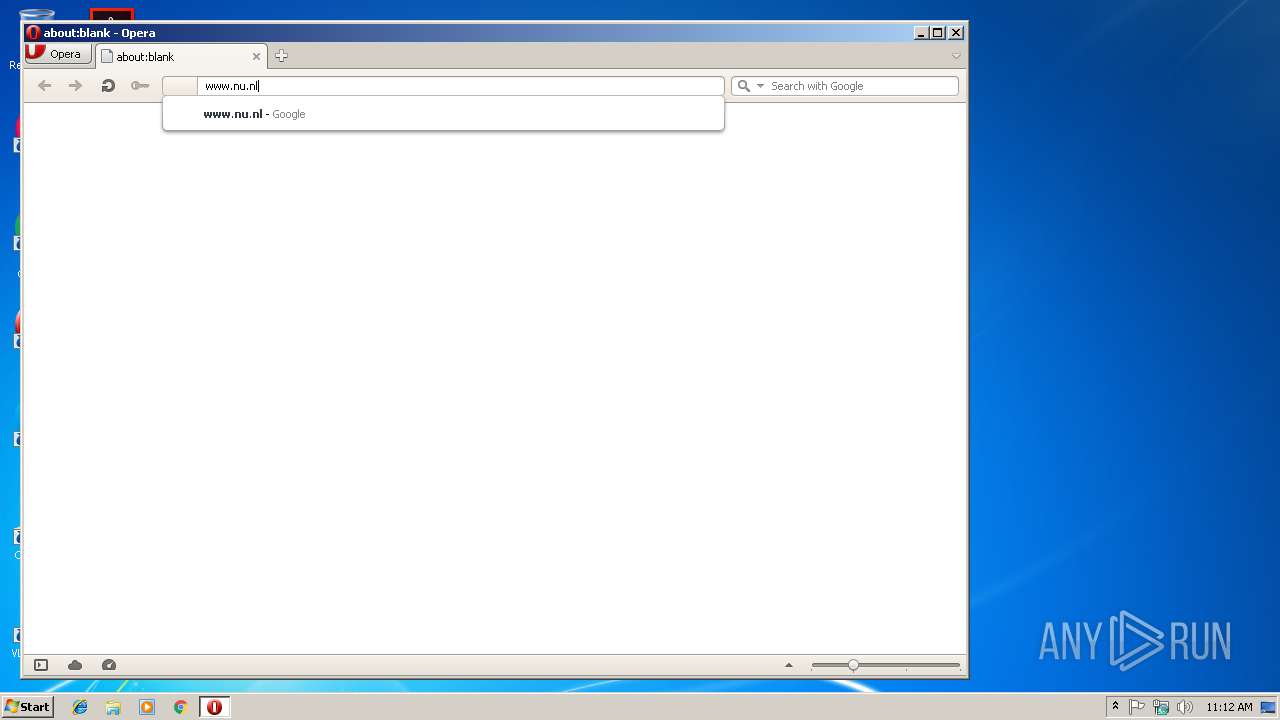
3624 | opera.exe | GET | 301 | 54.230.202.202:80 | http://www.nu.nl/ | US | — | — | whitelisted |
3624 | opera.exe | GET | 200 | 216.58.215.238:80 | http://ocsp.pki.goog/GTSGIAG3/MEkwRzBFMEMwQTAJBgUrDgMCGgUABBT27bBjYjKBmjX2jXWgnQJKEapsrQQUd8K4UJpndnaxLcKG0IOgfqZ%2BuksCCFtzSjxnxe1M | US | der | 463 b | whitelisted |
3624 | opera.exe | GET | 200 | 66.225.197.197:80 | http://crl4.digicert.com/DigiCertHighAssuranceEVRootCA.crl | US | der | 543 b | whitelisted |
3624 | opera.exe | GET | 200 | 52.85.182.139:80 | http://s.ss2.us/r.crl | US | der | 434 b | whitelisted |
3624 | opera.exe | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/DigiCertGlobalRootCA.crl | US | der | 581 b | whitelisted |
3624 | opera.exe | GET | 200 | 216.58.215.238:80 | http://crl.pki.goog/gsr2/gsr2.crl | US | der | 546 b | whitelisted |
3624 | opera.exe | GET | 200 | 93.184.220.29:80 | http://status.rapidssl.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRhhZrQET0hvbSHUJmNfBKqR%2FiT7wQUU8oXWfxrwAMhLxqu5KqoHIJW2nUCEAhxxlKPpaKNrqwHR4gF8bg%3D | US | der | 471 b | shared |
3624 | opera.exe | GET | 200 | 188.121.36.239:80 | http://ocsp.starfieldtech.com/MEowSDBGMEQwQjAJBgUrDgMCGgUABBT1ZqtwV0O1KcYi0gdzcFkHM%2BuArAQUJUWBaFAmOD07LSy%2BzWrZtj2zZmMCCQD52BZPtim28Q%3D%3D | NL | der | 1.80 Kb | whitelisted |
3624 | opera.exe | GET | 200 | 188.121.36.238:80 | http://crl.starfieldtech.com/sfroot.crl | NL | der | 434 b | whitelisted |
3624 | opera.exe | GET | 200 | 188.121.36.238:80 | http://crl.starfieldtech.com/sfroot-g2.crl | NL | der | 474 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3624 | opera.exe | 216.58.215.234:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3624 | opera.exe | 35.201.80.251:443 | media.nu.nl | Google Inc. | US | whitelisted |
3624 | opera.exe | 54.230.202.50:443 | content.jwplatform.com | Amazon.com, Inc. | US | suspicious |
3624 | opera.exe | 68.232.35.180:443 | tags.tiqcdn.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3624 | opera.exe | 216.58.215.238:80 | crl.pki.goog | Google Inc. | US | whitelisted |
3624 | opera.exe | 82.145.215.40:443 | certs.opera.com | Opera Software AS | — | whitelisted |
3624 | opera.exe | 66.225.197.197:80 | crl4.digicert.com | CacheNetworks, Inc. | US | whitelisted |
3624 | opera.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3624 | opera.exe | 54.230.202.202:80 | www.nu.nl | Amazon.com, Inc. | US | unknown |
3624 | opera.exe | 185.26.182.94:80 | sitecheck2.opera.com | Opera Software AS | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
certs.opera.com |
| whitelisted |
crl4.digicert.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.nu.nl |
| whitelisted |
sitecheck2.opera.com |
| whitelisted |
crl.rootg2.amazontrust.com |
| whitelisted |
s.ss2.us |
| whitelisted |
crl.rootca1.amazontrust.com |
| whitelisted |
consent.snmmd.nl |
| whitelisted |
fonts.googleapis.com |
| whitelisted |