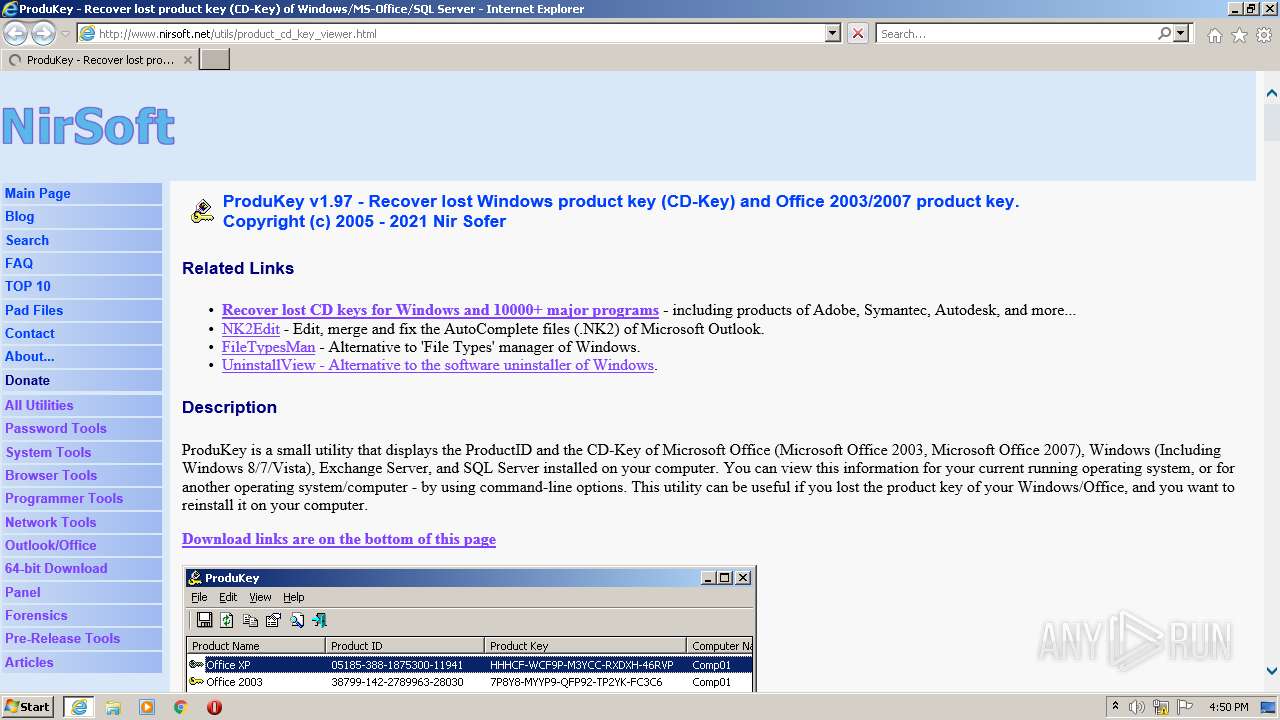
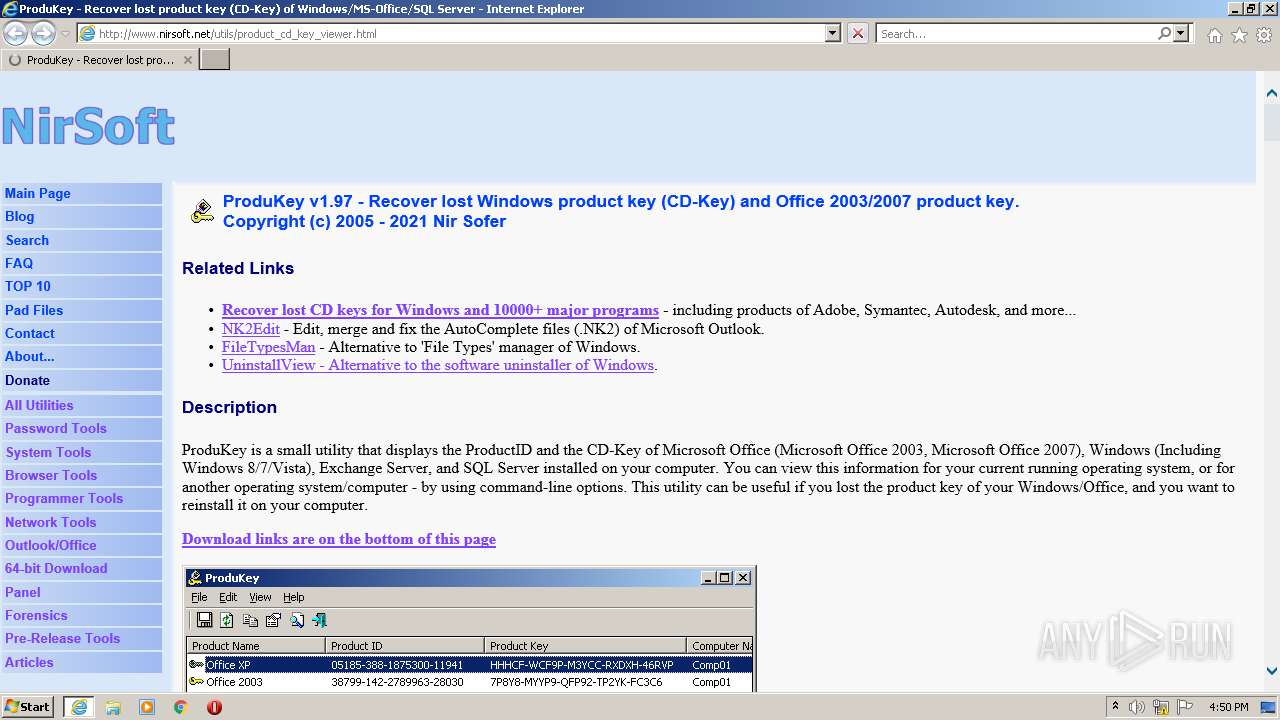
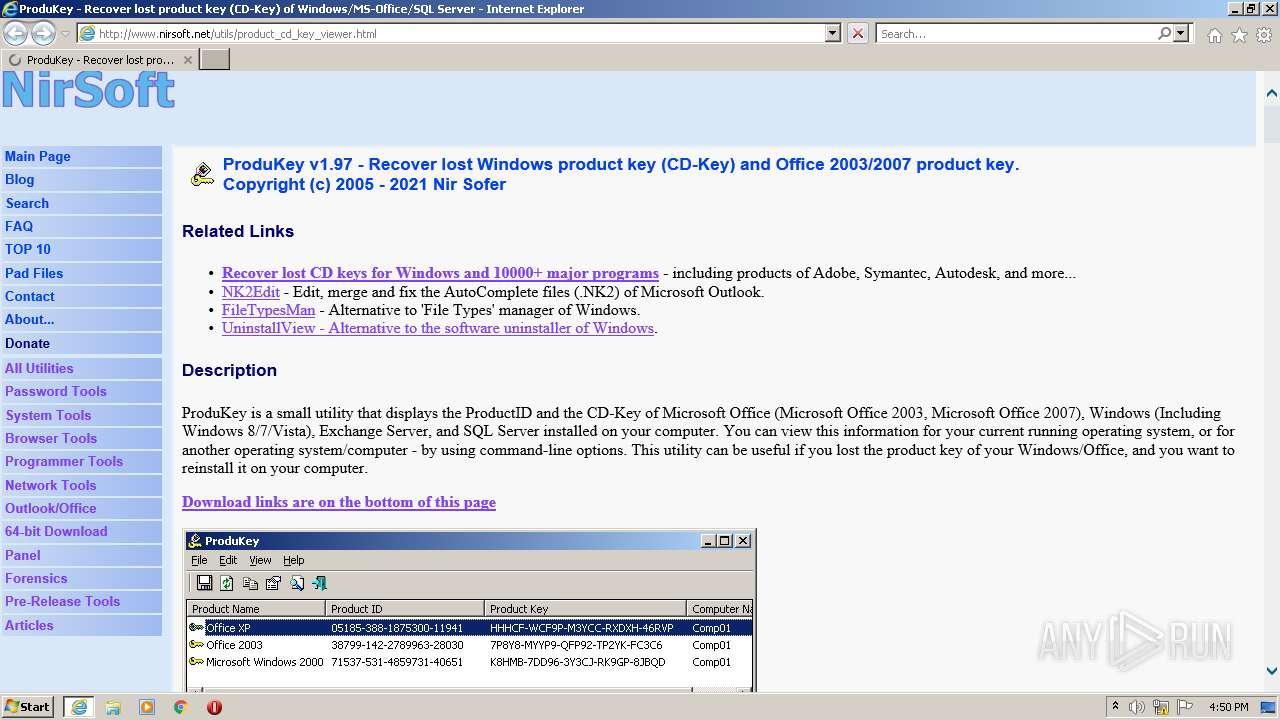
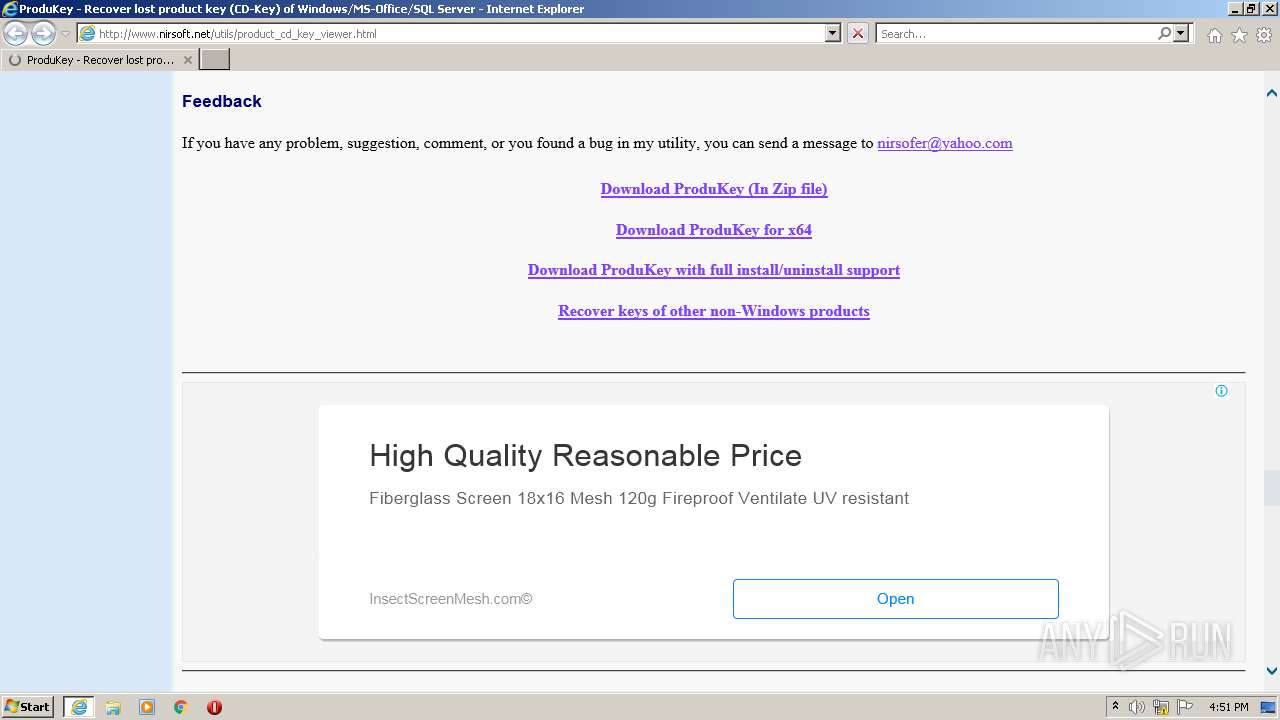
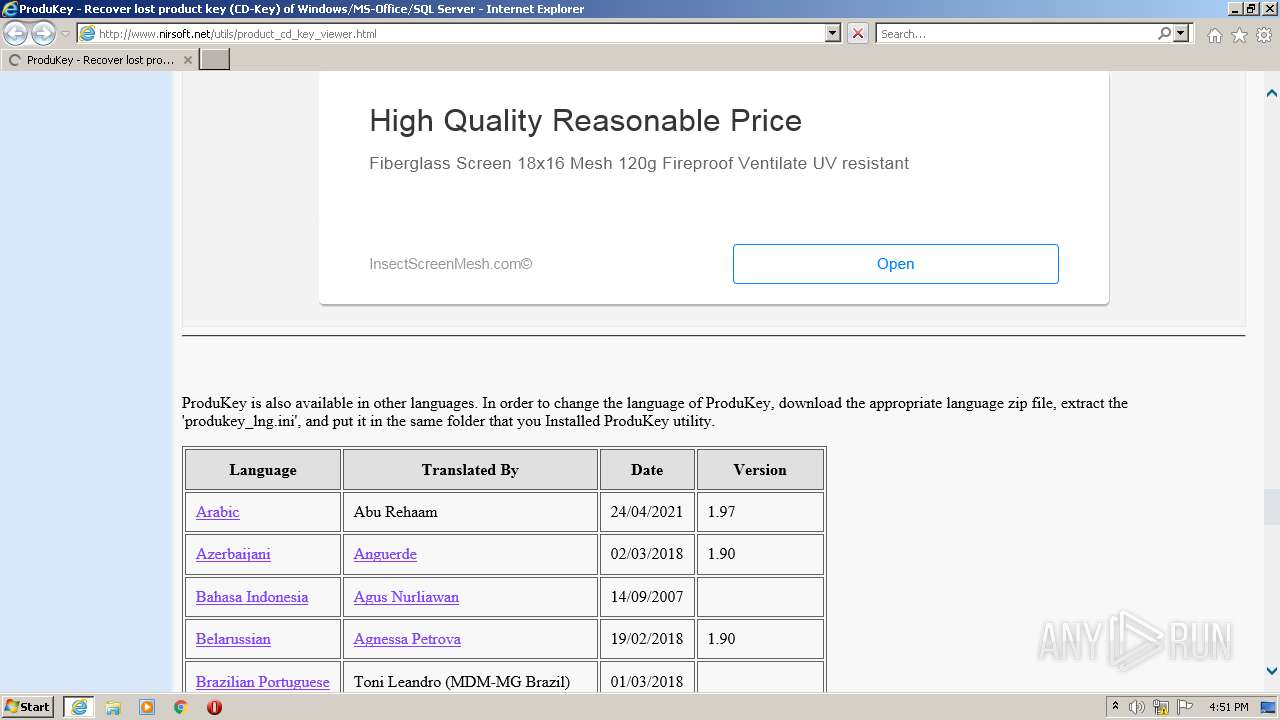
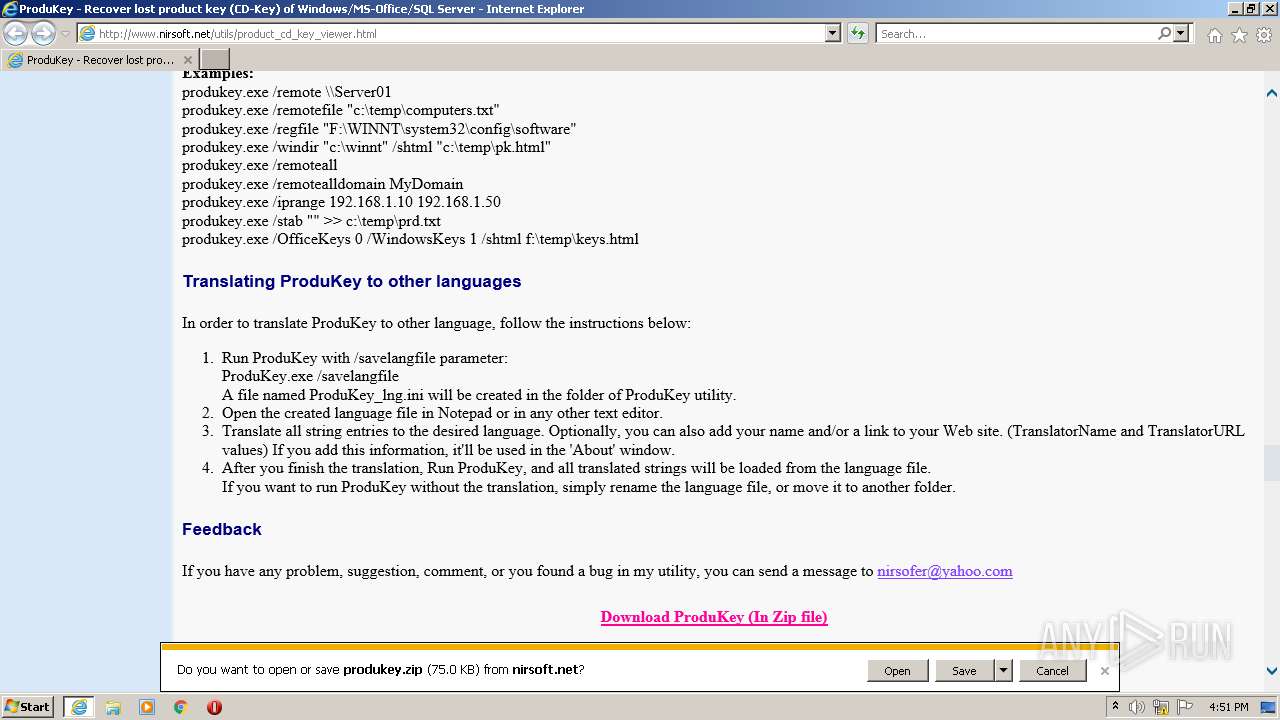
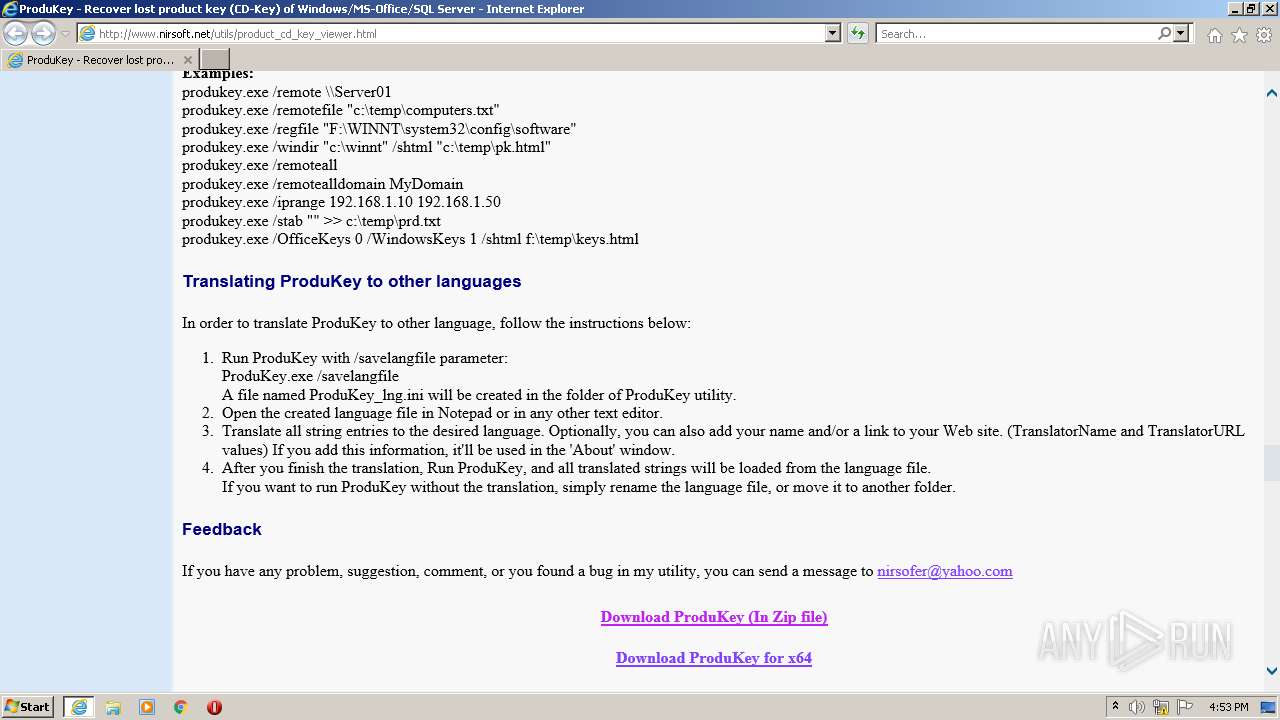
| URL: | http://www.nirsoft.net/utils/product_cd_key_viewer.html |
| Full analysis: | https://app.any.run/tasks/a8b71c20-6b2c-42ef-80a7-1fb367e1b1f4 |
| Verdict: | Malicious activity |
| Analysis date: | January 05, 2022, 16:50:41 |
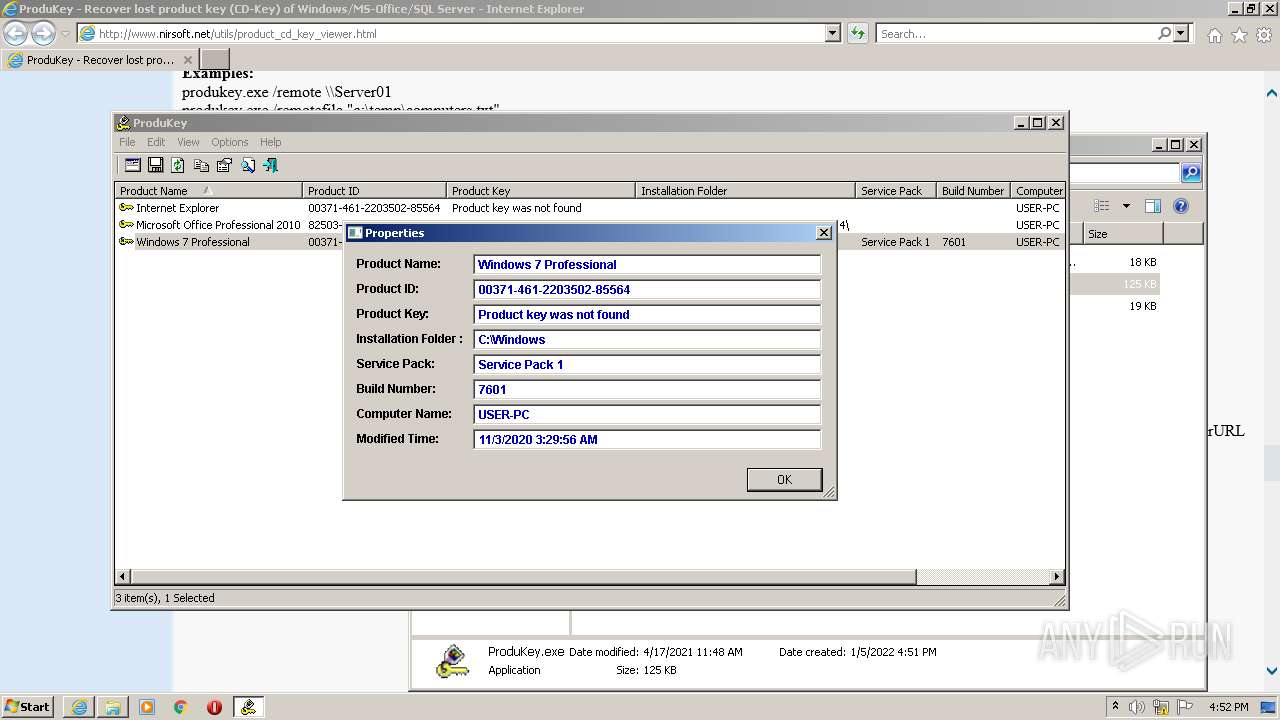
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | DA5722AC4E79F2B0261F7859E515BE38 |
| SHA1: | B0A849B69FB049BBADEC1E83D58E3C5D88CA1FD1 |
| SHA256: | B5072513B28904217FD1324EAB2CE284EB7E321A639287DBF8A76200AFF55218 |
| SSDEEP: | 3:N1KJS44BR/N9aTR6GB6vLA3guJ:Cc44BgR6GMvLA3v |
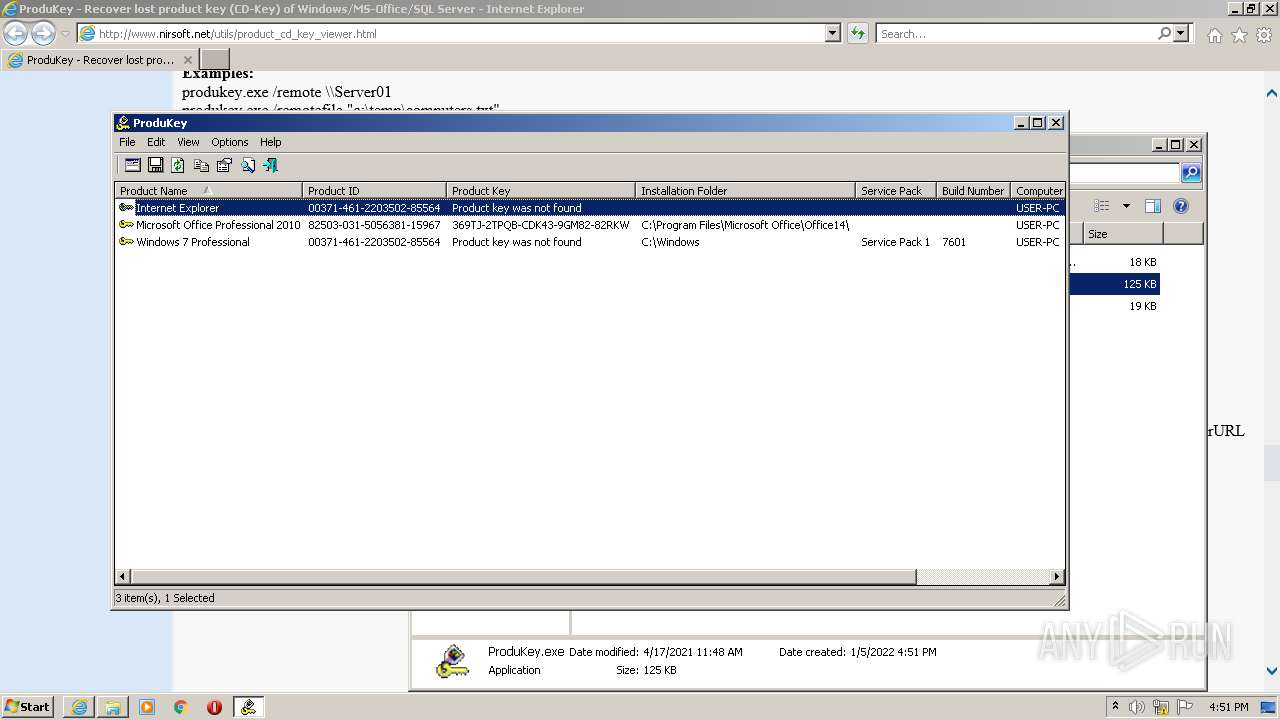
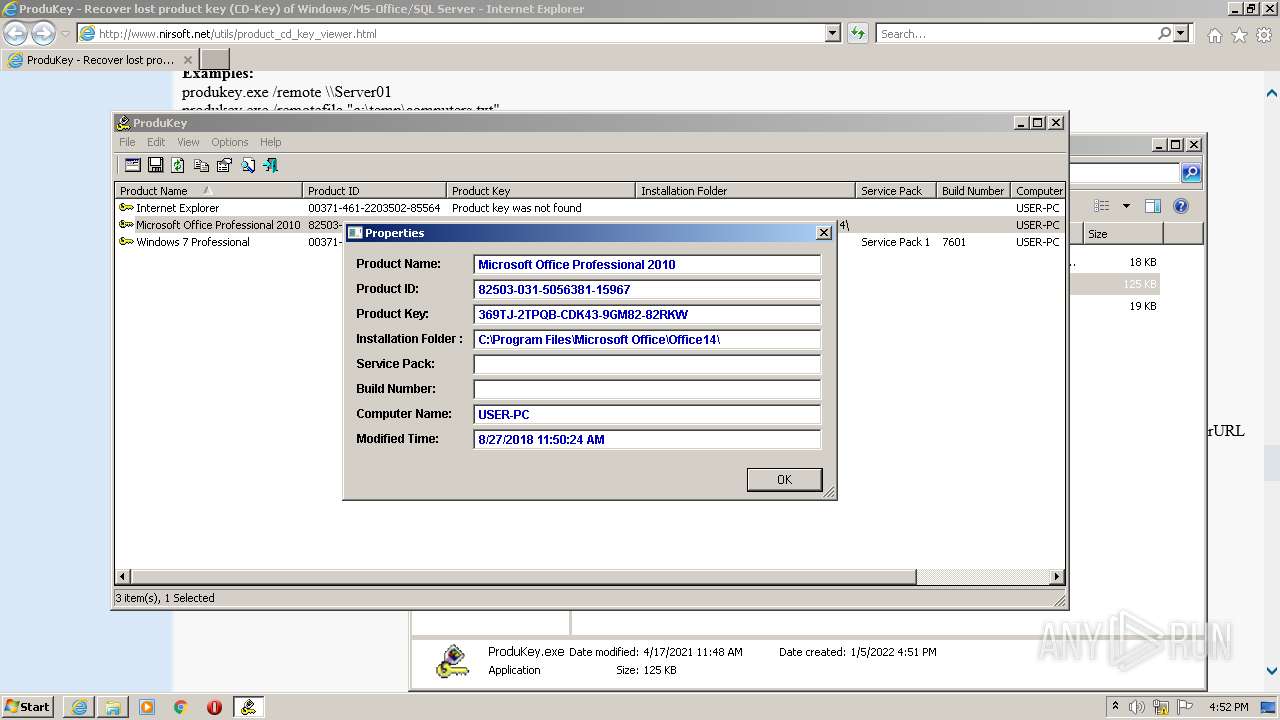
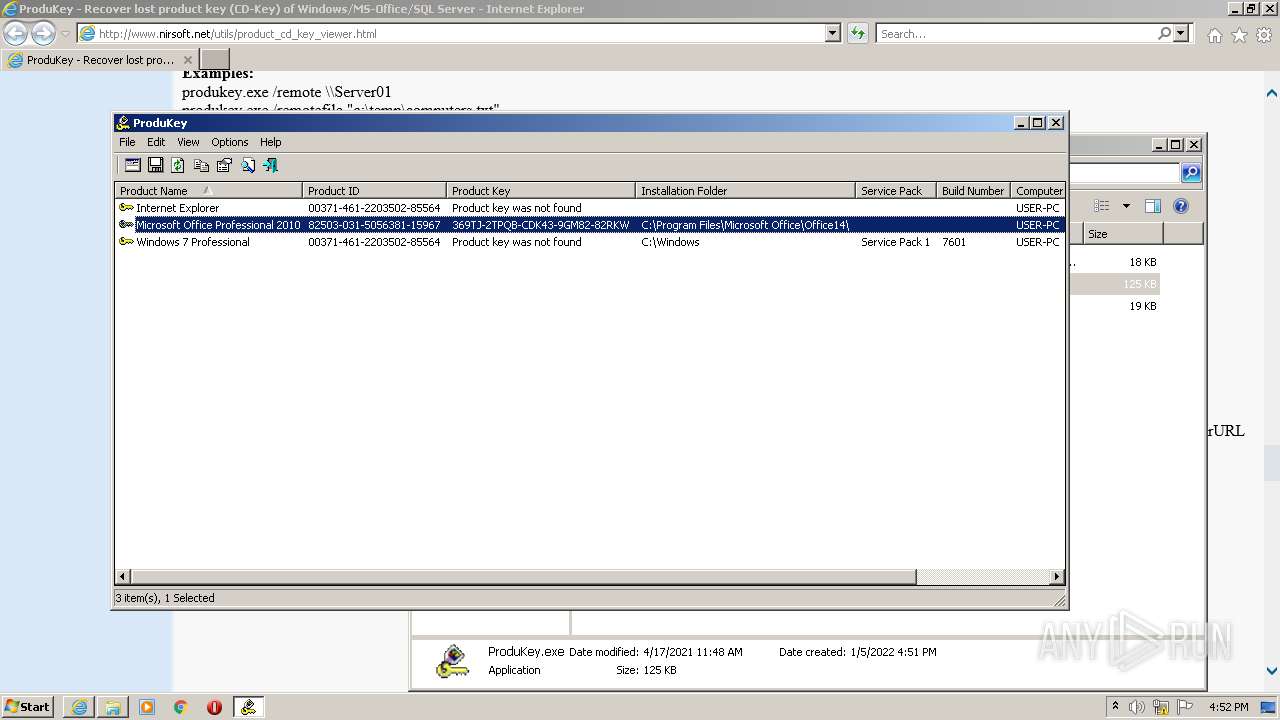
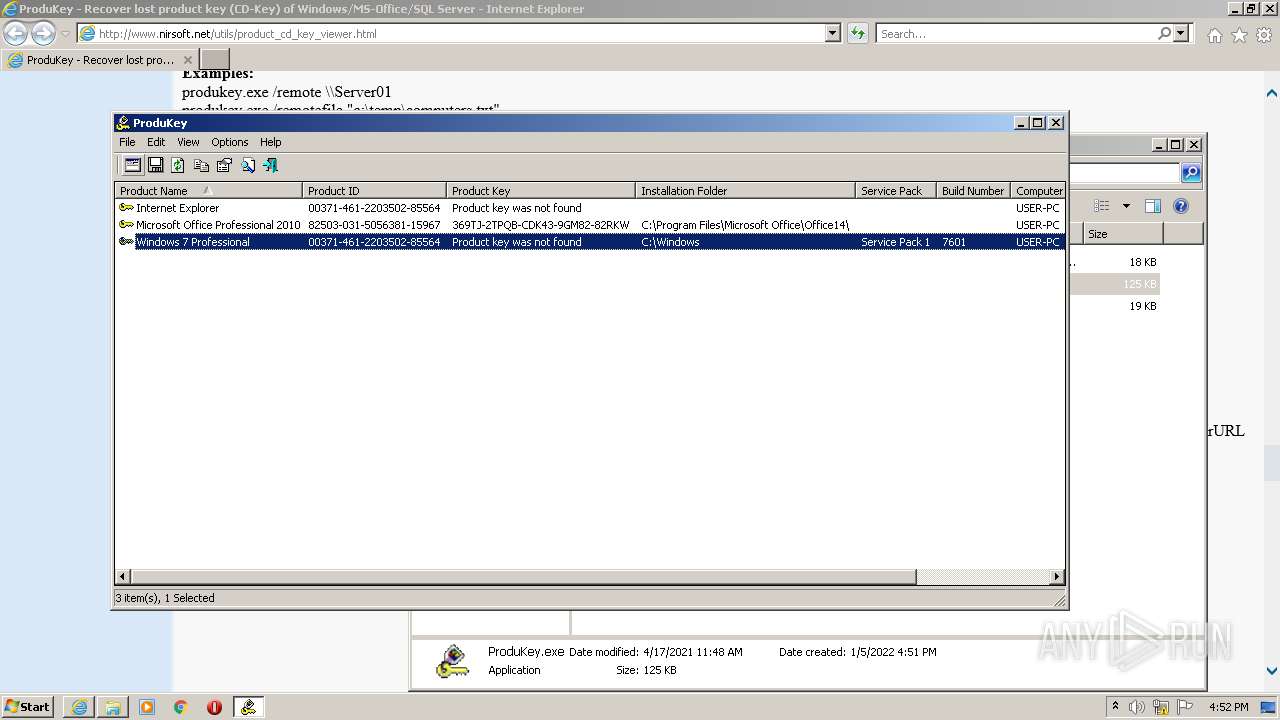
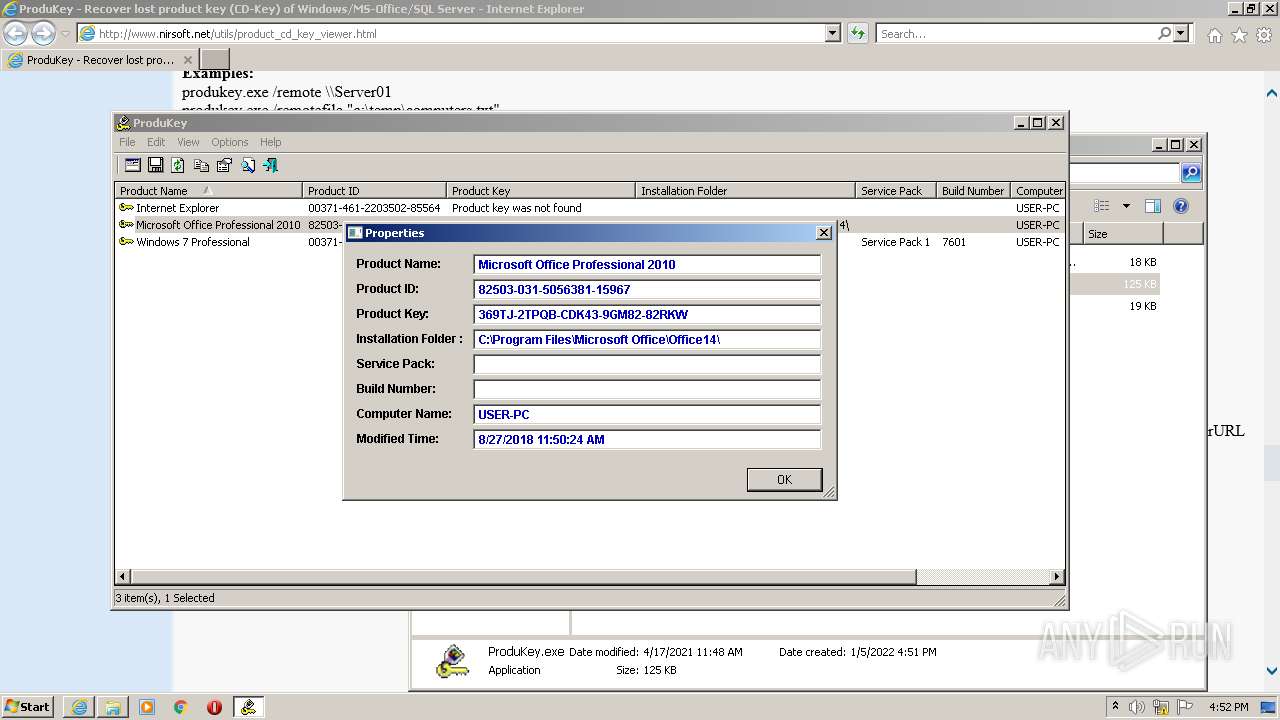
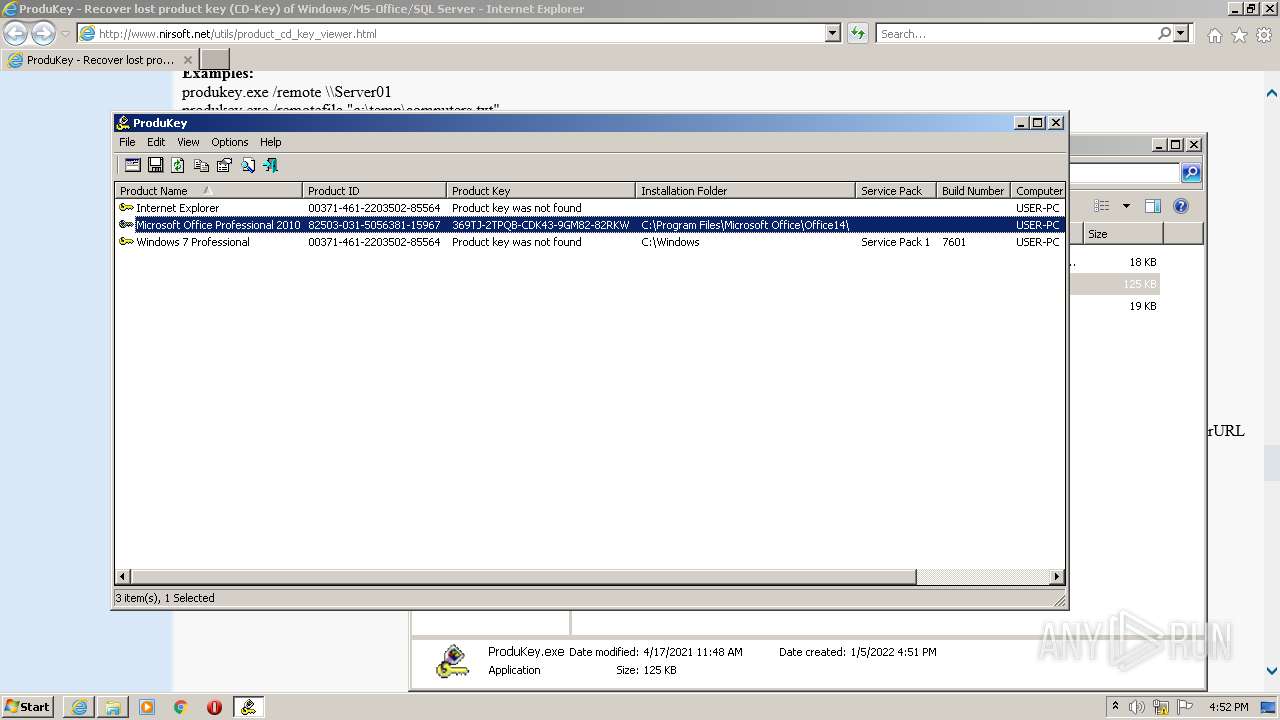
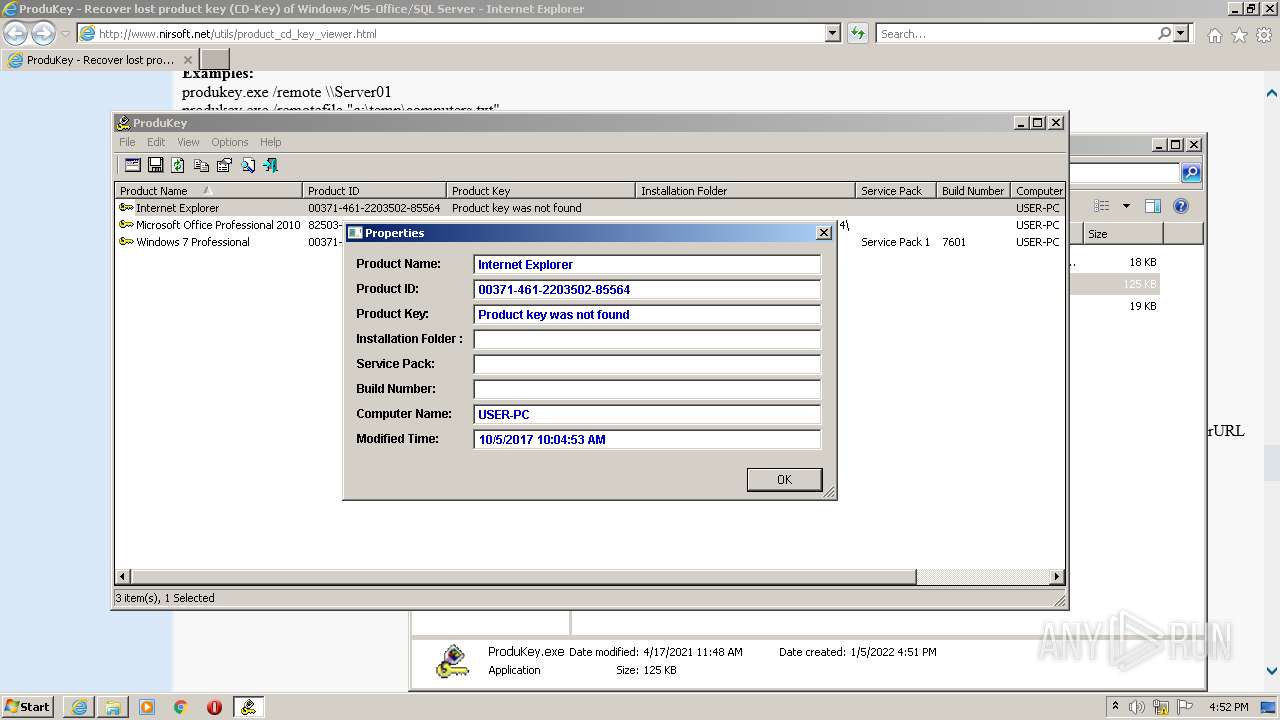
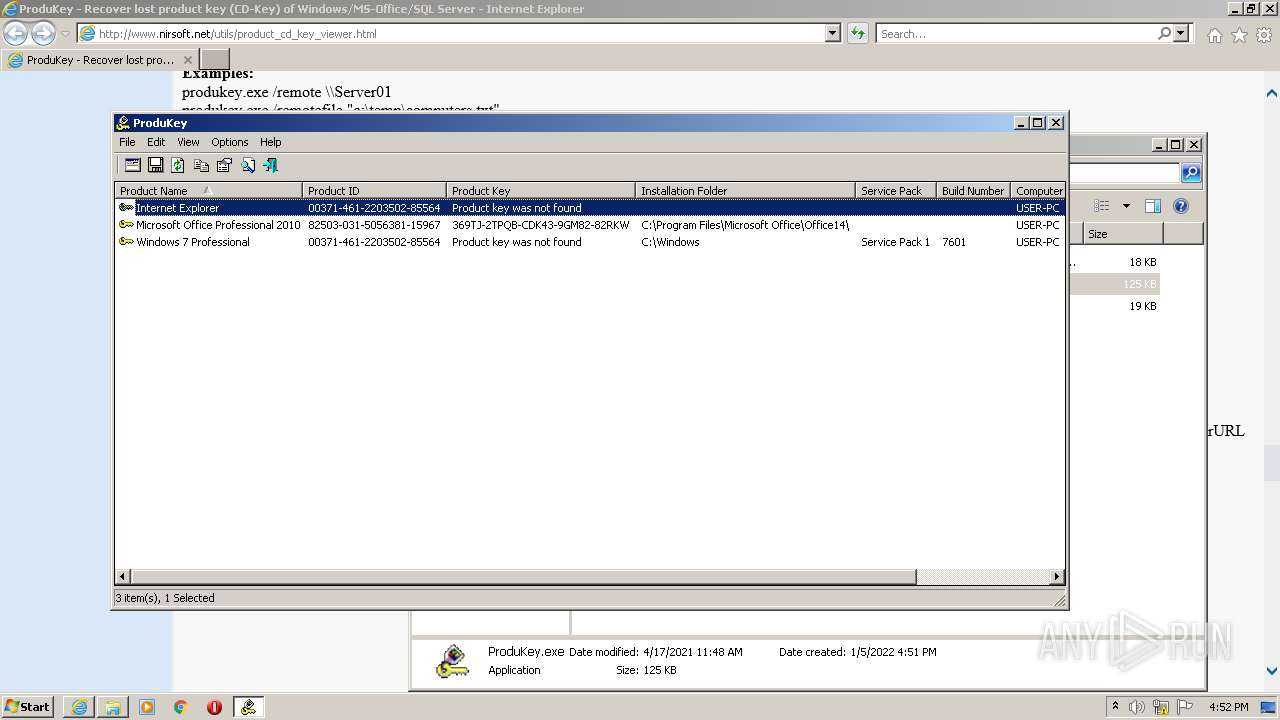
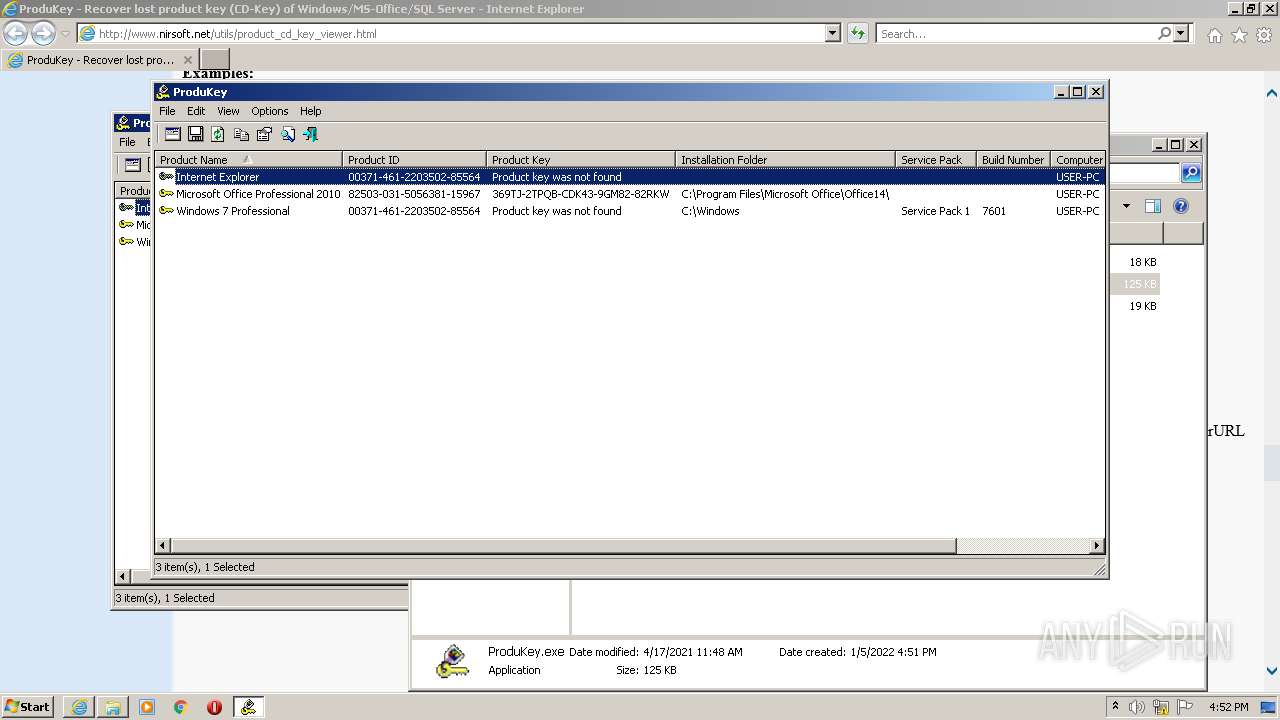
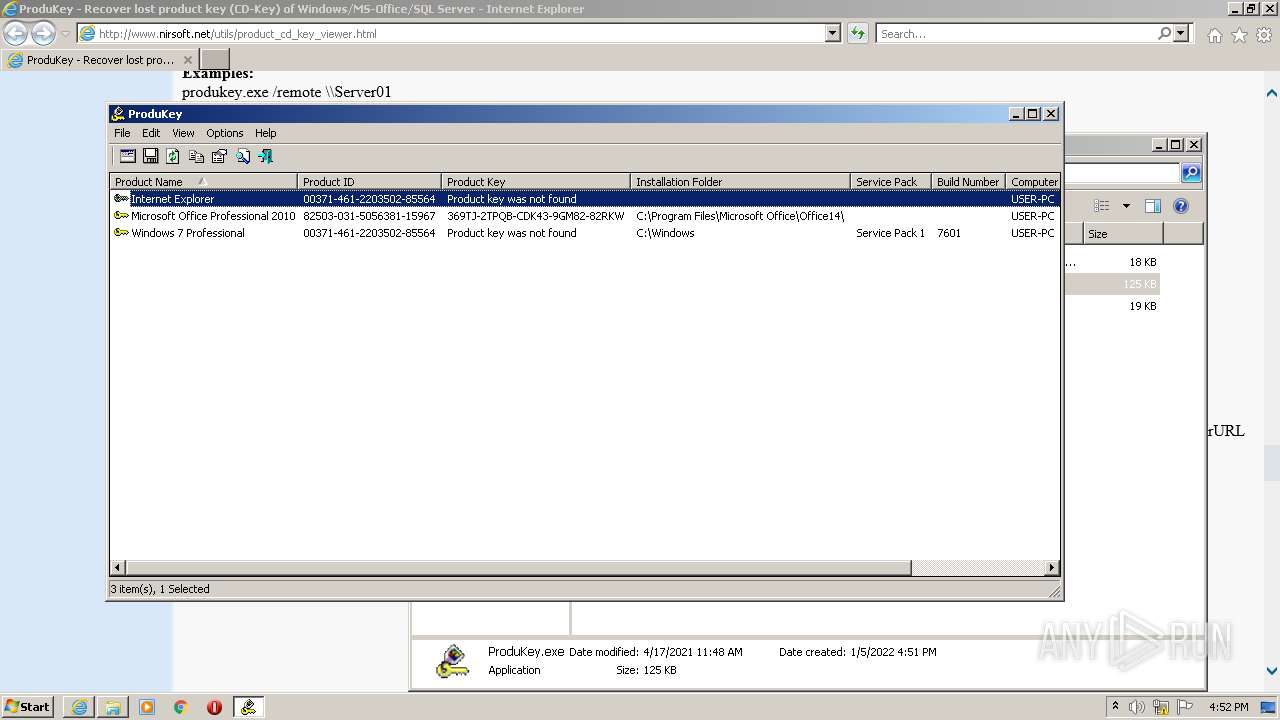
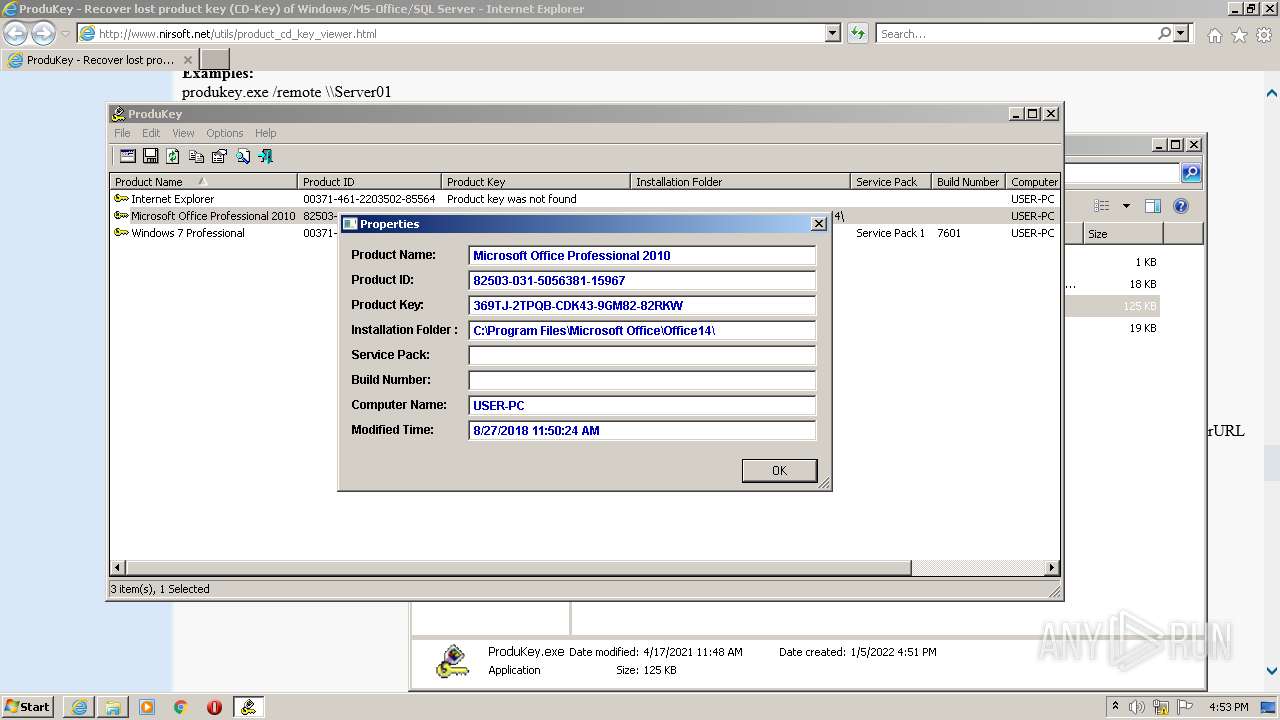
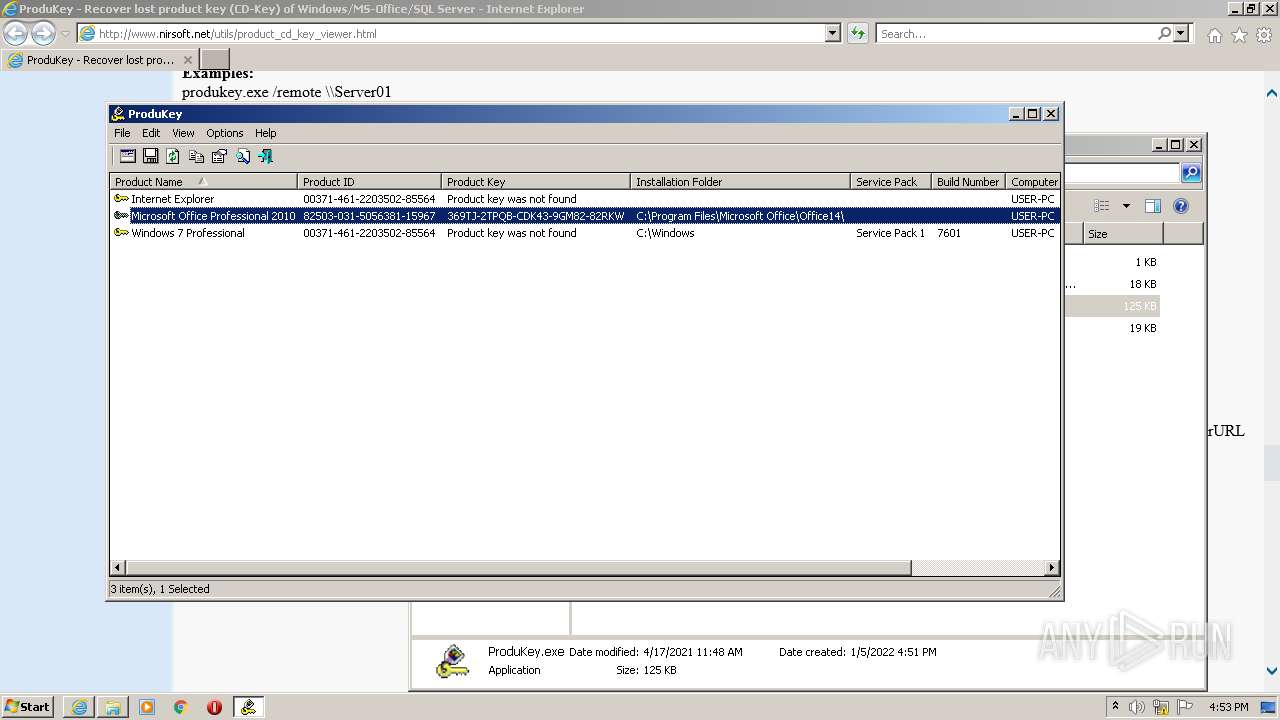
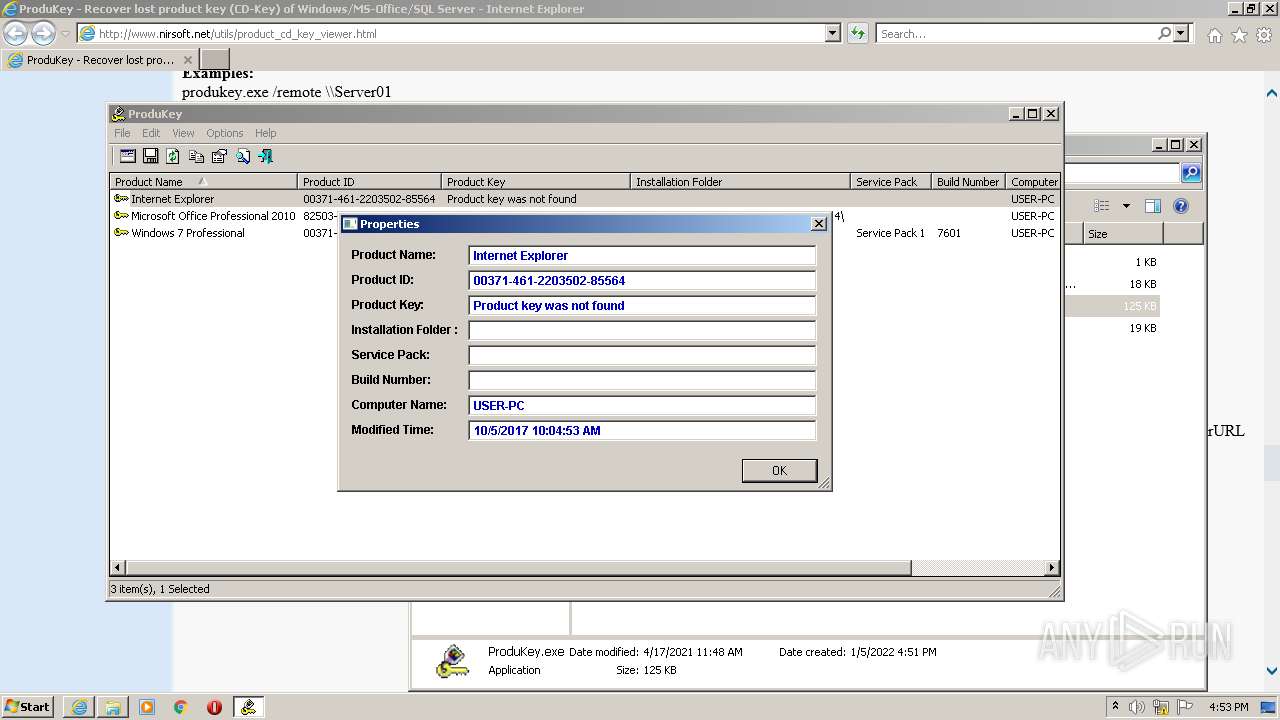
MALICIOUS
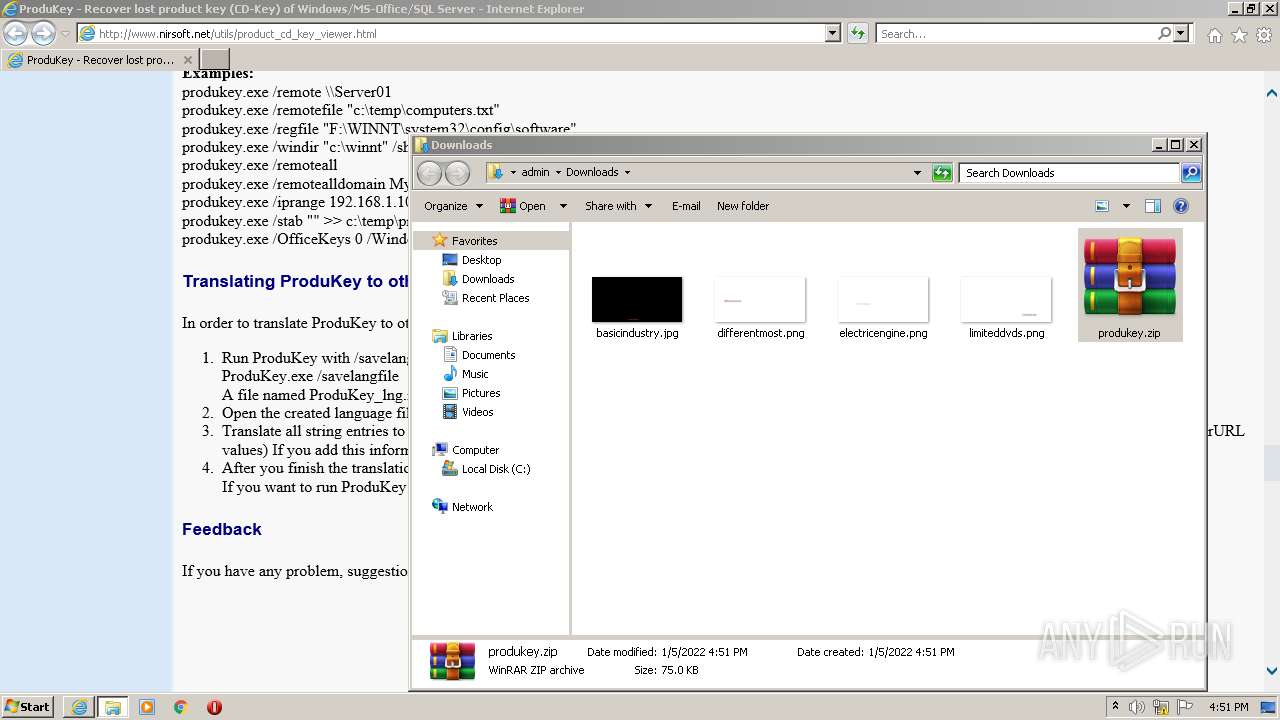
Application was dropped or rewritten from another process
- ProduKey.exe (PID: 3188)
- ProduKey.exe (PID: 2160)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2504)
Checks supported languages
- WinRAR.exe (PID: 2540)
- ProduKey.exe (PID: 3188)
- ProduKey.exe (PID: 2160)
Reads the computer name
- WinRAR.exe (PID: 2540)
- ProduKey.exe (PID: 3188)
- ProduKey.exe (PID: 2160)
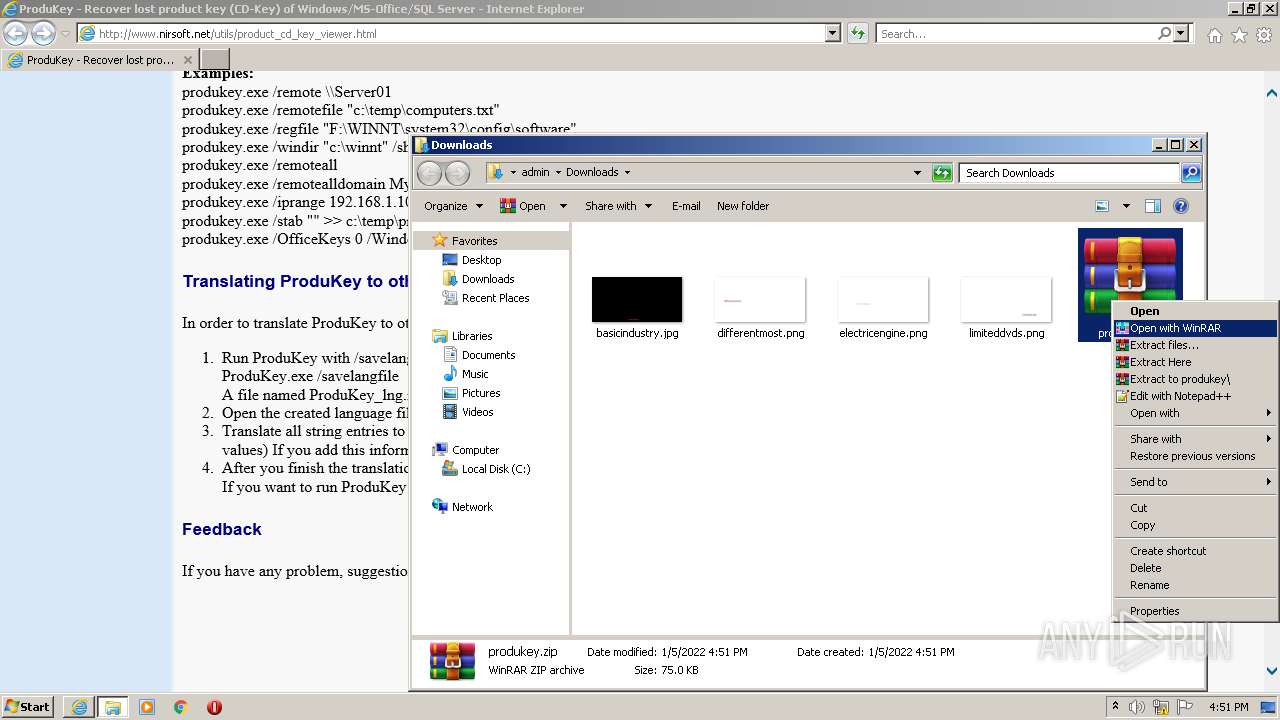
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2540)
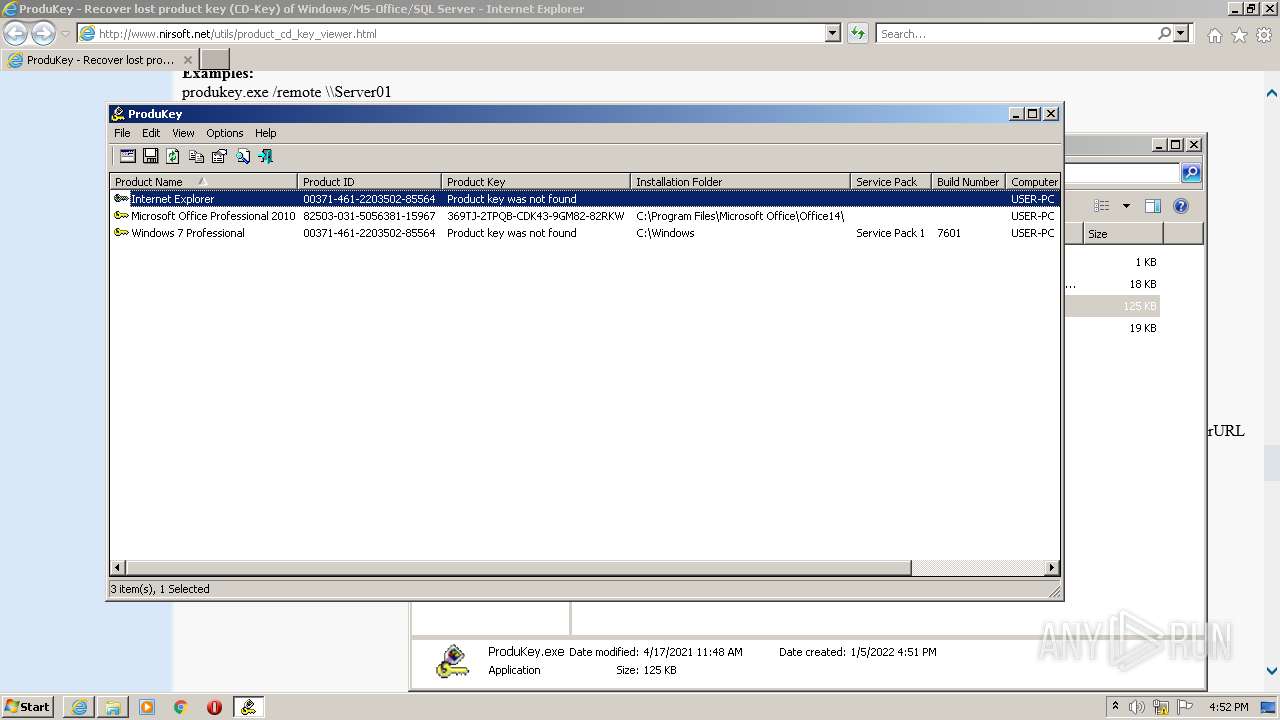
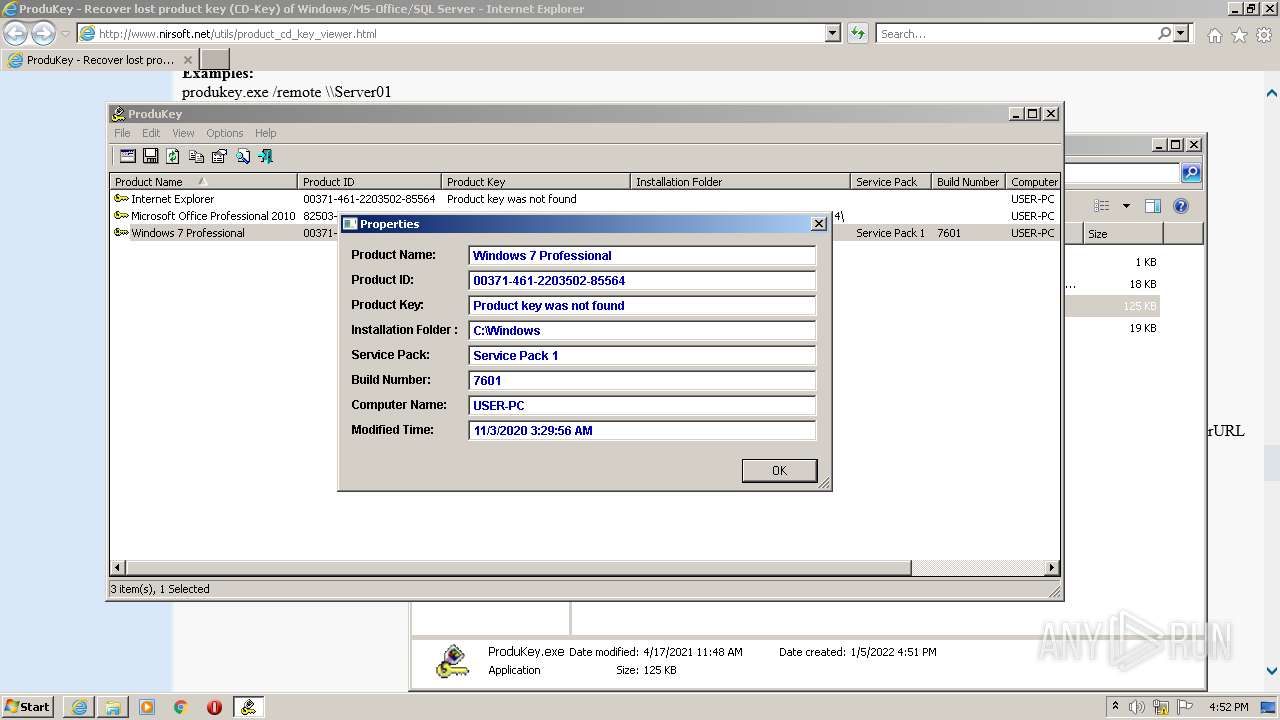
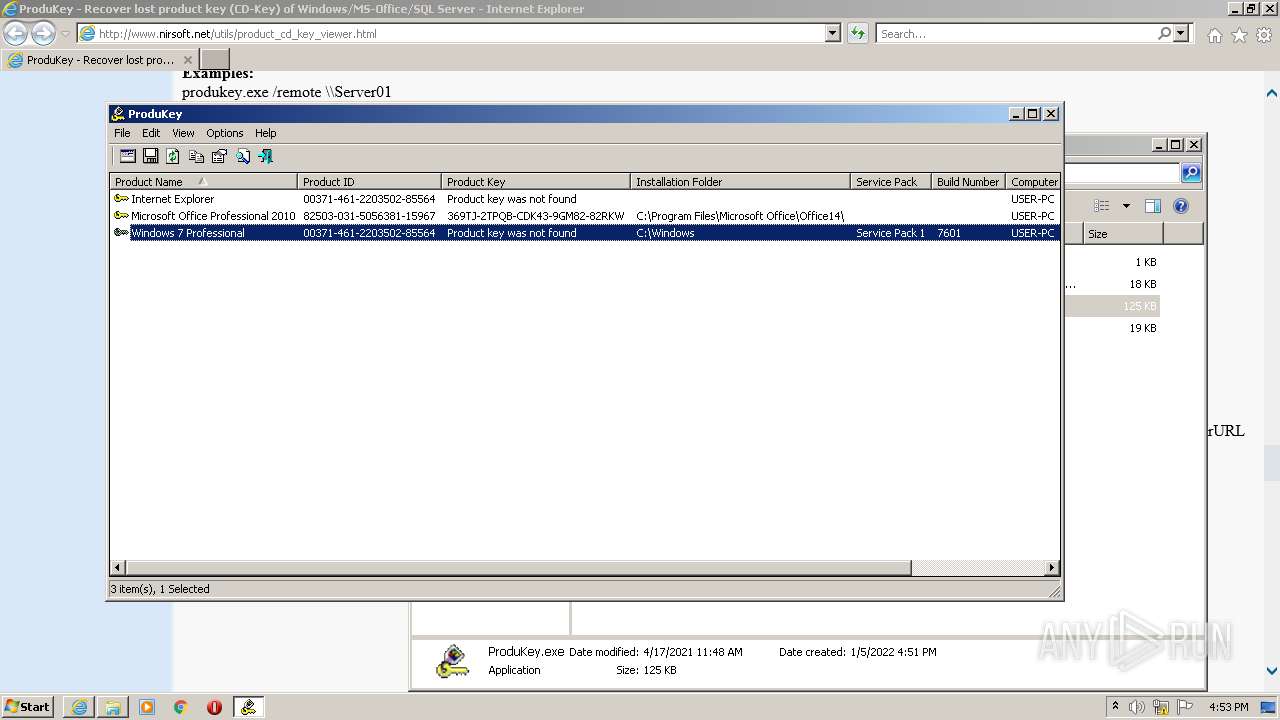
Reads Windows Product ID
- ProduKey.exe (PID: 3188)
- ProduKey.exe (PID: 2160)
Reads Environment values
- ProduKey.exe (PID: 2160)
- ProduKey.exe (PID: 3188)
INFO
Changes internet zones settings
- iexplore.exe (PID: 2520)
Checks supported languages
- iexplore.exe (PID: 2520)
- iexplore.exe (PID: 2504)
Reads the computer name
- iexplore.exe (PID: 2520)
- iexplore.exe (PID: 2504)
Application launched itself
- iexplore.exe (PID: 2520)
Reads settings of System Certificates
- iexplore.exe (PID: 2504)
- iexplore.exe (PID: 2520)
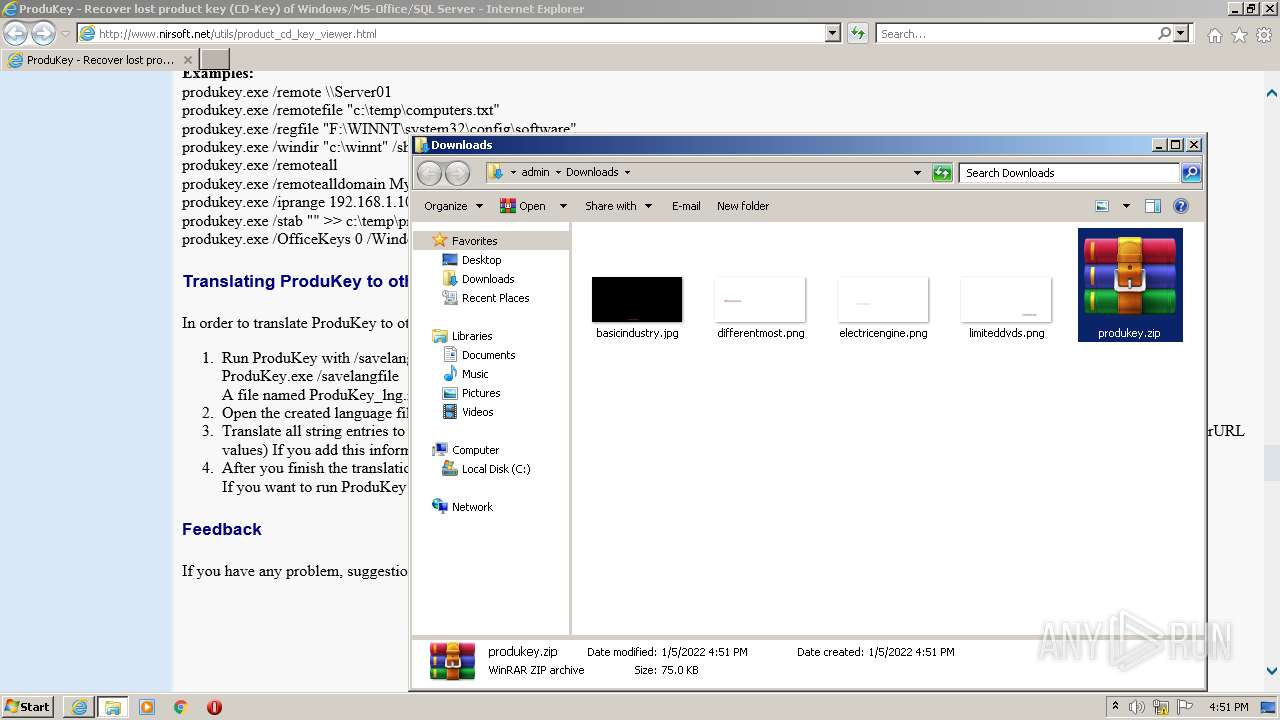
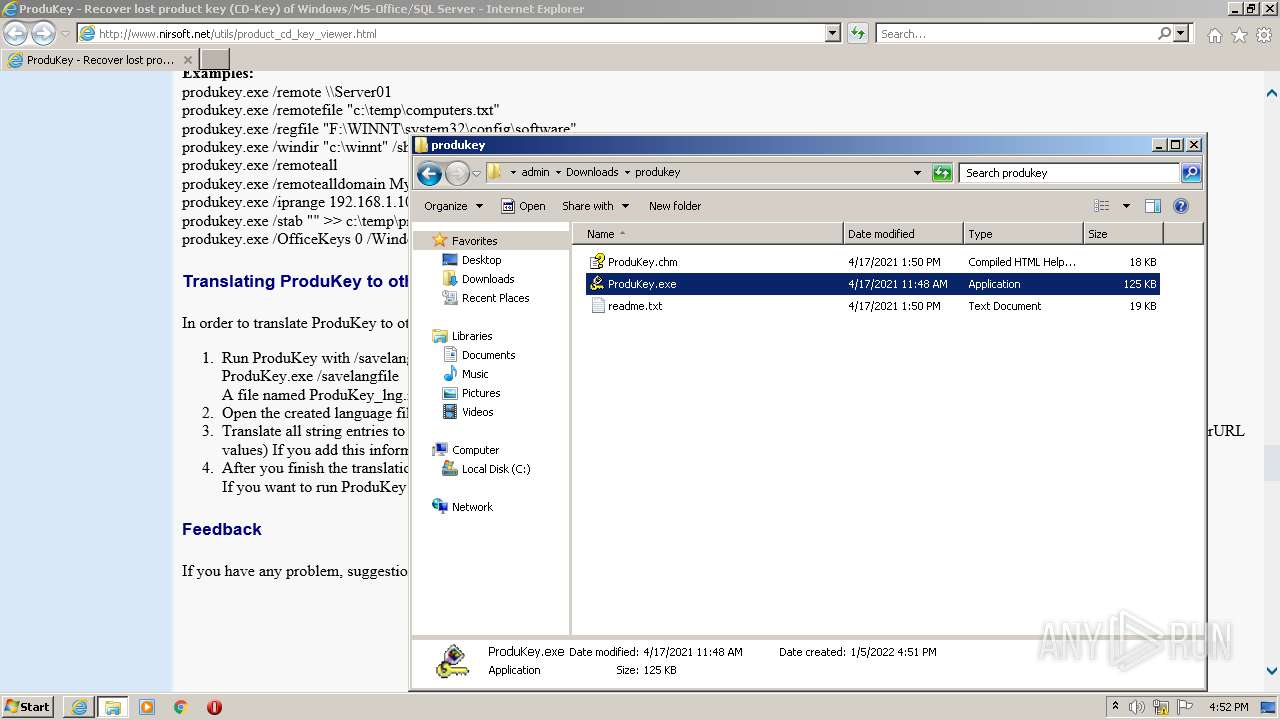
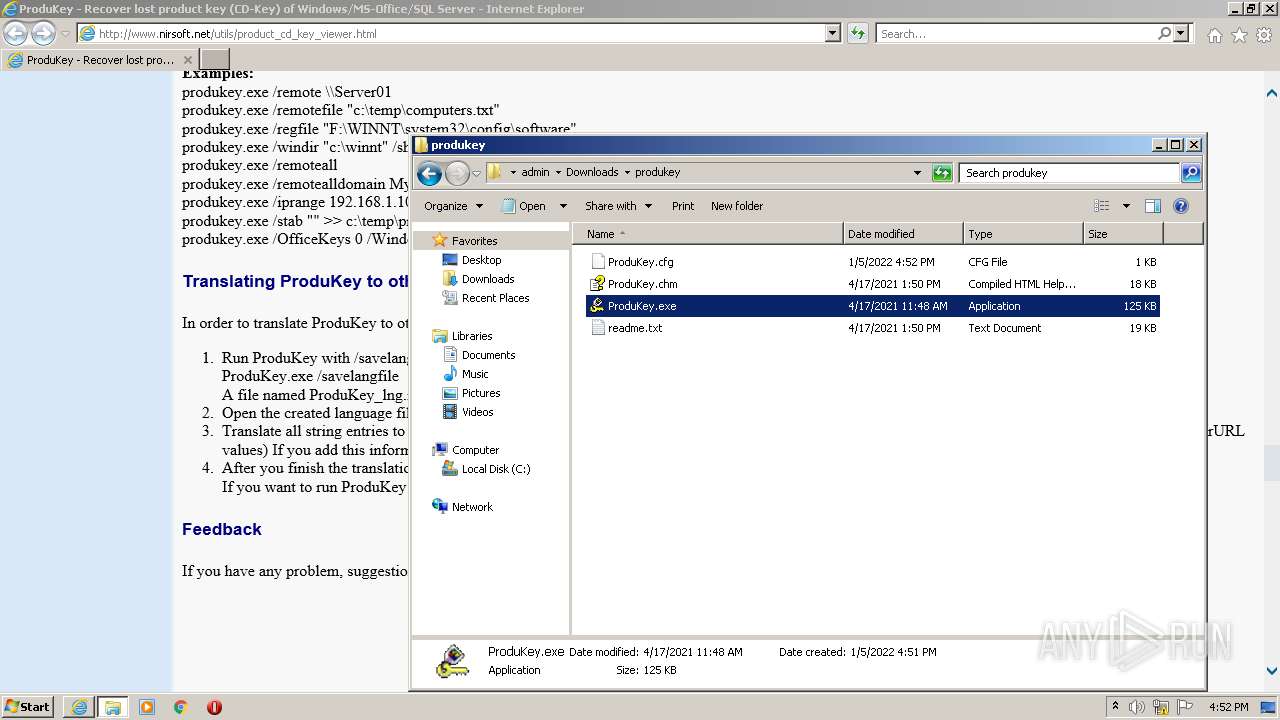
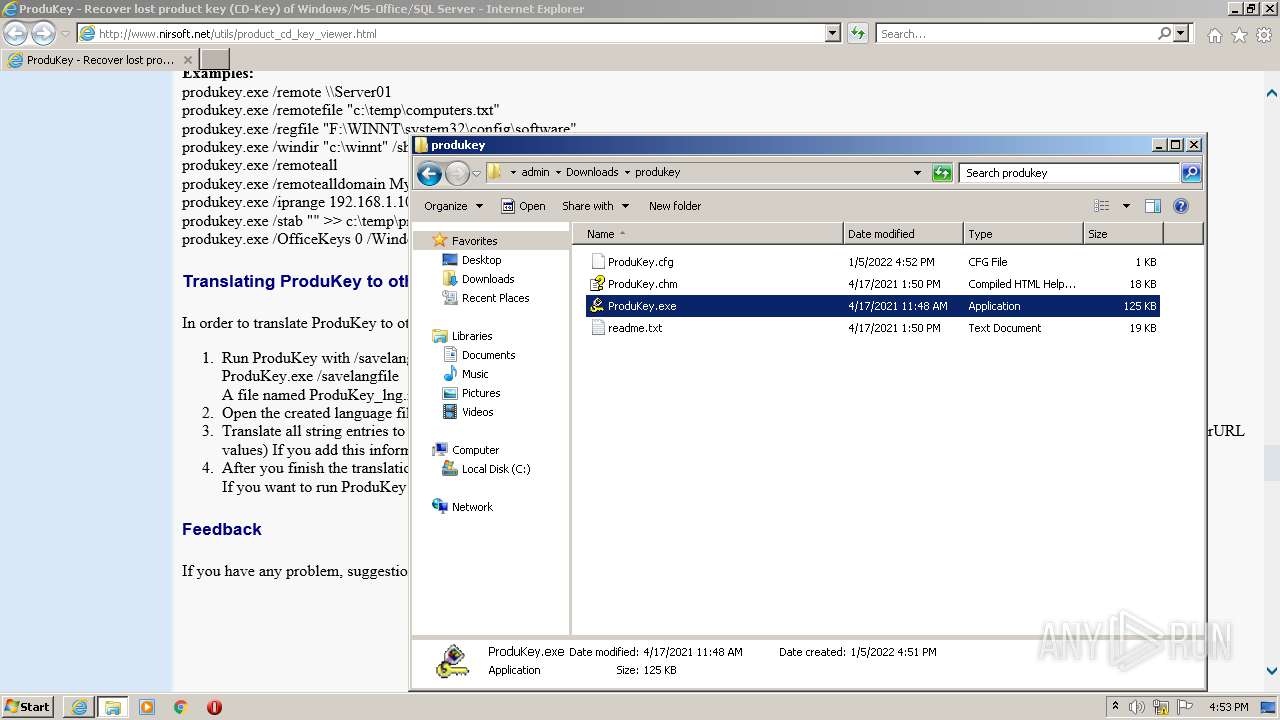
Manual execution by user
- WinRAR.exe (PID: 2540)
- ProduKey.exe (PID: 3188)
- ProduKey.exe (PID: 2160)
Modifies the phishing filter of IE
- iexplore.exe (PID: 2520)
Checks Windows Trust Settings
- iexplore.exe (PID: 2504)
- iexplore.exe (PID: 2520)
Creates files in the user directory
- iexplore.exe (PID: 2504)
- iexplore.exe (PID: 2520)
Reads internet explorer settings
- iexplore.exe (PID: 2504)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 2520)
Reads Microsoft Office registry keys
- ProduKey.exe (PID: 3188)
- ProduKey.exe (PID: 2160)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2520)
Changes settings of System certificates
- iexplore.exe (PID: 2520)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
43
Monitored processes
5
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
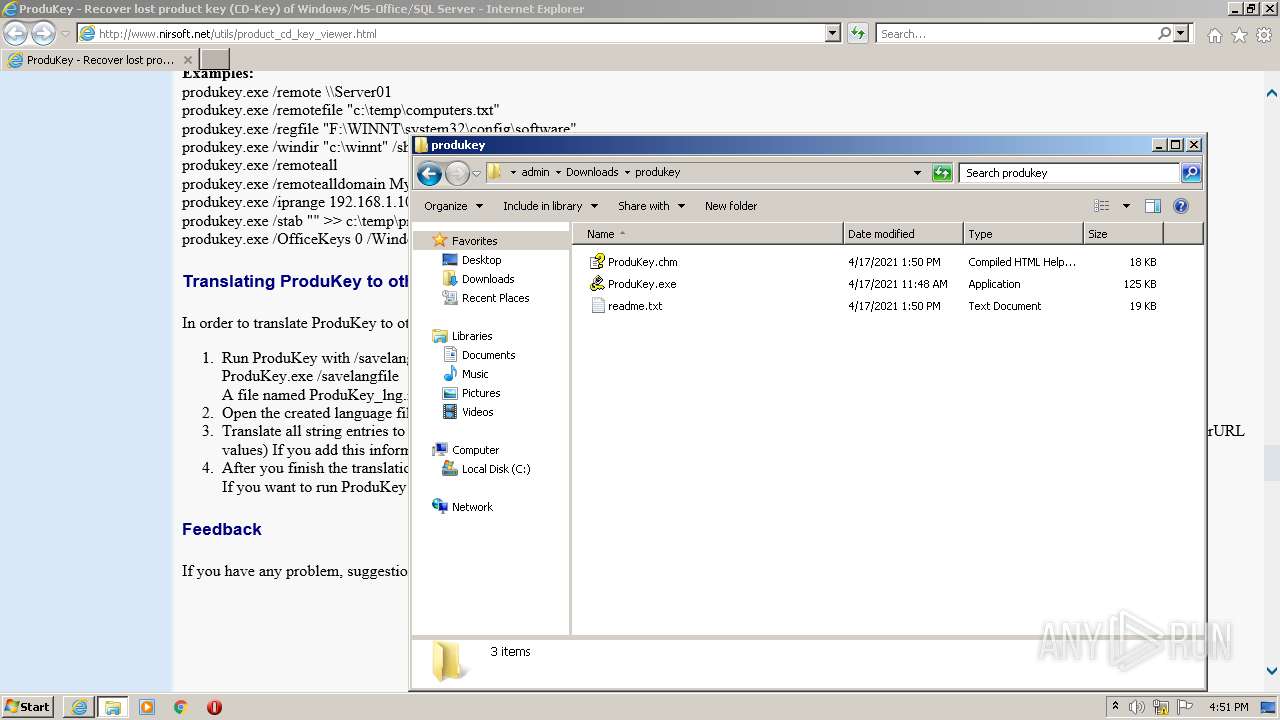
| 2160 | "C:\Users\admin\Downloads\produkey\ProduKey.exe" | C:\Users\admin\Downloads\produkey\ProduKey.exe | — | Explorer.EXE | |||||||||||
User: admin Company: NirSoft Integrity Level: MEDIUM Description: Shows Windows / Office product keys stored in the Registry Exit code: 0 Version: 1.97 Modules
| |||||||||||||||
| 2504 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2520 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2520 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://www.nirsoft.net/utils/product_cd_key_viewer.html" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
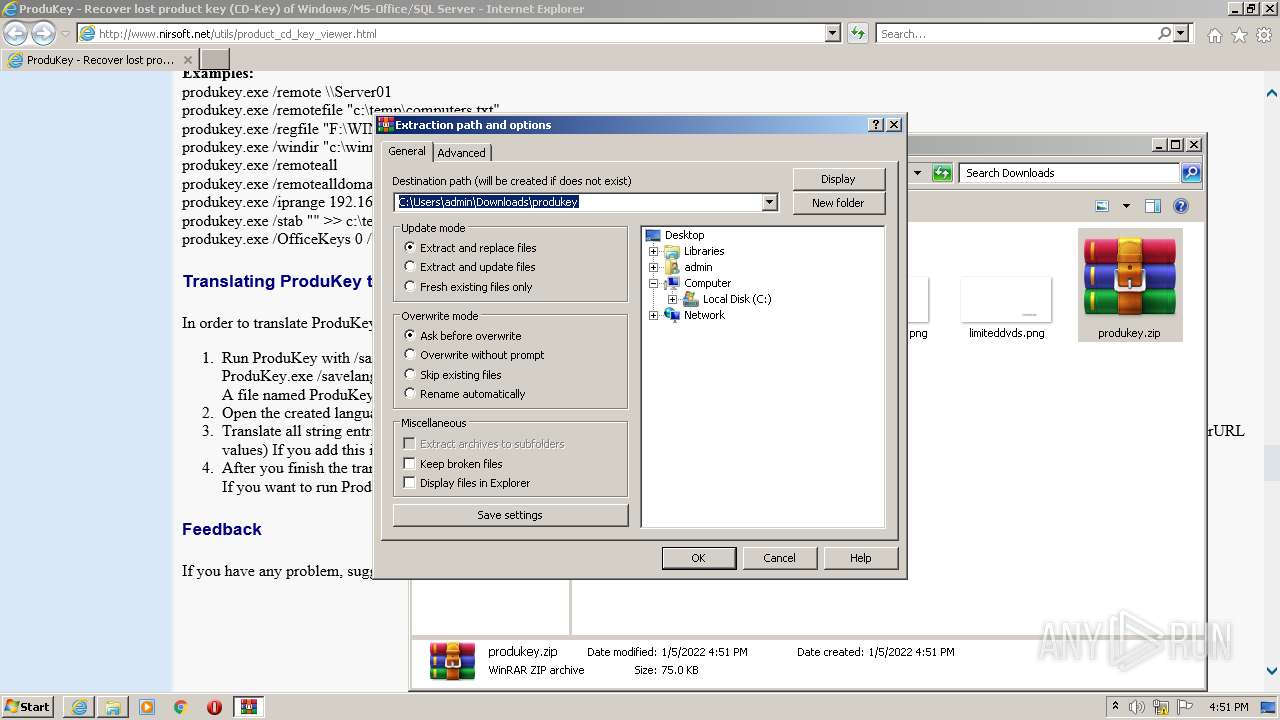
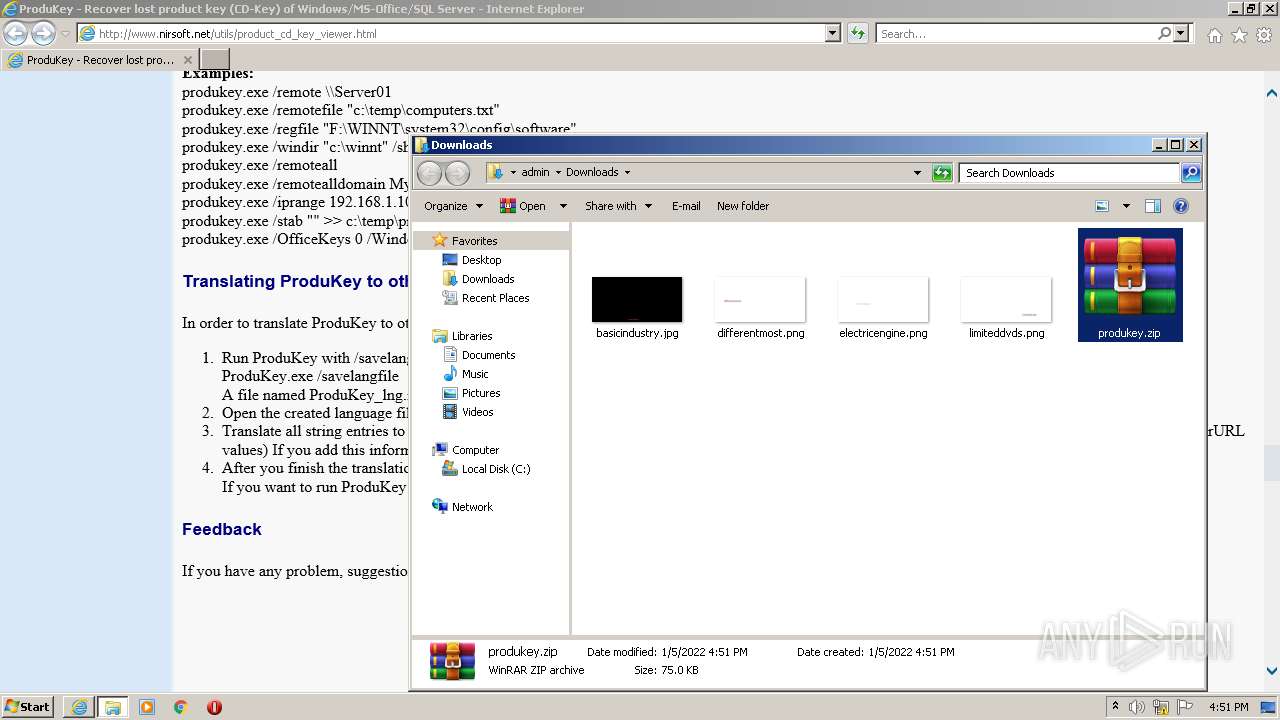
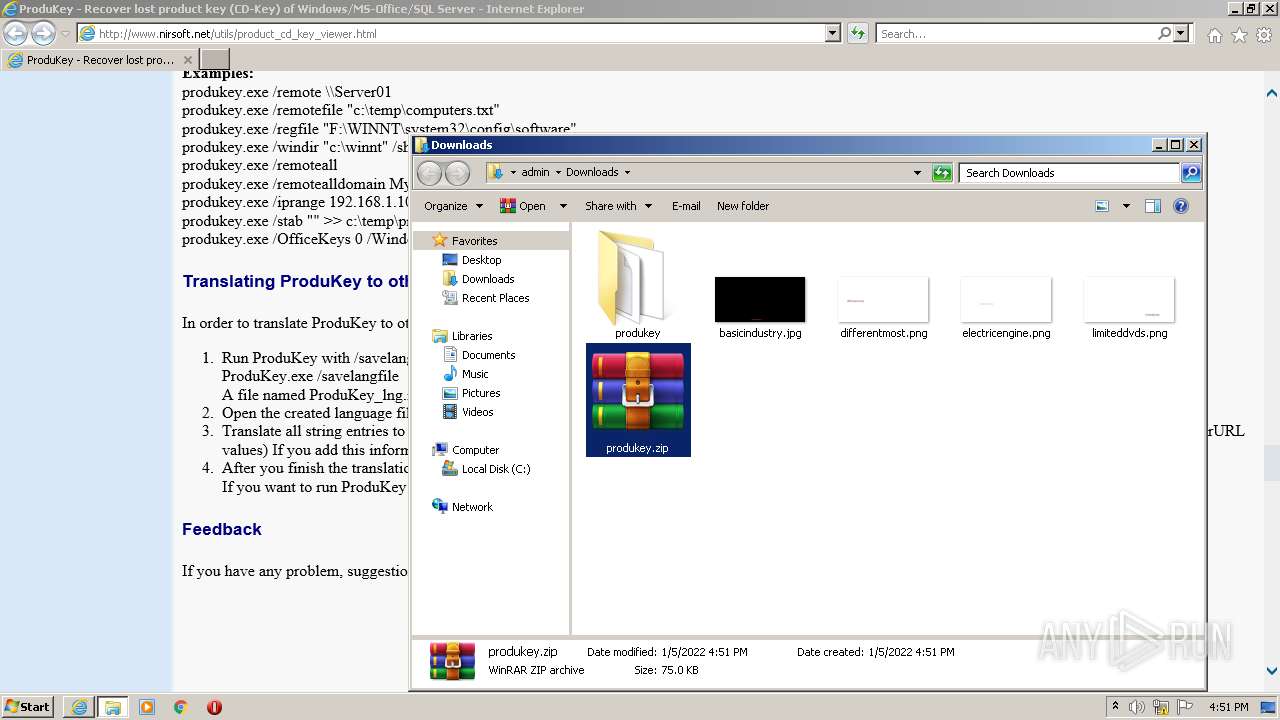
| 2540 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Downloads\produkey.zip" "?\" | C:\Program Files\WinRAR\WinRAR.exe | Explorer.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 3188 | "C:\Users\admin\Downloads\produkey\ProduKey.exe" | C:\Users\admin\Downloads\produkey\ProduKey.exe | — | Explorer.EXE | |||||||||||
User: admin Company: NirSoft Integrity Level: MEDIUM Description: Shows Windows / Office product keys stored in the Registry Exit code: 0 Version: 1.97 Modules
| |||||||||||||||
Total events
17 046
Read events
16 823
Write events
221
Delete events
2
Modification events
| (PID) Process: | (2520) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2520) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (2520) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30933588 | |||
| (PID) Process: | (2520) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (2520) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30933588 | |||
| (PID) Process: | (2520) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2520) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2520) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2520) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2520) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
1
Suspicious files
39
Text files
88
Unknown types
33
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2504 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\product_cd_key_viewer[1].htm | html | |
MD5:— | SHA256:— | |||
| 2504 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\nirsoft2[1].gif | image | |
MD5:2E7F628850F2705DDFCA2FB210322B00 | SHA256:0C4F483B95CFCE5C4E78F32946ED302502F365C272094950B254B6226C16C7F5 | |||
| 2504 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\223DE96EE265046957A660ED7C9DD9E7_EFF9B9BA98DEAA773F261FA85A0B1771 | der | |
MD5:— | SHA256:— | |||
| 2504 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\223DE96EE265046957A660ED7C9DD9E7_EFF9B9BA98DEAA773F261FA85A0B1771 | binary | |
MD5:— | SHA256:— | |||
| 2504 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\sync[1].js | text | |
MD5:— | SHA256:— | |||
| 2504 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\20ADE6165B9B25AE9FF1A4FA61BFAE23_42F91AA754714C910623A5E6A5DD1791 | der | |
MD5:— | SHA256:— | |||
| 2504 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\EB2C4AB8B68FFA4B7733A9139239A396_D76DB901EE986B889F30D8CC06229E2D | der | |
MD5:— | SHA256:— | |||
| 2504 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\addelivery[1].js | text | |
MD5:— | SHA256:— | |||
| 2504 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 2504 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\20ADE6165B9B25AE9FF1A4FA61BFAE23_42F91AA754714C910623A5E6A5DD1791 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
41
TCP/UDP connections
127
DNS requests
41
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
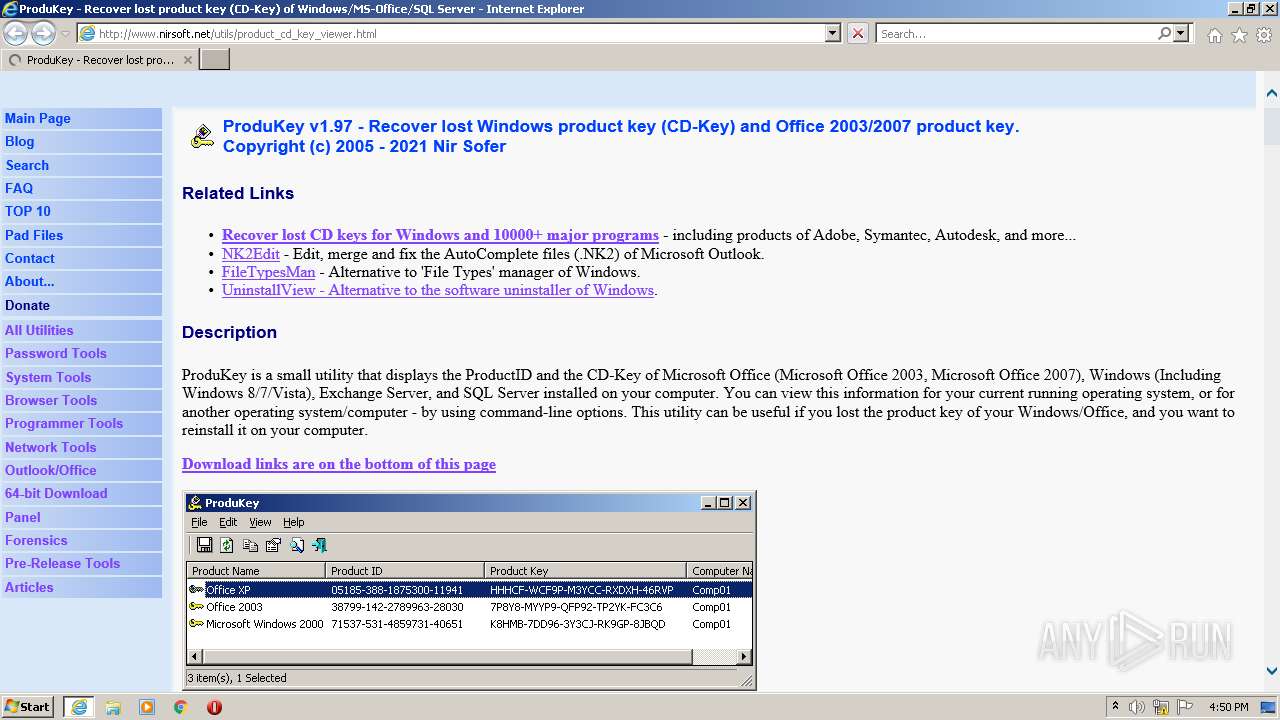
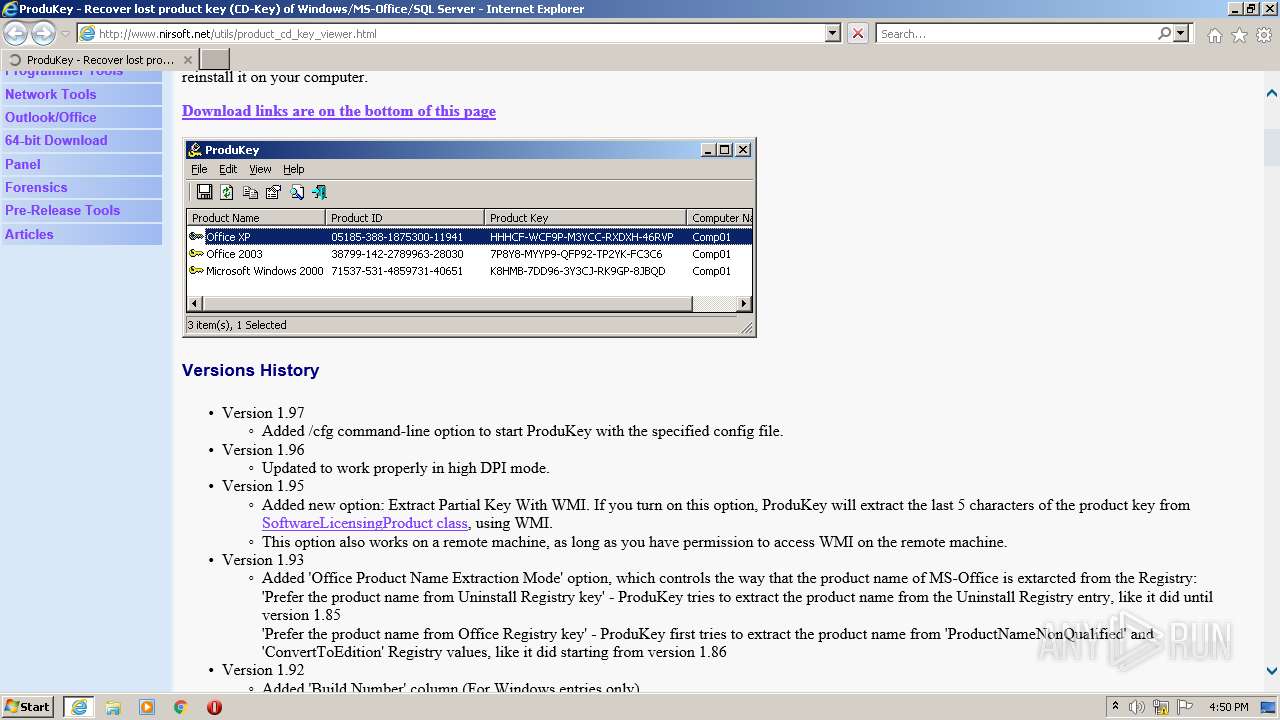
2504 | iexplore.exe | GET | 200 | 138.128.181.29:80 | http://www.nirsoft.net/utils/product_cd_key_viewer.html | US | html | 10.7 Kb | whitelisted |
2504 | iexplore.exe | GET | 200 | 192.124.249.41:80 | http://ocsp.godaddy.com//MEQwQjBAMD4wPDAJBgUrDgMCGgUABBTkIInKBAzXkF0Qh0pel3lfHJ9GPAQU0sSw0pHUTBFxs2HLPaH%2B3ahq1OMCAxvnFQ%3D%3D | US | der | 1.66 Kb | whitelisted |
2504 | iexplore.exe | GET | 200 | 192.124.249.41:80 | http://ocsp.godaddy.com//MEIwQDA%2BMDwwOjAJBgUrDgMCGgUABBQdI2%2BOBkuXH93foRUj4a7lAr4rGwQUOpqFBxBnKLbv9r0FQW4gwZTaD94CAQc%3D | US | der | 1.69 Kb | whitelisted |
2504 | iexplore.exe | GET | 200 | 142.250.186.35:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
2504 | iexplore.exe | GET | 200 | 192.124.249.41:80 | http://ocsp.godaddy.com//MEowSDBGMEQwQjAJBgUrDgMCGgUABBS2CA1fbGt26xPkOKX4ZguoUjM0TgQUQMK9J47MNIMwojPX%2B2yz8LQsgM4CCQDmOjriYr4IsA%3D%3D | US | der | 1.74 Kb | whitelisted |
2504 | iexplore.exe | GET | 200 | 142.250.186.35:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
2504 | iexplore.exe | GET | 200 | 142.250.186.35:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCECHMNwkPtKJCCgAAAAEl%2FQo%3D | US | der | 471 b | whitelisted |
2520 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
2504 | iexplore.exe | GET | 200 | 142.250.186.35:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCZ2fjZwSXF%2BwoAAAABJfz9 | US | der | 472 b | whitelisted |
2504 | iexplore.exe | GET | 200 | 138.128.181.29:80 | http://www.nirsoft.net/main.css | US | text | 1.53 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2520 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2504 | iexplore.exe | 142.250.186.35:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
2520 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2504 | iexplore.exe | 142.250.184.194:443 | googleads.g.doubleclick.net | Google Inc. | US | suspicious |
— | — | 142.250.184.194:443 | googleads.g.doubleclick.net | Google Inc. | US | suspicious |
2504 | iexplore.exe | 138.128.181.29:80 | www.nirsoft.net | HostDime.com, Inc. | US | suspicious |
2504 | iexplore.exe | 216.52.2.19:443 | ap.lijit.com | Voxel Dot Net, Inc. | US | unknown |
2504 | iexplore.exe | 104.84.56.126:80 | s7.addthis.com | Vodafone NZ Ltd. | US | unknown |
2504 | iexplore.exe | 142.250.185.66:443 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
2504 | iexplore.exe | 2.16.186.56:80 | ctldl.windowsupdate.com | Akamai International B.V. | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.nirsoft.net |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
ap.lijit.com |
| whitelisted |
s7.addthis.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.godaddy.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
s.update.ap.lijit.com |
| suspicious |