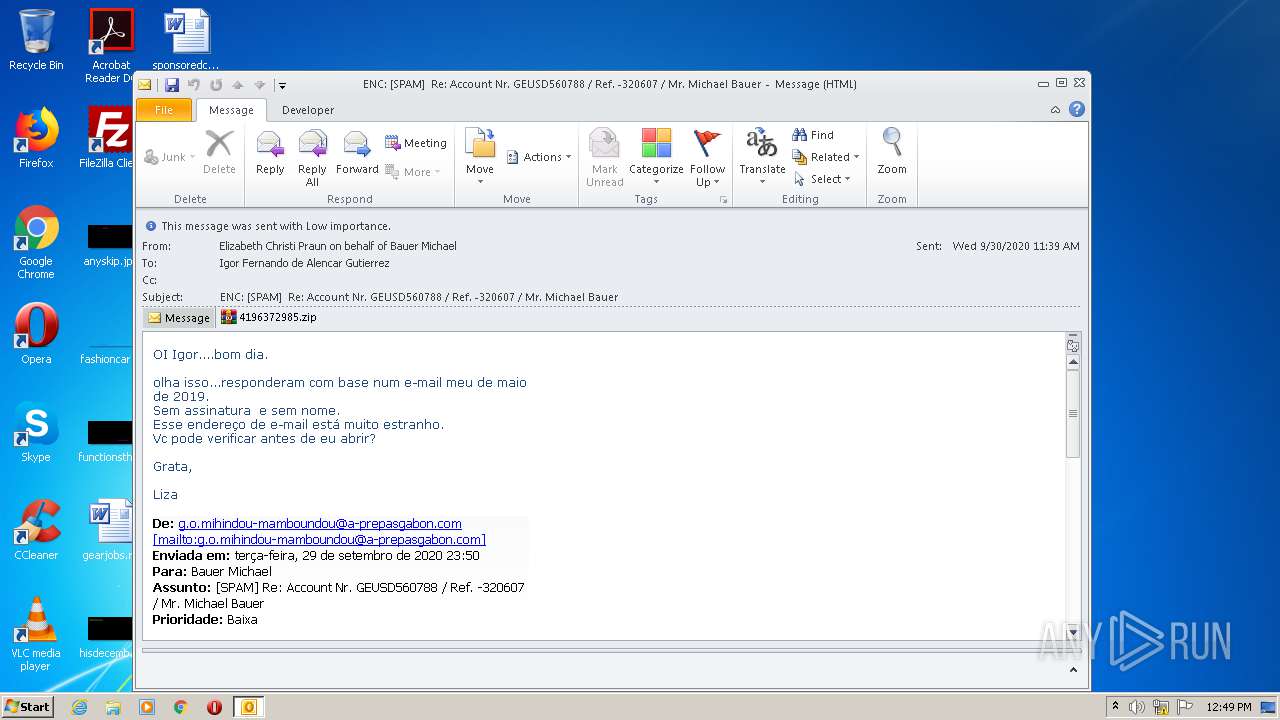
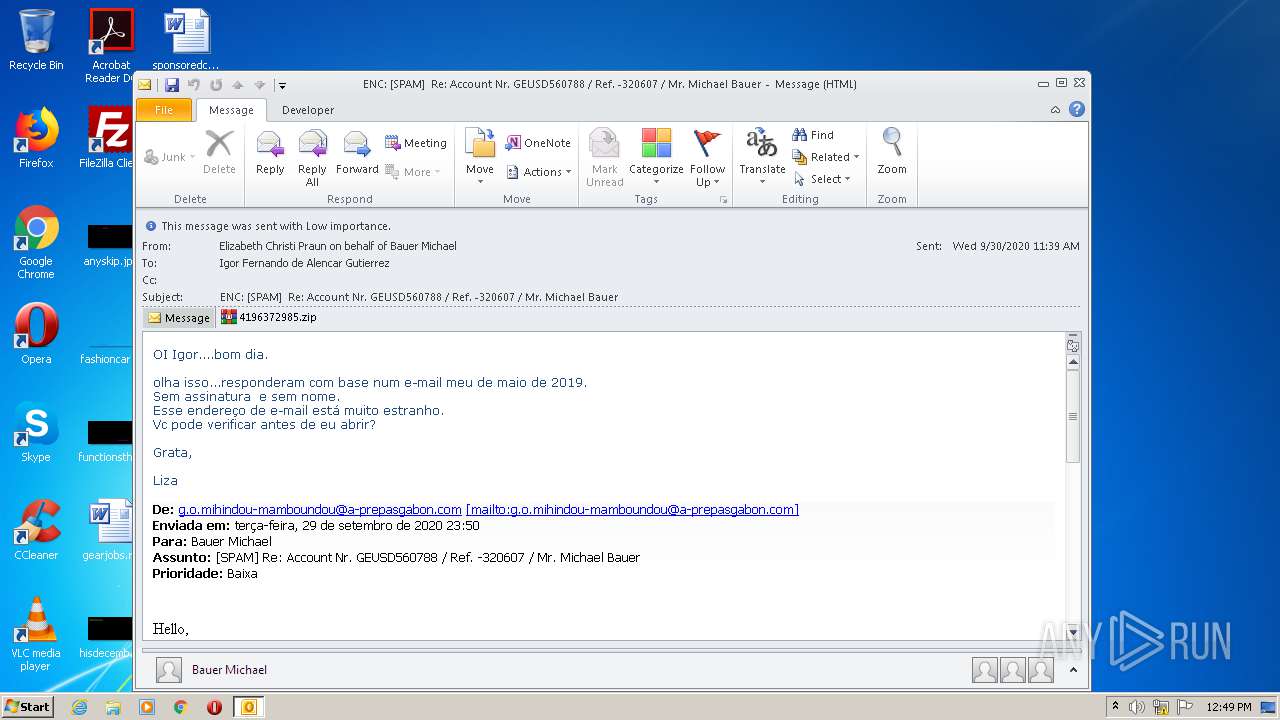
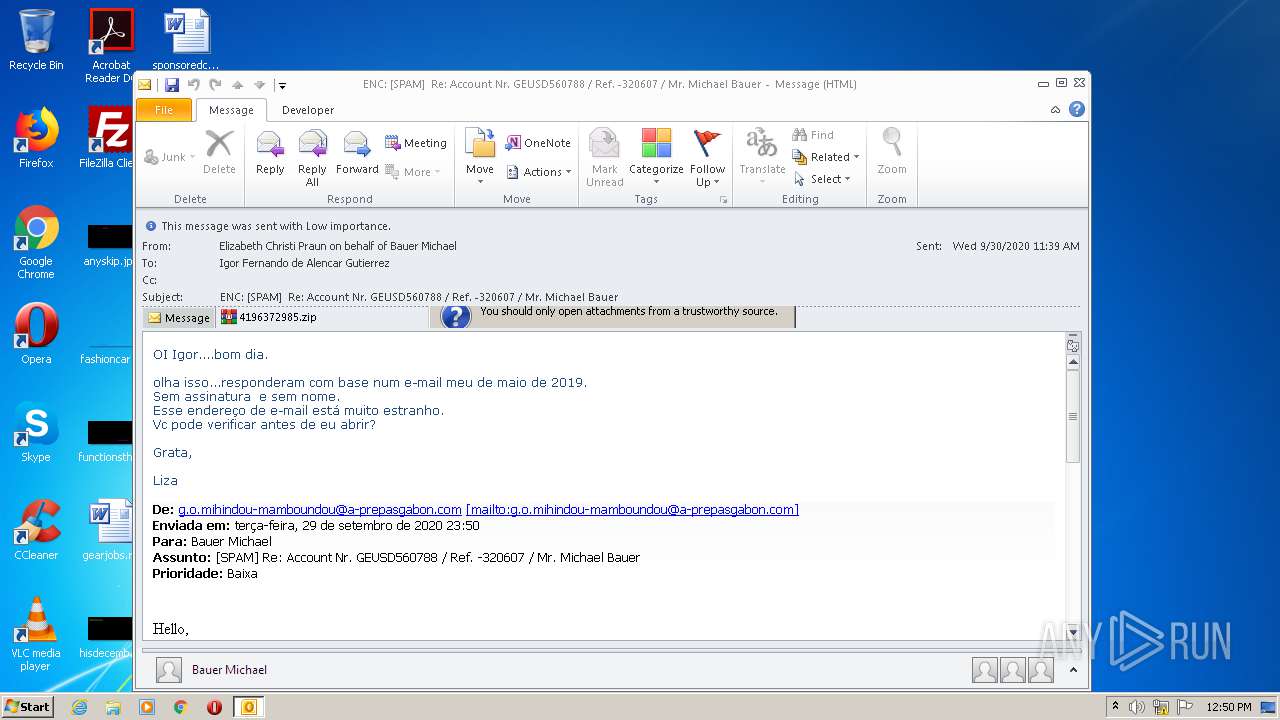
| File name: | ENC SPAM Re Account Nr. GEUSD560788 Ref. -320607 Mr. Michael Bauer.msg |
| Full analysis: | https://app.any.run/tasks/29f3c545-476c-4293-8177-f89c85542aec |
| Verdict: | Malicious activity |
| Analysis date: | September 30, 2020, 11:49:40 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | 7A17D86B18E5C579B61922F505E191E8 |
| SHA1: | DB989E65A638516E3FBD5AAD061A94A4FD03A4F3 |
| SHA256: | B4F7AB1B01CC8FBA07219FB5C3E8D84706603A319A6274986BBCE65CED9108DC |
| SSDEEP: | 768:PIfeapUAvqx8WsERYd45aPlnbEnZzpsicUghSErYX1yxozVM7GfwyUJgtD4Vfew8:gzpfY+d45OlbE19cFPr+rzhYyUJgtE |
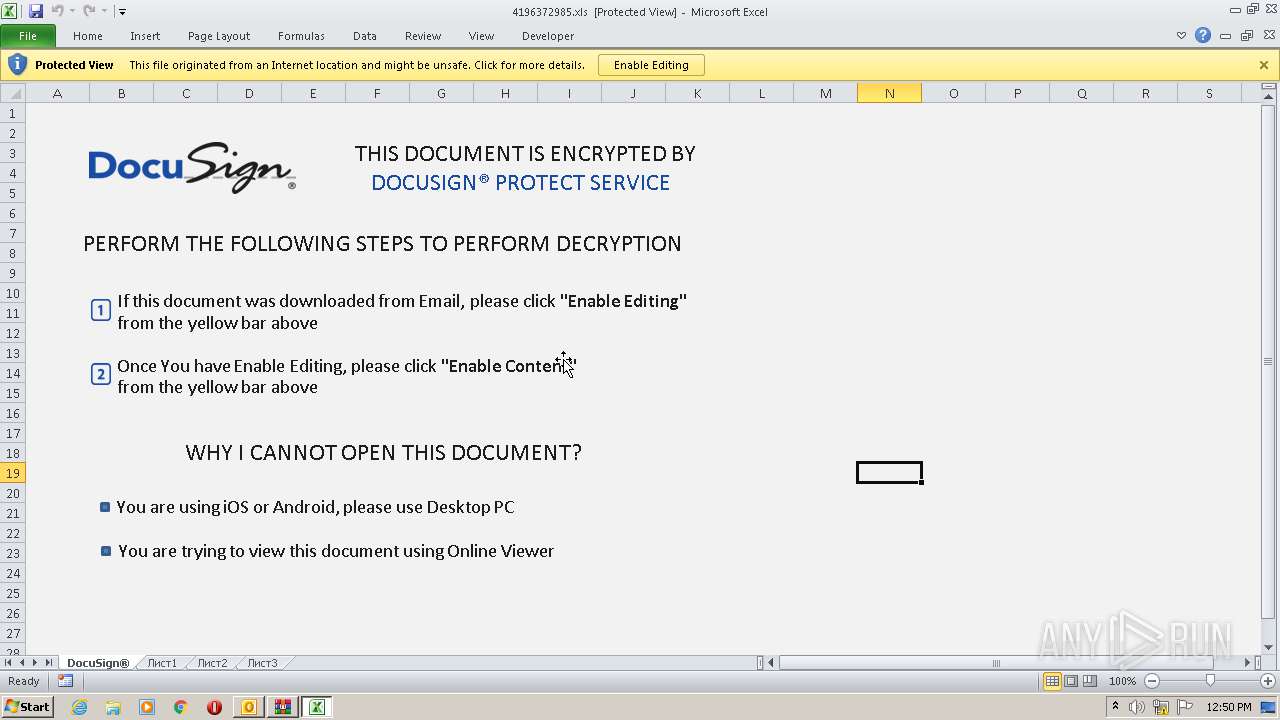
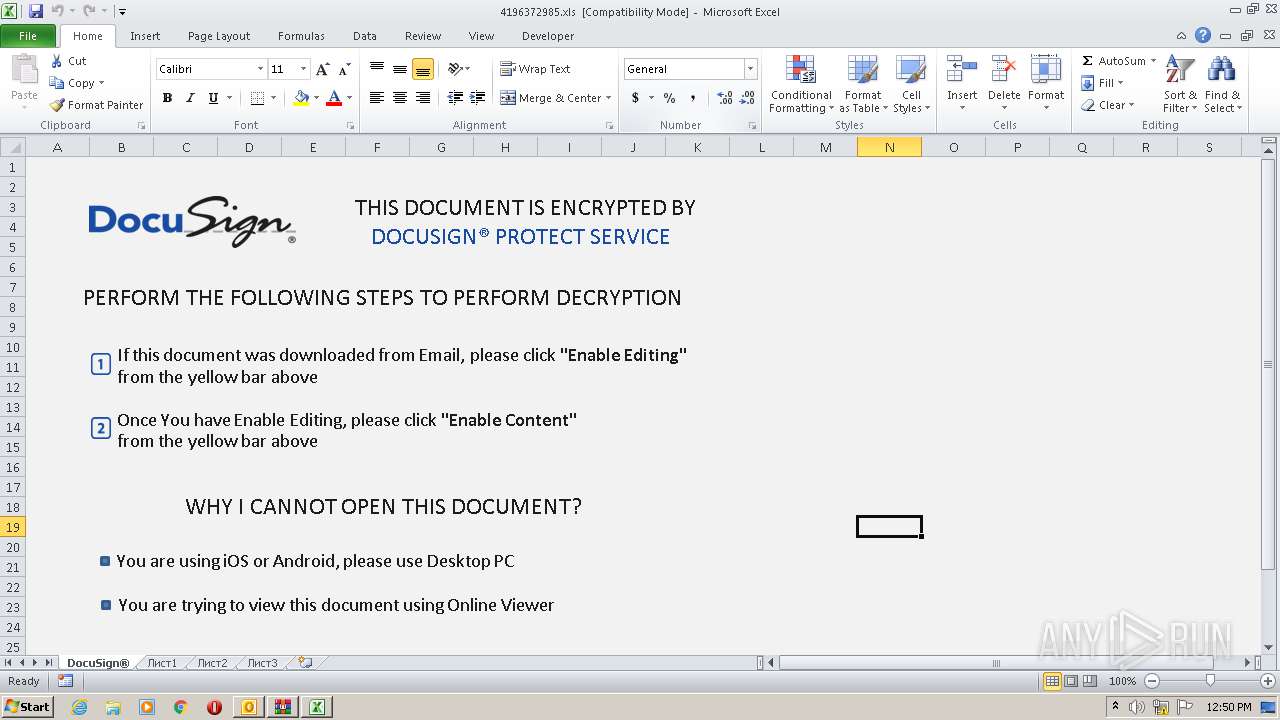
MALICIOUS
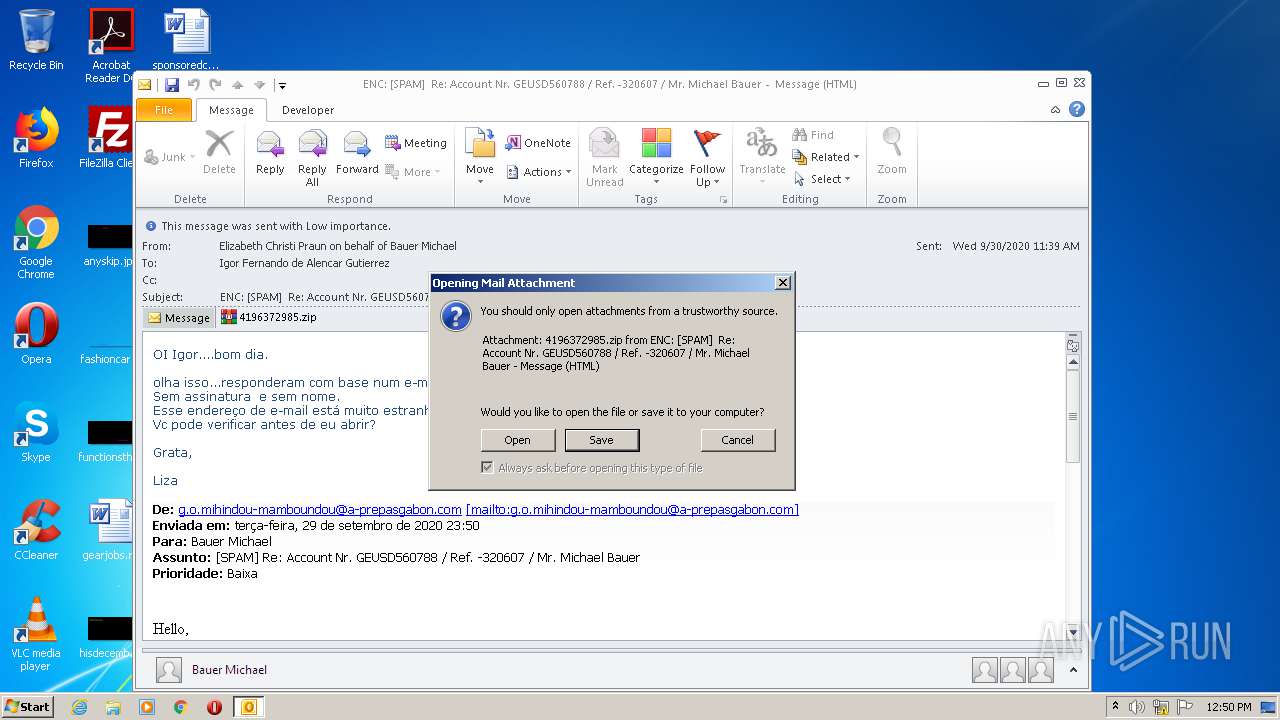
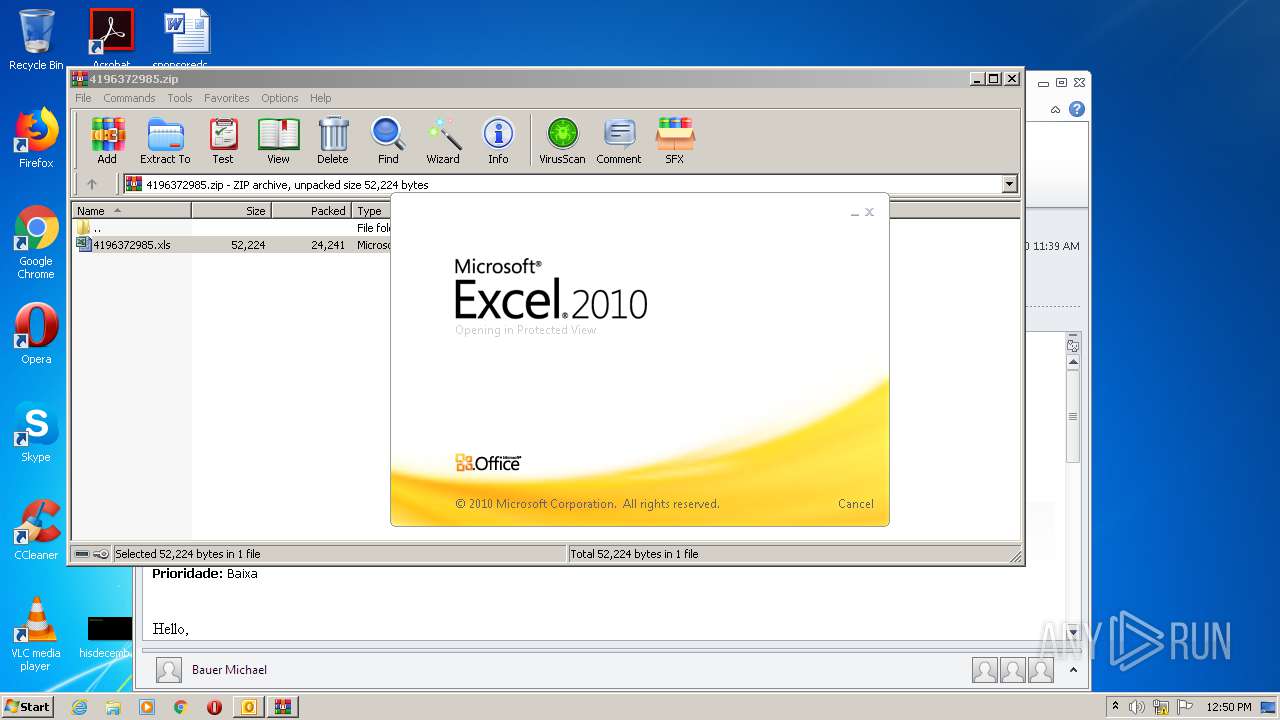
Unusual execution from Microsoft Office
- OUTLOOK.EXE (PID: 2208)
SUSPICIOUS
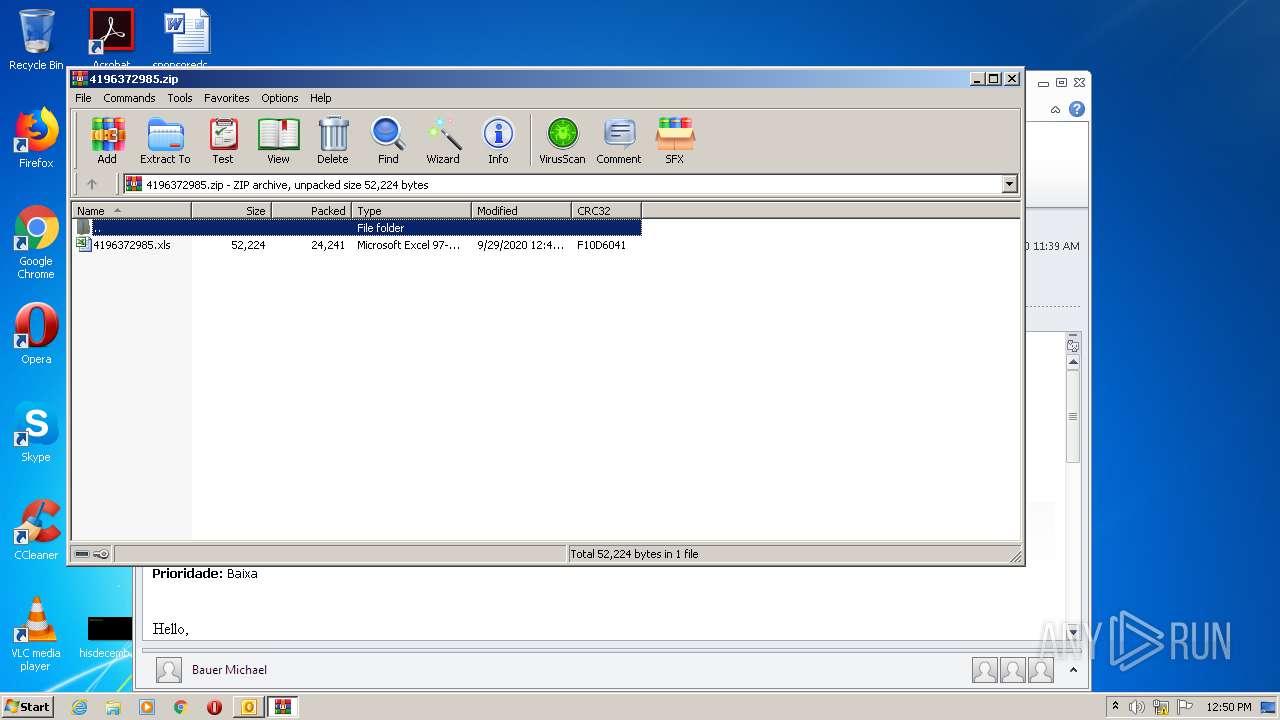
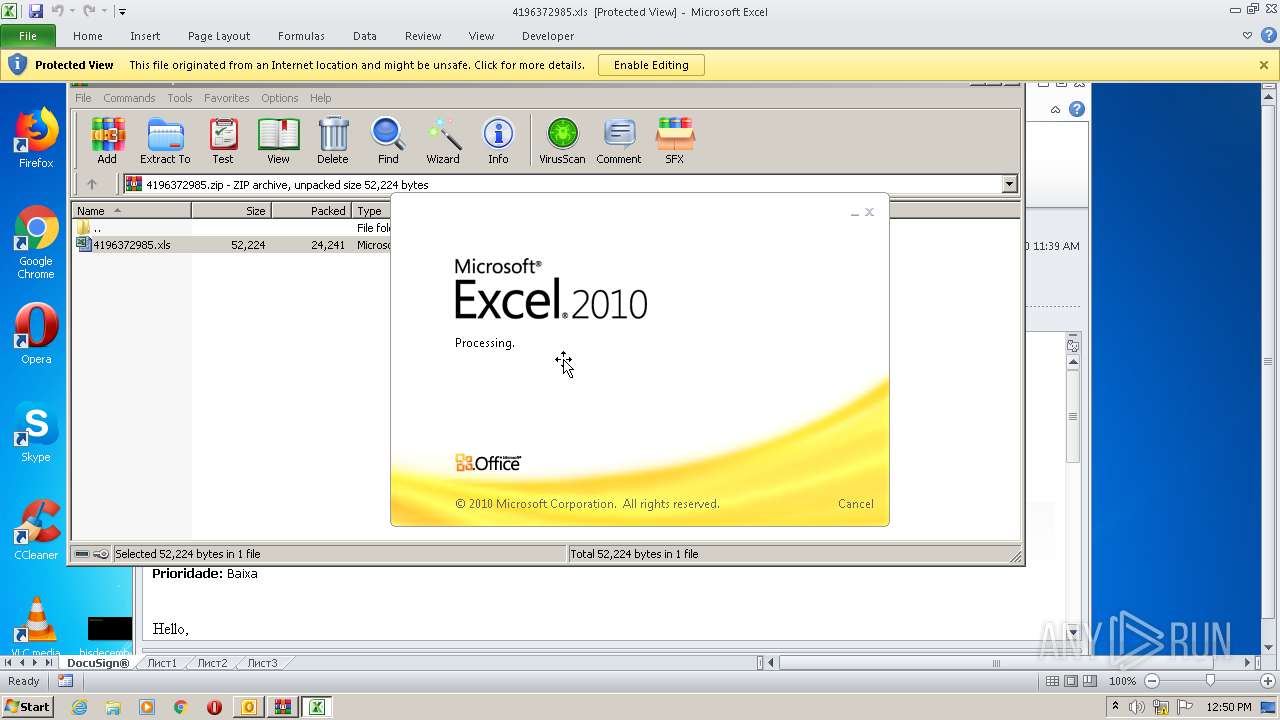
Starts Microsoft Office Application
- WinRAR.exe (PID: 2964)
- EXCEL.EXE (PID: 2140)
Creates files in the user directory
- OUTLOOK.EXE (PID: 2208)
Application launched itself
- EXCEL.EXE (PID: 2140)
INFO
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 2208)
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 2140)
- EXCEL.EXE (PID: 1540)
- OUTLOOK.EXE (PID: 2208)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
39
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1540 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | EXCEL.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
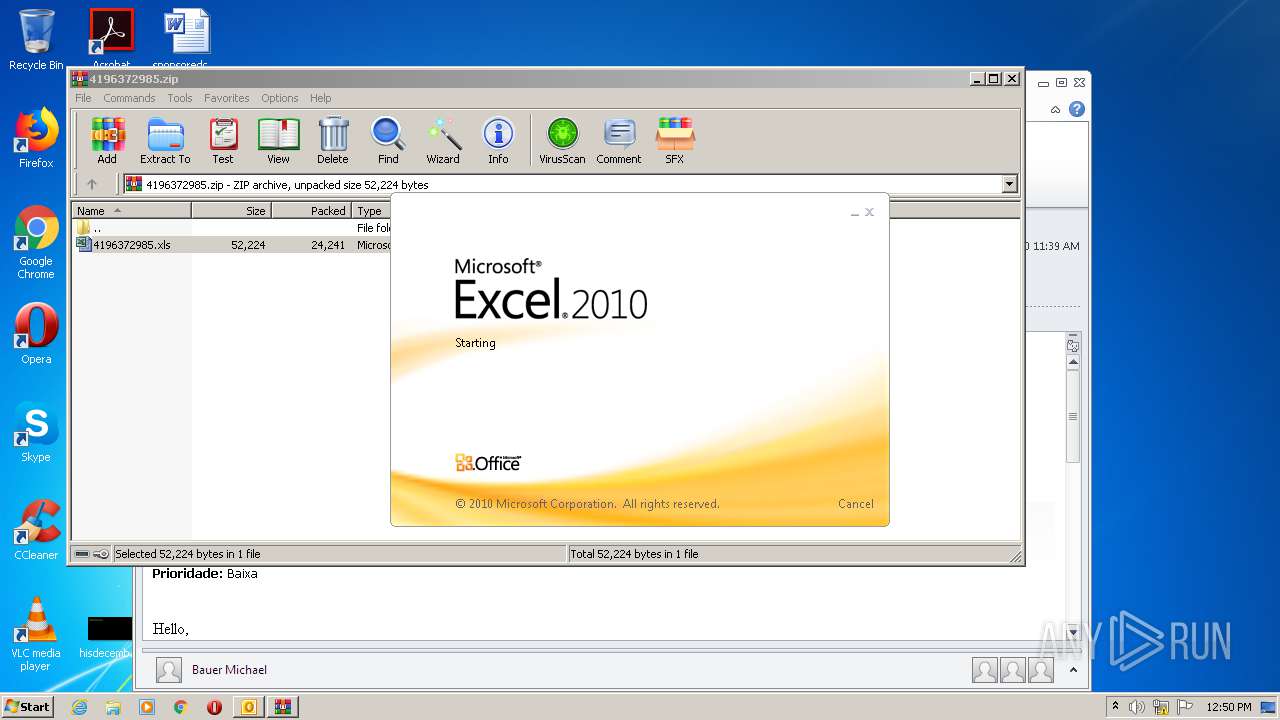
| 2140 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2208 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\ENC SPAM Re Account Nr. GEUSD560788 Ref. -320607 Mr. Michael Bauer.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
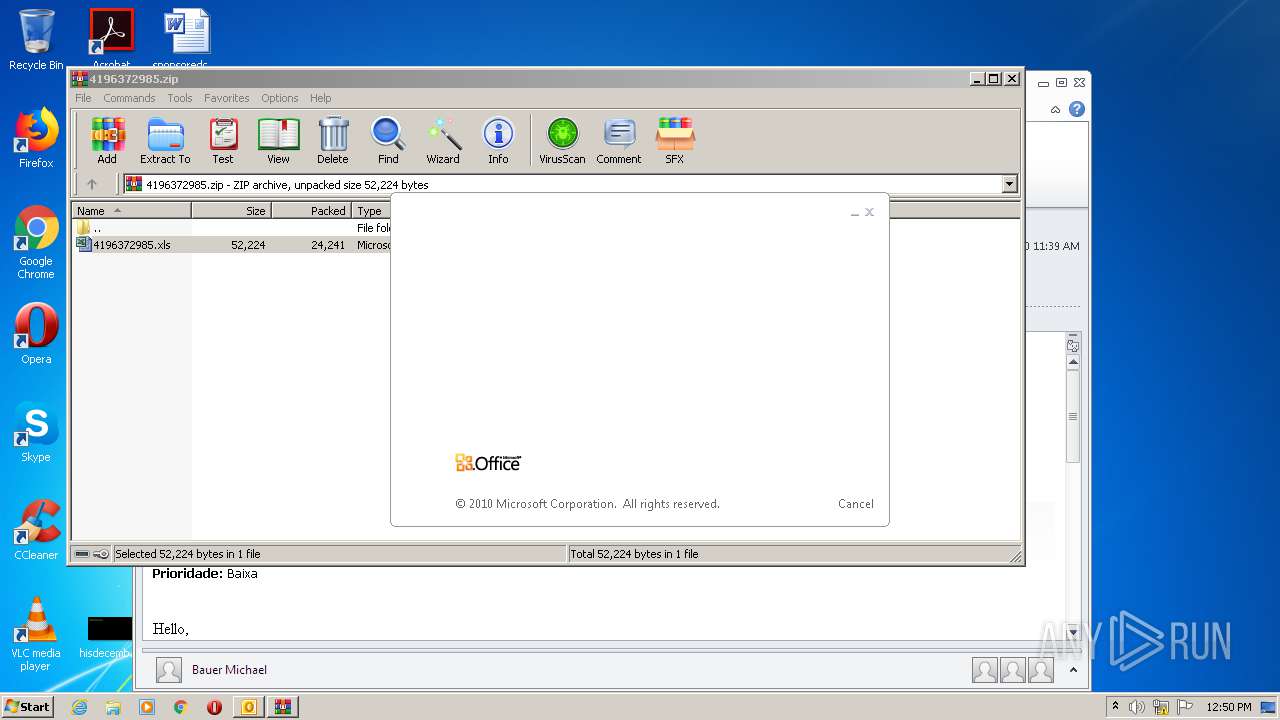
| 2964 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\CJHA5SZY\4196372985.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
3 422
Read events
2 756
Write events
628
Delete events
38
Modification events
| (PID) Process: | (2208) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2208) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2208) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2208) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2208) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2208) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2208) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2208) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2208) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (2208) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
Executable files
0
Suspicious files
5
Text files
29
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2208 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR7669.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2208 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\CJHA5SZY\4196372985 (2).zip\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 2140 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVRB17E.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2140 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\~DF6CE03B33E7242893.TMP | — | |
MD5:— | SHA256:— | |||
| 2140 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\OICE_68EE7FDD-1F14-40D5-809E-BA8931E36FE5.0\ADE17E6D.xls\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 1540 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\OICE_68EE7FDD-1F14-40D5-809E-BA8931E36FE5.0\~DF39A05C3EC78B389C.TMP | — | |
MD5:— | SHA256:— | |||
| 1540 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\OICE_68EE7FDD-1F14-40D5-809E-BA8931E36FE5.0\~DF2C91B2CDA337AE5E.TMP | — | |
MD5:— | SHA256:— | |||
| 2208 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
| 2208 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2208 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\CJHA5SZY\4196372985.zip | compressed | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2208 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |