| File name: | u1902.exe |
| Full analysis: | https://app.any.run/tasks/f37c179d-1f82-44ff-99cb-9fd1afb70154 |
| Verdict: | Malicious activity |
| Analysis date: | March 22, 2021, 22:58:26 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | 48FE7B7C67BC65AAA1F0A1318B45A3B5 |
| SHA1: | 9C3756CC878A5C80EEECC376A66F985969AEAE76 |
| SHA256: | B4D77967038ACE1D5ABFCED3EAE4152C7EB3D04C18FF54DF17D4DF6591B94702 |
| SSDEEP: | 98304:6XTU15sTq7nCmrxd9Jozx9vdS3/IZRt8+6XmExMSbejtRUCNuOV3aFSp:Ea5sTwC9dS3KRtH62igRUwdaFc |
MALICIOUS
Changes internet zones settings
- u1902.exe (PID: 1868)
Application was dropped or rewritten from another process
- u.exe (PID: 3532)
SUSPICIOUS
Executed via COM
- DllHost.exe (PID: 2820)
- DllHost.exe (PID: 2356)
Executable content was dropped or overwritten
- u1902.exe (PID: 1868)
Drops a file with too old compile date
- u1902.exe (PID: 1868)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (39.3) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (38.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (9.5) |
| .exe | | | Win32 Executable (generic) (6.5) |
| .exe | | | Generic Win/DOS Executable (2.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:02:12 09:13:16+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 3665920 |
| InitializedDataSize: | 12288 |
| UninitializedDataSize: | 1306624 |
| EntryPoint: | 0x4bec30 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 12-Feb-2019 08:13:16 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 12-Feb-2019 08:13:16 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x0013F000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x00140000 | 0x0037F000 | 0x0037EE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.81989 |
.rsrc | 0x004BF000 | 0x00003000 | 0x00002400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.66596 |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.DLL |
NETAPI32.dll |
SHELL32.dll |
USER32.dll |
WININET.dll |
WINMM.dll |
WINSPOOL.DRV |
Total processes
41
Monitored processes
4
Malicious processes
1
Suspicious processes
0
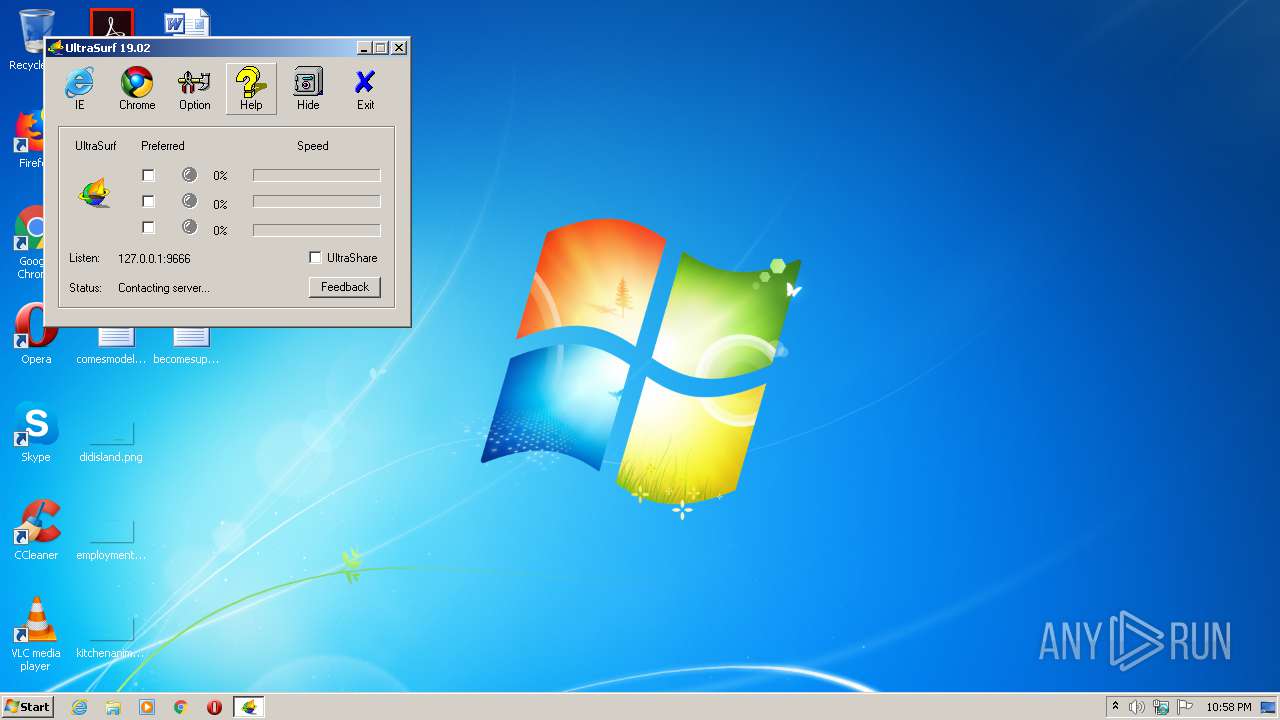
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1868 | "C:\Users\admin\AppData\Local\Temp\u1902.exe" | C:\Users\admin\AppData\Local\Temp\u1902.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2356 | C:\Windows\system32\DllHost.exe /Processid:{F9717507-6651-4EDB-BFF7-AE615179BCCF} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2820 | C:\Windows\system32\DllHost.exe /Processid:{F9717507-6651-4EDB-BFF7-AE615179BCCF} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3532 | C:\Users\admin\AppData\Local\Temp\utmp\u.exe -L="127.0.0.1:9666" -CID="18777450", -ProgPath="C:\Users\admin\AppData\Local\Temp\\" -TmpPath="C:\Users\admin\AppData\Local\Temp\utmp\\" -ConnMode=0 -version="1902100" | C:\Users\admin\AppData\Local\Temp\utmp\u.exe | u1902.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
218
Read events
101
Write events
100
Delete events
17
Modification events
| (PID) Process: | (1868) u1902.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (1868) u1902.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A5000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1868) u1902.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\MediaPlayer\Preferences |
| Operation: | write | Name: | UseHTTP |
Value: 1 | |||
| (PID) Process: | (1868) u1902.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\MediaPlayer\Preferences |
| Operation: | write | Name: | UseTCP |
Value: 0 | |||
| (PID) Process: | (1868) u1902.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\MediaPlayer\Preferences |
| Operation: | write | Name: | UseUDP |
Value: 0 | |||
| (PID) Process: | (1868) u1902.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\MediaPlayer\Preferences |
| Operation: | write | Name: | UseMulticast |
Value: 0 | |||
| (PID) Process: | (1868) u1902.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\MediaPlayer\Preferences\ProxySettings\HTTP |
| Operation: | write | Name: | ProxyBypass |
Value: 0 | |||
| (PID) Process: | (1868) u1902.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\MediaPlayer\Preferences\ProxySettings\HTTP |
| Operation: | write | Name: | ProxyStyle |
Value: 1 | |||
| (PID) Process: | (1868) u1902.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones\3 |
| Operation: | write | Name: | 1C00 |
Value: 00000000 | |||
| (PID) Process: | (1868) u1902.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones\3 |
| Operation: | write | Name: | CurrentLevel |
Value: 00000000 | |||
Executable files
1
Suspicious files
4
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1868 | u1902.exe | C:\Users\admin\AppData\Local\Temp\utmp\~mgtbrmtaa3v2c3p | binary | |
MD5:— | SHA256:— | |||
| 1868 | u1902.exe | C:\Users\admin\PUTTY.RND | binary | |
MD5:— | SHA256:— | |||
| 1868 | u1902.exe | C:\Users\admin\AppData\Local\Temp\utmp\~jtmteujzy8p5z9x | binary | |
MD5:— | SHA256:— | |||
| 1868 | u1902.exe | C:\Users\admin\AppData\Local\Temp\utmp\~grdccewps6k6s5x | binary | |
MD5:— | SHA256:— | |||
| 1868 | u1902.exe | C:\Users\admin\AppData\Local\Temp\utmp\u.exe | executable | |
MD5:6F39F6931A136376C66289970639A50C | SHA256:0217F1F5E59CD1459665D7B1B89D1C21B1F414D8FD37A50CAA7D760FB83B9D10 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
11
DNS requests
6
Threats
3
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3532 | u.exe | 152.199.19.160:443 | ajax.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3532 | u.exe | 172.217.18.101:443 | www.gmail.com | Google Inc. | US | whitelisted |
3532 | u.exe | 152.199.19.161:443 | do.skype.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
— | — | 143.204.209.12:443 | www.tsx.com | — | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ajax.microsoft.com |
| whitelisted |
www.gmail.com |
| shared |
do.skype.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
mail.google.com |
| shared |
www.tsx.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3532 | u.exe | Potential Corporate Privacy Violation | POLICY [PTsecurity] Possible JA3 UltraSurf Proxy Anonymizer |
3532 | u.exe | Potential Corporate Privacy Violation | POLICY [PTsecurity] Possible JA3 UltraSurf Proxy Anonymizer |
3532 | u.exe | Potential Corporate Privacy Violation | POLICY [PTsecurity] Possible JA3 UltraSurf Proxy Anonymizer |