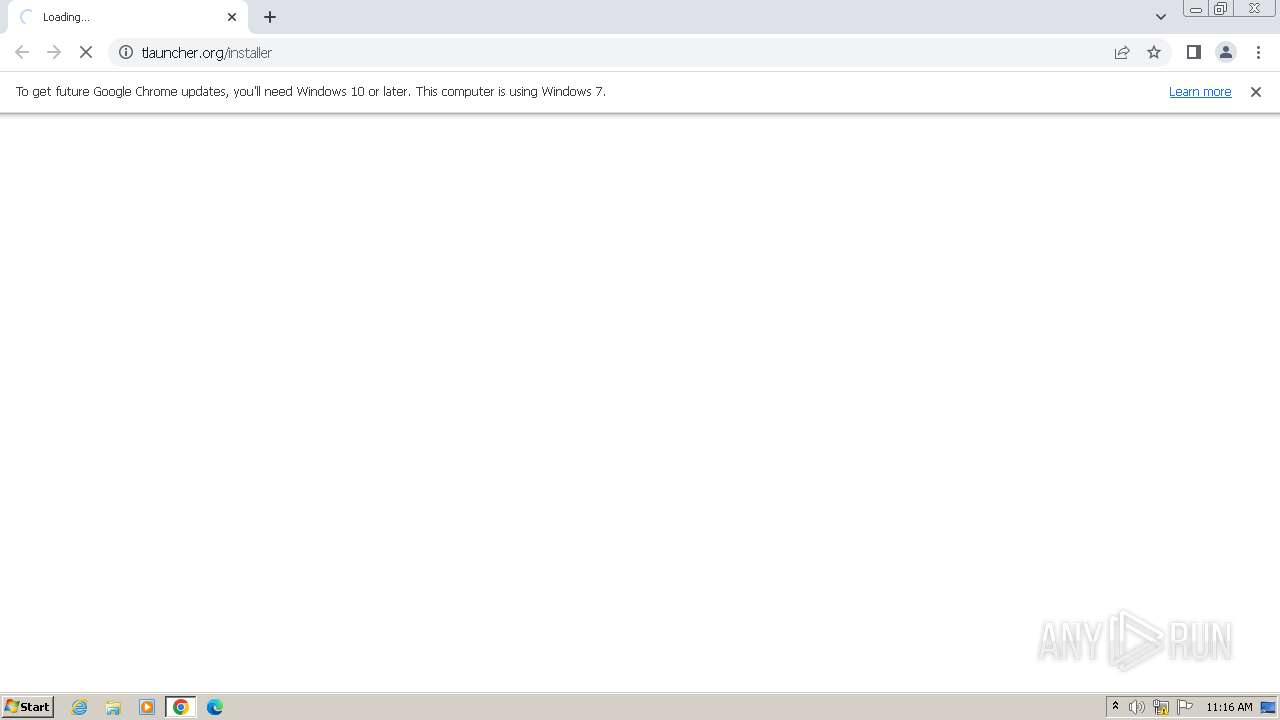
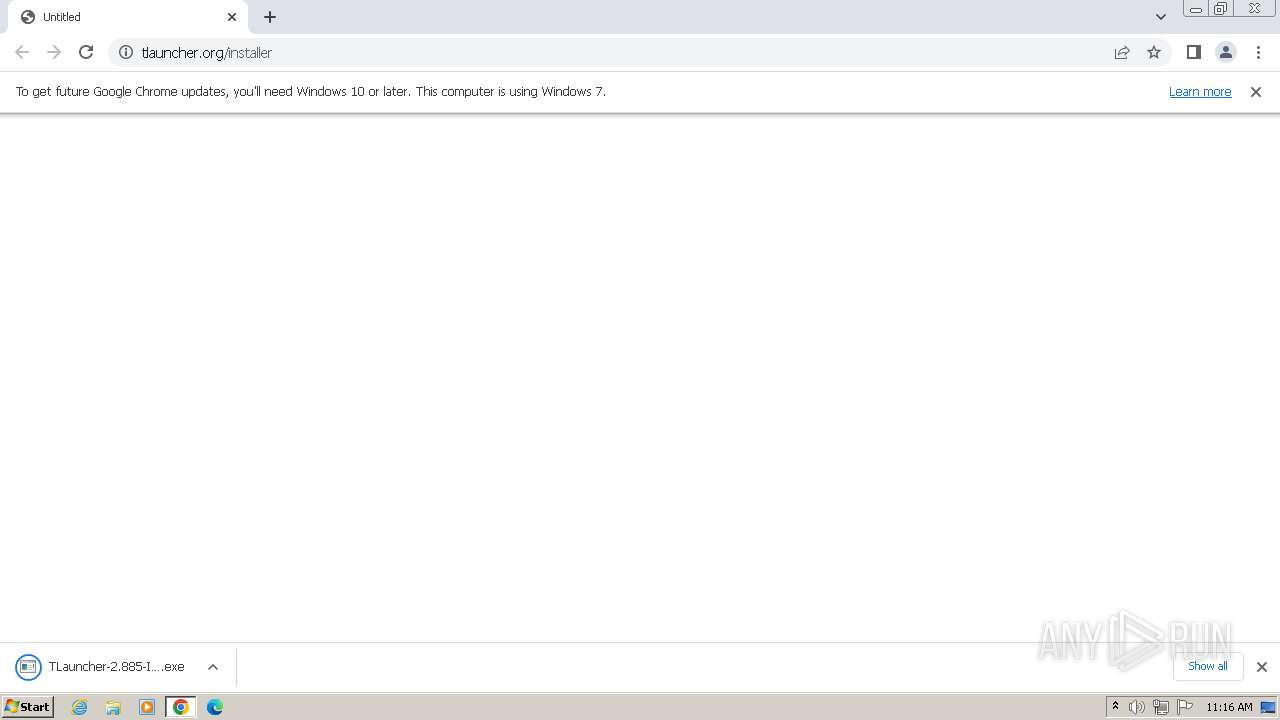
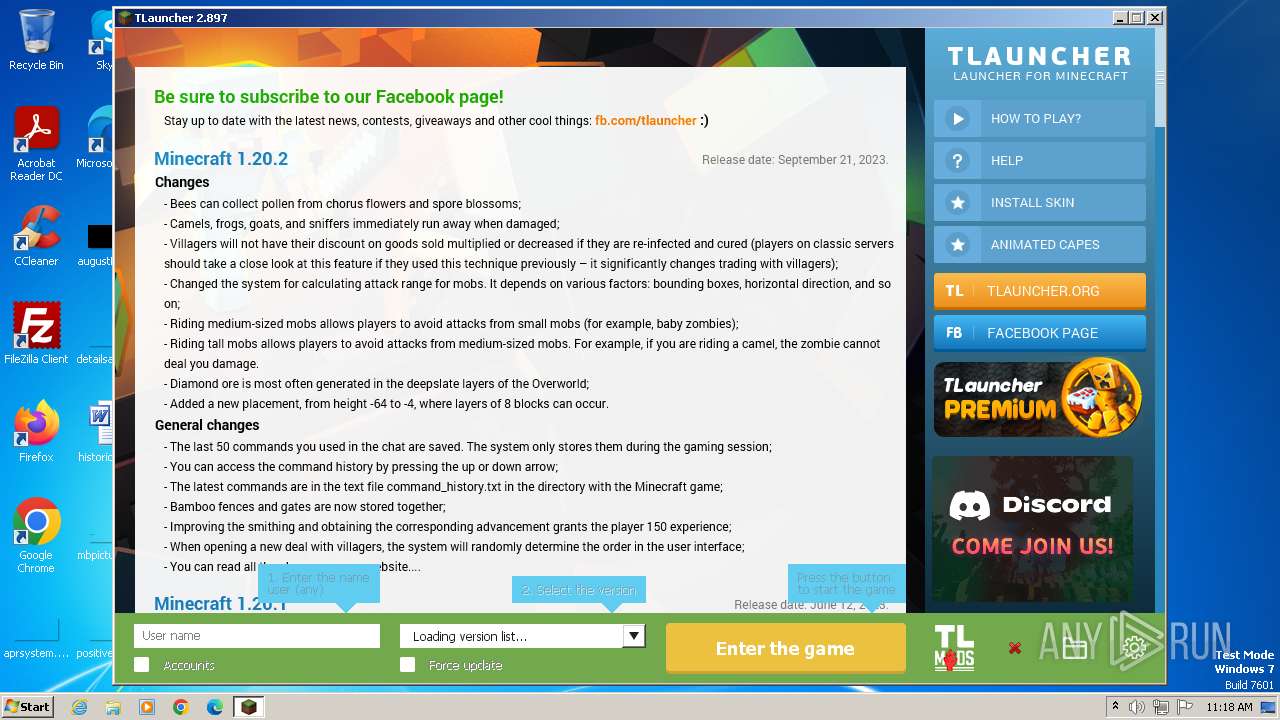
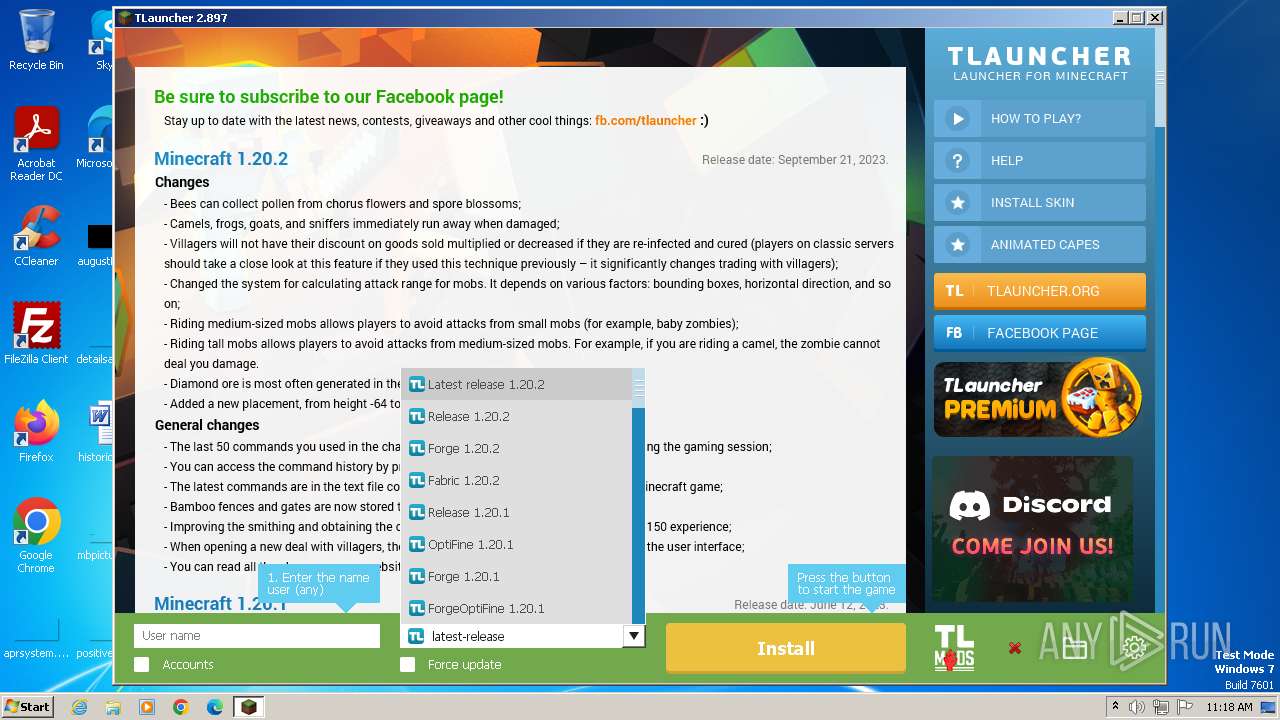
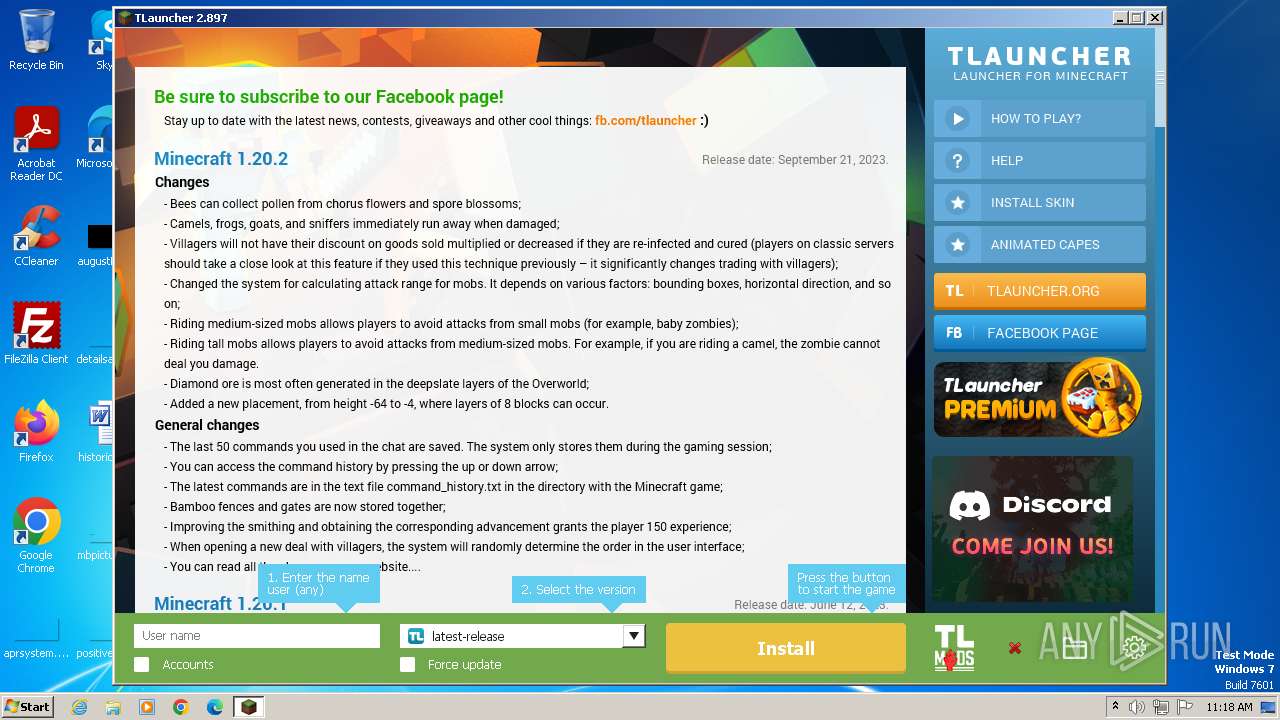
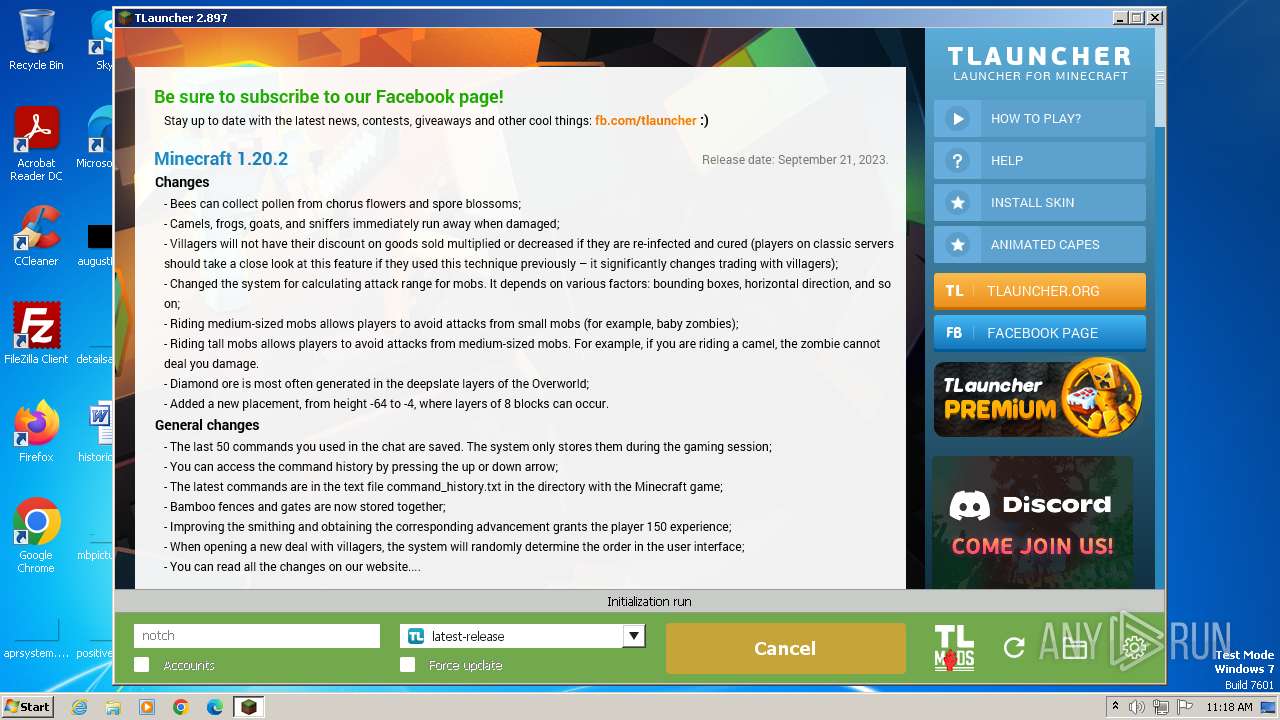
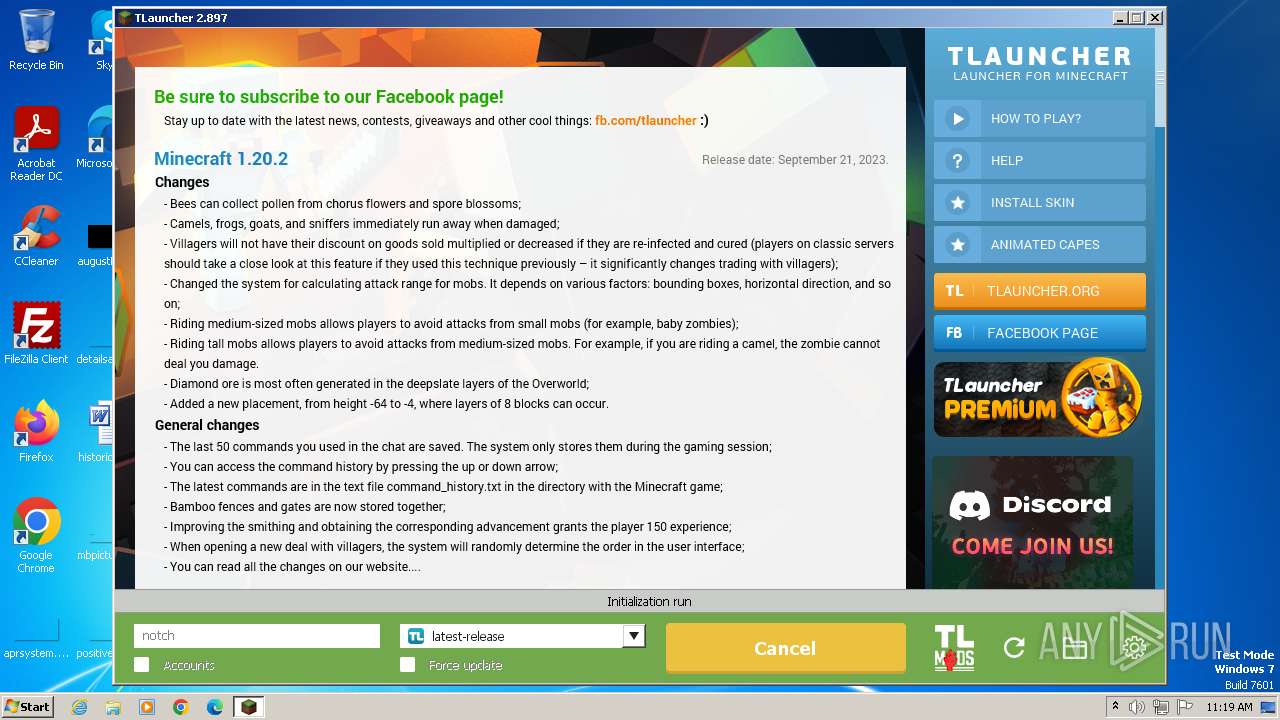
| URL: | https://tlauncher.org/installer |
| Full analysis: | https://app.any.run/tasks/bcf175a6-ae61-45d4-a244-5c8a28508f6b |
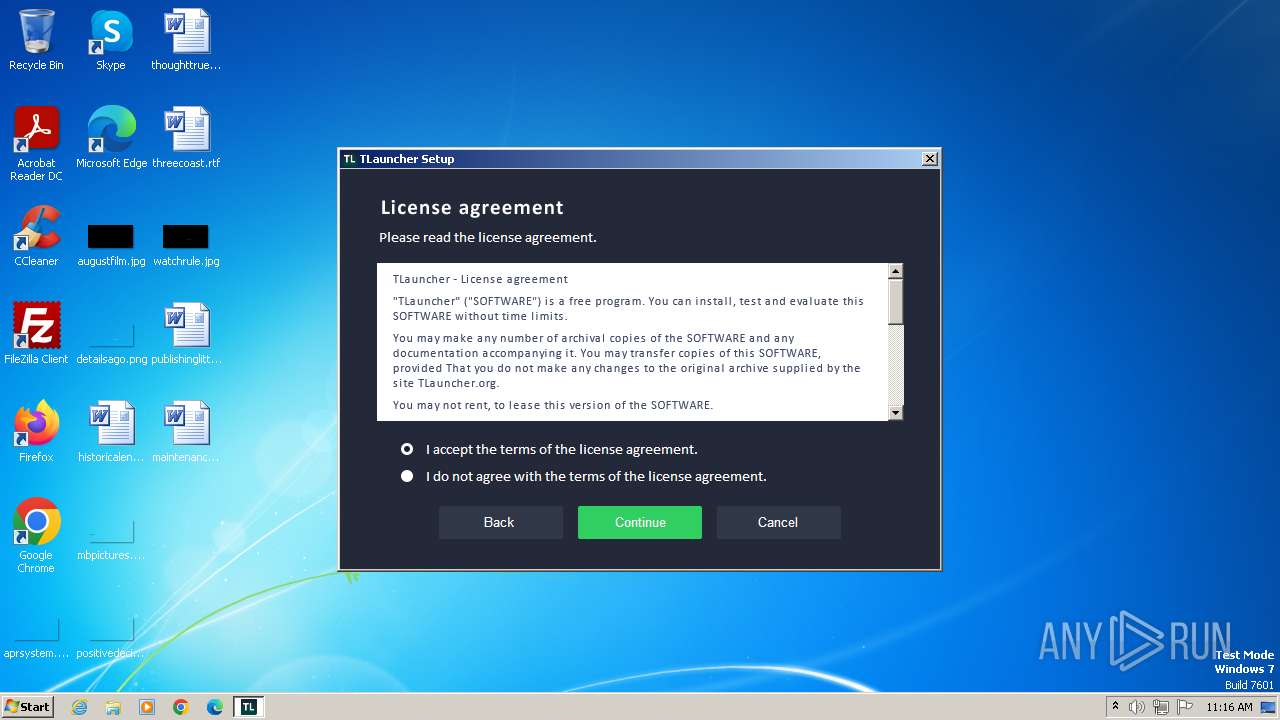
| Verdict: | Malicious activity |
| Analysis date: | December 01, 2023, 11:16:14 |
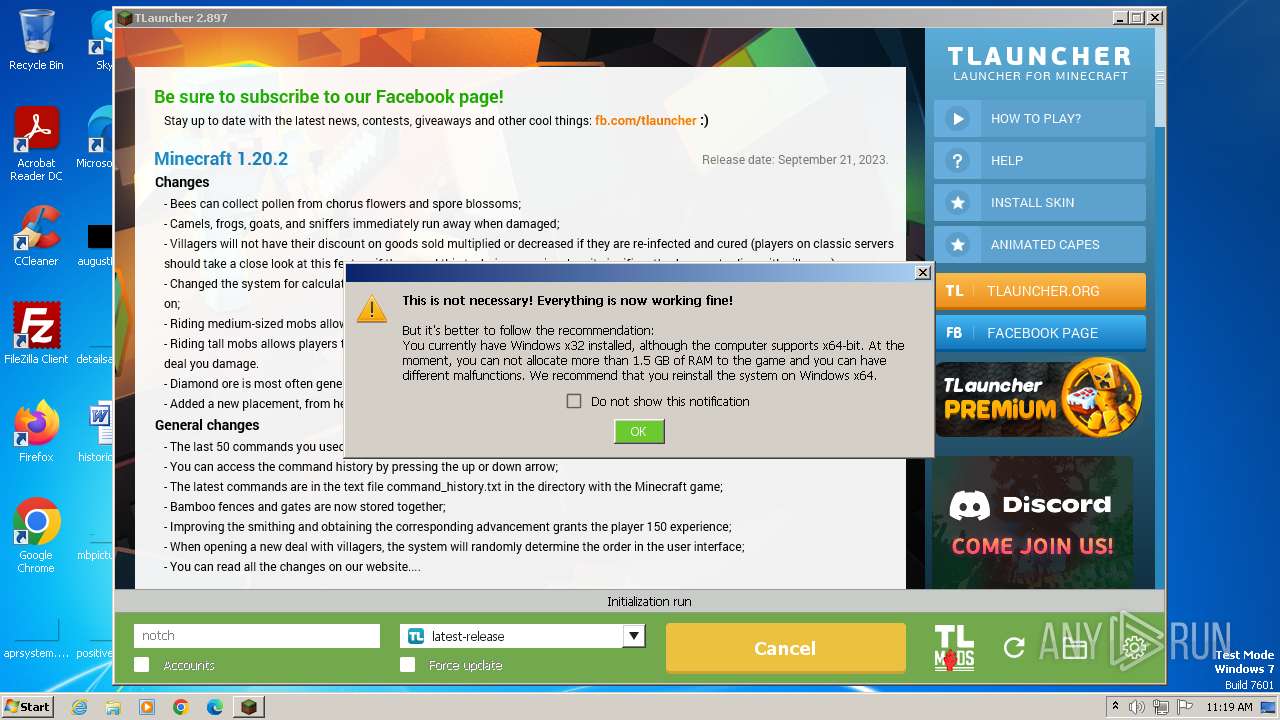
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | F5818708A23ED11C618056110D380758 |
| SHA1: | 54790604A2BD759EBCCAF7CCE7EFB49CE24FCEAA |
| SHA256: | B4C6549734FB3075A2AE0A3ED4106A25D1A79981A00321E959B20FDE6B4644BD |
| SSDEEP: | 3:N8BEeLu5MiqOXn:2K5kOXn |
MALICIOUS
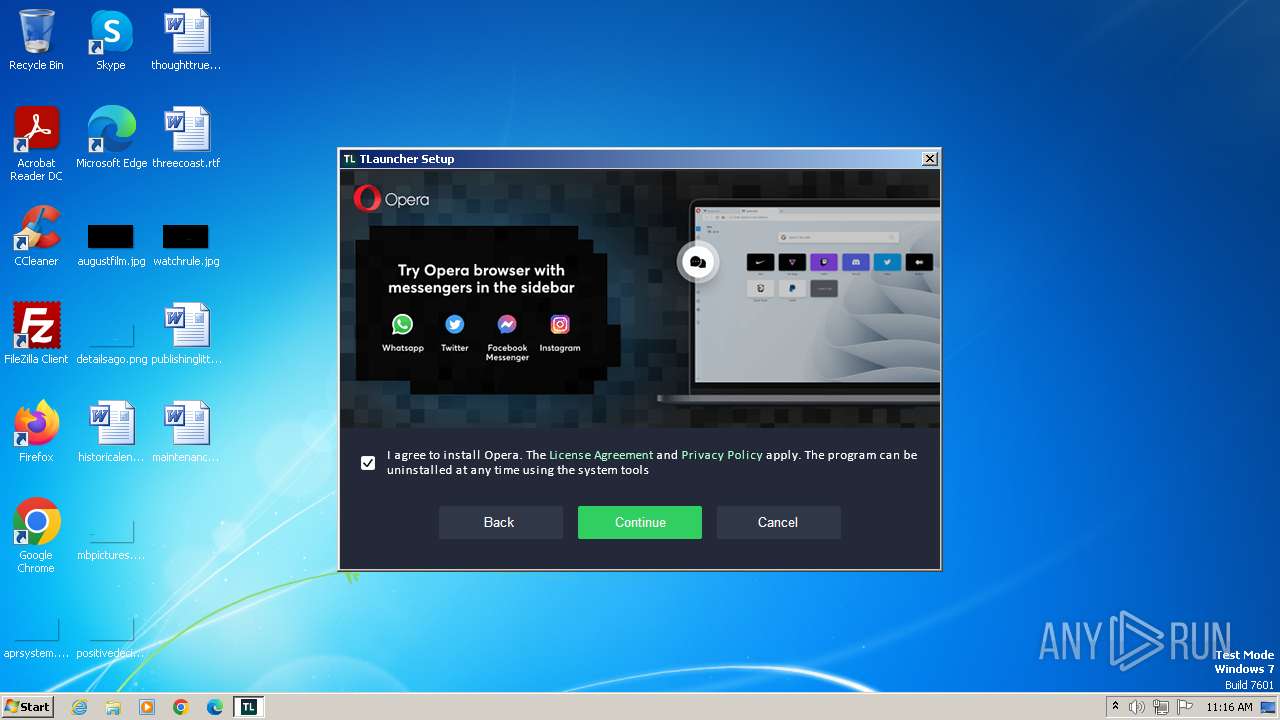
Drops the executable file immediately after the start
- TLauncher-2.885-Installer-1.1.3.exe (PID: 952)
- irsetup.exe (PID: 2436)
- BrowserInstaller.exe (PID: 3920)
- javaw.exe (PID: 3508)
- javaw.exe (PID: 3244)
Actions looks like stealing of personal data
- irsetup.exe (PID: 2436)
SUSPICIOUS
Process drops legitimate windows executable
- chrome.exe (PID: 3476)
- javaw.exe (PID: 3508)
- javaw.exe (PID: 3244)
Reads the Internet Settings
- TLauncher-2.885-Installer-1.1.3.exe (PID: 952)
- BrowserInstaller.exe (PID: 3920)
- irsetup.exe (PID: 2436)
- irsetup.exe (PID: 988)
- WMIC.exe (PID: 1784)
- WMIC.exe (PID: 1756)
- WMIC.exe (PID: 3168)
- WMIC.exe (PID: 644)
Reads the Windows owner or organization settings
- irsetup.exe (PID: 2436)
- irsetup.exe (PID: 988)
Reads settings of System Certificates
- irsetup.exe (PID: 2436)
- irsetup.exe (PID: 988)
- dxdiag.exe (PID: 2524)
Reads security settings of Internet Explorer
- irsetup.exe (PID: 2436)
- irsetup.exe (PID: 988)
Checks Windows Trust Settings
- irsetup.exe (PID: 2436)
- irsetup.exe (PID: 988)
Reads Microsoft Outlook installation path
- irsetup.exe (PID: 2436)
Checks for Java to be installed
- irsetup.exe (PID: 2436)
- TLauncher.exe (PID: 3668)
Reads Internet Explorer settings
- irsetup.exe (PID: 2436)
Uses WMIC.EXE to obtain operating system information
- cmd.exe (PID: 3812)
- cmd.exe (PID: 3052)
Process requests binary or script from the Internet
- javaw.exe (PID: 3508)
- javaw.exe (PID: 3244)
Starts application with an unusual extension
- cmd.exe (PID: 3052)
- cmd.exe (PID: 3812)
- cmd.exe (PID: 3272)
- cmd.exe (PID: 2404)
- cmd.exe (PID: 1036)
- cmd.exe (PID: 1116)
- cmd.exe (PID: 3100)
The process drops C-runtime libraries
- javaw.exe (PID: 3508)
- javaw.exe (PID: 3244)
Uses ICACLS.EXE to modify access control lists
- javaw.exe (PID: 3244)
Starts CMD.EXE for commands execution
- javaw.exe (PID: 3508)
- javaw.exe (PID: 3244)
Adds/modifies Windows certificates
- irsetup.exe (PID: 2436)
Uses WMIC.EXE to obtain CPU information
- cmd.exe (PID: 2404)
Uses WMIC.EXE to obtain quick Fix Engineering (patches) data
- cmd.exe (PID: 3100)
The process creates files with name similar to system file names
- javaw.exe (PID: 3244)
INFO
Reads the computer name
- wmpnscfg.exe (PID: 2064)
- TLauncher-2.885-Installer-1.1.3.exe (PID: 952)
- irsetup.exe (PID: 2436)
- BrowserInstaller.exe (PID: 3920)
- irsetup.exe (PID: 988)
- javaw.exe (PID: 3508)
- javaw.exe (PID: 3244)
Checks supported languages
- wmpnscfg.exe (PID: 2064)
- TLauncher-2.885-Installer-1.1.3.exe (PID: 952)
- irsetup.exe (PID: 2436)
- BrowserInstaller.exe (PID: 3920)
- irsetup.exe (PID: 988)
- TLauncher.exe (PID: 3668)
- javaw.exe (PID: 3508)
- chcp.com (PID: 3640)
- javaw.exe (PID: 3244)
- chcp.com (PID: 916)
- chcp.com (PID: 1876)
- chcp.com (PID: 1860)
- chcp.com (PID: 3676)
- chcp.com (PID: 3784)
- chcp.com (PID: 2876)
Drops the executable file immediately after the start
- chrome.exe (PID: 3476)
Manual execution by a user
- wmpnscfg.exe (PID: 2064)
The process uses the downloaded file
- chrome.exe (PID: 2492)
- chrome.exe (PID: 3476)
- chrome.exe (PID: 3604)
- chrome.exe (PID: 2892)
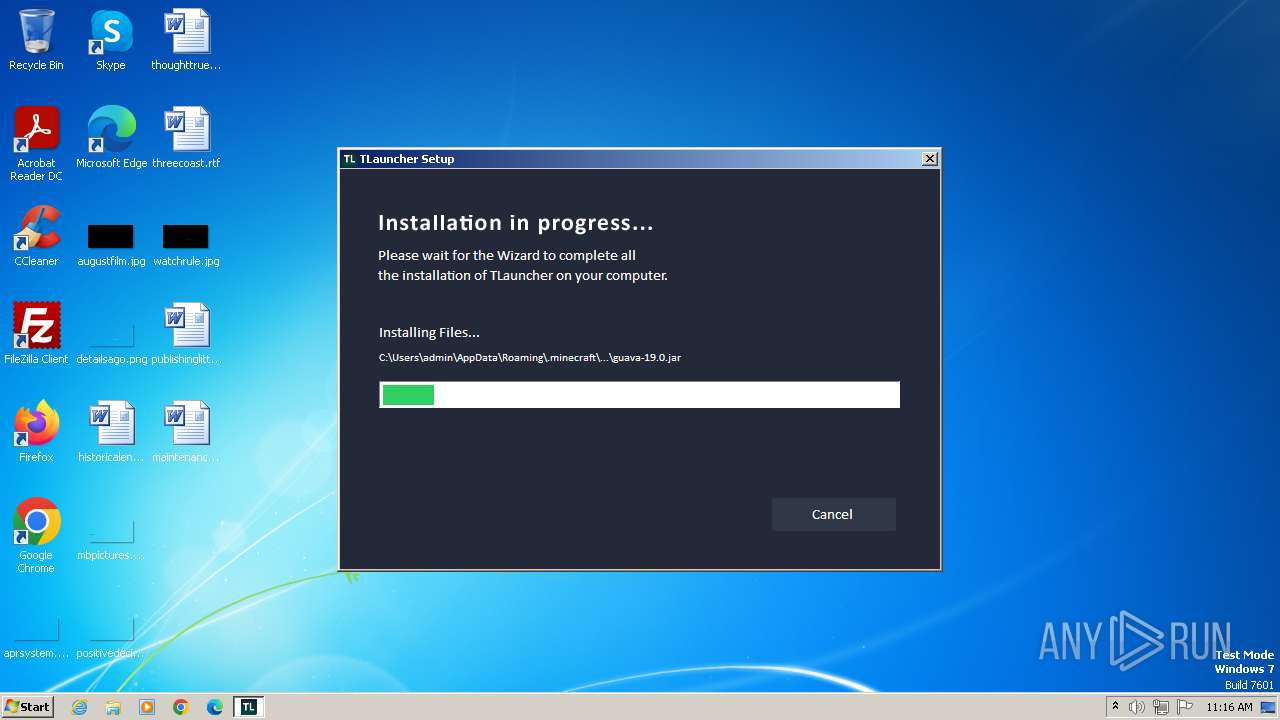
Create files in a temporary directory
- TLauncher-2.885-Installer-1.1.3.exe (PID: 952)
- irsetup.exe (PID: 2436)
- BrowserInstaller.exe (PID: 3920)
- irsetup.exe (PID: 988)
- javaw.exe (PID: 3508)
- javaw.exe (PID: 3244)
Application launched itself
- chrome.exe (PID: 3476)
Checks proxy server information
- irsetup.exe (PID: 988)
- irsetup.exe (PID: 2436)
Reads the machine GUID from the registry
- irsetup.exe (PID: 2436)
- irsetup.exe (PID: 988)
- javaw.exe (PID: 3508)
- javaw.exe (PID: 3244)
Creates files or folders in the user directory
- irsetup.exe (PID: 988)
- irsetup.exe (PID: 2436)
- javaw.exe (PID: 3508)
- javaw.exe (PID: 3244)
Creates files in the program directory
- irsetup.exe (PID: 2436)
- javaw.exe (PID: 3508)
- javaw.exe (PID: 3244)
Reads security settings of Internet Explorer
- dxdiag.exe (PID: 2524)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
107
Monitored processes
50
Malicious processes
9
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 644 | wmic qfe get HotFixID | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 916 | chcp 437 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Change CodePage Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
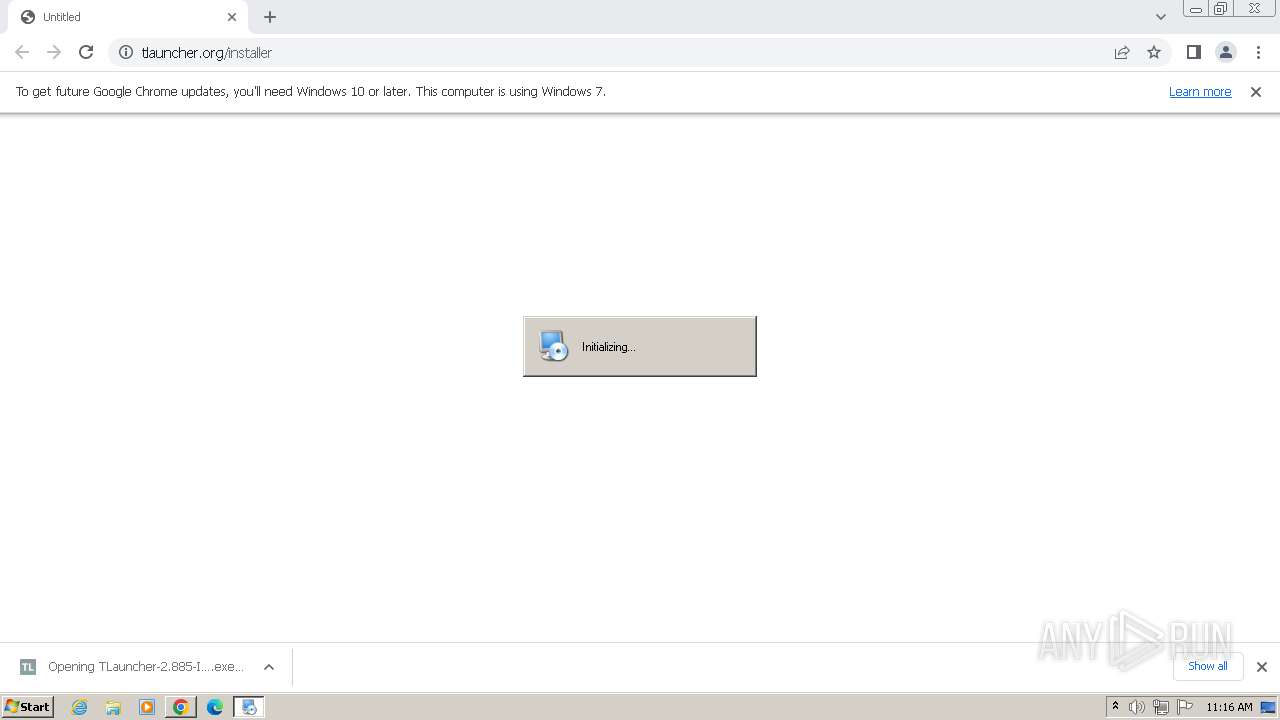
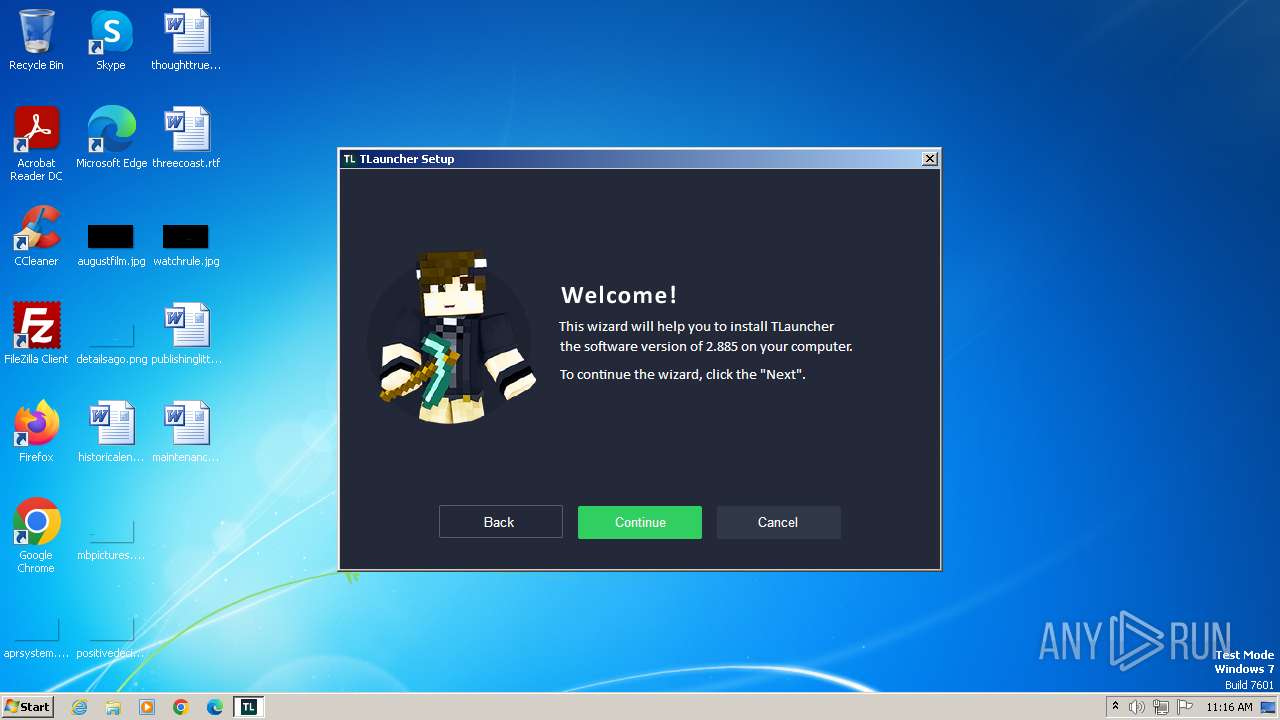
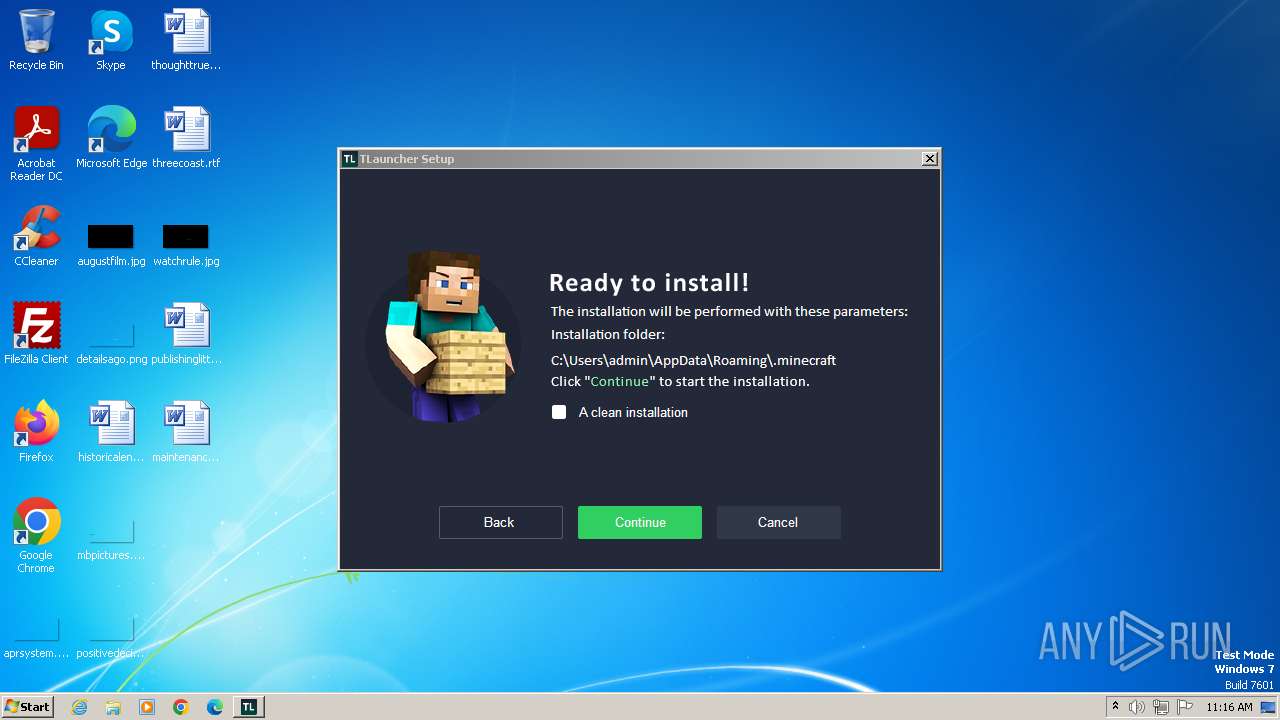
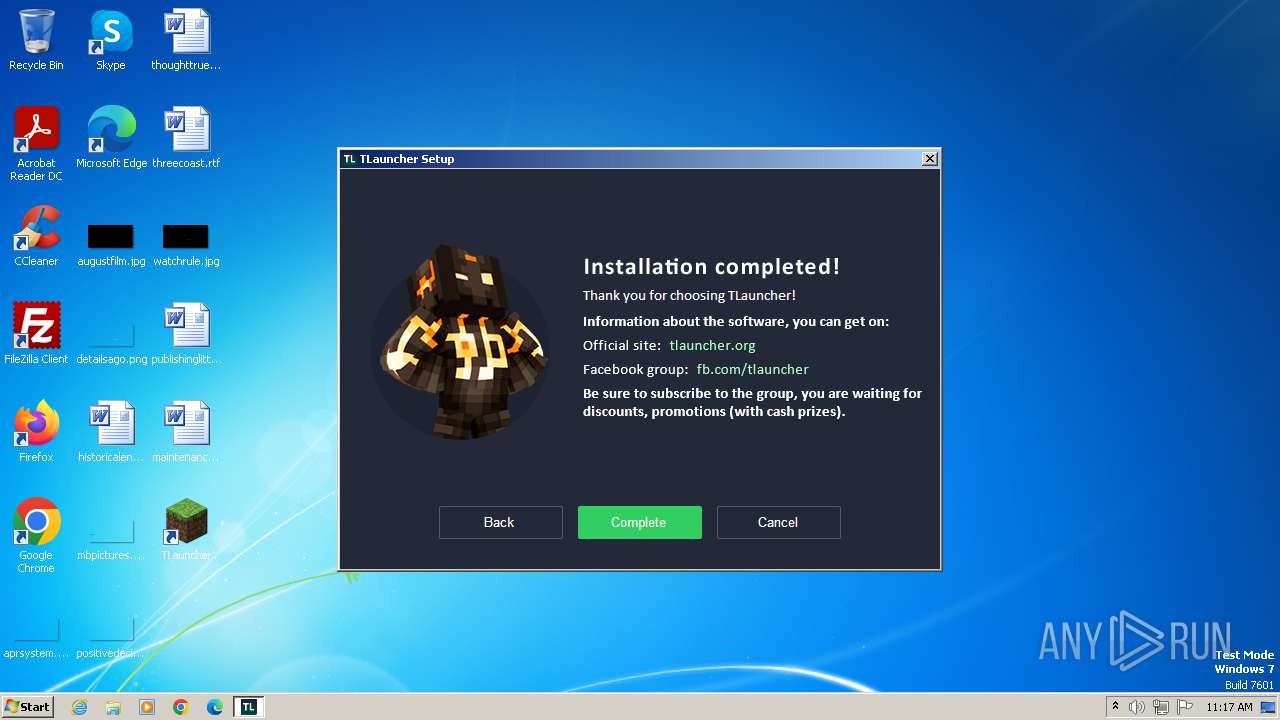
| 952 | "C:\Users\admin\Downloads\TLauncher-2.885-Installer-1.1.3.exe" | C:\Users\admin\Downloads\TLauncher-2.885-Installer-1.1.3.exe | chrome.exe | ||||||||||||
User: admin Company: TLauncher Inc. Integrity Level: HIGH Description: TLauncher Setup Exit code: 0 Version: 1.1.3.0 Modules
| |||||||||||||||
| 988 | "C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_1\irsetup.exe" /S:C:\Users\admin\AppData\Local\Temp\setuparguments.ini __IRAOFF:1816850 "__IRAFN:C:\Users\admin\AppData\Local\Temp\BrowserInstaller.exe" "__IRCT:3" "__IRTSS:1841988" "__IRSID:S-1-5-21-1302019708-1500728564-335382590-1000" | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_1\irsetup.exe | BrowserInstaller.exe | ||||||||||||
User: admin Company: Indigo Rose Corporation Integrity Level: HIGH Description: Setup Application Exit code: 0 Version: 9.5.3.0 Modules
| |||||||||||||||
| 1036 | cmd.exe /C chcp 437 & dxdiag /whql:off /t C:\Users\admin\AppData\Roaming\.minecraft\logs\tlauncher\dxdiag.txt | C:\Windows\System32\cmd.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1116 | cmd.exe /C chcp 437 & set processor | C:\Windows\System32\cmd.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1352 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --first-renderer-process --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=2000 --field-trial-handle=1096,i,18142086002633310574,16095521504409264859,131072 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1756 | wmic os get osarchitecture | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1784 | wmic os get osarchitecture | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1840 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=2020 --field-trial-handle=1096,i,18142086002633310574,16095521504409264859,131072 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
25 809
Read events
25 553
Write events
240
Delete events
16
Modification events
| (PID) Process: | (3476) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3476) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3476) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3476) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3476) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3476) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
| (PID) Process: | (3476) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3476) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3476) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
| (PID) Process: | (3476) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_enableddate |
Value: 0 | |||
Executable files
392
Suspicious files
833
Text files
1 139
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3476 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF2066cc.TMP | — | |
MD5:— | SHA256:— | |||
| 3476 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3476 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 3476 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:43550DBA2277BE44F5F842196E084145 | SHA256:D19055342C06316F8B80D0B029BD233A3E48AD4C591953AF7B712ADA7F68F403 | |||
| 3476 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 3476 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF2066cc.TMP | text | |
MD5:513218482935B0D388C0A990D868387A | SHA256:8E39CBAAF4AACC3A01AFA74EA8C30FB24FE69A22B8B30728AFB1614FD68809D9 | |||
| 3476 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\LOG.old~RF206fa6.TMP | — | |
MD5:— | SHA256:— | |||
| 3476 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3476 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:9F941EA08DBDCA2EB3CFA1DBBBA6F5DC | SHA256:127F71DF0D2AD895D4F293E62284D85971AE047CA15F90B87BF6335898B0B655 | |||
| 3476 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\266d74a9-8141-4516-9b40-f56205012d07.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
100
DNS requests
36
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
988 | irsetup.exe | GET | 200 | 104.18.21.226:80 | http://ocsp.globalsign.com/rootr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEH1NQqkrQx1%2BZFPnwZqNWHc%3D | unknown | binary | 1.41 Kb | unknown |
988 | irsetup.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?78fc474796997210 | unknown | compressed | 4.66 Kb | unknown |
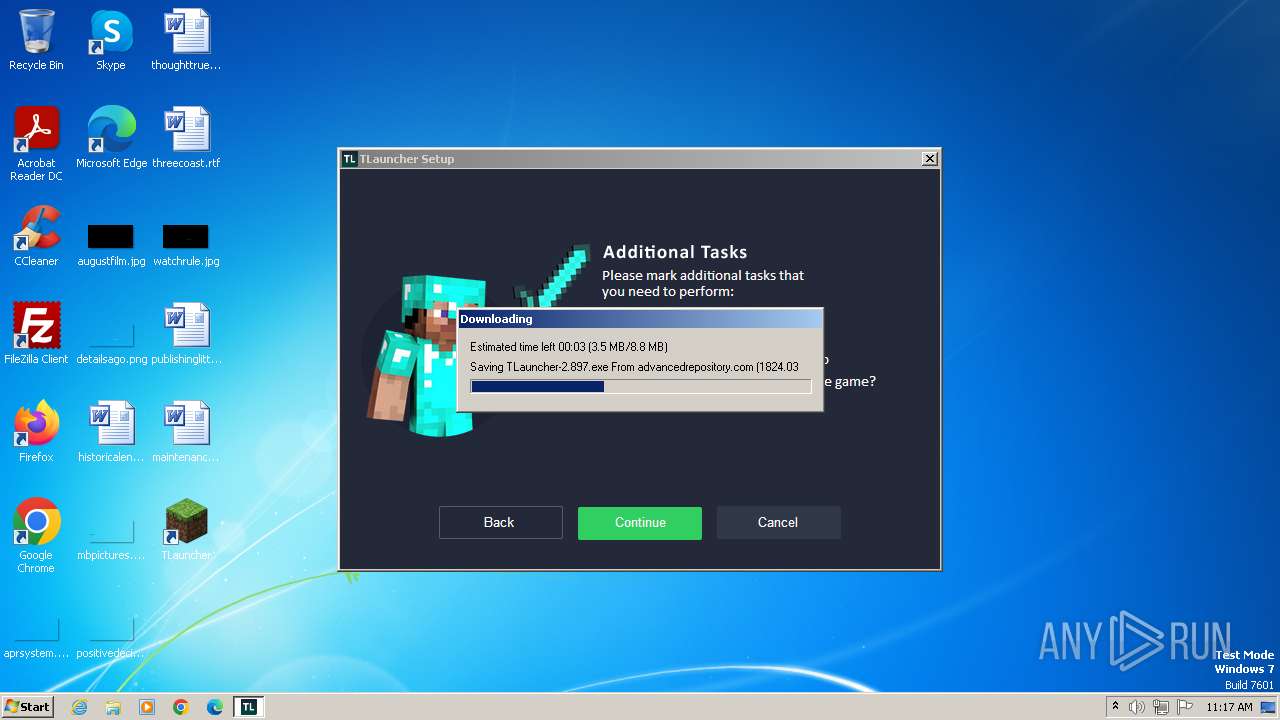
3508 | javaw.exe | GET | 302 | 78.46.66.120:80 | http://res.tlauncher.org/b/client/jre/windows/jre-8u111-windows-i586.tar.gz | unknown | — | — | unknown |
3508 | javaw.exe | GET | 302 | 78.46.66.120:80 | http://res.tlauncher.org/b/libraries/org/tlauncher/picture-bundle/3.72/picture-bundle-3.72.jar | unknown | — | — | unknown |
1080 | svchost.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?20da42ca9bb40799 | unknown | compressed | 65.2 Kb | unknown |
3244 | javaw.exe | GET | 200 | 104.20.234.70:80 | http://repo.tlauncher.org/update/downloads/configs/inner_servers-1.1.json | unknown | binary | 5.35 Kb | unknown |
3244 | javaw.exe | HEAD | 200 | 104.20.234.70:80 | http://page.tlauncher.org/ | unknown | — | — | unknown |
3244 | javaw.exe | GET | 200 | 104.26.4.134:80 | http://img.fastrepo.org/update/downloads/configs/client/video/tl-discord-en.png | unknown | image | 49.2 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3592 | chrome.exe | 142.250.186.173:443 | accounts.google.com | GOOGLE | US | unknown |
3476 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3592 | chrome.exe | 104.20.235.70:443 | tlauncher.org | CLOUDFLARENET | — | unknown |
3476 | chrome.exe | 224.0.0.251:5353 | — | — | — | unknown |
3592 | chrome.exe | 216.58.212.164:443 | www.google.com | GOOGLE | US | whitelisted |
3592 | chrome.exe | 172.217.20.74:443 | optimizationguide-pa.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
tlauncher.org |
| unknown |
dl2.tlauncher.org |
| unknown |
www.google.com |
| whitelisted |
optimizationguide-pa.googleapis.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.globalsign.com |
| whitelisted |
advancedrepository.com |
| unknown |
res.tlauncher.org |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3508 | javaw.exe | Potentially Bad Traffic | ET POLICY Vulnerable Java Version 1.8.x Detected |
3508 | javaw.exe | Potentially Bad Traffic | ET POLICY Vulnerable Java Version 1.8.x Detected |