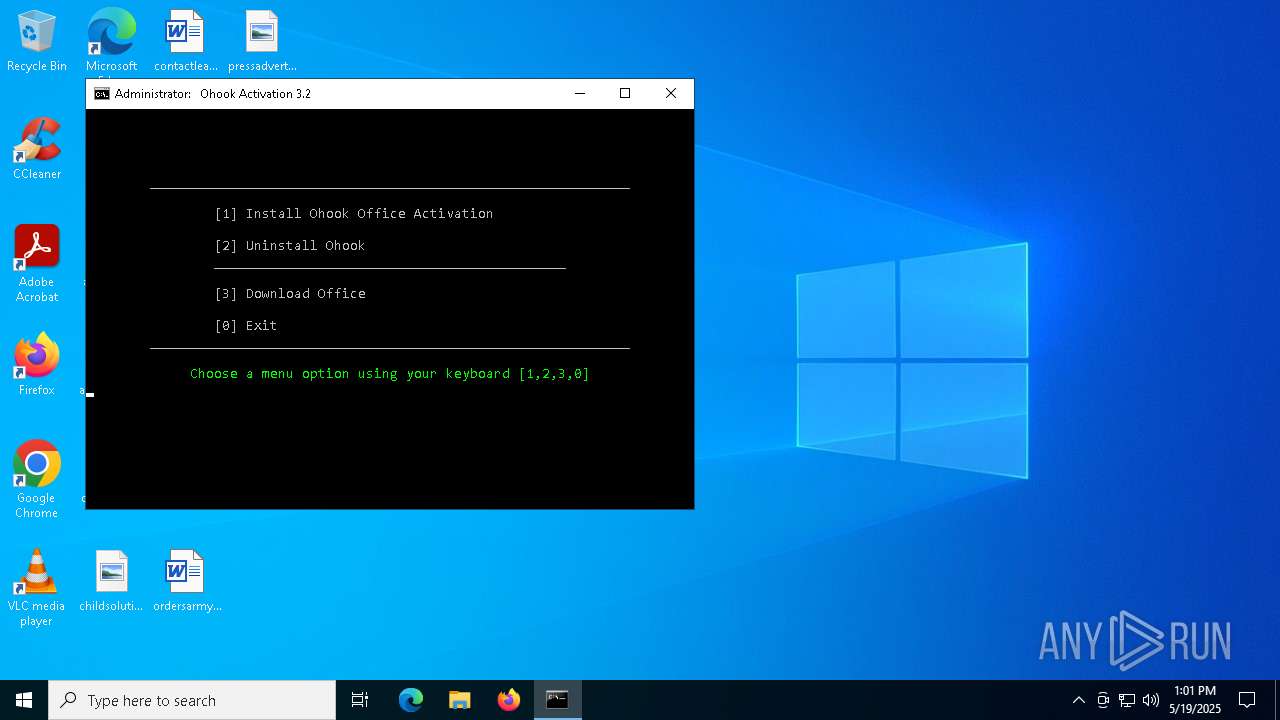
| File name: | Ohook_Activation_AIO.cmd |
| Full analysis: | https://app.any.run/tasks/9a785329-f63d-4c1c-8309-6909d9e03d23 |
| Verdict: | Malicious activity |
| Analysis date: | May 19, 2025, 13:01:28 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | text/x-msdos-batch |
| File info: | DOS batch file, ASCII text, with very long lines (452), with CRLF line terminators |
| MD5: | 6E407B8D41B4F26441B7E40CB41CEFD3 |
| SHA1: | 78479E6B450C2162068D4EEEDE114E1B672F9E64 |
| SHA256: | B4C2005DD3C46BFD7C3B9A2C2CFB4CF38729C889981B6BA4898C93098C587F07 |
| SSDEEP: | 3072:mk/z/N/lb5/bqnaVnI/uICKv2xcGyMZgnnwT:7Bq2jIWY5Q |
MALICIOUS
No malicious indicators.SUSPICIOUS
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 7440)
- cmd.exe (PID: 8028)
- cmd.exe (PID: 4268)
- cmd.exe (PID: 7996)
Starts SC.EXE for service management
- cmd.exe (PID: 7440)
- cmd.exe (PID: 8028)
- cmd.exe (PID: 4268)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 7440)
- cmd.exe (PID: 7668)
- powershell.exe (PID: 7796)
- cmd.exe (PID: 8028)
- cmd.exe (PID: 5408)
- cmd.exe (PID: 7628)
- cmd.exe (PID: 4268)
Windows service management via SC.EXE
- sc.exe (PID: 7504)
- sc.exe (PID: 8168)
- sc.exe (PID: 7436)
Application launched itself
- cmd.exe (PID: 7440)
- cmd.exe (PID: 7668)
- cmd.exe (PID: 8028)
- cmd.exe (PID: 5408)
- cmd.exe (PID: 7628)
- cmd.exe (PID: 4268)
Executing commands from a ".bat" file
- cmd.exe (PID: 7440)
- powershell.exe (PID: 7796)
- cmd.exe (PID: 8028)
- cmd.exe (PID: 4268)
Executing commands from ".cmd" file
- cmd.exe (PID: 7440)
- powershell.exe (PID: 7796)
- cmd.exe (PID: 8028)
- cmd.exe (PID: 4268)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 7440)
- cmd.exe (PID: 2088)
- cmd.exe (PID: 7784)
Executes script without checking the security policy
- powershell.exe (PID: 7796)
- powershell.exe (PID: 4408)
- powershell.exe (PID: 7868)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 7440)
- cmd.exe (PID: 2088)
- cmd.exe (PID: 7784)
Hides command output
- cmd.exe (PID: 2088)
- cmd.exe (PID: 7784)
- cmd.exe (PID: 7996)
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 2088)
- cmd.exe (PID: 7784)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 2088)
- cmd.exe (PID: 7784)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 8028)
Get information on the list of running processes
- cmd.exe (PID: 4268)
- cmd.exe (PID: 7996)
INFO
Checks operating system version
- cmd.exe (PID: 7440)
- cmd.exe (PID: 8028)
- cmd.exe (PID: 4268)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 4408)
- powershell.exe (PID: 7868)
Starts MODE.COM to configure console settings
- mode.com (PID: 672)
- mode.com (PID: 6080)
- mode.com (PID: 7020)
Checks supported languages
- mode.com (PID: 672)
- mode.com (PID: 6080)
- mode.com (PID: 7020)
Checks proxy server information
- slui.exe (PID: 5680)
Reads the software policy settings
- slui.exe (PID: 5680)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .bib/bibtex/txt | | | BibTeX references (100) |
|---|
Total processes
224
Monitored processes
96
Malicious processes
4
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 496 | C:\WINDOWS\System32\cmd.exe /S /D /c" echo -smss.exe- -csrss.exe- -wininit.exe- -services.exe- -lsass.exe- -svchost.exe- -fontdrvhost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -spoolsv.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -dasHost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -OfficeClickToRun.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -dllhost.exe- -svchost.exe- -MoUsoCoreWorker.exe- -svchost.exe- -svchost.exe- -svchost.exe- -uhssvc.exe- -svchost.exe- -svchost.exe- -csrss.exe- -winlogon.exe- -fontdrvhost.exe- -dwm.exe- -sihost.exe- -svchost.exe- -svchost.exe- -explorer.exe- -svchost.exe- -dllhost.exe- -RuntimeBroker.exe- -SearchApp.exe- -RuntimeBroker.exe- -ctfmon.exe- -RuntimeBroker.exe- -SystemSettings.exe- -ApplicationFrameHost.exe- -UserOOBEBroker.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -TextInputHost.exe- -dllhost.exe- -audiodg.exe- -svchost.exe- -RuntimeBroker.exe- -svchost.exe- -RuntimeBroker.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -upfc.exe- -taskhostw.exe- -sppsvc.exe- -SppExtComObj.Exe- -slui.exe- -cmd.exe- -conhost.exe- -cmd.exe- -tasklist.exe- -findstr.exe- -WmiPrvSE.exe- " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 516 | find /i "-winword.exe-" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 660 | C:\WINDOWS\System32\cmd.exe /S /D /c" echo "C:\Users\admin\Desktop\Ohook_Activation_AIO.cmd.bat" " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 672 | mode con | C:\Windows\System32\mode.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: DOS Device MODE Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 680 | C:\WINDOWS\System32\cmd.exe /c mode con | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 728 | C:\WINDOWS\System32\cmd.exe /S /D /c" echo -smss.exe- -csrss.exe- -wininit.exe- -services.exe- -lsass.exe- -svchost.exe- -fontdrvhost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -spoolsv.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -dasHost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -OfficeClickToRun.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -dllhost.exe- -svchost.exe- -MoUsoCoreWorker.exe- -svchost.exe- -svchost.exe- -svchost.exe- -uhssvc.exe- -svchost.exe- -svchost.exe- -csrss.exe- -winlogon.exe- -fontdrvhost.exe- -dwm.exe- -sihost.exe- -svchost.exe- -svchost.exe- -explorer.exe- -svchost.exe- -dllhost.exe- -RuntimeBroker.exe- -SearchApp.exe- -RuntimeBroker.exe- -ctfmon.exe- -RuntimeBroker.exe- -SystemSettings.exe- -ApplicationFrameHost.exe- -UserOOBEBroker.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -TextInputHost.exe- -dllhost.exe- -audiodg.exe- -svchost.exe- -RuntimeBroker.exe- -svchost.exe- -RuntimeBroker.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -upfc.exe- -taskhostw.exe- -sppsvc.exe- -SppExtComObj.Exe- -slui.exe- -cmd.exe- -conhost.exe- -cmd.exe- -tasklist.exe- -findstr.exe- -WmiPrvSE.exe- " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1072 | find /i "ARM64" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1188 | fltmc | C:\Windows\System32\fltMC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Filter Manager Control Program Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1452 | find /i "C:\Users\admin\AppData\Local\Temp" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2088 | C:\WINDOWS\System32\cmd.exe /c C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe -nop -c "if ($PSVersionTable.PSEdition -ne 'Core') {$f=[io.file]::ReadAllText('C:\Users\admin\Desktop\Ohook_Activation_AIO.cmd.bat') -split ':pstst';iex ($f[1])}" 2>nul | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
17 473
Read events
17 473
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
1
Text files
6
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7796 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_nd03zloh.ycj.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4408 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ycvfbnu2.r0d.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7868 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_idfzv0dw.azl.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7868 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_3wlb4iwd.niu.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7796 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_iylkknhp.nrc.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7796 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:C7B09127683F3EB9A9E25315AE6AE86B | SHA256:D9A2EBE4E12F359FF2421625D9EDDD548CE724F5AFAC607890D8D2D3AB4B7A28 | |||
| 4408 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_5pnncxs2.rfy.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
54
DNS requests
20
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2432 | RUXIMICS.exe | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4180 | SIHClient.exe | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
4180 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
2432 | RUXIMICS.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4180 | SIHClient.exe | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicTimStaPCA_2010-07-01.crl | unknown | — | — | whitelisted |
4180 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4180 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
4180 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
4180 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2432 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.190.160.132:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.160.132:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2432 | RUXIMICS.exe | 23.53.40.176:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2432 | RUXIMICS.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
activated.win |
| unknown |
updatecheck32.activated.win |
| unknown |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |