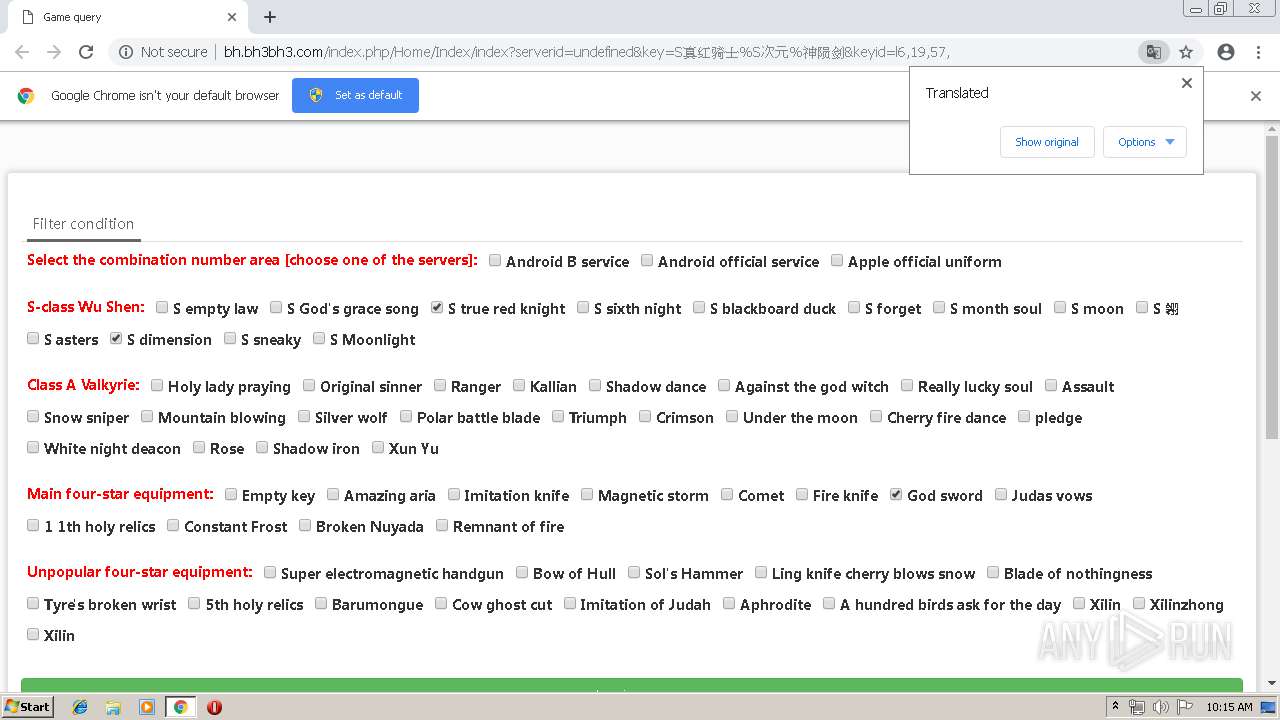
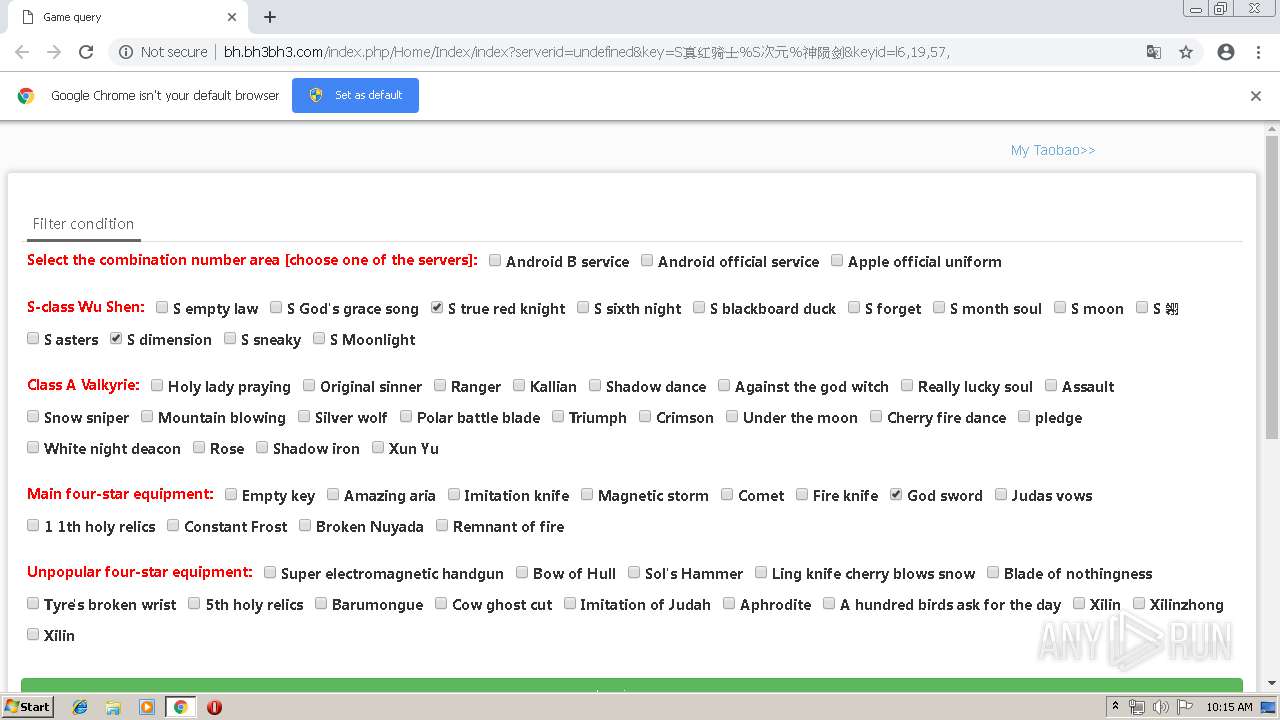
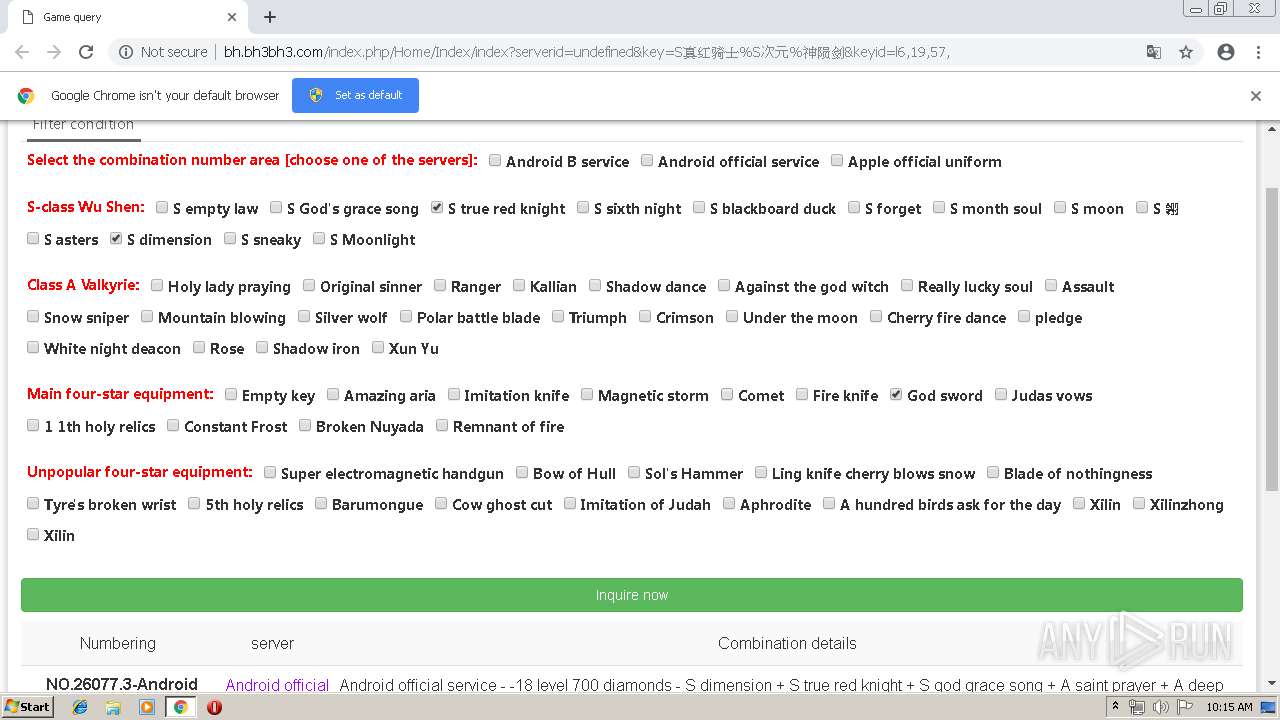
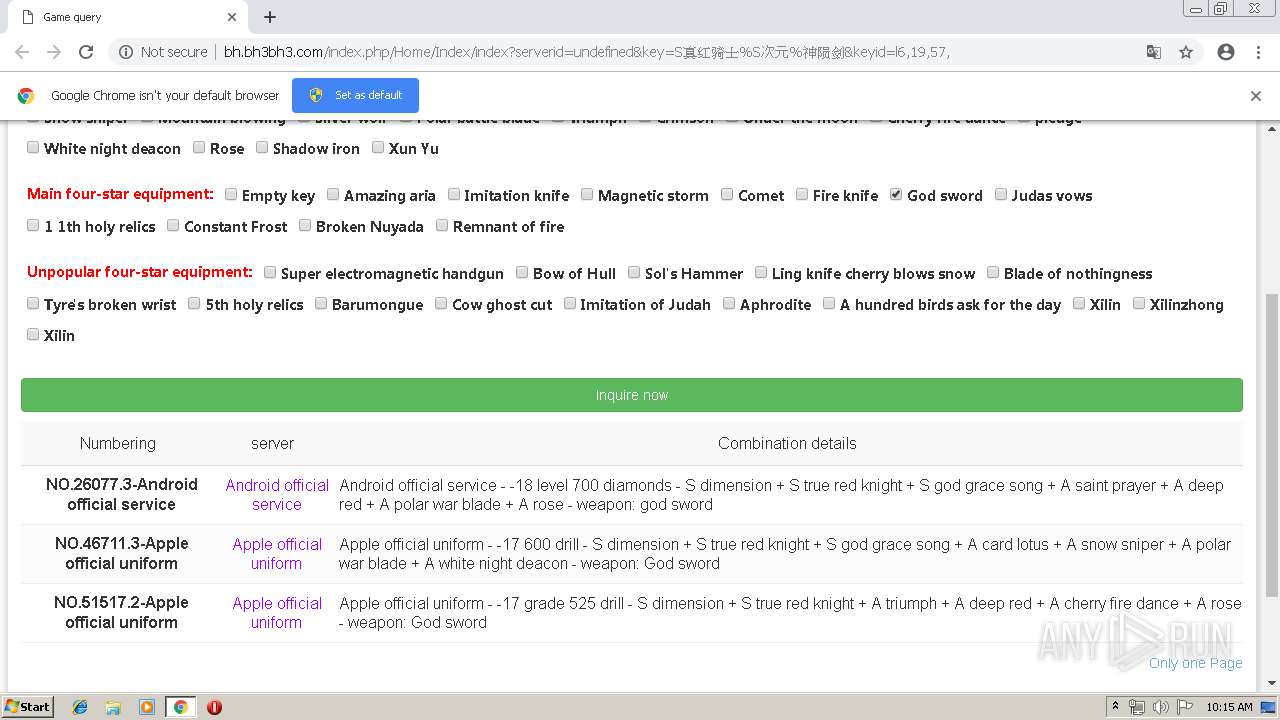
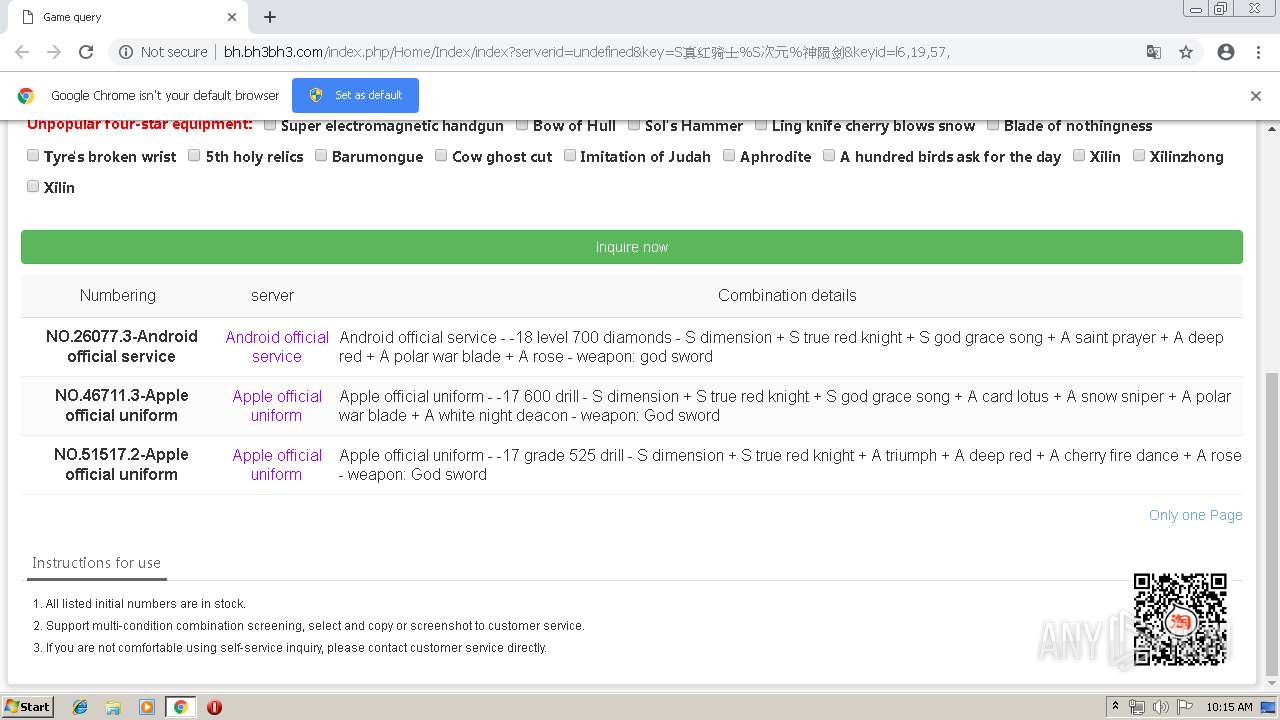
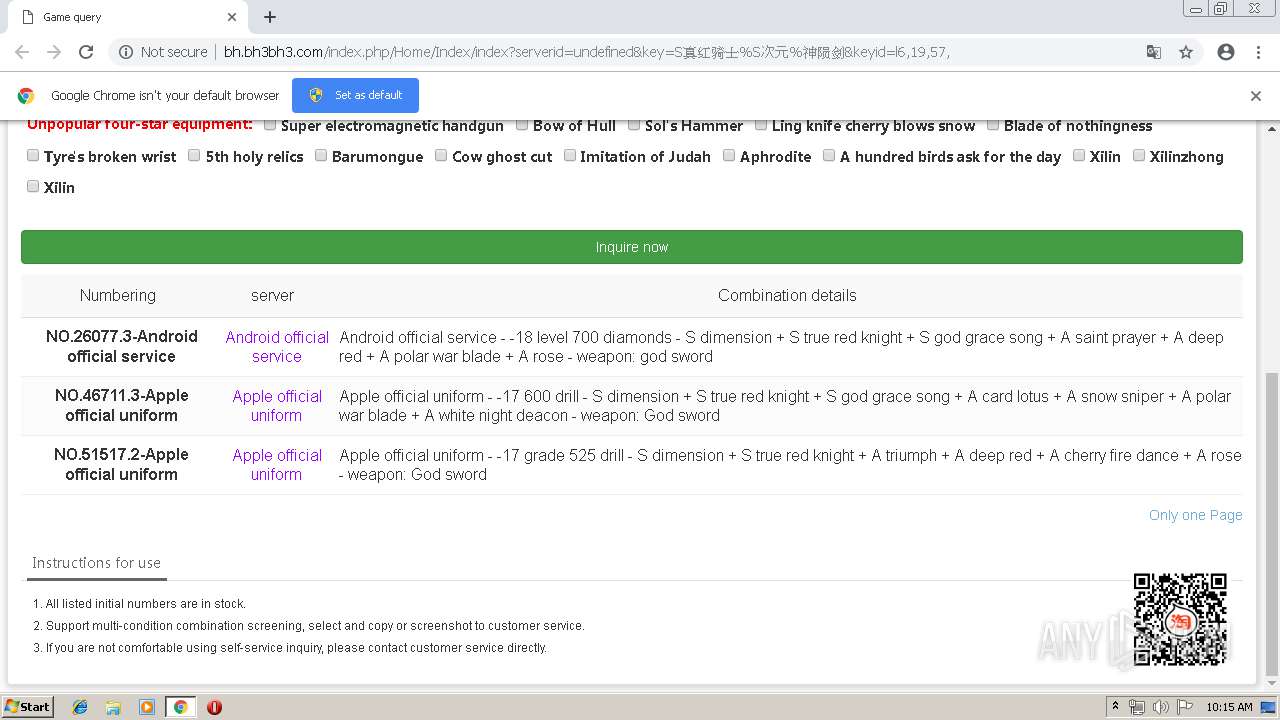
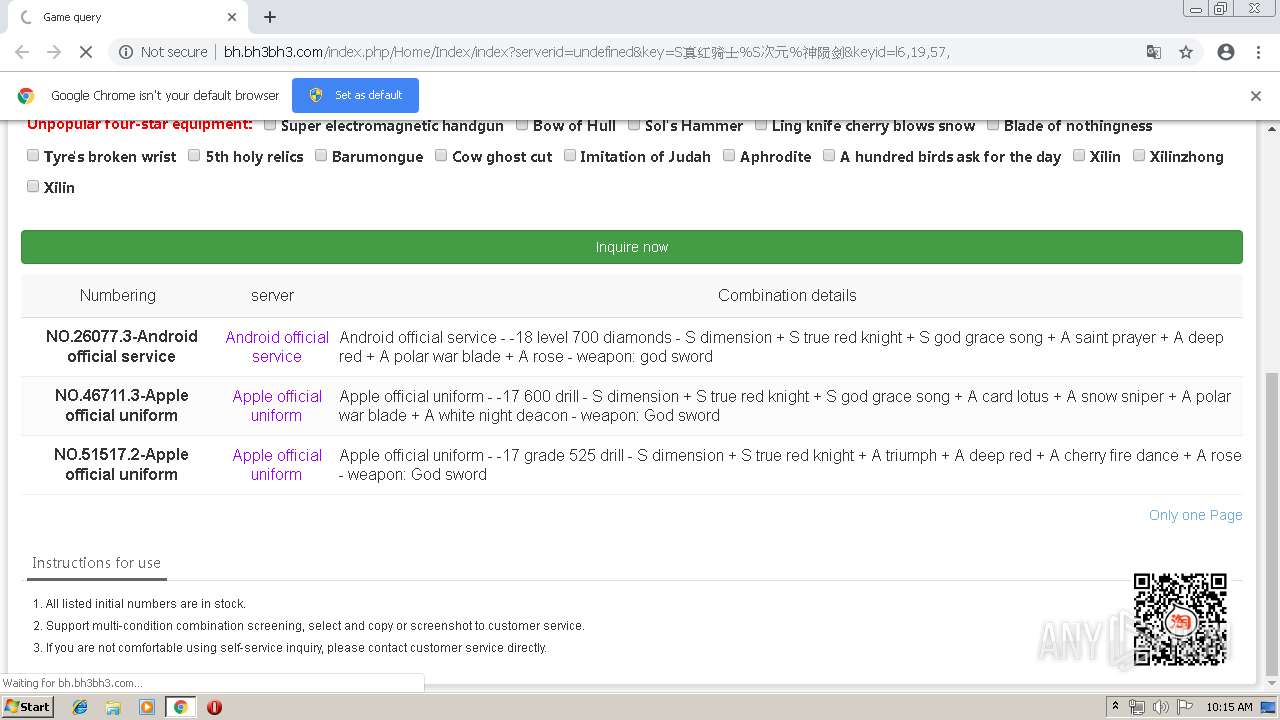
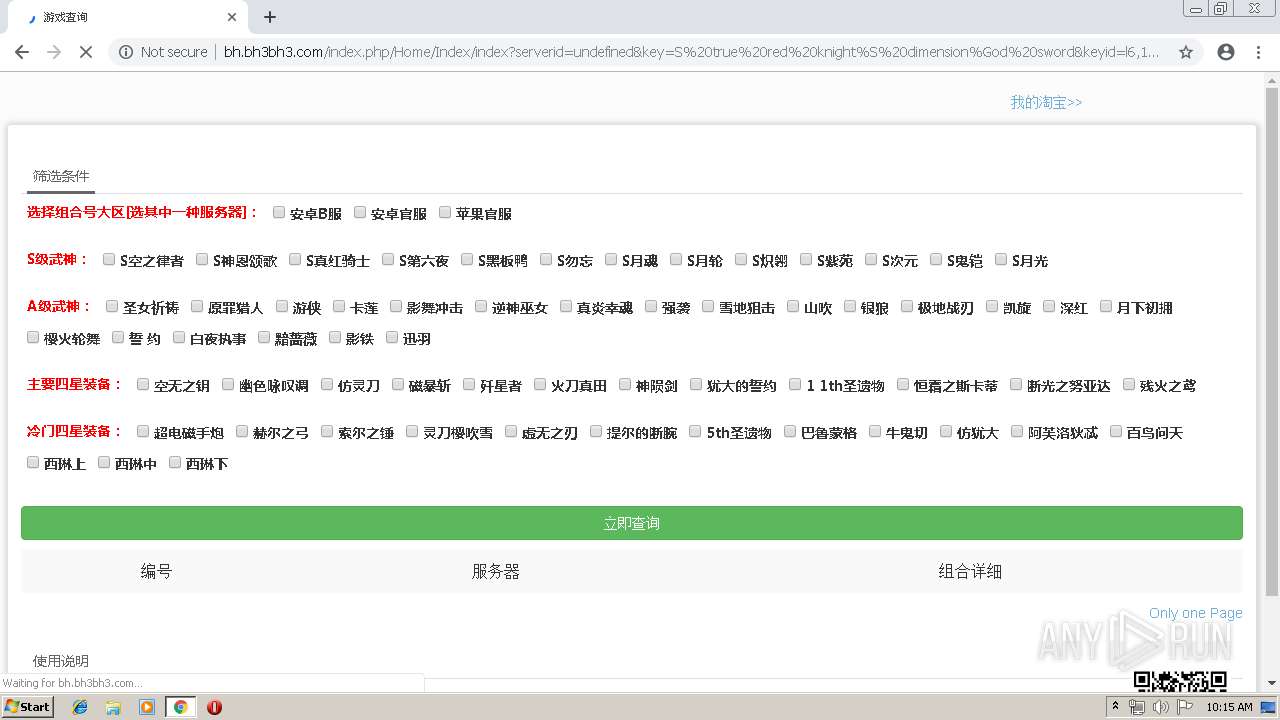
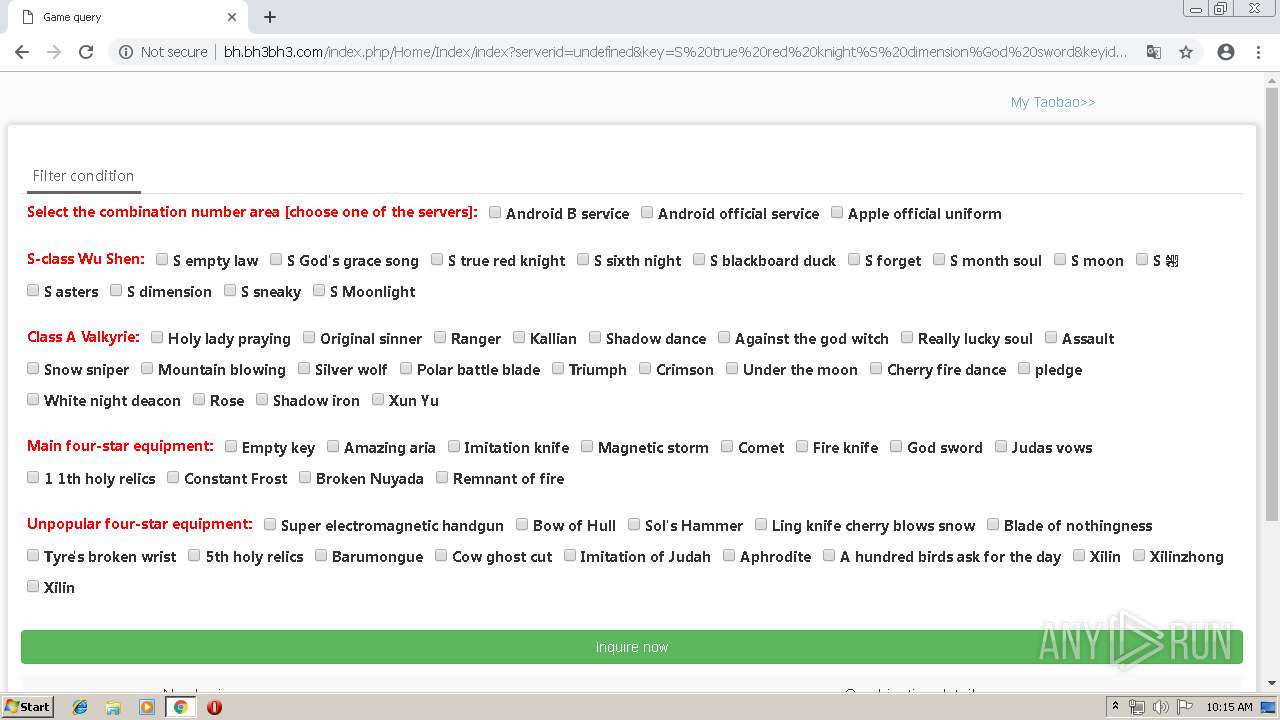
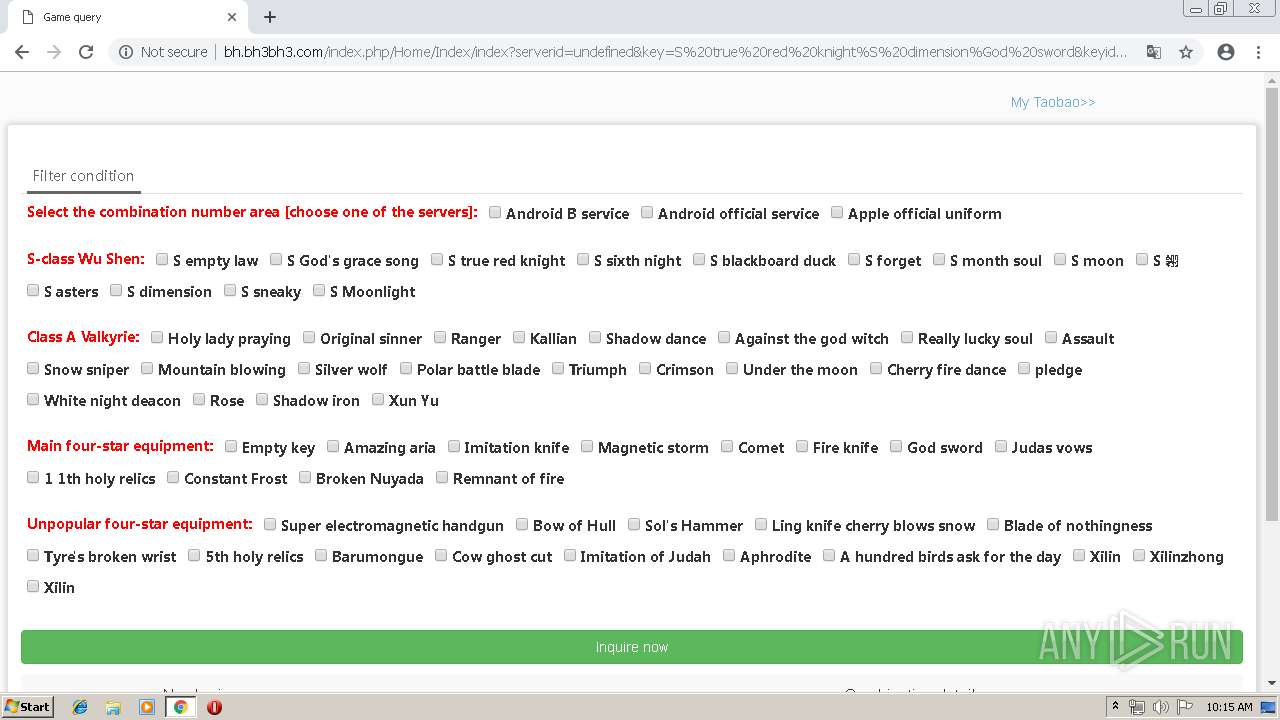
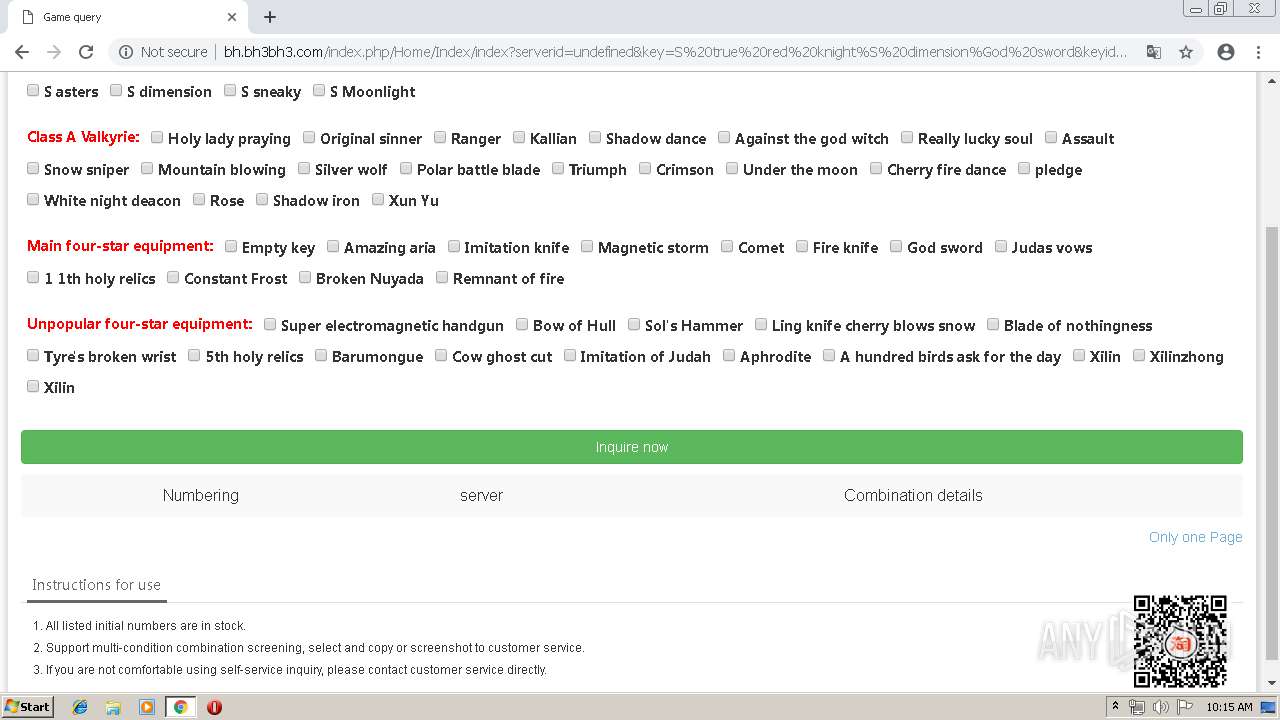
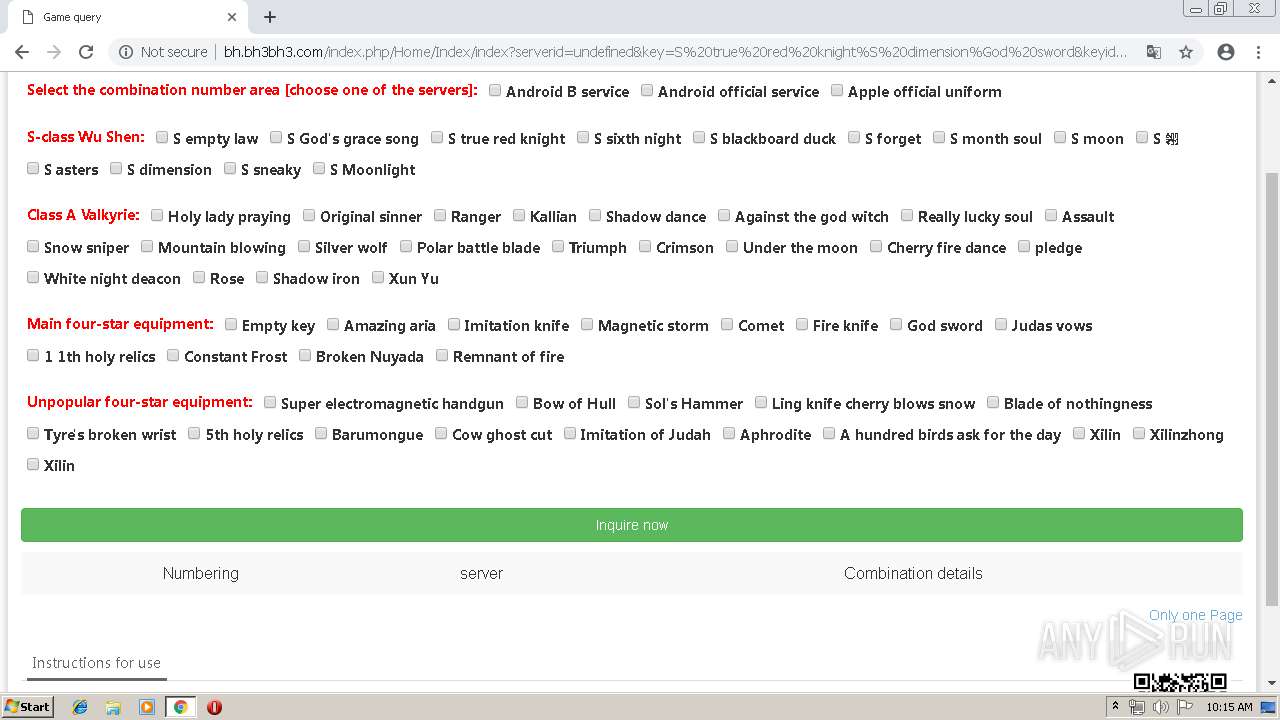
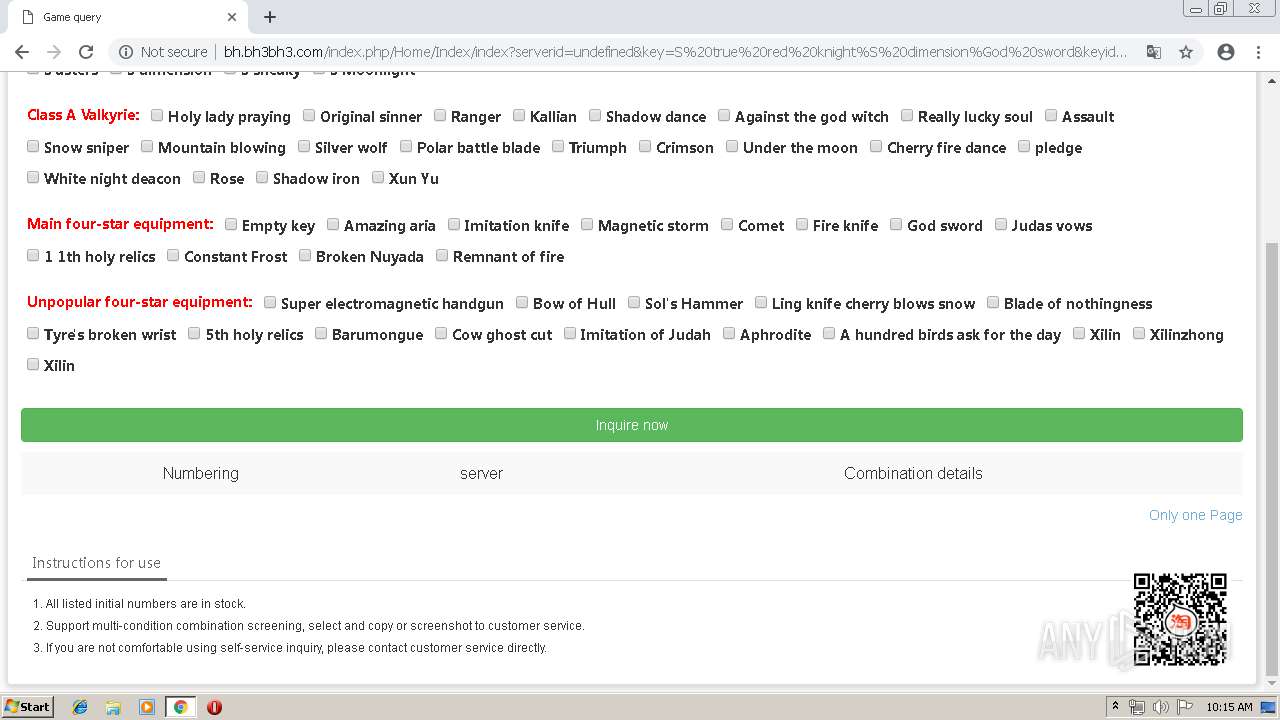
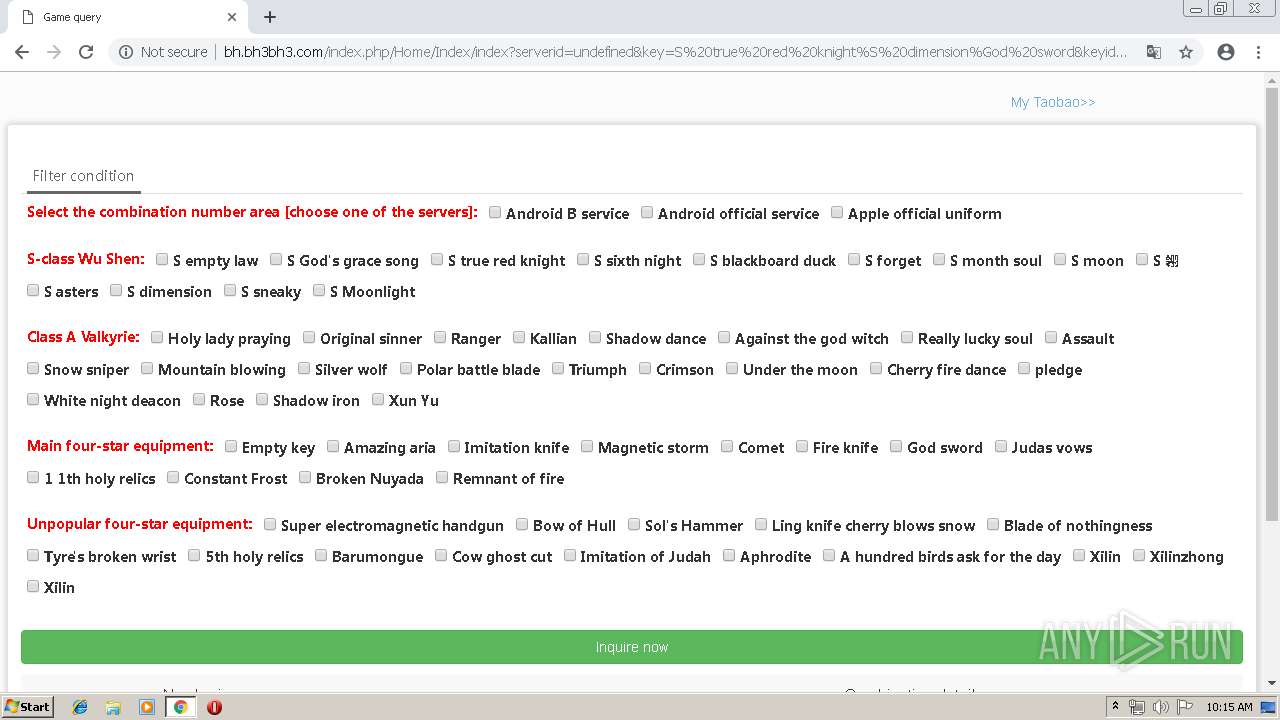
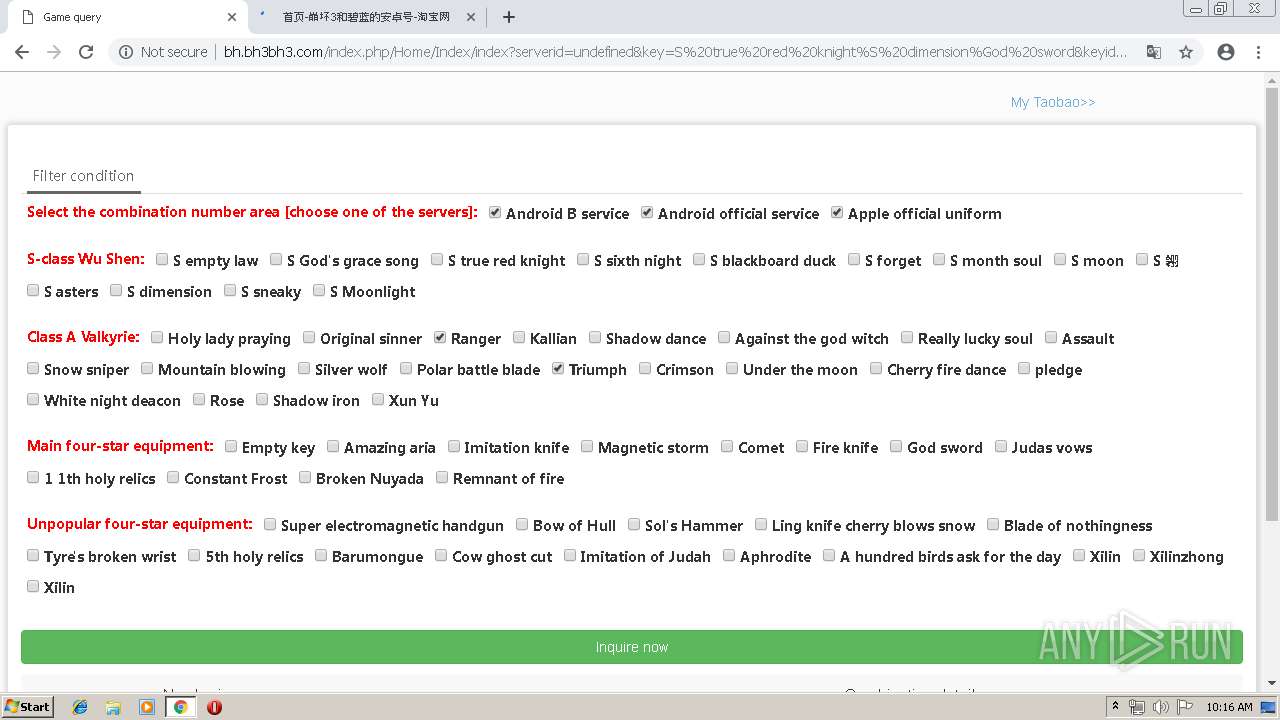
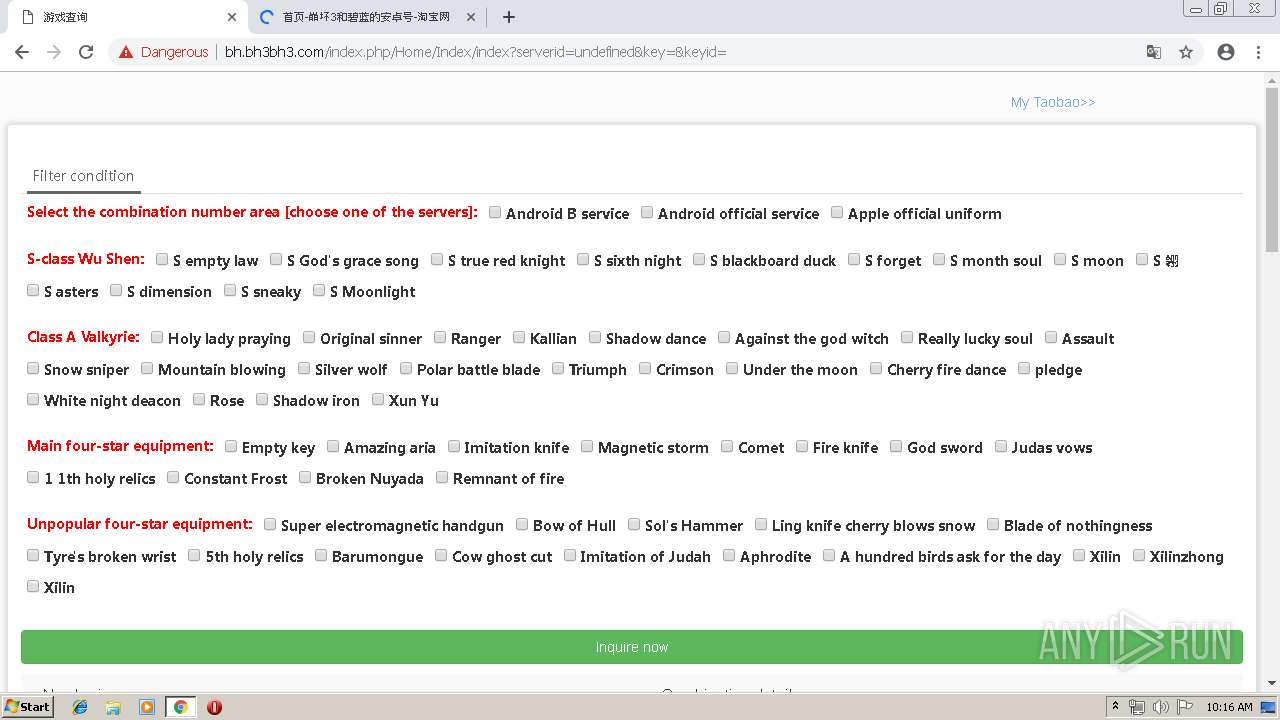
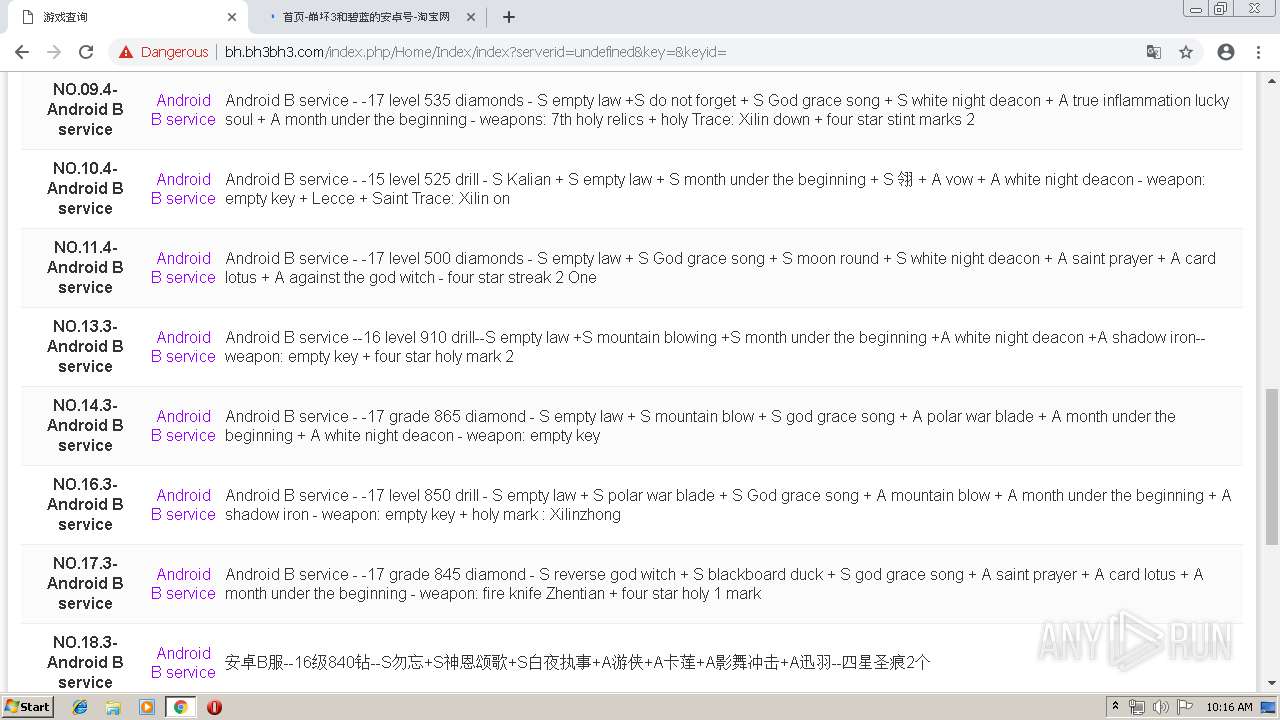
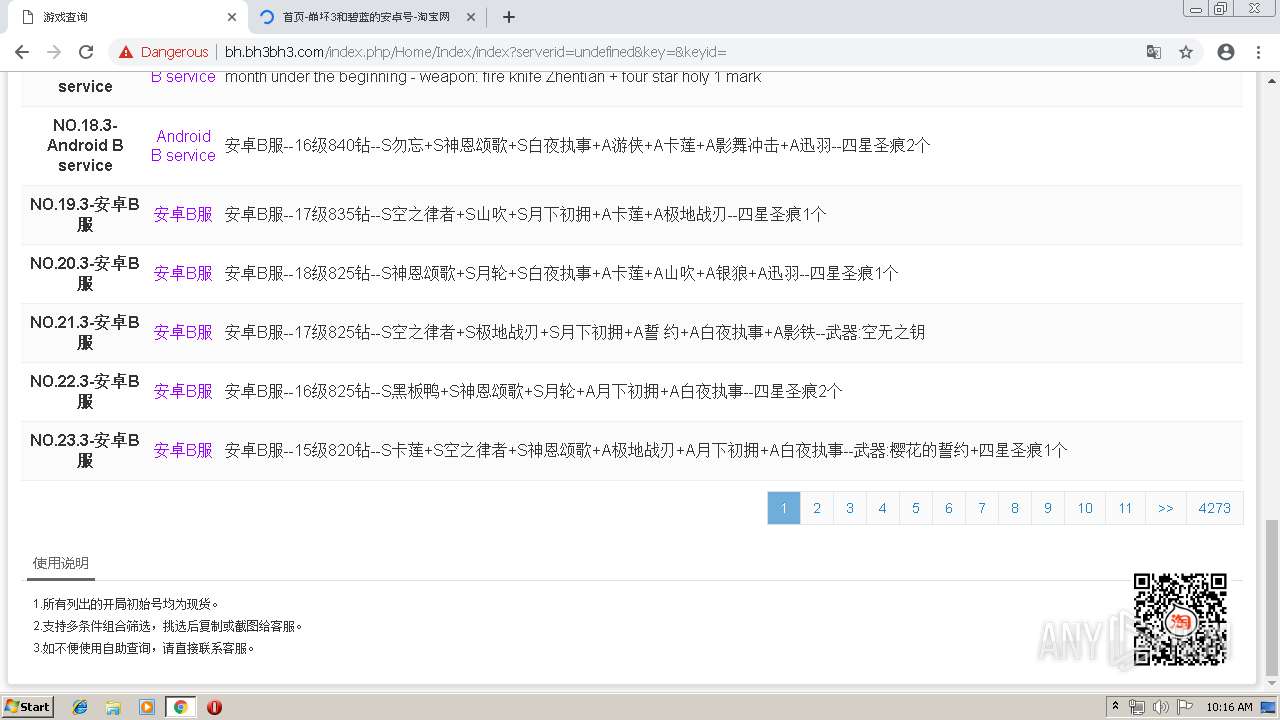
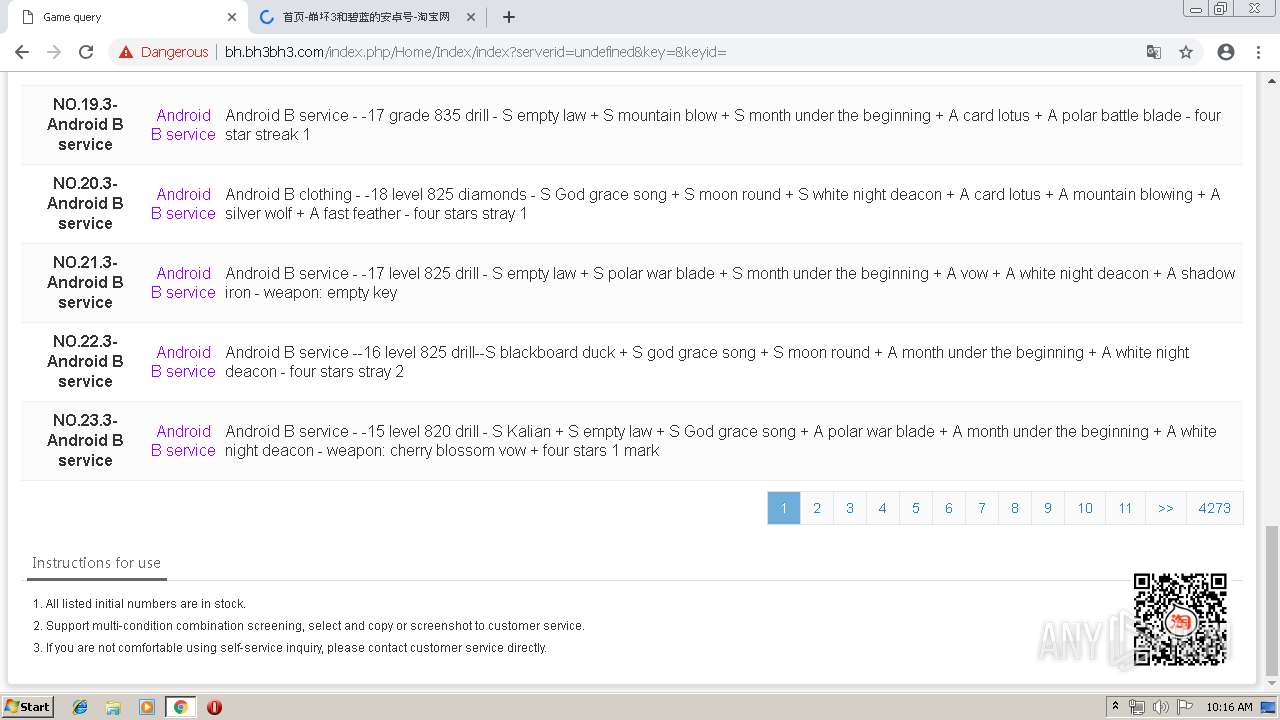
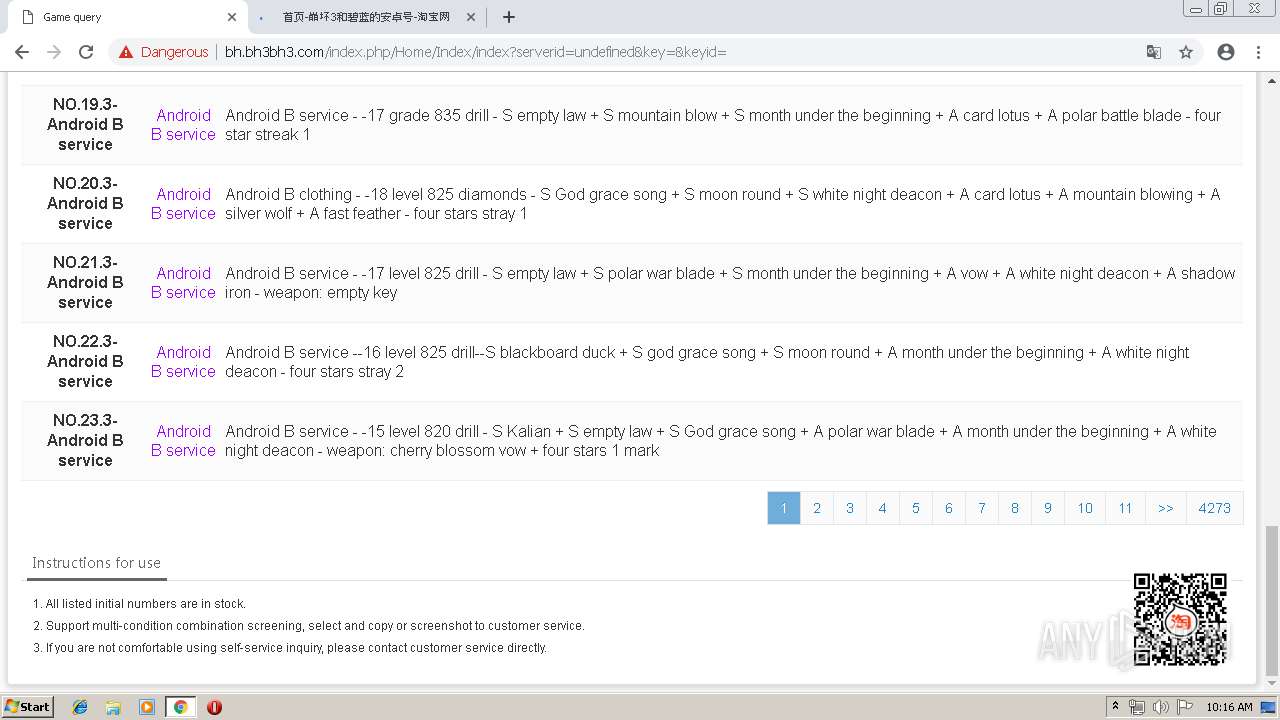
| URL: | http://bh.bh3bh3.com/index.php/Home/Index/index?serverid=undefined&key=S%E7%9C%9F%E7%BA%A2%E9%AA%91%E5%A3%AB%S%E6%AC%A1%E5%85%83%%E7%A5%9E%E9%99%A8%E5%89%91&keyid=l6,19,57, |
| Full analysis: | https://app.any.run/tasks/b5040012-e0b7-481a-95ff-e07bcb4b01f0 |
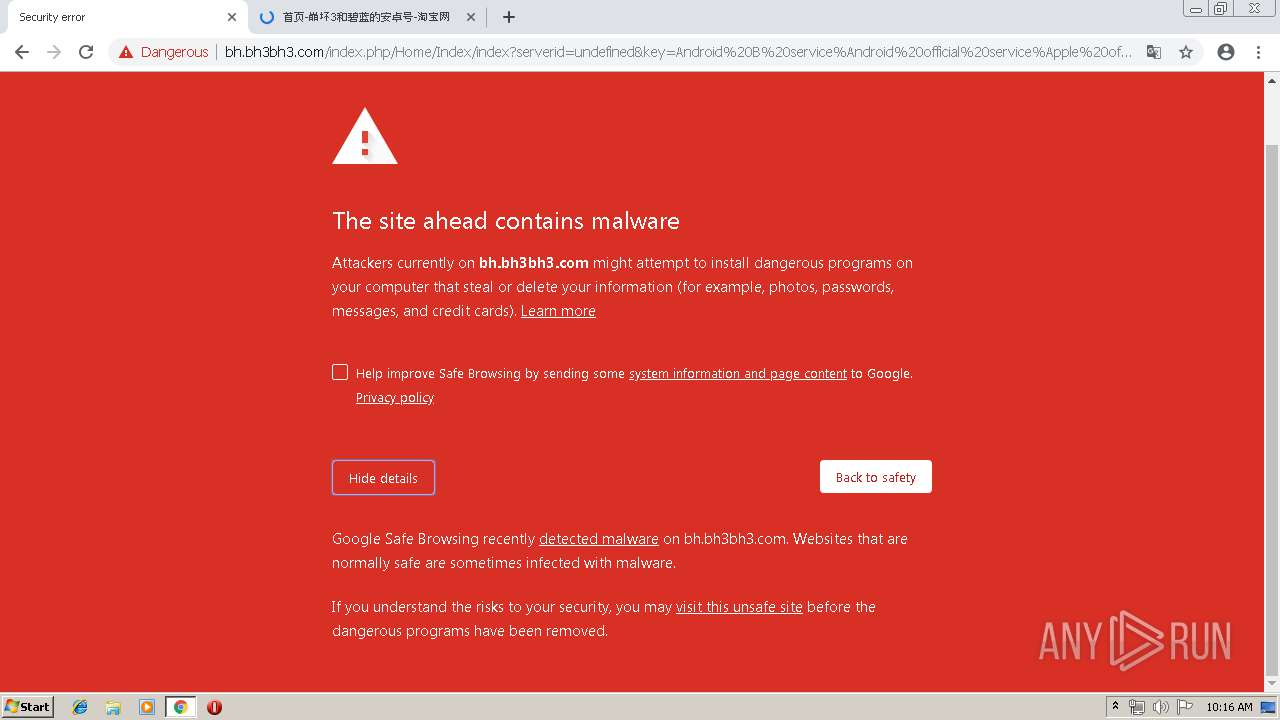
| Verdict: | Malicious activity |
| Threats: | Ramnit is a highly modular banking trojan and worm that evolved from a file-infecting virus into a powerful cybercrime tool. It specializes in financial fraud, credential theft, remote access, and malware delivery, being a serious threat to businesses and individuals. First spotted in 2010, Ramnit became popular after the 2014 takedown of the GameOver Zeus botnet, as cybercriminals sought alternatives for banking fraud. |
| Analysis date: | May 15, 2019, 09:14:33 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 83BD28AFE8209BE633D687F164F0D049 |
| SHA1: | 6A7A9609197CE863126380D511A84074EE264AED |
| SHA256: | B49D67BA78B6EC454E6B41CF82B68CC290D33144B3C095CF8B8BA74E40869027 |
| SSDEEP: | 3:N1Kc5QKbbHtIAKrdKpUT2YLKvcbAgwDh3yEgHTAJUFFUAmVcSUVAflSA2J86:Cc5fbbHtIzLT2CbQhxJxALV5xL |
MALICIOUS
RAMNIT was detected
- chrome.exe (PID: 2256)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2256)
INFO
Application launched itself
- chrome.exe (PID: 2256)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
56
Monitored processes
25
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 596 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=944,15087736579650055368,10115477344319233266,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=16558983073555306921 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16558983073555306921 --renderer-client-id=22 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3484 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 892 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=944,15087736579650055368,10115477344319233266,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=1989885956274655470 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1989885956274655470 --renderer-client-id=20 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4024 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 944 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=944,15087736579650055368,10115477344319233266,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=13047866595922722626 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13047866595922722626 --renderer-client-id=19 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3620 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1448 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=944,15087736579650055368,10115477344319233266,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8369878076442086896 --mojo-platform-channel-handle=3972 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1656 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=944,15087736579650055368,10115477344319233266,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=17886513107392092211 --mojo-platform-channel-handle=960 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1820 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2628 --on-initialized-event-handle=308 --parent-handle=312 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1888 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=944,15087736579650055368,10115477344319233266,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=15149641673107375122 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15149641673107375122 --renderer-client-id=21 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3916 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2164 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=944,15087736579650055368,10115477344319233266,131072 --enable-features=PasswordImport --service-pipe-token=15940773516111222484 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15940773516111222484 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2036 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2236 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=944,15087736579650055368,10115477344319233266,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7361151073985047828 --mojo-platform-channel-handle=4380 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2256 | "C:\Program Files\Google\Chrome\Application\chrome.exe" http://bh.bh3bh3.com/index.php/Home/Index/index?serverid=undefined&key=S%E7%9C%9F%E7%BA%A2%E9%AA%91%E5%A3%AB%S%E6%AC%A1%E5%85%83%%E7%A5%9E%E9%99%A8%E5%89%91&keyid=l6,19,57, | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
629
Read events
533
Write events
91
Delete events
5
Modification events
| (PID) Process: | (2256) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2256) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2256) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2256) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2256) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1820) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2256-13202385288084500 |
Value: 259 | |||
| (PID) Process: | (2256) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2256) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2256) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (2256) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2256-13202385288084500 |
Value: 259 | |||
Executable files
0
Suspicious files
127
Text files
243
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2256 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2256 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2256 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2256 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 2256 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 2256 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\2b4f5552-61c8-44b5-98be-fbb9bf3f097e.tmp | — | |
MD5:— | SHA256:— | |||
| 2256 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2256 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2256 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2256 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
28
TCP/UDP connections
70
DNS requests
54
Threats
37
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2256 | chrome.exe | GET | 204 | 172.217.18.110:80 | http://translate.google.com/gen204?sl=zh-CN&tl=en&textlen=104&sp=nmt&ttt=1082&ttl=343&ttf=88&sr=1&nca=te_time&client=te_lib&logld=vTE_20190506_00 | US | — | — | whitelisted |
2256 | chrome.exe | GET | 204 | 172.217.18.110:80 | http://translate.google.com/gen204?nca=te_li&client=te_lib&logld=vTE_20190506_00 | US | — | — | whitelisted |
2256 | chrome.exe | GET | 204 | 172.217.18.110:80 | http://translate.google.com/gen204?nca=te_li&client=te_lib&logld=vTE_20190506_00 | US | — | — | whitelisted |
2256 | chrome.exe | GET | 204 | 172.217.18.110:80 | http://translate.google.com/gen204?sl=zh-CN&tl=en&textlen=10&sp=nmt&ttt=108&ttl=29&ttf=88&sr=1&nca=te_time&client=te_lib&logld=vTE_20190506_00 | US | — | — | whitelisted |
2256 | chrome.exe | GET | 204 | 172.217.18.110:80 | http://translate.google.com/gen204?nca=te_li&client=te_lib&logld=vTE_20190506_00 | US | — | — | whitelisted |
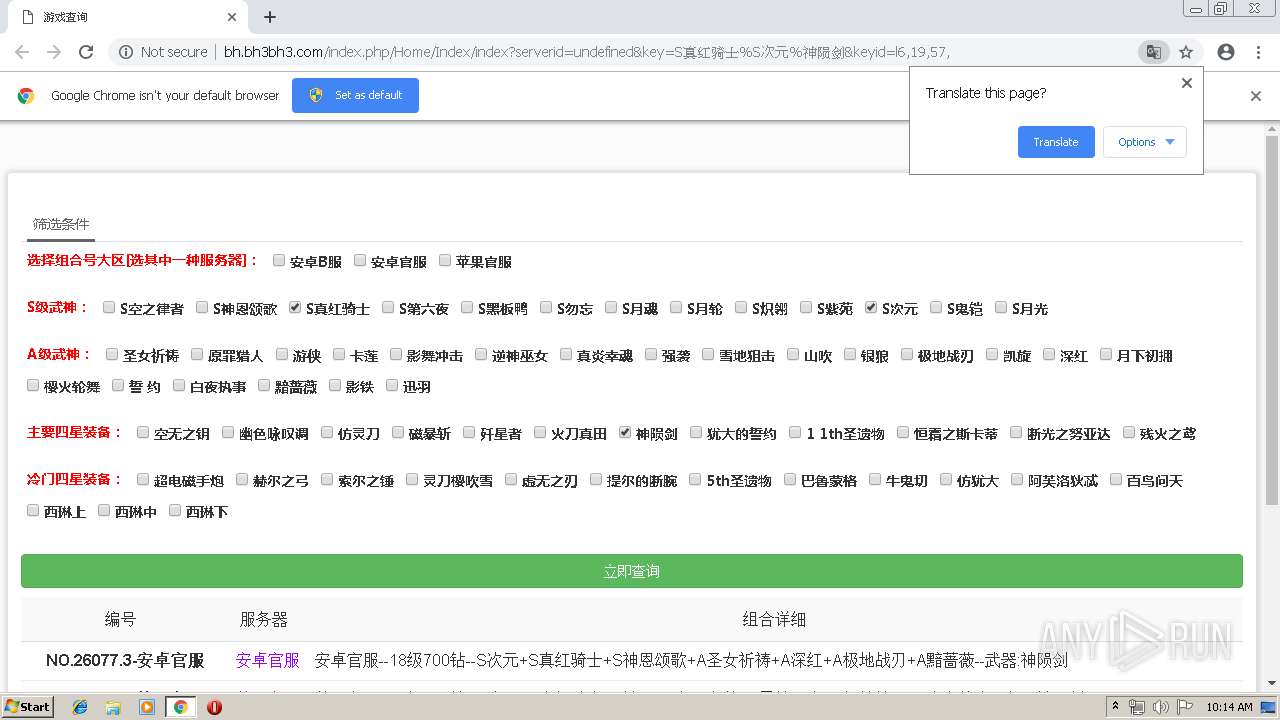
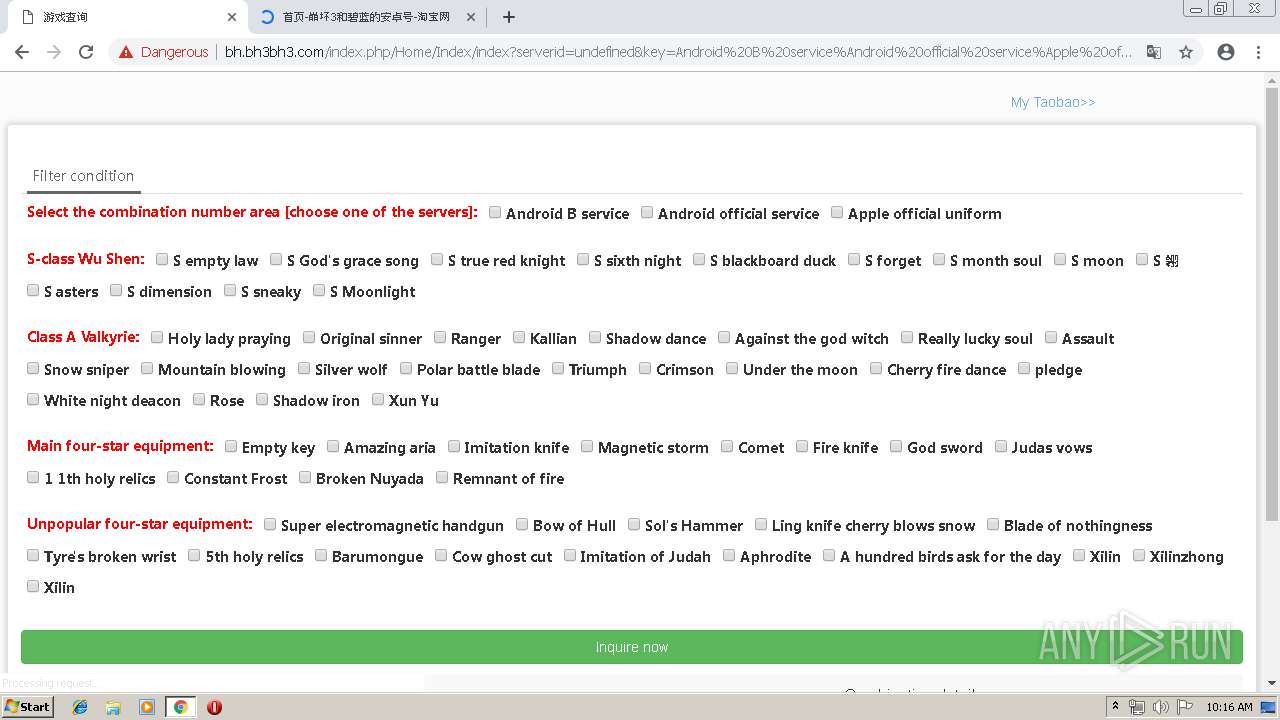
2256 | chrome.exe | GET | 200 | 121.42.120.210:80 | http://bh.bh3bh3.com/Public/css/global.css | CN | text | 2.69 Kb | malicious |
2256 | chrome.exe | GET | 200 | 121.42.120.210:80 | http://bh.bh3bh3.com/index.php/Home/Index/index?serverid=undefined&key=S%E7%9C%9F%E7%BA%A2%E9%AA%91%E5%A3%AB%S%E6%AC%A1%E5%85%83%%E7%A5%9E%E9%99%A8%E5%89%91&keyid=l6,19,57, | CN | html | 67.0 Kb | malicious |
2256 | chrome.exe | GET | 200 | 121.42.120.210:80 | http://bh.bh3bh3.com/Public/css/bootstrap.min.css | CN | text | 19.4 Kb | malicious |
2256 | chrome.exe | GET | 200 | 121.42.120.210:80 | http://bh.bh3bh3.com/Public/css/jquery.searchableSelect.css | CN | text | 890 b | malicious |
2256 | chrome.exe | GET | 200 | 121.42.120.210:80 | http://bh.bh3bh3.com/Public/js/bootstrap.min.js | CN | text | 10.6 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2256 | chrome.exe | 172.217.18.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2256 | chrome.exe | 172.217.16.141:443 | accounts.google.com | Google Inc. | US | suspicious |
2256 | chrome.exe | 121.42.120.210:80 | bh.bh3bh3.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | suspicious |
2256 | chrome.exe | 172.217.22.36:443 | www.google.com | Google Inc. | US | whitelisted |
2256 | chrome.exe | 216.58.207.42:443 | translate.googleapis.com | Google Inc. | US | whitelisted |
2256 | chrome.exe | 216.58.206.14:443 | clients2.google.com | Google Inc. | US | whitelisted |
2256 | chrome.exe | 172.217.22.65:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
2256 | chrome.exe | 216.58.205.238:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
2256 | chrome.exe | 74.125.173.233:80 | r4---sn-4g5ednz7.gvt1.com | Google Inc. | US | whitelisted |
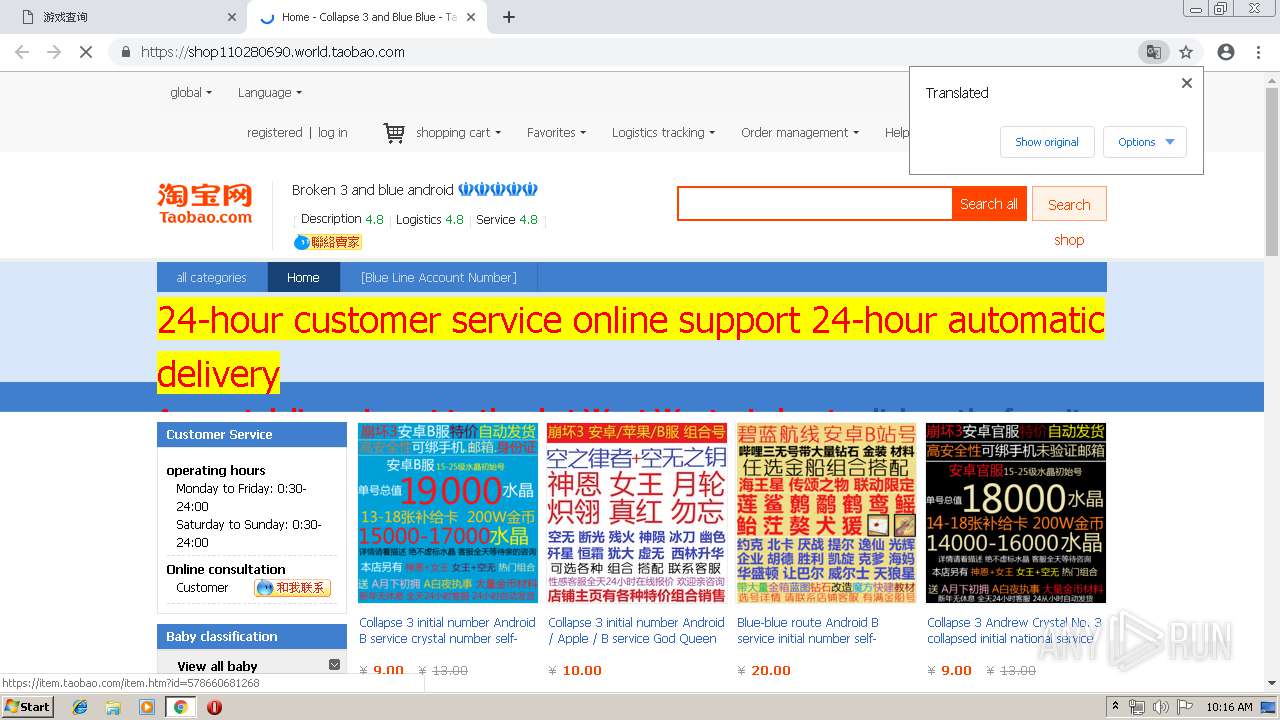
2256 | chrome.exe | 140.205.172.65:443 | shop110280690.world.taobao.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
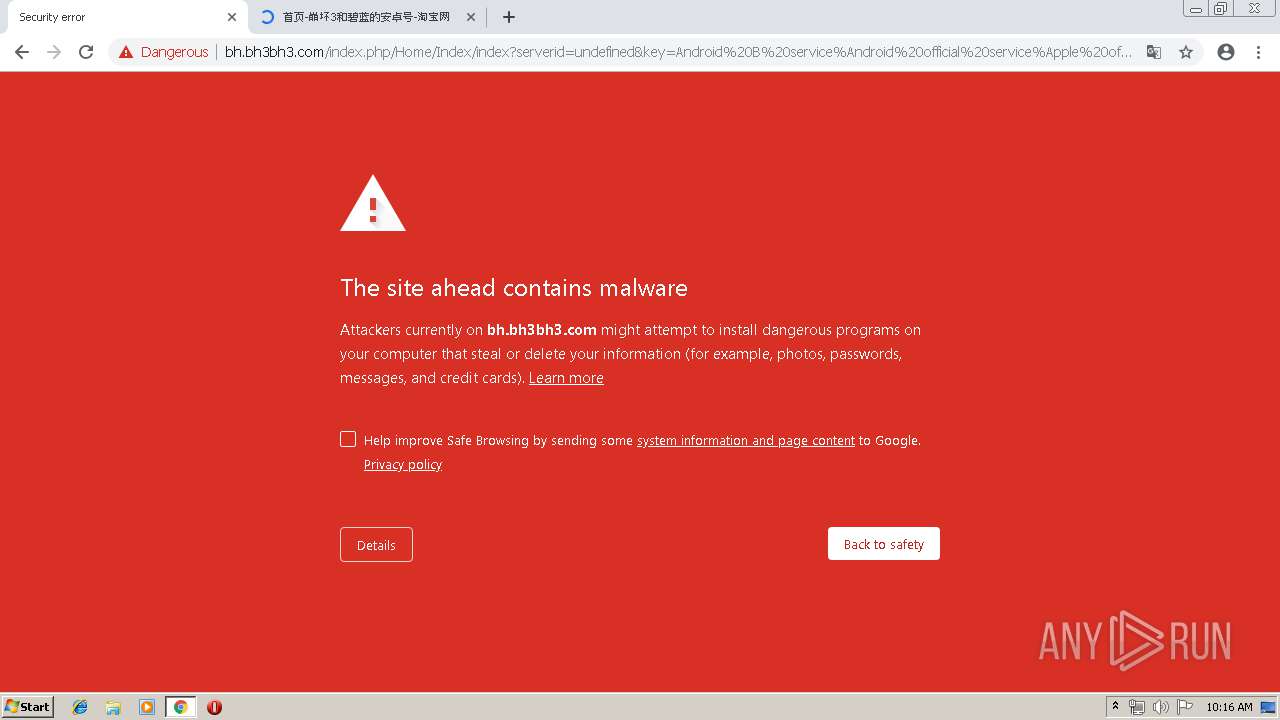
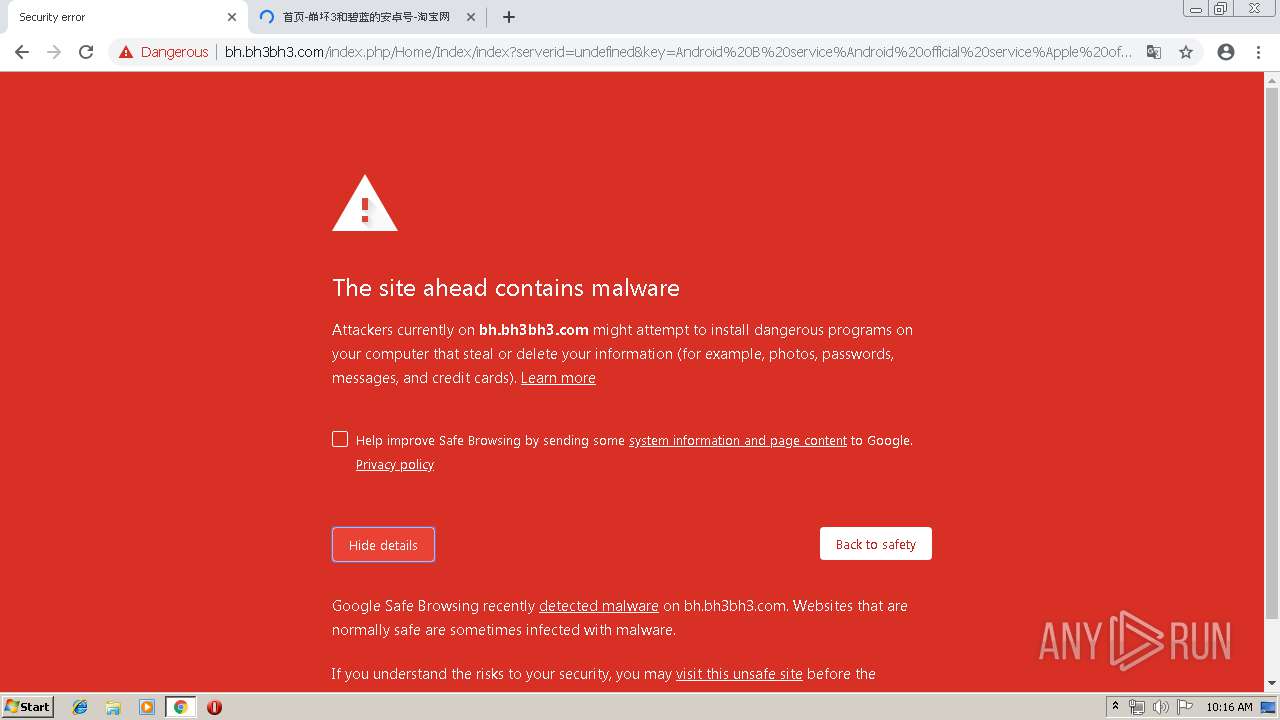
bh.bh3bh3.com |
| malicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
shop110280690.taobao.com |
| unknown |
www.badaonet.com |
| malicious |
translate.googleapis.com |
| whitelisted |
clients2.google.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2256 | chrome.exe | A Network Trojan was detected | ET CURRENT_EVENTS DRIVEBY EXE Embeded in Page Likely Evil M1 |
2256 | chrome.exe | A Network Trojan was detected | ET TROJAN PE EXE or DLL Windows file download Text |
2256 | chrome.exe | A Network Trojan was detected | ET TROJAN RAMNIT.A M2 |
2256 | chrome.exe | A Network Trojan was detected | ET CURRENT_EVENTS DRIVEBY EXE Embeded in Page Likely Evil M1 |
2256 | chrome.exe | A Network Trojan was detected | ET TROJAN PE EXE or DLL Windows file download Text |
2256 | chrome.exe | A Network Trojan was detected | ET TROJAN RAMNIT.A M2 |
2256 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
2256 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
2256 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
2256 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |