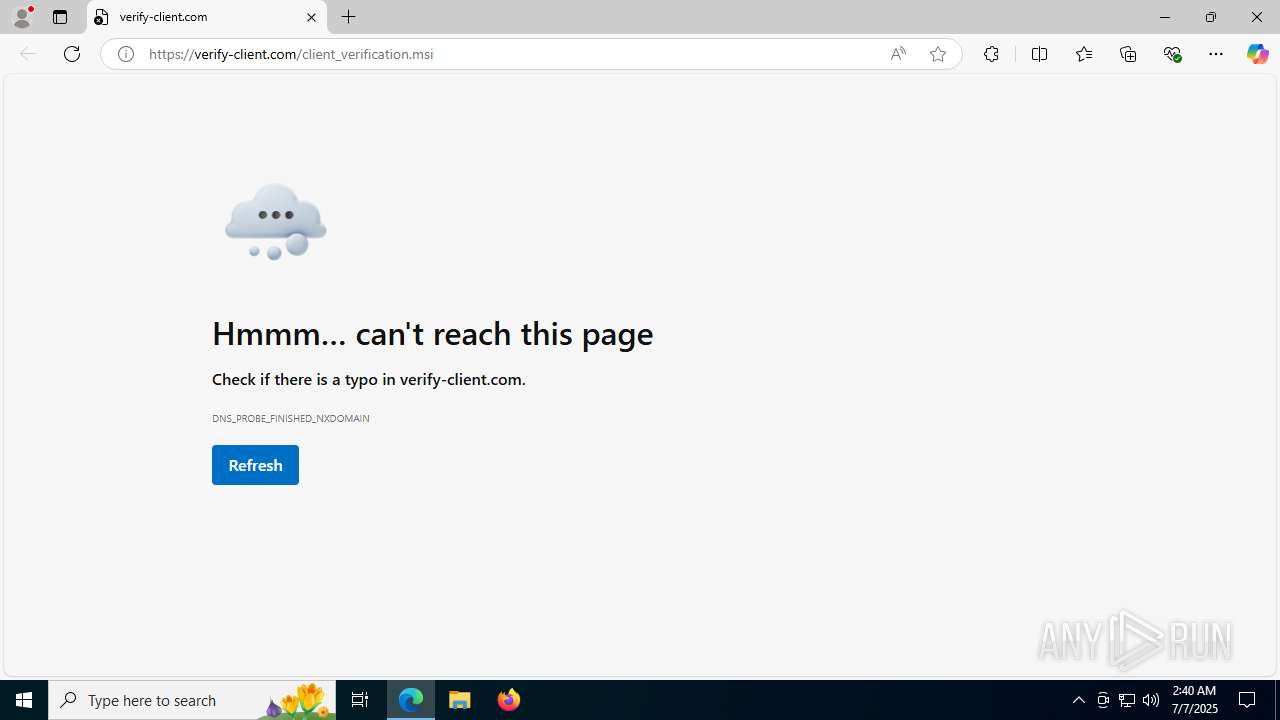
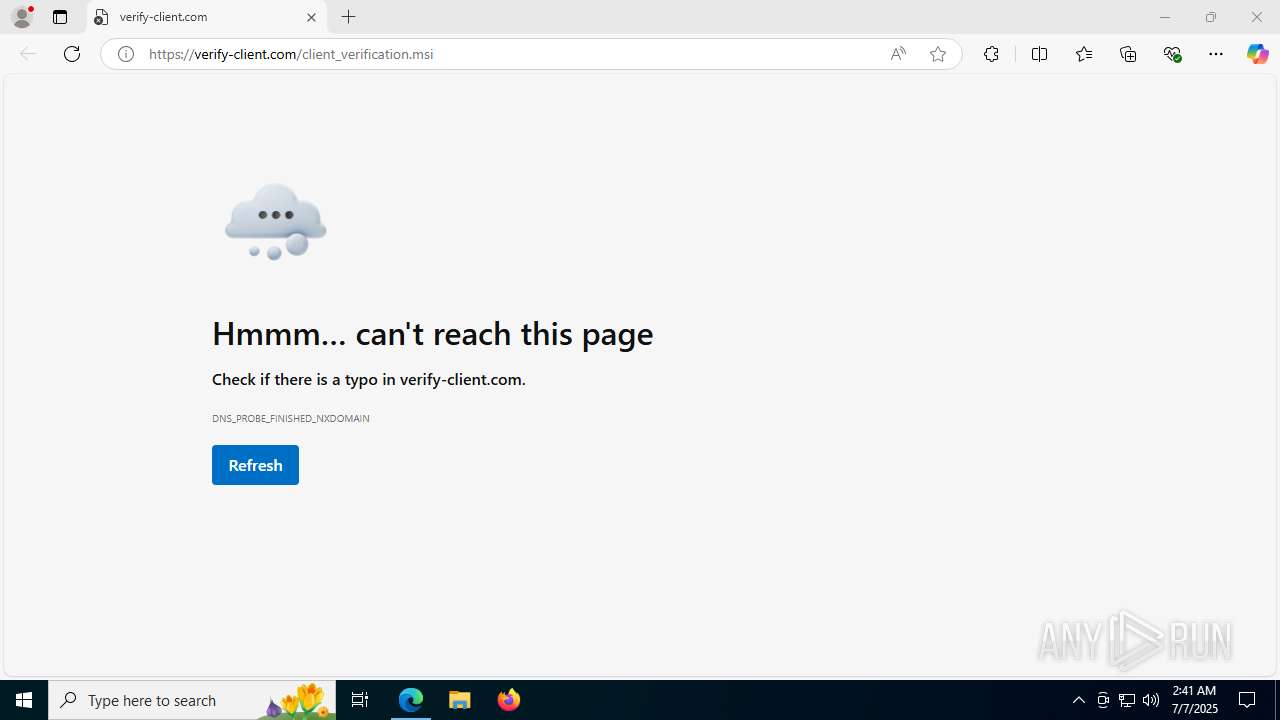
| URL: | https://verify-client.com/client_verification.msi |
| Full analysis: | https://app.any.run/tasks/e5382e56-2ebe-4a34-a1f8-194d58aa4a53 |
| Verdict: | Malicious activity |
| Analysis date: | July 07, 2025, 02:40:46 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 8E19A2EA597B33F1A46A5E18FADAA642 |
| SHA1: | 2DF6AC03F0F0EA83FEE59E7C88C59E503B183B53 |
| SHA256: | B49C17281DCF6E11A4AFD10141916C73A1BC2703D5FFD6E137DF36A590F82253 |
| SSDEEP: | 3:N80MtTAl2LMuuHas:2HM1l |
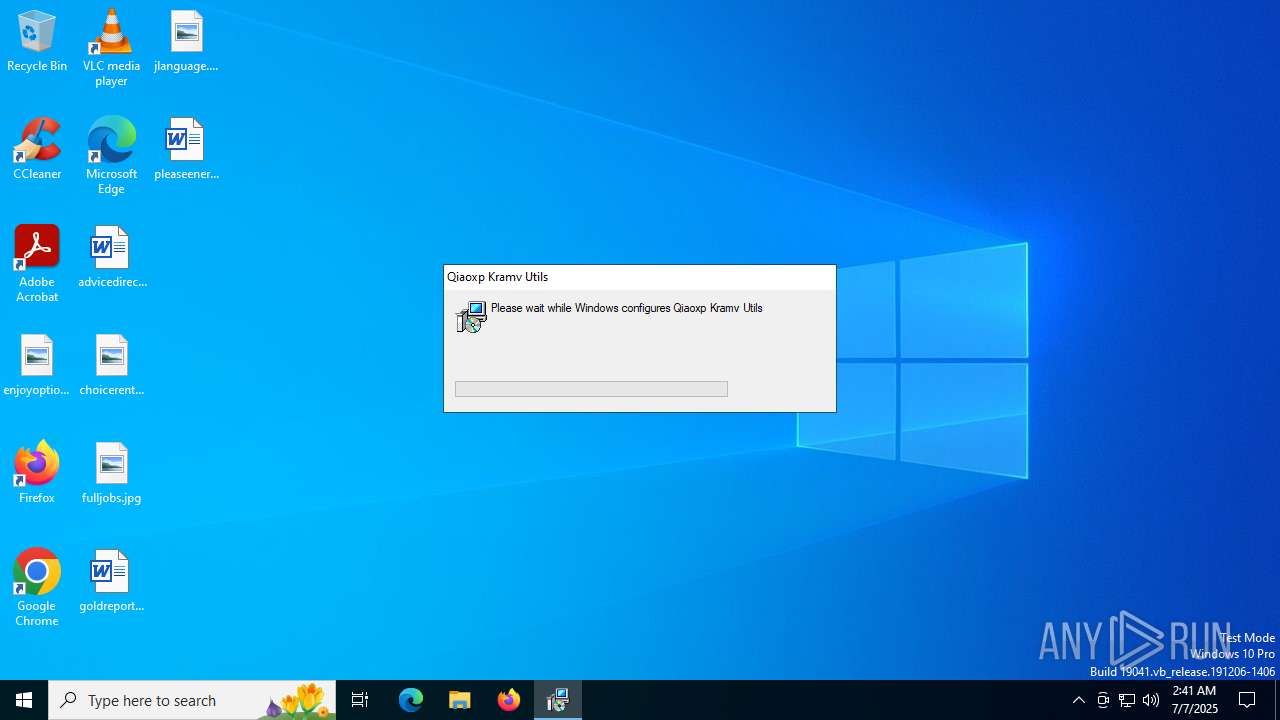
MALICIOUS
Bypass execution policy to execute commands
- powershell.exe (PID: 7472)
Changes powershell execution policy (Bypass)
- msiexec.exe (PID: 1740)
SUSPICIOUS
Reads the Windows owner or organization settings
- msiexec.exe (PID: 7756)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 7756)
- msiexec.exe (PID: 1740)
Process drops legitimate windows executable
- msiexec.exe (PID: 7756)
The process drops C-runtime libraries
- msiexec.exe (PID: 7756)
The process creates files with name similar to system file names
- msiexec.exe (PID: 7756)
The process bypasses the loading of PowerShell profile settings
- msiexec.exe (PID: 1740)
The process hide an interactive prompt from the user
- msiexec.exe (PID: 1740)
The process executes Powershell scripts
- msiexec.exe (PID: 1740)
Starts POWERSHELL.EXE for commands execution
- msiexec.exe (PID: 1740)
Executing commands from a ".bat" file
- msiexec.exe (PID: 7756)
Starts CMD.EXE for commands execution
- msiexec.exe (PID: 7756)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 8040)
There is functionality for taking screenshot (YARA)
- clipx.exe (PID: 8032)
Drops 7-zip archiver for unpacking
- msiexec.exe (PID: 7756)
INFO
Application launched itself
- msedge.exe (PID: 4324)
- msedge.exe (PID: 8052)
Checks supported languages
- identity_helper.exe (PID: 7496)
- msiexec.exe (PID: 7756)
- msiexec.exe (PID: 1976)
- msiexec.exe (PID: 1740)
- EnhancedUI.exe (PID: 6700)
- identity_helper.exe (PID: 7628)
- 7z.exe (PID: 1192)
- clipx.exe (PID: 8032)
Reads the computer name
- msiexec.exe (PID: 7756)
- identity_helper.exe (PID: 7496)
- msiexec.exe (PID: 1976)
- msiexec.exe (PID: 1740)
- identity_helper.exe (PID: 7628)
- clipx.exe (PID: 8032)
- 7z.exe (PID: 1192)
Reads the software policy settings
- msiexec.exe (PID: 7756)
- powershell.exe (PID: 7472)
- msiexec.exe (PID: 1740)
- slui.exe (PID: 2232)
Reads Environment values
- identity_helper.exe (PID: 7496)
- msiexec.exe (PID: 1740)
- identity_helper.exe (PID: 7628)
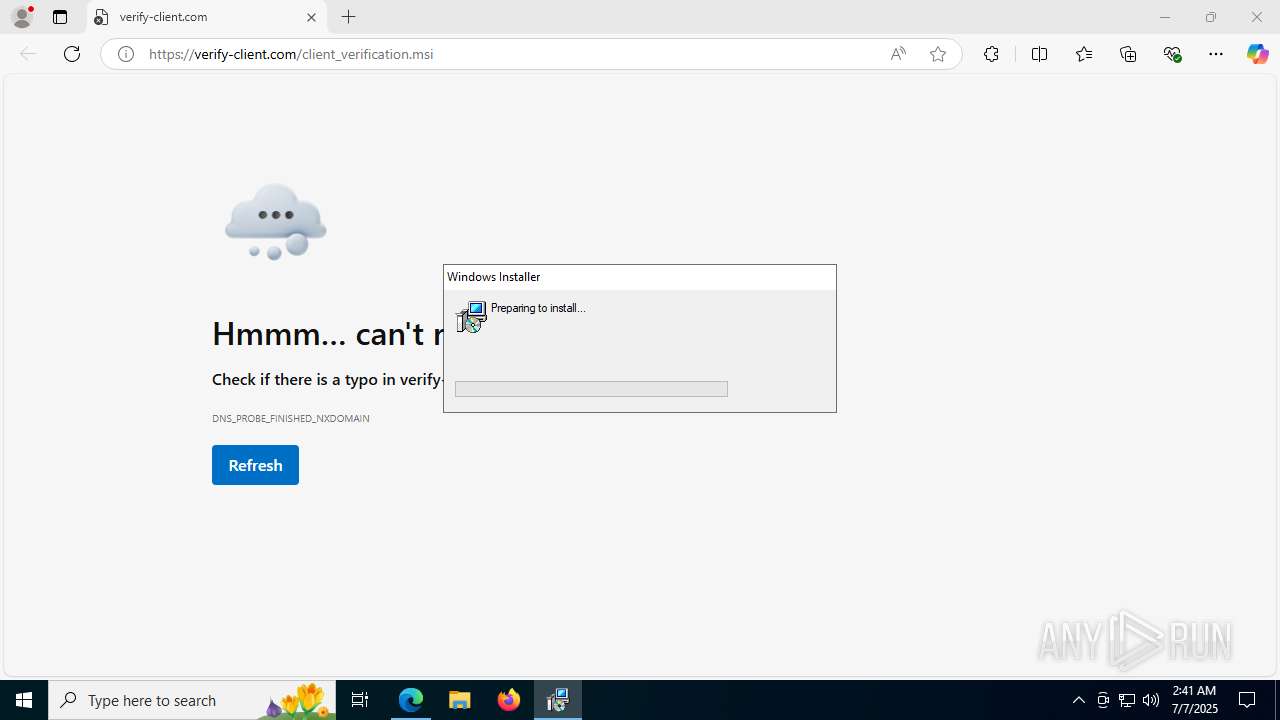
Manual execution by a user
- msiexec.exe (PID: 7260)
Executable content was dropped or overwritten
- msiexec.exe (PID: 7756)
The sample compiled with english language support
- msiexec.exe (PID: 7756)
Create files in a temporary directory
- msiexec.exe (PID: 7756)
- msiexec.exe (PID: 1740)
- powershell.exe (PID: 7472)
- msiexec.exe (PID: 7260)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 7472)
Reads security settings of Internet Explorer
- powershell.exe (PID: 7472)
Checks proxy server information
- msiexec.exe (PID: 1740)
- slui.exe (PID: 2232)
Reads the machine GUID from the registry
- msiexec.exe (PID: 1740)
Creates files or folders in the user directory
- msiexec.exe (PID: 1740)
- msiexec.exe (PID: 7756)
- clipx.exe (PID: 8032)
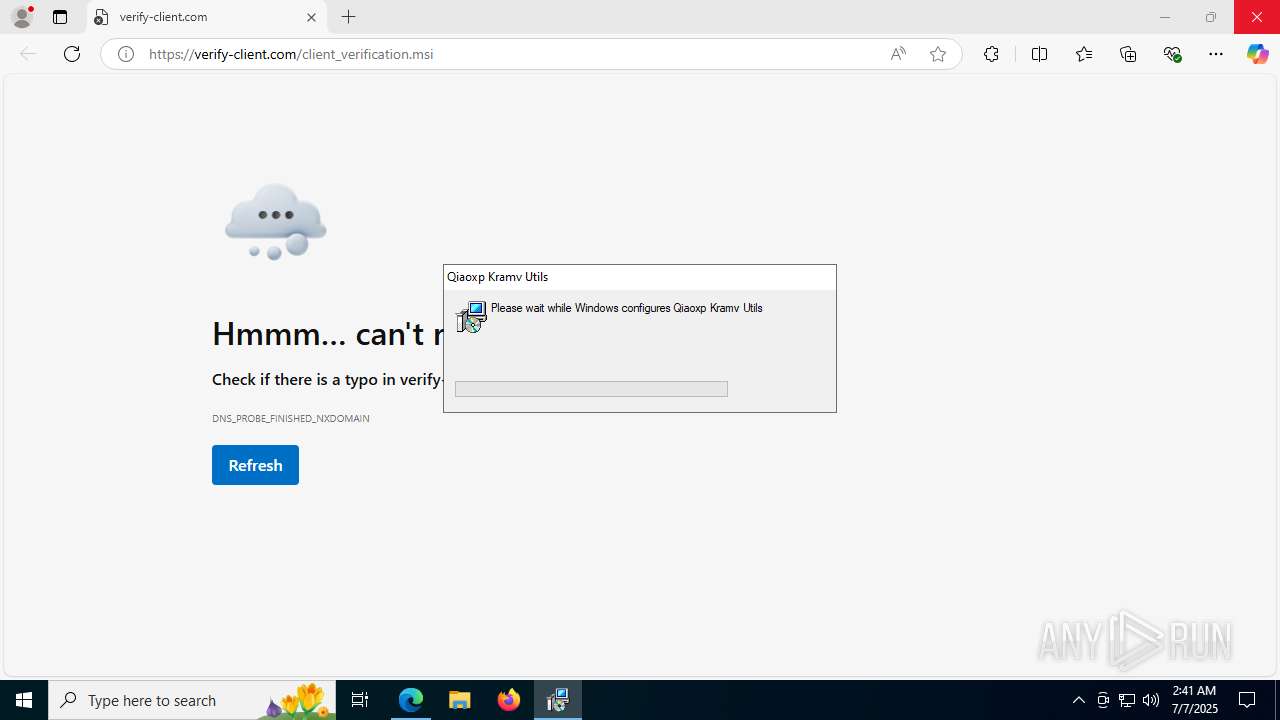
Creates a software uninstall entry
- msiexec.exe (PID: 7756)
UPX packer has been detected
- clipx.exe (PID: 8032)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
207
Monitored processes
56
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1192 | "C:\Users\admin\AppData\Roaming\Qiaoxp Kramv Utils\7z.exe" x "C:\Users\admin\AppData\Roaming\Qiaoxp Kramv Utils\\kraqci.dat" -o"C:\Users\admin\AppData\Roaming\Qiaoxp Kramv Utils\" -y -p0 | C:\Users\admin\AppData\Roaming\Qiaoxp Kramv Utils\7z.exe | — | msiexec.exe | |||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7-Zip Console Exit code: 2 Version: 24.09 Modules
| |||||||||||||||
| 1216 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --always-read-main-dll --field-trial-handle=5004,i,5486993031971570143,9953067411226747308,262144 --variations-seed-version --mojo-platform-channel-handle=5032 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1480 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5488,i,16025321064089497072,12459606569102895812,262144 --variations-seed-version --mojo-platform-channel-handle=3108 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1728 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=5268,i,16025321064089497072,12459606569102895812,262144 --variations-seed-version --mojo-platform-channel-handle=5160 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1732 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=4412,i,16025321064089497072,12459606569102895812,262144 --variations-seed-version --mojo-platform-channel-handle=5464 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1740 | C:\Windows\syswow64\MsiExec.exe -Embedding C09220FED4B30E5B9598EDC4224C28DA | C:\Windows\SysWOW64\msiexec.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1976 | C:\Windows\syswow64\MsiExec.exe -Embedding EFFC2238791ECDBDCEC6FBF46277CC8A U | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2136 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2708,i,5486993031971570143,9953067411226747308,262144 --variations-seed-version --mojo-platform-channel-handle=2816 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2136 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=4372,i,16025321064089497072,12459606569102895812,262144 --variations-seed-version --mojo-platform-channel-handle=4784 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2180 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2636,i,16025321064089497072,12459606569102895812,262144 --variations-seed-version --mojo-platform-channel-handle=2712 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
16 719
Read events
16 441
Write events
265
Delete events
13
Modification events
| (PID) Process: | (7052) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | L1WatermarkLowPart |
Value: 0 | |||
| (PID) Process: | (7052) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | L1WatermarkHighPart |
Value: 0 | |||
| (PID) Process: | (7052) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 0 | |||
| (PID) Process: | (7052) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 0 | |||
| (PID) Process: | (7052) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (7052) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31190760 | |||
| (PID) Process: | (7052) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (7052) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (7052) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (7052) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
Executable files
147
Suspicious files
351
Text files
103
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4324 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF1756ca.TMP | — | |
MD5:— | SHA256:— | |||
| 4324 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4324 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF1756da.TMP | — | |
MD5:— | SHA256:— | |||
| 4324 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF1756da.TMP | — | |
MD5:— | SHA256:— | |||
| 4324 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF1756ca.TMP | — | |
MD5:— | SHA256:— | |||
| 4324 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4324 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4324 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF1756da.TMP | — | |
MD5:— | SHA256:— | |||
| 4324 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4324 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF1756da.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
30
TCP/UDP connections
68
DNS requests
90
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7132 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:iGLS7VhndcHateH8hPeO52b5motf--p7mZGcRWj5FPY&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 2.20.245.137:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1964 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5328 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1028 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1028 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1740 | msiexec.exe | GET | 200 | 104.18.20.213:80 | http://r10.c.lencr.org/70.crl | unknown | — | — | whitelisted |
3980 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1751950765&P2=404&P3=2&P4=cYd8cC7pnIWtxoAt71PW3%2f5Lx%2fugWe6pxRDI%2b%2fehOKyENlD4mDl%2b10Gst4b%2b8%2fjqb%2bzg4WDf2EGUh%2fcGh3xUkA%3d%3d | unknown | — | — | whitelisted |
2940 | svchost.exe | GET | 200 | 69.192.161.44:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4512 | RUXIMICS.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7132 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7132 | msedge.exe | 150.171.28.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7132 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7132 | msedge.exe | 2.23.227.199:443 | copilot.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
7132 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
verify-client.com |
| unknown |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
www.bing.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
edgeassetservice.azureedge.net |
| whitelisted |
www.googleapis.com |
| whitelisted |
Threats
Process | Message |
|---|---|
clipx.exe | >
|
clipx.exe | >>>
|
clipx.exe | Auto-initializing 2 services (user pass)
|
clipx.exe | >>>
|
clipx.exe | Auto-initializing 0 services (system pass)
|
clipx.exe | >
|