| File name: | KMSAuto Net.exe |
| Full analysis: | https://app.any.run/tasks/a8223e74-cd51-479b-929a-5a832e0a56ab |
| Verdict: | Malicious activity |
| Analysis date: | February 19, 2026, 10:24:58 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | FCBA020455D659579C5B16C64689130F |
| SHA1: | 7ED8AE3ACA1F573FDD04064EF6E997BDF4F9ECF1 |
| SHA256: | B49A692A5B5752888A2339C161A64FE7CD42C62295EE1B1F529D0C710663B81C |
| SSDEEP: | 98304:g09lD3d1Ev9E01DwQDYpveEzROLQs29E0ZrsK5sdEtzVeOlptfE/9SMjP7VvHO5F:NmV/ZfM |
MALICIOUS
Executing a file with an untrusted certificate
- certmgr.exe (PID: 5888)
- certmgr.exe (PID: 2424)
- FakeClient.exe (PID: 7208)
- certmgr.exe (PID: 7372)
- certmgr.exe (PID: 7476)
- certmgr.exe (PID: 1684)
- certmgr.exe (PID: 3988)
Changes settings of System certificates
- certmgr.exe (PID: 2424)
- certmgr.exe (PID: 5888)
- certmgr.exe (PID: 7372)
- certmgr.exe (PID: 7476)
- certmgr.exe (PID: 3988)
- certmgr.exe (PID: 1684)
- devcon.exe (PID: 6544)
Starts NET.EXE for service management
- net.exe (PID: 8536)
- KMSAuto Net.exe (PID: 8004)
- net.exe (PID: 1600)
- net.exe (PID: 3624)
- net.exe (PID: 8444)
- net.exe (PID: 8048)
Changes image file execution options
- reg.exe (PID: 4816)
SUSPICIOUS
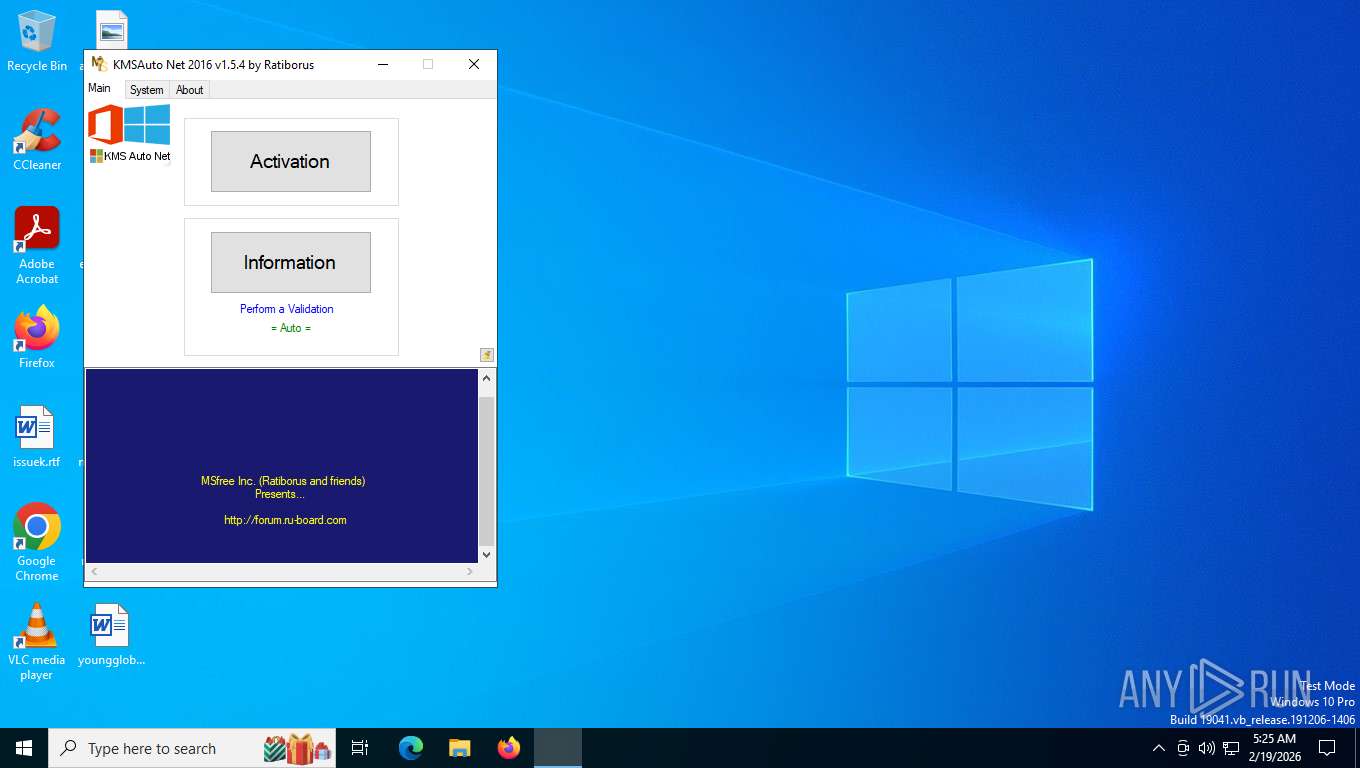
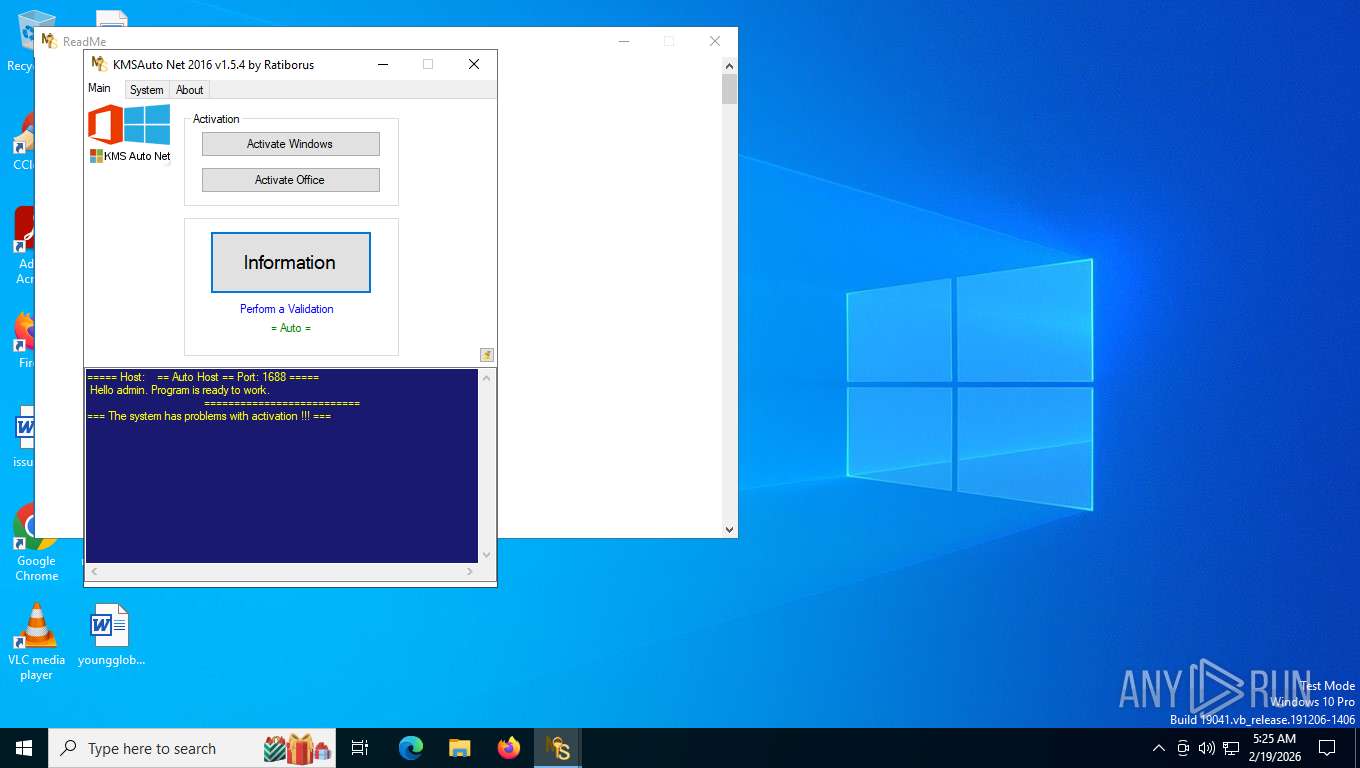
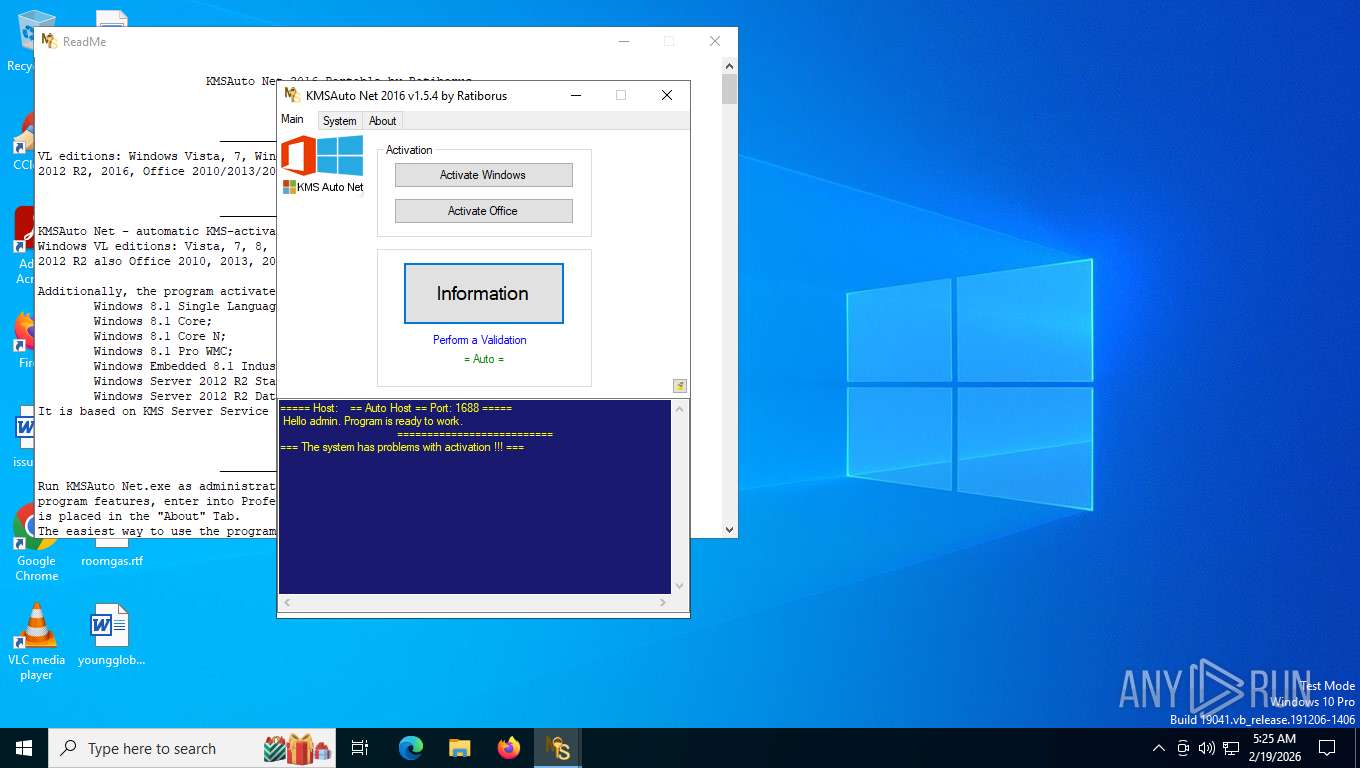
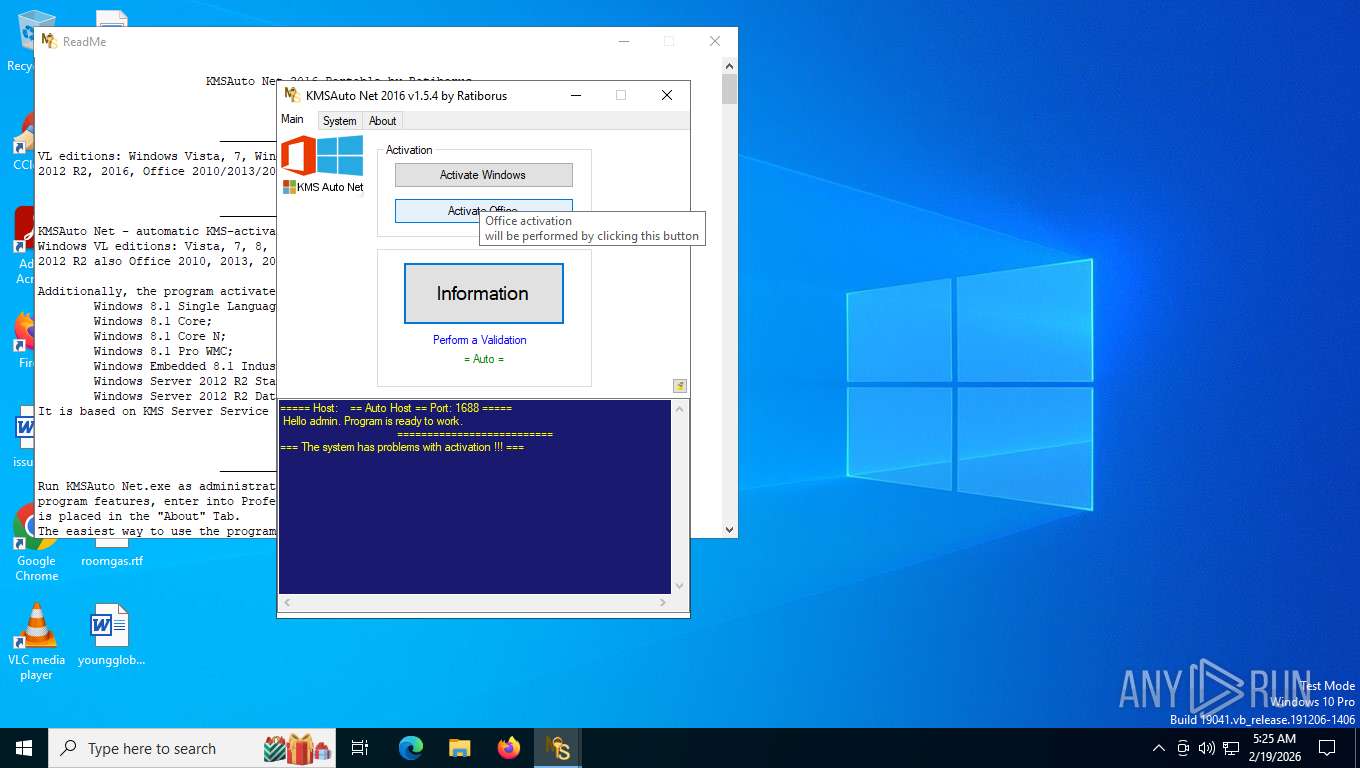
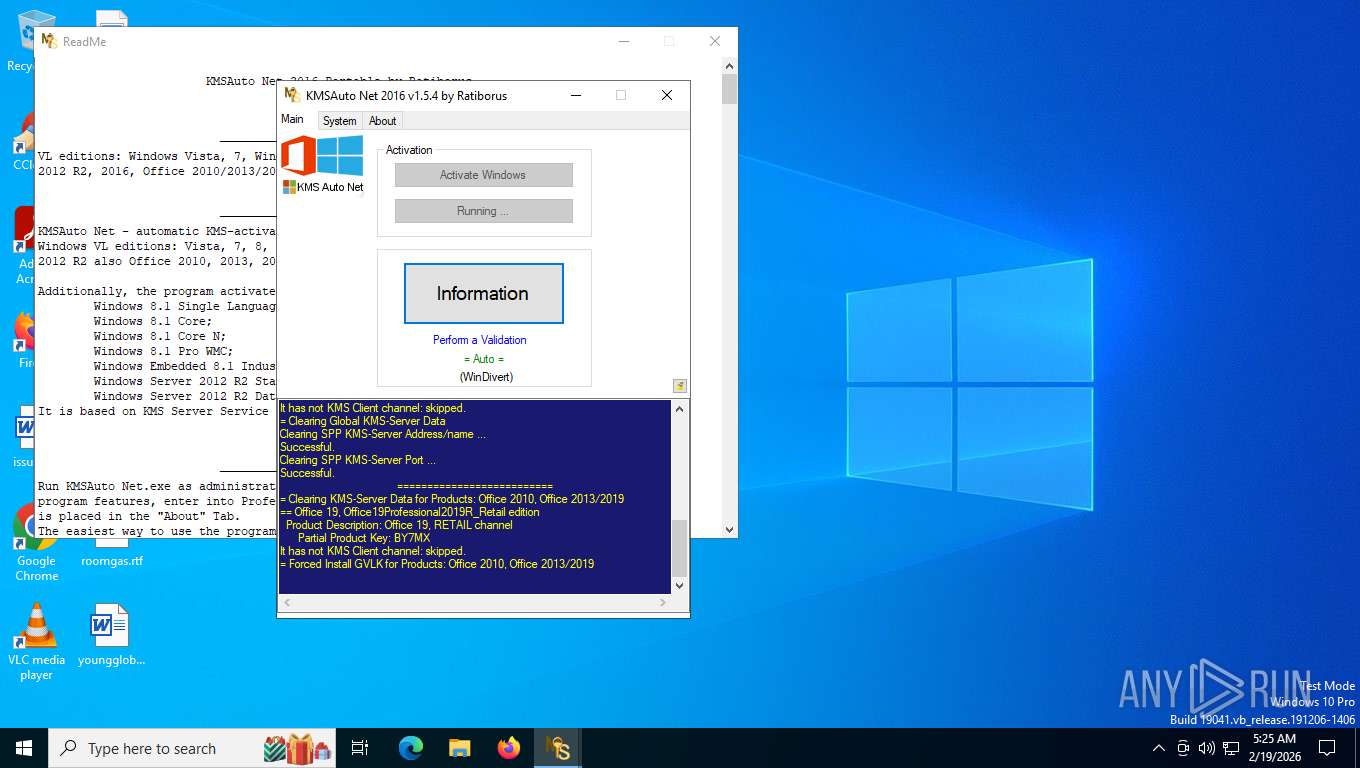
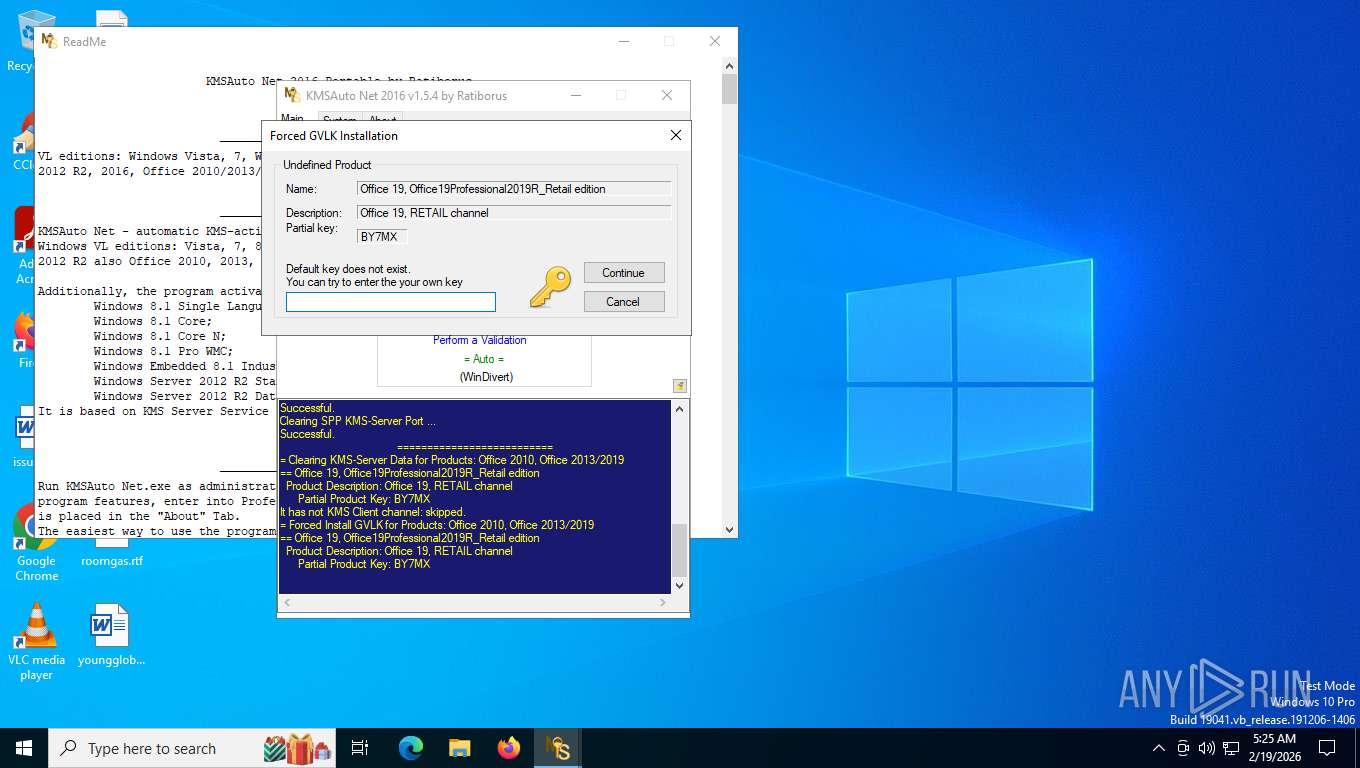
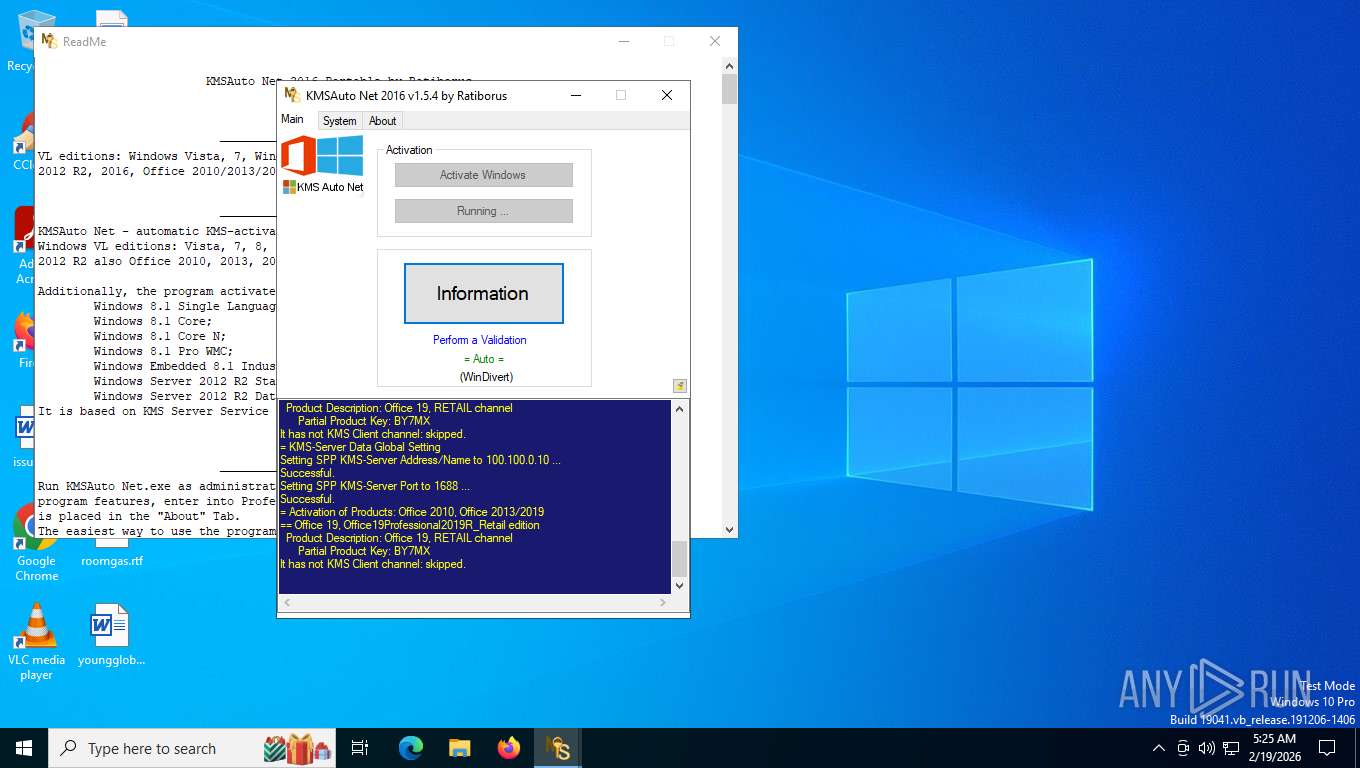
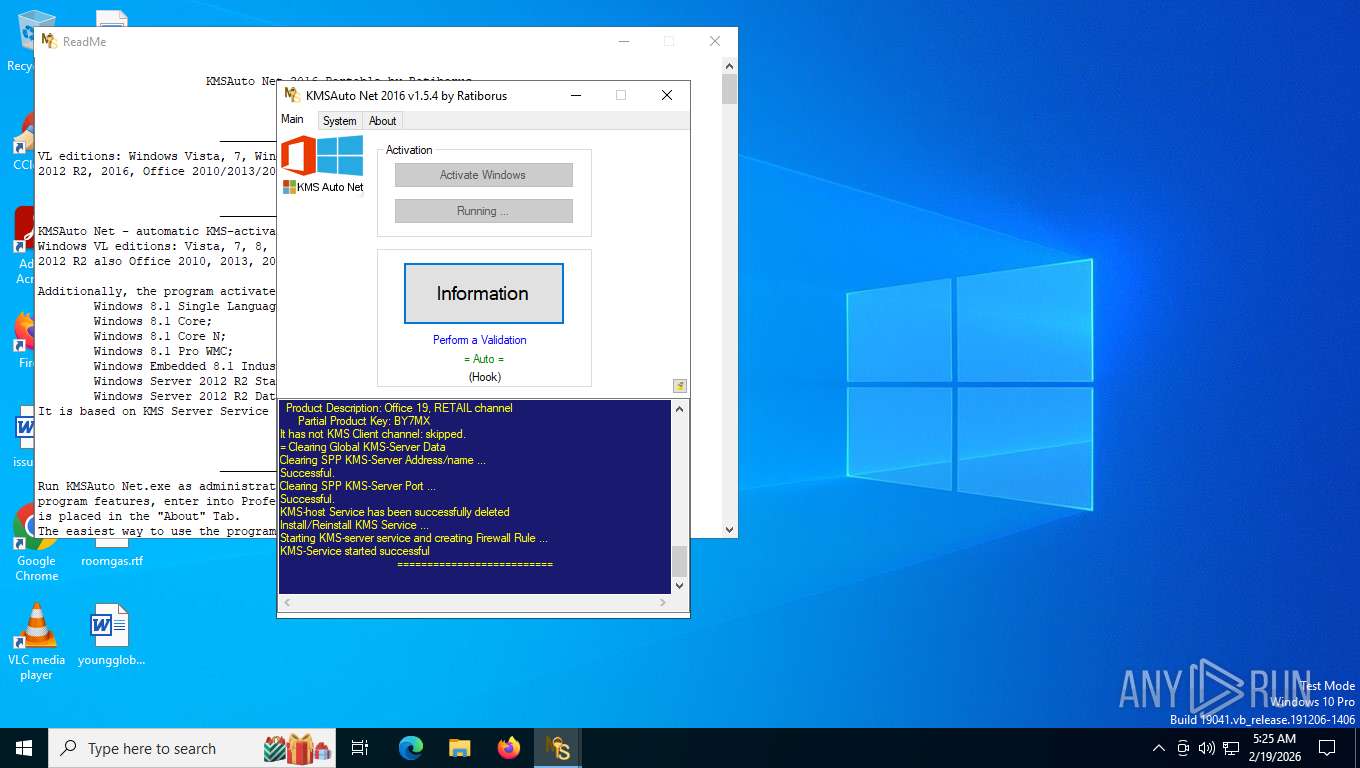
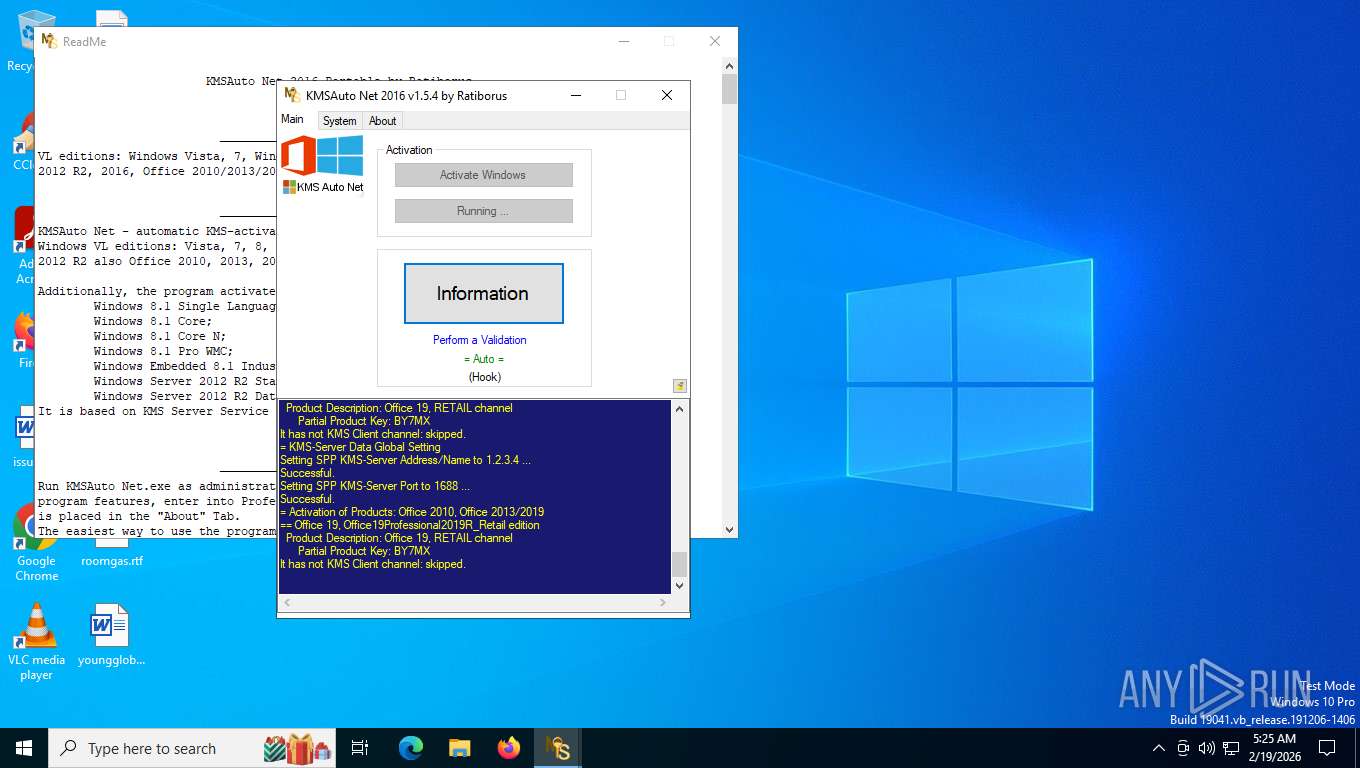
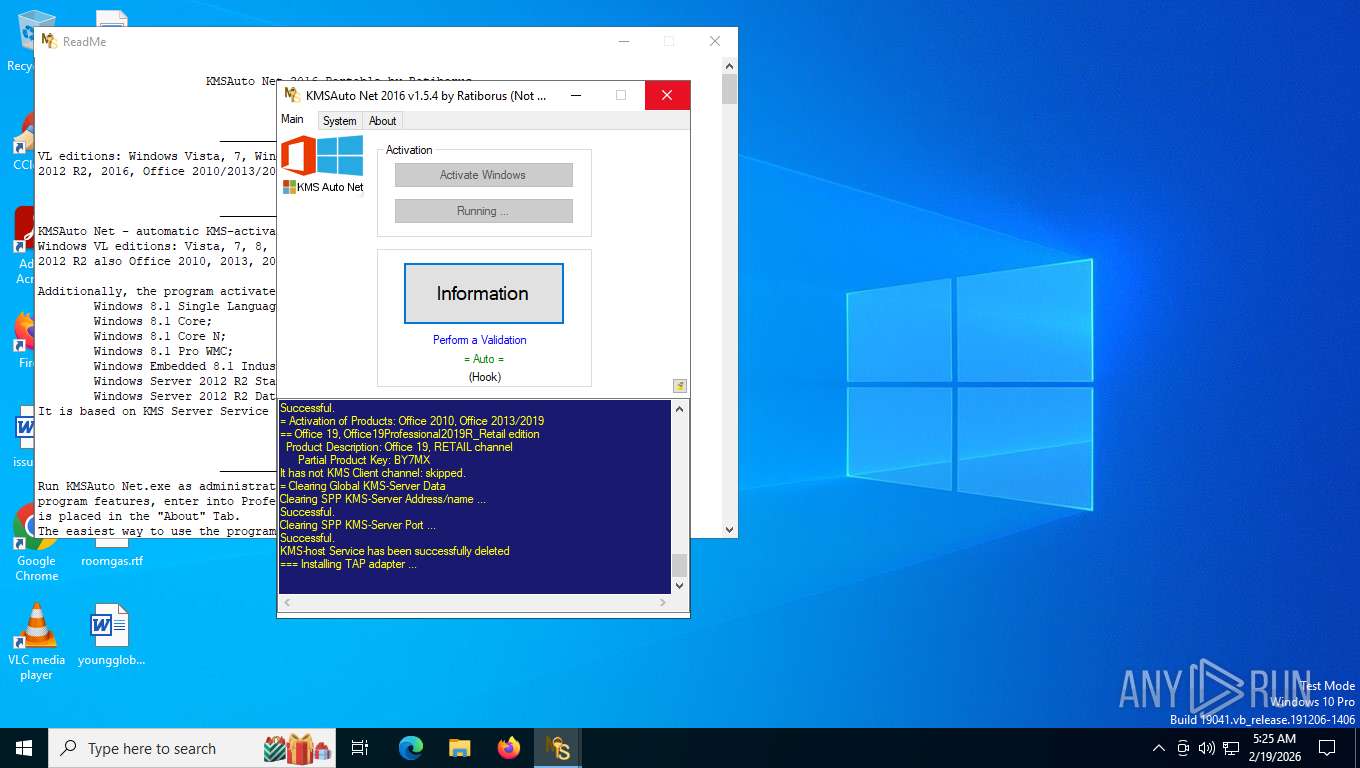
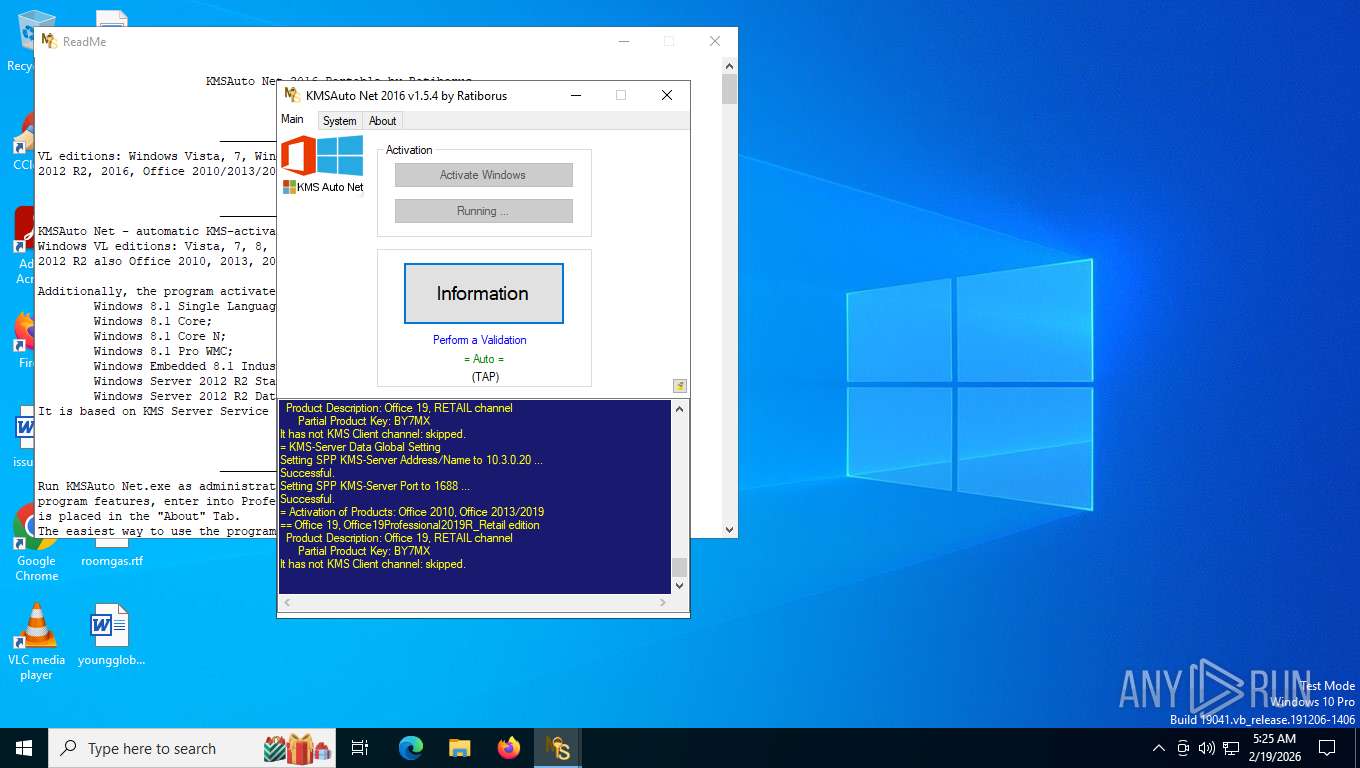
KMS tool has been detected
- KMSAuto Net.exe (PID: 8004)
- KMSAuto Net.exe (PID: 8344)
- KMSAuto Net.exe (PID: 8004)
Starts CMD.EXE for commands execution
- KMSAuto Net.exe (PID: 8004)
- cmd.exe (PID: 9112)
- cmd.exe (PID: 6940)
- cmd.exe (PID: 876)
Reads Internet Explorer settings
- KMSAuto Net.exe (PID: 8004)
File deletion via cmd.exe
- cmd.exe (PID: 8352)
- cmd.exe (PID: 6476)
- cmd.exe (PID: 6200)
- cmd.exe (PID: 7432)
- cmd.exe (PID: 3624)
- cmd.exe (PID: 3516)
- cmd.exe (PID: 6360)
- cmd.exe (PID: 5392)
- cmd.exe (PID: 7028)
- cmd.exe (PID: 6484)
- cmd.exe (PID: 4288)
- cmd.exe (PID: 5392)
- cmd.exe (PID: 524)
- cmd.exe (PID: 6148)
- cmd.exe (PID: 876)
- cmd.exe (PID: 7240)
- cmd.exe (PID: 1676)
- cmd.exe (PID: 5284)
- cmd.exe (PID: 508)
Adds/modifies Windows certificates
- certmgr.exe (PID: 2424)
- certmgr.exe (PID: 5888)
- certmgr.exe (PID: 7372)
- certmgr.exe (PID: 7476)
- certmgr.exe (PID: 3988)
- certmgr.exe (PID: 1684)
- devcon.exe (PID: 6544)
Starts application with an unusual extension
- cmd.exe (PID: 4336)
- cmd.exe (PID: 508)
- cmd.exe (PID: 7304)
- cmd.exe (PID: 7376)
- cmd.exe (PID: 1848)
- cmd.exe (PID: 2228)
- cmd.exe (PID: 7460)
- cmd.exe (PID: 2364)
- cmd.exe (PID: 1632)
- cmd.exe (PID: 8028)
- cmd.exe (PID: 4784)
- cmd.exe (PID: 3548)
- cmd.exe (PID: 8660)
Uses NETSH.EXE to delete a firewall rule or allowed programs
- KMSAuto Net.exe (PID: 8004)
Uses NETSH.EXE to add a firewall rule or allowed programs
- KMSAuto Net.exe (PID: 8004)
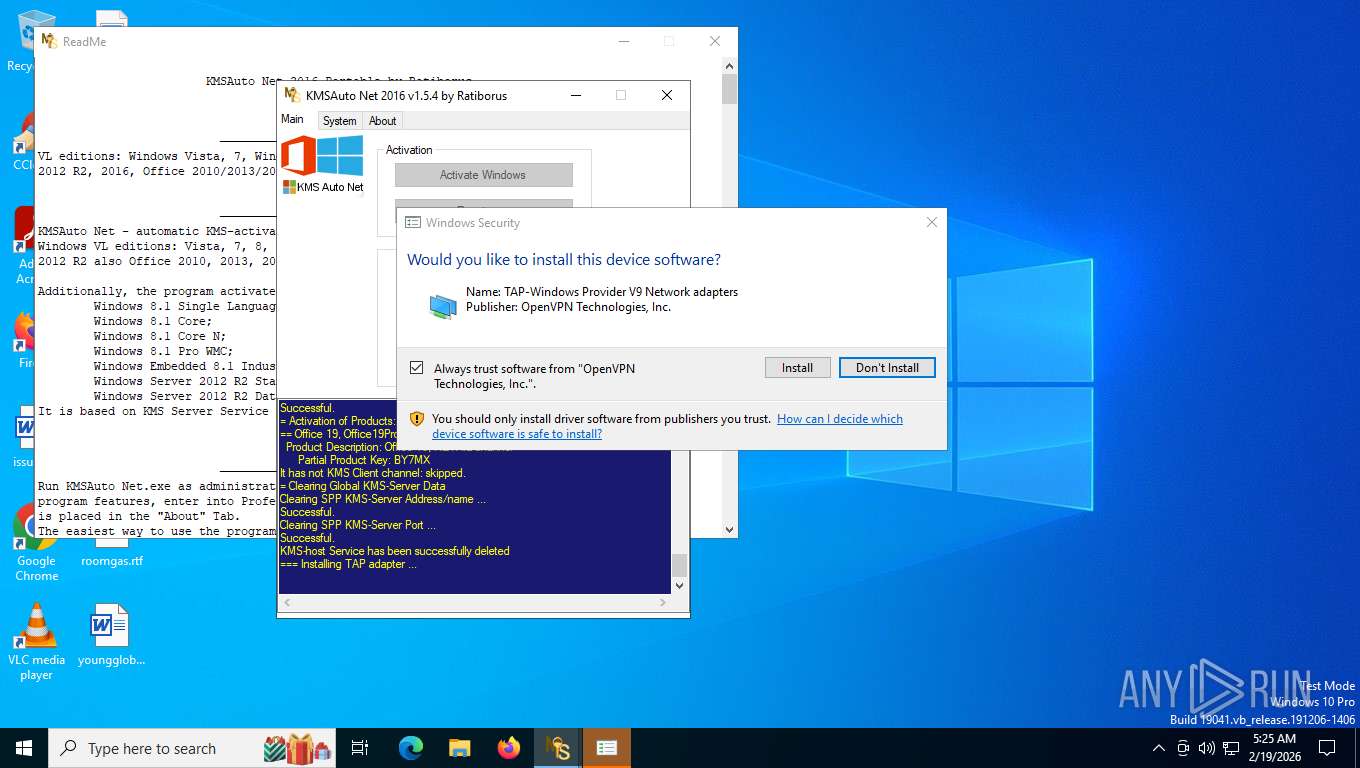
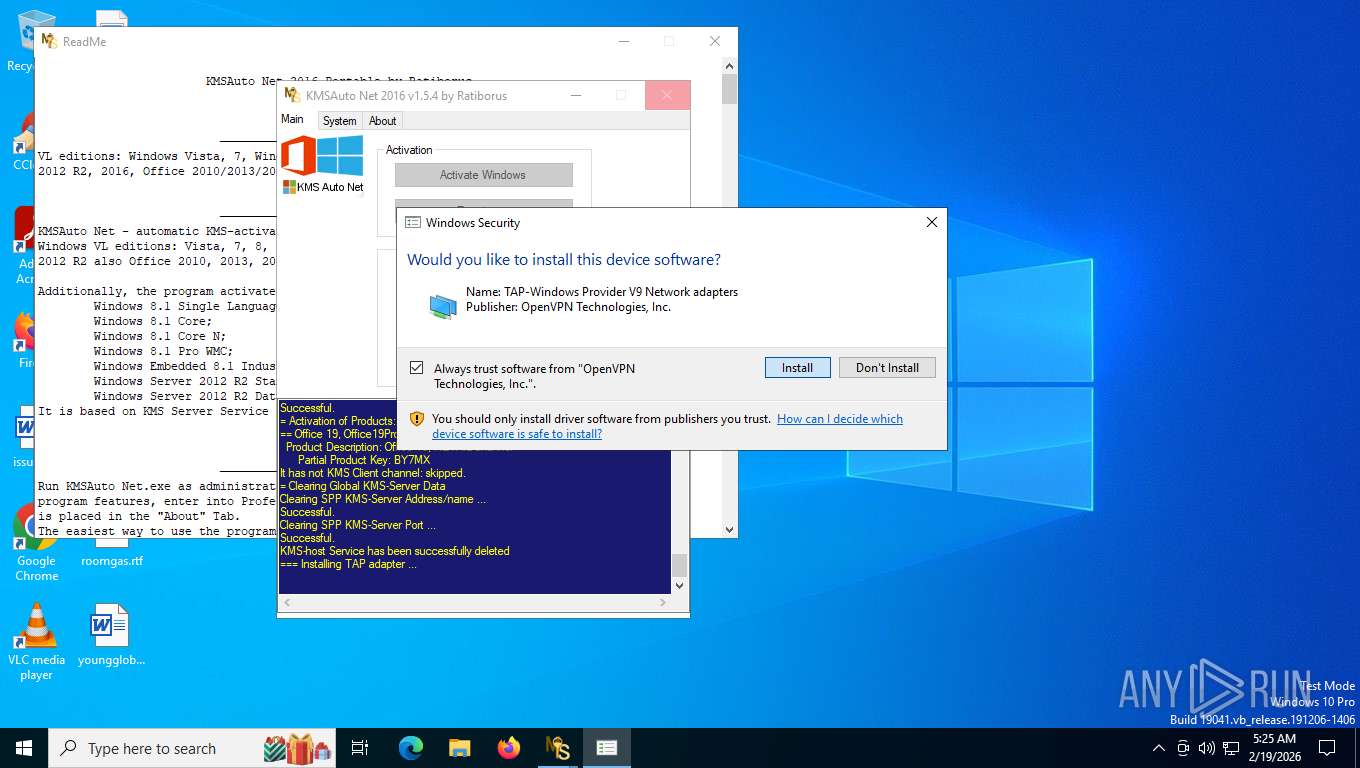
Drops a system driver (possible attempt to evade defenses)
- bin_x64.dat (PID: 1492)
- bin_x64.dat (PID: 7636)
- bin_x64.dat (PID: 9184)
- bin_x64.dat (PID: 2764)
- drvinst.exe (PID: 4300)
- devcon.exe (PID: 6544)
- drvinst.exe (PID: 4312)
- bin_x64.dat (PID: 3508)
- bin_x64.dat (PID: 5628)
Executable content was dropped or overwritten
- KMSAuto Net.exe (PID: 8004)
Application launched itself
- cmd.exe (PID: 9112)
- cmd.exe (PID: 6940)
- cmd.exe (PID: 876)
Creates a new Windows service
- sc.exe (PID: 6444)
- sc.exe (PID: 8776)
- sc.exe (PID: 4796)
Windows service management via SC.EXE
- sc.exe (PID: 4116)
- sc.exe (PID: 7788)
- sc.exe (PID: 2748)
- sc.exe (PID: 8916)
- sc.exe (PID: 1708)
- sc.exe (PID: 2368)
Creates or modifies Windows services
- KMSAuto Net.exe (PID: 8004)
Executes as Windows Service
- KMSSS.exe (PID: 8304)
- KMSSS.exe (PID: 9188)
- TunMirror.exe (PID: 7588)
- KMSSS.exe (PID: 4584)
Uses ROUTE.EXE to modify routing table
- cmd.exe (PID: 2096)
Uses REG/REGEDIT.EXE to modify registry
- KMSAuto Net.exe (PID: 8004)
- cmd.exe (PID: 2460)
- cmd.exe (PID: 9088)
Stops a currently running service
- sc.exe (PID: 1944)
- sc.exe (PID: 4680)
- sc.exe (PID: 8608)
Uses ROUTE.EXE to obtain the routing table information
- cmd.exe (PID: 6804)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 6000)
- cmd.exe (PID: 8760)
- cmd.exe (PID: 7488)
Uses WMIC.EXE
- cmd.exe (PID: 1424)
- cmd.exe (PID: 2256)
- cmd.exe (PID: 7972)
Suspicious use of NETSH.EXE
- cmd.exe (PID: 8052)
INFO
Creates a new folder
- cmd.exe (PID: 6156)
- cmd.exe (PID: 4288)
- cmd.exe (PID: 2340)
- cmd.exe (PID: 3588)
Create files in a temporary directory
- cmd.exe (PID: 7876)
- KMSAuto Net.exe (PID: 8004)
- SppPatcher_x64.dat (PID: 3536)
- cmd.exe (PID: 1424)
- cmd.exe (PID: 2256)
- devcon.exe (PID: 6544)
- cmd.exe (PID: 7972)
Reads the machine GUID from the registry
- KMSAuto Net.exe (PID: 8004)
- KMSSS.exe (PID: 8304)
- KMSSS.exe (PID: 9188)
- devcon.exe (PID: 6544)
- TunMirror.exe (PID: 4332)
- drvinst.exe (PID: 4312)
- KMSSS.exe (PID: 4584)
- TunMirror.exe (PID: 2608)
Checks supported languages
- KMSAuto Net.exe (PID: 8004)
- wzt.dat (PID: 5768)
- certmgr.exe (PID: 2424)
- certmgr.exe (PID: 5888)
- bin.dat (PID: 7580)
- bin_x64.dat (PID: 1492)
- AESDecoder.exe (PID: 6952)
- KMSSS.exe (PID: 8304)
- FakeClient.exe (PID: 7208)
- bin_x64.dat (PID: 7636)
- wzt.dat (PID: 7540)
- certmgr.exe (PID: 7372)
- certmgr.exe (PID: 7476)
- bin.dat (PID: 6240)
- AESDecoder.exe (PID: 4332)
- bin_x64.dat (PID: 9184)
- KMSSS.exe (PID: 9188)
- SppPatcher_x64.dat (PID: 3536)
- certmgr.exe (PID: 1684)
- AESDecoder.exe (PID: 4352)
- bin_x64.dat (PID: 2764)
- wzt.dat (PID: 8552)
- certmgr.exe (PID: 3988)
- bin.dat (PID: 3796)
- devcon.exe (PID: 6544)
- drvinst.exe (PID: 4300)
- TunMirror.exe (PID: 4332)
- drvinst.exe (PID: 4312)
- TunMirror.exe (PID: 7588)
- bin_x64.dat (PID: 3508)
- bin_x64.dat (PID: 5628)
- TunMirror.exe (PID: 2608)
- KMSSS.exe (PID: 4584)
Creates files or folders in the user directory
- KMSAuto Net.exe (PID: 8004)
Reads the computer name
- KMSAuto Net.exe (PID: 8004)
- FakeClient.exe (PID: 7208)
- KMSSS.exe (PID: 8304)
- KMSSS.exe (PID: 9188)
- devcon.exe (PID: 6544)
- drvinst.exe (PID: 4312)
- drvinst.exe (PID: 4300)
- TunMirror.exe (PID: 4332)
- TunMirror.exe (PID: 7588)
- KMSSS.exe (PID: 4584)
- TunMirror.exe (PID: 2608)
Reads product name
- KMSAuto Net.exe (PID: 8004)
There is functionality for taking screenshot (YARA)
- KMSAuto Net.exe (PID: 8004)
Reads Environment values
- KMSAuto Net.exe (PID: 8004)
UPX packer has been detected
- KMSAuto Net.exe (PID: 8004)
Creates files in the program directory
- wzt.dat (PID: 5768)
- cmd.exe (PID: 4288)
- KMSAuto Net.exe (PID: 8004)
- bin_x64.dat (PID: 1492)
- bin.dat (PID: 7580)
- AESDecoder.exe (PID: 6952)
- KMSSS.exe (PID: 8304)
- bin_x64.dat (PID: 7636)
- cmd.exe (PID: 2340)
- wzt.dat (PID: 7540)
- AESDecoder.exe (PID: 4332)
- bin_x64.dat (PID: 9184)
- bin.dat (PID: 6240)
- KMSSS.exe (PID: 9188)
- cmd.exe (PID: 3588)
- AESDecoder.exe (PID: 4352)
- bin.dat (PID: 3796)
- wzt.dat (PID: 8552)
- bin_x64.dat (PID: 2764)
- TunMirror.exe (PID: 4332)
- bin_x64.dat (PID: 3508)
- TunMirror.exe (PID: 2608)
- bin_x64.dat (PID: 5628)
- KMSSS.exe (PID: 4584)
FOR cycle in command line
- cmd.exe (PID: 9112)
- cmd.exe (PID: 6940)
- cmd.exe (PID: 876)
Adds a route via ROUTE.EXE
- ROUTE.EXE (PID: 8816)
Deletes a route via ROUTE.EXE
- ROUTE.EXE (PID: 5516)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 1984)
- WMIC.exe (PID: 7392)
- devcon.exe (PID: 6544)
- rundll32.exe (PID: 1080)
- WMIC.exe (PID: 9004)
- TunMirror.exe (PID: 4332)
Disables trace logs
- netsh.exe (PID: 748)
Changes settings of System certificates
- drvinst.exe (PID: 4312)
Adds/modifies Windows certificates
- drvinst.exe (PID: 4312)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (46.3) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (17.4) |
| .exe | | | UPX compressed Win32 Executable (17.1) |
| .scr | | | Windows screen saver (8.2) |
| .dll | | | Win32 Dynamic Link Library (generic) (4.1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:10:15 06:57:50+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32 |
| LinkerVersion: | 80 |
| CodeSize: | 8269824 |
| InitializedDataSize: | 49152 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x7e4fce |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.5.4.0 |
| ProductVersionNumber: | 1.5.4.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | MSFree Inc. |
| FileDescription: | KMSAuto Net |
| FileVersion: | 1.5.4 |
| InternalName: | KMSAuto Net.exe |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFileName: | KMSAuto Net.exe |
| ProductName: | KMSAuto Net |
| ProductVersion: | 1.5.4 |
| AssemblyVersion: | 1.5.4.0 |
Total processes
465
Monitored processes
311
Malicious processes
7
Suspicious processes
9
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 148 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 148 | C:\WINDOWS\Sysnative\reg delete "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\OfficeSoftwareProtectionPlatform\59A52881-A989-479D-AF46-F275C6370663" /f | C:\Windows\System32\reg.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 224 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | reg.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 412 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 508 | C:\WINDOWS\Sysnative\cmd.exe /D /c wzt.dat -y -pkmsauto | C:\Windows\System32\cmd.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 508 | C:\WINDOWS\Sysnative\cmd.exe /D /c del /F /Q "bin_x64.dat" | C:\Windows\System32\cmd.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 524 | C:\WINDOWS\Sysnative\cmd.exe /D /c del /F /Q "SppPatcher_x64.dat" | C:\Windows\System32\cmd.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 524 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 664 | C:\WINDOWS\Sysnative\cmd.exe /D /c certmgr.exe -add wzteam.cer -n wzteam -s -r localMachine TRUSTEDPUBLISHER | C:\Windows\System32\cmd.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 748 | C:\WINDOWS\Sysnative\reg delete "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\OfficeSoftwareProtectionPlatform\59A52881-A989-479D-AF46-F275C6370663" /f | C:\Windows\System32\reg.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
28 488
Read events
28 390
Write events
74
Delete events
24
Modification events
| (PID) Process: | (2424) certmgr.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates |
| Operation: | delete value | Name: | 648384A4DEE53D4C1C87E10D67CC99307CCC9C98 |
Value: | |||
| (PID) Process: | (2424) certmgr.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates\648384A4DEE53D4C1C87E10D67CC99307CCC9C98 |
| Operation: | write | Name: | Blob |
Value: 030000000100000014000000648384A4DEE53D4C1C87E10D67CC99307CCC9C982000000001000000FE010000308201FA30820167A00302010202108AC1A3101349C28A4D33947CFCD07662300906052B0E03021D05003011310F300D06035504031306575A5465616D301E170D3136313130323138343730365A170D3339313233313233353935395A3011310F300D06035504031306575A5465616D30819F300D06092A864886F70D010101050003818D0030818902818100AD2F8AA939C3EB40D1D6DE0509B9F4E7EBF8475B98C49E9FB4AD556D408E9B84E80D014078D65BE351E8A5D84CE2E92E84504F82E09DFA6C8310B58955527CEC2843039328B51891F2A09F70FD7E1348668A0AF780F741A30254397E9135220D442704C2395810A0A65B6B4EC54558E26C468C6087FD3BB1A1DE8414ADE68AAF0203010001A35B305930130603551D25040C300A06082B0601050507030330420603551D01043B30398010106AC14D8CB580F787E68A2938AB9BF3A1133011310F300D06035504031306575A5465616D82108AC1A3101349C28A4D33947CFCD07662300906052B0E03021D050003818100601D9E4107BECC4352D02281EC0764B2865E4ED60EE58228B7375D707730DEDE148E9ED41CE051C44D4E15D041CF8C601A054CA14B4A484F7DBAAB409E1D75CEBE6F8FA171E97E16EAE94B6757DA5C61B0B6F85CE2FEA31F50D664CC5BC1A40476A44EDDD5390357BC0D44C37B4969B5E4E923FEE772AFD4643B21BA918D40A8 | |||
| (PID) Process: | (5888) certmgr.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\TrustedPublisher\Certificates |
| Operation: | delete value | Name: | 648384A4DEE53D4C1C87E10D67CC99307CCC9C98 |
Value: | |||
| (PID) Process: | (5888) certmgr.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\TrustedPublisher\Certificates\648384A4DEE53D4C1C87E10D67CC99307CCC9C98 |
| Operation: | write | Name: | Blob |
Value: 030000000100000014000000648384A4DEE53D4C1C87E10D67CC99307CCC9C982000000001000000FE010000308201FA30820167A00302010202108AC1A3101349C28A4D33947CFCD07662300906052B0E03021D05003011310F300D06035504031306575A5465616D301E170D3136313130323138343730365A170D3339313233313233353935395A3011310F300D06035504031306575A5465616D30819F300D06092A864886F70D010101050003818D0030818902818100AD2F8AA939C3EB40D1D6DE0509B9F4E7EBF8475B98C49E9FB4AD556D408E9B84E80D014078D65BE351E8A5D84CE2E92E84504F82E09DFA6C8310B58955527CEC2843039328B51891F2A09F70FD7E1348668A0AF780F741A30254397E9135220D442704C2395810A0A65B6B4EC54558E26C468C6087FD3BB1A1DE8414ADE68AAF0203010001A35B305930130603551D25040C300A06082B0601050507030330420603551D01043B30398010106AC14D8CB580F787E68A2938AB9BF3A1133011310F300D06035504031306575A5465616D82108AC1A3101349C28A4D33947CFCD07662300906052B0E03021D050003818100601D9E4107BECC4352D02281EC0764B2865E4ED60EE58228B7375D707730DEDE148E9ED41CE051C44D4E15D041CF8C601A054CA14B4A484F7DBAAB409E1D75CEBE6F8FA171E97E16EAE94B6757DA5C61B0B6F85CE2FEA31F50D664CC5BC1A40476A44EDDD5390357BC0D44C37B4969B5E4E923FEE772AFD4643B21BA918D40A8 | |||
| (PID) Process: | (1672) NETSTAT.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\RFC1156Agent\CurrentVersion\Parameters |
| Operation: | write | Name: | TrapPollTimeMilliSecs |
Value: 15000 | |||
| (PID) Process: | (8004) KMSAuto Net.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\KMSEmulator |
| Operation: | write | Name: | ImagePath |
Value: "C:\ProgramData\KMSAuto\bin\KMSSS.exe" -Port 1688 -PWin RandomKMSPID -PO14 RandomKMSPID -PO15 RandomKMSPID -PO16 RandomKMSPID -AI 43200 -RI 43200 -Log -IP | |||
| (PID) Process: | (8004) KMSAuto Net.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\KMSEmulator |
| Operation: | write | Name: | Description |
Value: KMS-host for all Microsoft VL Products | |||
| (PID) Process: | (8004) KMSAuto Net.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\KMSEmulator |
| Operation: | write | Name: | DisplayName |
Value: KMS-host Service | |||
| (PID) Process: | (7372) certmgr.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates\648384A4DEE53D4C1C87E10D67CC99307CCC9C98 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (7372) certmgr.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates |
| Operation: | delete value | Name: | 648384A4DEE53D4C1C87E10D67CC99307CCC9C98 |
Value: | |||
Executable files
1
Suspicious files
0
Text files
0
Unknown types
146
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7876 | cmd.exe | C:\Users\admin\AppData\Local\Temp\test.test | binary | |
MD5:9F06243ABCB89C70E0C331C61D871FA7 | SHA256:837CCB607E312B170FAC7383D7CCFD61FA5072793F19A25E75FBACB56539B86B | |||
| 7580 | bin.dat | C:\ProgramData\KMSAuto\bin\TunMirror.exe | binary | |
MD5:2ED9C12A91E795804B1B770958C647AC | SHA256:CB56C248A38292C234D1AABE5E33A671FE8AE8AED28E0C8C4FBE767E4E7B82F5 | |||
| 1492 | bin_x64.dat | C:\ProgramData\KMSAuto\bin\driver\x64TAP2\tapoas.inf | binary | |
MD5:61243CB103543EE3163BF16DF69BCB54 | SHA256:1652B1DE2F15EEACBD06E0AB14ADA5A466316FFD3AB88D4A2A46CFCBD25FDFA1 | |||
| 7580 | bin.dat | C:\ProgramData\KMSAuto\bin\AESDecoder.exe | binary | |
MD5:B90ED3E4DBB23A464723706F12C86065 | SHA256:8391D5B724D235BA52531D9A6D85E466382CE15CBD6BA97C4AD1278ED1F03BD7 | |||
| 8004 | KMSAuto Net.exe | C:\Users\admin\AppData\Local\MSfree Inc\kmsauto.ini | binary | |
MD5:AF6A20FD7DFADCD582CCF2B1BFAAF82B | SHA256:0BEE97833A70AA9BA271E93226DACE849836C64919FBFE15543D694E219D4AF2 | |||
| 6952 | AESDecoder.exe | C:\ProgramData\KMSAuto\bin\TunMirror2.exe | binary | |
MD5:3B33E3AB6E91806DF4CAE19405AB8846 | SHA256:D9CD47831FABA4053225DAC181709FD7AB9D066C3DE6F541968FFFEEEE4A9BF9 | |||
| 8004 | KMSAuto Net.exe | C:\ProgramData\KMSAuto\bin_x64.dat | binary | |
MD5:B3600980E71C0C996DF5B1221B188AA3 | SHA256:8507A80748D27BA147535197BA043732DF5686BCAA089A2EF99D698569D8C6DD | |||
| 1492 | bin_x64.dat | C:\ProgramData\KMSAuto\bin\driver\x64TAP1\devcon.exe | binary | |
MD5:3904D0698962E09DA946046020CBCB17 | SHA256:A51E25ACC489948B31B1384E1DC29518D19B421D6BC0CED90587128899275289 | |||
| 1492 | bin_x64.dat | C:\ProgramData\KMSAuto\bin\driver\oas_sert.cer | binary | |
MD5:0041584E5F66762B1FA9BE8910D0B92B | SHA256:BB27684B569CBB72DEC63EA6FDEF8E5F410CDAEB73717EEE1B36478DBCFF94CC | |||
| 1492 | bin_x64.dat | C:\ProgramData\KMSAuto\bin\driver\x64TAP2\tapoas.cat | binary | |
MD5:8DC91F1BF59F58554DC195C9FFCB59EC | SHA256:0B42F01E4C8732D246260B6BA76A5E096E1DA3047898DFF6FB71EEDE68951C87 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
24
TCP/UDP connections
46
DNS requests
18
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
8176 | svchost.exe | GET | 304 | 40.127.240.158:443 | https://settings-win.data.microsoft.com/settings/v3.0/WSD/UpdateHealthTools?os=Windows&osVer=10.0.19041.1.amd64fre.vb_release.191206-&sku=48&deviceClass=Windows.Desktop&locale=en-US&deviceId=s:BAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&sampleId=s:95271487&appVer=10.0.19041.3626&FlightRing=Retail&TelemetryLevel=1&HidOverGattReg=C%3A%5CWINDOWS%5CSystem32%5CDriverStore%5CFileRepository%5Chidbthle.inf_amd64_9610b4821fdf82a5%5CMicrosoft.Bluetooth.Profiles.HidOverGatt.dll&AppVer=&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&OEMModel=DELL&UpdateOfferedDays=4294967295&ProcessorManufacturer=AuthenticAMD&InstallDate=1661339444&OEMModelBaseBoard=&BranchReadinessLevel=CB&OEMSubModel=J5CR&IsCloudDomainJoined=0&DeferFeatureUpdatePeriodInDays=30&IsDeviceRetailDemo=0&FlightingBranchName=&OSUILocale=en-US&DeviceFamily=Windows.Desktop&WuClientVer=10.0.19041.3996&UninstallActive=1&IsFlightingEnabled=0&OSSkuId=48&ProcessorClockSpeed=3094&TotalPhysicalRAM=6144&SecureBootCapable=0&App=SedimentPack&ProcessorCores=6&CurrentBranch=vb_release&InstallLanguage=en-US&DeferQualityUpdatePeriodInDays=0&OEMName_Uncleaned=DELL&TPMVersion=0&PrimaryDiskTotalCapacity=262144&InstallationType=Client&AttrDataVer=186&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&IsEdgeWithChromiumInstalled=1&OSVersion=10.0.19045.4046&IsMDMEnrolled=0&ActivationChannel=Retail&FirmwareVersion=A.40&TrendInstalledKey=1&OSArchitecture=AMD64&DefaultUserRegion=244&UpdateManagementGroup=2 | US | — | — | whitelisted |
6768 | MoUsoCoreWorker.exe | GET | 304 | 40.127.240.158:443 | https://settings-win.data.microsoft.com/settings/v3.0/OneSettings/Client?OSVersionFull=10.0.19045.4046.amd64fre.vb_release.191206-1406&LocalDeviceID=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&FlightRing=Retail&AttrDataVer=186&OSUILocale=en-US&OSSkuId=48&App=WOSC&AppVer=&IsFlightingEnabled=0&TelemetryLevel=1&DeviceFamily=Windows.Desktop | US | — | — | whitelisted |
4952 | SIHClient.exe | GET | 304 | 74.178.76.128:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | US | — | — | whitelisted |
4952 | SIHClient.exe | GET | 200 | 135.233.95.135:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | US | — | — | whitelisted |
4952 | SIHClient.exe | GET | 200 | 74.178.76.128:443 | https://slscr.update.microsoft.com/sls/ping | US | — | — | whitelisted |
4952 | SIHClient.exe | GET | 304 | 74.178.76.128:443 | https://slscr.update.microsoft.com/SLS/%7BE7A50285-D08D-499D-9FF8-180FDC2332BC%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | US | — | — | whitelisted |
8176 | svchost.exe | GET | 200 | 51.104.136.2:443 | https://settings-win.data.microsoft.com/settings/v3.0/WSD/WaaSAssessment?os=Windows&osVer=10.0.19041.1.amd64fre.vb_release.191206-&ring=Retail&sku=48&deviceClass=Windows.Desktop&locale=en-US&deviceId=BAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&FlightRing=Retail&TelemetryLevel=1&HidOverGattReg=C%3A%5CWINDOWS%5CSystem32%5CDriverStore%5CFileRepository%5Chidbthle.inf_amd64_9610b4821fdf82a5%5CMicrosoft.Bluetooth.Profiles.HidOverGatt.dll&AppVer=10.0&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&OEMModel=DELL&UpdateOfferedDays=4294967295&ProcessorManufacturer=AuthenticAMD&InstallDate=1661339444&OEMModelBaseBoard=&BranchReadinessLevel=CB&OEMSubModel=J5CR&IsCloudDomainJoined=0&DeferFeatureUpdatePeriodInDays=30&IsDeviceRetailDemo=0&FlightingBranchName=&OSUILocale=en-US&DeviceFamily=Windows.Desktop&WuClientVer=10.0.19041.3996&UninstallActive=1&IsFlightingEnabled=0&OSSkuId=48&ProcessorClockSpeed=3094&TotalPhysicalRAM=6144&SecureBootCapable=0&App=WaaSAssessment&ProcessorCores=6&CurrentBranch=vb_release&InstallLanguage=en-US&DeferQualityUpdatePeriodInDays=0&ServicingBranch=CB&OEMName_Uncleaned=DELL&TPMVersion=0&PrimaryDiskTotalCapacity=262144&InstallationType=Client&AttrDataVer=186&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&IsEdgeWithChromiumInstalled=1&OSVersion=10.0.19045.4046&IsMDMEnrolled=0&ActivationChannel=Retail&HonorWUfBDeferrals=0&FirmwareVersion=A.40&TrendInstalledKey=1&OSArchitecture=AMD64&DefaultUserRegion=244&UpdateManagementGroup=2 | US | — | 5.70 Kb | whitelisted |
8176 | svchost.exe | GET | 200 | 23.216.77.25:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
8176 | svchost.exe | GET | 200 | 23.59.18.102:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | US | binary | 814 b | whitelisted |
356 | svchost.exe | POST | 200 | 20.190.159.129:443 | https://login.live.com/RST2.srf | US | binary | 11.1 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
8176 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7532 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
8176 | svchost.exe | 23.216.77.25:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
8176 | svchost.exe | 23.59.18.102:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
8176 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3412 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
8176 | svchost.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
Process | Message |
|---|---|
FakeClient.exe | WdfCoInstaller: [02/19/2026 05:25.20.021] ReadComponents: WdfSection for Driver Service windivert using KMDF lib version Major 0x1, minor 0x9
|
FakeClient.exe | WdfCoInstaller: [02/19/2026 05:25.20.036] BootApplication: could not open service windivert, error error(1060) The specified service does not exist as an installed service.
|
FakeClient.exe | WdfCoInstaller: [02/19/2026 05:25.20.036] BootApplication: GetStartType error error(87) The parameter is incorrect.
Driver Service name windivert
|