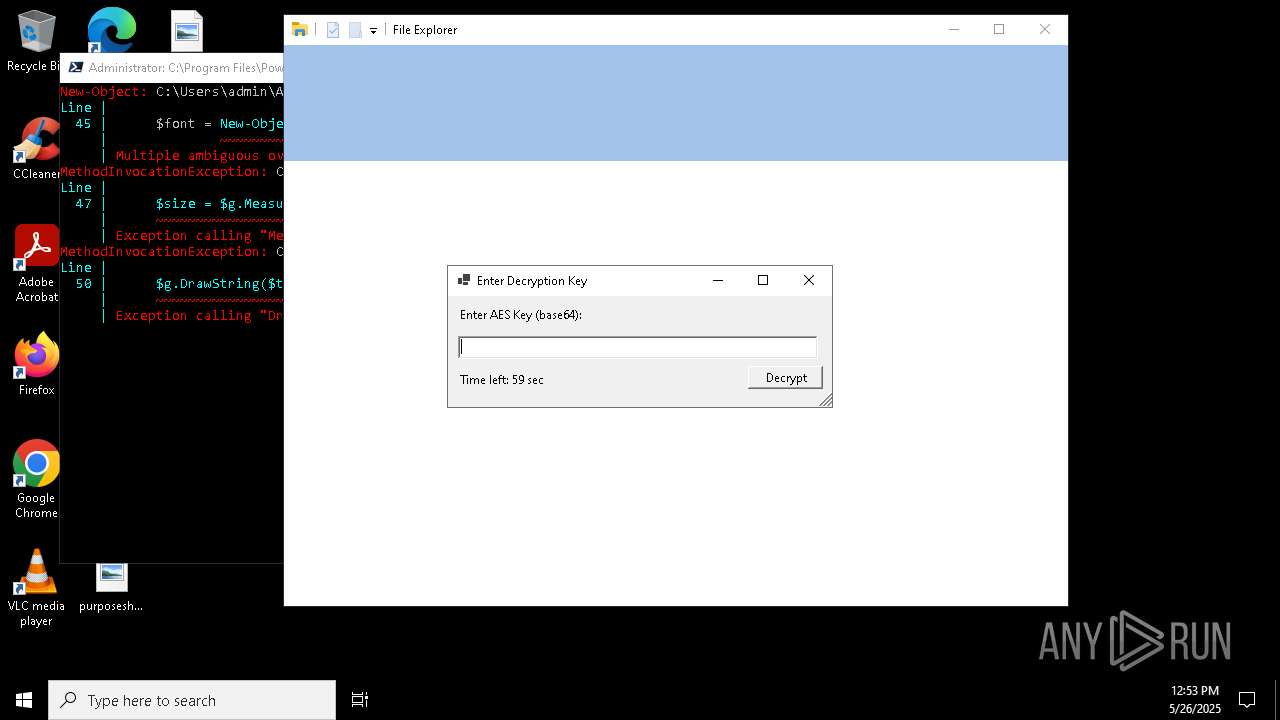
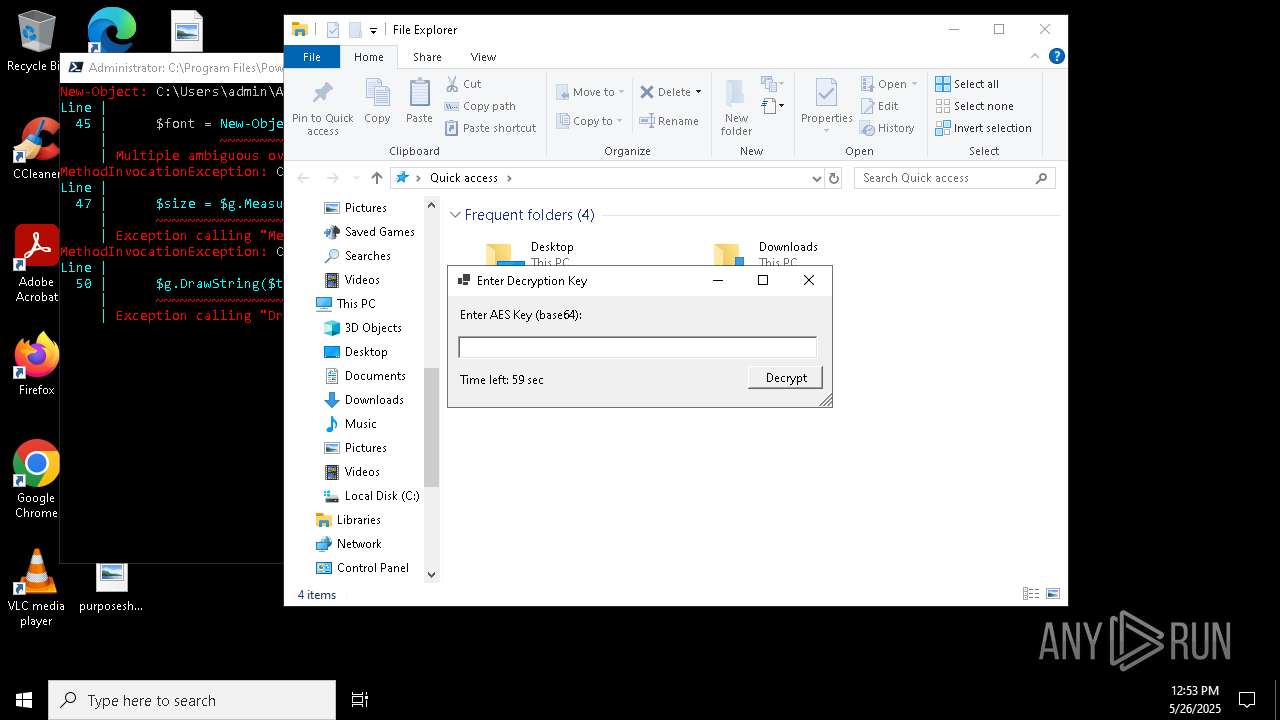
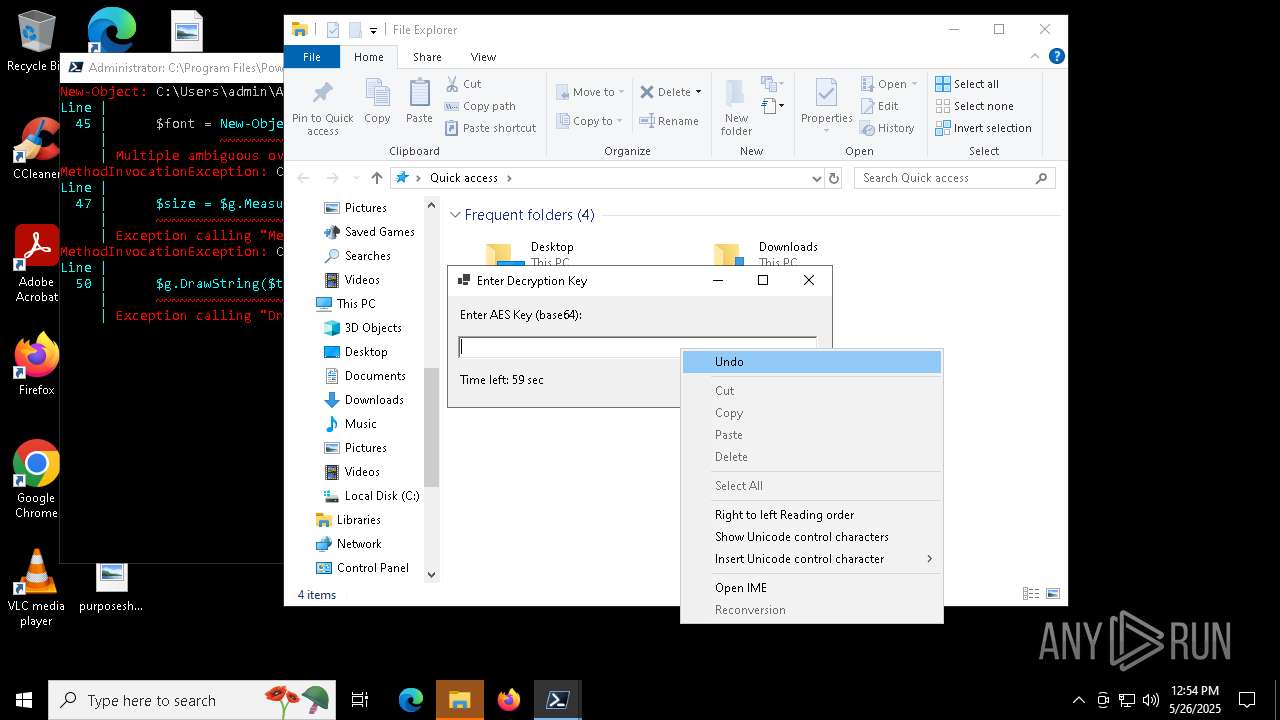
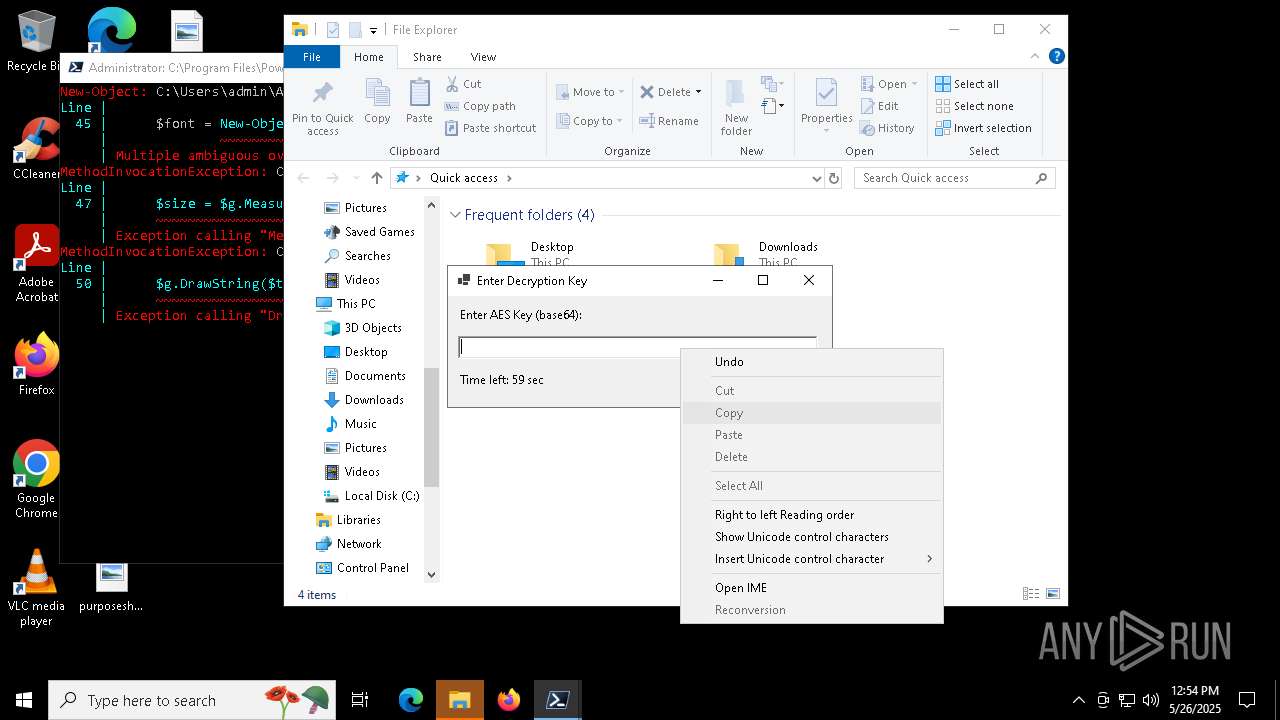
| File name: | script.ps1 |
| Full analysis: | https://app.any.run/tasks/29d20340-3e63-4eb0-9a13-3a5e8427c568 |
| Verdict: | Malicious activity |
| Analysis date: | May 26, 2025, 12:53:32 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/javascript |
| File info: | JavaScript source, Unicode text, UTF-8 text, with CRLF line terminators |
| MD5: | FBC6B98D05F8161D8F3365623C506357 |
| SHA1: | B64B342CF2C58022A6A1D1C83EB07F31A13F325C |
| SHA256: | B47B8BFC6C17EB267DA62976E088EA4DCF1058AD5724344A80C6FF6DF3590217 |
| SSDEEP: | 192:L4EVtZFXsooqZdT6+GM3I0AN04w1eTn08Bymhjr9jYp6gID70QfNiB:NZ0qZl6ZAI0OwUTn931VYsC |
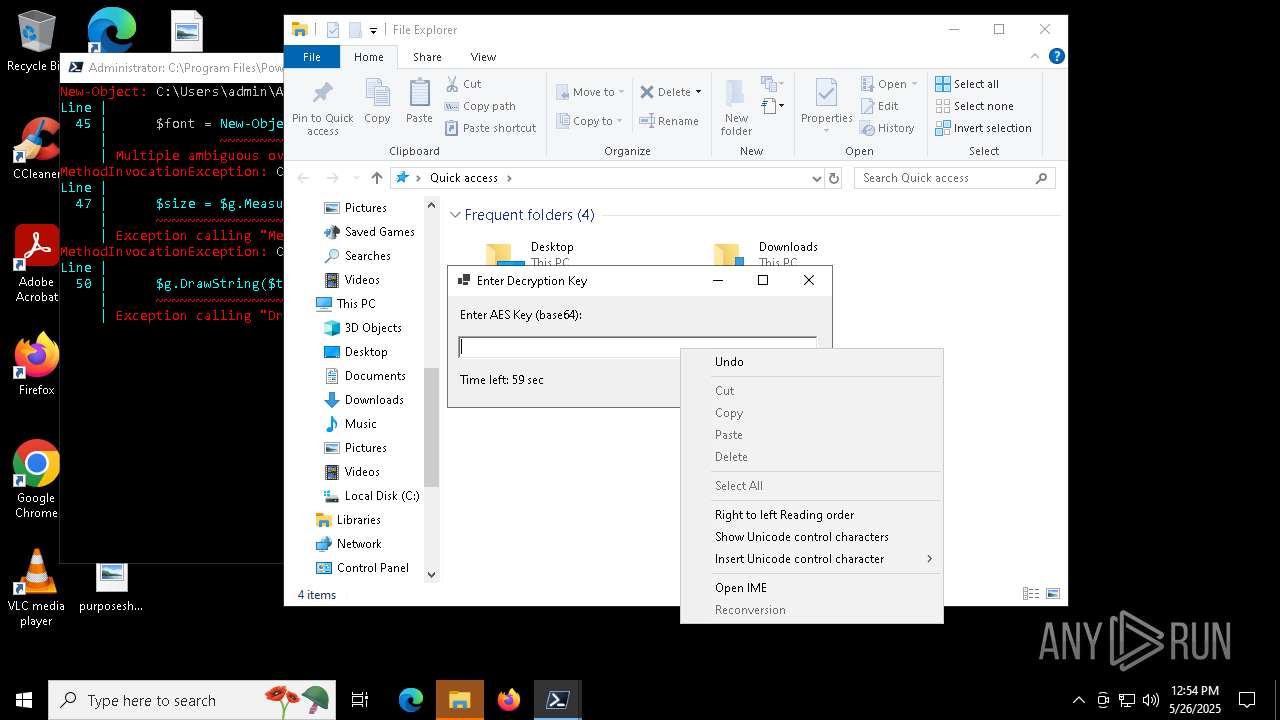
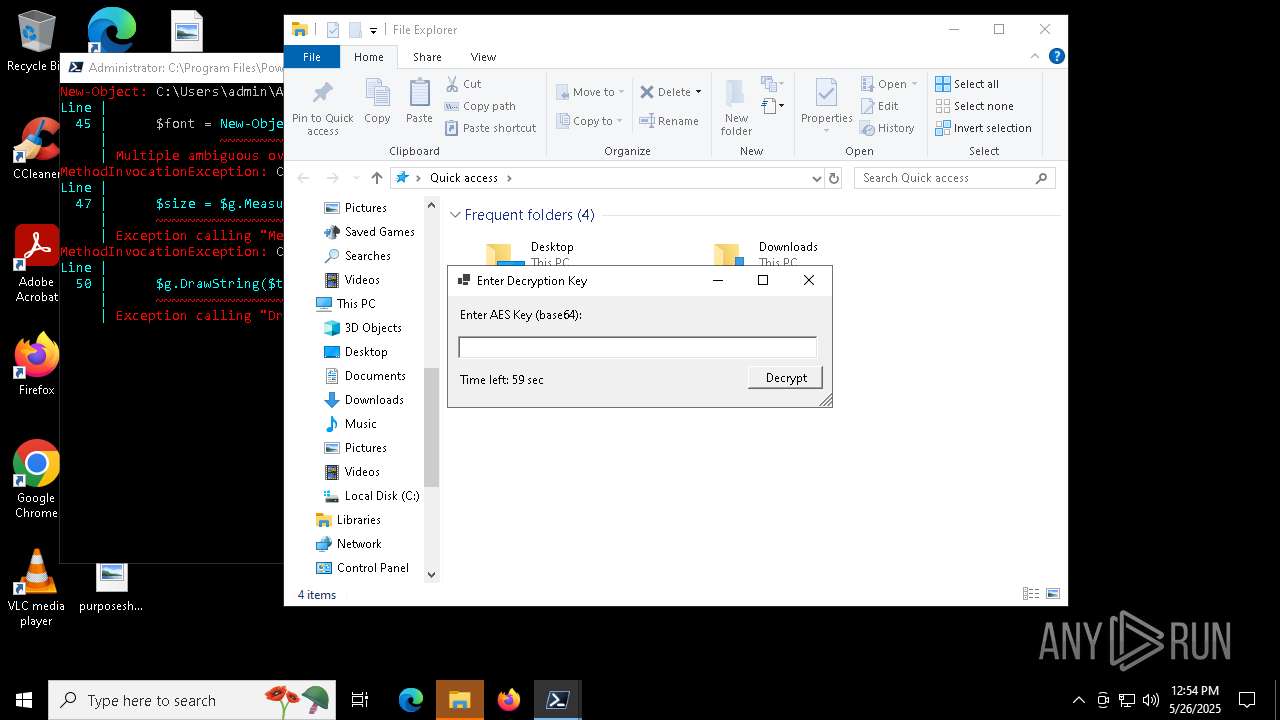
MALICIOUS
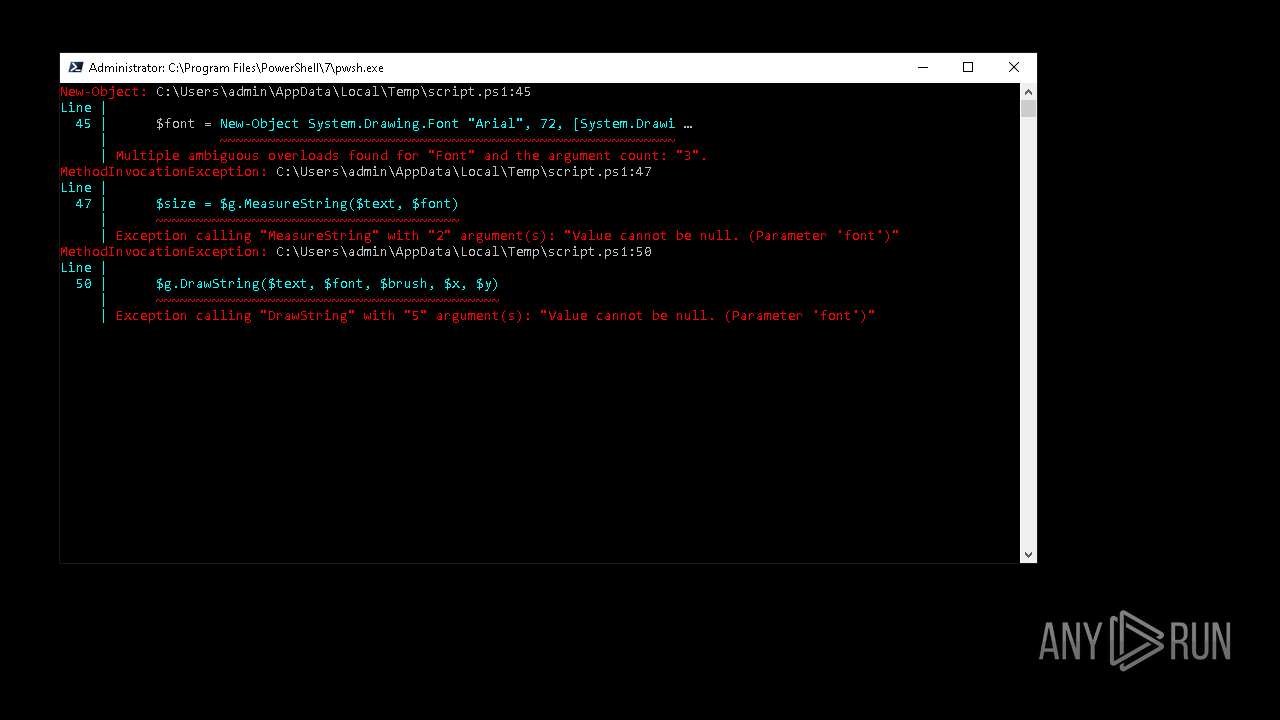
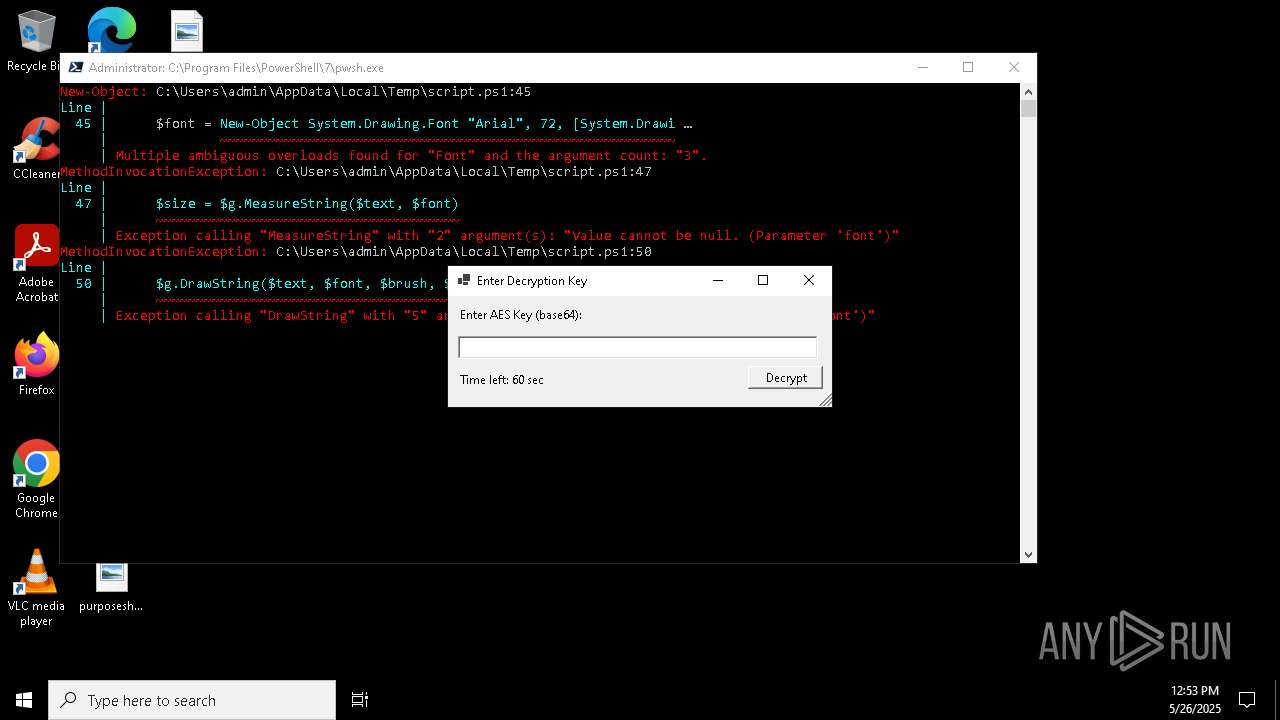
Bypass execution policy to execute commands
- powershell.exe (PID: 7440)
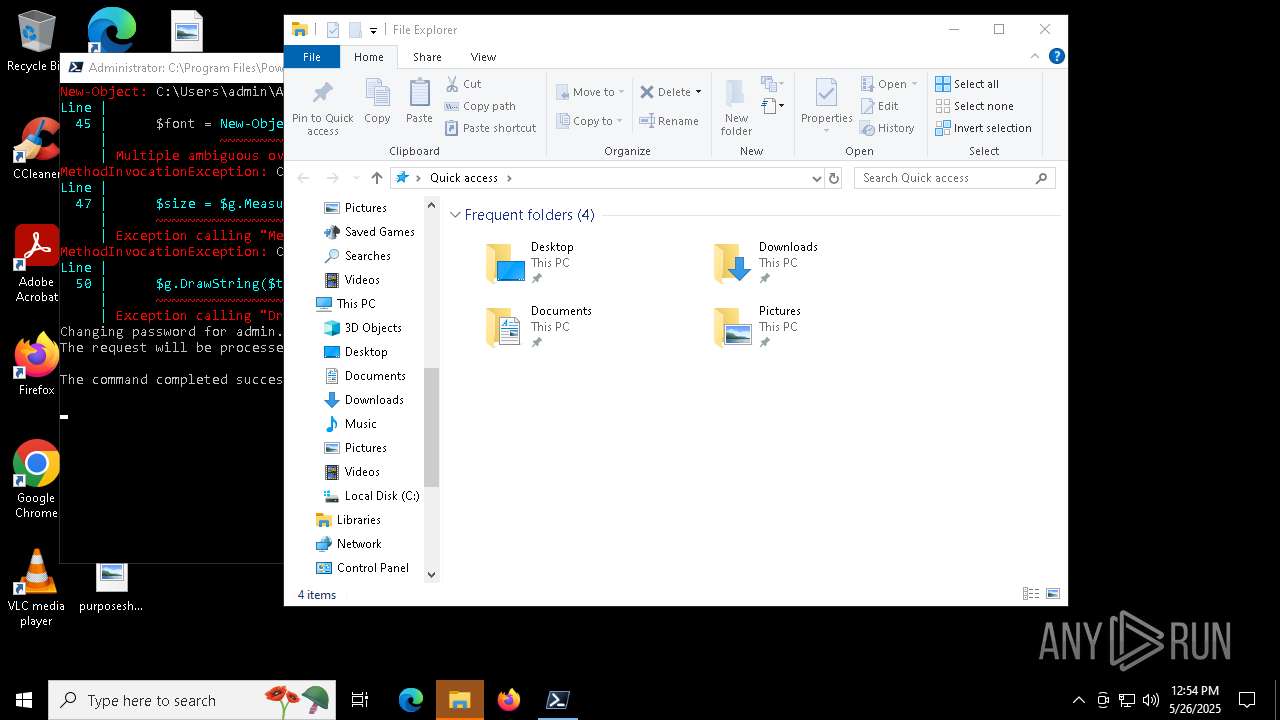
Starts NET.EXE to view/add/change user profiles
- net.exe (PID: 5700)
- pwsh.exe (PID: 7860)
- net.exe (PID: 7060)
SUSPICIOUS
Reads the date of Windows installation
- pwsh.exe (PID: 7860)
- StartMenuExperienceHost.exe (PID: 976)
Reads security settings of Internet Explorer
- GameBar.exe (PID: 732)
- StartMenuExperienceHost.exe (PID: 976)
Checks a user's role membership (POWERSHELL)
- powershell.exe (PID: 7440)
The process executes via Task Scheduler
- explorer.exe (PID: 8100)
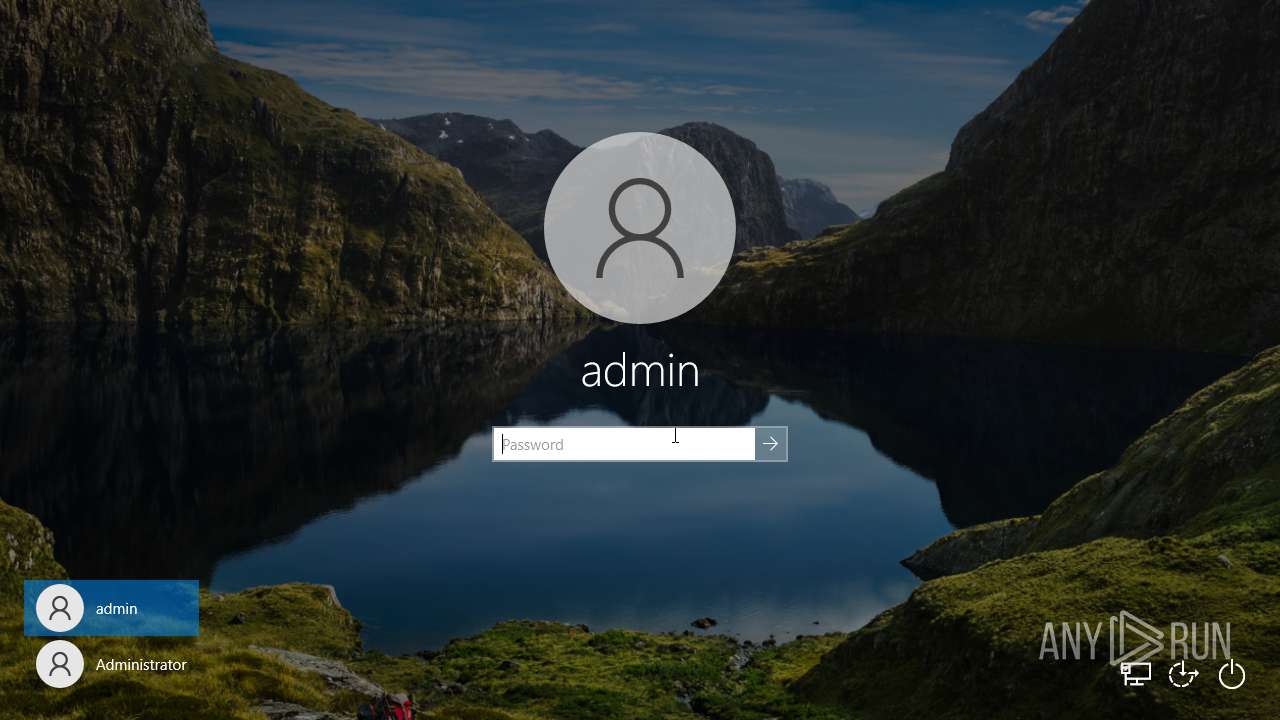
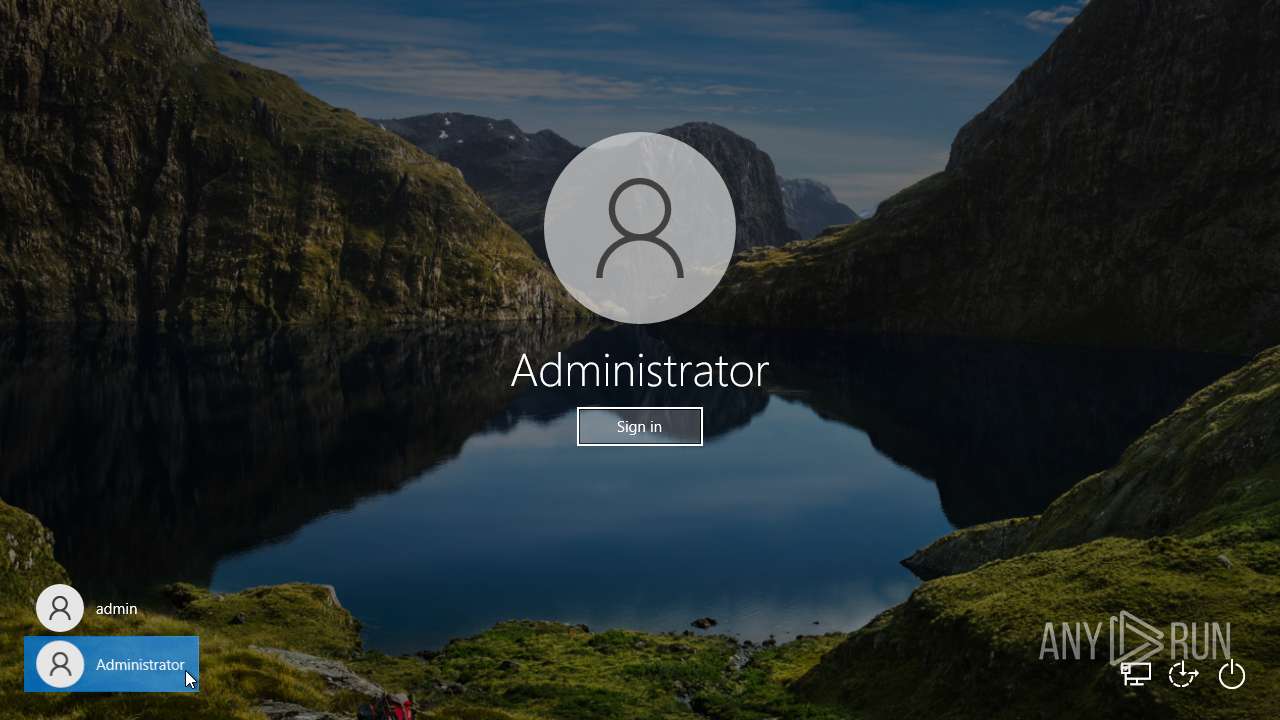
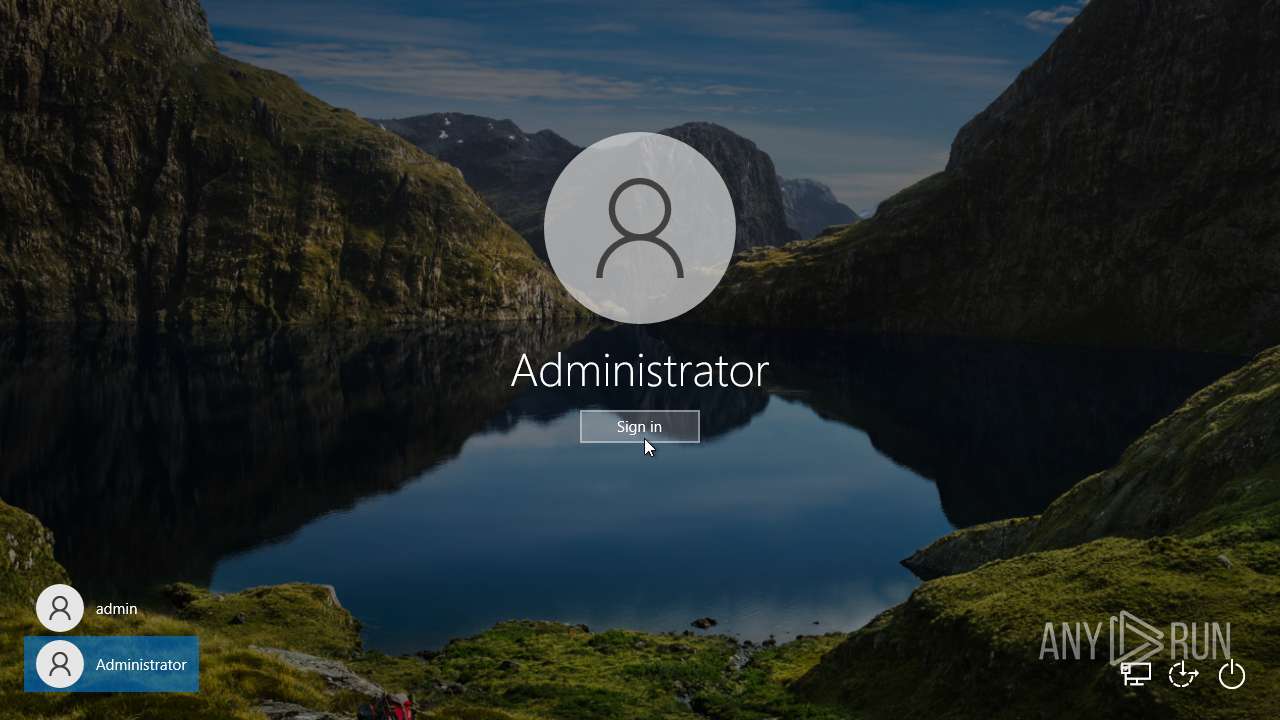
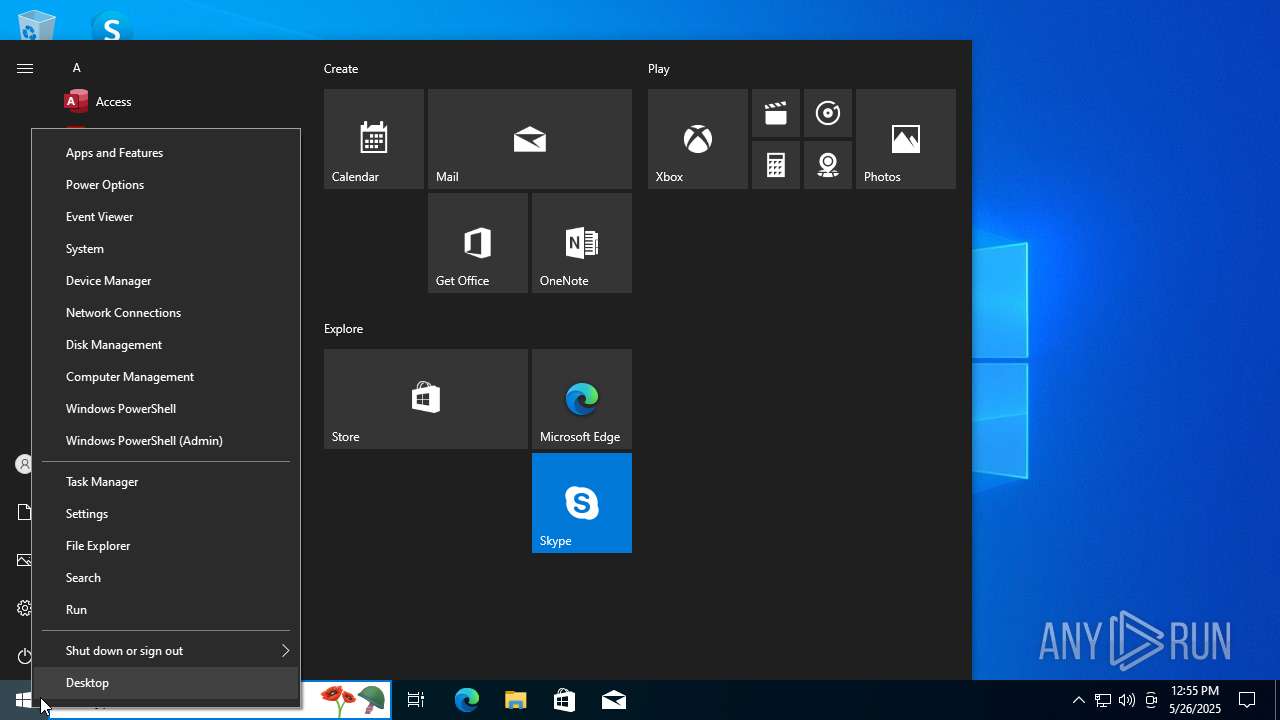
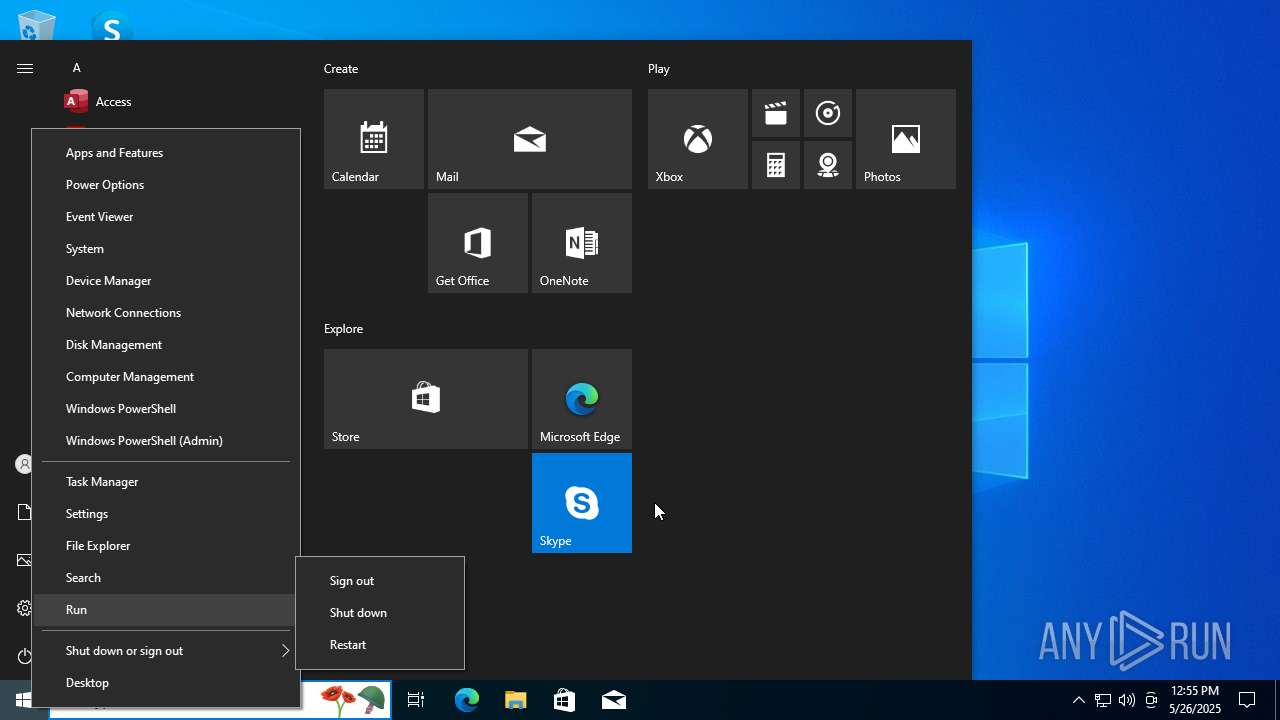
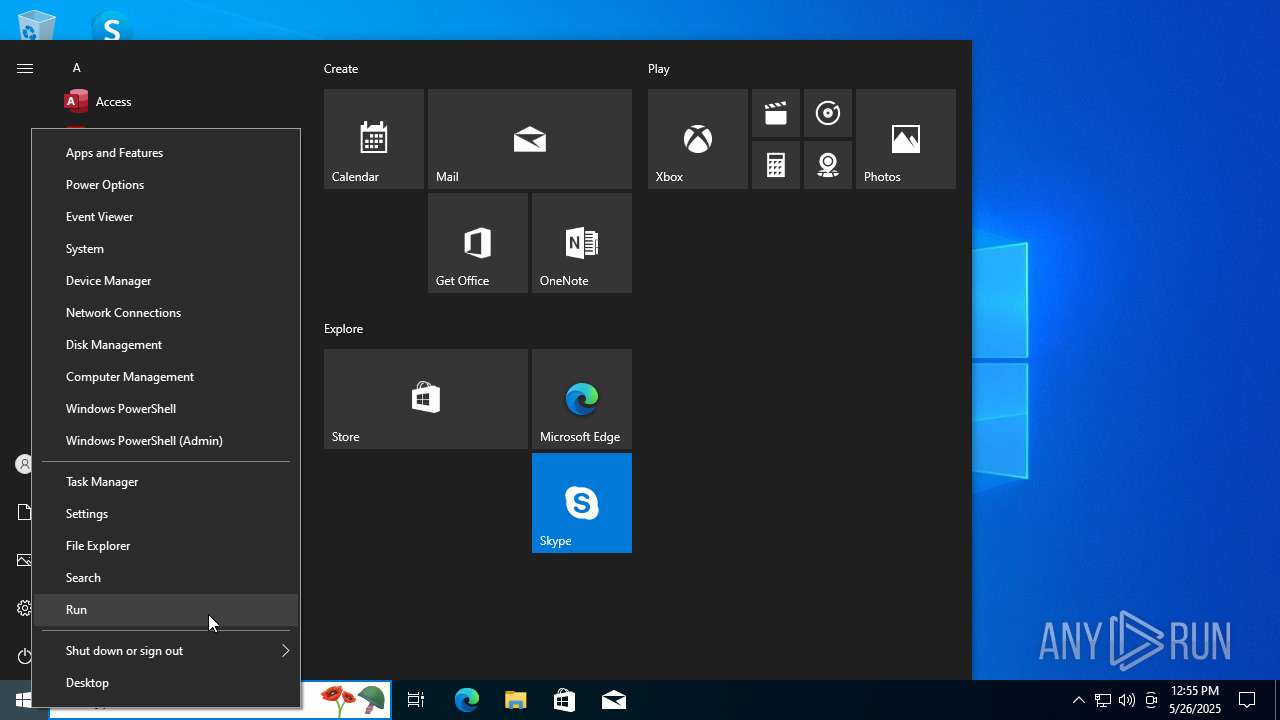
The system shut down or reboot
- pwsh.exe (PID: 7860)
INFO
Reads the computer name
- pwsh.exe (PID: 7860)
- TextInputHost.exe (PID: 4428)
- GameBar.exe (PID: 732)
- StartMenuExperienceHost.exe (PID: 976)
- SearchApp.exe (PID: 7632)
Checks supported languages
- pwsh.exe (PID: 7860)
- GameBar.exe (PID: 732)
- TextInputHost.exe (PID: 4428)
- StartMenuExperienceHost.exe (PID: 976)
- SearchApp.exe (PID: 7632)
Process checks computer location settings
- pwsh.exe (PID: 7860)
- StartMenuExperienceHost.exe (PID: 976)
- SearchApp.exe (PID: 7632)
Checks proxy server information
- SearchApp.exe (PID: 7632)
Reads the machine GUID from the registry
- SearchApp.exe (PID: 7632)
Reads Environment values
- SearchApp.exe (PID: 7632)
Reads the software policy settings
- SearchApp.exe (PID: 7632)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
153
Monitored processes
19
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 732 | "C:\Program Files\WindowsApps\Microsoft.XboxGamingOverlay_2.34.28001.0_x64__8wekyb3d8bbwe\GameBar.exe" -ServerName:App.AppXbdkk0yrkwpcgeaem8zk81k8py1eaahny.mca | C:\Program Files\WindowsApps\Microsoft.XboxGamingOverlay_2.34.28001.0_x64__8wekyb3d8bbwe\GameBar.exe | — | svchost.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 976 | "C:\WINDOWS\SystemApps\Microsoft.Windows.StartMenuExperienceHost_cw5n1h2txyewy\StartMenuExperienceHost.exe" -ServerName:App.AppXywbrabmsek0gm3tkwpr5kwzbs55tkqay.mca | C:\Windows\SystemApps\Microsoft.Windows.StartMenuExperienceHost_cw5n1h2txyewy\StartMenuExperienceHost.exe | — | svchost.exe | |||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 2260 | C:\WINDOWS\system32\net1 user admin W2HcMLerpCGMEoE2Hc7m46kEuU6QFOwJeFbq4rPdQQXSxSX208iBKitVcReXL9I8 /domain | C:\Windows\System32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3980 | "C:\WINDOWS\system32\shutdown.exe" /l /f | C:\Windows\System32\shutdown.exe | — | pwsh.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Shutdown and Annotation Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4260 | C:\WINDOWS\System32\mobsync.exe -Embedding | C:\Windows\System32\mobsync.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Sync Center Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4428 | "C:\WINDOWS\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe" -ServerName:InputApp.AppXjd5de1g66v206tj52m9d0dtpppx4cgpn.mca | C:\Windows\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Version: 123.26505.0.0 Modules
| |||||||||||||||
| 5248 | C:\WINDOWS\System32\rundll32.exe shell32.dll,SHCreateLocalServerRunDll {9BA05972-F6A8-11CF-A442-00A0C90A8F39} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5700 | "C:\WINDOWS\system32\net.exe" user admin W2HcMLerpCGMEoE2Hc7m46kEuU6QFOwJeFbq4rPdQQXSxSX208iBKitVcReXL9I8 /domain | C:\Windows\System32\net.exe | — | pwsh.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6088 | C:\WINDOWS\system32\net1 user admin W2HcMLerpCGMEoE2Hc7m46kEuU6QFOwJeFbq4rPdQQXSxSX208iBKitVcReXL9I8 | C:\Windows\System32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7060 | "C:\WINDOWS\system32\net.exe" user admin W2HcMLerpCGMEoE2Hc7m46kEuU6QFOwJeFbq4rPdQQXSxSX208iBKitVcReXL9I8 | C:\Windows\System32\net.exe | — | pwsh.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
18 191
Read events
18 086
Write events
97
Delete events
8
Modification events
| (PID) Process: | (8064) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\MountPoints2\CPC\Volume\{eaf65672-68c3-4f99-8d5c-104b5f4d8fff} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (8064) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\MountPoints2\CPC\Volume\{2f5c5e73-85a9-11eb-90a8-9a9b76358421} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (8064) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\MountPoints2\CPC\Volume\{2f5c5e72-85a9-11eb-90a8-9a9b76358421} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (8064) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\MountPoints2\CPC\Volume\{2f5c5e71-85a9-11eb-90a8-9a9b76358421} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (8064) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\MountPoints2\CPC\Volume |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (732) GameBar.exe | Key: | \REGISTRY\A\{7acfcc82-578e-b376-c3e8-56b09bb30581}\LocalState |
| Operation: | write | Name: | CurrentDisplayMonitor |
Value: 670061006D0065000000C1A336363DCEDB01 | |||
| (PID) Process: | (732) GameBar.exe | Key: | \REGISTRY\A\{7acfcc82-578e-b376-c3e8-56b09bb30581}\LocalState |
| Operation: | write | Name: | InstalledVersionMajor |
Value: 020098DC31363DCEDB01 | |||
| (PID) Process: | (732) GameBar.exe | Key: | \REGISTRY\A\{7acfcc82-578e-b376-c3e8-56b09bb30581}\LocalState |
| Operation: | write | Name: | InstalledVersionMinor |
Value: 220098DC31363DCEDB01 | |||
| (PID) Process: | (732) GameBar.exe | Key: | \REGISTRY\A\{7acfcc82-578e-b376-c3e8-56b09bb30581}\LocalState |
| Operation: | write | Name: | InstalledVersionBuild |
Value: 616D98DC31363DCEDB01 | |||
| (PID) Process: | (732) GameBar.exe | Key: | \REGISTRY\A\{7acfcc82-578e-b376-c3e8-56b09bb30581}\LocalState |
| Operation: | write | Name: | InstalledVersionRevision |
Value: 000098DC31363DCEDB01 | |||
Executable files
2
Suspicious files
67
Text files
92
Unknown types
0
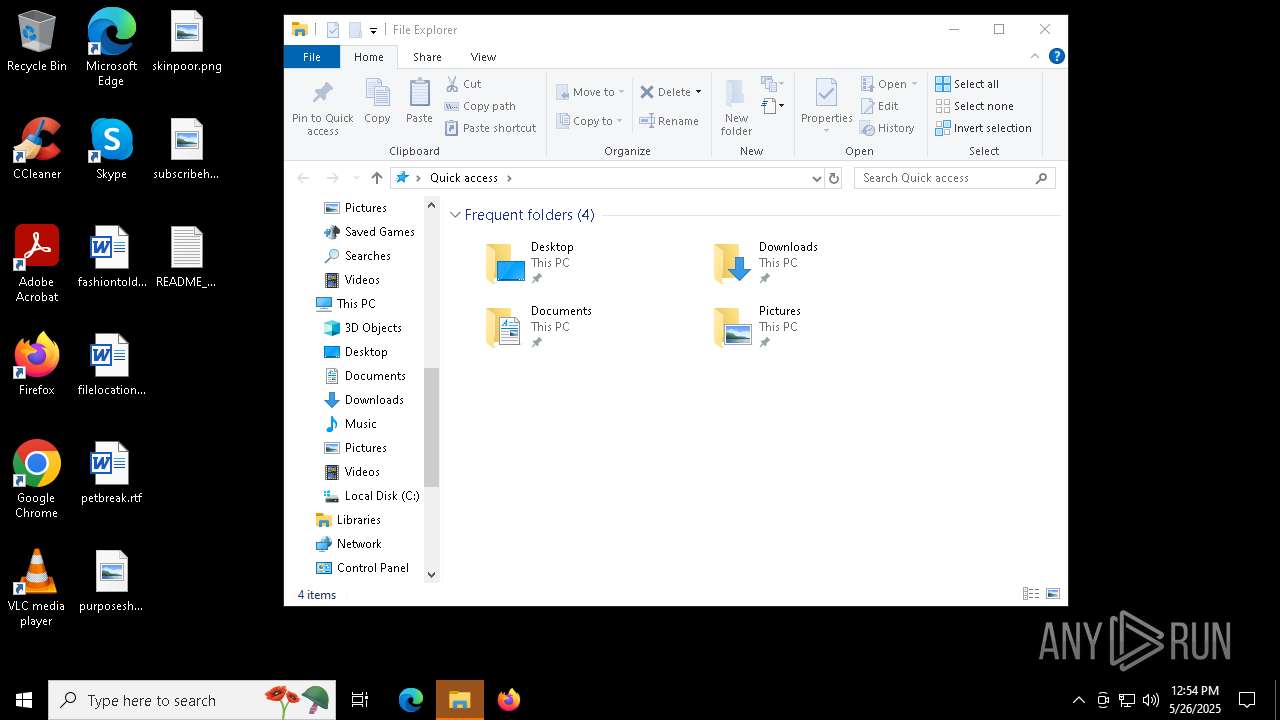
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7860 | pwsh.exe | C:\Users\admin\AppData\Local\Temp\wallpaper.bmp | — | |
MD5:— | SHA256:— | |||
| 7440 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF10a77d.TMP | binary | |
MD5:D040F64E9E7A2BB91ABCA5613424598E | SHA256:D04E0A6940609BD6F3B561B0F6027F5CA4E8C5CF0FB0D0874B380A0374A8D670 | |||
| 7860 | pwsh.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\6AX9T0JLKXRGH8BNCVO2.temp | binary | |
MD5:2B6D1E03A085C9163665A7A9F07F8720 | SHA256:4905CADCDE10898FCF0CE0181CBCD20428151C1D467D6A9FA81C50F1257D629D | |||
| 7440 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:9D64DEA9FD6E81AF5CE78D4E52DB0496 | SHA256:60D624B518B753924040B772C7A2F131BD5E9A80C03A62B055AC2F6CD94305B1 | |||
| 7440 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_drd5sblq.v0v.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7440 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\YFR9XK8TESZV2MJ9TYCR.temp | binary | |
MD5:BFCA1AC987DE11DC44640A127C22ED4A | SHA256:9283A110E05CB192EC393044643A62942A521346744423DEDB16822A91360C04 | |||
| 7860 | pwsh.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\3c3871276e149215.customDestinations-ms~RF10b5a6.TMP | binary | |
MD5:46E1C931FBFF22C77310388EB2BC9B98 | SHA256:704B8AE61BD9951DEA597ED475FD91BAD6ECDEC71726941BDAC64686A59263DB | |||
| 7860 | pwsh.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_kudpj44z.b20.psm1 | text | |
MD5:CFB16D03B223E74B7BA15D909B673B7F | SHA256:4558E0A3C70E0C765E2CD74C9822CC247FAD242CA7423F3C571283EAB03AA071 | |||
| 7440 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | binary | |
MD5:BFCA1AC987DE11DC44640A127C22ED4A | SHA256:9283A110E05CB192EC393044643A62942A521346744423DEDB16822A91360C04 | |||
| 7860 | pwsh.exe | C:\Users\admin\Desktop\fashiontold.rtf | binary | |
MD5:A2F9956B84C229314056B26E4470D3A9 | SHA256:AD2DC93C3E01769E57D48CB8BB18862973E76B2720335FFFC318063D1B8357FB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
61
DNS requests
49
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.168.114:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4660 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/MicCodSigPCA2011_2011-07-08.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
7632 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 2.16.168.114:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
— | — | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
2416 | RUXIMICS.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5796 | svchost.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 40.126.31.73:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.bing.com |
| whitelisted |
th.bing.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |