| File name: | JKL-764-JPL-93873637BNSS.SCR |
| Full analysis: | https://app.any.run/tasks/577eec22-40f2-42ec-9850-47eb757cb28e |
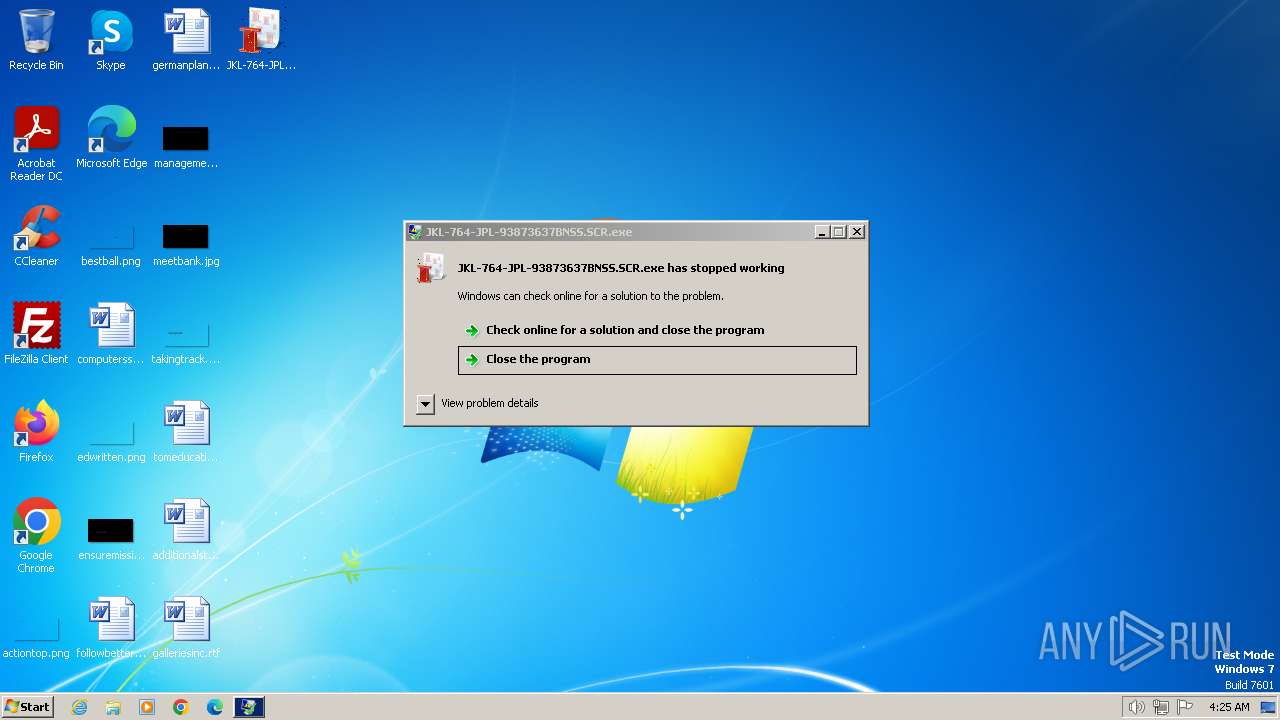
| Verdict: | Malicious activity |
| Analysis date: | January 29, 2024, 04:24:19 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 136665CCDC5A00AC893337CA535A9B00 |
| SHA1: | B711F4996E91585FB28EA367613AE8994BB9DD84 |
| SHA256: | B47914D632508339A012E07CC4030B35B25A78665513276C26496AFFEFD01B90 |
| SSDEEP: | 24576:ECtj+tea9DhNoCgZ32gDkJOyFjZ8ud83Z:ECUtea9DhNoLZ32gDkJOyFjZ8ud83Z |
MALICIOUS
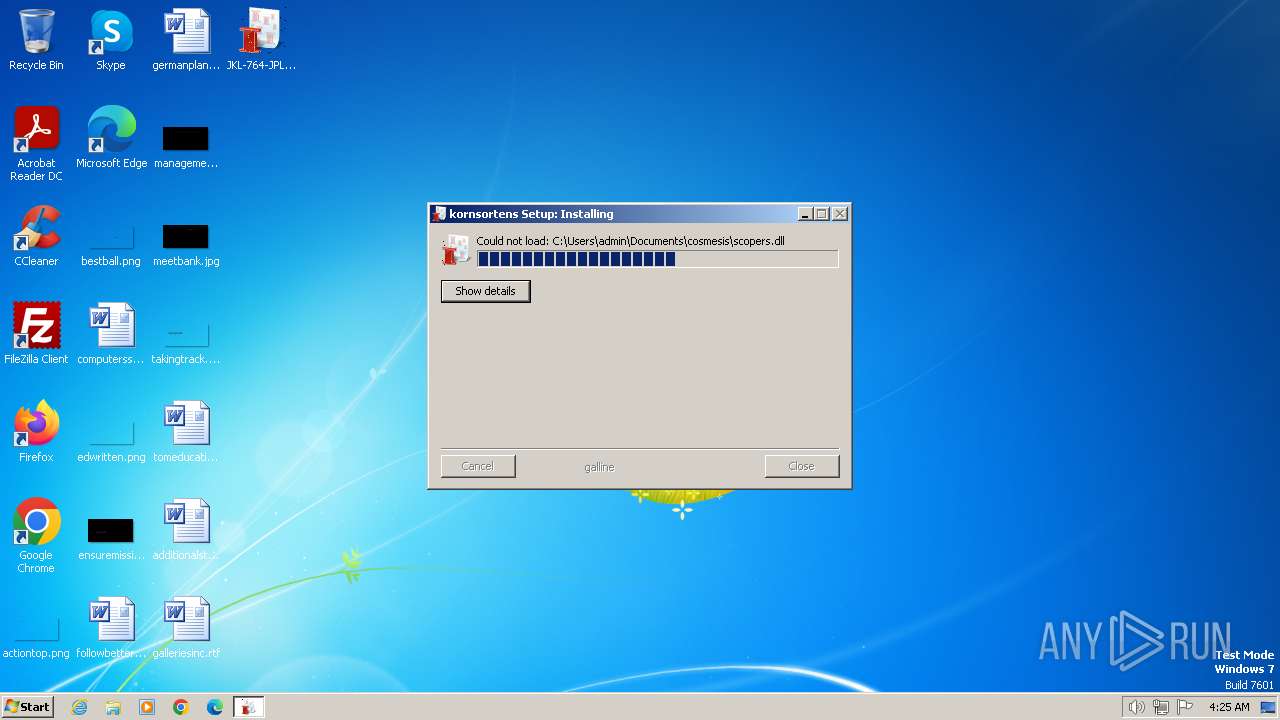
Drops the executable file immediately after the start
- JKL-764-JPL-93873637BNSS.SCR.exe (PID: 1936)
- JKL-764-JPL-93873637BNSS.SCR.exe (PID: 2724)
SUSPICIOUS
Malware-specific behavior (creating "System.dll" in Temp)
- JKL-764-JPL-93873637BNSS.SCR.exe (PID: 1936)
- JKL-764-JPL-93873637BNSS.SCR.exe (PID: 2724)
The process creates files with name similar to system file names
- JKL-764-JPL-93873637BNSS.SCR.exe (PID: 1936)
- JKL-764-JPL-93873637BNSS.SCR.exe (PID: 2724)
Executable content was dropped or overwritten
- JKL-764-JPL-93873637BNSS.SCR.exe (PID: 1936)
- JKL-764-JPL-93873637BNSS.SCR.exe (PID: 2724)
INFO
Checks supported languages
- JKL-764-JPL-93873637BNSS.SCR.exe (PID: 1936)
- JKL-764-JPL-93873637BNSS.SCR.exe (PID: 2724)
Reads the computer name
- JKL-764-JPL-93873637BNSS.SCR.exe (PID: 1936)
- JKL-764-JPL-93873637BNSS.SCR.exe (PID: 2724)
Create files in a temporary directory
- JKL-764-JPL-93873637BNSS.SCR.exe (PID: 1936)
- JKL-764-JPL-93873637BNSS.SCR.exe (PID: 2724)
Creates files or folders in the user directory
- JKL-764-JPL-93873637BNSS.SCR.exe (PID: 1936)
Manual execution by a user
- JKL-764-JPL-93873637BNSS.SCR.exe (PID: 2724)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:12:15 23:24:36+01:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 26112 |
| InitializedDataSize: | 141824 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x34a5 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.2.0.0 |
| ProductVersionNumber: | 2.2.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| Comments: | tyggefladers trash |
| ProductVersion: | 2.2.0.0 |
Total processes
42
Monitored processes
2
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1936 | "C:\Users\admin\Desktop\JKL-764-JPL-93873637BNSS.SCR.exe" | C:\Users\admin\Desktop\JKL-764-JPL-93873637BNSS.SCR.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2724 | "C:\Users\admin\Desktop\JKL-764-JPL-93873637BNSS.SCR.exe" | C:\Users\admin\Desktop\JKL-764-JPL-93873637BNSS.SCR.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225477 Modules
| |||||||||||||||
Total events
321
Read events
316
Write events
5
Delete events
0
Modification events
| (PID) Process: | (1936) JKL-764-JPL-93873637BNSS.SCR.exe | Key: | HKEY_CURRENT_USER\Software\Intercepter |
| Operation: | write | Name: | Unzip |
Value: %pyurias%\medvirken.Kli225 | |||
| (PID) Process: | (2724) JKL-764-JPL-93873637BNSS.SCR.exe | Key: | HKEY_CURRENT_USER\Software\Intercepter |
| Operation: | write | Name: | Unzip |
Value: %pyurias%\medvirken.Kli225 | |||
| (PID) Process: | (2724) JKL-764-JPL-93873637BNSS.SCR.exe | Key: | HKEY_CURRENT_USER\Software\transmaking |
| Operation: | write | Name: | Sithen |
Value: %superpious%\cermet\dibrach.cua | |||
| (PID) Process: | (2724) JKL-764-JPL-93873637BNSS.SCR.exe | Key: | HKEY_CURRENT_USER\Software\Avlsgaards\recharges |
| Operation: | write | Name: | primfaktoroplsningers |
Value: FFFFFF85 | |||
Executable files
3
Suspicious files
3
Text files
5
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1936 | JKL-764-JPL-93873637BNSS.SCR.exe | C:\Users\admin\AppData\Local\Temp\Carmind.ini | text | |
MD5:49434B1537E73A3AED797EE18137F672 | SHA256:7ECC988E91194E2D004BDF6E6E88ADFB1548114ED481A0B4C08AD392722A73E7 | |||
| 1936 | JKL-764-JPL-93873637BNSS.SCR.exe | C:\Users\admin\hjlpers\mutationernes\user-status-pending-symbolic.symbolic.png | image | |
MD5:510BF68FAB8C89BB84C83F5DB1FEB62A | SHA256:4C5FAD50942204C11E84F6C3AC1EEAF3480A51F4EFF6F2AFEEA190D567B0DBCF | |||
| 1936 | JKL-764-JPL-93873637BNSS.SCR.exe | C:\Users\admin\AppData\Roaming\stilene.ini | text | |
MD5:F91E7282F527F51D6A7760D6F23E1873 | SHA256:FA527707880590055CE6FB59C07242F7142C656736B4790EC3FB337EFE9C8EF0 | |||
| 2724 | JKL-764-JPL-93873637BNSS.SCR.exe | C:\Users\admin\AppData\Local\Temp\nsjCED5.tmp\System.dll | executable | |
MD5:0D7AD4F45DC6F5AA87F606D0331C6901 | SHA256:3EB38AE99653A7DBC724132EE240F6E5C4AF4BFE7C01D31D23FAF373F9F2EACA | |||
| 1936 | JKL-764-JPL-93873637BNSS.SCR.exe | C:\Users\admin\hjlpers\mutationernes\Grundslgerne.Dun | binary | |
MD5:33D1B82E120EF9E254A0FFAF3E27E98C | SHA256:F9212A269A1C42094FE1AC998FF61F4DE24665ECC2ACAAE1D109941E31B76DE6 | |||
| 1936 | JKL-764-JPL-93873637BNSS.SCR.exe | C:\Users\admin\hjlpers\mutationernes\Lancetter\Milieubeskyttelsesreglementer\wcapi.dll | executable | |
MD5:062434166C64D50B84518692BE7E78DC | SHA256:5AF5384CB1F83BAB386DDF98E6B57639E896265008438A2730E17B93E65577E5 | |||
| 1936 | JKL-764-JPL-93873637BNSS.SCR.exe | C:\Users\admin\hjlpers\mutationernes\Barbecuer.Ret | binary | |
MD5:D0899A0B8F6067ACBC8B5E678090ABE6 | SHA256:DC97DBC064133C5D0F0787DF1A646501230668C959C33123745B74C587C34DC3 | |||
| 1936 | JKL-764-JPL-93873637BNSS.SCR.exe | C:\Users\admin\AppData\Local\Temp\nscA624.tmp\System.dll | executable | |
MD5:0D7AD4F45DC6F5AA87F606D0331C6901 | SHA256:3EB38AE99653A7DBC724132EE240F6E5C4AF4BFE7C01D31D23FAF373F9F2EACA | |||
| 1936 | JKL-764-JPL-93873637BNSS.SCR.exe | C:\Users\admin\hjlpers\mutationernes\dialog-error-symbolic.symbolic.png | image | |
MD5:690A9407D0D54F8FC840626F55C2A9EC | SHA256:4A3C7B75E01AB44F69DD012D92A82970504BCE96DF6E7E4CD6430EABE6AA5DF4 | |||
| 2724 | JKL-764-JPL-93873637BNSS.SCR.exe | C:\Users\admin\AppData\Local\Temp\nsyCE95.tmp | binary | |
MD5:EDFFCA0E010E9E0BDBE839DEC9A6E4AE | SHA256:0217DE93A03A0DF255D06B3699A9A6DB39B701D2E1213201C71B3AD00B77BB36 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
3
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |