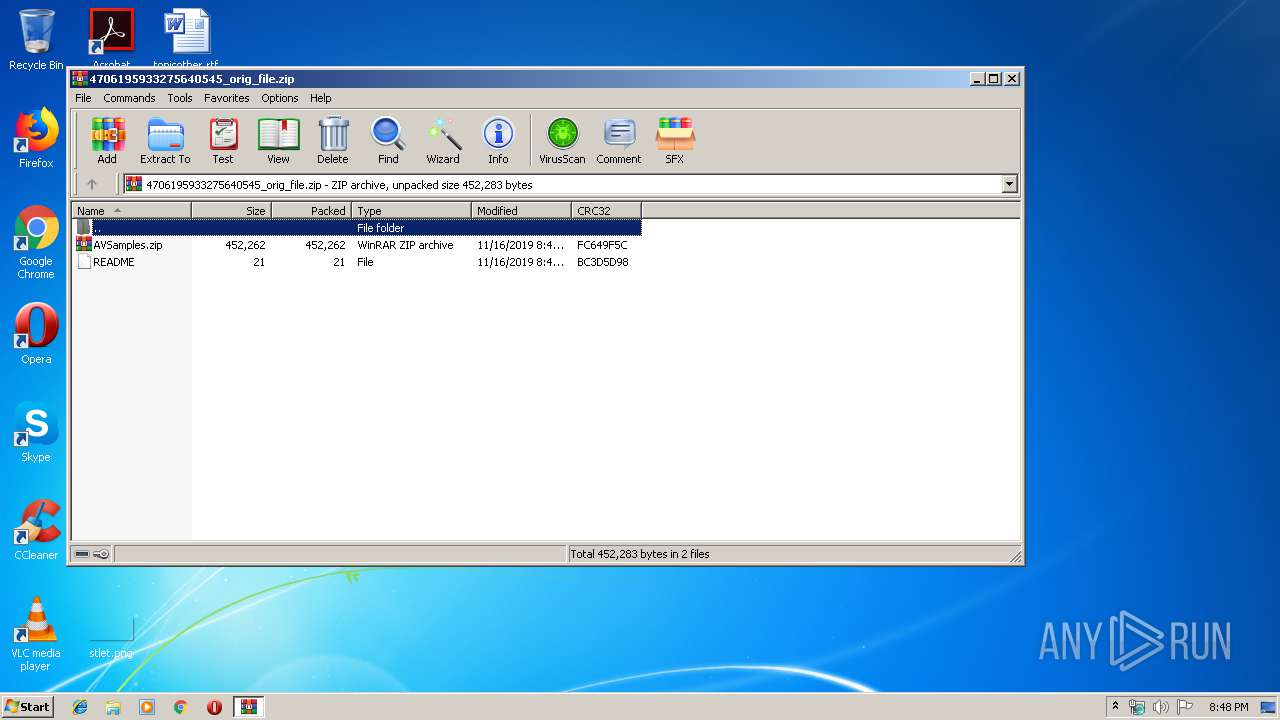
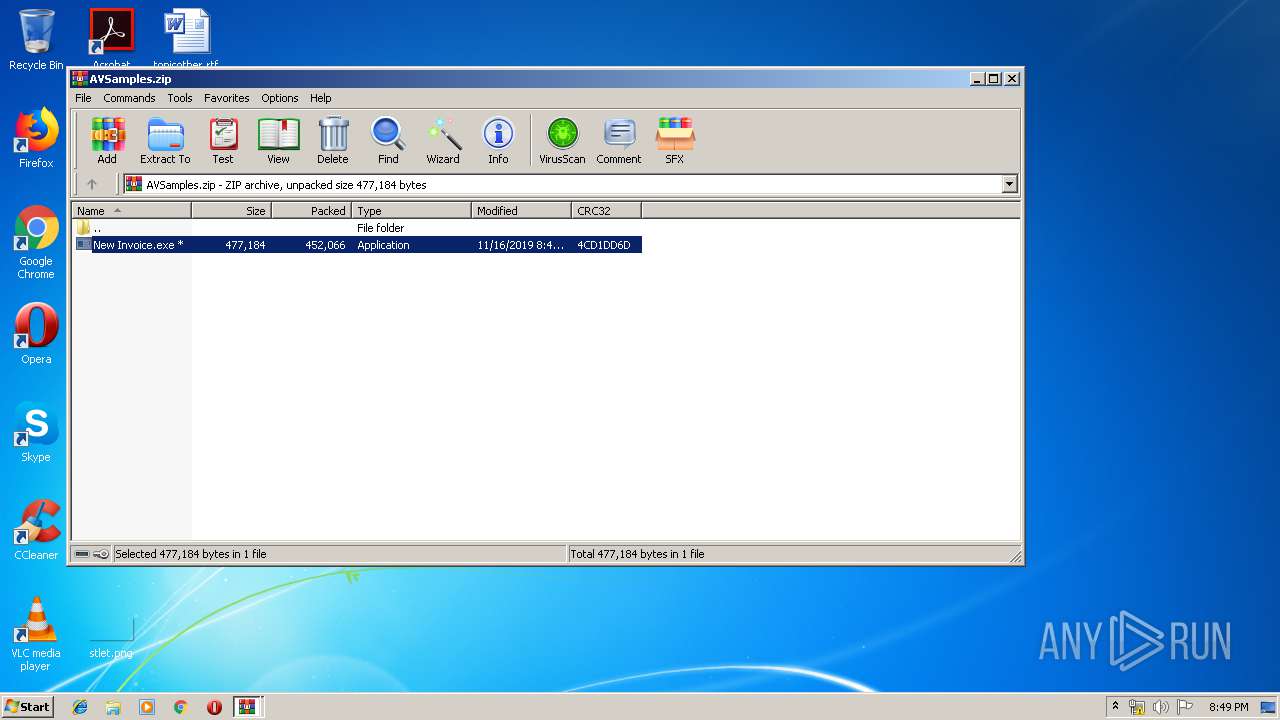
| File name: | 4706195933275640545_orig_file.zip |
| Full analysis: | https://app.any.run/tasks/c4f47e24-81c7-413e-84b9-0ef293888cc7 |
| Verdict: | Malicious activity |
| Analysis date: | November 16, 2019, 20:48:26 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract |
| MD5: | E10E2CD384F223ED561AF13ED4D8CDA2 |
| SHA1: | FE02500D87BB63AF7B96BE10FD296B85042B6884 |
| SHA256: | B4539BECB83EF0E1FF3E39428E747E9D52945E8E14EDE50A4A52294728FF491C |
| SSDEEP: | 6144:Sa2nx/PyoY+q/45wST+6SwPvXwTKavyeoN0Uu+vzhmtBC0PjQL9k4CuKPx47gmhF:StxyoYf6SIyo+UX1mtBCuQLto451uw |
MALICIOUS
Application was dropped or rewritten from another process
- New Invoice.exe (PID: 1600)
- New Invoice.exe (PID: 2644)
- New Invoice.exe (PID: 2040)
Changes the autorun value in the registry
- New Invoice.exe (PID: 2040)
Actions looks like stealing of personal data
- New Invoice.exe (PID: 2040)
SUSPICIOUS
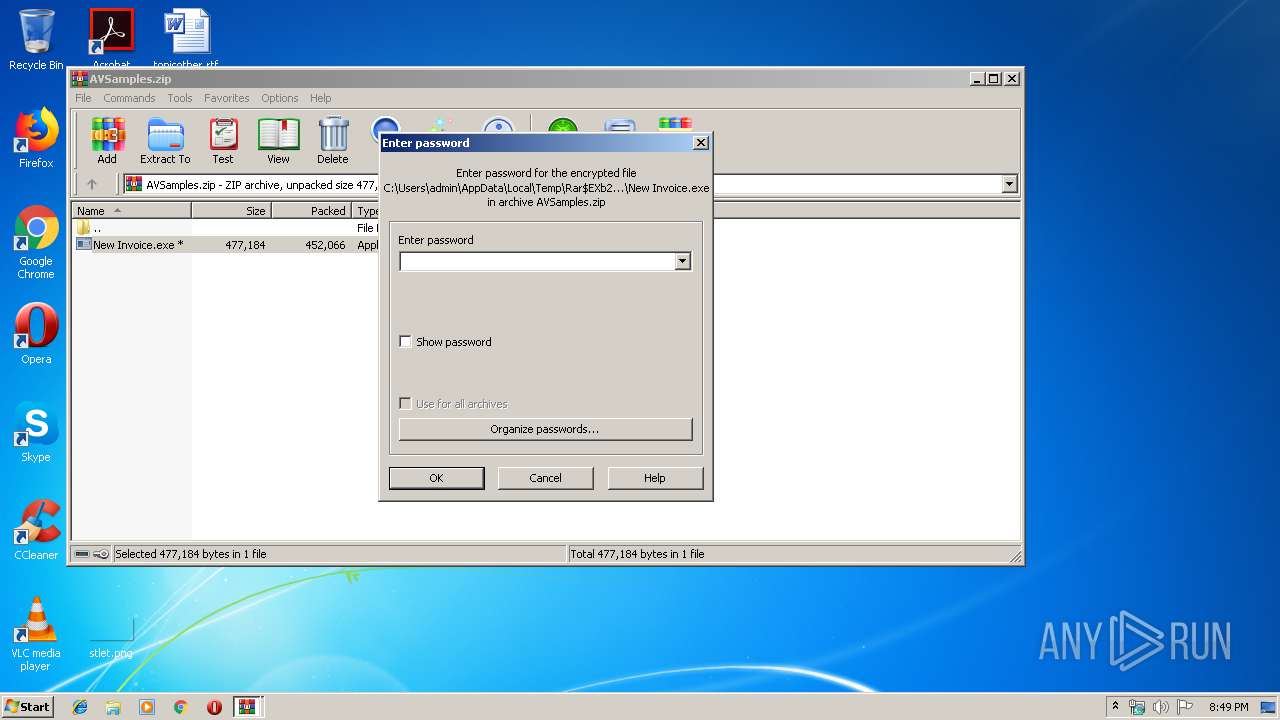
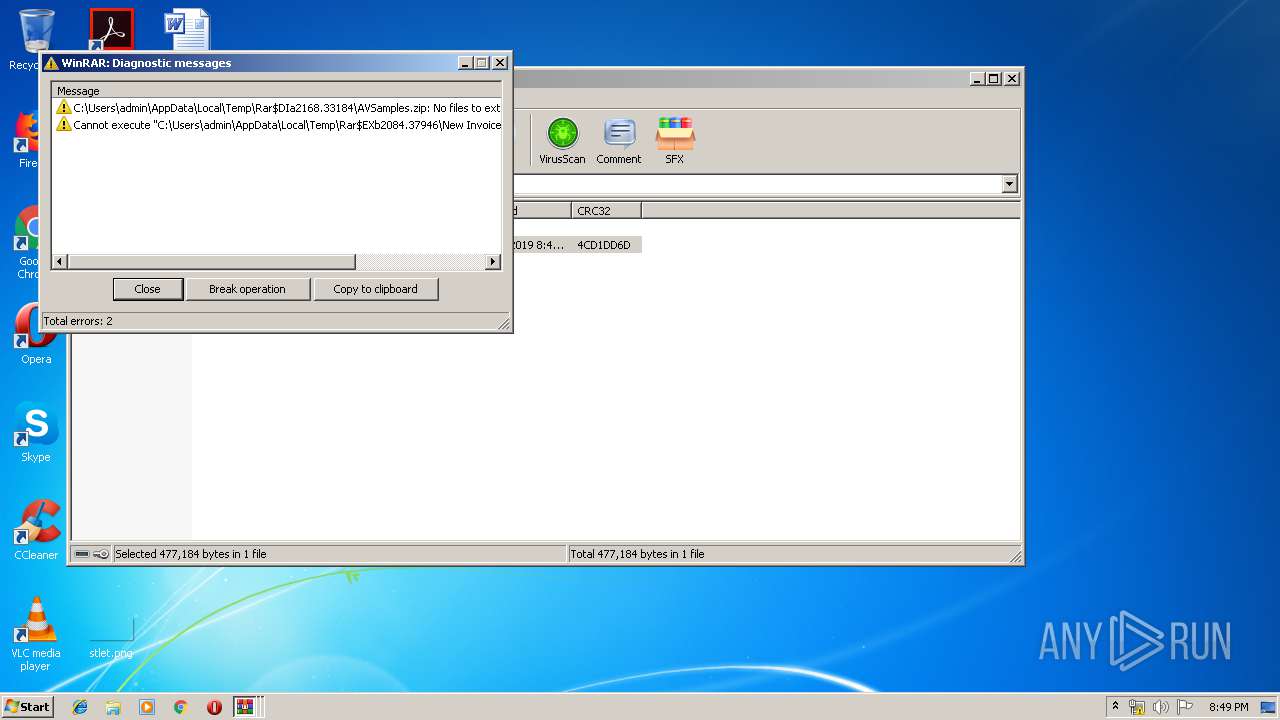
Application launched itself
- WinRAR.exe (PID: 2168)
- New Invoice.exe (PID: 1600)
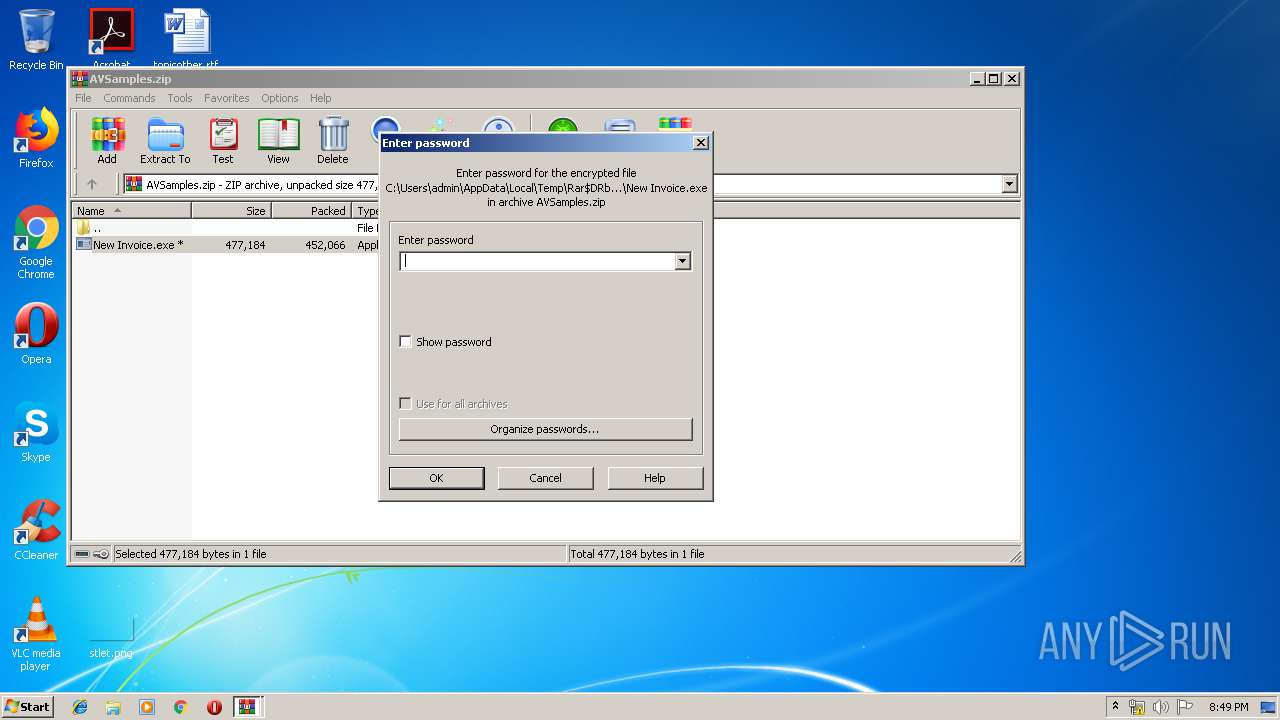
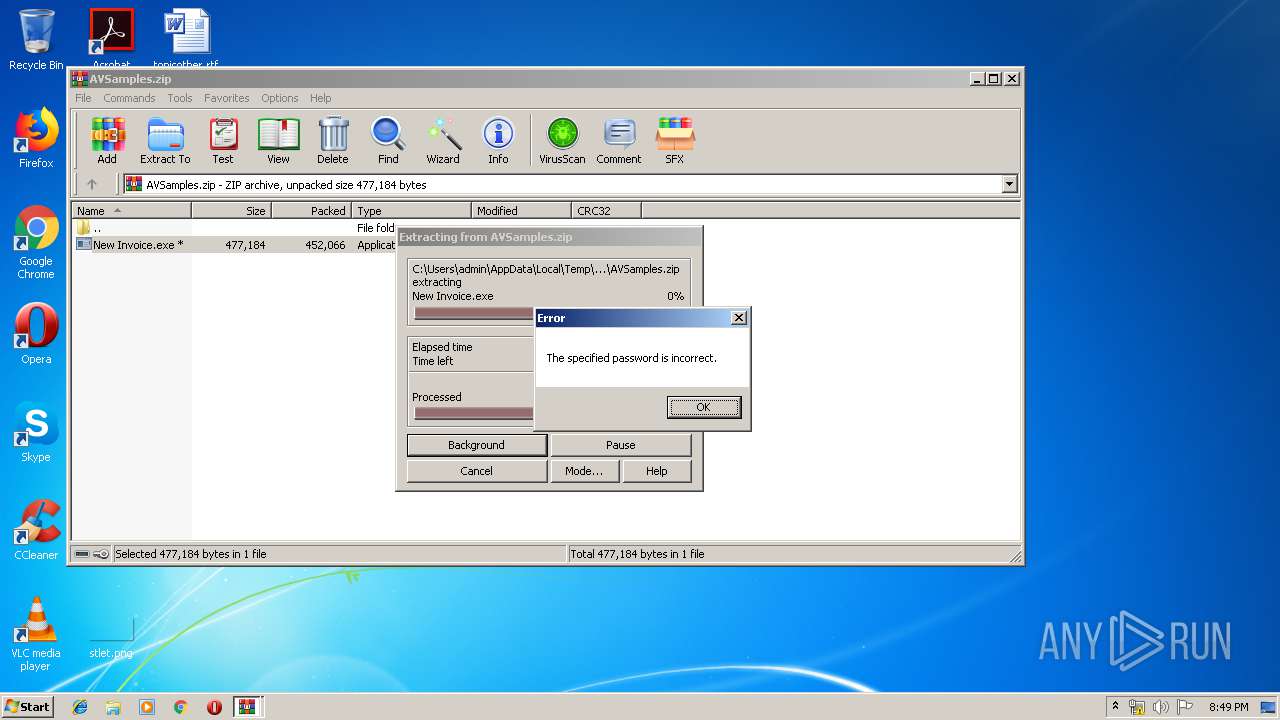
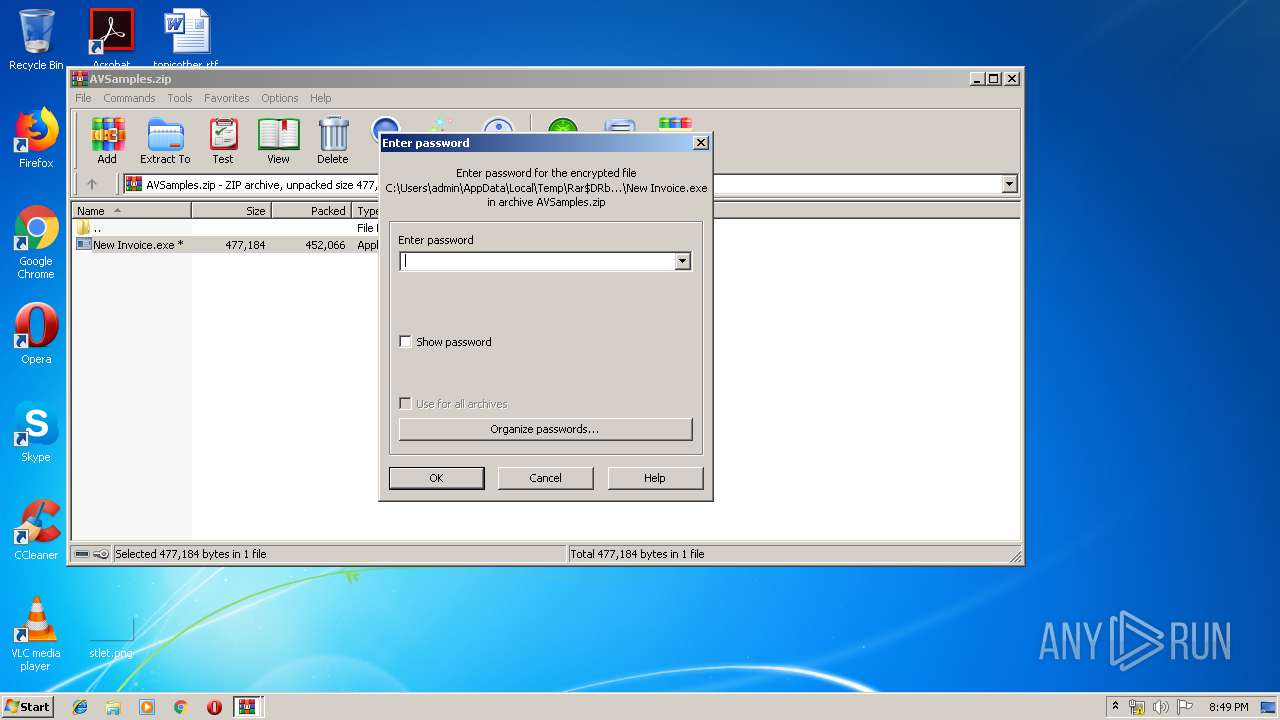
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2084)
- New Invoice.exe (PID: 2040)
Creates files in the user directory
- New Invoice.exe (PID: 2040)
Reads the BIOS version
- New Invoice.exe (PID: 1600)
INFO
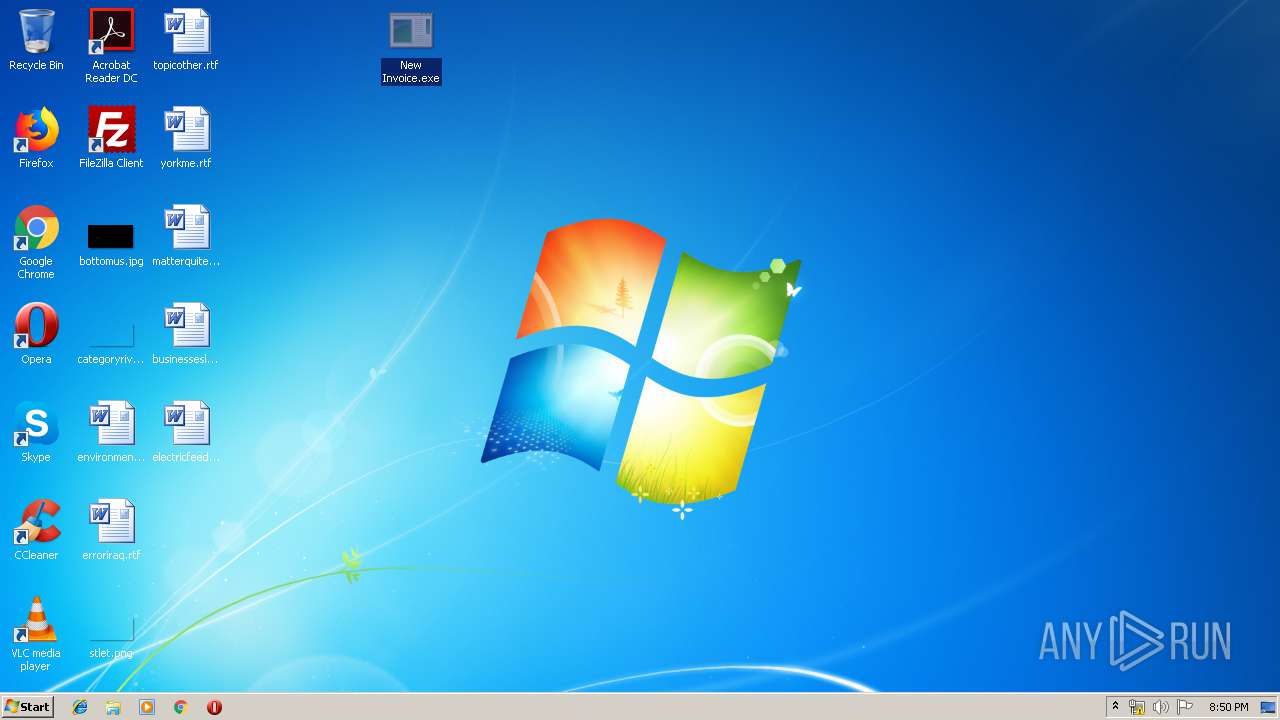
Manual execution by user
- New Invoice.exe (PID: 2644)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
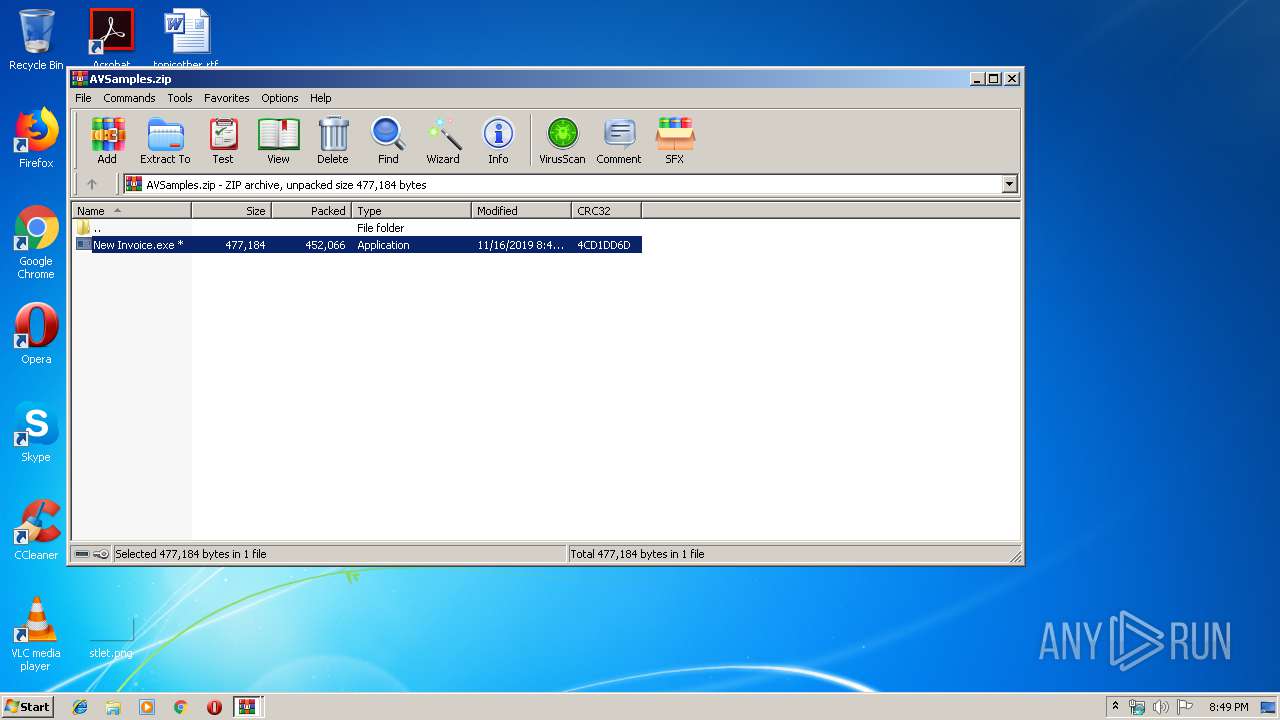
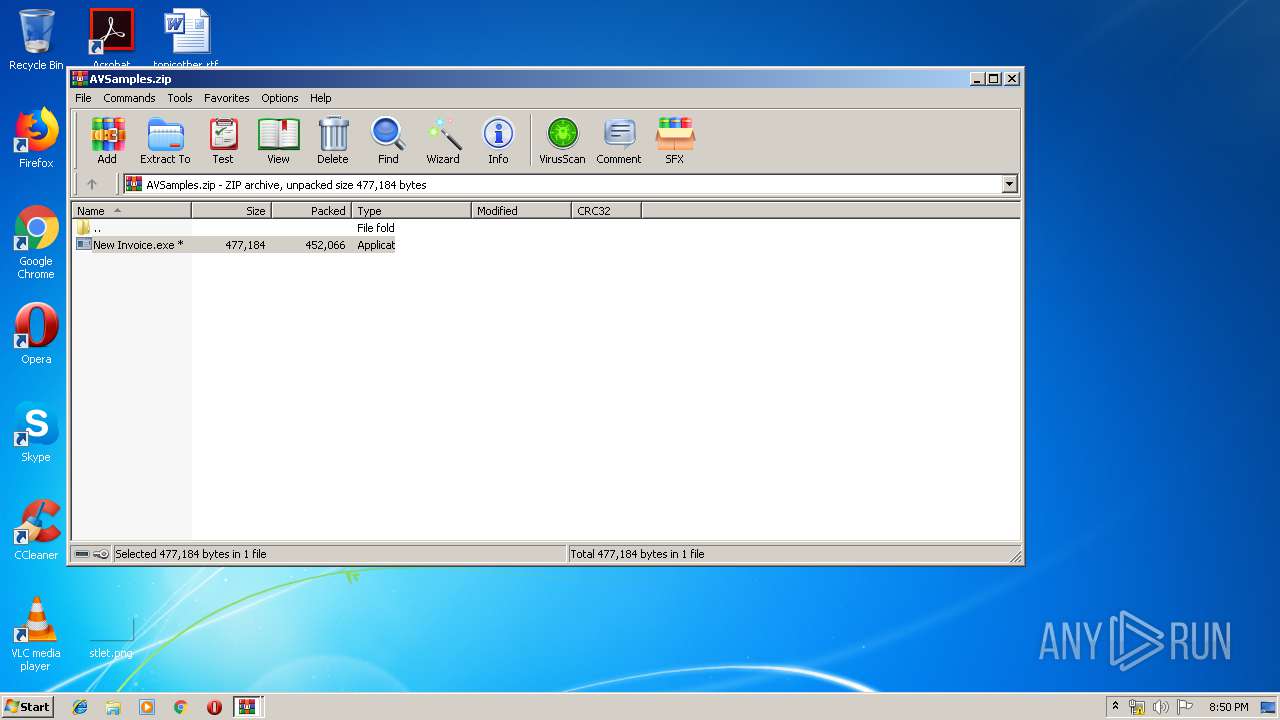
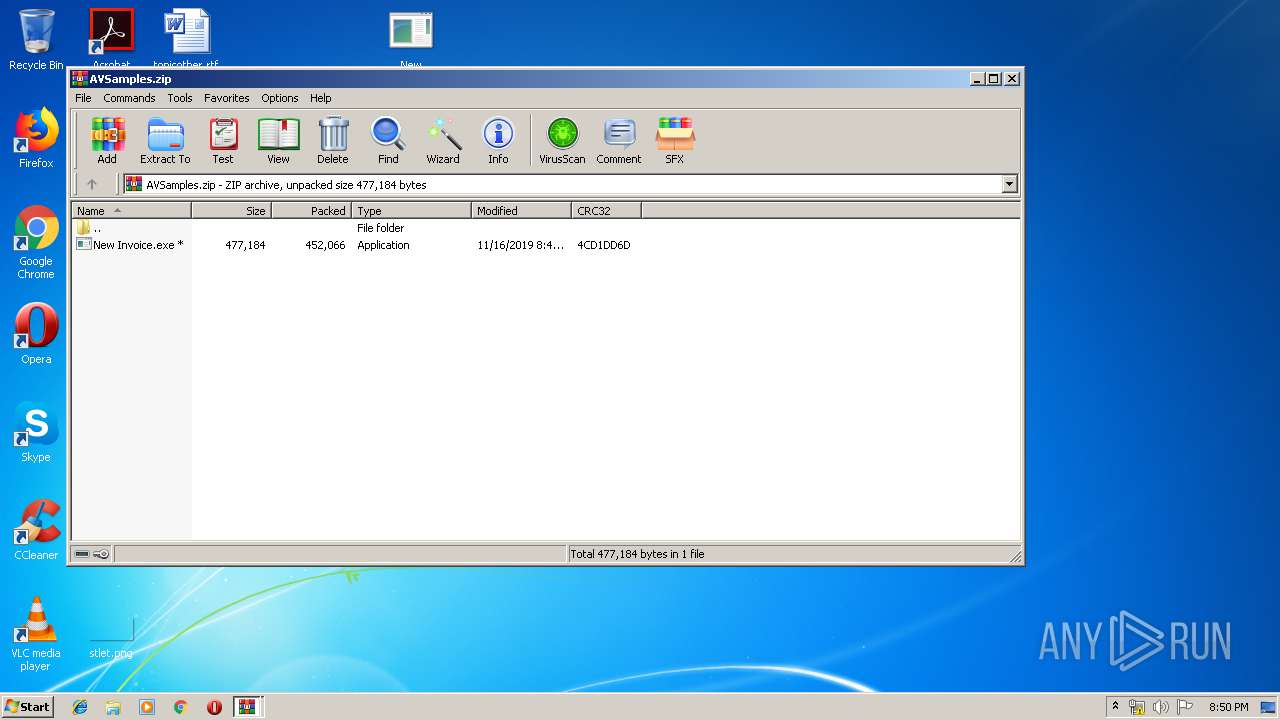
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2019:11:16 23:47:13 |
| ZipCRC: | 0xfc649f5c |
| ZipCompressedSize: | 452262 |
| ZipUncompressedSize: | 452262 |
| ZipFileName: | AVSamples.zip |
Total processes
42
Monitored processes
5
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
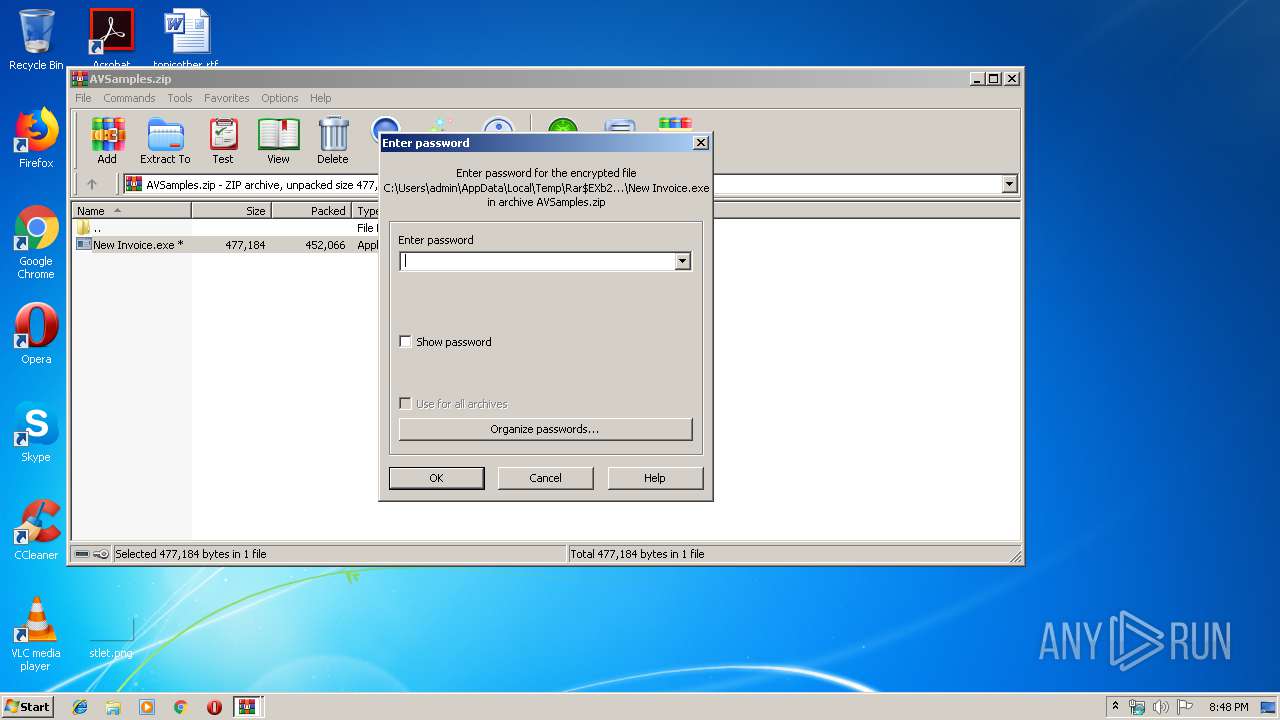
| 1600 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb2084.33743\New Invoice.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb2084.33743\New Invoice.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Markus Benovsky Integrity Level: MEDIUM Description: ObcidiaNetwork Exit code: 0 Version: 1.5.0.0 Modules
| |||||||||||||||
| 2040 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb2084.33743\New Invoice.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb2084.33743\New Invoice.exe | New Invoice.exe | ||||||||||||
User: admin Company: Markus Benovsky Integrity Level: MEDIUM Description: ObcidiaNetwork Exit code: 0 Version: 1.5.0.0 Modules
| |||||||||||||||
| 2084 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\Rar$DIa2168.33184\AVSamples.zip | C:\Program Files\WinRAR\WinRAR.exe | WinRAR.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2168 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\4706195933275640545_orig_file.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2644 | "C:\Users\admin\Desktop\New Invoice.exe" | C:\Users\admin\Desktop\New Invoice.exe | — | explorer.exe | |||||||||||
User: admin Company: Markus Benovsky Integrity Level: MEDIUM Description: ObcidiaNetwork Exit code: 4294967295 Version: 1.5.0.0 Modules
| |||||||||||||||
Total events
1 002
Read events
936
Write events
66
Delete events
0
Modification events
| (PID) Process: | (2168) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2168) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2168) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2168) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\4706195933275640545_orig_file.zip | |||
| (PID) Process: | (2168) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2168) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2168) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2168) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2084) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2084) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
Executable files
3
Suspicious files
1
Text files
0
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
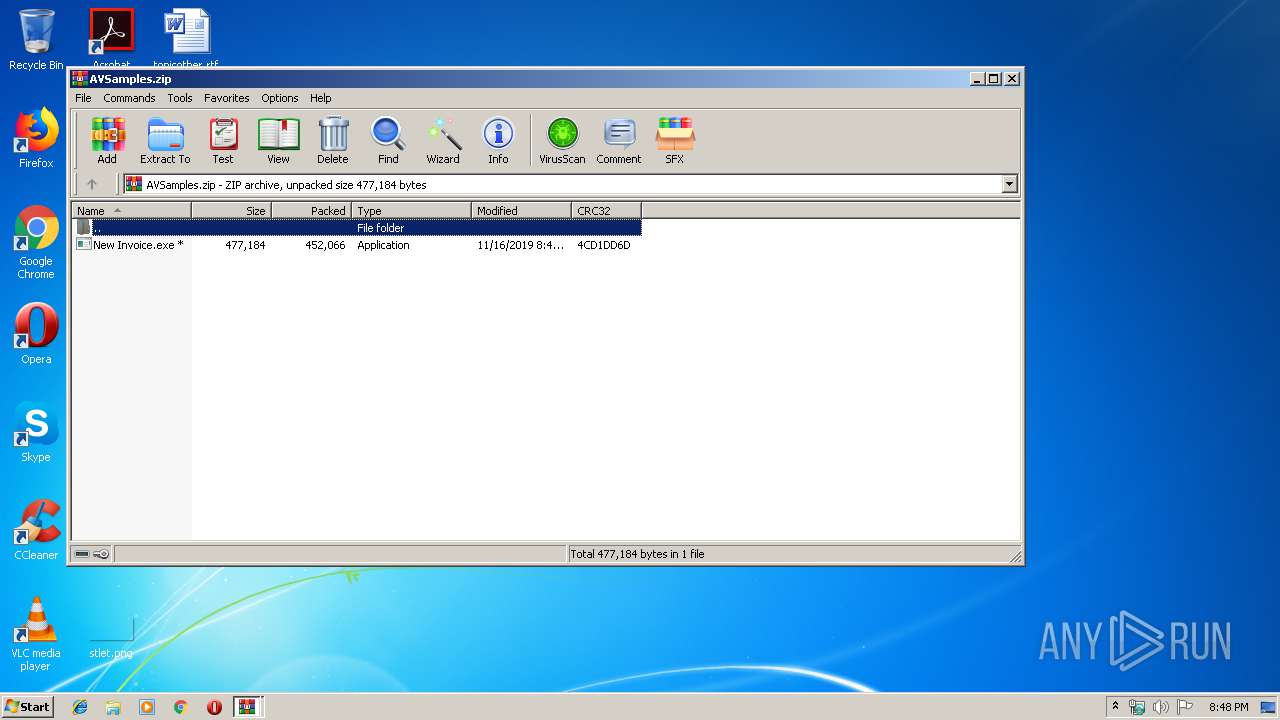
| 2168 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa2168.33184\AVSamples.zip | compressed | |
MD5:— | SHA256:— | |||
| 2040 | New Invoice.exe | C:\Users\admin\AppData\Roaming\GvwZwPp\cEAzX.exe | executable | |
MD5:— | SHA256:— | |||
| 2040 | New Invoice.exe | C:\Users\admin\AppData\Local\Temp\51faa74e-5f7a-4cb6-9189-a8413b2b28a7 | sqlite | |
MD5:— | SHA256:— | |||
| 2084 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb2084.33743\New Invoice.exe | executable | |
MD5:— | SHA256:— | |||
| 2084 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2084.38990\New Invoice.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
1
Threats
1
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2040 | New Invoice.exe | 192.185.28.88:587 | mail.octindia.com | CyrusOne LLC | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
mail.octindia.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2040 | New Invoice.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |