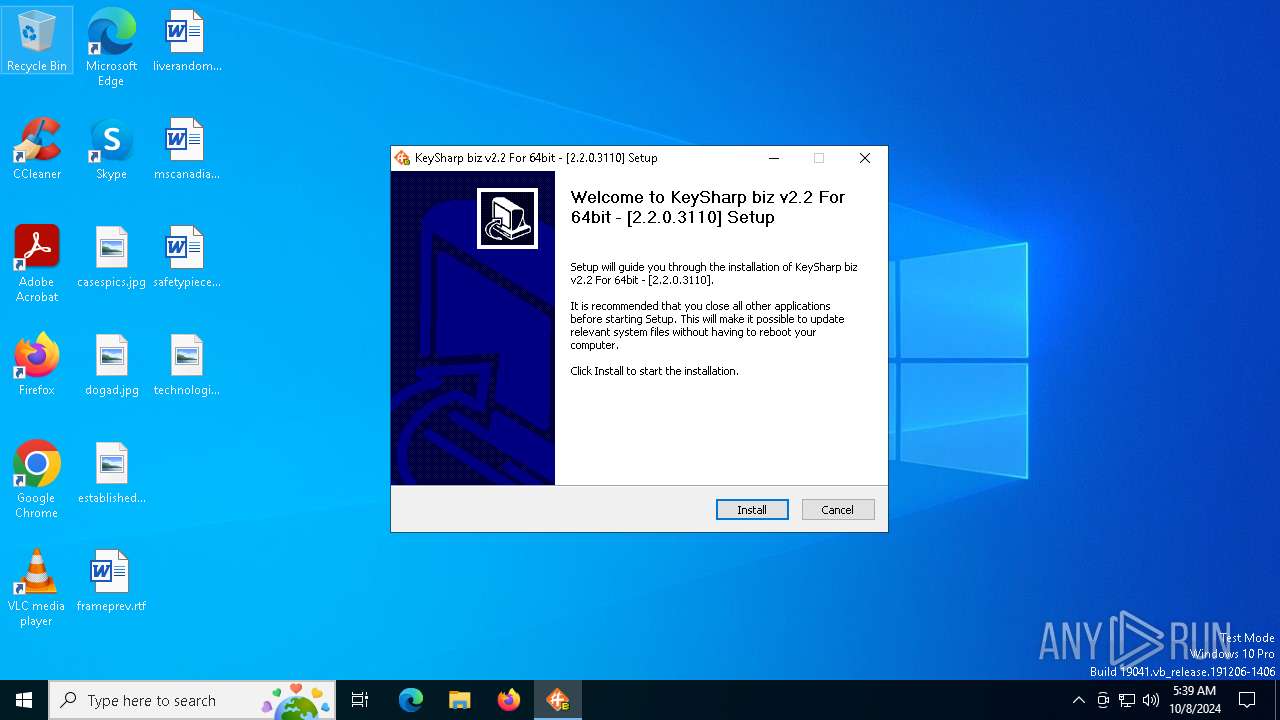
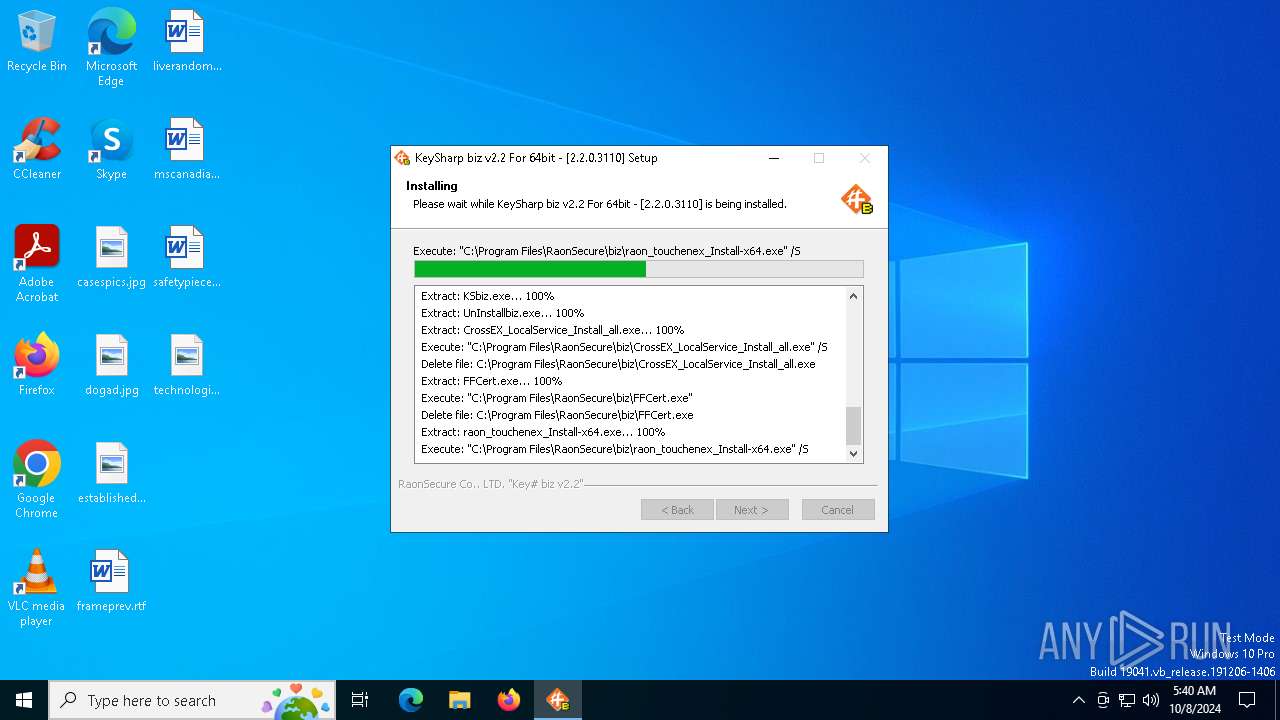
| File name: | KSbiz_Installer_64bit_v2_2_0_3110.exe |
| Full analysis: | https://app.any.run/tasks/75172018-29fb-45f7-a57d-22b5d124881b |
| Verdict: | Malicious activity |
| Analysis date: | October 08, 2024, 05:39:47 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | C9752959CBB2E1028C4C2746EB530D6C |
| SHA1: | AB12BB63AA891CB4A6EAD150207D34AB8D469977 |
| SHA256: | B45202D099C8219F9D7781425A2ECFDE973D8C38A7D181B92445640EA193CC5F |
| SSDEEP: | 98304:y/UHna+0hYiz7L6qPN6PDpaQ8BWE+zYyip02xn6KwYc7JmGF7RdwRoHVU8uNKjfr:uWJg8DuWDTVW0utxaCy |
MALICIOUS
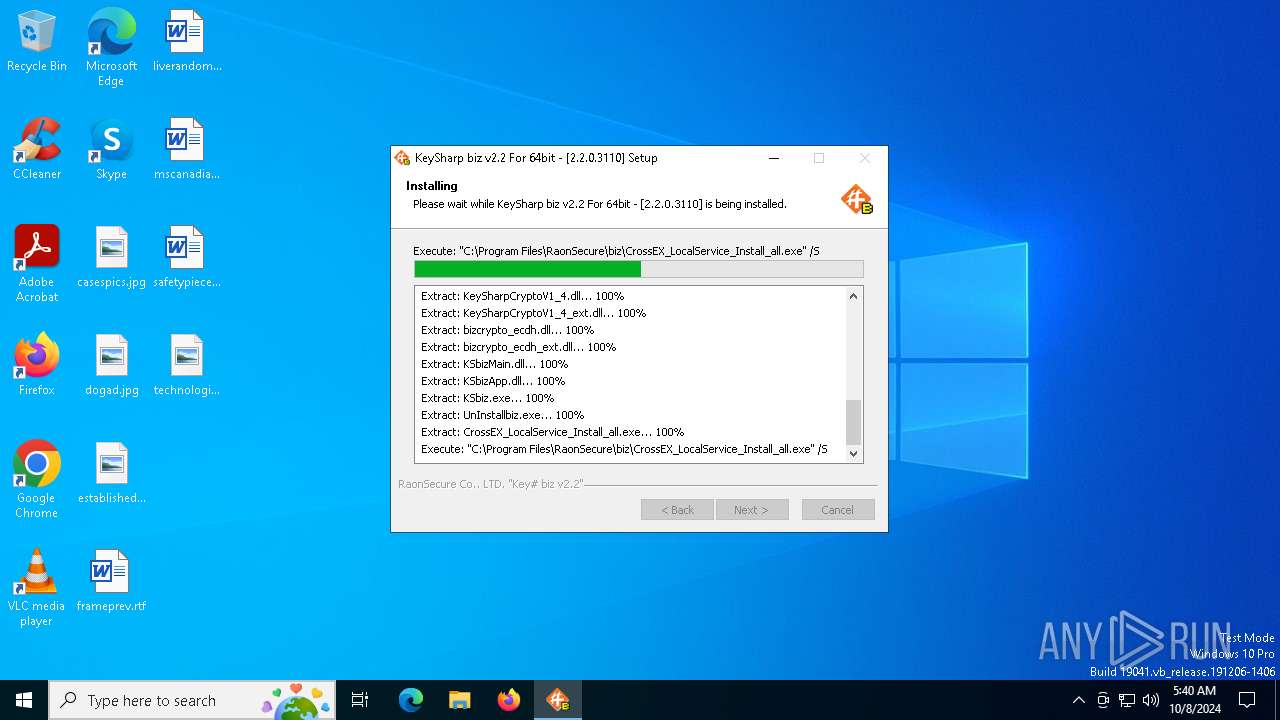
Changes the autorun value in the registry
- CrossEX_LocalService_Install_all.exe (PID: 6388)
Registers / Runs the DLL via REGSVR32.EXE
- raon_touchenex_Install-x64.exe (PID: 1492)
SUSPICIOUS
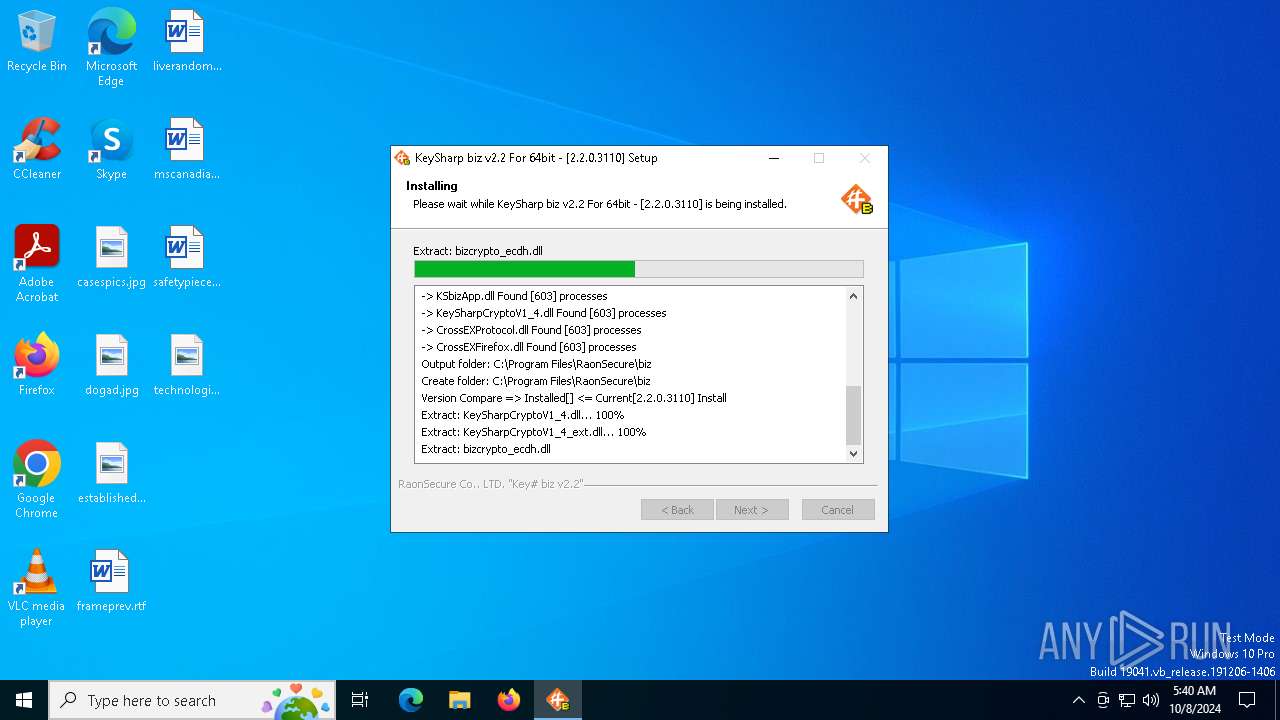
Malware-specific behavior (creating "System.dll" in Temp)
- KSbiz_Installer_64bit_v2_2_0_3110.exe (PID: 5960)
- CrossEX_LocalService_Install_all.exe (PID: 6388)
- raon_touchenex_Install-x64.exe (PID: 1492)
The process creates files with name similar to system file names
- KSbiz_Installer_64bit_v2_2_0_3110.exe (PID: 5960)
- CrossEX_LocalService_Install_all.exe (PID: 6388)
Executable content was dropped or overwritten
- KSbiz_Installer_64bit_v2_2_0_3110.exe (PID: 5960)
- CrossEX_LocalService_Install_all.exe (PID: 6388)
- raon_touchenex_Install-x64.exe (PID: 1492)
- FFCert.exe (PID: 2128)
Creates a software uninstall entry
- CrossEX_LocalService_Install_all.exe (PID: 6388)
Adds/modifies Windows certificates
- CrossEX_LocalService_Install_all.exe (PID: 6388)
- KSbiz_Installer_64bit_v2_2_0_3110.exe (PID: 5960)
Executes as Windows Service
- ObCrossEXService.exe (PID: 6020)
Process drops legitimate windows executable
- FFCert.exe (PID: 2128)
The process drops C-runtime libraries
- FFCert.exe (PID: 2128)
INFO
Checks supported languages
- KSbiz_Installer_64bit_v2_2_0_3110.exe (PID: 5960)
- CrossEX_LocalService_Install_all.exe (PID: 6388)
- CrossEXService.exe (PID: 6844)
- ObCrossEXService.exe (PID: 6020)
- FFCert.exe (PID: 2128)
Creates files in the program directory
- CrossEX_LocalService_Install_all.exe (PID: 6388)
- KSbiz_Installer_64bit_v2_2_0_3110.exe (PID: 5960)
Reads the computer name
- KSbiz_Installer_64bit_v2_2_0_3110.exe (PID: 5960)
- CrossEXService.exe (PID: 6844)
- ObCrossEXService.exe (PID: 6020)
Reads the machine GUID from the registry
- CrossEX_LocalService_Install_all.exe (PID: 6388)
- CrossEXService.exe (PID: 6844)
Create files in a temporary directory
- KSbiz_Installer_64bit_v2_2_0_3110.exe (PID: 5960)
- CrossEX_LocalService_Install_all.exe (PID: 6388)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:01:30 03:57:19+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 25600 |
| InitializedDataSize: | 3805696 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x336c |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.2.0.3110 |
| ProductVersionNumber: | 2.2.0.3110 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Korean |
| CharacterSet: | Windows, Korea (Shift - KSC 5601) |
| Comments: | - |
| CompanyName: | RaonSecure Co., Ltd. |
| FileDescription: | KeySharp biz v2.2 |
| FileVersion: | 2.2.0.3110 |
| LegalCopyright: | RaonSecure Co., Ltd. |
| LegalTrademarks: | - |
| ProductName: | KeySharp biz v2.2 |
| ProductVersion: | 2.2.0.3110 |
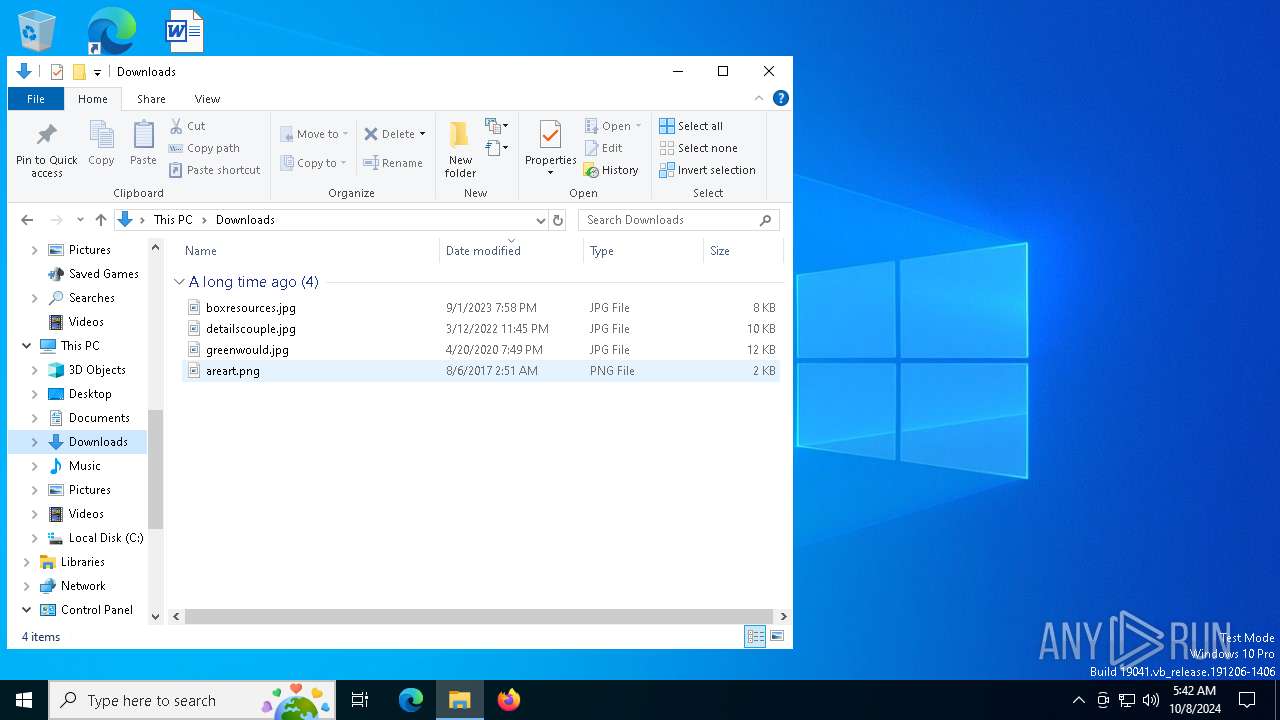
Total processes
152
Monitored processes
20
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 132 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | sc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 532 | sc start "CrossEX Live Checker" | C:\Windows\SysWOW64\sc.exe | — | CrossEX_LocalService_Install_all.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1232 | "C:\WINDOWS\system32\regsvr32.exe" "C:\Program Files\RaonSecure\bridge\CrossEX\touchenex\1.0.1.1550\CrossEXProtocol.dll" /S | C:\Windows\SysWOW64\regsvr32.exe | — | raon_touchenex_Install-x64.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1328 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | sc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1492 | "C:\Program Files\RaonSecure\biz\raon_touchenex_Install-x64.exe" /S | C:\Program Files\RaonSecure\biz\raon_touchenex_Install-x64.exe | KSbiz_Installer_64bit_v2_2_0_3110.exe | ||||||||||||
User: admin Company: iniLINE Co., Ltd. Integrity Level: HIGH Description: iniLINE CrossEX 64bit Exit code: 0 Version: 1.0.1.1550 Modules
| |||||||||||||||
| 2128 | "C:\Program Files\RaonSecure\biz\FFCert.exe" | C:\Program Files\RaonSecure\biz\FFCert.exe | KSbiz_Installer_64bit_v2_2_0_3110.exe | ||||||||||||
User: admin Company: RaonSecure Co., Ltd. Integrity Level: HIGH Description: FFCert Exit code: 0 Version: 1.0.0.8 Modules
| |||||||||||||||
| 2208 | "C:\Users\admin\AppData\Local\Temp\ffcert_raon\bin\certutil.exe" -L -d sql:"C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release" | C:\Users\admin\AppData\Local\Temp\ffcert_raon\bin\certutil.exe | — | Firefox_CertUtil.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2868 | "C:\Program Files\RaonSecure\bridge\CrossEX\touchenex\1.0.1.1550\CrossEXProtocol.dll" /S | C:\Windows\System32\regsvr32.exe | — | regsvr32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4596 | "C:\Users\admin\AppData\Local\Temp\ffcert_raon\bin\certutil.exe" -A -d sql:"C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release" -i "C:\Program Files (X86)\iniLINE\CrossEX\crossex\rootCA.crt" -n "iniLINE CrossEX RootCA2" -t "CT,C,C" | C:\Users\admin\AppData\Local\Temp\ffcert_raon\bin\certutil.exe | — | Firefox_CertUtil.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 4748 | sc create "CrossEX Live Checker" binpath= "\"C:\Program Files (x86)\iniLINE\CrossEX\crossex\ObCrossEXService.exe\"" start= auto | C:\Windows\SysWOW64\sc.exe | — | CrossEX_LocalService_Install_all.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
13 098
Read events
13 056
Write events
33
Delete events
9
Modification events
| (PID) Process: | (5960) KSbiz_Installer_64bit_v2_2_0_3110.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates |
| Operation: | delete value | Name: | 0563B8630D62D75ABBC8AB1E4BDFB5A899B24D43 |
Value: | |||
| (PID) Process: | (5960) KSbiz_Installer_64bit_v2_2_0_3110.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates\0563B8630D62D75ABBC8AB1E4BDFB5A899B24D43 |
| Operation: | write | Name: | Blob |
Value: 0300000001000000140000000563B8630D62D75ABBC8AB1E4BDFB5A899B24D432000000001000000BB030000308203B73082029FA00302010202100CE7E0E517D846FE8FE560FC1BF03039300D06092A864886F70D01010505003065310B300906035504061302555331153013060355040A130C446967694365727420496E6331193017060355040B13107777772E64696769636572742E636F6D312430220603550403131B4469676943657274204173737572656420494420526F6F74204341301E170D3036313131303030303030305A170D3331313131303030303030305A3065310B300906035504061302555331153013060355040A130C446967694365727420496E6331193017060355040B13107777772E64696769636572742E636F6D312430220603550403131B4469676943657274204173737572656420494420526F6F7420434130820122300D06092A864886F70D01010105000382010F003082010A0282010100AD0E15CEE443805CB187F3B760F97112A5AEDC269488AAF4CEF520392858600CF880DAA9159532613CB5B128848A8ADC9F0A0C83177A8F90AC8AE779535C31842AF60F98323676CCDEDD3CA8A2EF6AFB21F25261DF9F20D71FE2B1D9FE1864D2125B5FF9581835BC47CDA136F96B7FD4B0383EC11BC38C33D9D82F18FE280FB3A783D6C36E44C061359616FE599C8B766DD7F1A24B0D2BFF0B72DA9E60D08E9035C678558720A1CFE56D0AC8497C3198336C22E987D0325AA2BA138211ED39179D993A72A1E6FAA4D9D5173175AE857D22AE3F014686F62879C8B1DAE45717C47E1C0EB0B492A656B3BDB297EDAAA7F0B7C5A83F9516D0FFA196EB085F18774F0203010001A3633061300E0603551D0F0101FF040403020186300F0603551D130101FF040530030101FF301D0603551D0E0416041445EBA2AFF492CB82312D518BA7A7219DF36DC80F301F0603551D2304183016801445EBA2AFF492CB82312D518BA7A7219DF36DC80F300D06092A864886F70D01010505000382010100A20EBCDFE2EDF0E372737A6494BFF77266D832E4427562AE87EBF2D5D9DE56B39FCCCE1428B90D97605C124C58E4D33D834945589735691AA847EA56C679AB12D8678184DF7F093C94E6B8262C20BD3DB32889F75FFF22E297841FE965EF87E0DFC16749B35DEBB2092AEB26ED78BE7D3F2BF3B726356D5F8901B6495B9F01059BAB3D25C1CCB67FC2F16F86C6FA6468EB812D94EB42B7FA8C1EDD62F1BE5067B76CBDF3F11F6B0C3607167F377CA95B6D7AF112466083D72704BE4BCE97BEC3672A6811DF80E70C3366BF130D146EF37F1F63101EFA8D1B256D6C8FA5B76101B1D2A326A110719DADE2C3F9C39951B72B0708CE2EE650B2A7FA0A452FA2F0F2 | |||
| (PID) Process: | (5960) KSbiz_Installer_64bit_v2_2_0_3110.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates |
| Operation: | delete value | Name: | B1BC968BD4F49D622AA89A81F2150152A41D829C |
Value: | |||
| (PID) Process: | (5960) KSbiz_Installer_64bit_v2_2_0_3110.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates\B1BC968BD4F49D622AA89A81F2150152A41D829C |
| Operation: | write | Name: | Blob |
Value: 030000000100000014000000B1BC968BD4F49D622AA89A81F2150152A41D829C200000000100000079030000308203753082025DA003020102020B040000000001154B5AC394300D06092A864886F70D01010505003057310B300906035504061302424531193017060355040A1310476C6F62616C5369676E206E762D73613110300E060355040B1307526F6F74204341311B301906035504031312476C6F62616C5369676E20526F6F74204341301E170D3938303930313132303030305A170D3238303132383132303030305A3057310B300906035504061302424531193017060355040A1310476C6F62616C5369676E206E762D73613110300E060355040B1307526F6F74204341311B301906035504031312476C6F62616C5369676E20526F6F7420434130820122300D06092A864886F70D01010105000382010F003082010A0282010100DA0EE6998DCEA3E34F8A7EFBF18B83256BEA481FF12AB0B9951104BDF063D1E26766CF1CDDCF1B482BEE8D898E9AAF298065ABE9C72D12CBAB1C4C7007A13D0A30CD158D4FF8DDD48C50151CEF50EEC42EF7FCE952F2917DE06DD535308E5E4373F241E9D56AE3B2893A5639386F063C88695B2A4DC5A754B86C89CC9BF93CCAE5FD89F5123C927896D6DC746E934461D18DC746B2750E86E8198AD56D6CD5781695A2E9C80A38EBF224134F73549313853A1BBC1E34B58B058CB9778BB1DB1F2091AB09536E90CE7B3774B97047912251631679AEB1AE412608C8192BD146AA48D6642AD78334FF2C2AC16C19434A0785E7D37CF62168EFEAF2529F7F9390CF0203010001A3423040300E0603551D0F0101FF040403020106300F0603551D130101FF040530030101FF301D0603551D0E04160414607B661A450D97CA89502F7D04CD34A8FFFCFD4B300D06092A864886F70D01010505000382010100D673E77C4F76D08DBFECBAA2BE34C52832B57CFC6C9C2C2BBD099E53BF6B5EAA1148B6E508A3B3CA3D614DD34609B33EC3A0E363551BF2BAEFAD39E143B938A3E62F8A263BEFA05056F9C60AFD38CDC40B705194979804DFC35F94D515C914419CC45D7564150DFF5530EC868FFF0DEF2CB96346F6AAFCDFBC69FD2E1248649AE095F0A6EF298F01B115B50C1DA5FE692C6924781EB3A71C7162EECAC897AC175D8AC2F847866E2AC4563195D06789852BF96CA65D469D0CAA82E49951DD70B7DB563D61E46AE15CD6F6FE3DDE41CC07AE6352BF5353F42BE9C7FDB6F7825F85D24118DB81B3041CC51FA4806F1520C9DE0C880A1DD66655E2FC48C9292669E0 | |||
| (PID) Process: | (5960) KSbiz_Installer_64bit_v2_2_0_3110.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates |
| Operation: | delete value | Name: | 91C6D6EE3E8AC86384E548C299295C756C817B81 |
Value: | |||
| (PID) Process: | (5960) KSbiz_Installer_64bit_v2_2_0_3110.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates\91C6D6EE3E8AC86384E548C299295C756C817B81 |
| Operation: | write | Name: | Blob |
Value: 03000000010000001400000091C6D6EE3E8AC86384E548C299295C756C817B812000000001000000240400003082042030820308A0030201020210344ED55720D5EDEC49F42FCE37DB2B6D300D06092A864886F70D01010505003081A9310B300906035504061302555331153013060355040A130C7468617774652C20496E632E31283026060355040B131F43657274696669636174696F6E205365727669636573204469766973696F6E31383036060355040B132F2863292032303036207468617774652C20496E632E202D20466F7220617574686F72697A656420757365206F6E6C79311F301D06035504031316746861777465205072696D61727920526F6F74204341301E170D3036313131373030303030305A170D3336303731363233353935395A3081A9310B300906035504061302555331153013060355040A130C7468617774652C20496E632E31283026060355040B131F43657274696669636174696F6E205365727669636573204469766973696F6E31383036060355040B132F2863292032303036207468617774652C20496E632E202D20466F7220617574686F72697A656420757365206F6E6C79311F301D06035504031316746861777465205072696D61727920526F6F7420434130820122300D06092A864886F70D01010105000382010F003082010A0282010100ACA0F0FB8059D49CC7A4CF9DA159730910450C0D2C6E68F16C5B4868495937FC0B3319C2777FCC102D95341CE6EB4D09A71CD2B8C9973602B789D4245F06C0CC4494948D02626FEB5ADD118D289A5C8490107A0DBD74662F6A38A0E2D55444EB1D079F07BA6FEEE9FD4E0B29F53E84A001F19CABF81C7E89A4E8A1D871650DA3517BEEBCD222600DB95B9DDFBAFC515B0BAF98B2E92EE904E86287DE2BC8D74EC14C641EDDCF8758BA4A4FCA68071D1C9D4AC6D52F91CC7C71721CC5C067EB32FDC9925C94DA85C09BBF537D2B09F48C9D911F976A52CBDE0936A477D87B875044D53E6E2969FB3949261E09A5807B402DEBE82785C9FE61FD7EE67C971DD59D0203010001A3423040300F0603551D130101FF040530030101FF300E0603551D0F0101FF040403020106301D0603551D0E041604147B5B45CFAFCECB7AFD31921A6AB6F346EB574850300D06092A864886F70D010105050003820101007911C04BB391B6FCF0E967D40D6E45BE55E893D2CE033FEDDA25B01D57CB1E3A76A04CEC5076E864720CA4A9F1B88BD6D68784BB32E54111C077D9B3609DEB1BD5D16E4444A9A601EC55621D77B85C8E48497C9C3B5711ACAD73378E2F785C906847D96060E6FC073D222017C4F716E9C4D872F9C8737CDF162F15A93EFD6A27B6A1EB5ABA981FD5E34D640A9D13C861BAF5391C87BAB8BD7B227FF6FEAC4079E5AC106F3D8F1B79768BC437B3211884E53600EB632099B9E9FE3304BB41C8C102F94463209E81CE42D3D63F2C76D3639C59DD8FA6E10EA02E41F72E9547CFBCFD33F3F60B617E7E912B8147C22730EEA7105D378F5C392BE404F07B8D568C68 | |||
| (PID) Process: | (5960) KSbiz_Installer_64bit_v2_2_0_3110.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates |
| Operation: | delete value | Name: | BE36A4562FB2EE05DBB3D32323ADF445084ED656 |
Value: | |||
| (PID) Process: | (5960) KSbiz_Installer_64bit_v2_2_0_3110.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates\BE36A4562FB2EE05DBB3D32323ADF445084ED656 |
| Operation: | write | Name: | Blob |
Value: 030000000100000014000000BE36A4562FB2EE05DBB3D32323ADF445084ED6562000000001000000A5020000308202A13082020AA003020102020100300D06092A864886F70D010104050030818B310B3009060355040613025A41311530130603550408130C5765737465726E2043617065311430120603550407130B44757262616E76696C6C65310F300D060355040A1306546861777465311D301B060355040B13145468617774652043657274696669636174696F6E311F301D060355040313165468617774652054696D657374616D70696E67204341301E170D3937303130313030303030305A170D3230313233313233353935395A30818B310B3009060355040613025A41311530130603550408130C5765737465726E2043617065311430120603550407130B44757262616E76696C6C65310F300D060355040A1306546861777465311D301B060355040B13145468617774652043657274696669636174696F6E311F301D060355040313165468617774652054696D657374616D70696E6720434130819F300D06092A864886F70D010101050003818D0030818902818100D62B587861458653EA347B519CEDB0E62E180EFEE05FA827D3B4C9E07C594E160E735460C17FF69F2EE93A8524153CDB470463C39EC4941A5ADF4C7AF3D9431D3C107A7925DB90FEF051E730D64100FD9F28DF79BE94BB9DB614E32385D7A941E04CA479B02B1A8BF2F83B8A3E45AC719200B4904198FB5FEDFAB72E8AF888370203010001A3133011300F0603551D130101FF040530030101FF300D06092A864886F70D01010405000381810067DBE2C2E6873D40838637357D1FCE9AC30C6620A8BAAA048986C2F510080DBFCBA2058AD04D363EF4D7EF69C65EE4B0946F4AB9E7DE5B88B67BDBE327E576C3F035C1CBB5279B3379DC90A6009E77FAFCCD279442169CD31C68ECBF5CDDE5A97B100A32745413318B85038491B75801301438AF28CAFCB150191909AC8949D3 | |||
| (PID) Process: | (5960) KSbiz_Installer_64bit_v2_2_0_3110.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates |
| Operation: | delete value | Name: | 4EB6D578499B1CCF5F581EAD56BE3D9B6744A5E5 |
Value: | |||
| (PID) Process: | (5960) KSbiz_Installer_64bit_v2_2_0_3110.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates\4EB6D578499B1CCF5F581EAD56BE3D9B6744A5E5 |
| Operation: | write | Name: | Blob |
Value: 0300000001000000140000004EB6D578499B1CCF5F581EAD56BE3D9B6744A5E52000000001000000D7040000308204D3308203BBA003020102021018DAD19E267DE8BB4A2158CDCC6B3B4A300D06092A864886F70D01010505003081CA310B300906035504061302555331173015060355040A130E566572695369676E2C20496E632E311F301D060355040B1316566572695369676E205472757374204E6574776F726B313A3038060355040B1331286329203230303620566572695369676E2C20496E632E202D20466F7220617574686F72697A656420757365206F6E6C79314530430603550403133C566572695369676E20436C6173732033205075626C6963205072696D6172792043657274696669636174696F6E20417574686F72697479202D204735301E170D3036313130383030303030305A170D3336303731363233353935395A3081CA310B300906035504061302555331173015060355040A130E566572695369676E2C20496E632E311F301D060355040B1316566572695369676E205472757374204E6574776F726B313A3038060355040B1331286329203230303620566572695369676E2C20496E632E202D20466F7220617574686F72697A656420757365206F6E6C79314530430603550403133C566572695369676E20436C6173732033205075626C6963205072696D6172792043657274696669636174696F6E20417574686F72697479202D20473530820122300D06092A864886F70D01010105000382010F003082010A0282010100AF240808297A359E600CAAE74B3B4EDC7CBC3C451CBB2BE0FE2902F95708A364851527F5F1ADC831895D22E82AAAA642B38FF8B955B7B1B74BB3FE8F7E0757ECEF43DB66621561CF600DA4D8DEF8E0C362083D5413EB49CA59548526E52B8F1B9FEBF5A191C23349D843636A524BD28FE870514DD189697BC770F6B3DC1274DB7B5D4B56D396BF1577A1B0F4A225F2AF1C926718E5F40604EF90B9E400E4DD3AB519FF02BAF43CEEE08BEB378BECF4D7ACF2F6F03DAFDD759133191D1C40CB7424192193D914FEAC2A52C78FD50449E48D6347883C6983CBFE47BD2B7E4FC595AE0E9DD4D143C06773E314087EE53F9F73B8330ACF5D3F3487968AEE53E825150203010001A381B23081AF300F0603551D130101FF040530030101FF300E0603551D0F0101FF040403020106306D06082B0601050507010C0461305FA15DA05B3059305730551609696D6167652F6769663021301F300706052B0E03021A04148FE5D31A86AC8D8E6BC3CF806AD448182C7B192E30251623687474703A2F2F6C6F676F2E766572697369676E2E636F6D2F76736C6F676F2E676966301D0603551D0E041604147FD365A7C2DDECBBF03009F34339FA02AF333133300D06092A864886F70D0101050500038201010093244A305F62CFD81A982F3DEADC992DBD77F6A5792238ECC4A7A07812AD620E457064C5E797662D98097E5FAFD6CC2865F201AA081A47DEF9F97C925A0869200DD93E6D6E3C0D6ED8E606914018B9F8C1EDDFDB41AAE09620C9CD64153881C994EEA284290B136F8EDB0CDD2502DBA48B1944D2417A05694A584F60CA7E826A0B02AA251739B5DB7FE784652A958ABD86DE5E8116832D10CCDEFDA8822A6D281F0D0BC4E5E71A2619E1F4116F10B595FCE7420532DBCE9D515E28B69E85D35BEFA57D4540728EB70E6B0E06FB33354871B89D278BC4655F0D86769C447AF6955CF65D320833A454B6183F685CF2424A853854835FD1E82CF2AC11D6A8ED636A | |||
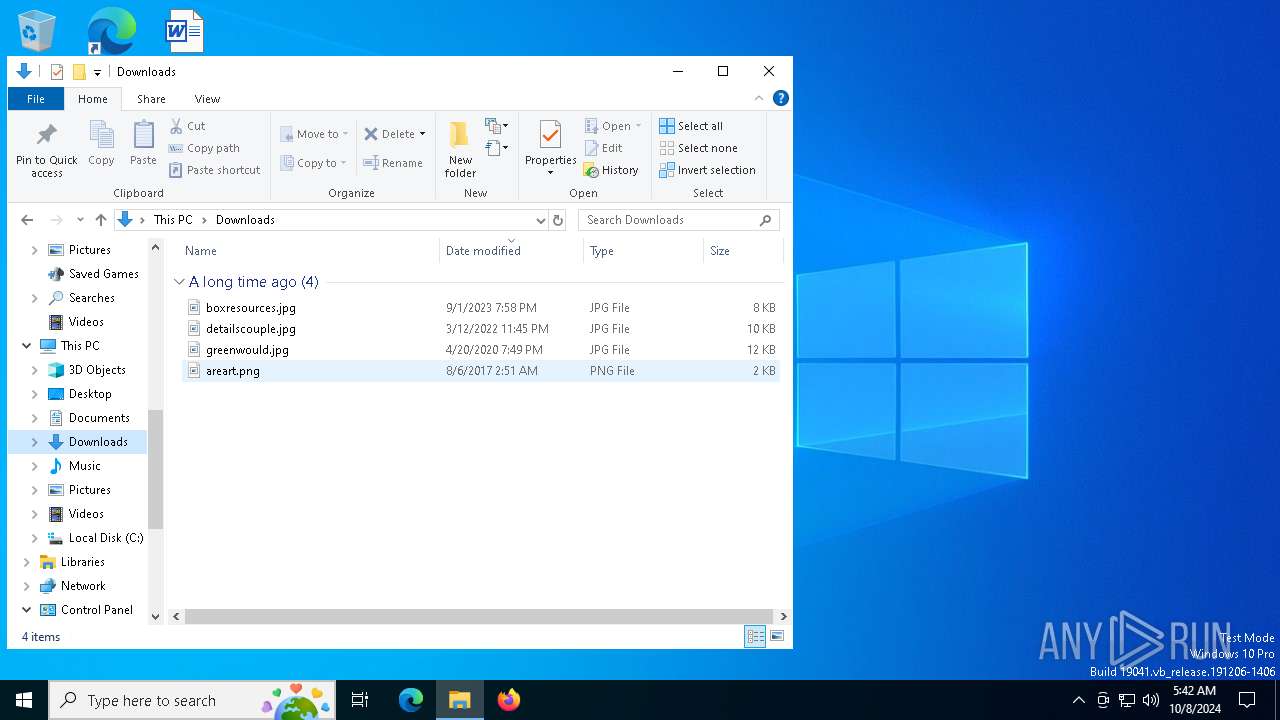
Executable files
40
Suspicious files
23
Text files
4
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5960 | KSbiz_Installer_64bit_v2_2_0_3110.exe | C:\Program Files\RaonSecure\biz\_rca_thawte_root.cer | binary | |
MD5:8CCADC0B22CEF5BE72AC411A11A8D812 | SHA256:8D722F81A9C113C0791DF136A2966DB26C950A971DB46B4199F4EA54B78BFB9F | |||
| 5960 | KSbiz_Installer_64bit_v2_2_0_3110.exe | C:\Users\admin\AppData\Local\Temp\nsq6233.tmp\nsProcess.dll | executable | |
MD5:665ABF2ECB2928F01498C84FA0E66442 | SHA256:83A45BC2DF616D5D6331692A5DC559C566A588F4E1DDA17D6D7FCF2F48F93949 | |||
| 5960 | KSbiz_Installer_64bit_v2_2_0_3110.exe | C:\Program Files\RaonSecure\biz\KeySharpCryptoV1_4_ext.dll | executable | |
MD5:B96672CDE41D1477567B2CBC21E830D8 | SHA256:ACC76D52B137C464F2C633DD7C91640D4E39E8F3C923C302B9AD96547264D9E3 | |||
| 5960 | KSbiz_Installer_64bit_v2_2_0_3110.exe | C:\Program Files\RaonSecure\biz\_rca_digicert_root.cer | der | |
MD5:87CE0B7B2A0E4900E158719B37A89372 | SHA256:3E9099B5015E8F486C00BCEA9D111EE721FABA355A89BCF1DF69561E3DC6325C | |||
| 5960 | KSbiz_Installer_64bit_v2_2_0_3110.exe | C:\Program Files\RaonSecure\biz\KeySharpCryptoV1_4.dll | executable | |
MD5:84B735903D030F2604F79F312B3E0B0E | SHA256:C889CB536DCBBB9FF630FDD5E5E6394FE82877959525CC2ED0F745538CB1F807 | |||
| 5960 | KSbiz_Installer_64bit_v2_2_0_3110.exe | C:\Program Files\RaonSecure\biz\_rca_verisign_root.cer | binary | |
MD5:8EADB501AA4D81E48C1DD1E114009519 | SHA256:2399561127A57125DE8CEFEA610DDF2FA078B5C8067F4E828290BFB860E84B3C | |||
| 5960 | KSbiz_Installer_64bit_v2_2_0_3110.exe | C:\Program Files\RaonSecure\biz\bizcrypto_ecdh.dll | executable | |
MD5:F5188D8E56FDC1AE925B69119AACE84C | SHA256:6AA20A9634AE6A94EB7AFC5C4A22F85A9C0185C9C4B3859BF91018AC3993C0EB | |||
| 5960 | KSbiz_Installer_64bit_v2_2_0_3110.exe | C:\Program Files\RaonSecure\biz\_rca_globalsign_root.cer | binary | |
MD5:3E455215095192E1B75D379FB187298A | SHA256:EBD41040E4BB3EC742C9E381D31EF2A41A48B6685C96E7CEF3C1DF6CD4331C99 | |||
| 5960 | KSbiz_Installer_64bit_v2_2_0_3110.exe | C:\Program Files\RaonSecure\biz\_rca_thawte_time.cer | binary | |
MD5:7F667A71D3EB6978209A51149D83DA20 | SHA256:6B6C1E01F590F5AFC5FCF85CD0B9396884048659FC2C6D1170D68B045216C3FD | |||
| 5960 | KSbiz_Installer_64bit_v2_2_0_3110.exe | C:\Users\admin\AppData\Local\Temp\nsq6233.tmp\modern-wizard.bmp | image | |
MD5:CBE40FD2B1EC96DAEDC65DA172D90022 | SHA256:3AD2DC318056D0A2024AF1804EA741146CFC18CC404649A44610CBF8B2056CF2 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
44
DNS requests
17
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2120 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5880 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2144 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1168 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
2144 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6796 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6796 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3260 | svchost.exe | 40.115.3.253:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5880 | svchost.exe | 20.190.160.14:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5880 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |