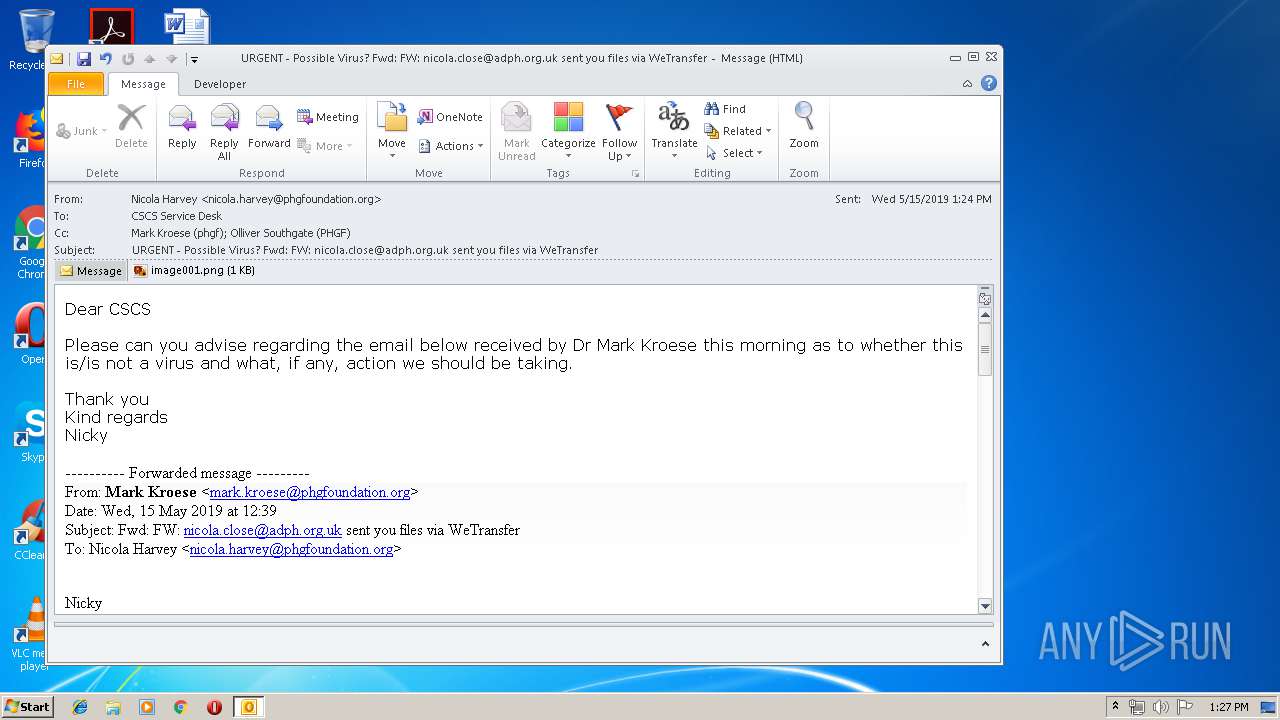
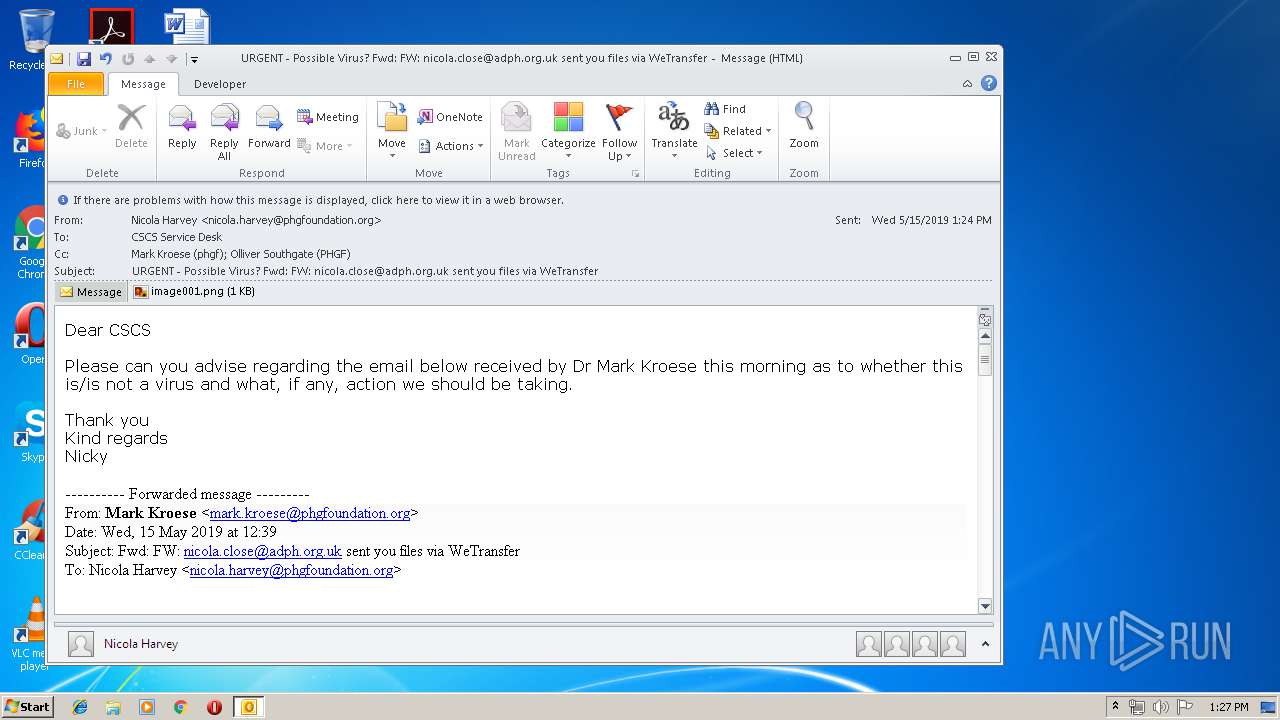
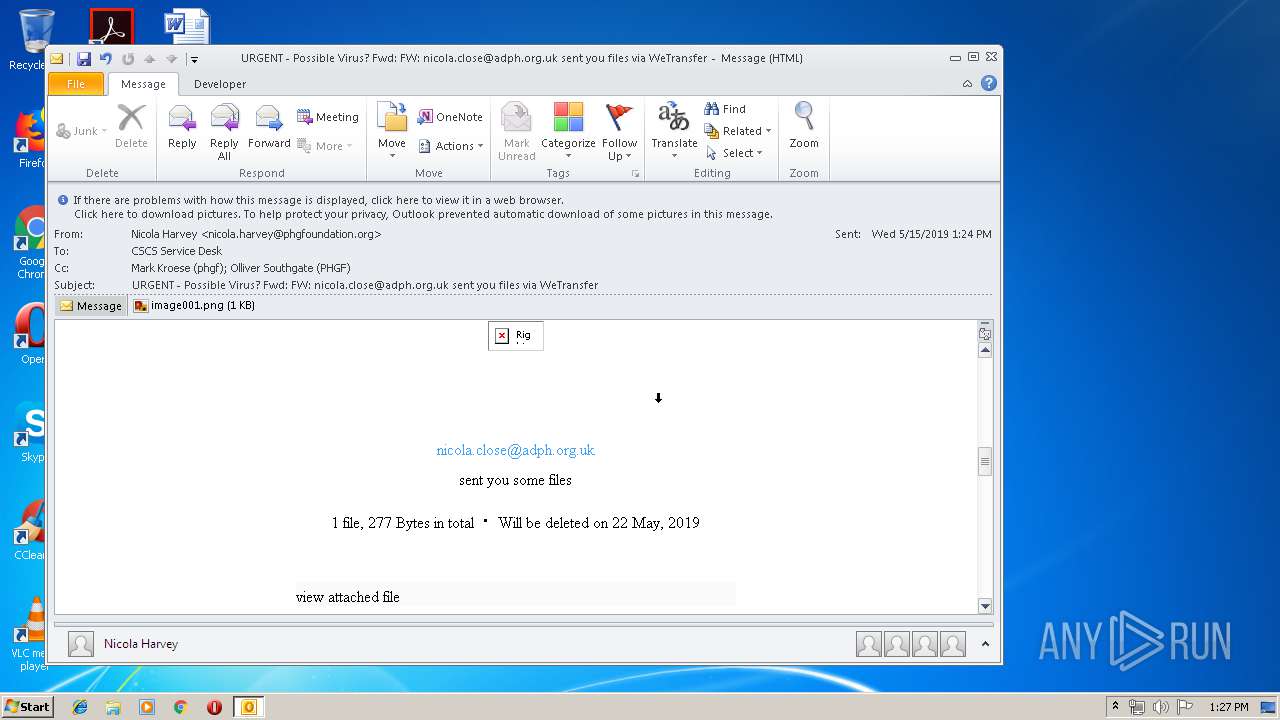
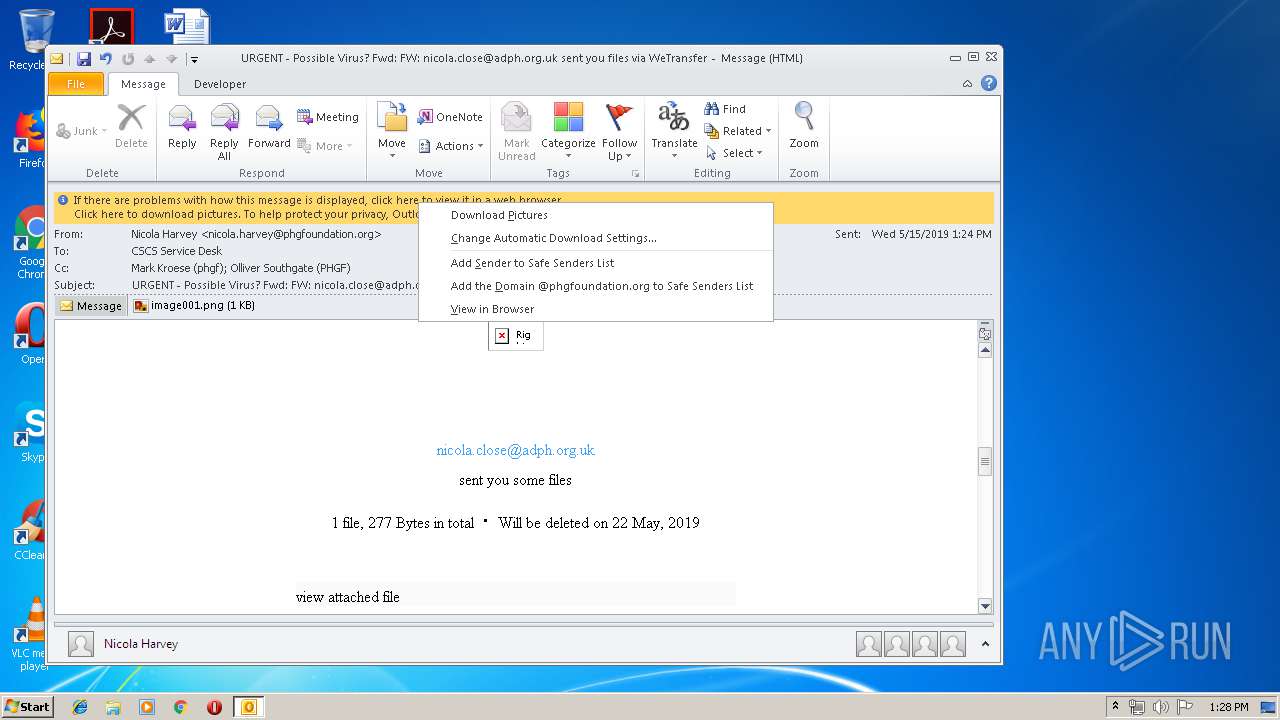
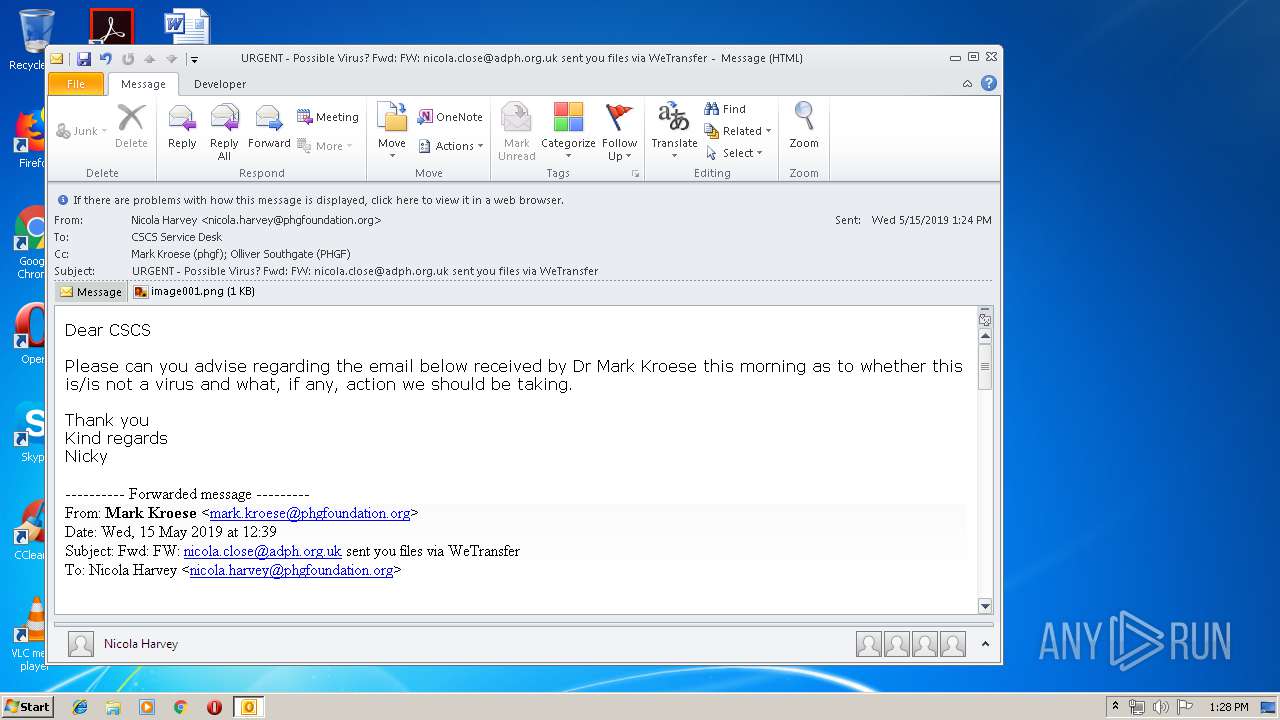
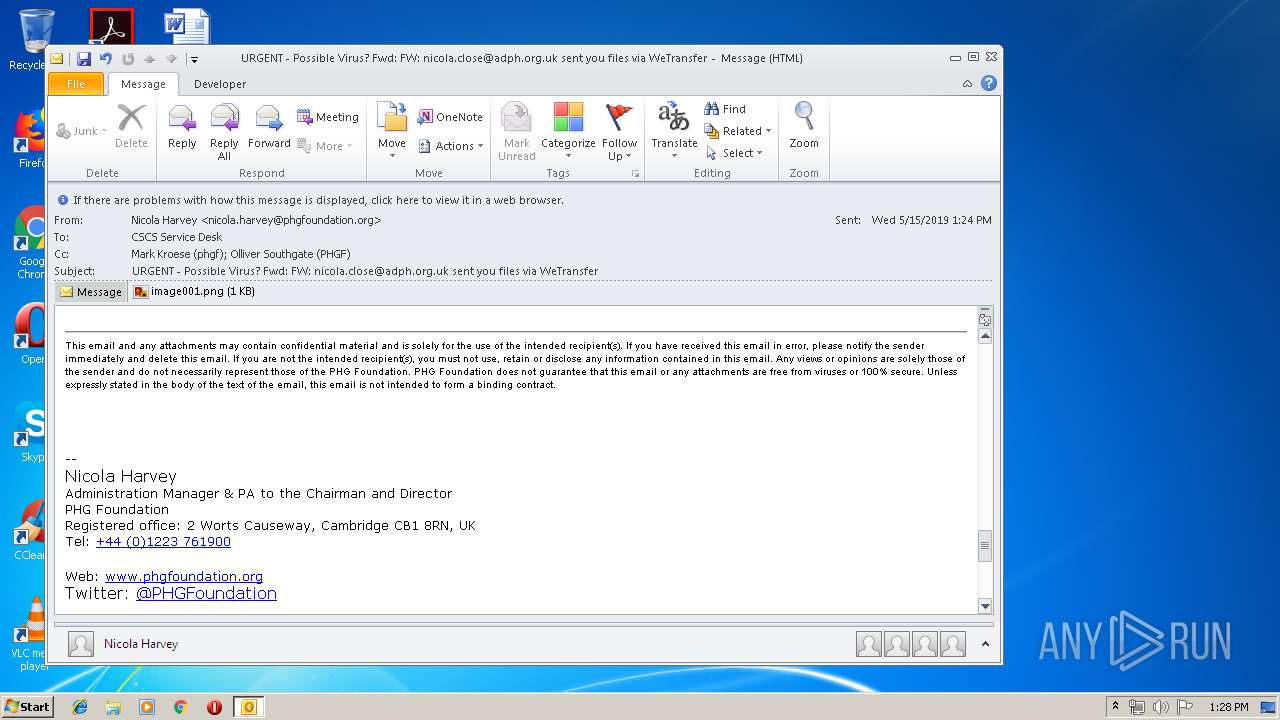
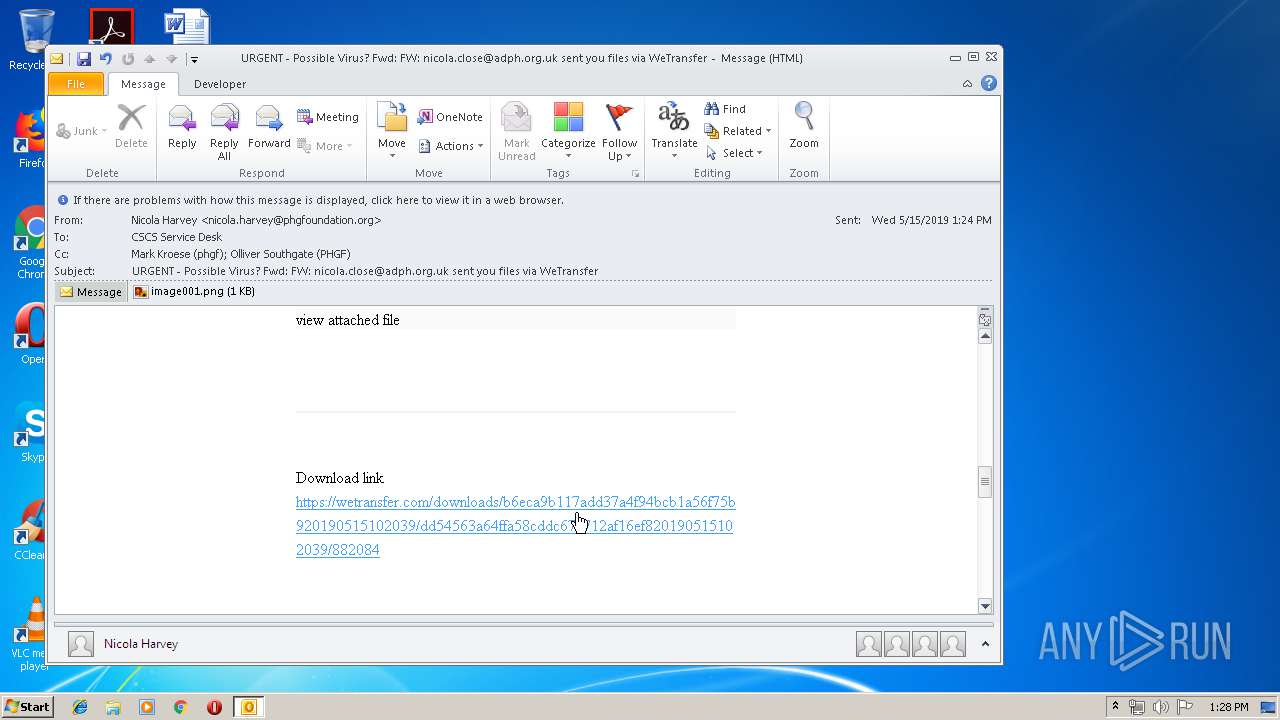
| File name: | URGENT - Possible Virus Fwd FW nicola.close@adph.org.uk sent you files via WeTransfer.msg |
| Full analysis: | https://app.any.run/tasks/5d1b3462-4b4a-432f-a3f1-9140c661705a |
| Verdict: | Malicious activity |
| Analysis date: | May 15, 2019, 12:27:07 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | 7E3CC215BD36EFFDCFE3036725B463FF |
| SHA1: | A1E1D7F6F51F88BCCBC6299AC4498376A5C1B8F5 |
| SHA256: | B4517AA5C2AB32EACB2A6A9DA6369E2527169EC5973E4B419B00F7FFB46ED82A |
| SSDEEP: | 3072:WWqhzXU7N1Is4gFN4LqpqPRC0D1OT28W88mXqHrdaXMRlcEG:F+zqnIs4mT0BOT7XMR |
MALICIOUS
Unusual execution from Microsoft Office
- OUTLOOK.EXE (PID: 3384)
SUSPICIOUS
Starts itself from another location
- OUTLOOK.EXE (PID: 3384)
Creates files in the user directory
- OUTLOOK.EXE (PID: 3384)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 3384)
Starts Internet Explorer
- OUTLOOK.EXE (PID: 3384)
INFO
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 3384)
- OUTLOOK.EXE (PID: 252)
Changes internet zones settings
- iexplore.exe (PID: 3088)
Creates files in the user directory
- iexplore.exe (PID: 2284)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3088)
Reads Internet Cache Settings
- iexplore.exe (PID: 2284)
Reads settings of System Certificates
- OUTLOOK.EXE (PID: 3384)
- iexplore.exe (PID: 3088)
Changes settings of System certificates
- iexplore.exe (PID: 3088)
Reads internet explorer settings
- iexplore.exe (PID: 2284)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
37
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
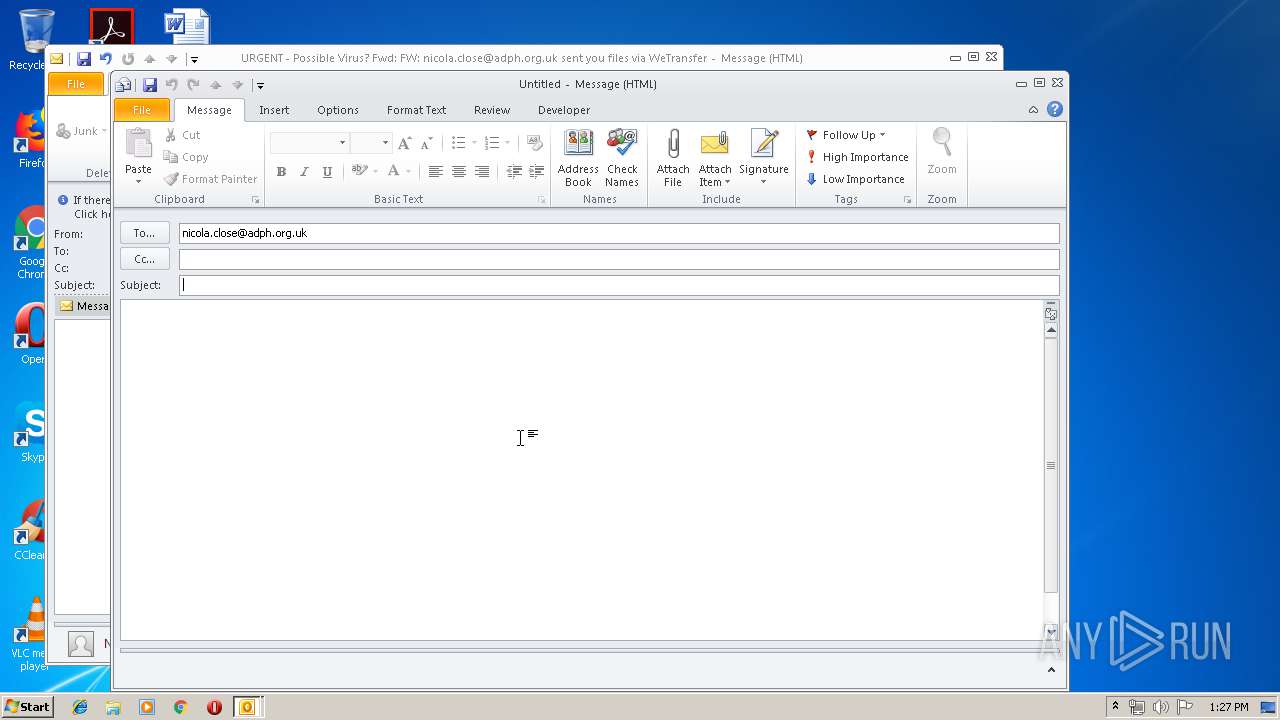
| 252 | "C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE" -c IPM.Note /m "mailto:nicola.close@adph.org.uk" | C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 2284 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3088 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
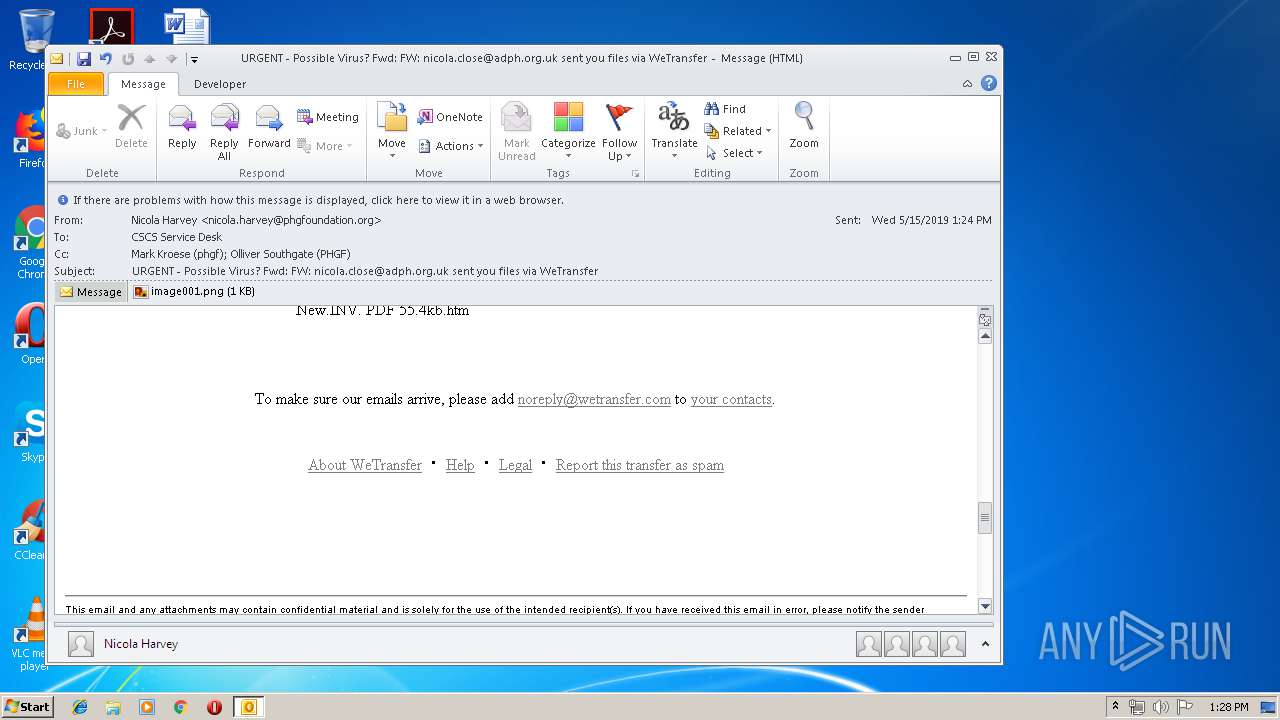
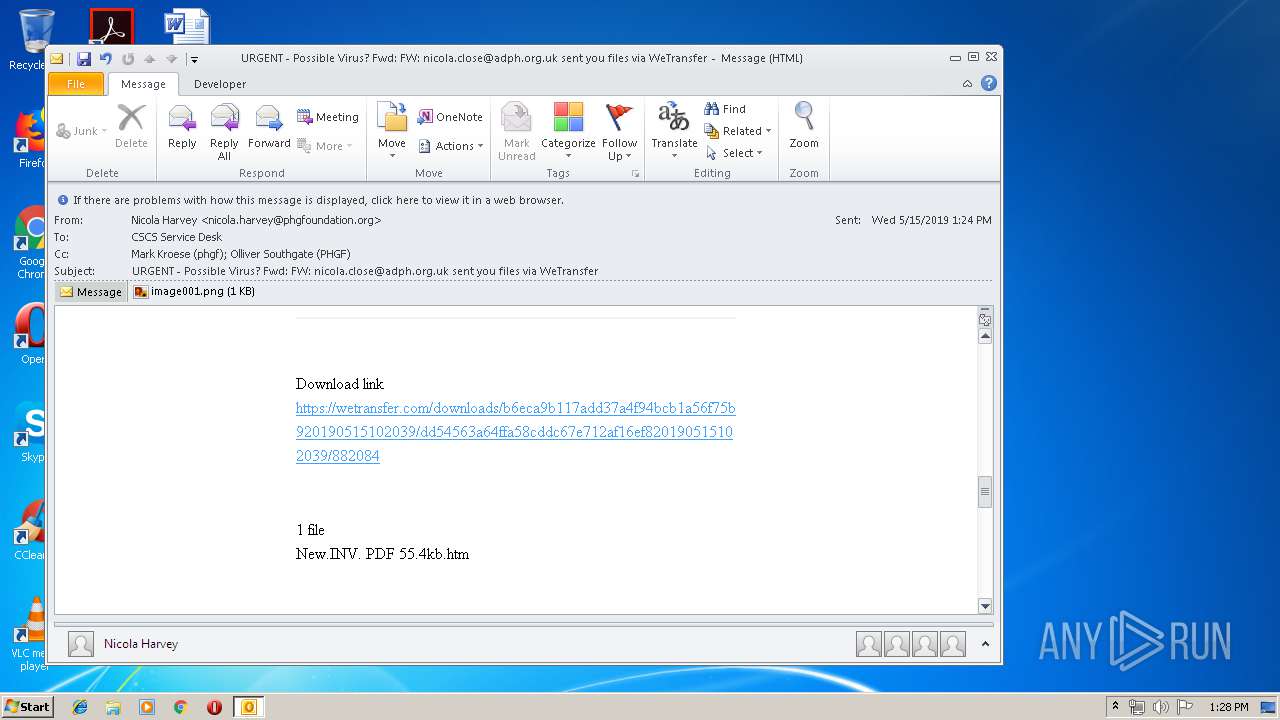
| 3088 | "C:\Program Files\Internet Explorer\iexplore.exe" https://wetransfer.com/downloads/b6eca9b117add37a4f94bcb1a56f75b920190515102039/dd54563a64ffa58cddc67e712af16ef820190515102039/882084 | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3384 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\URGENT - Possible Virus Fwd FW nicola.close@adph.org.uk sent you files via WeTransfer.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
Total events
1 705
Read events
1 203
Write events
470
Delete events
32
Modification events
| (PID) Process: | (3384) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3384) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3384) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\Resiliency\StartupItems |
| Operation: | write | Name: | j;= |
Value: 6A3B3D00380D0000010000000000000000000000 | |||
| (PID) Process: | (3384) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook |
| Operation: | write | Name: | MTTT |
Value: 380D00003C6C528C190BD50100000000 | |||
| (PID) Process: | (3384) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionNumber |
Value: 0 | |||
| (PID) Process: | (3384) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionDate |
Value: 220039200 | |||
| (PID) Process: | (3384) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\0a0d020000000000c000000000000046 |
| Operation: | write | Name: | 00030429 |
Value: 03000000 | |||
| (PID) Process: | (3384) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | {ED475418-B0D6-11D2-8C3B-00104B2A6676} |
Value: | |||
| (PID) Process: | (3384) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | LastChangeVer |
Value: 1200000000000000 | |||
| (PID) Process: | (3384) OUTLOOK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109A10090400000000000F01FEC\Usage |
| Operation: | write | Name: | OutlookMAPI2Intl_1033 |
Value: 1320091669 | |||
Executable files
0
Suspicious files
5
Text files
45
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3384 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRF4A.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 252 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR8601.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3384 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\open[1].gif | — | |
MD5:— | SHA256:— | |||
| 3384 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CabAB8B.tmp | — | |
MD5:— | SHA256:— | |||
| 3384 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\TarAB8C.tmp | — | |
MD5:— | SHA256:— | |||
| 3384 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CabABAC.tmp | — | |
MD5:— | SHA256:— | |||
| 3384 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\TarABAD.tmp | — | |
MD5:— | SHA256:— | |||
| 3384 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@google[1].txt | — | |
MD5:— | SHA256:— | |||
| 3384 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CabAC99.tmp | — | |
MD5:— | SHA256:— | |||
| 3384 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\TarAC9A.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
19
DNS requests
11
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3384 | OUTLOOK.EXE | GET | 200 | 205.185.216.10:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 56.1 Kb | whitelisted |
3384 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
3384 | OUTLOOK.EXE | GET | 200 | 143.204.98.159:80 | http://x.ss2.us/x.cer | US | der | 1.27 Kb | whitelisted |
3384 | OUTLOOK.EXE | GET | 200 | 167.89.123.54:80 | http://email.wetransfer.com/wf/open?upn=nyz2CgSinkhLLXKE5y9NvdofvxymledPqh9iIiv6zre0MRLksURHkLxc7MTFNxsWIzZMmE0-2FqQ8oCWCJh2T8oD-2FFbSv10V6nkF57TnS-2Faujk8B4BilS153HwkOe2RdyhP80Ol3mxr-2FQDyXx5G4YDDFNcAv1-2BETfRwSNJYnFor-2FZG0wA7K9TfswuANZ0-2FfGrXKbf796sXVVc8eKJ9fEfXhwvnJN0JTV40PtV9pnmIS-2BrQn95kwplXA00sOGs9EKMfTfxv0rb4l0HLxqvHNh96RIWanhs2WMdTrdlC-2F5Opv4dWNq-2B24I5L0v6iYTg6WQzCWnHBt1MZD1SB0FC-2B8qWR-2FbqxNAhkIgWuGOVx64qJsqGPbzqVgR3LB55qth2Zld8CX0Op9iI7Tg0NiARQpJBDYQ-3D-3D | US | image | 43 b | suspicious |
3088 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3384 | OUTLOOK.EXE | 167.89.123.54:80 | email.wetransfer.com | SendGrid, Inc. | US | suspicious |
3384 | OUTLOOK.EXE | 172.217.21.206:443 | docs.google.com | Google Inc. | US | whitelisted |
— | — | 205.185.216.10:80 | www.download.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
2284 | iexplore.exe | 52.211.136.15:443 | wetransfer.com | Amazon.com, Inc. | IE | unknown |
3384 | OUTLOOK.EXE | 143.204.101.127:443 | prod-cdn.wetransfer.net | — | US | unknown |
— | — | 143.204.98.159:80 | x.ss2.us | — | US | suspicious |
2284 | iexplore.exe | 143.204.98.115:443 | d19ptbnuzhibkh.cloudfront.net | — | US | suspicious |
2284 | iexplore.exe | 216.58.207.72:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
3088 | iexplore.exe | 143.204.101.127:443 | prod-cdn.wetransfer.net | — | US | unknown |
3384 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
prod-cdn.wetransfer.net |
| whitelisted |
email.wetransfer.com |
| suspicious |
docs.google.com |
| shared |
x.ss2.us |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |
doc-0o-9k-docs.googleusercontent.com |
| shared |
wetransfer.com |
| shared |
www.bing.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |