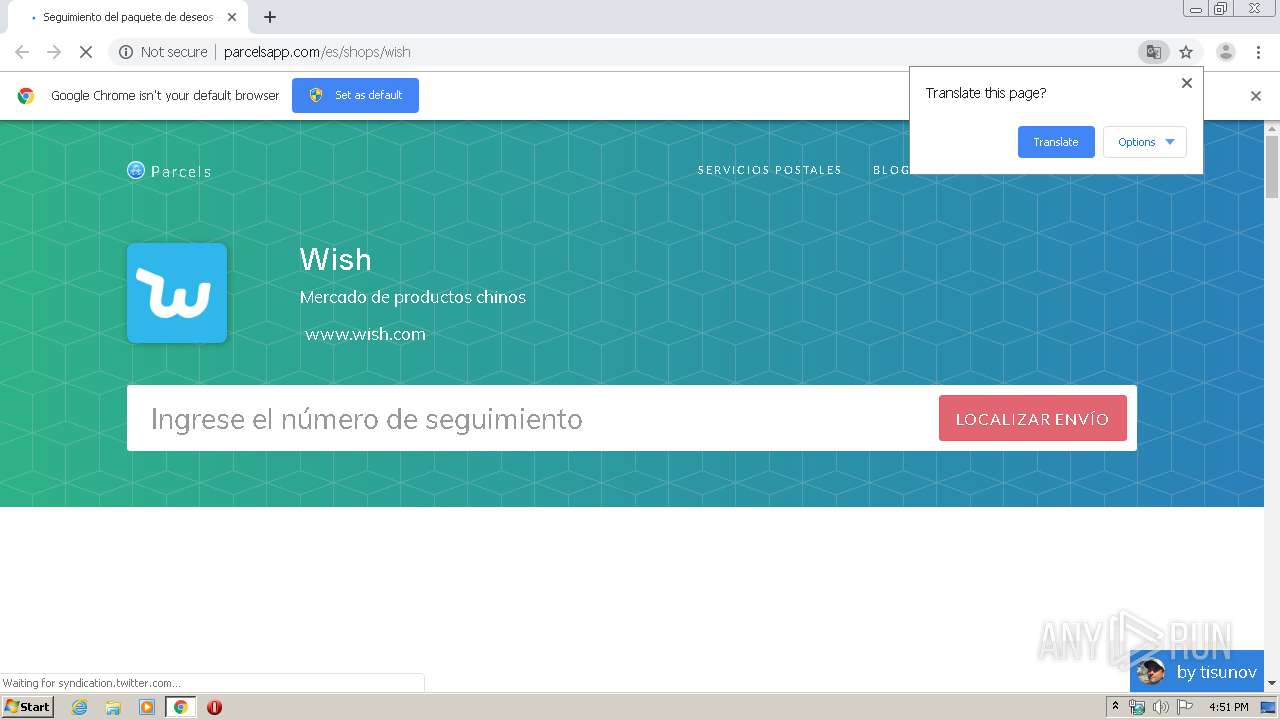
| URL: | http://parcelsapp.com/es/shops/wish |
| Full analysis: | https://app.any.run/tasks/6d98b8f3-10db-4fad-aaec-d614ecd49c26 |
| Verdict: | Malicious activity |
| Analysis date: | March 30, 2020, 15:51:09 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 1A90266365B7524812B9C60C66D2672C |
| SHA1: | 451933157791EA3BAB7C838E1312858CACD4D2AF |
| SHA256: | B44F0FF4BF9A1AA9AC4F2B1D3608A2035B4C1AEEE12D32AFC4C4DC46A59B2B5B |
| SSDEEP: | 3:N1KOEXolU4WCWN:COR34N |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 1748)
INFO
Reads the hosts file
- chrome.exe (PID: 3364)
- chrome.exe (PID: 1748)
Application launched itself
- chrome.exe (PID: 1748)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
65
Monitored processes
29
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 604 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,14334500486330115458,1680929877215465718,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14708004215022881785 --mojo-platform-channel-handle=4580 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 680 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6fa8a9d0,0x6fa8a9e0,0x6fa8a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1500 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,14334500486330115458,1680929877215465718,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=164413700704511281 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2280 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1632 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,14334500486330115458,1680929877215465718,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11840842235309895575 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2932 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1720 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,14334500486330115458,1680929877215465718,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9508707819506287370 --mojo-platform-channel-handle=3820 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1748 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://parcelsapp.com/es/shops/wish" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1920 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,14334500486330115458,1680929877215465718,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=90461216877202528 --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3416 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2056 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,14334500486330115458,1680929877215465718,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12735110560225129733 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2500 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2076 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,14334500486330115458,1680929877215465718,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6198177351442009930 --mojo-platform-channel-handle=3732 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2388 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,14334500486330115458,1680929877215465718,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=703241684843289275 --mojo-platform-channel-handle=3696 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
602
Read events
531
Write events
67
Delete events
4
Modification events
| (PID) Process: | (3236) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1748-13230057084932125 |
Value: 259 | |||
| (PID) Process: | (1748) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1748) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1748) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1748) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1748) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1748) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1748) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1748) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (1748) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
45
Text files
235
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1748 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5E82157D-6D4.pma | — | |
MD5:— | SHA256:— | |||
| 1748 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1748 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\1aa47222-54db-47e2-8ab0-ddcd1a7dff0c.tmp | — | |
MD5:— | SHA256:— | |||
| 1748 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1748 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old~RFa66c5e.TMP | text | |
MD5:— | SHA256:— | |||
| 1748 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1748 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RFa66c20.TMP | text | |
MD5:— | SHA256:— | |||
| 1748 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1748 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1748 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFa66d29.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
29
TCP/UDP connections
72
DNS requests
43
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3364 | chrome.exe | GET | 200 | 176.58.96.46:80 | http://parcelsapp.com/es/shops/wish | GB | html | 9.70 Kb | whitelisted |
3364 | chrome.exe | GET | 200 | 52.222.149.252:80 | http://cdn.parcelsapp.com/assets/application-b9831a1b89fcf3da3c5f8c823449a1b16249a29fceaebf47769c9e79b32897a3.css | US | text | 87.3 Kb | shared |
3364 | chrome.exe | GET | 200 | 52.222.149.252:80 | http://cdn.parcelsapp.com/assets/landing/carriers/wish-e44e34a1e105ecf5652f74abb6294666f6a54cbc7ebec40682d935b9a21045a8.jpg | US | image | 4.79 Kb | shared |
3364 | chrome.exe | GET | 200 | 151.101.112.157:80 | http://platform.twitter.com/widgets.js | US | text | 28.4 Kb | whitelisted |
3364 | chrome.exe | GET | 200 | 52.222.149.252:80 | http://cdn.parcelsapp.com/assets/landing/es/google-play-badge-44e6d6d8724459ea7ffd7948989392b942d601abde4ed54795b7da25abdbb740.svg | US | image | 5.91 Kb | shared |
3364 | chrome.exe | GET | 200 | 52.222.149.252:80 | http://cdn.parcelsapp.com/assets/application-4d8bafb73071bda129ac6b231e5126dd4d30110223755d5cbb090053b93b2fba.js | US | text | 72.7 Kb | shared |
3364 | chrome.exe | GET | 200 | 216.58.210.2:80 | http://pagead2.googlesyndication.com/pagead/js/adsbygoogle.js | US | text | 38.2 Kb | whitelisted |
3364 | chrome.exe | GET | 200 | 52.222.149.252:80 | http://cdn.parcelsapp.com/packs/application-c8a7c20af642119d53e1.js | US | text | 20.1 Kb | shared |
3364 | chrome.exe | GET | 200 | 52.222.149.252:80 | http://cdn.parcelsapp.com/assets/landing/es/app-store-badge-ff496c9c90216f0f065120b8f52ea6d1b0b618c00aaac03d30c3ecc1b13ce3b2.svg | US | image | 4.43 Kb | shared |
3364 | chrome.exe | GET | 200 | 176.58.96.46:80 | http://parcelsapp.com/ads.js | GB | text | 111 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3364 | chrome.exe | 172.217.18.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3364 | chrome.exe | 176.58.96.46:80 | parcelsapp.com | Linode, LLC | GB | unknown |
3364 | chrome.exe | 172.217.16.205:443 | accounts.google.com | Google Inc. | US | whitelisted |
3364 | chrome.exe | 104.17.65.4:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | unknown |
3364 | chrome.exe | 23.111.9.35:443 | use.fontawesome.com | netDNA | US | suspicious |
3364 | chrome.exe | 216.58.210.2:80 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
3364 | chrome.exe | 151.101.2.109:443 | cdn.polyfill.io | Fastly | US | suspicious |
3364 | chrome.exe | 151.101.112.157:80 | platform.twitter.com | Fastly | US | suspicious |
3364 | chrome.exe | 172.217.22.68:443 | www.google.com | Google Inc. | US | whitelisted |
3364 | chrome.exe | 172.217.22.35:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
parcelsapp.com |
| whitelisted |
accounts.google.com |
| shared |
cdn.parcelsapp.com |
| shared |
use.fontawesome.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
cdn.polyfill.io |
| whitelisted |
platform.twitter.com |
| whitelisted |
www.google.com |
| malicious |