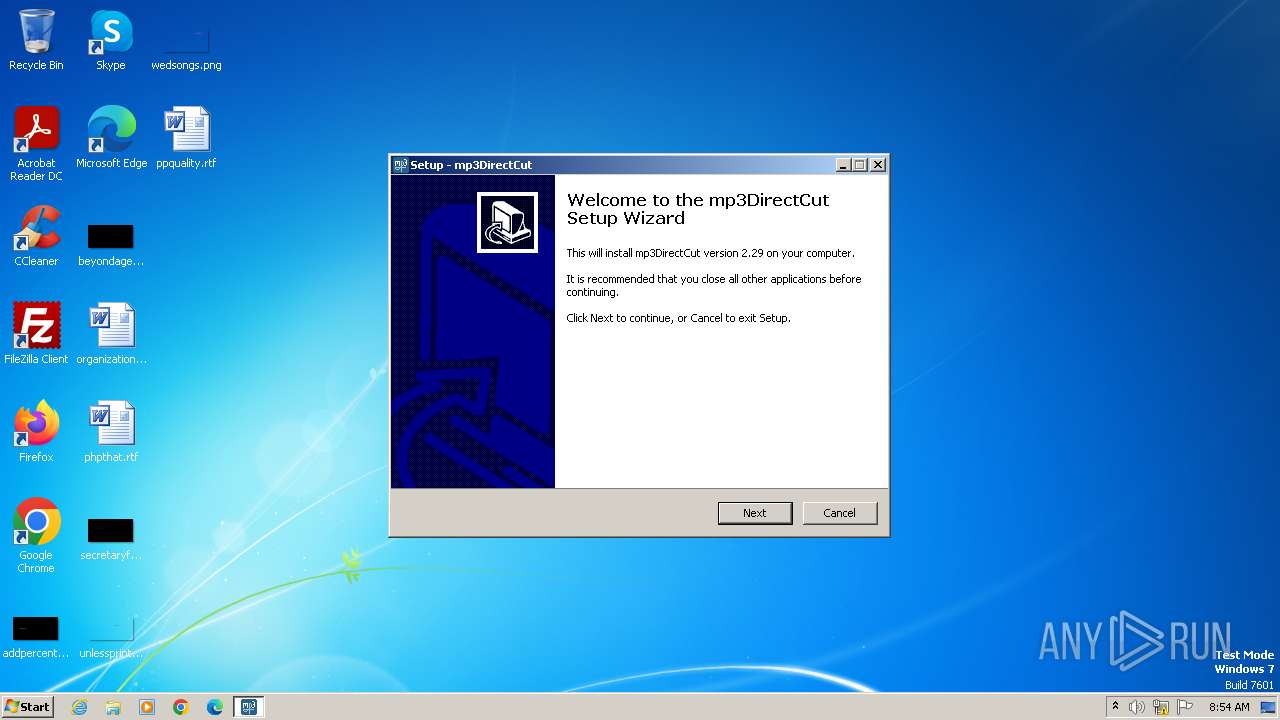
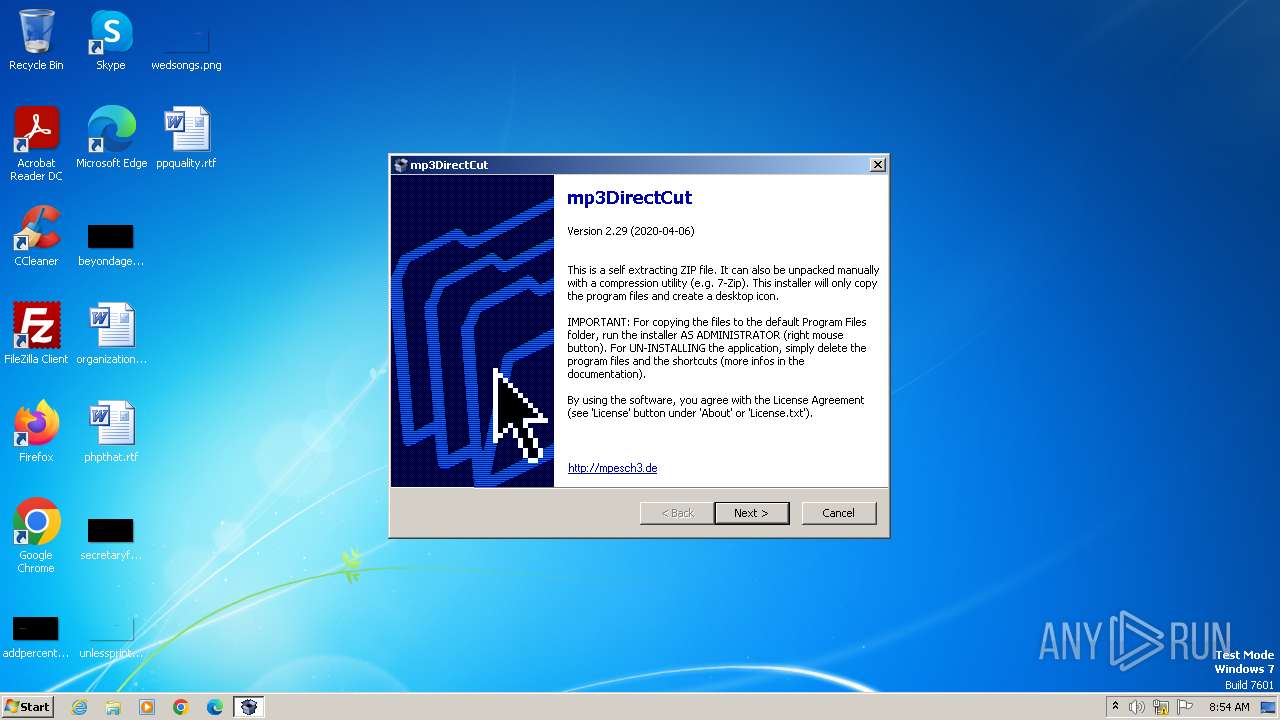
| File name: | mp3directcut.exe |
| Full analysis: | https://app.any.run/tasks/24c1fcfd-cb1a-48f1-9b79-b111baf1ff3f |
| Verdict: | Malicious activity |
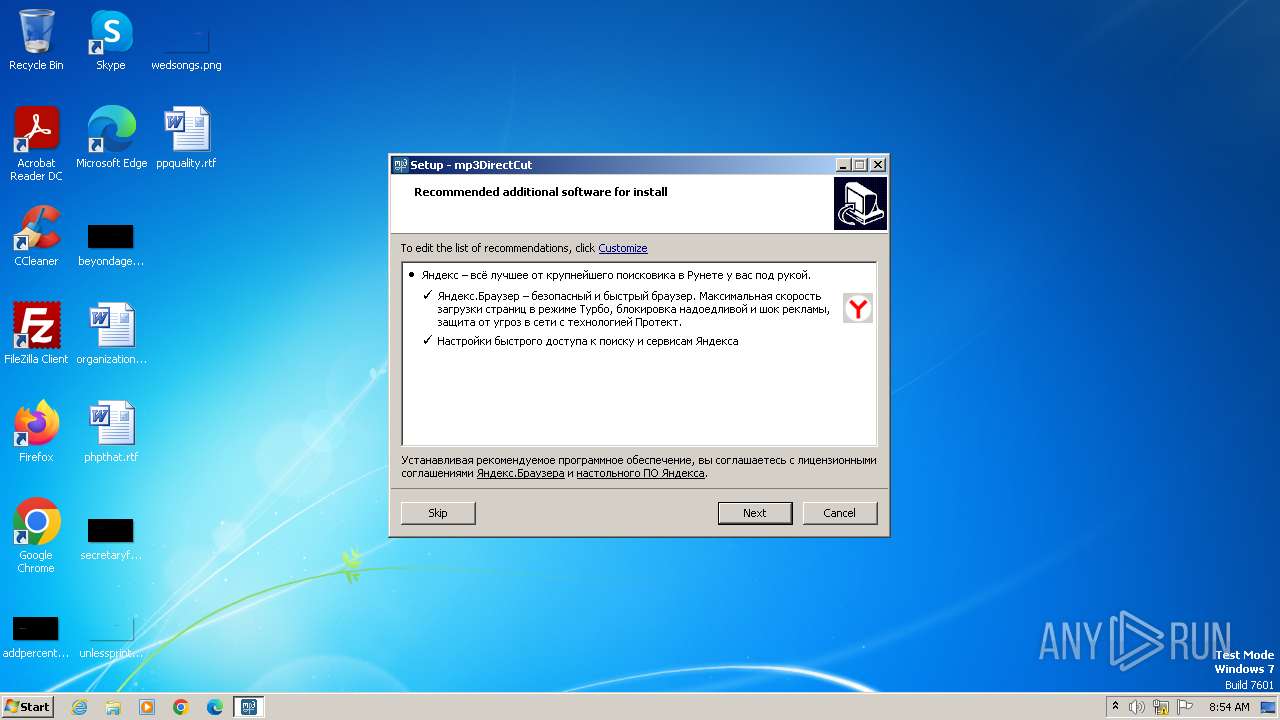
| Threats: | A loader is malicious software that infiltrates devices to deliver malicious payloads. This malware is capable of infecting victims’ computers, analyzing their system information, and installing other types of threats, such as trojans or stealers. Criminals usually deliver loaders through phishing emails and links by relying on social engineering to trick users into downloading and running their executables. Loaders employ advanced evasion and persistence tactics to avoid detection. |
| Analysis date: | November 27, 2023, 08:53:46 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | EF5B3B2F3E3F7F22095F4AF0D3216802 |
| SHA1: | A8EFBEFDDF67387299983FD7A42693543396317D |
| SHA256: | B433817776C7D0D413D6413FEEEF77F29D5E6963883A5A1052AAA7A57E6EAEA6 |
| SSDEEP: | 98304:Mw7OE9A3sgx3mNvN++ohOnW1VRVSfen79TjeS3A8Y9NFro1irm85QoyJT4daYZU3:xkTiyQ8x |
MALICIOUS
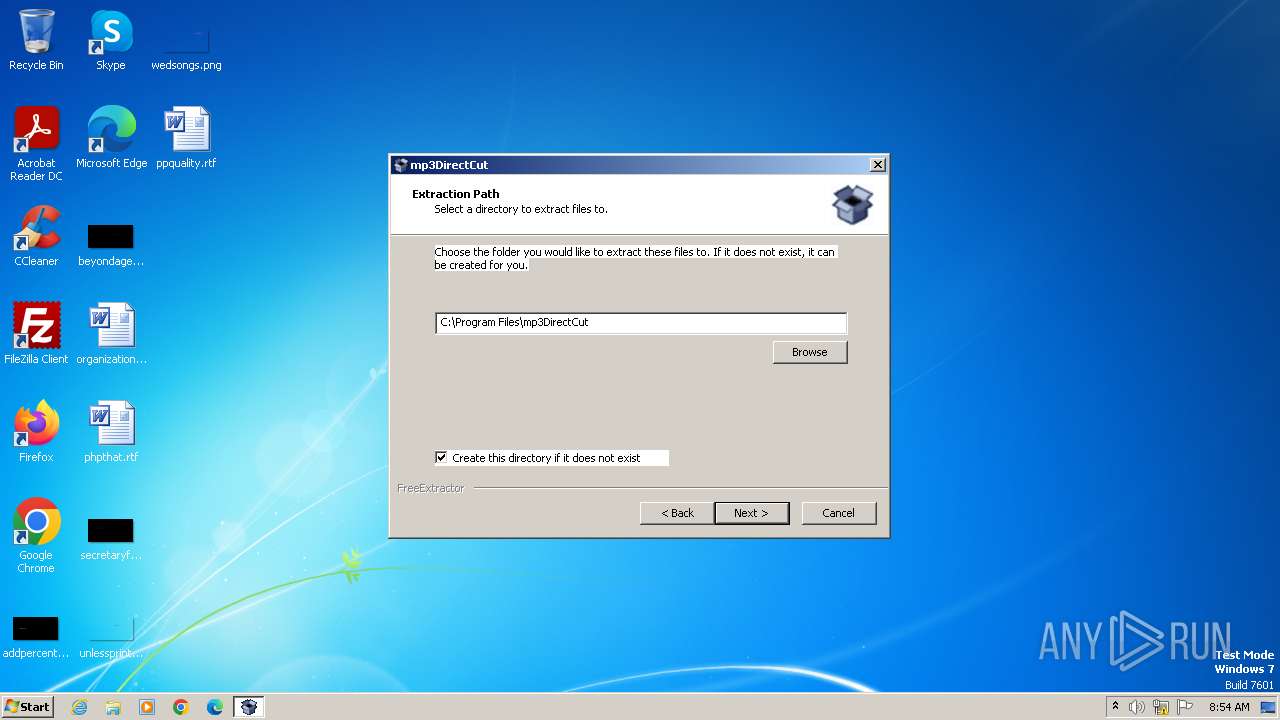
Drops the executable file immediately after the start
- mp3DC229.exe (PID: 1788)
- M9irY_u2TrO (PID: 1988)
- M9irY_u2TrO.tmp (PID: 3592)
- downloader.exe (PID: 3924)
- msiexec.exe (PID: 3428)
- msiexec.exe (PID: 3208)
- Yandex.exe (PID: 2100)
- Yandex.exe (PID: 3864)
Actions looks like stealing of personal data
- lite_installer.exe (PID: 3416)
- seederexe.exe (PID: 3308)
Steals credentials from Web Browsers
- seederexe.exe (PID: 3308)
SUSPICIOUS
Starts application with an unusual extension
- mp3directcut.exe (PID: 2476)
Reads the Windows owner or organization settings
- M9irY_u2TrO.tmp (PID: 3592)
- msiexec.exe (PID: 3208)
Reads settings of System Certificates
- M9irY_u2TrO.tmp (PID: 3592)
- downloader.exe (PID: 3924)
Reads the Internet Settings
- M9irY_u2TrO.tmp (PID: 3592)
- downloader.exe (PID: 3924)
- lite_installer.exe (PID: 3416)
Checks Windows Trust Settings
- downloader.exe (PID: 3924)
- msiexec.exe (PID: 3208)
Reads security settings of Internet Explorer
- downloader.exe (PID: 3924)
Process drops legitimate windows executable
- downloader.exe (PID: 3924)
Process requests binary or script from the Internet
- M9irY_u2TrO.tmp (PID: 3592)
- downloader.exe (PID: 3924)
- lite_installer.exe (PID: 3416)
Adds/modifies Windows certificates
- M9irY_u2TrO.tmp (PID: 3592)
Reads Mozilla Firefox installation path
- seederexe.exe (PID: 3308)
Application launched itself
- downloader.exe (PID: 3924)
Changes the Home page of Internet Explorer
- seederexe.exe (PID: 3308)
Changes the title of the Internet Explorer window
- seederexe.exe (PID: 3308)
INFO
Create files in a temporary directory
- mp3directcut.exe (PID: 2476)
- M9irY_u2TrO (PID: 1988)
- downloader.exe (PID: 3924)
- YandexPackSetup.exe (PID: 3564)
- msiexec.exe (PID: 3428)
- lite_installer.exe (PID: 3416)
- msiexec.exe (PID: 3208)
- seederexe.exe (PID: 3308)
- downloader.exe (PID: 3472)
- sender.exe (PID: 3420)
- mp3DC229.exe (PID: 1788)
- M9irY_u2TrO.tmp (PID: 3592)
Checks supported languages
- mp3directcut.exe (PID: 2476)
- M9irY_u2TrO (PID: 1988)
- M9irY_u2TrO.tmp (PID: 3592)
- wmpnscfg.exe (PID: 2432)
- downloader.exe (PID: 3924)
- YandexPackSetup.exe (PID: 3564)
- msiexec.exe (PID: 3428)
- msiexec.exe (PID: 3208)
- lite_installer.exe (PID: 3416)
- seederexe.exe (PID: 3308)
- downloader.exe (PID: 3472)
- Yandex.exe (PID: 2100)
- Yandex.exe (PID: 3864)
- sender.exe (PID: 3420)
- mp3DC229.exe (PID: 1788)
Reads the computer name
- mp3directcut.exe (PID: 2476)
- M9irY_u2TrO.tmp (PID: 3592)
- wmpnscfg.exe (PID: 2432)
- downloader.exe (PID: 3924)
- msiexec.exe (PID: 3428)
- YandexPackSetup.exe (PID: 3564)
- msiexec.exe (PID: 3208)
- lite_installer.exe (PID: 3416)
- seederexe.exe (PID: 3308)
- downloader.exe (PID: 3472)
- Yandex.exe (PID: 2100)
- Yandex.exe (PID: 3864)
- mp3DC229.exe (PID: 1788)
- sender.exe (PID: 3420)
Reads the machine GUID from the registry
- M9irY_u2TrO.tmp (PID: 3592)
- wmpnscfg.exe (PID: 2432)
- downloader.exe (PID: 3924)
- msiexec.exe (PID: 3208)
- msiexec.exe (PID: 3428)
- YandexPackSetup.exe (PID: 3564)
- lite_installer.exe (PID: 3416)
- seederexe.exe (PID: 3308)
- Yandex.exe (PID: 2100)
- Yandex.exe (PID: 3864)
- sender.exe (PID: 3420)
Checks proxy server information
- M9irY_u2TrO.tmp (PID: 3592)
- downloader.exe (PID: 3924)
- lite_installer.exe (PID: 3416)
Creates files or folders in the user directory
- downloader.exe (PID: 3924)
- msiexec.exe (PID: 3428)
- lite_installer.exe (PID: 3416)
- msiexec.exe (PID: 3208)
- seederexe.exe (PID: 3308)
- Yandex.exe (PID: 2100)
- Yandex.exe (PID: 3864)
Application launched itself
- msiexec.exe (PID: 3208)
Process checks computer location settings
- msiexec.exe (PID: 3428)
Reads Environment values
- msiexec.exe (PID: 3428)
Creates files in the program directory
- mp3DC229.exe (PID: 1788)
Manual execution by a user
- wmpnscfg.exe (PID: 2432)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:03:15 09:41:23+01:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit, No debug |
| PEType: | PE32 |
| LinkerVersion: | 2.33 |
| CodeSize: | 40448 |
| InitializedDataSize: | 18432 |
| UninitializedDataSize: | 304128 |
| EntryPoint: | 0x5de0 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.29.0.0 |
| ProductVersionNumber: | 2.29.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| FileDescription: | mp3DirectCut |
| FileVersion: | 2.29.0.0 |
| LegalCopyright: | - |
| ProductName: | mp3DirectCut |
Total processes
58
Monitored processes
16
Malicious processes
8
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 888 | "C:\Users\admin\AppData\Local\Temp\mp3directcut.exe" | C:\Users\admin\AppData\Local\Temp\mp3directcut.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: mp3DirectCut Exit code: 3221226540 Version: 2.29.0.0 Modules
| |||||||||||||||
| 1788 | "C:\Users\admin\AppData\Local\Temp\is-8VQCL.tmp\z5jfA7M_ep2UQyTC8xy_a\mp3DC229.exe" | C:\Users\admin\AppData\Local\Temp\is-8VQCL.tmp\z5jfA7M_ep2UQyTC8xy_a\mp3DC229.exe | — | M9irY_u2TrO.tmp | |||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Modules
| |||||||||||||||
| 1988 | "C:\Users\admin\AppData\Local\Temp\nsfEC32.tmp\M9irY_u2TrO" | C:\Users\admin\AppData\Local\Temp\nsfEC32.tmp\M9irY_u2TrO | — | mp3directcut.exe | |||||||||||
User: admin Company: Integrity Level: HIGH Description: mp3DirectCut Setup (r2311261200) Exit code: 0 Version: 2.29 Modules
| |||||||||||||||
| 2100 | C:\Users\admin\AppData\Local\Yandex\YaPin\Yandex.exe --silent --pin-taskbar=y --pin-desktop=n | C:\Users\admin\AppData\Local\Yandex\YaPin\Yandex.exe | — | seederexe.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: YandexPin Exit code: 1 Version: 3.7.9.0 Modules
| |||||||||||||||
| 2432 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2476 | "C:\Users\admin\AppData\Local\Temp\mp3directcut.exe" | C:\Users\admin\AppData\Local\Temp\mp3directcut.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: mp3DirectCut Exit code: 0 Version: 2.29.0.0 Modules
| |||||||||||||||
| 3208 | C:\Windows\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3308 | "C:\Users\admin\AppData\Local\Temp\5E11512A-280D-4035-A089-368DD9216D72\seederexe.exe" "--yqs=y" "--yhp=y" "--ilight=" "--oem=" "--nopin=n" "--pin_custom=n" "--pin_desktop=n" "--pin_taskbar=y" "--locale=us" "--browser=y" "--browser_default=" "--loglevel=trace" "--ess=" "--clids=C:\Users\admin\AppData\Local\Temp\clids-yasearch.xml" "--sender=C:\Users\admin\AppData\Local\Temp\4504E39A-DFCB-47F9-BC86-BD94F2598788\sender.exe" "--is_elevated=yes" "--ui_level=2" "--good_token=1" "--no_opera=n" | C:\Users\admin\AppData\Local\Temp\5E11512A-280D-4035-A089-368DD9216D72\seederexe.exe | msiexec.exe | ||||||||||||
User: admin Company: Yandex Integrity Level: MEDIUM Description: Browser Integration Module Exit code: 0 Version: 3.7.10.0 Modules
| |||||||||||||||
| 3416 | "C:\Users\admin\AppData\Local\Temp\337AB85D-4519-475F-AA40-421BF91FFFFA\lite_installer.exe" --use-user-default-locale --silent --remote-url=http://downloader.yandex.net/downloadable_soft/browser/pseudoportal-ru/Yandex.exe --cumtom-welcome-page=https://browser.yandex.ru/promo/welcome_com/5/ --YABROWSER | C:\Users\admin\AppData\Local\Temp\337AB85D-4519-475F-AA40-421BF91FFFFA\lite_installer.exe | msiexec.exe | ||||||||||||
User: admin Company: Yandex Integrity Level: MEDIUM Description: YandexBrowserDownloader Exit code: 0 Version: 1.0.1.88 Modules
| |||||||||||||||
| 3420 | C:\Users\admin\AppData\Local\Temp\4504E39A-DFCB-47F9-BC86-BD94F2598788\sender.exe --send "/status.xml?clid=2413737-15&uuid=10b71020-75D3-4974-9302-50488DB78dc6&vnt=Windows 7x32&file-no=8%0A10%0A11%0A13%0A15%0A17%0A18%0A20%0A21%0A22%0A24%0A25%0A38%0A40%0A42%0A45%0A50%0A57%0A61%0A89%0A103%0A111%0A123%0A124%0A125%0A129%0A" | C:\Users\admin\AppData\Local\Temp\4504E39A-DFCB-47F9-BC86-BD94F2598788\sender.exe | seederexe.exe | ||||||||||||
User: admin Company: Yandex Integrity Level: MEDIUM Description: Yandex Statistics Exit code: 0 Version: 0.0.2.14 Modules
| |||||||||||||||
Total events
21 035
Read events
20 483
Write events
532
Delete events
20
Modification events
| (PID) Process: | (3592) M9irY_u2TrO.tmp | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\17F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2432) wmpnscfg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Media Player NSS\3.0\Events\{620DA738-AC22-44B9-BB8E-90D02EB67F81}\{A33D39F0-9C43-43B3-8093-35DE099AA815} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (2432) wmpnscfg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Media Player NSS\3.0\Events\{620DA738-AC22-44B9-BB8E-90D02EB67F81} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (2432) wmpnscfg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\MediaPlayer\Health\{7AEAA492-9A8E-4D02-88F3-4B59133D533C} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (3592) M9irY_u2TrO.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3592) M9irY_u2TrO.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000059010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A8016B000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3592) M9irY_u2TrO.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3592) M9irY_u2TrO.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3592) M9irY_u2TrO.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3592) M9irY_u2TrO.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
27
Suspicious files
57
Text files
168
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2476 | mp3directcut.exe | C:\Users\admin\AppData\Local\Temp\nsfEC32.tmp\M9irY_u2TrO | — | |
MD5:— | SHA256:— | |||
| 3592 | M9irY_u2TrO.tmp | C:\Users\admin\AppData\Local\Temp\is-8VQCL.tmp\n_LSIs5L_rxC1o0hiKP\Checkboxes_125.png | image | |
MD5:BFC3DDB0FCB282FCCF7CC4EABF6A1D99 | SHA256:423C54D09144BA773E17E95F1DB22E85E47E3DB58256AF765D21934D65533513 | |||
| 3592 | M9irY_u2TrO.tmp | C:\Users\admin\AppData\Local\Temp\is-8VQCL.tmp\is-H94VL.ini | text | |
MD5:F91EBC94A05130703323D768E4091FED | SHA256:9F37377BCD7AA63617EF860FE7C32EEBDDE97E3F46F0B549C2F4ED3559F1880E | |||
| 3592 | M9irY_u2TrO.tmp | C:\Users\admin\AppData\Local\Temp\is-8VQCL.tmp\n_LSIs5L_rxC1o0hiKP\Accept_buttons_125.png | image | |
MD5:6F60AC8D87538CCFBF77B44DE07D695C | SHA256:91D0C34184342AE204BFACA0662FC02F2CC8638F94D67B28A0BA363DA1DBCC95 | |||
| 3592 | M9irY_u2TrO.tmp | C:\Users\admin\AppData\Local\Temp\is-8VQCL.tmp\ftAKdMYcY9PPW7o3Wr2AZ.dll | executable | |
MD5:BB744D784D9548A56D859FA4C4FD1F5A | SHA256:524C210F1DBD5D73040EFDBAD31F6F9E683F6E146EB5F0949C9B3EE2C2CAB2E0 | |||
| 3592 | M9irY_u2TrO.tmp | C:\Users\admin\AppData\Local\Temp\is-8VQCL.tmp\botva2.dll | executable | |
MD5:EF899FA243C07B7B82B3A45F6EC36771 | SHA256:DA7D0368712EE419952EB2640A65A7F24E39FB7872442ED4D2EE847EC4CFDE77 | |||
| 3592 | M9irY_u2TrO.tmp | C:\Users\admin\AppData\Local\Temp\is-8VQCL.tmp\{app}\rDxKLnJ\n_LSIs5L_rxC1o0hiKP | binary | |
MD5:C1515AC6AB5D3AFE9A0625183AAB153F | SHA256:5557DA7731FC0405FBC5DE40CFFD5D2A1460B2519DD2E50915E7794D04BA409B | |||
| 3592 | M9irY_u2TrO.tmp | C:\Users\admin\AppData\Local\Temp\is-8VQCL.tmp\n_LSIs5L_rxC1o0hiKP\Accept_buttons_150.png | image | |
MD5:216480982115385689910C22155587BC | SHA256:E207A18366D9768595EEA3EDE3ACF9509071A964788037F3AA6BB6831A3BA51E | |||
| 3592 | M9irY_u2TrO.tmp | C:\Users\admin\AppData\Local\Temp\is-8VQCL.tmp\n_LSIs5L_rxC1o0hiKP\Accept_buttons_200.png | image | |
MD5:66ED96978B9869BEA3AE689B265FC1FE | SHA256:65A8D030FC4508ACE386703F90455B98DCB042F9C8BB5A083C95436A2AC75E61 | |||
| 3592 | M9irY_u2TrO.tmp | C:\Users\admin\AppData\Local\Temp\is-8VQCL.tmp\n_LSIs5L_rxC1o0hiKP\Accept_buttons_175.png | image | |
MD5:FCE8F803891426B137713E4595B05B42 | SHA256:0C48C8AF091A7602366631E35F1DEC2F31E17D6726707F1D51476EC0DB0CB9B5 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
18
TCP/UDP connections
23
DNS requests
15
Threats
13
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3592 | M9irY_u2TrO.tmp | HEAD | 302 | 5.45.205.245:80 | http://download.yandex.ru/yandex-pack/downloader/downloader.exe | unknown | — | — | unknown |
3592 | M9irY_u2TrO.tmp | HEAD | 200 | 185.70.202.14:80 | http://ext-cachev2-itt02.cdn.yandex.net/download.yandex.ru/yandex-pack/downloader/downloader.exe?lid=1529 | unknown | — | — | unknown |
3592 | M9irY_u2TrO.tmp | GET | 302 | 5.45.205.245:80 | http://download.yandex.ru/yandex-pack/downloader/downloader.exe | unknown | — | — | unknown |
3924 | downloader.exe | GET | 302 | 5.45.205.245:80 | http://download.yandex.ru/yandex-pack/downloader/info.rss | unknown | — | — | unknown |
3592 | M9irY_u2TrO.tmp | GET | 200 | 149.5.241.43:80 | http://ext-cachev2-cogent03.cdn.yandex.net/download.yandex.ru/yandex-pack/downloader/downloader.exe?lid=1503 | unknown | executable | 203 Kb | unknown |
3924 | downloader.exe | GET | 302 | 5.45.205.243:80 | http://downloader.yandex.net/yandex-pack/26983/YandexPackSetup.exe | unknown | — | — | unknown |
3924 | downloader.exe | GET | 200 | 149.5.241.43:80 | http://ext-cachev2-cogent03.cdn.yandex.net/download.yandex.ru/yandex-pack/downloader/info.rss?lid=1503 | unknown | xml | 267 b | unknown |
3924 | downloader.exe | GET | 200 | 185.70.202.14:80 | http://ext-cachev2-itt02.cdn.yandex.net/downloader.yandex.net/yandex-pack/26983/YandexPackSetup.exe?lid=1529 | unknown | executable | 10.1 Mb | unknown |
3924 | downloader.exe | GET | 200 | 104.18.21.226:80 | http://secure.globalsign.com/cacert/codesigningrootr45.crt | unknown | binary | 1.37 Kb | unknown |
3924 | downloader.exe | GET | 200 | 23.53.40.42:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?74b97ee8ce044a1f | unknown | compressed | 61.6 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3592 | M9irY_u2TrO.tmp | 188.114.97.3:443 | conf.datarcv.ru | CLOUDFLARENET | NL | unknown |
3592 | M9irY_u2TrO.tmp | 188.114.96.3:443 | conf.datarcv.ru | CLOUDFLARENET | NL | unknown |
3592 | M9irY_u2TrO.tmp | 216.58.206.40:443 | ssl.google-analytics.com | GOOGLE | US | unknown |
3592 | M9irY_u2TrO.tmp | 5.45.205.245:80 | download.yandex.ru | YANDEX LLC | RU | whitelisted |
3592 | M9irY_u2TrO.tmp | 185.70.202.14:80 | ext-cachev2-itt02.cdn.yandex.net | TELECOM ITALIA SPARKLE S.p.A. | IT | unknown |
3592 | M9irY_u2TrO.tmp | 149.5.241.43:80 | ext-cachev2-cogent03.cdn.yandex.net | COGENT-174 | FR | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
conf.datarcv.ru |
| unknown |
stat.datarcv.ru |
| unknown |
ssl.google-analytics.com |
| whitelisted |
download.yandex.ru |
| whitelisted |
ext-cachev2-itt02.cdn.yandex.net |
| whitelisted |
ext-cachev2-cogent03.cdn.yandex.net |
| whitelisted |
downloader.yandex.net |
| whitelisted |
secure.globalsign.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
clck.yandex.ru |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3592 | M9irY_u2TrO.tmp | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3924 | downloader.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3472 | downloader.exe | Attempted Information Leak | ET POLICY curl User-Agent Outbound |
3416 | lite_installer.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3416 | lite_installer.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
3592 | M9irY_u2TrO.tmp | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
7 ETPRO signatures available at the full report
Process | Message |
|---|---|
YandexPackSetup.exe | IsMSISrvFree() In |
YandexPackSetup.exe | IsMSISrvFree() : OpenMutex() err ret = 2
|
YandexPackSetup.exe | IsAlreadyRun() In
|
YandexPackSetup.exe | IsAlreadyRun() Out : ret (BOOL) = 0
|
YandexPackSetup.exe | IsMSISrvFree() Out ret = 1
|
YandexPackSetup.exe | GetSidFromEnumSess(): i = 0 : szUserName = Administrator, szDomain = USER-PC, dwSessionId = 0
|
YandexPackSetup.exe | GetSidFromEnumSess(): LsaEnumerateLogonSessions() lpszSid = S-1-5-21-1302019708-1500728564-335382590-1000
|
YandexPackSetup.exe | GetSidFromEnumSess(): ProfileImagePath(1) = C:\Users\admin
|
YandexPackSetup.exe | GetLoggedCreds_WTSSessionInfo(): szUserName = admin, szDomain = USER-PC, dwSessionId = 1
|
YandexPackSetup.exe | GetSidFromEnumSess(): LsaEnumerateLogonSessions() lpszSid = S-1-5-21-1302019708-1500728564-335382590-1000
|