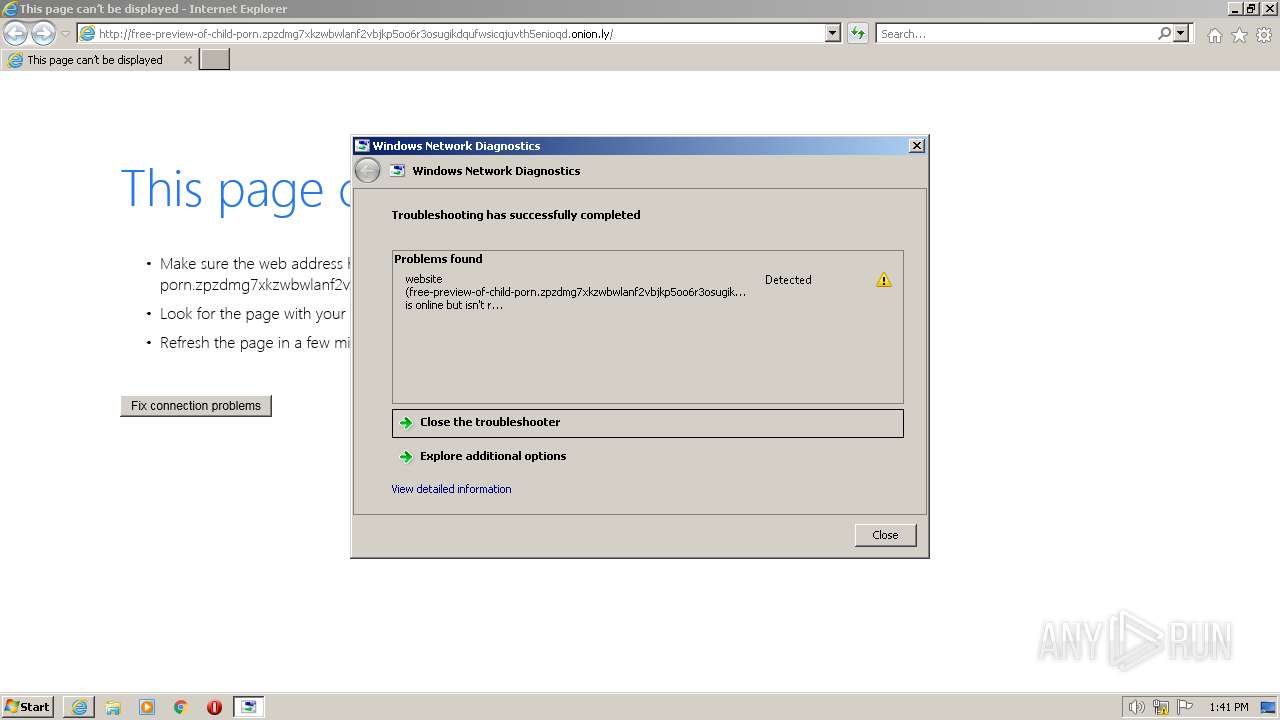
| URL: | http://free-preview-of-child-porn.zpzdmg7xkzwbwlanf2vbjkp5oo6r3osugikdqufwsicqjuvth5enioqd.onion.ly/ |
| Full analysis: | https://app.any.run/tasks/c142d7a3-afac-4a82-9f28-8873a38e24bd |
| Verdict: | Malicious activity |
| Analysis date: | June 28, 2023, 12:39:56 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 61639CFD21061714B9CEBDA3F492B234 |
| SHA1: | 1C02B8F6B58D5F9717BD4B9EBDF601FB3A414A5E |
| SHA256: | B4214B29042DD3189468F372C7E0651F00BD664E842CAE55FF8971DED2A1C7DB |
| SSDEEP: | 3:N1KYQt3I+VKbLf1BI7OsLSf4XmNSvQdCWpMe5:CYipVxDGf4XmAvQdCWj |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads the Internet Settings
- sdiagnhost.exe (PID: 3528)
- sdiagnhost.exe (PID: 2128)
Process uses IPCONFIG to discover network configuration
- sdiagnhost.exe (PID: 3528)
Uses ROUTE.EXE to obtain the routing table information
- sdiagnhost.exe (PID: 3528)
Executable content was dropped or overwritten
- msdt.exe (PID: 2608)
Reads settings of System Certificates
- msdt.exe (PID: 2608)
INFO
Create files in a temporary directory
- msdt.exe (PID: 2608)
- sdiagnhost.exe (PID: 3528)
- makecab.exe (PID: 1776)
The process checks LSA protection
- msdt.exe (PID: 2608)
- ipconfig.exe (PID: 1584)
- sdiagnhost.exe (PID: 2128)
- sdiagnhost.exe (PID: 3528)
- wmpnscfg.exe (PID: 3580)
Application launched itself
- iexplore.exe (PID: 3096)
Reads security settings of Internet Explorer
- sdiagnhost.exe (PID: 3528)
- msdt.exe (PID: 2608)
- sdiagnhost.exe (PID: 2128)
Dropped object may contain TOR URL's
- msdt.exe (PID: 2608)
- sdiagnhost.exe (PID: 3528)
Creates files or folders in the user directory
- msdt.exe (PID: 2608)
Manual execution by a user
- wmpnscfg.exe (PID: 3580)
Reads the machine GUID from the registry
- wmpnscfg.exe (PID: 3580)
Checks supported languages
- wmpnscfg.exe (PID: 3580)
Reads the computer name
- wmpnscfg.exe (PID: 3580)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
47
Monitored processes
9
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 868 | "C:\Windows\system32\ROUTE.EXE" print | C:\Windows\System32\ROUTE.EXE | — | sdiagnhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Route Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1584 | "C:\Windows\system32\ipconfig.exe" /all | C:\Windows\System32\ipconfig.exe | — | sdiagnhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: IP Configuration Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1776 | "C:\Windows\system32\makecab.exe" /f NetworkConfiguration.ddf | C:\Windows\System32\makecab.exe | — | sdiagnhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Cabinet Maker Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2128 | C:\Windows\System32\sdiagnhost.exe -Embedding | C:\Windows\System32\sdiagnhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Scripted Diagnostics Native Host Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2608 | -modal 590240 -skip TRUE -path C:\Windows\diagnostics\system\networking -af C:\Users\admin\AppData\Local\Temp\NDFF268.tmp -ep NetworkDiagnosticsWeb | C:\Windows\System32\msdt.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Diagnostics Troubleshooting Wizard Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3096 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://free-preview-of-child-porn.zpzdmg7xkzwbwlanf2vbjkp5oo6r3osugikdqufwsicqjuvth5enioqd.onion.ly/" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3528 | C:\Windows\System32\sdiagnhost.exe -Embedding | C:\Windows\System32\sdiagnhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Scripted Diagnostics Native Host Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3552 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3096 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3580 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
11 347
Read events
11 214
Write events
130
Delete events
3
Modification events
| (PID) Process: | (3096) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (3096) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (3096) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (3096) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3096) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3096) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3096) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3096) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3096) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3096) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
4
Suspicious files
26
Text files
43
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3096 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:F0C6481412BE36B109567BA1397B0C8C | SHA256:36A78A7603F8D39F221CCD5B2B12D3D6B9B67357E5B04E96EE0213F89198E435 | |||
| 3096 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\urlblockindex[2].bin | binary | |
MD5:FA518E3DFAE8CA3A0E495460FD60C791 | SHA256:775853600060162C4B4E5F883F9FD5A278E61C471B3EE1826396B6D129499AA7 | |||
| 3096 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | binary | |
MD5:DA2215C4410102096B859C34641C1C55 | SHA256:59A9869F27AF892CBEE4A1DC648DD61C43B1375940194844538931B0E436784F | |||
| 3096 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | binary | |
MD5:4684586CFA459FA1ECF9C04686524BE5 | SHA256:A0CAB0DFF001FE54929EE7243EFB92CC260429D37A098BC8B784DB008EB60F0A | |||
| 3096 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\VersionManager\versionlist.xml | xml | |
MD5:CBD0581678FA40F0EDCBC7C59E0CAD10 | SHA256:159BD4343F344A08F6AF3B716B6FA679859C1BD1D7030D26FF5EF0255B86E1D9 | |||
| 3096 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | binary | |
MD5:4BFB6D711F959FF0C772F0E18976C5A1 | SHA256:3BC0DB722559C8989C951ABB04DF4CAD9668D3DED1021EAADC657788097590EB | |||
| 3096 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\VersionManager\ver33BA.tmp | xml | |
MD5:CBD0581678FA40F0EDCBC7C59E0CAD10 | SHA256:159BD4343F344A08F6AF3B716B6FA679859C1BD1D7030D26FF5EF0255B86E1D9 | |||
| 3096 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | binary | |
MD5:3758078AD083EC1D09E9055A1EAB0467 | SHA256:FDFF9C730FC26B57724E4D839D2F00A8C020F729D0FE23D094F8594D3FB2FD57 | |||
| 2608 | msdt.exe | C:\Users\admin\AppData\Local\Temp\SDIAG_3eeea640-8b08-4267-9ee5-d1ba4531d868\DiagPackage.diagpkg | xml | |
MD5:C9FB87FA3460FAE6D5D599236CFD77E2 | SHA256:CDE728C08A4E50A02FCFF35C90EE2B3B33AB24C8B858F180B6A67BFA94DEF35F | |||
| 3096 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\NDFF268.tmp | binary | |
MD5:5565F74870E509C76721C011F663B709 | SHA256:9EB02645D568DDCA3124612A9B295DA66CB8592103CCA7D08B7FBC72C3E48442 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
27
DNS requests
12
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3096 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
3096 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?0988c3d78d136b55 | US | compressed | 4.70 Kb | whitelisted |
3096 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | binary | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3552 | iexplore.exe | 198.251.88.180:80 | — | PONYNET | LU | suspicious |
1076 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2748 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3096 | iexplore.exe | 184.86.251.9:443 | www.bing.com | Akamai International B.V. | DE | suspicious |
3096 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
3096 | iexplore.exe | 184.86.251.30:443 | www.bing.com | Akamai International B.V. | DE | suspicious |
3096 | iexplore.exe | 184.86.251.17:443 | www.bing.com | Akamai International B.V. | DE | suspicious |
3096 | iexplore.exe | 204.79.197.200:443 | ieonline.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl3.digicert.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
ieonline.microsoft.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
dns.msftncsi.com |
| shared |