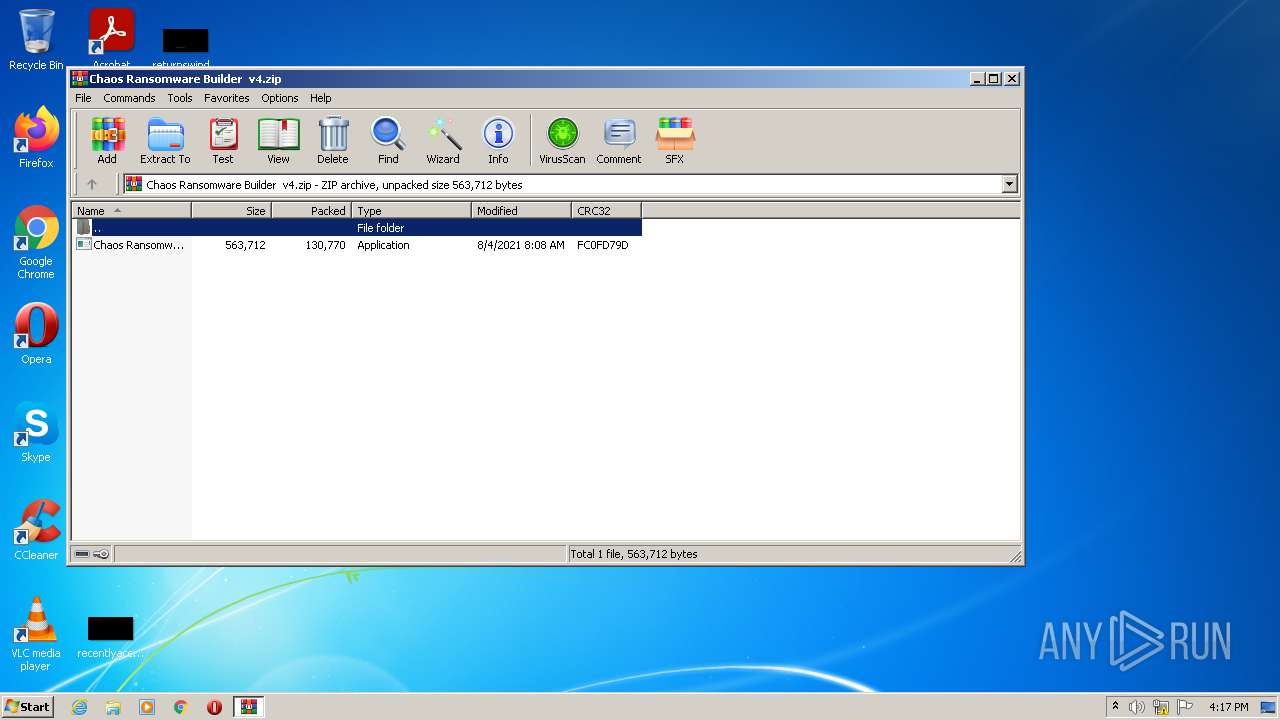
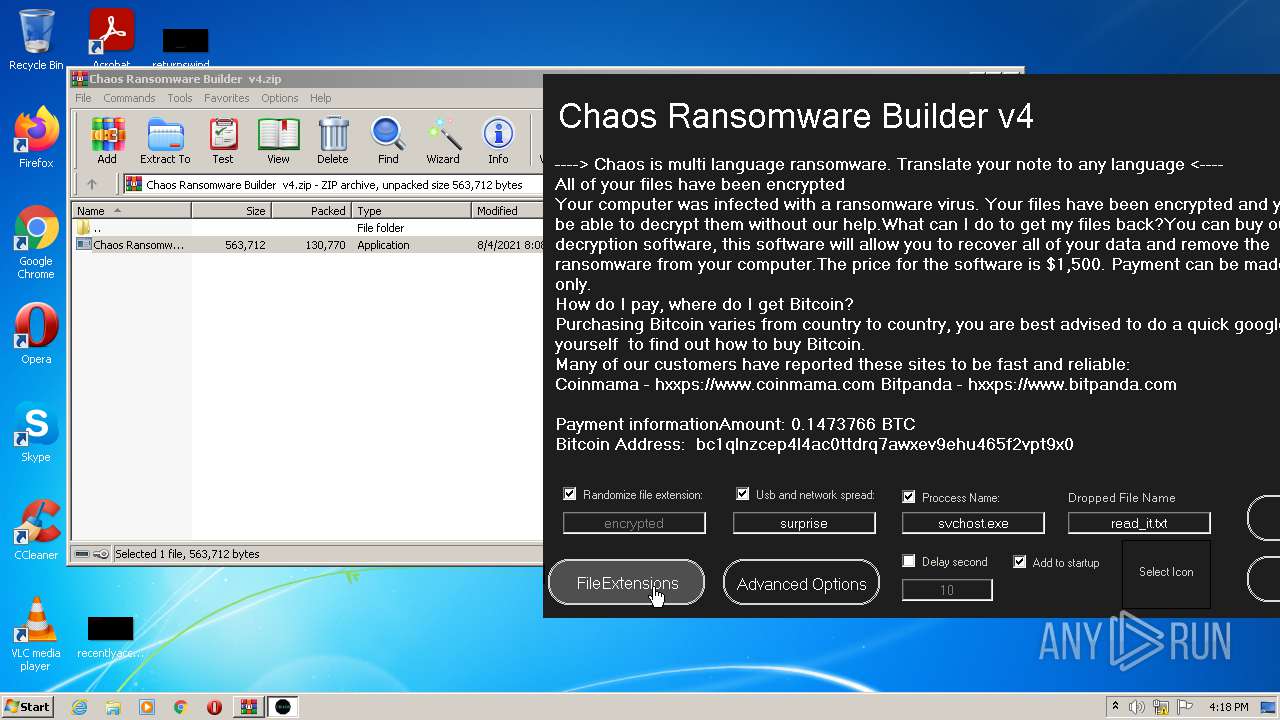
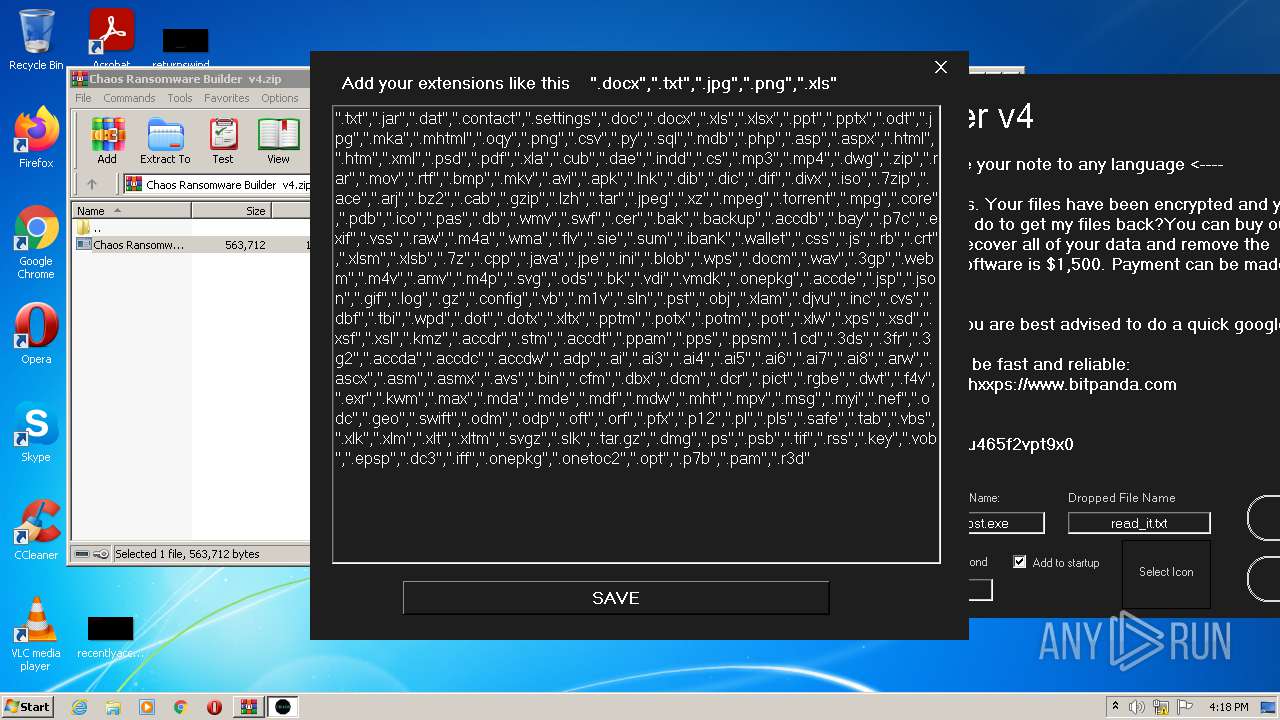
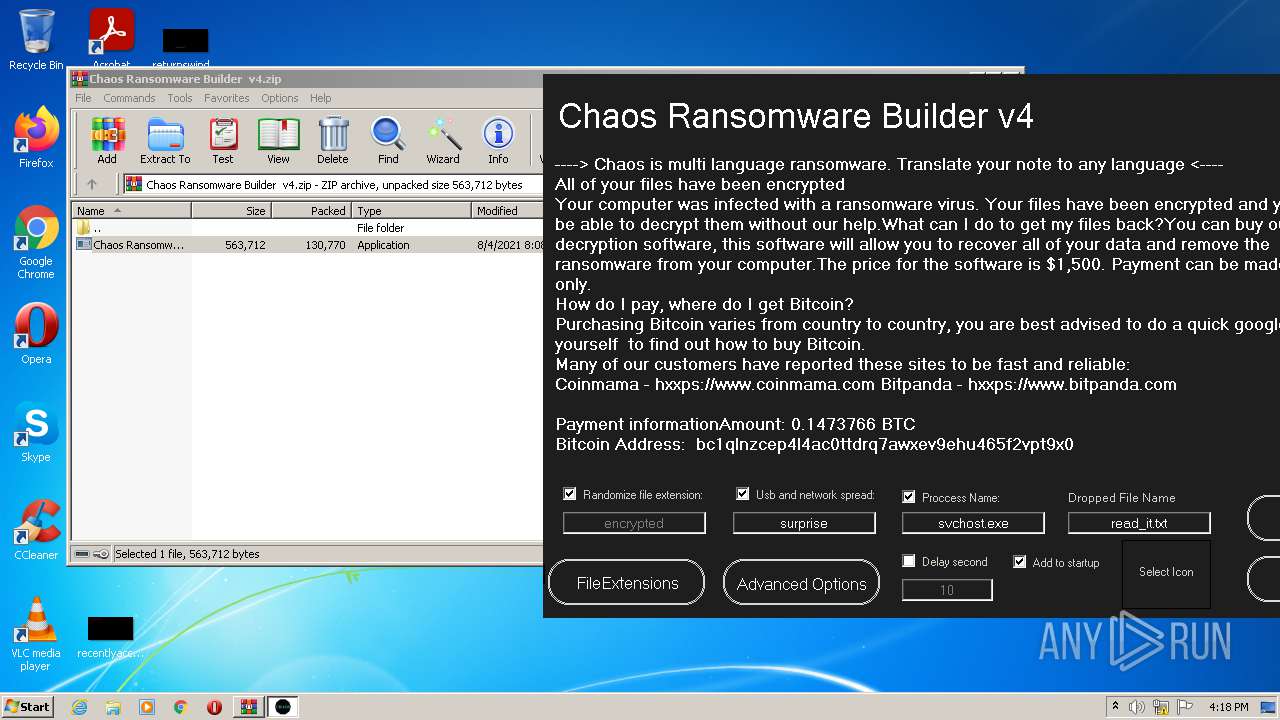
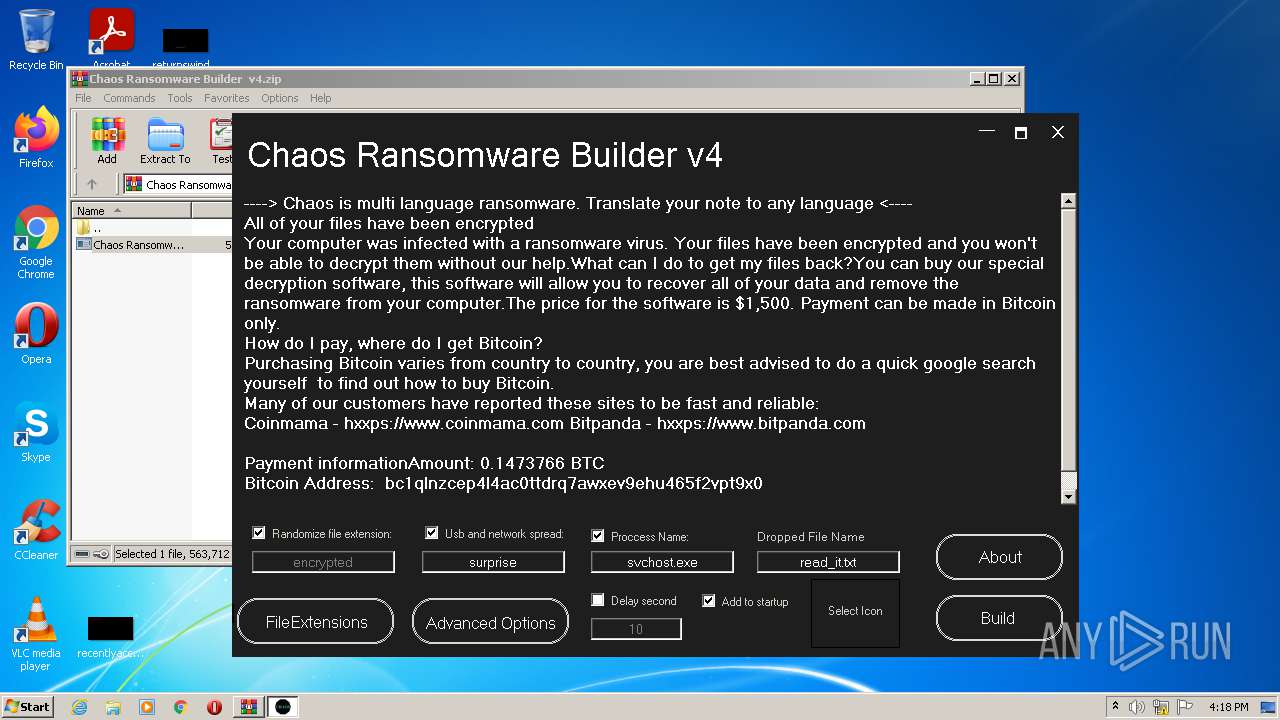
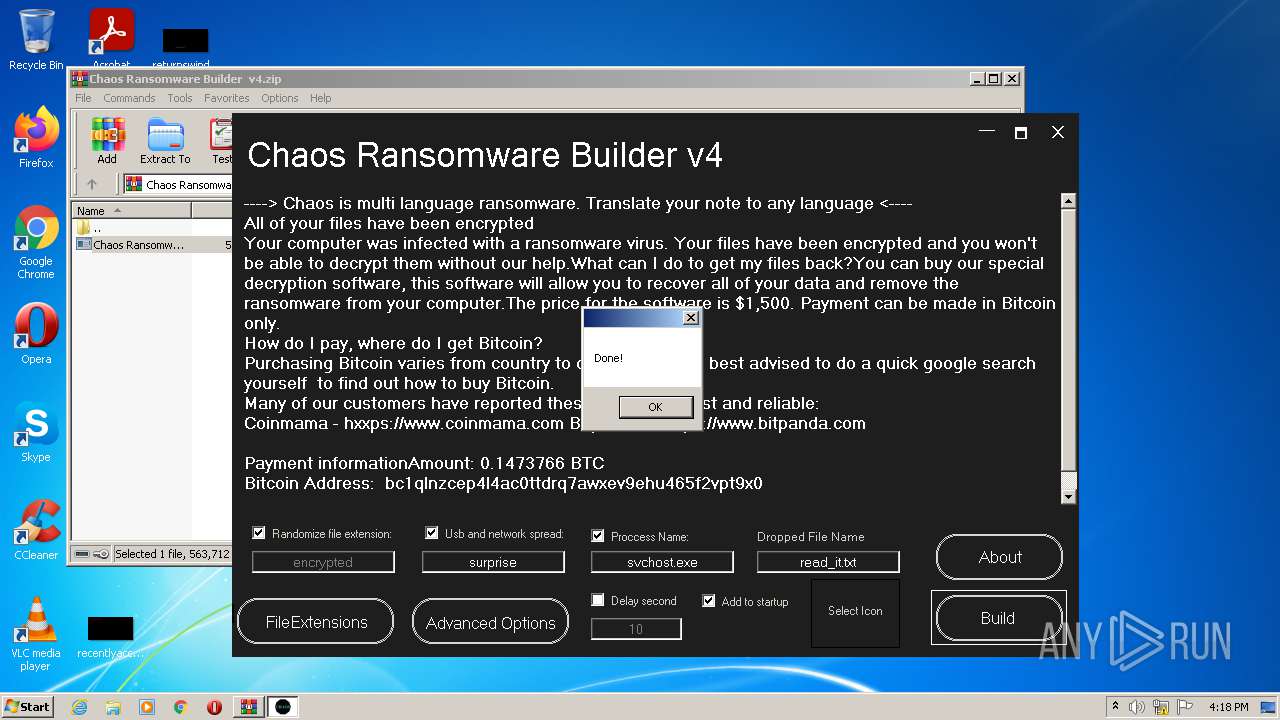
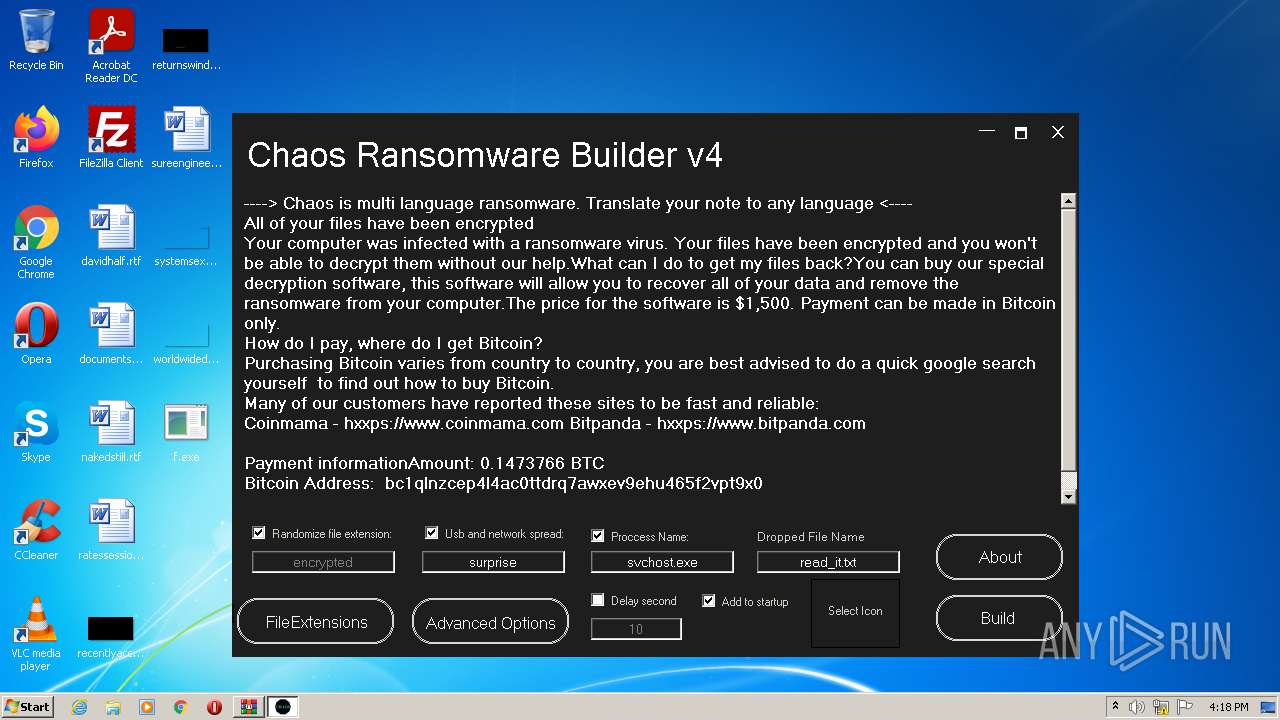
| File name: | Chaos Ransomware Builder v4.zip |
| Full analysis: | https://app.any.run/tasks/3be431c3-e9b3-41c4-8c0f-c9c5a5e4a4fa |
| Verdict: | Malicious activity |
| Analysis date: | December 19, 2021, 16:17:43 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 41FDC2F2BF1BE4361E3C9EE6A650DAC0 |
| SHA1: | 8D65A729FE806F6564EEEE079CE96D30824BCC25 |
| SHA256: | B40C52F62DB0108C1132FE90904A316FDC52F9A7A95BBEFD1146778B02DDAF7D |
| SSDEEP: | 3072:5DqTMmLNHAFYHXfoS/3MekTGXbycnUfZlvMs29L5Q:WMeOYHXfBkGXbycUfZlvMs2M |
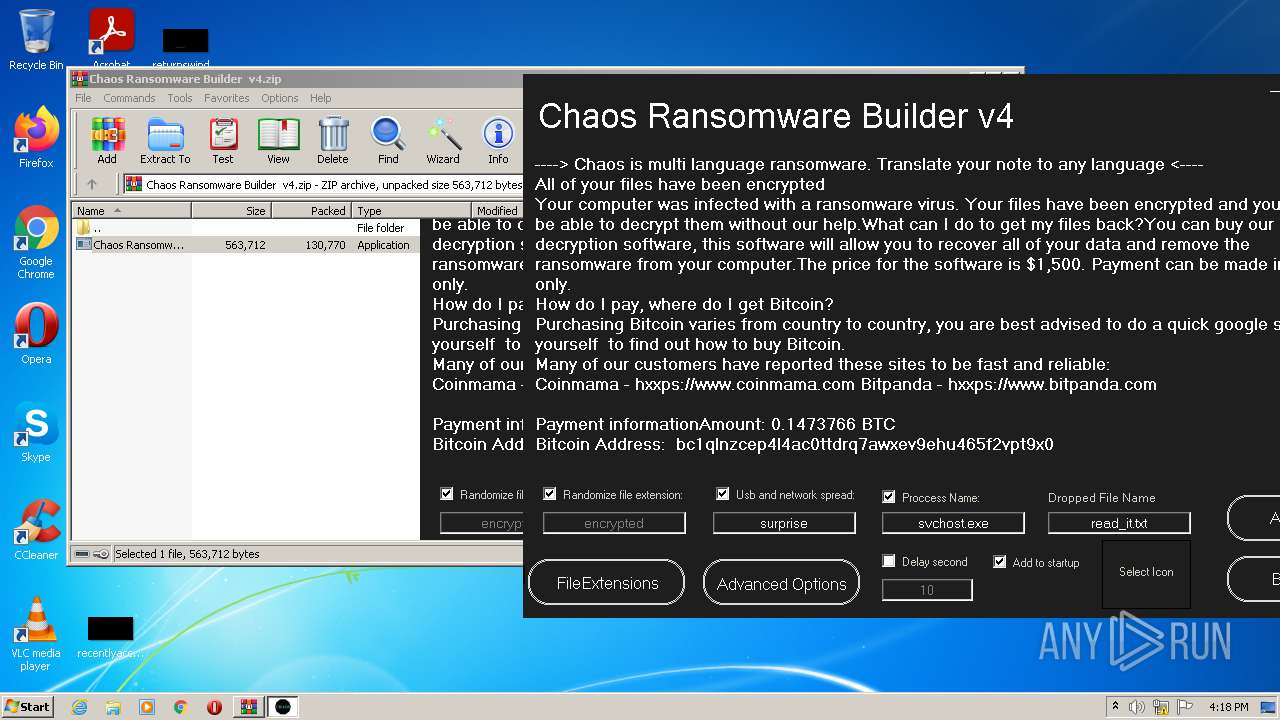
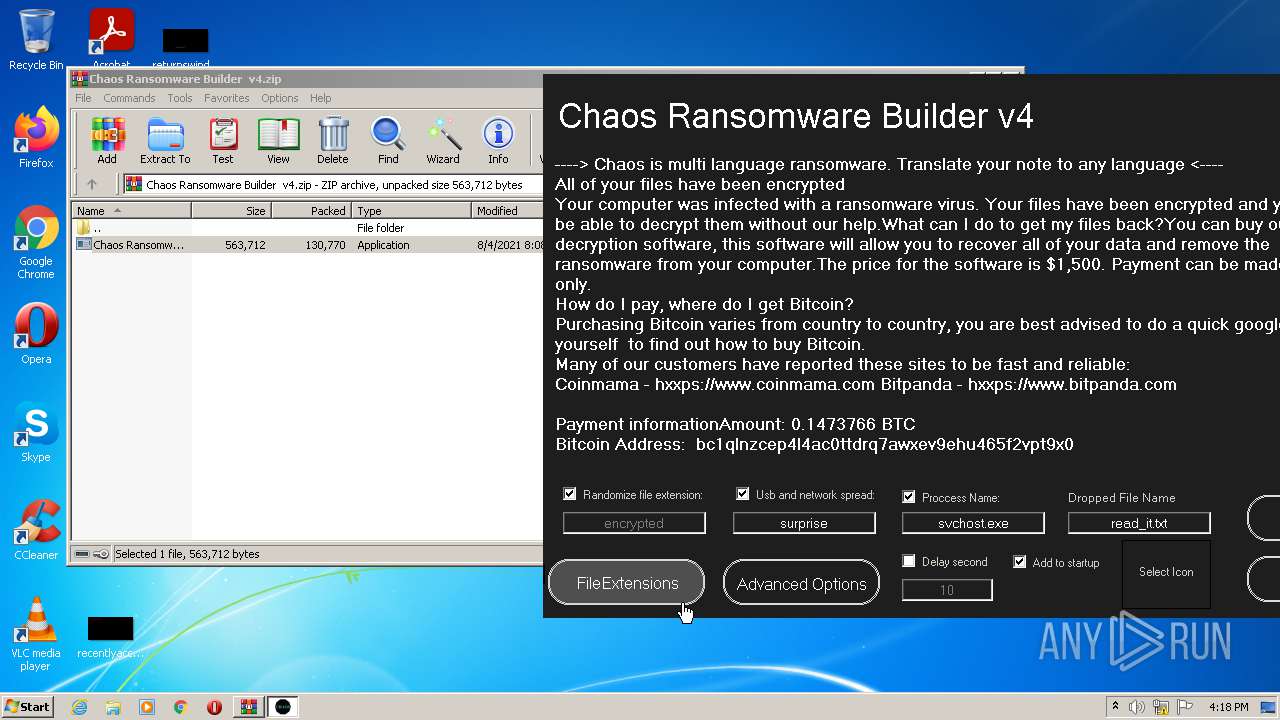
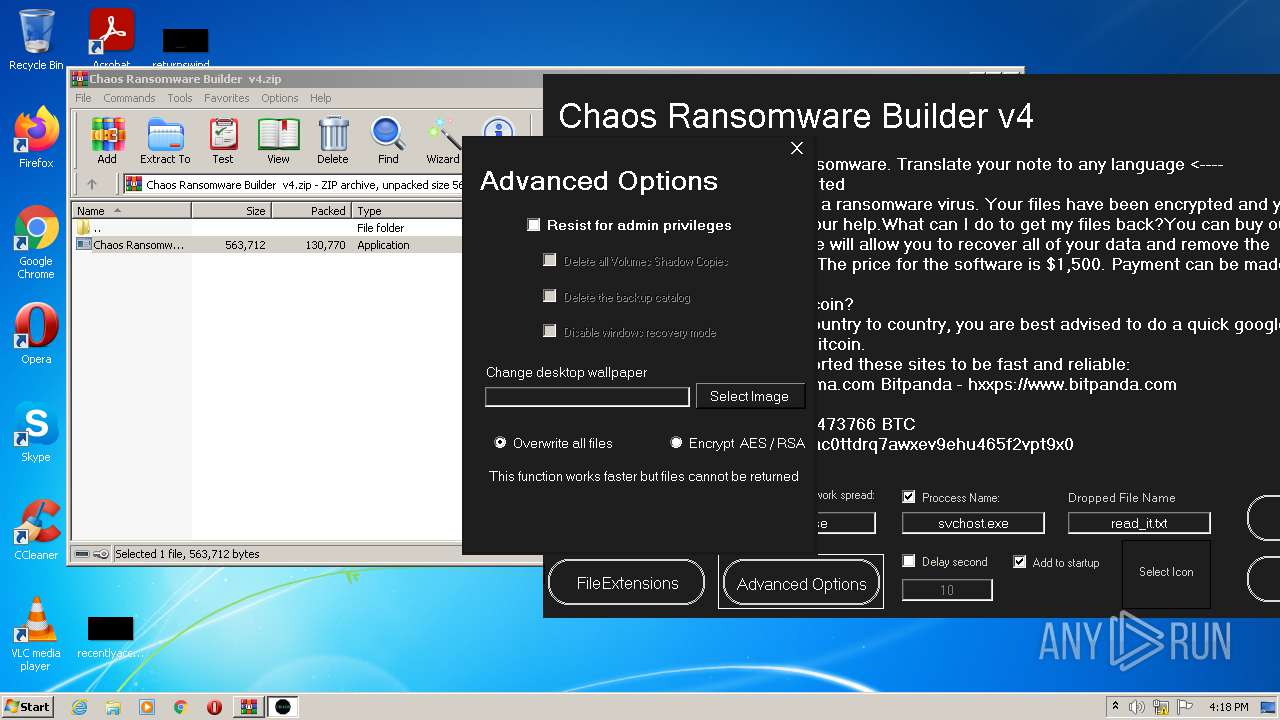
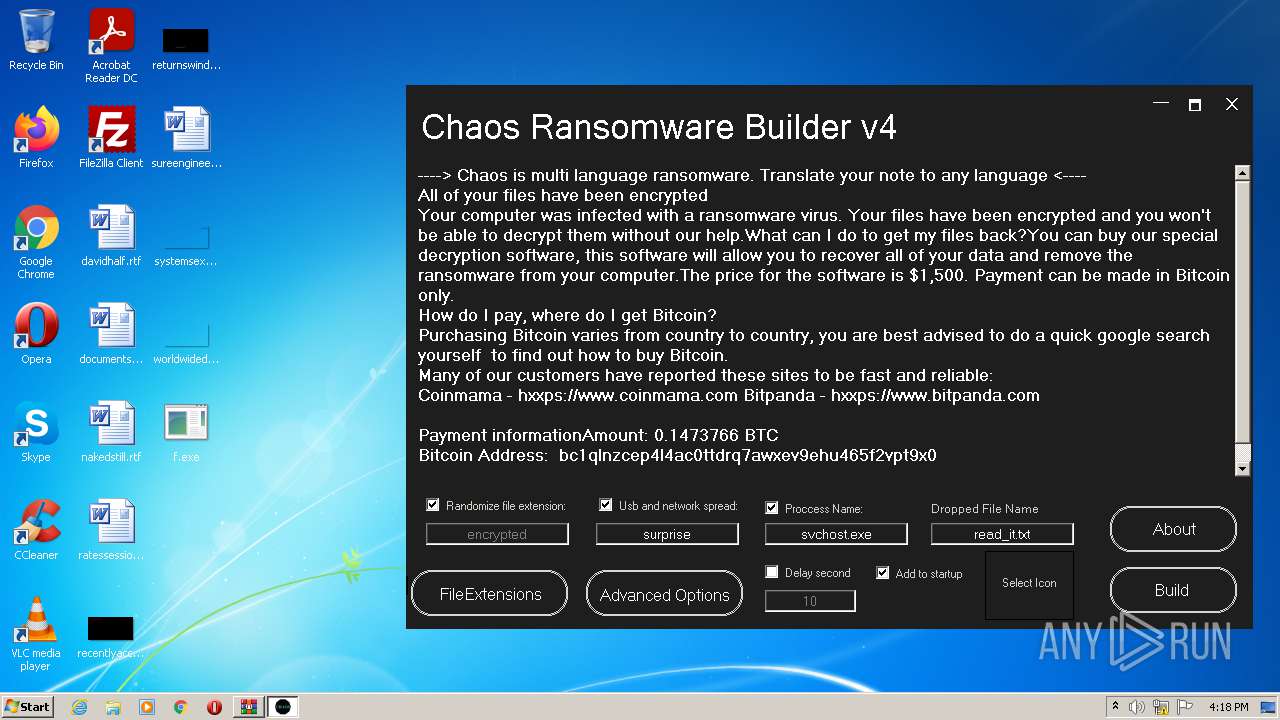
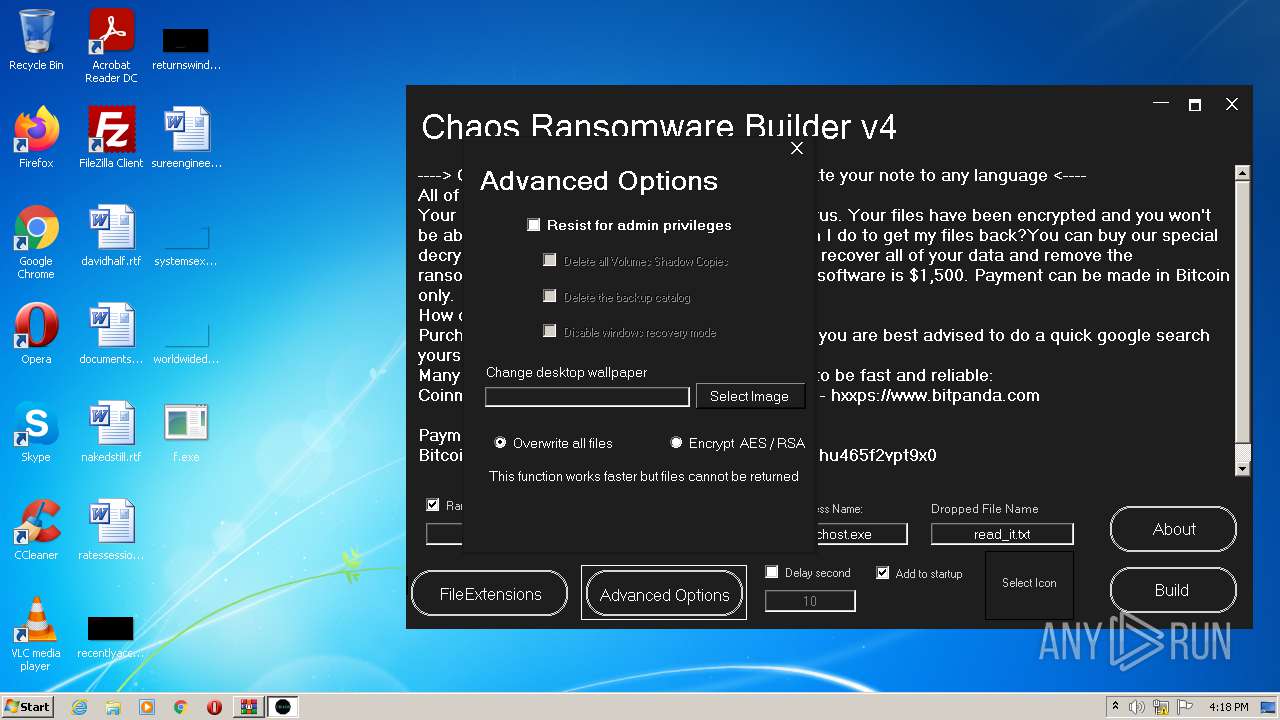
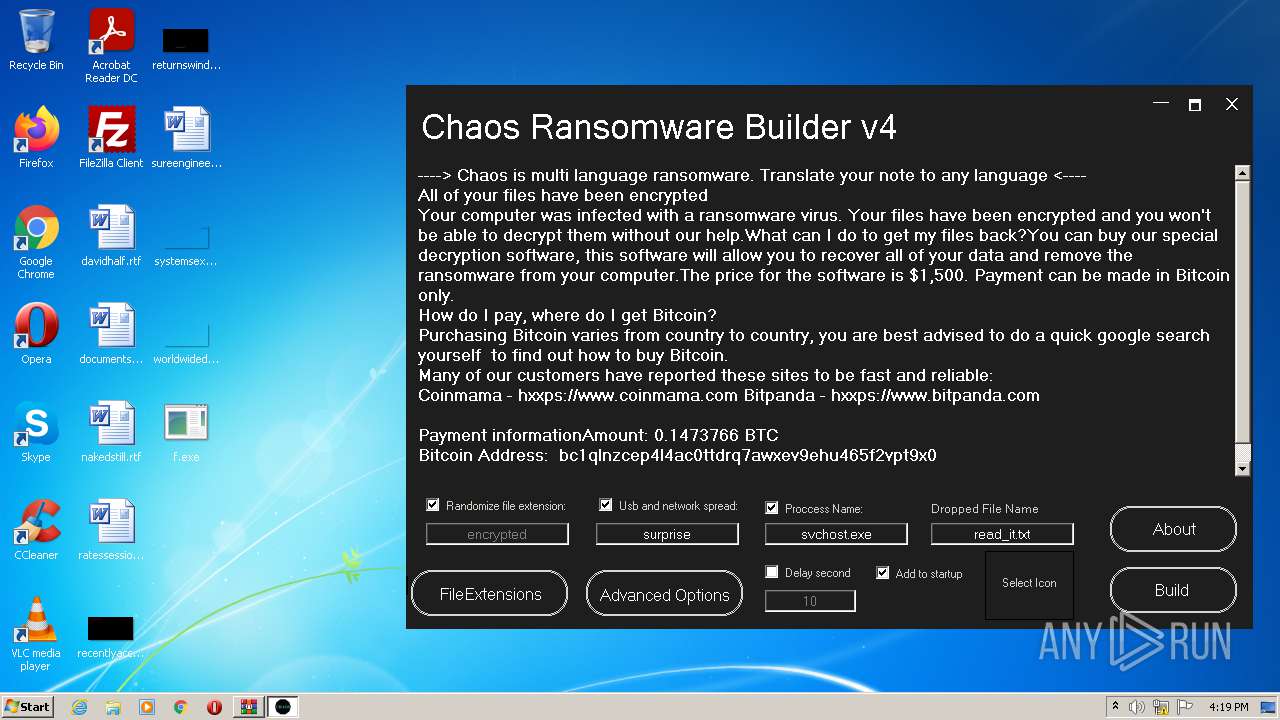
MALICIOUS
Application was dropped or rewritten from another process
- Chaos Ransomware Builder v4.exe (PID: 2400)
- Chaos Ransomware Builder v4.exe (PID: 3232)
- f.exe (PID: 2224)
- svchost.exe (PID: 576)
Starts Visual C# compiler
- Chaos Ransomware Builder v4.exe (PID: 3232)
Drops executable file immediately after starts
- csc.exe (PID: 2168)
- f.exe (PID: 2224)
Writes to a start menu file
- svchost.exe (PID: 576)
SUSPICIOUS
Checks supported languages
- WinRAR.exe (PID: 2476)
- Chaos Ransomware Builder v4.exe (PID: 3232)
- csc.exe (PID: 2168)
- cvtres.exe (PID: 520)
- f.exe (PID: 2224)
- svchost.exe (PID: 576)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2476)
- csc.exe (PID: 2168)
- f.exe (PID: 2224)
Reads the computer name
- WinRAR.exe (PID: 2476)
- Chaos Ransomware Builder v4.exe (PID: 3232)
- f.exe (PID: 2224)
- svchost.exe (PID: 576)
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 2476)
Drops a file with a compile date too recent
- csc.exe (PID: 2168)
- f.exe (PID: 2224)
Creates executable files which already exist in Windows
- f.exe (PID: 2224)
Creates files in the user directory
- f.exe (PID: 2224)
- svchost.exe (PID: 576)
Starts itself from another location
- f.exe (PID: 2224)
Executed via COM
- DllHost.exe (PID: 3872)
INFO
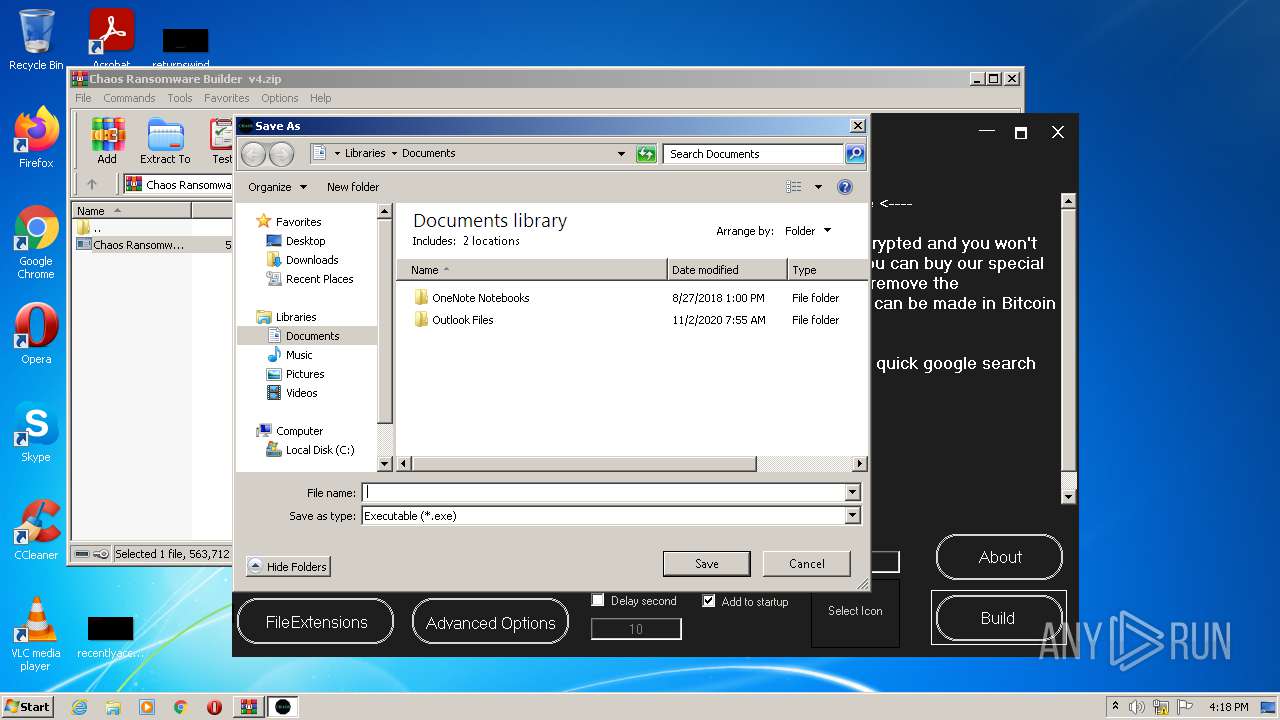
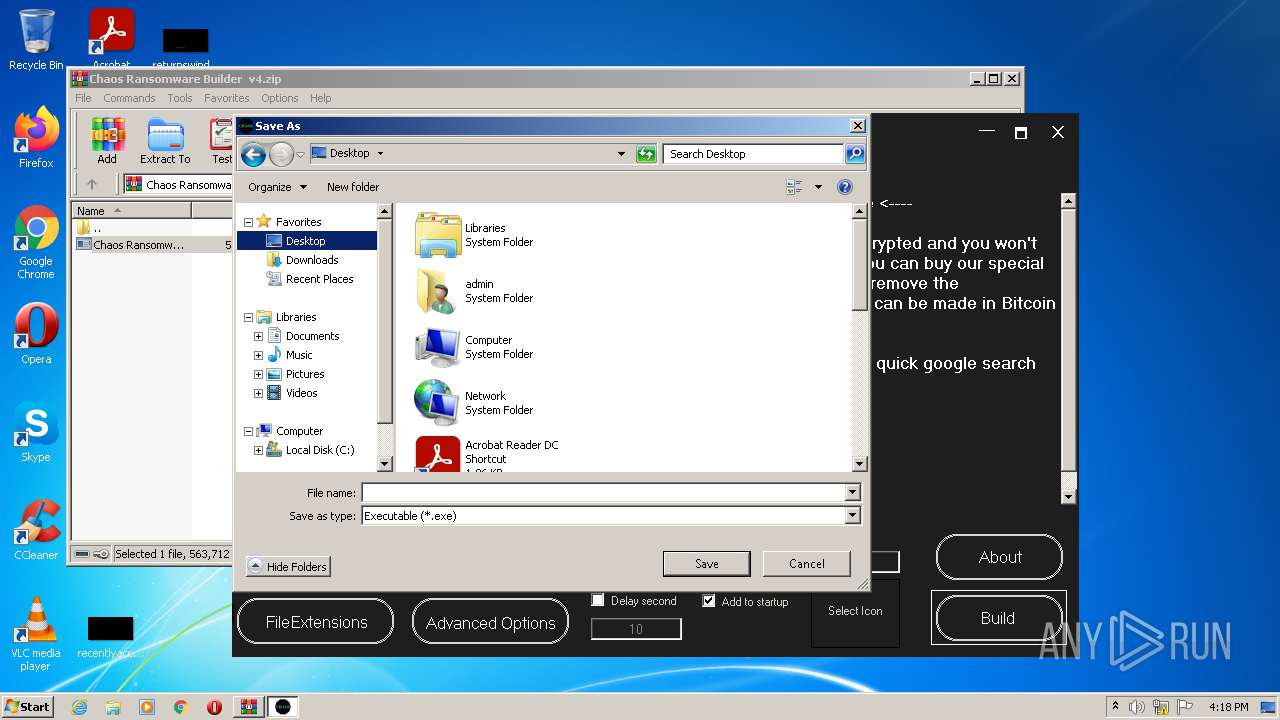
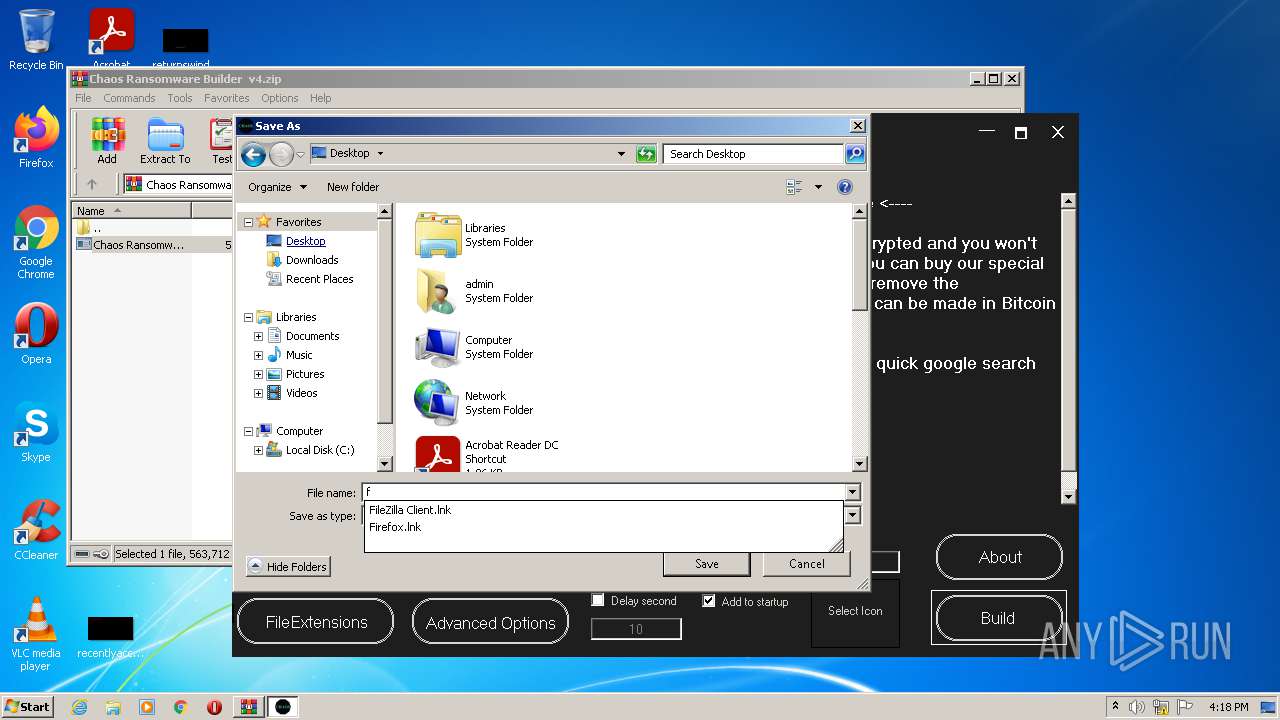
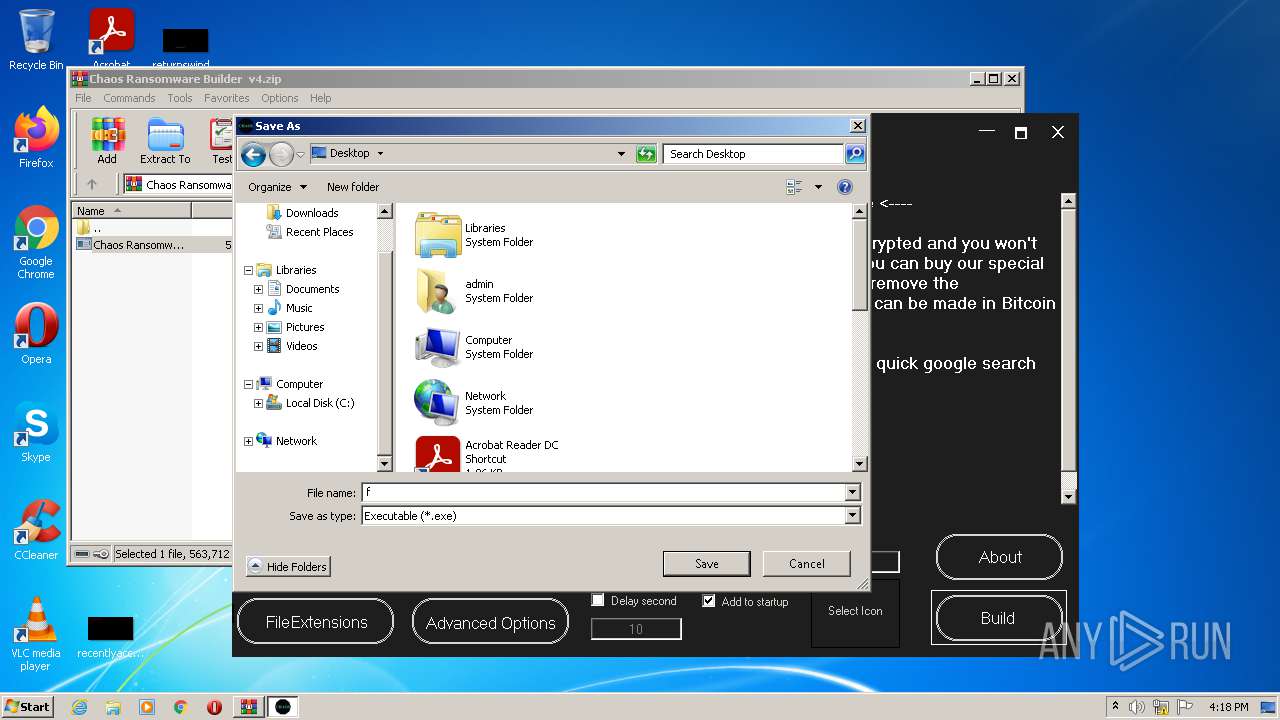
Manual execution by user
- f.exe (PID: 2224)
Checks supported languages
- NOTEPAD.EXE (PID: 3016)
- DllHost.exe (PID: 3872)
Reads the computer name
- DllHost.exe (PID: 3872)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipFileName: | Chaos Ransomware Builder v4.exe |
|---|---|
| ZipUncompressedSize: | 563712 |
| ZipCompressedSize: | 130770 |
| ZipCRC: | 0xfc0fd79d |
| ZipModifyDate: | 2021:08:04 11:08:15 |
| ZipCompression: | Deflated |
| ZipBitFlag: | - |
| ZipRequiredVersion: | 20 |
Total processes
49
Monitored processes
9
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 520 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RESF737.tmp" "c:\Users\admin\Desktop\CSC8092BDAD66DF451087D1C8CFA1B87950.TMP" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft� Resource File To COFF Object Conversion Utility Exit code: 0 Version: 12.00.51209.34209 built by: FX452RTMGDR Modules
| |||||||||||||||
| 576 | "C:\Users\admin\AppData\Roaming\svchost.exe" | C:\Users\admin\AppData\Roaming\svchost.exe | f.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
| 2168 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\u25xk4pt.cmdline" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\csc.exe | Chaos Ransomware Builder v4.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Visual C# Command Line Compiler Exit code: 0 Version: 4.0.30319.34209 built by: FX452RTMGDR Modules
| |||||||||||||||
| 2224 | "C:\Users\admin\Desktop\f.exe" | C:\Users\admin\Desktop\f.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 1 Version: 0.0.0.0 Modules
| |||||||||||||||
| 2400 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2476.33723\Chaos Ransomware Builder v4.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2476.33723\Chaos Ransomware Builder v4.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Chaos Ransomware v4 Exit code: 3221226540 Version: 3.0.0.0 Modules
| |||||||||||||||
| 2476 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Chaos Ransomware Builder v4.zip" | C:\Program Files\WinRAR\WinRAR.exe | Explorer.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
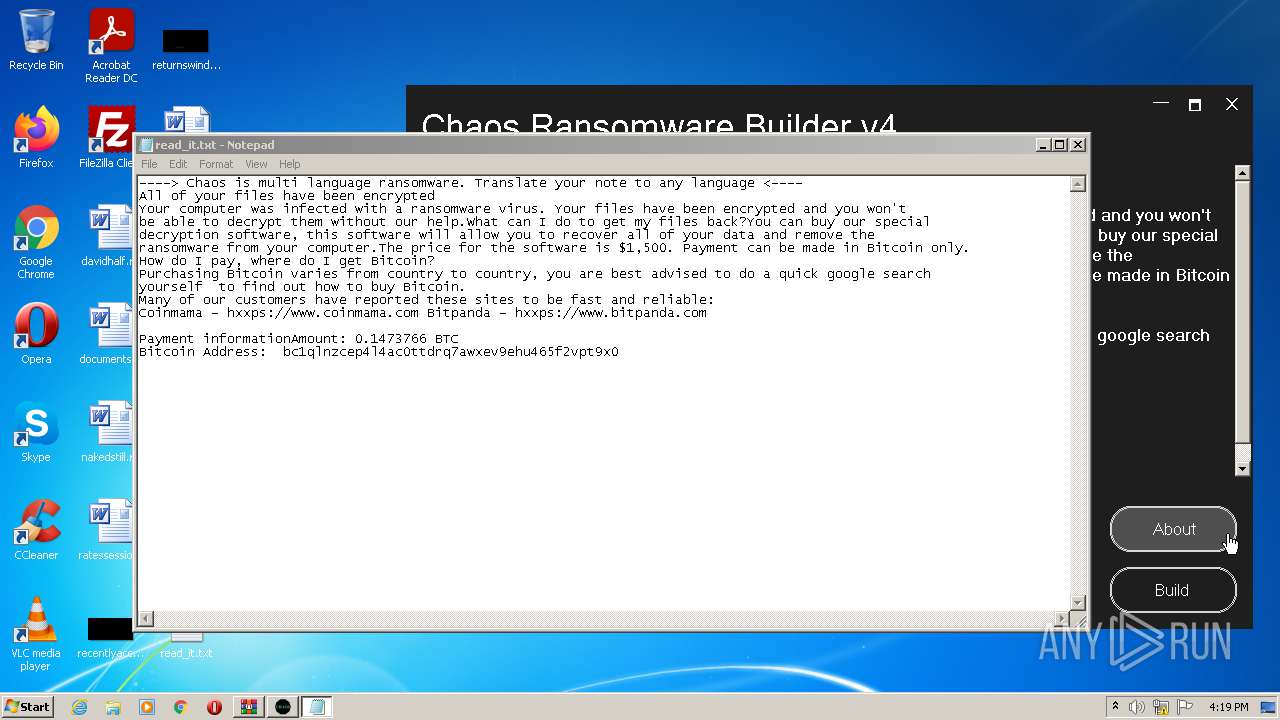
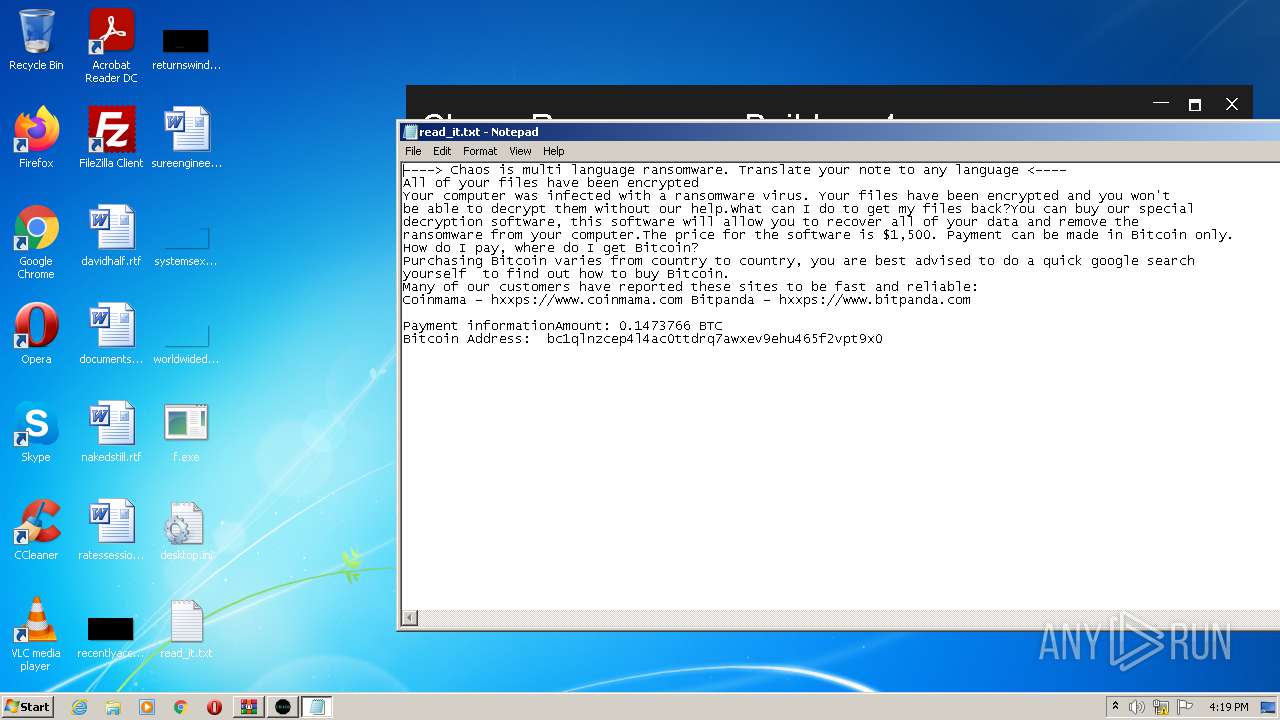
| 3016 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Roaming\read_it.txt | C:\Windows\system32\NOTEPAD.EXE | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3232 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2476.33723\Chaos Ransomware Builder v4.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2476.33723\Chaos Ransomware Builder v4.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Chaos Ransomware v4 Exit code: 0 Version: 3.0.0.0 Modules
| |||||||||||||||
| 3872 | C:\Windows\system32\DllHost.exe /Processid:{76D0CB12-7604-4048-B83C-1005C7DDC503} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
4 764
Read events
4 630
Write events
131
Delete events
3
Modification events
| (PID) Process: | (2476) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2476) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2476) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2476) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (2476) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (2476) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Chaos Ransomware Builder v4.zip | |||
| (PID) Process: | (2476) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2476) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2476) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2476) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
3
Suspicious files
0
Text files
99
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3232 | Chaos Ransomware Builder v4.exe | C:\Users\admin\AppData\Local\Temp\u25xk4pt.cmdline | text | |
MD5:368B90D9C4833C528CE826082F903D4A | SHA256:968534D2F010BCB6226654E59F6FF96F3FB268FD424C758F0844E4D297B5AE04 | |||
| 520 | cvtres.exe | C:\Users\admin\AppData\Local\Temp\RESF737.tmp | o | |
MD5:0B3DC79BCBCA4F01F2F2B0A51ECCBFC3 | SHA256:C63EB613708AC8B0F5D411B76961F072A043D74A081B8CA13A91CC88B6215457 | |||
| 2224 | f.exe | C:\Users\admin\AppData\Roaming\svchost.exe | executable | |
MD5:1304F2CA54DC9E842C18BE7675F7CE94 | SHA256:4BD54E6535C81596C46056AC632613AA3CD9B73A6E29816CF61DFA533C76D757 | |||
| 2168 | csc.exe | C:\Users\admin\AppData\Local\Temp\u25xk4pt.out | text | |
MD5:F29D624A80D1A5D9483197779216F78A | SHA256:207ACF84B658E327D9612BAE108A9DEAAEED5A1C4CB347A777565C50FFFDDF93 | |||
| 2168 | csc.exe | C:\Users\admin\Desktop\CSC8092BDAD66DF451087D1C8CFA1B87950.TMP | res | |
MD5:2B75AC68C6BFC838520A6EC213F7B63A | SHA256:074ED926EF8A4815BC405E7C9C894AF10609F10FE8280E5DC331A7B020F9DDA2 | |||
| 576 | svchost.exe | C:\Users\admin\Contacts\read_it.txt | text | |
MD5:4217B8B83CE3C3F70029A056546F8FD0 | SHA256:7D767E907BE373C680D1F7884D779588EB643BEBB3F27BF3B5ED4864AA4D8121 | |||
| 576 | svchost.exe | C:\Users\admin\Music\read_it.txt | text | |
MD5:4217B8B83CE3C3F70029A056546F8FD0 | SHA256:7D767E907BE373C680D1F7884D779588EB643BEBB3F27BF3B5ED4864AA4D8121 | |||
| 576 | svchost.exe | C:\Users\admin\Links\read_it.txt | text | |
MD5:4217B8B83CE3C3F70029A056546F8FD0 | SHA256:7D767E907BE373C680D1F7884D779588EB643BEBB3F27BF3B5ED4864AA4D8121 | |||
| 2476 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2476.33723\Chaos Ransomware Builder v4.exe | executable | |
MD5:8B855E56E41A6E10D28522A20C1E0341 | SHA256:F2665F89BA53ABD3DEB81988C0D5194992214053E77FC89B98B64A31A7504D77 | |||
| 2168 | csc.exe | C:\Users\admin\Desktop\f.exe | executable | |
MD5:1304F2CA54DC9E842C18BE7675F7CE94 | SHA256:4BD54E6535C81596C46056AC632613AA3CD9B73A6E29816CF61DFA533C76D757 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report