| File name: | b3f9e57b47a910f6cc5f7cb4e24c4e8749242c60e5b3d2f0008de8e068413a32 |
| Full analysis: | https://app.any.run/tasks/05120c58-1e7b-4e0e-925a-bd0489f876b1 |
| Verdict: | Malicious activity |
| Analysis date: | December 13, 2024, 21:23:11 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, Code page: -535, Template: Normal, Last Saved By: george, Revision Number: 3, Name of Creating Application: Microsoft Office Word, Total Editing Time: 02:00, Create Time/Date: Fri Dec 13 07:28:00 2024, Last Saved Time/Date: Fri Dec 13 11:04:00 2024, Number of Pages: 46, Number of Words: 5143, Number of Characters: 29321, Security: 0 |
| MD5: | 5E5B4D1E6DB3D15D4BDE7B254A6971D7 |
| SHA1: | 0412158F7E631434D43B1362589EBDFE8D0D86DB |
| SHA256: | B3F9E57B47A910F6CC5F7CB4E24C4E8749242C60E5B3D2F0008DE8E068413A32 |
| SSDEEP: | 98304:RLjGZ44Hd0k4TLGcfTmWvcMCRbMPQZUYcaoIkQGYMAynuTvAo3qHGeucVhz:5Kt/y |
MALICIOUS
Unusual execution from MS Office
- WINWORD.EXE (PID: 4264)
Microsoft Office executes commands via PowerShell or Cmd
- WINWORD.EXE (PID: 4264)
Starts POWERSHELL.EXE for commands execution
- WINWORD.EXE (PID: 4264)
SUSPICIOUS
BASE64 encoded PowerShell command has been detected
- WINWORD.EXE (PID: 4264)
Runs shell command (SCRIPT)
- WINWORD.EXE (PID: 4264)
Base64-obfuscated command line is found
- WINWORD.EXE (PID: 4264)
INFO
The process uses the downloaded file
- WINWORD.EXE (PID: 4264)
- powershell.exe (PID: 5236)
Reads security settings of Internet Explorer
- notepad.exe (PID: 3732)
Sends debugging messages
- WINWORD.EXE (PID: 4264)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Identification: | Word 8.0 |
|---|---|
| LanguageCode: | English (US) |
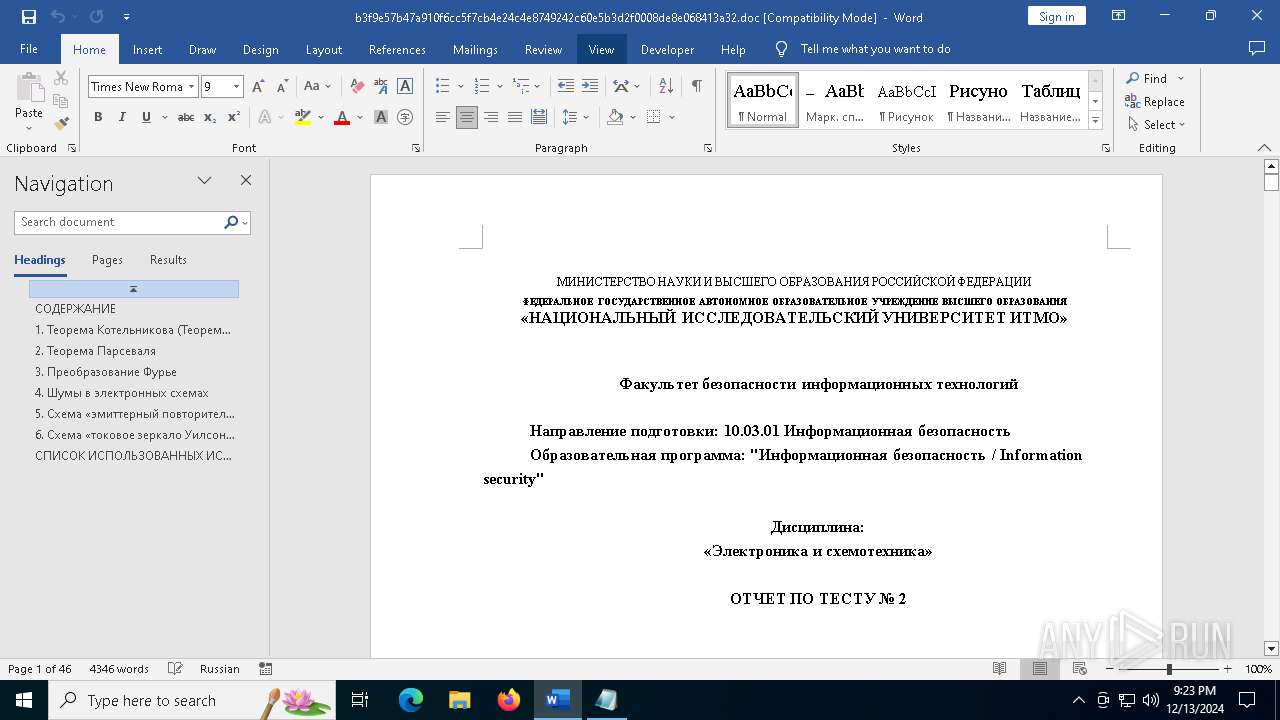
| DocFlags: | Has picture, 1Table, ExtChar |
| System: | Windows |
| Word97: | No |
| Title: | - |
| Subject: | - |
| Author: | я |
| Keywords: | - |
| Comments: | - |
| Template: | Normal |
| LastModifiedBy: | george |
| Software: | Microsoft Office Word |
| CreateDate: | 2024:12:13 07:28:00 |
| ModifyDate: | 2024:12:13 11:04:00 |
| Security: | None |
| Company: | - |
| CharCountWithSpaces: | 34396 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | |
| HeadingPairs: |
|
| CodePage: | Unicode (UTF-8) |
| Hyperlinks: |
|
| ContentTypeId: | 0x0101000631687E8029D14B878CA838C9CA142A |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
| LastPrinted: | 0000:00:00 00:00:00 |
| RevisionNumber: | 3 |
| TotalEditTime: | 2 minutes |
| Words: | 5143 |
| Characters: | 29321 |
| Pages: | 46 |
| Paragraphs: | 68 |
| Lines: | 244 |
Total processes
126
Monitored processes
5
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
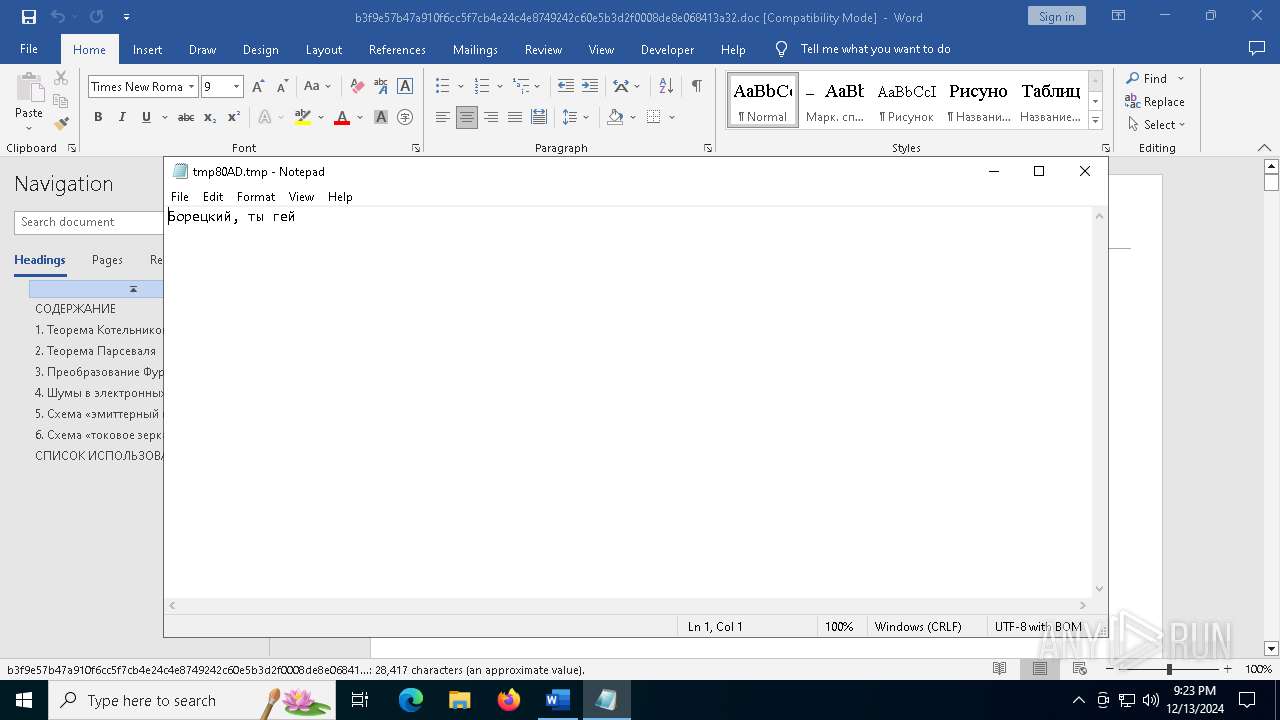
| 3732 | "C:\WINDOWS\system32\notepad.exe" C:\Users\admin\AppData\Local\Temp\tmp80AD.tmp | C:\Windows\System32\notepad.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4264 | "C:\Program Files\Microsoft Office\Root\Office16\WINWORD.EXE" /n C:\Users\admin\Desktop\b3f9e57b47a910f6cc5f7cb4e24c4e8749242c60e5b3d2f0008de8e068413a32.doc /o "" | C:\Program Files\Microsoft Office\root\Office16\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Version: 16.0.16026.20146 Modules
| |||||||||||||||
| 4520 | "C:\Program Files\Microsoft Office\root\VFS\ProgramFilesCommonX64\Microsoft Shared\OFFICE16\ai.exe" "40BAD1F6-D5A4-4BC4-AAC7-5F41CE8497B7" "251BDE47-5A37-43CB-8984-29448F5AFA83" "4264" | C:\Program Files\Microsoft Office\root\VFS\ProgramFilesCommonX64\Microsoft Shared\OFFICE16\ai.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Artificial Intelligence (AI) Host for the Microsoft® Windows® Operating System and Platform x64. Version: 0.12.2.0 Modules
| |||||||||||||||
| 5236 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -e JAB0AGUAeAB0AEMAbwBuAHQAZQBuAHQAIAA9ACAAIgARBD4EQAQ1BEYEOgQ4BDkELAAgAEIESwQgADMENQQ5BCIAOwAkAHQAZQBtAHAARgBpAGwAZQAgAD0AIABOAGUAdwAtAFQAZQBtAHAAbwByAGEAcgB5AEYAaQBsAGUAOwAkAHQAZQBtAHAARgBpAGwAZQBQAGEAdABoACAAPQAgACQAdABlAG0AcABGAGkAbABlAC4ARgB1AGwAbABOAGEAbQBlADsAJAB0AGUAeAB0AEMAbwBuAHQAZQBuAHQAIAB8ACAATwB1AHQALQBGAGkAbABlACAALQBGAGkAbABlAFAAYQB0AGgAIAAkAHQAZQBtAHAARgBpAGwAZQBQAGEAdABoACAALQBFAG4AYwBvAGQAaQBuAGcAIABVAFQARgA4ADsAUwB0AGEAcgB0AC0AUAByAG8AYwBlAHMAcwAgAG4AbwB0AGUAcABhAGQALgBlAHgAZQAgACQAdABlAG0AcABGAGkAbABlAFAAYQB0AGgAOwA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5604 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
19 584
Read events
19 201
Write events
360
Delete events
23
Modification events
| (PID) Process: | (4264) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\Common\ClientTelemetry\Sampling |
| Operation: | write | Name: | 0 |
Value: 017012000000001000B24E9A3E02000000000000000600000000000000 | |||
| (PID) Process: | (4264) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\Common\CrashPersistence\WINWORD\4264 |
| Operation: | write | Name: | 0 |
Value: 0B0E1095BD25A4D1D38449A823CB55D54DEAF523004688C684E3D3B4D3ED016A04102400449A7D64B29D01008500A907556E6B6E6F776EC906022222CA0DC2190000C91003783634C511A821D2120B770069006E0077006F00720064002E00650078006500C51620C517808004C91808323231322D44656300 | |||
| (PID) Process: | (4264) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | en-US |
Value: 2 | |||
| (PID) Process: | (4264) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | de-de |
Value: 2 | |||
| (PID) Process: | (4264) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | fr-fr |
Value: 2 | |||
| (PID) Process: | (4264) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | es-es |
Value: 2 | |||
| (PID) Process: | (4264) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | it-it |
Value: 2 | |||
| (PID) Process: | (4264) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | ja-jp |
Value: 2 | |||
| (PID) Process: | (4264) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | ko-kr |
Value: 2 | |||
| (PID) Process: | (4264) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | pt-br |
Value: 2 | |||
Executable files
18
Suspicious files
125
Text files
35
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5236 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\LKKQHM9W1JRXY4AVTJSI.temp | binary | |
MD5:DEA56EA6175287ED587EB340692A4924 | SHA256:74C9B364D4B7EED6EE9EBABA75315CC4C514861A79833E6F844A0449D50E6AF8 | |||
| 4264 | WINWORD.EXE | C:\Users\admin\Desktop\~$f9e57b47a910f6cc5f7cb4e24c4e8749242c60e5b3d2f0008de8e068413a32.doc | binary | |
MD5:42BEB9D68638B56A222AFFB0A199A71B | SHA256:85BF7B9A819FB4F15F03241C44ED3B64454BCC282DDE1CCCBD3A64EE9CAB6A8C | |||
| 5236 | powershell.exe | C:\Users\admin\AppData\Local\Temp\tmp80AD.tmp | text | |
MD5:B685BE298B0829E25958A50BD187F460 | SHA256:B1432B38F3BD38D4E17451E48619681DDAB999663CFD45D50AB89BB1DDCDC0B1 | |||
| 4264 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:8D10BB1833727CC72EA8B144A7EA82B5 | SHA256:8322F1DFEB2F02122C27976298FE989ECC0208E217EC872700AEB44272FE77A3 | |||
| 5236 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_v3aqpgi5.w13.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5236 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF137468.TMP | binary | |
MD5:D040F64E9E7A2BB91ABCA5613424598E | SHA256:D04E0A6940609BD6F3B561B0F6027F5CA4E8C5CF0FB0D0874B380A0374A8D670 | |||
| 4264 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\UsageMetricsStore\FileActivityStoreV3\Word\ASkwMDAwMDAwMC0wMDAwLTAwMDAtMDAwMC0wMDAwMDAwMDAwMDBfTnVsbAA.S | binary | |
MD5:9C2D6F1DA2C2835D6C3FE3F15556DC76 | SHA256:6C0BABCE792985136DBA2C03D9DAE5FFDFB4F6DE3A0D8DC9140F473200277A3A | |||
| 4264 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\AddInClassifierCache\OfficeSharedEntities.bin | text | |
MD5:CC90D669144261B198DEAD45AA266572 | SHA256:89C701EEFF939A44F28921FD85365ECD87041935DCD0FE0BAF04957DA12C9899 | |||
| 4264 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\b3f9e57b47a910f6cc5f7cb4e24c4e8749242c60e5b3d2f0008de8e068413a32.doc.LNK | binary | |
MD5:0D401812BBCC57C63762D9AA543EFA57 | SHA256:DBDDD1175DFE819B91B30674B39A6313C0A0411E68C7FDC6DE79A1E19BF721D7 | |||
| 5236 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_gfruaysu.3ur.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
71
TCP/UDP connections
85
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6068 | svchost.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6068 | svchost.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.48.23.29:443 | https://omex.cdn.office.net/addinclassifier/officesharedentities | unknown | text | 314 Kb | whitelisted |
— | — | GET | 200 | 52.109.28.46:443 | https://officeclient.microsoft.com/config16/?lcid=1033&syslcid=1033&uilcid=1033&build=16.0.16026&crev=3 | unknown | xml | 178 Kb | whitelisted |
— | — | POST | 200 | 20.42.73.31:443 | https://self.events.data.microsoft.com/OneCollector/1.0/ | unknown | binary | 9 b | whitelisted |
— | — | GET | 200 | 23.53.43.83:443 | https://metadata.templates.cdn.office.net/client/templates/gallery?lcid=1033&syslcid=1033&uilcid=1033&app=0&ver=16&tl=2&build=16.0.16026>ype=0%2C1%2C2%2C5%2C | unknown | xml | 10.7 Kb | whitelisted |
— | — | GET | 200 | 184.24.77.20:443 | https://binaries.templates.cdn.office.net/support/templates/en-us/tp02851220.cab | unknown | compressed | 30.7 Kb | whitelisted |
— | — | GET | 200 | 52.111.231.8:443 | https://messaging.lifecycle.office.com/getcustommessage16?app=0&ui=en-US&src=BizBar&messagetype=BizBar&hwid=04111-083-043729&ver=16.0.16026&lc=en-US&platform=10%3A0%3A19045%3A2%3A0%3A0%3A256%3A1%3A&productid=%7B1717C1E0-47D3-4899-A6D3-1022DB7415E0%7D%3A00411-10830-43729-AA720%3AOffice%2019%2C%20Office19Professional2019R_Retail%20edition&clientsessionid=%7BA425BD95-D3D1-4984-A823-CB55D54DEAF5%7D&datapropertybag=%7B%22Audience%22%3A%22Production%22%2C%22AudienceGroup%22%3A%22Production%22%2C%22AudienceChannel%22%3A%22CC%22%2C%22Flight%22%3A%22ofsh6c2b1tla1a31%2Cofcrui4yvdulbf31%2Cofhpex3jznepoo31%2Cofpioygfqmufst31%2Cofjhlwlmoc1pz531%22%7D | unknown | text | 542 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
6068 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.23.209.140:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
— | — | 192.168.100.255:138 | — | — | — | whitelisted |
4264 | WINWORD.EXE | 52.109.28.46:443 | officeclient.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | GB | whitelisted |
6068 | svchost.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
6068 | svchost.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
officeclient.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
ecs.office.com |
| whitelisted |
omex.cdn.office.net |
| whitelisted |
messaging.lifecycle.office.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
WINWORD.EXE | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
WINWORD.EXE | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
WINWORD.EXE | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|