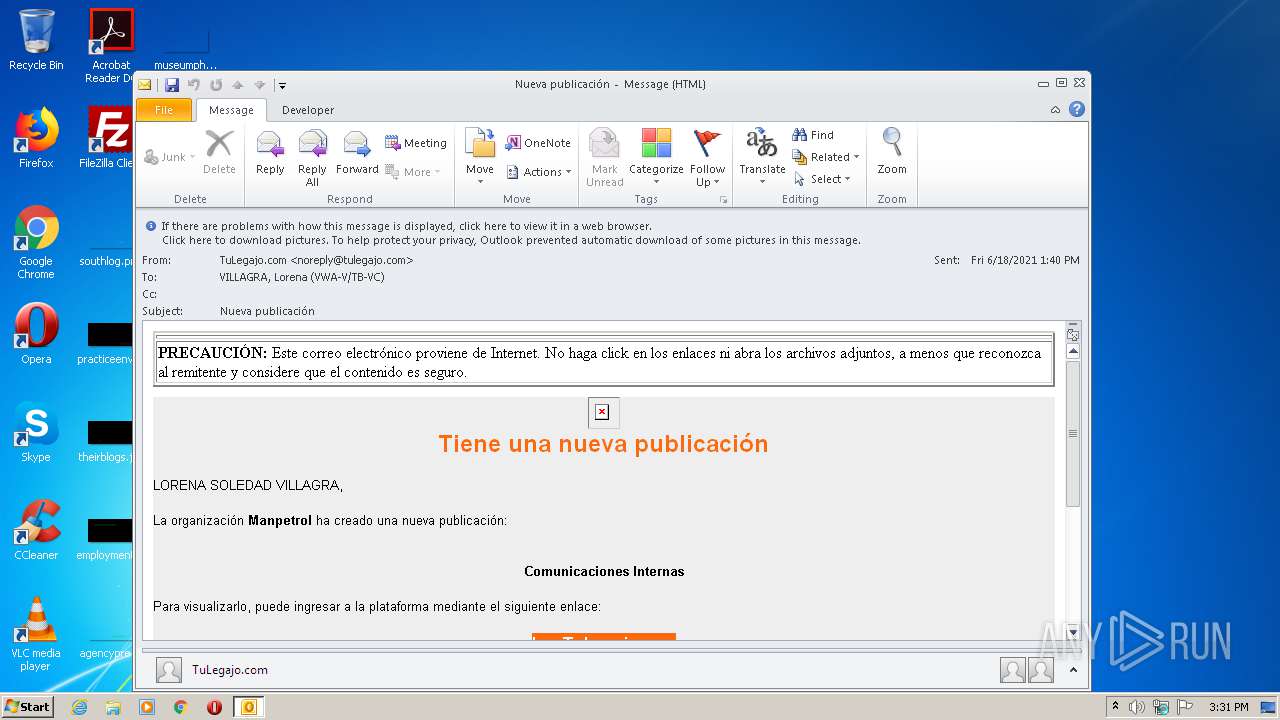
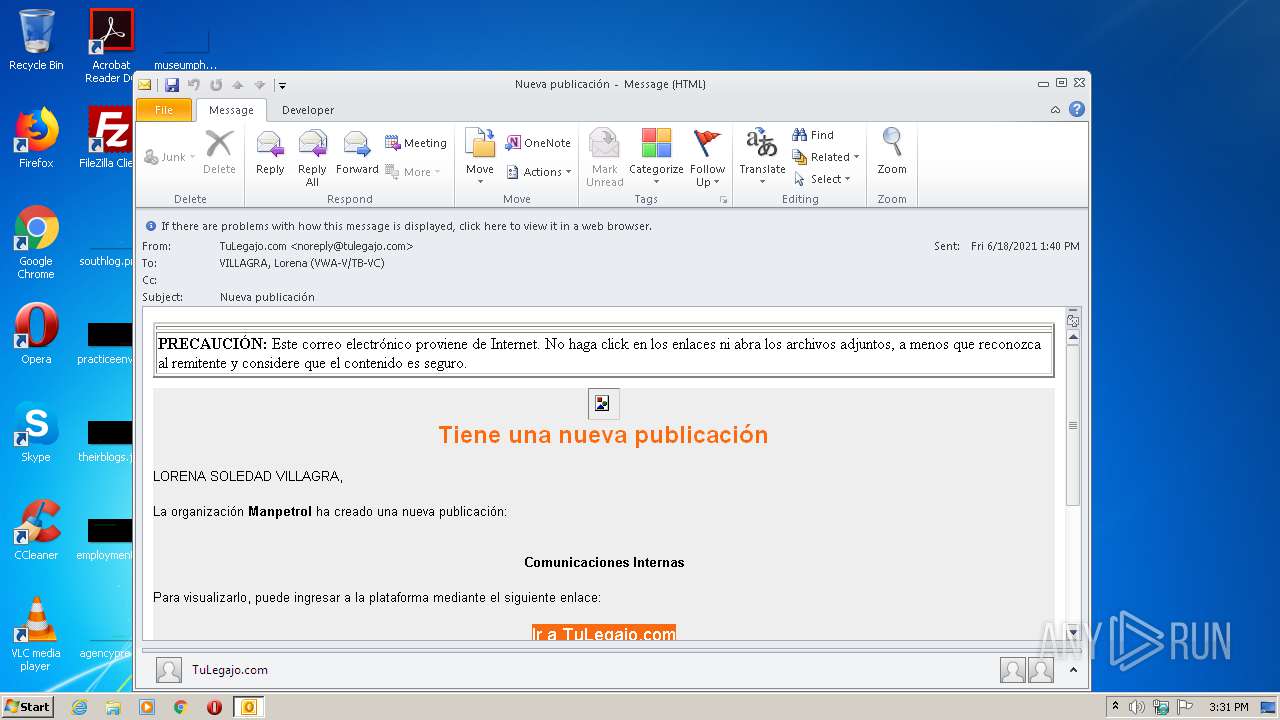
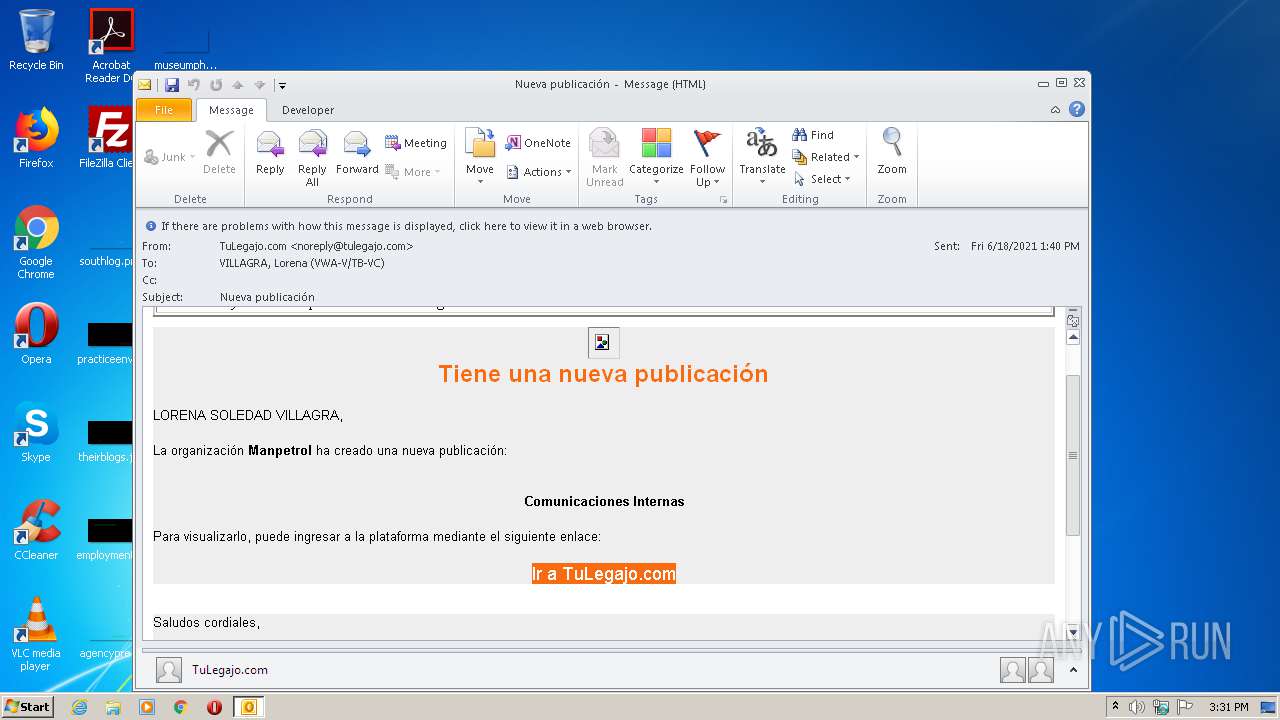
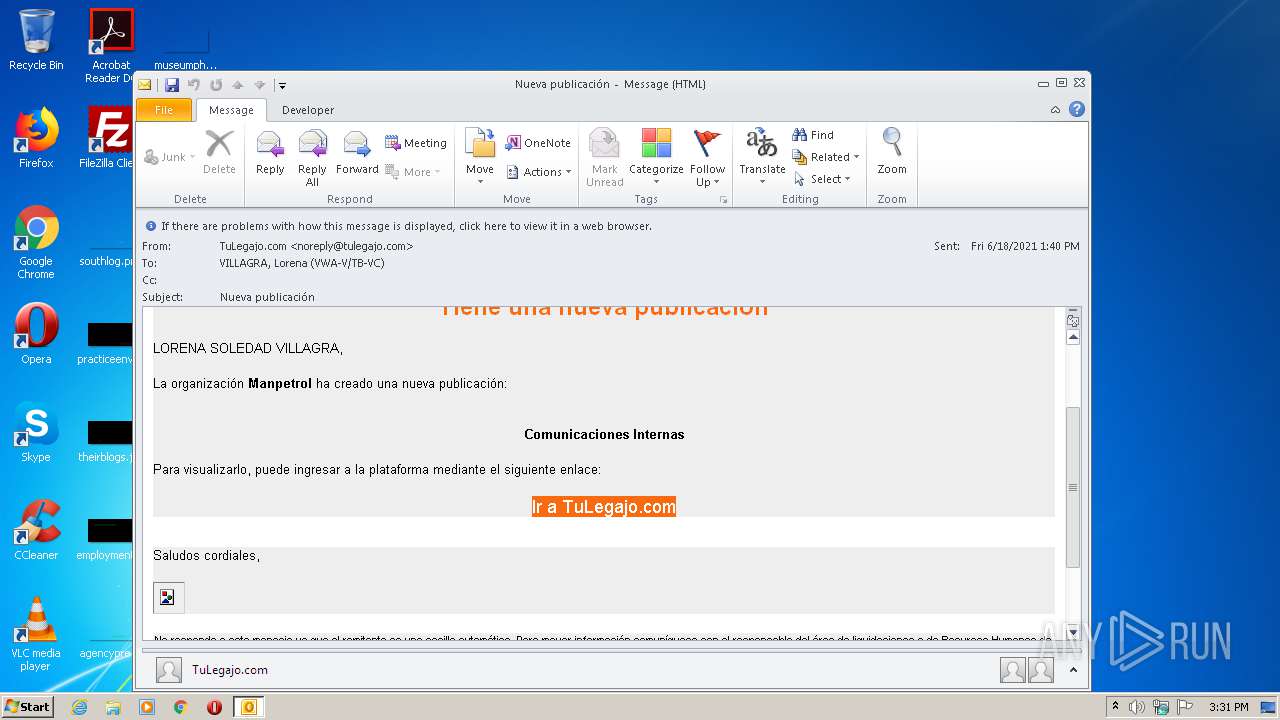
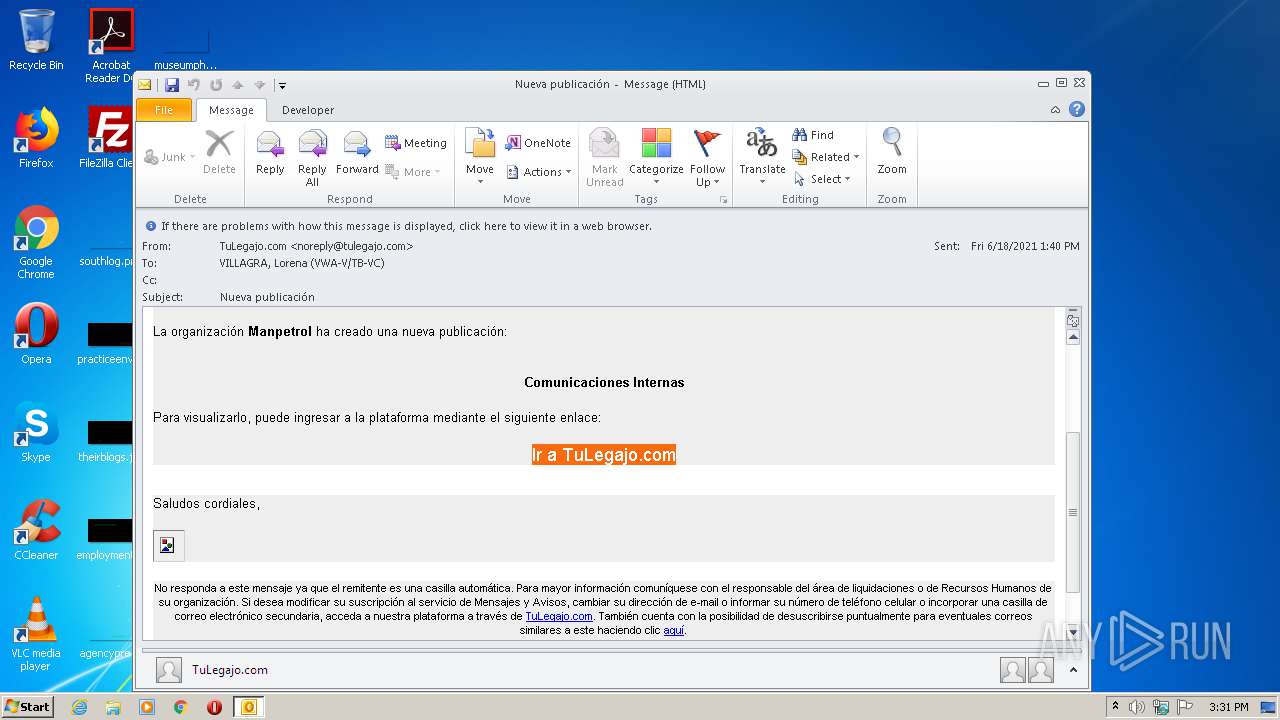
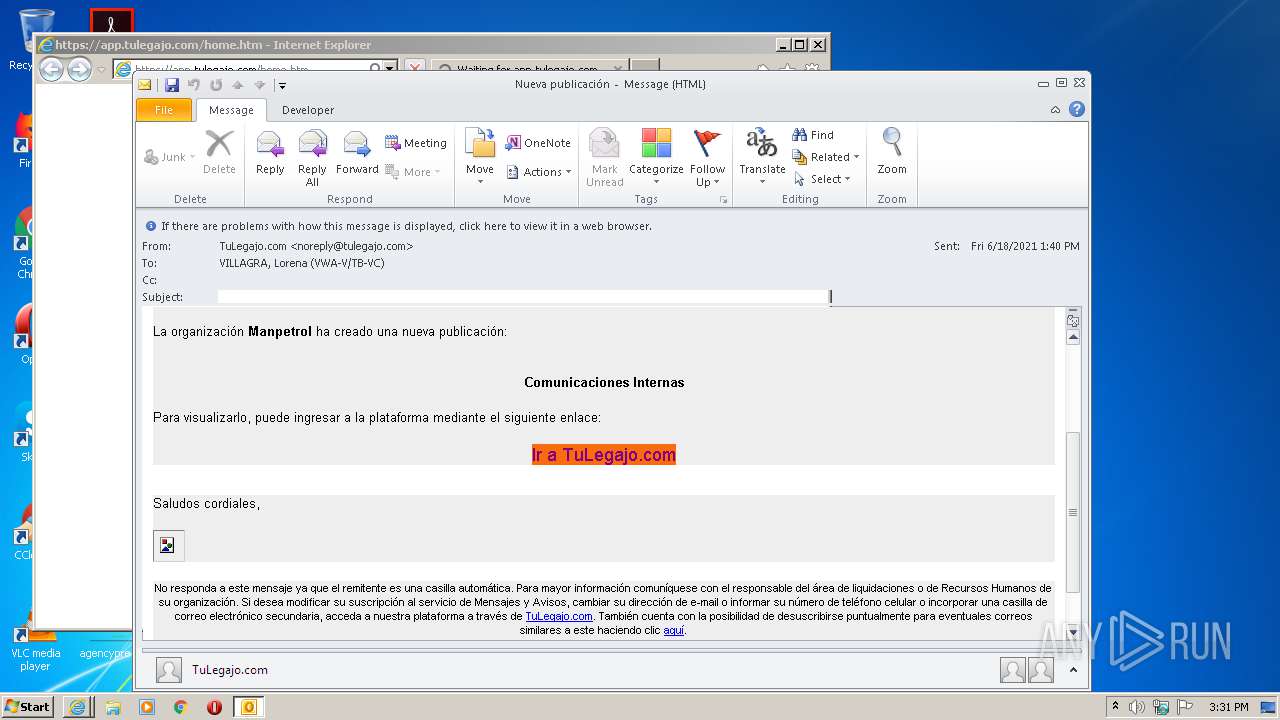
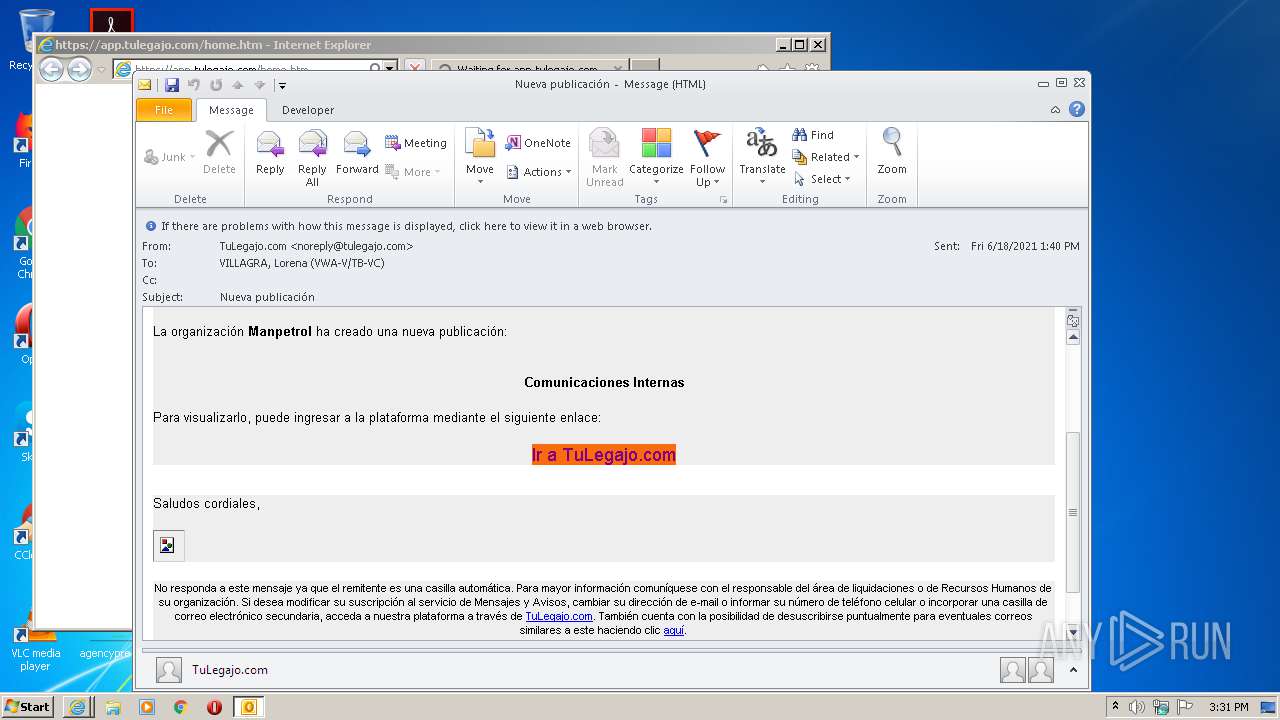
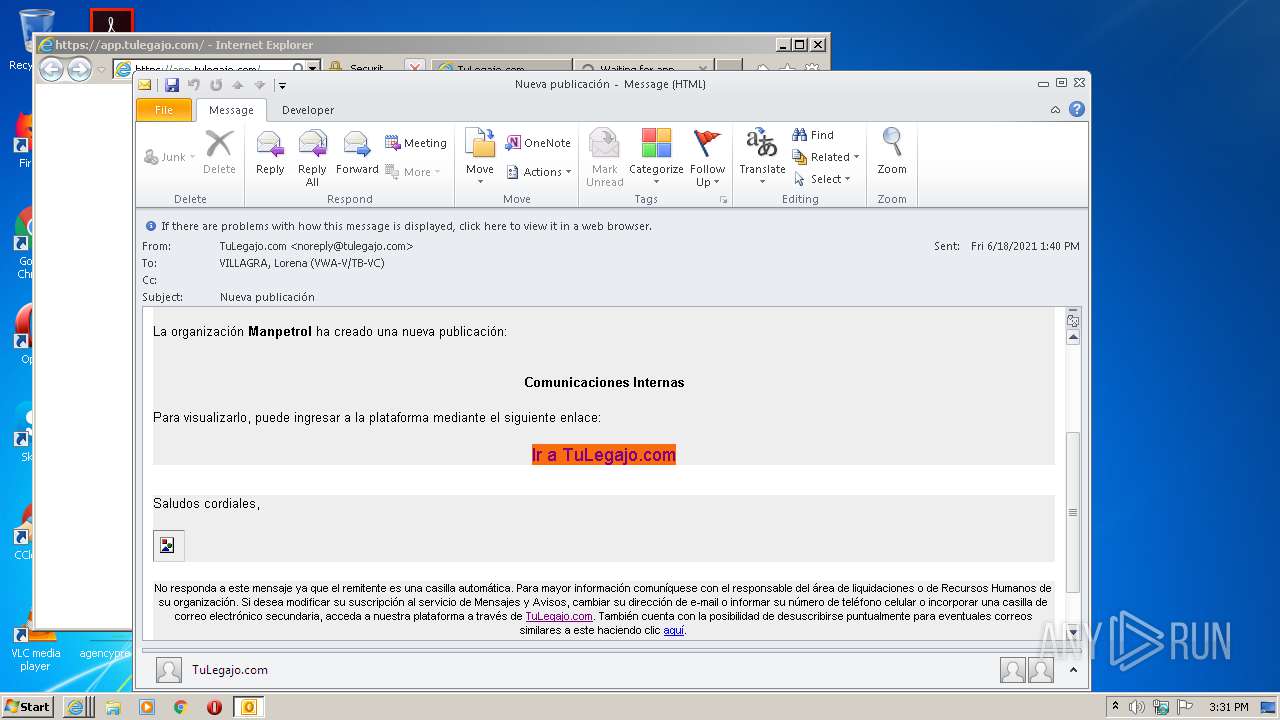
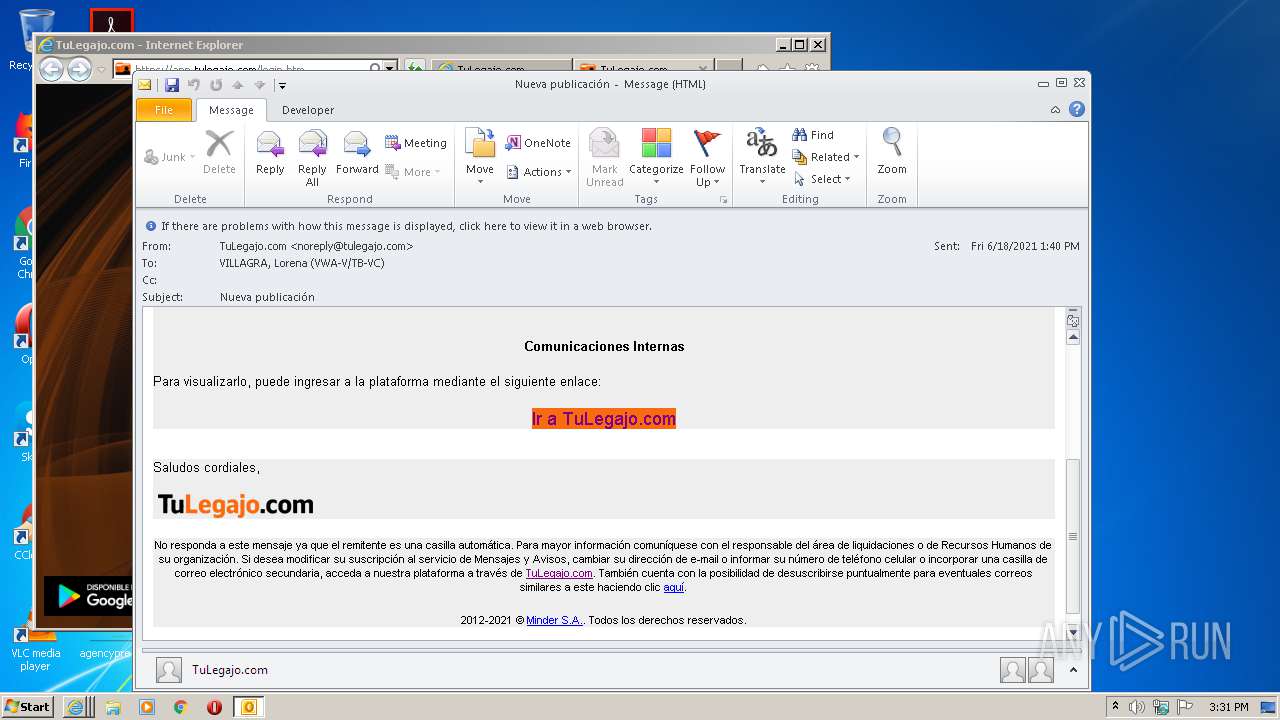
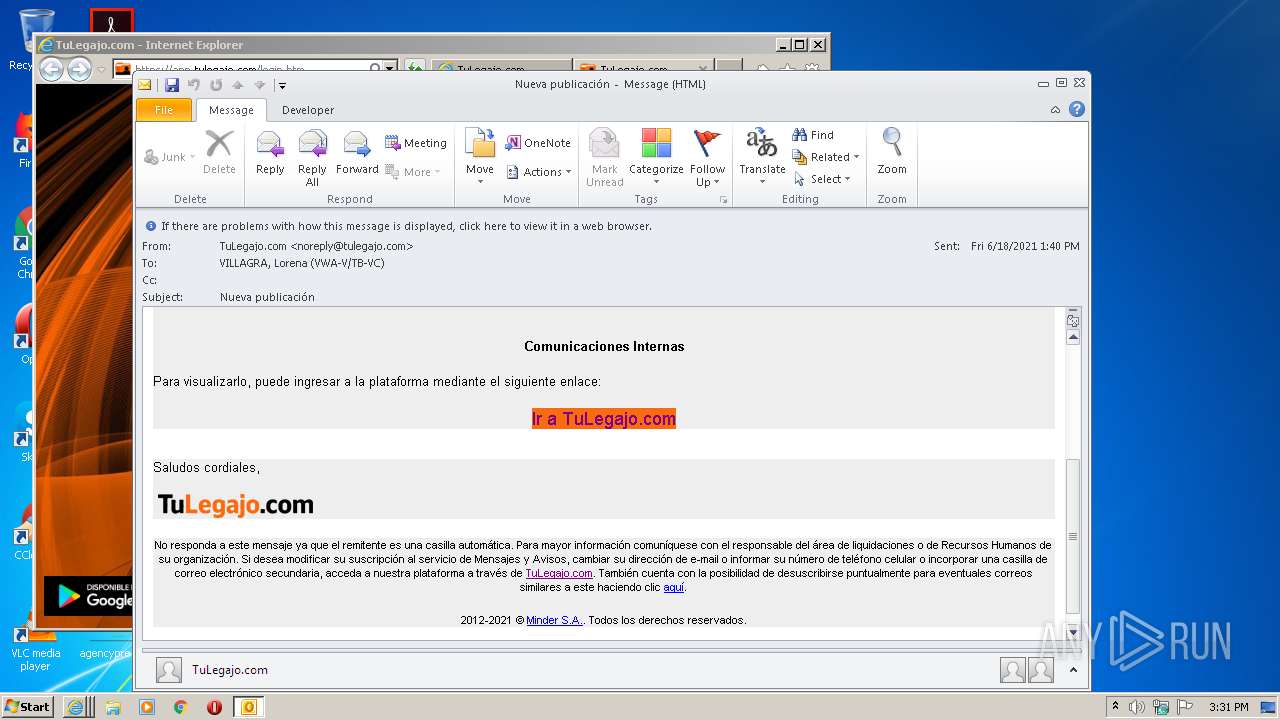
| File name: | Nueva publicación.msg |
| Full analysis: | https://app.any.run/tasks/5a9de6e1-548d-4c81-8279-5b732c4aacae |
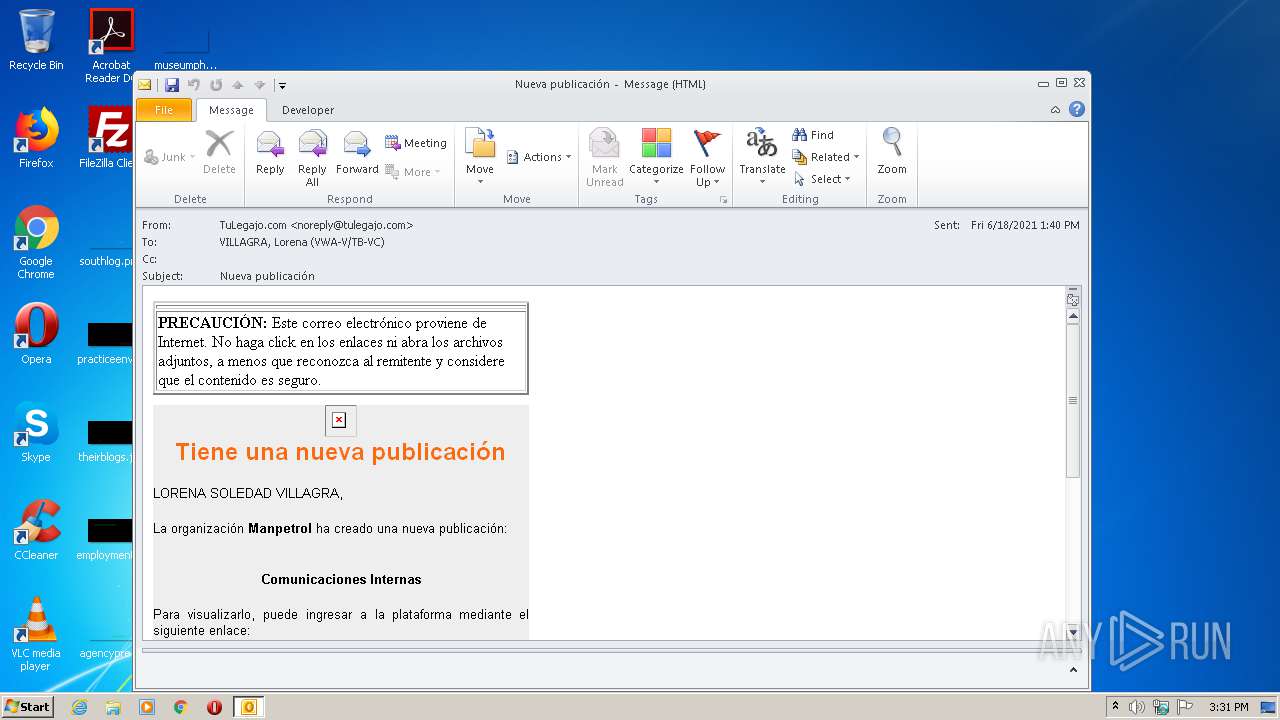
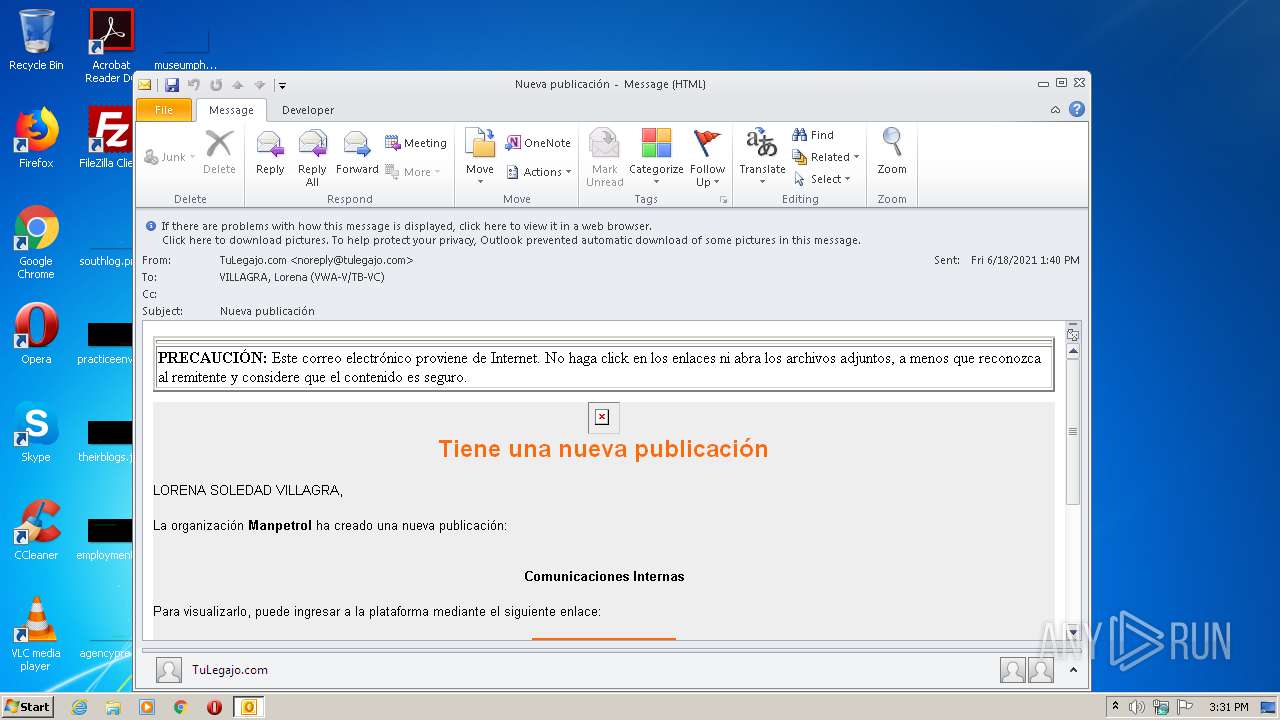
| Verdict: | Malicious activity |
| Analysis date: | June 28, 2021, 14:30:58 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | 6EDA51A56AA303F834BE5BA572F2214D |
| SHA1: | 5081B1DE4ADFB347311EC615DA002F0EC1A37454 |
| SHA256: | B3F690946ADA45AD3DABCC4BFF3B440167CDCB115D4C2625D5CE617D31AF77DE |
| SSDEEP: | 1536:IUVwRyN/acQRyDOe1RlciJy5iJti/AOjl6EjCqHRWJnP4:3ORyN/acMyDJ4N8JU/AOjl6EjCUWZP4 |
MALICIOUS
Unusual execution from Microsoft Office
- OUTLOOK.EXE (PID: 1312)
SUSPICIOUS
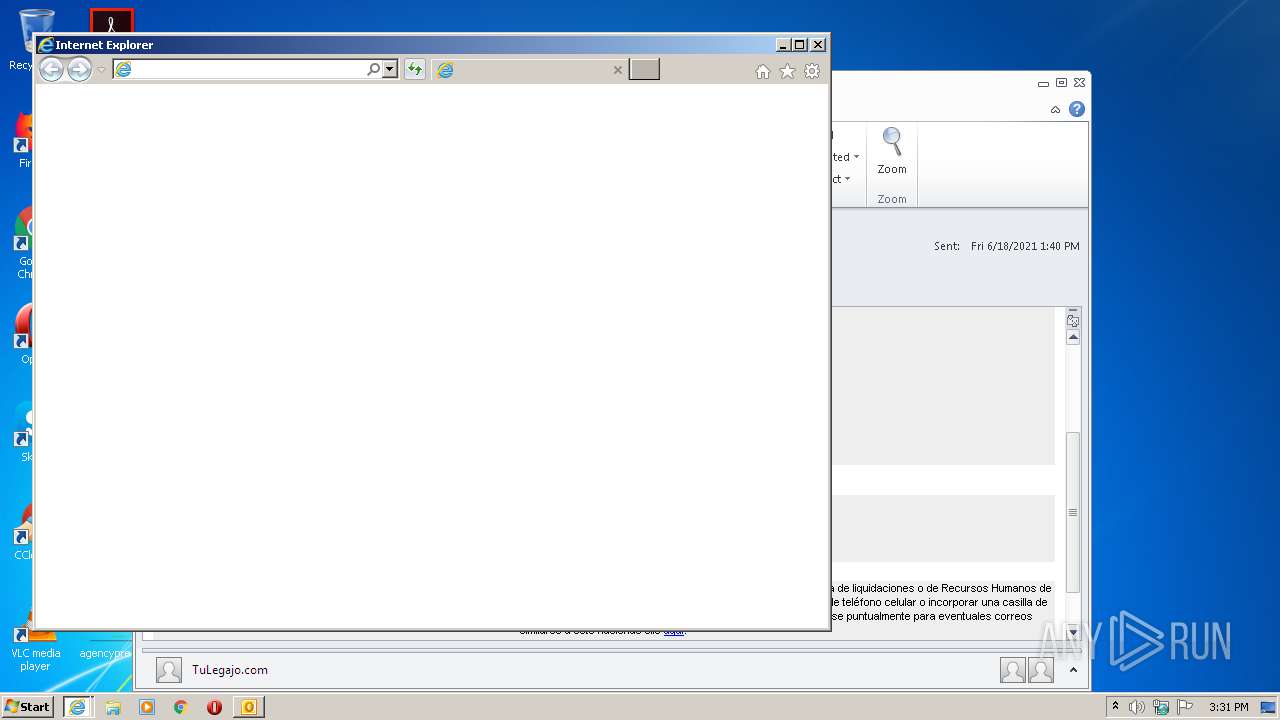
Starts Internet Explorer
- OUTLOOK.EXE (PID: 1312)
INFO
Changes internet zones settings
- iexplore.exe (PID: 3140)
- iexplore.exe (PID: 2372)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 1312)
Creates files in the user directory
- OUTLOOK.EXE (PID: 1312)
- iexplore.exe (PID: 3964)
Application launched itself
- iexplore.exe (PID: 2372)
- iexplore.exe (PID: 3140)
Reads settings of System Certificates
- iexplore.exe (PID: 3920)
- iexplore.exe (PID: 3964)
- iexplore.exe (PID: 3140)
- iexplore.exe (PID: 2820)
- iexplore.exe (PID: 2596)
- iexplore.exe (PID: 2372)
Reads internet explorer settings
- iexplore.exe (PID: 3920)
- iexplore.exe (PID: 3964)
- iexplore.exe (PID: 2820)
- iexplore.exe (PID: 2596)
Changes settings of System certificates
- iexplore.exe (PID: 3140)
- iexplore.exe (PID: 2372)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3140)
- iexplore.exe (PID: 2372)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
44
Monitored processes
7
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1312 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\Nueva publicación.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
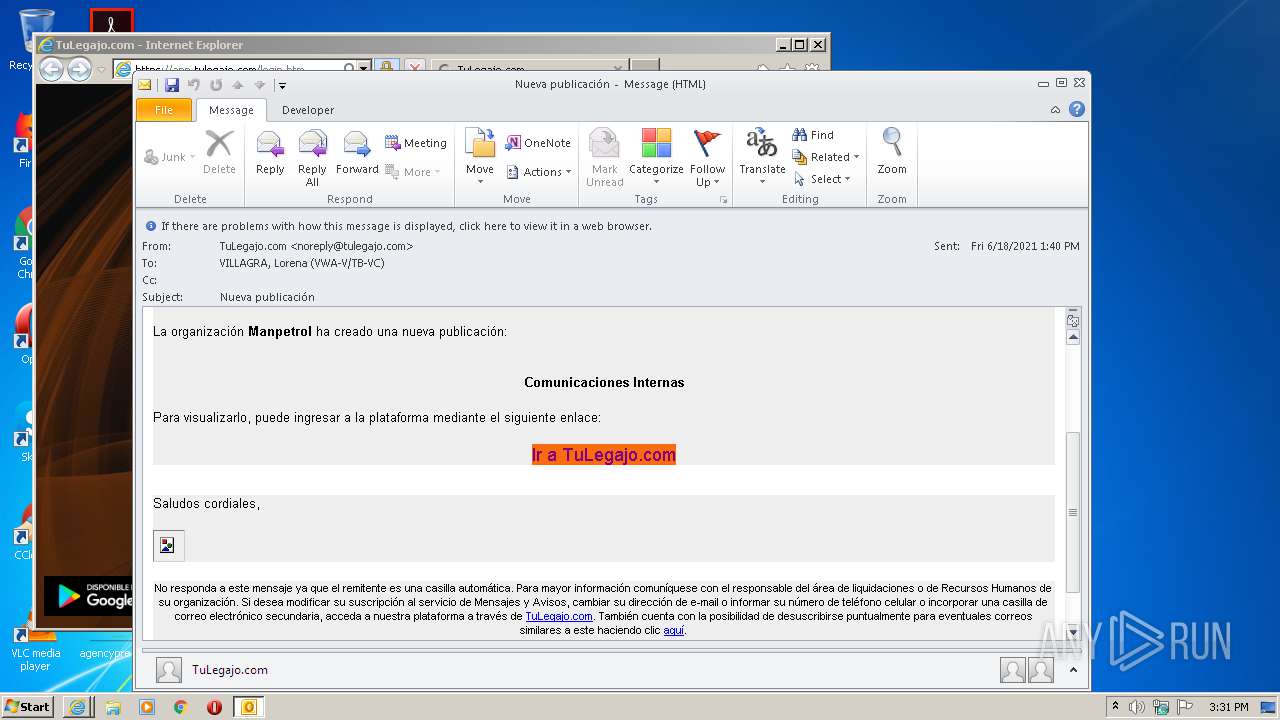
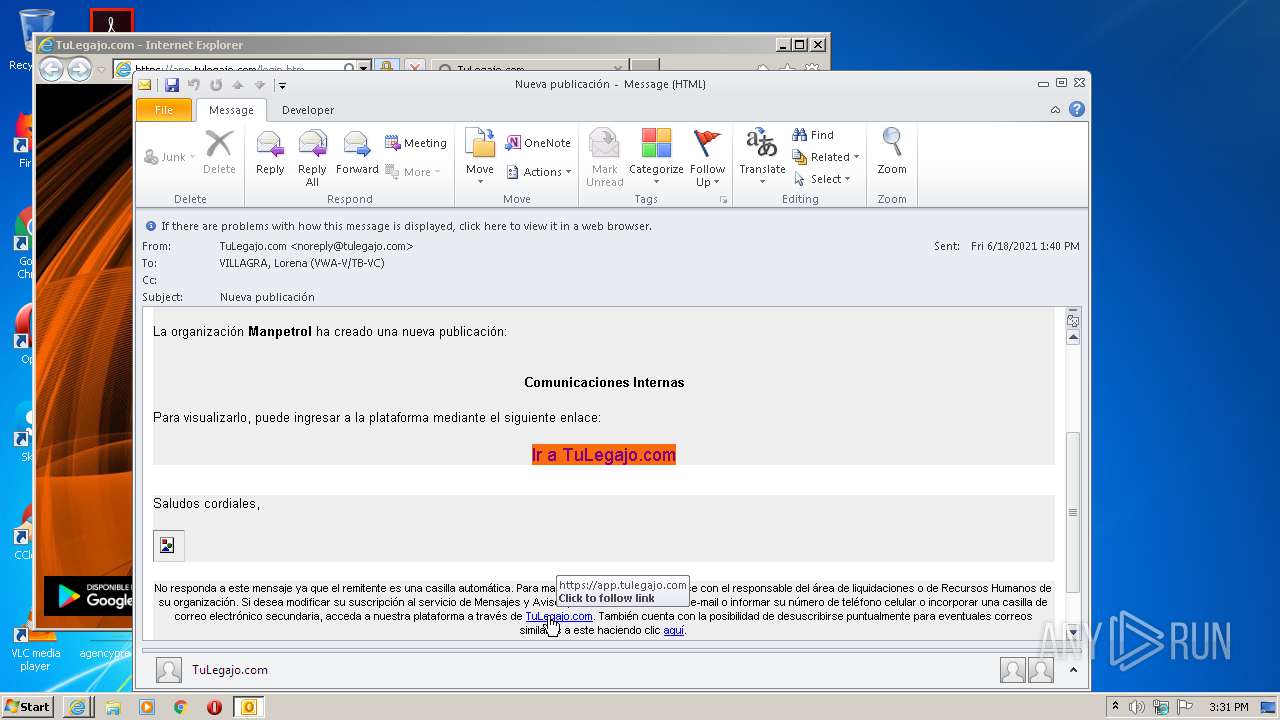
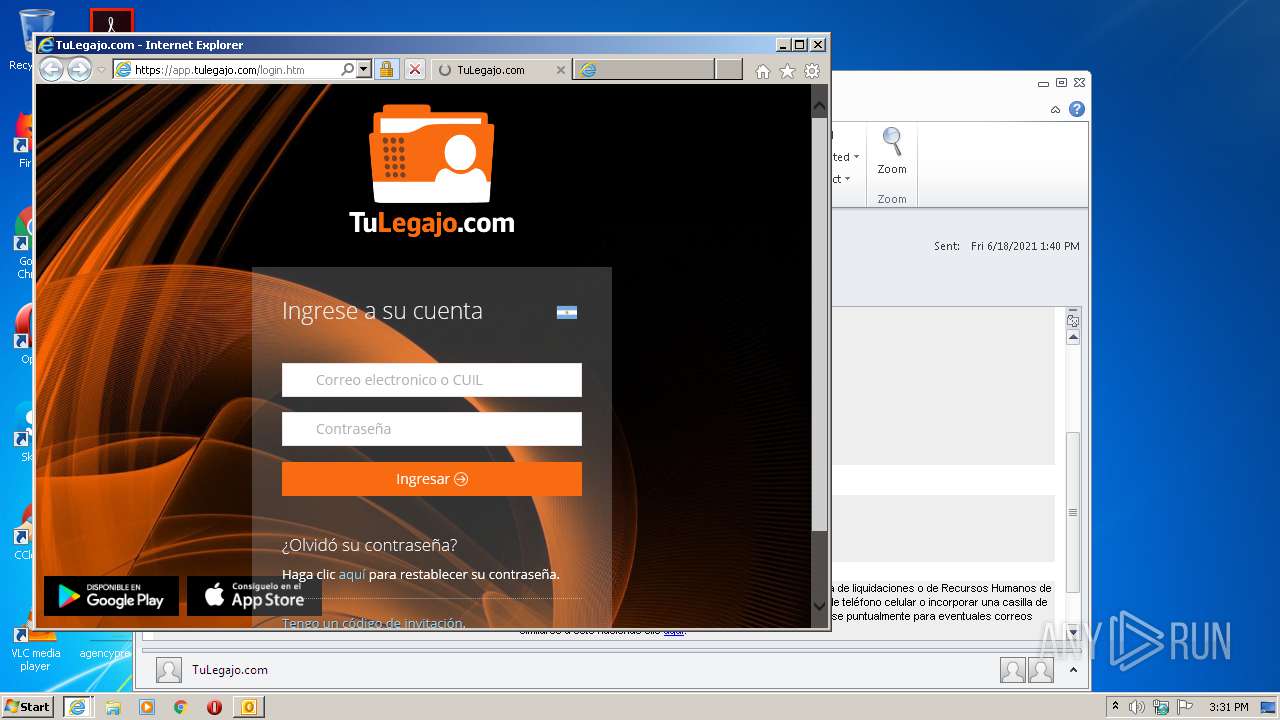
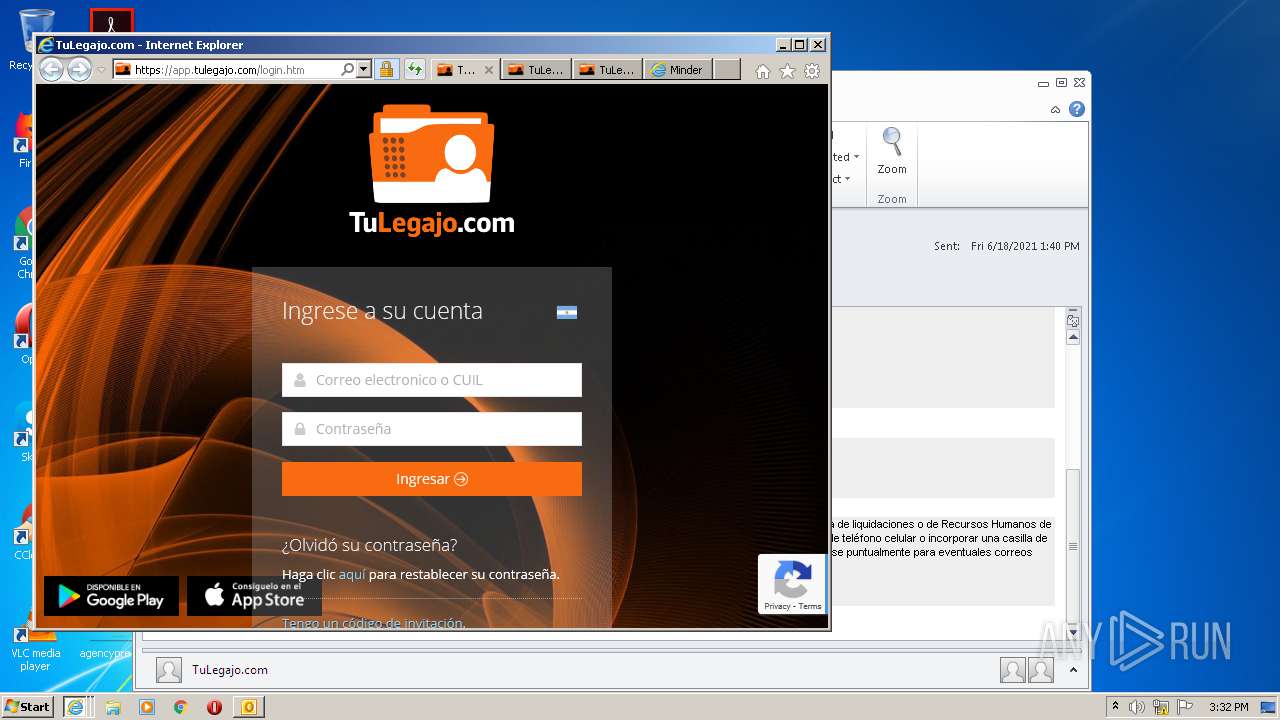
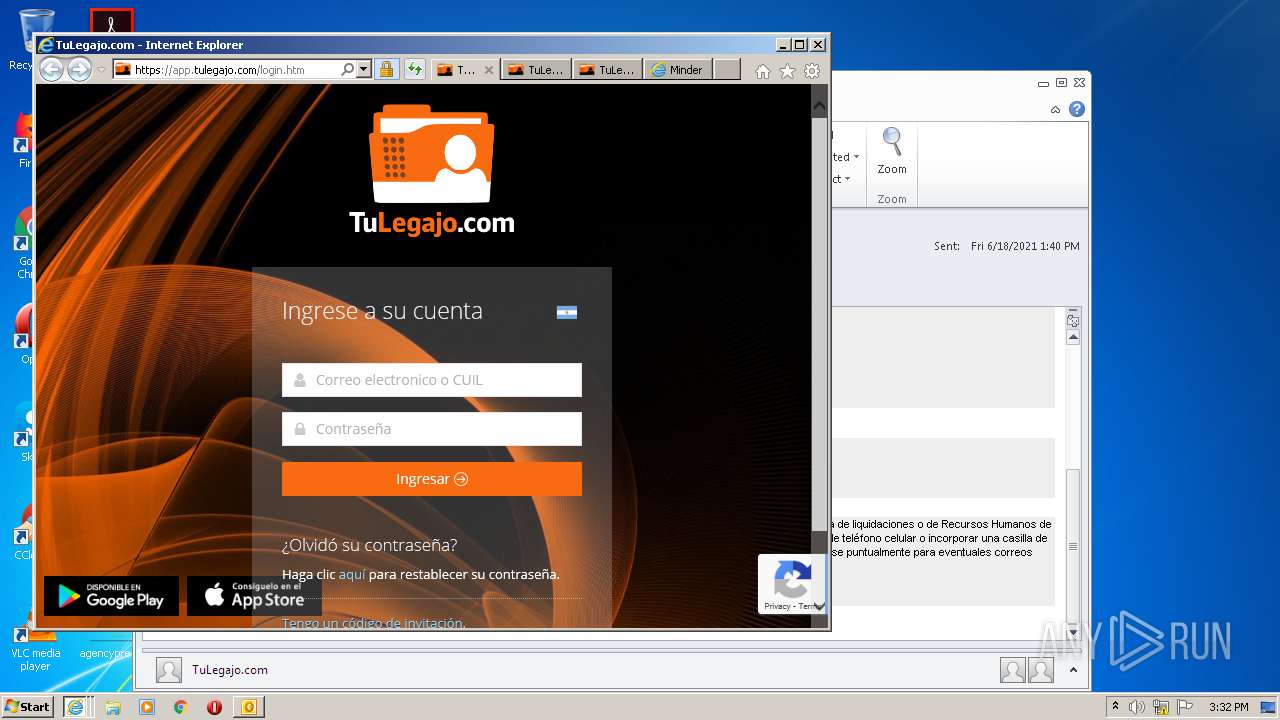
| 2372 | "C:\Program Files\Internet Explorer\iexplore.exe" https://app.tulegajo.com/home.htm | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2596 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2372 CREDAT:726311 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2820 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2372 CREDAT:3937553 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3140 | "C:\Program Files\Internet Explorer\iexplore.exe" https://app.tulegajo.com/home.htm | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3920 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3140 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3964 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2372 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
3 485
Read events
2 695
Write events
765
Delete events
25
Modification events
| (PID) Process: | (1312) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (1312) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (1312) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (1312) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (1312) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (1312) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (1312) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (1312) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (1312) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (1312) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
Executable files
0
Suspicious files
60
Text files
142
Unknown types
55
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1312 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR2123.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3920 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab7398.tmp | — | |
MD5:— | SHA256:— | |||
| 3920 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar7399.tmp | — | |
MD5:— | SHA256:— | |||
| 1312 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
| 1312 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3920 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B66240B0F6C84BD4857ABA60CF5CE4A0_5043E0F5DF723415C9EECC201C838A62 | der | |
MD5:— | SHA256:— | |||
| 3920 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\75CA58072B9926F763A91F0CC2798706_93E4B2BA79A897B3100CCB27F2D3BF4F | der | |
MD5:— | SHA256:— | |||
| 3920 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\BAD725C80F9E10846F35D039A996E4A8_88B6AE015495C1ECC395D19C1DD02894 | binary | |
MD5:— | SHA256:— | |||
| 1312 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_ConversationPrefs_2_A6A3CEFC954C7A43AF74E5AFFE380DB3.dat | xml | |
MD5:57F30B1BCA811C2FCB81F4C13F6A927B | SHA256:612BAD93621991CB09C347FF01EC600B46617247D5C041311FF459E247D8C2D3 | |||
| 1312 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_WorkHours_1_9992772E62F54F4685F05796F6944586.dat | xml | |
MD5:807EF0FC900FEB3DA82927990083D6E7 | SHA256:4411E7DC978011222764943081500FFF0E43CBF7CCD44264BD1AB6306CA68913 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
30
TCP/UDP connections
92
DNS requests
30
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3920 | iexplore.exe | GET | 200 | 172.217.23.99:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
3920 | iexplore.exe | GET | 200 | 143.204.101.123:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | der | 1.70 Kb | whitelisted |
3920 | iexplore.exe | GET | 200 | 13.224.194.68:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwZ%2FlFeFh%2Bisd96yUzJbvJmLVg0%3D | US | der | 1.39 Kb | shared |
3920 | iexplore.exe | GET | 200 | 13.224.194.48:80 | http://ocsp.sca1b.amazontrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQz9arGHWbnBV0DFzpNHz4YcTiFDQQUWaRmBlKge5WSPKOUByeWdFv5PdACEA%2BE5VBiwPwO4qysDdG18Jo%3D | US | der | 471 b | whitelisted |
3920 | iexplore.exe | GET | 200 | 172.217.23.99:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
3920 | iexplore.exe | GET | 200 | 172.217.23.99:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
3920 | iexplore.exe | GET | 200 | 172.217.23.99:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
3920 | iexplore.exe | GET | 200 | 172.217.23.99:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCa%2BkMO6O7i%2FwoAAAAA3KDI | US | der | 472 b | whitelisted |
3920 | iexplore.exe | GET | 200 | 13.224.194.48:80 | http://ocsp.sca1b.amazontrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQz9arGHWbnBV0DFzpNHz4YcTiFDQQUWaRmBlKge5WSPKOUByeWdFv5PdACEAa0Jlx%2BXGw8Av%2FnP9TgR%2FI%3D | US | der | 471 b | whitelisted |
3920 | iexplore.exe | GET | 200 | 172.217.23.99:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQCxnynH5ycfFgUAAAAAh%2BRd | US | der | 472 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1312 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
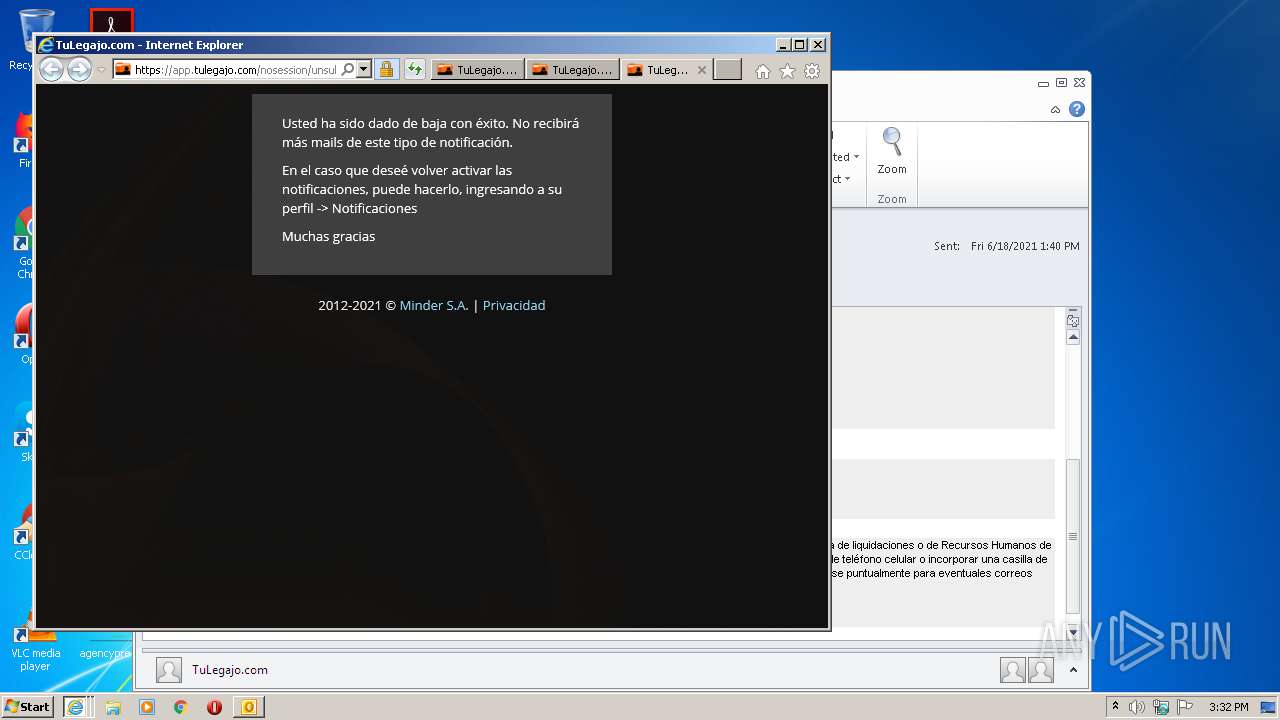
3920 | iexplore.exe | 44.228.164.23:443 | app.tulegajo.com | University of California, San Diego | US | unknown |
1312 | OUTLOOK.EXE | 13.224.193.39:443 | cdn1.reciboselectronicos.com | — | US | unknown |
3920 | iexplore.exe | 13.224.194.172:80 | o.ss2.us | — | US | suspicious |
3964 | iexplore.exe | 44.228.164.23:443 | app.tulegajo.com | University of California, San Diego | US | unknown |
— | — | 143.204.101.124:80 | ocsp.rootg2.amazontrust.com | — | US | whitelisted |
— | — | 143.204.101.123:80 | o.ss2.us | — | US | malicious |
3920 | iexplore.exe | 13.224.194.68:80 | ocsp.rootca1.amazontrust.com | — | US | whitelisted |
3920 | iexplore.exe | 52.218.221.40:443 | s3-us-west-2.amazonaws.com | Amazon.com, Inc. | US | unknown |
3920 | iexplore.exe | 142.250.74.202:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
cdn1.reciboselectronicos.com |
| suspicious |
app.tulegajo.com |
| unknown |
o.ss2.us |
| whitelisted |
ocsp.rootg2.amazontrust.com |
| whitelisted |
ocsp.rootca1.amazontrust.com |
| shared |
ocsp.sca1b.amazontrust.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
cdn1.tulegajo.com |
| malicious |
s3-us-west-2.amazonaws.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1060 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |