| URL: | https://cutt.ly/7RKqkKv |
| Full analysis: | https://app.any.run/tasks/54e1d0d8-745c-4347-a283-014bf5e7a675 |
| Verdict: | Malicious activity |
| Analysis date: | September 26, 2023, 13:11:46 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | C7C69EDBF88C99C2A2AAFFE5F48B73F6 |
| SHA1: | 5C362BF19E829067274E4A646B9EEBD881321A7B |
| SHA256: | B3E7572ADB0F21701644AD971A366D5AC5723423F3A6BBF759673630B420078A |
| SSDEEP: | 3:N8NRYKEuUl:24 |
MALICIOUS
Application was dropped or rewritten from another process
- HostBlock.exe (PID: 3984)
- HostBlock.exe (PID: 3408)
SUSPICIOUS
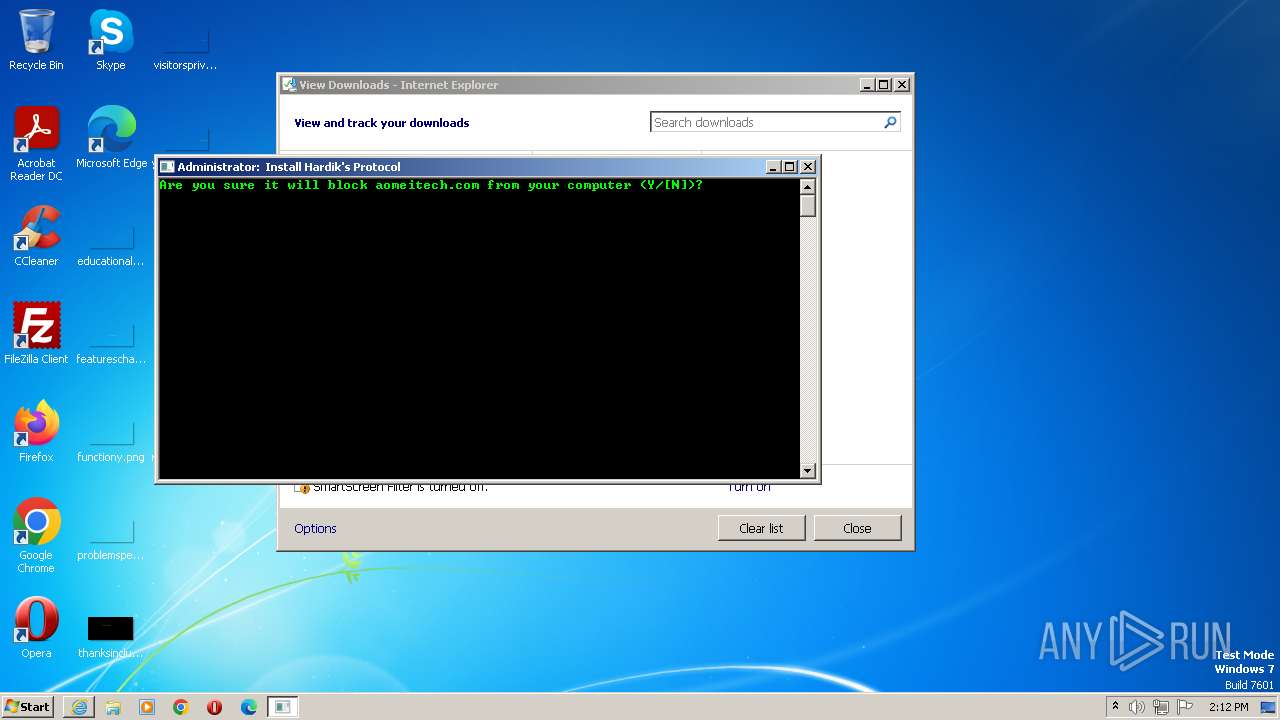
Executing commands from a ".bat" file
- HostBlock.exe (PID: 3408)
Starts CMD.EXE for commands execution
- HostBlock.exe (PID: 3408)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 3372)
INFO
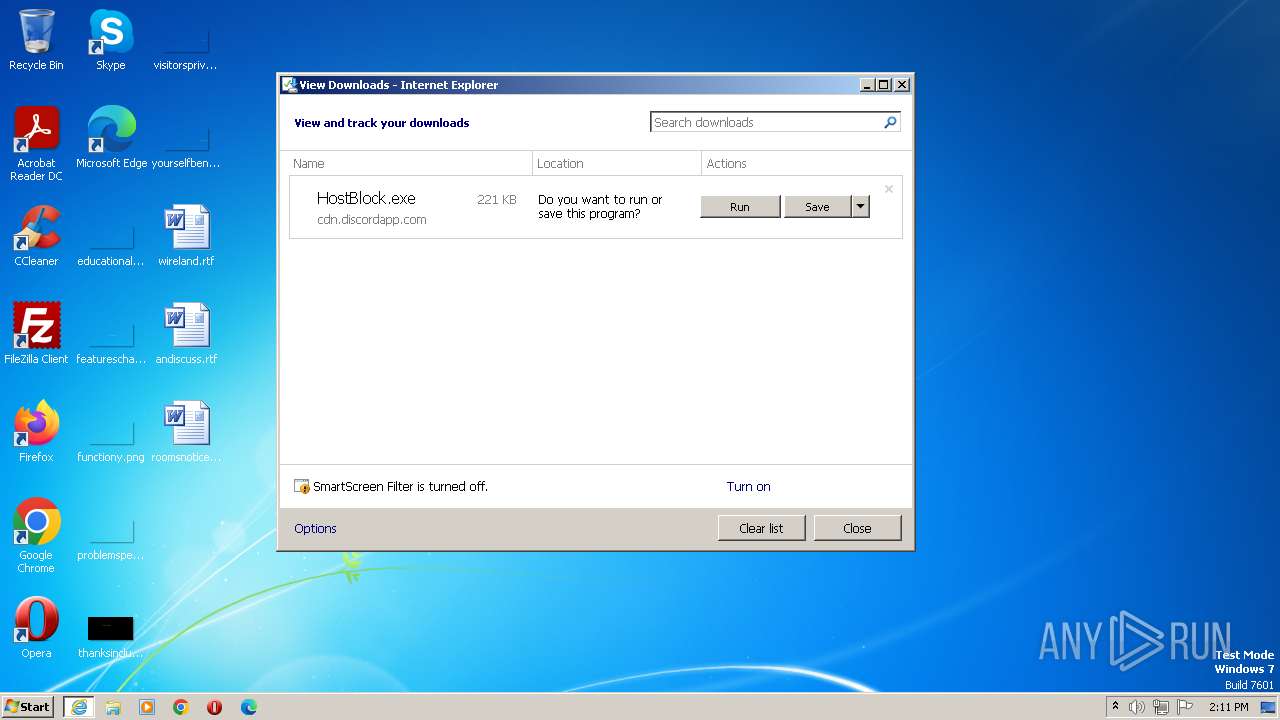
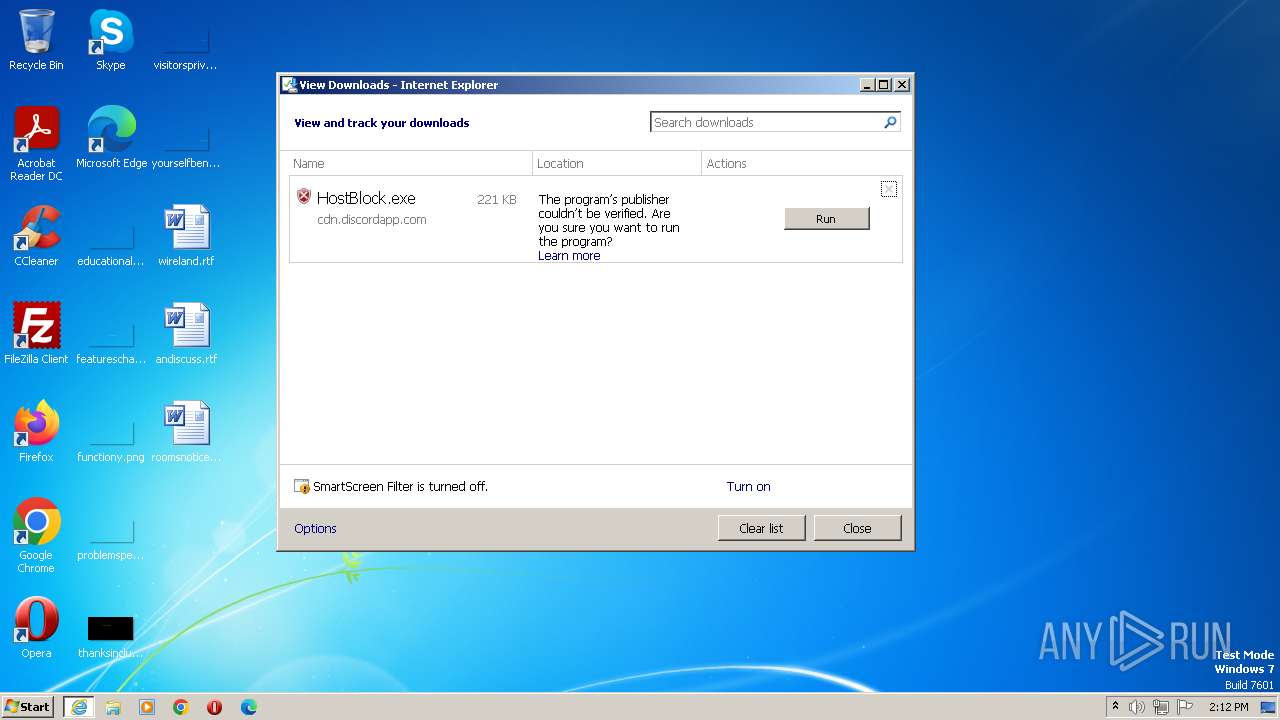
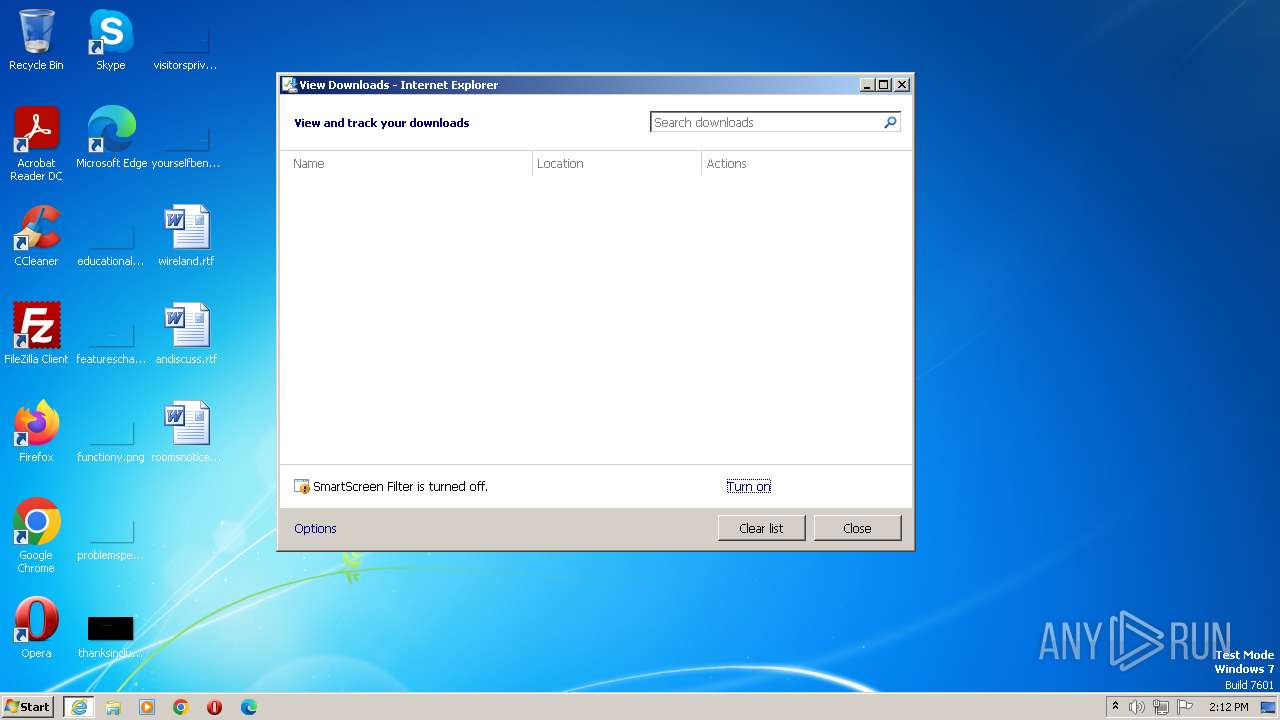
The process uses the downloaded file
- iexplore.exe (PID: 3484)
- chrome.exe (PID: 648)
- chrome.exe (PID: 3316)
Checks supported languages
- HostBlock.exe (PID: 3408)
Application launched itself
- iexplore.exe (PID: 3484)
- chrome.exe (PID: 2460)
Create files in a temporary directory
- HostBlock.exe (PID: 3408)
Manual execution by a user
- explorer.exe (PID: 3240)
- chrome.exe (PID: 2460)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
68
Monitored processes
28
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 648 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=4028 --field-trial-handle=1148,i,1449532708432807446,674941819858144093,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 856 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1416 --field-trial-handle=1148,i,1449532708432807446,674941819858144093,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
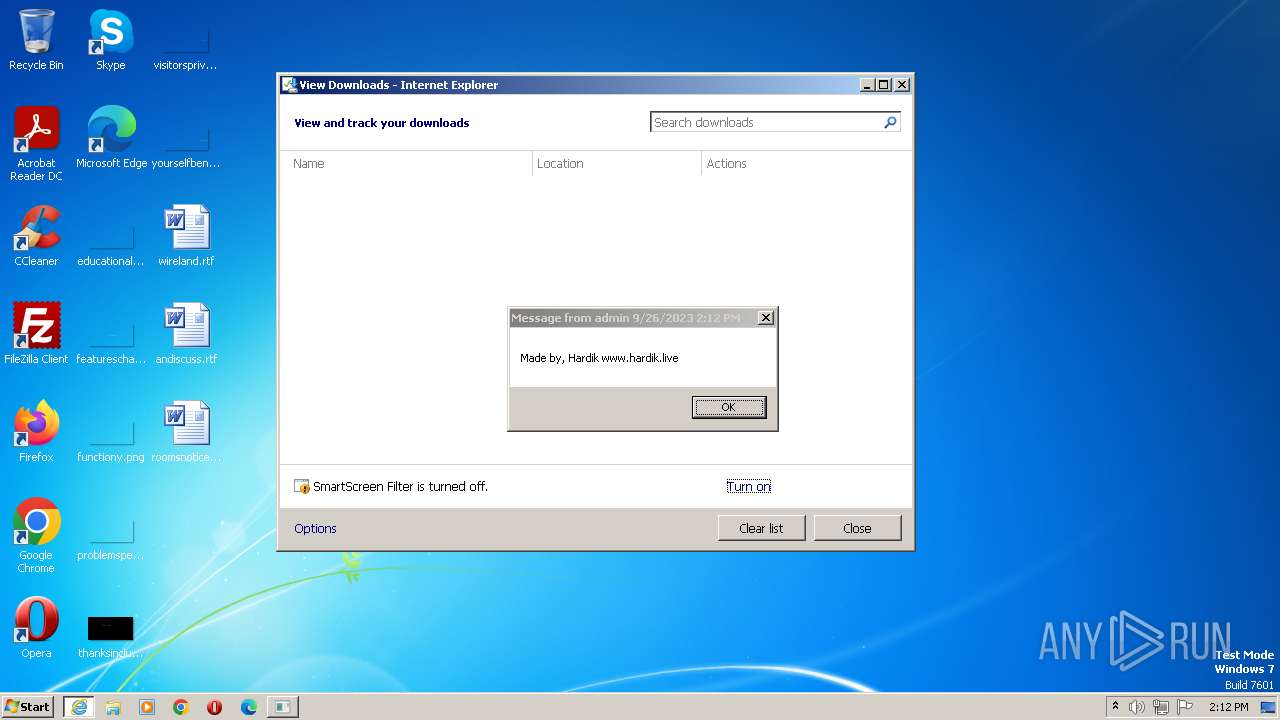
| 952 | msg admin Made by, Hardik www.hardik.live | C:\Windows\System32\msg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Message Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1036 | Reg.exe add "HKCR\Hardik" /v "Url Protocol" /t REG_SZ /d "https://hardik.live" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1700 | Reg.exe query "HKU\S-1-5-19\Environment" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1764 | Reg.exe add "HKCR\Hardik\shell" /ve /t REG_SZ /d "URL:hardik Protocol" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1952 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=2116 --field-trial-handle=1148,i,1449532708432807446,674941819858144093,131072 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2340 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=109.0.5414.120 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6d2b8b38,0x6d2b8b48,0x6d2b8b54 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2372 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3484 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2408 | Reg.exe add "HKCR\Hardik\shell\open\Command" /ve /t REG_SZ /d "powershell.exe \"rundll32 url.dll,FileProtocolHandler https://hardik.live\"" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
14 190
Read events
14 097
Write events
92
Delete events
1
Modification events
| (PID) Process: | (3484) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (3484) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (3484) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (3484) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3484) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3484) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3484) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3484) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3484) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3484) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
3
Suspicious files
36
Text files
34
Unknown types
1
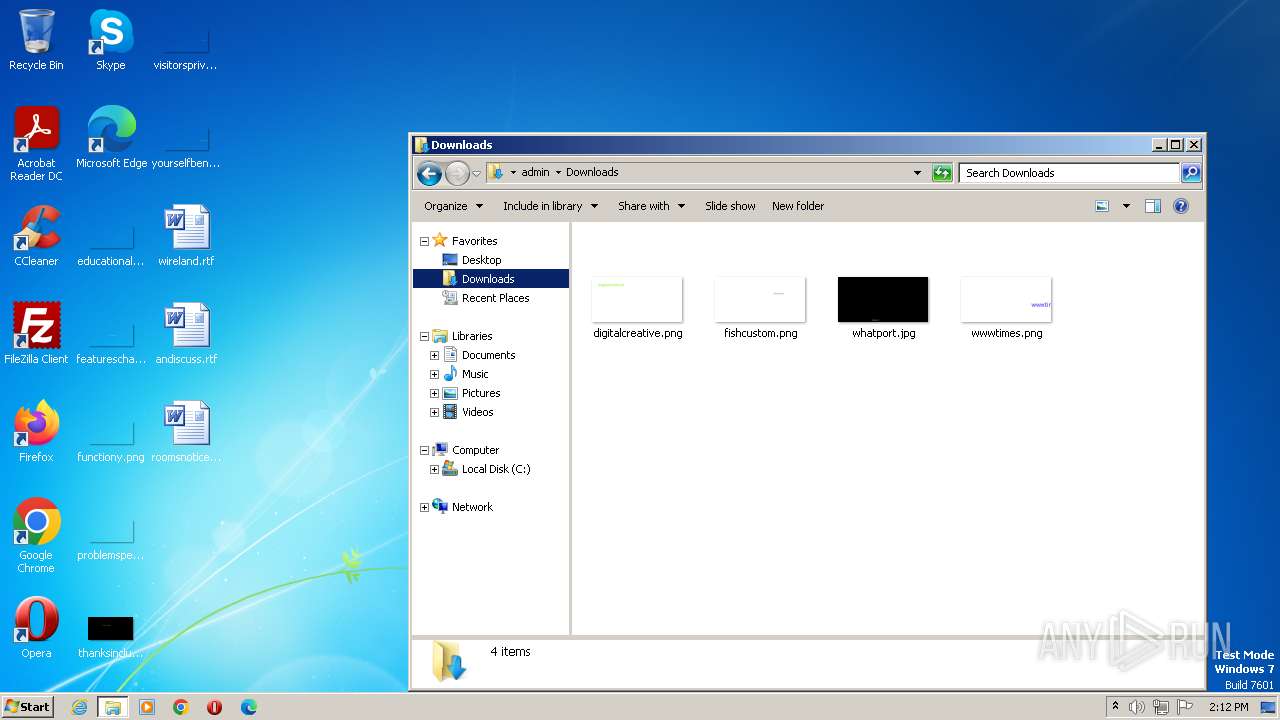
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3484 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{42796419-5C6E-11EE-ACBF-12A9866C77DE}.dat | binary | |
MD5:D467C9DDED99329A3B118B8556FDA38A | SHA256:EB91EB3DF753C84D30A56AED8B1EA1A0E0644769BBB0FF73A8C42B6FEEA2278B | |||
| 2460 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF101407.TMP | — | |
MD5:— | SHA256:— | |||
| 2460 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2372 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\HostBlock[1].exe | executable | |
MD5:A6C037F789C4715F9400B3C399583A45 | SHA256:907D00583196A9028621C729F9EDA3BCF1AA890B69B6792ED0B9697901E867FF | |||
| 2372 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_430EA0912164D1B129D6E1DC07C63959 | binary | |
MD5:7CAAB75E08B352ED8BAA17DBE88309F7 | SHA256:197757AE4ED598FB0C399A3E05B9C4AC2547DE6C23DCC717B021C6CCD962BE4B | |||
| 3484 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\HostBlock.exe.bmkzji1.partial:Zone.Identifier | text | |
MD5:FBCCF14D504B7B2DBCB5A5BDA75BD93B | SHA256:EACD09517CE90D34BA562171D15AC40D302F0E691B439F91BE1B6406E25F5913 | |||
| 2460 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF101436.TMP | text | |
MD5:D5C9ECBD2DCA29D89266782824D7AF99 | SHA256:D22D1243ACC064A30823180D0E583C853E9395367C78C2AD9DE59A463904F702 | |||
| 2460 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\69f501eb-6bae-485d-9530-93aa6f92c8d0.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 3372 | cmd.exe | C:\Windows\System32\drivers\etc\hosts | text | |
MD5:F2E1CE677999A7DA7BF25742CE588F9A | SHA256:8250D6FADCB2962239BABC336B58CF06040102E4993C637DDC1484E7A75B0AE3 | |||
| 2372 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\955R81JG.txt | text | |
MD5:7157E96E256F2C73F2EBC3D5DF21BD59 | SHA256:2C36FEDC5B6EEA9DDABC7315515D1630E2C67AE16BEC0745C798071CEB6FF8C6 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
19
DNS requests
14
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2372 | iexplore.exe | GET | 200 | 8.253.207.120:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?d3a29e5f0beeb90c | unknown | compressed | 4.66 Kb | unknown |
2372 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | unknown | der | 1.47 Kb | unknown |
2372 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA0HeCoTP8b5pXKW4TH%2F0Xk%3D | unknown | der | 471 b | unknown |
2372 | iexplore.exe | GET | 200 | 8.253.207.120:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?6b7d3d28ce4cf84a | unknown | compressed | 4.66 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2372 | iexplore.exe | 104.22.1.232:443 | cutt.ly | CLOUDFLARENET | — | unknown |
3284 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2372 | iexplore.exe | 8.253.207.120:80 | ctldl.windowsupdate.com | LEVEL3 | US | unknown |
2372 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
2372 | iexplore.exe | 162.159.130.233:443 | cdn.discordapp.com | CLOUDFLARENET | — | shared |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
856 | chrome.exe | 142.250.186.131:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
2460 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
856 | chrome.exe | 142.250.185.141:443 | accounts.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cutt.ly |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
cdn.discordapp.com |
| shared |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
optimizationguide-pa.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1088 | svchost.exe | Misc activity | ET INFO URL Shortener Service Domain in DNS Lookup (cutt .ly) |
2372 | iexplore.exe | Misc activity | ET INFO Observed URL Shortener Service Domain (cutt .ly in TLS SNI) |
2372 | iexplore.exe | Misc activity | ET INFO Observed URL Shortener Service Domain (cutt .ly in TLS SNI) |
1088 | svchost.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discordapp .com) |
2372 | iexplore.exe | Misc activity | ET INFO Observed Discord Domain (discordapp .com in TLS SNI) |
2372 | iexplore.exe | Misc activity | ET INFO Observed Discord Domain (discordapp .com in TLS SNI) |