| File name: | ipts.exe |
| Full analysis: | https://app.any.run/tasks/4a23c239-ef97-43e4-8a28-50fb09bb7474 |
| Verdict: | No threats detected |
| Analysis date: | April 25, 2020, 20:27:13 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 65714499E3AC6CA88250BD788D544D2C |
| SHA1: | 7BACBD736A45450981B2B02045D18139D4D6FBC6 |
| SHA256: | B3E6261864A914A95201E31319EAB0A631F8AFA6AD29D6E84FA54A66627682AC |
| SSDEEP: | 24576:lOt5ugSbeSpotiwGR6943mopVTt89hT0iOnkr7:euWC7Ty9hT0Znkr7 |
MALICIOUS
No malicious indicators.SUSPICIOUS
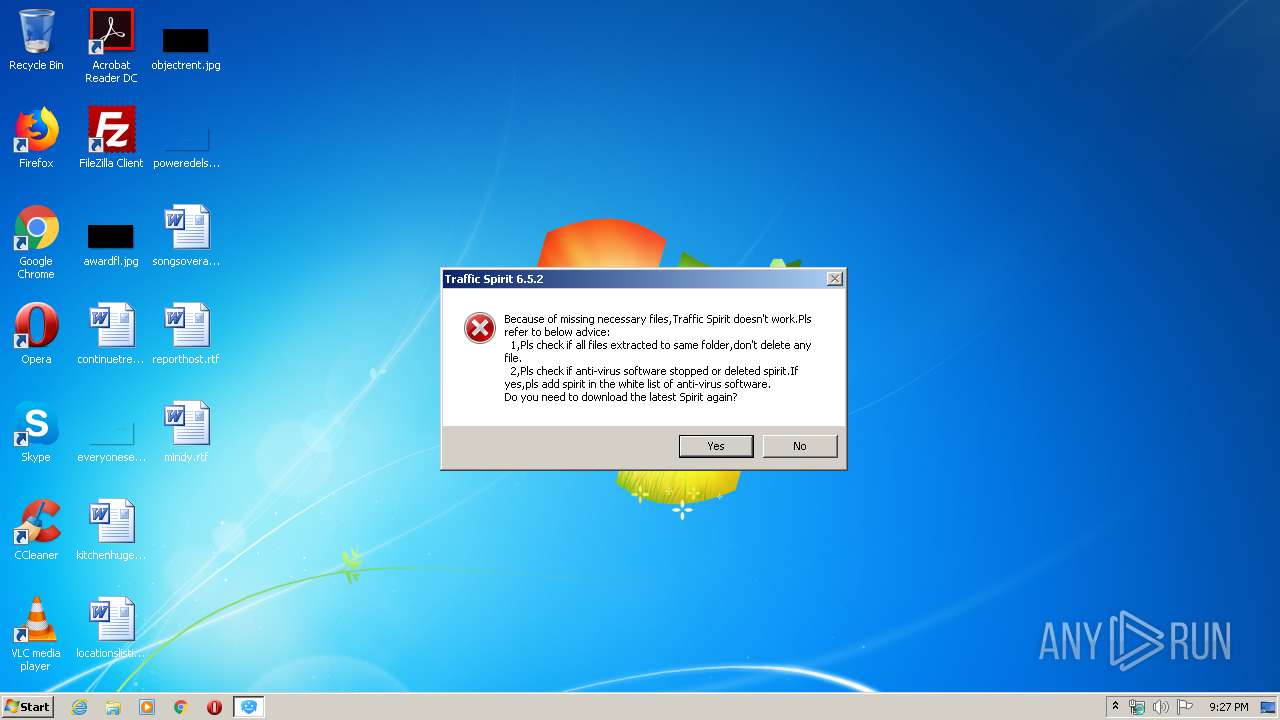
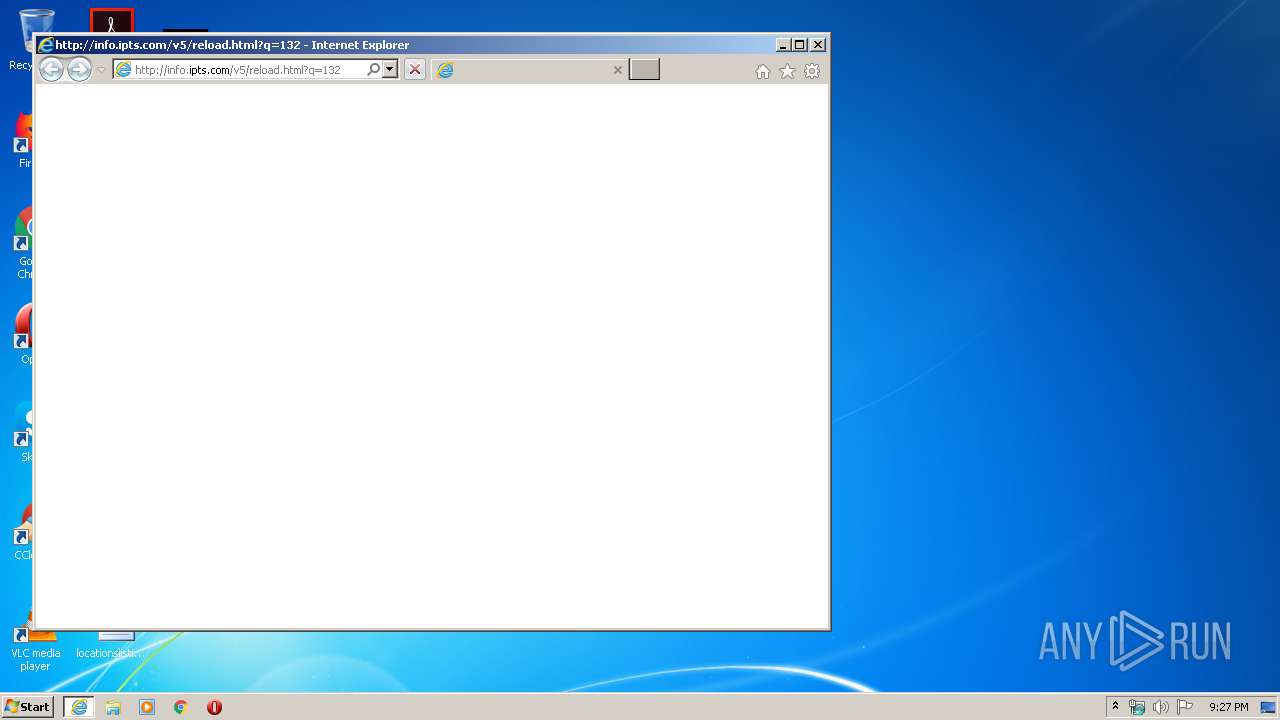
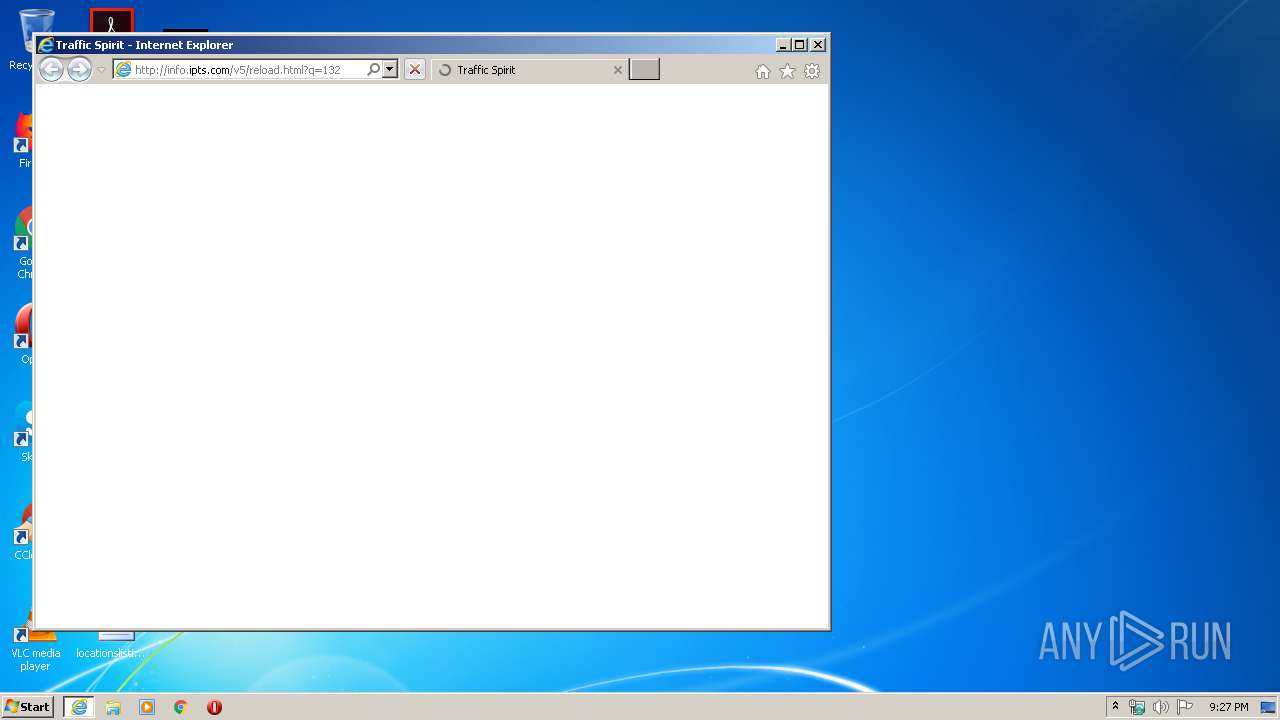
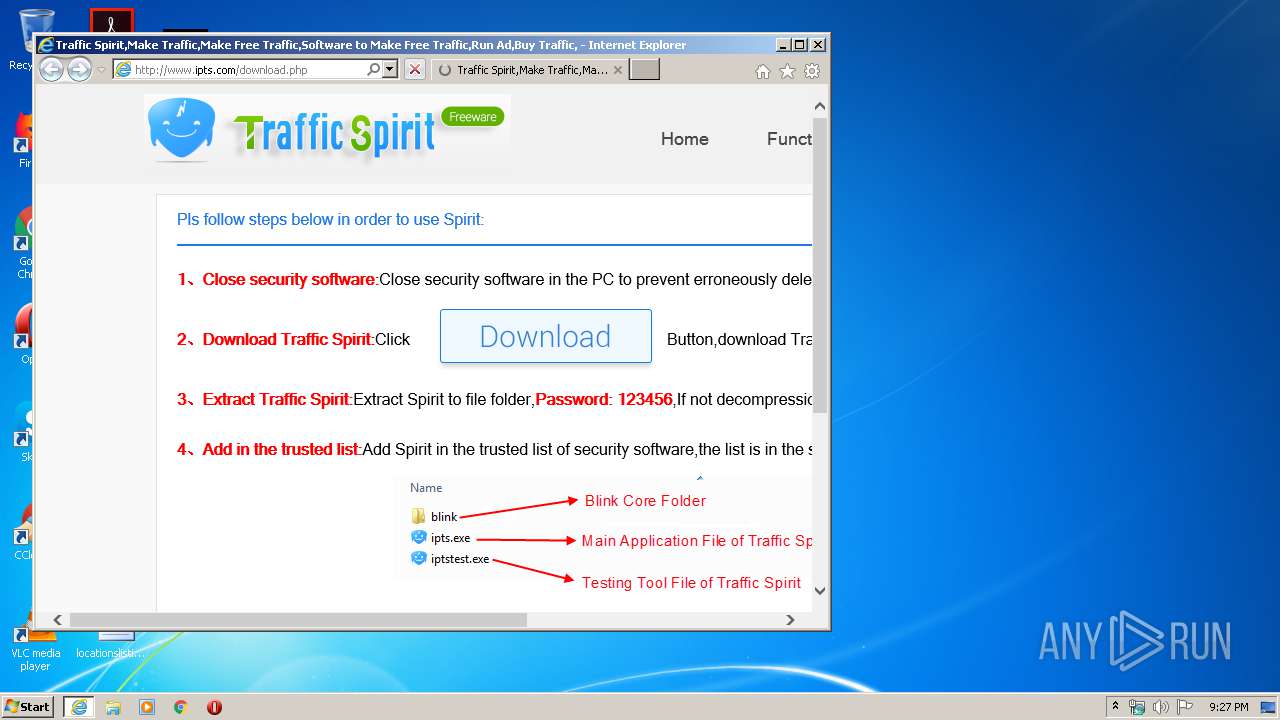
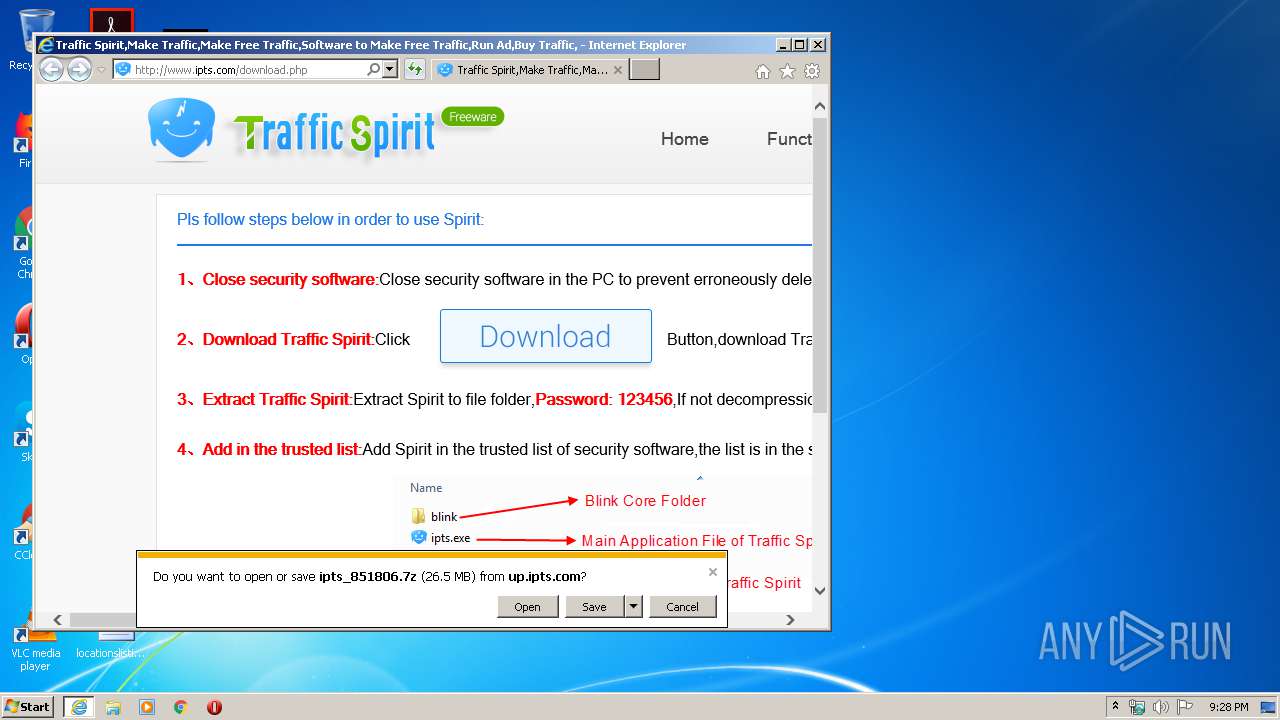
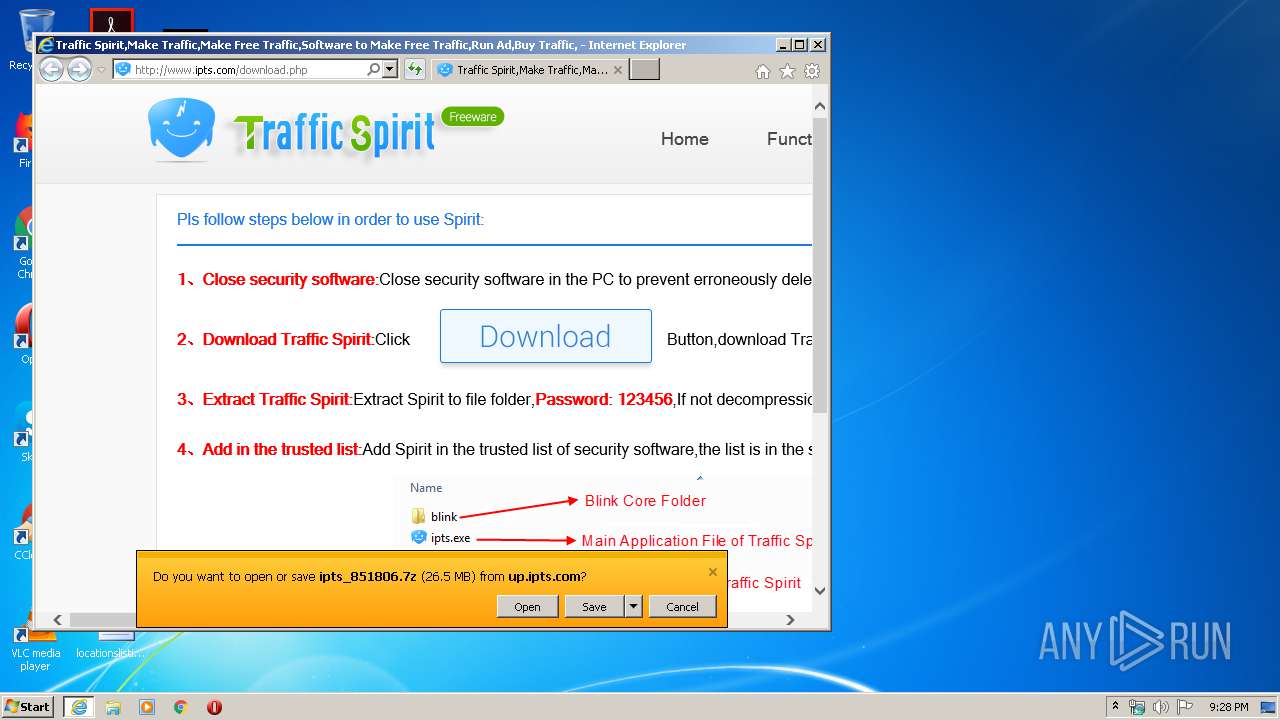
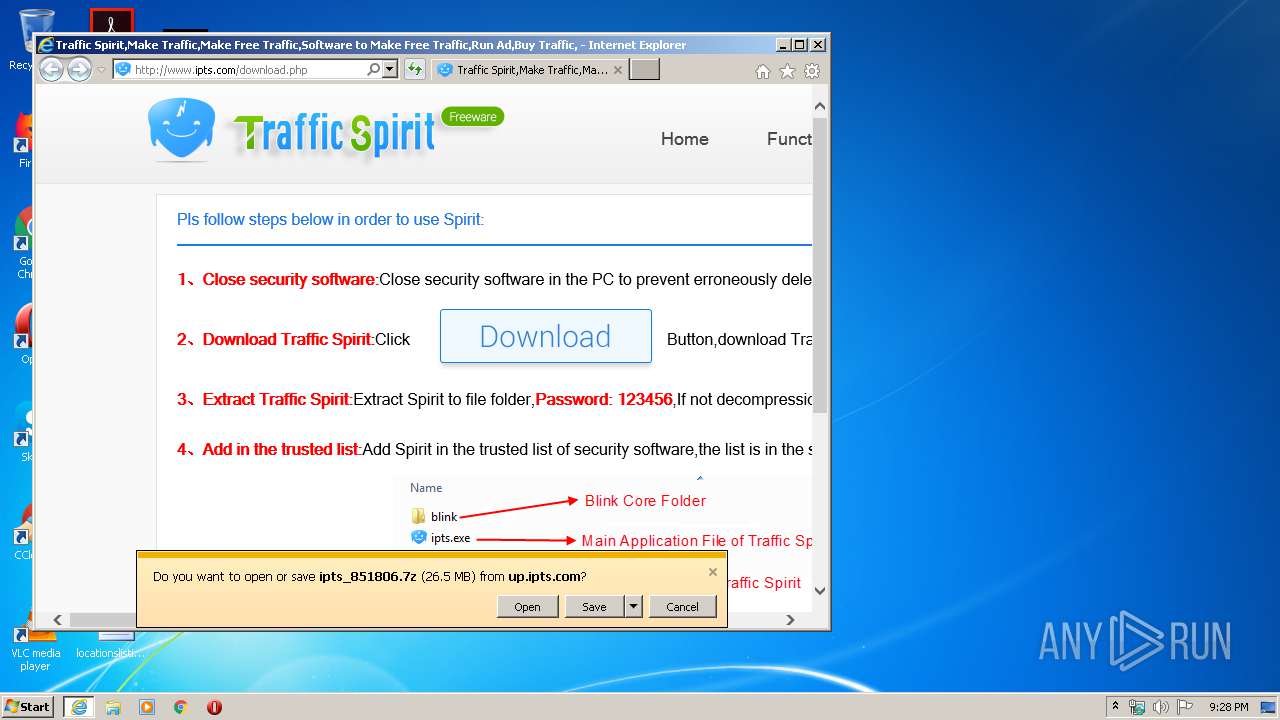
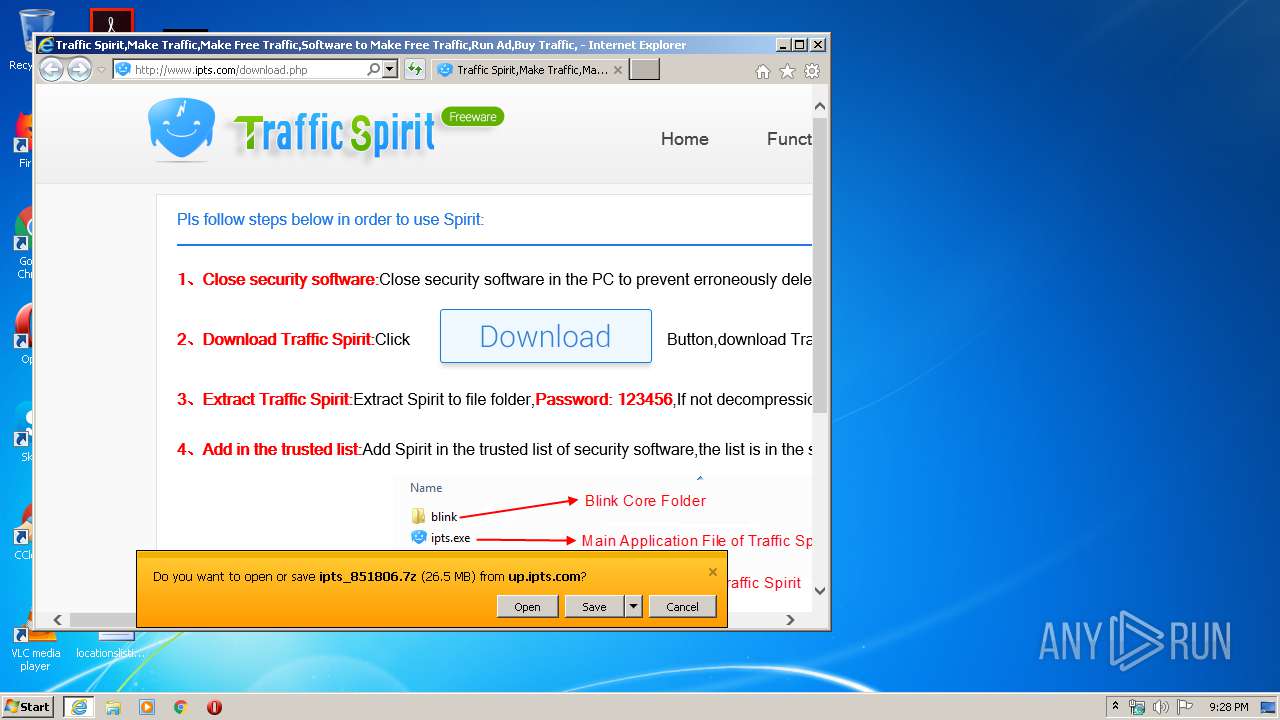
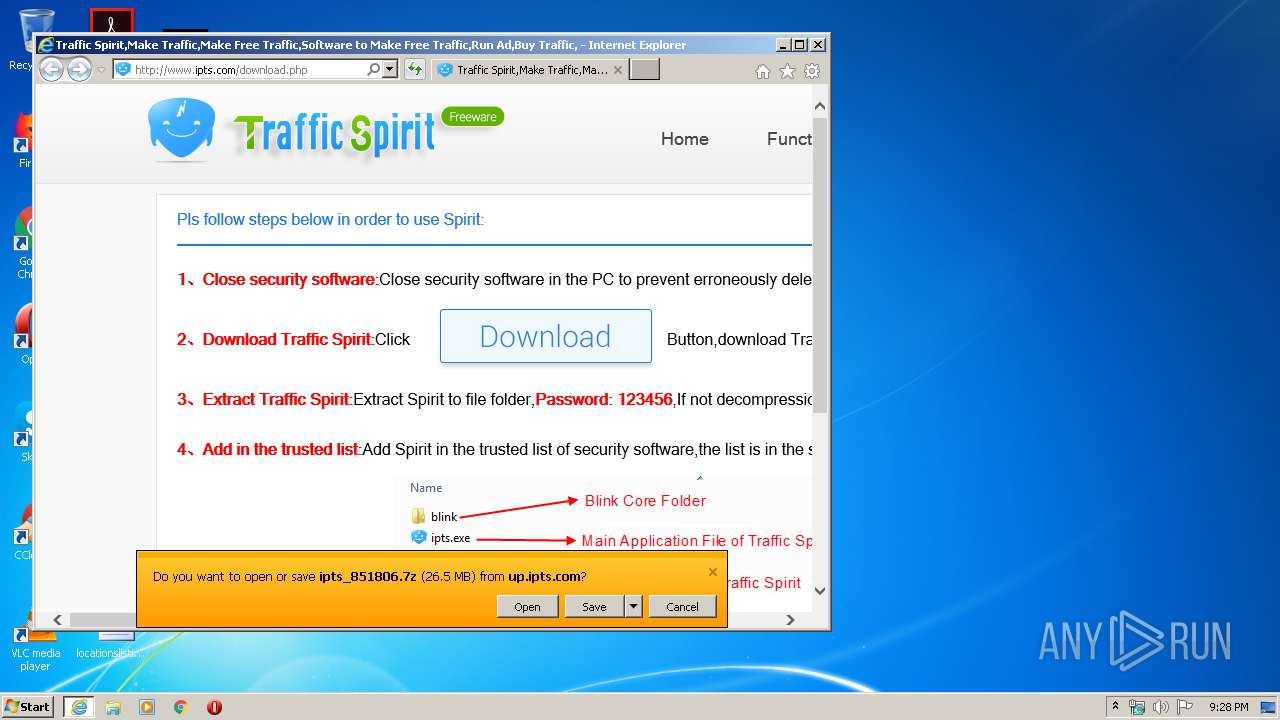
Starts Internet Explorer
- ipts.exe (PID: 3004)
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 3316)
- iexplore.exe (PID: 1504)
Reads internet explorer settings
- iexplore.exe (PID: 1504)
Modifies the phishing filter of IE
- iexplore.exe (PID: 3316)
Creates files in the user directory
- iexplore.exe (PID: 3316)
- iexplore.exe (PID: 1504)
Changes internet zones settings
- iexplore.exe (PID: 3316)
Reads settings of System Certificates
- iexplore.exe (PID: 3316)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3316)
Changes settings of System certificates
- iexplore.exe (PID: 3316)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:11:25 06:21:51+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 697856 |
| InitializedDataSize: | 396288 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x7bfab |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2019.11.25.35 |
| ProductVersionNumber: | 6.5.2.35 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| Comments: | Traffic Spirit(35) |
| CompanyName: | Spiritsoft |
| FileDescription: | Traffic Spirit |
| FileVersion: | 2019.11.25.35 |
| InternalName: | ipts.exe |
| LegalCopyright: | Copyright 2016 Spiritsoft All Rights Reserved. |
| OriginalFileName: | ipts.exe |
| ProductName: | Traffic Spirit |
| ProductVersion: | 6.5.2.35 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 25-Nov-2019 05:21:51 |
| Detected languages: |
|
| TLS Callbacks: | 1 callback(s) detected. |
| Debug artifacts: |
|
| Comments: | Traffic Spirit(35) |
| CompanyName: | Spiritsoft |
| FileDescription: | Traffic Spirit |
| FileVersion: | 2019.11.25.35 |
| InternalName: | ipts.exe |
| LegalCopyright: | Copyright 2016 Spiritsoft All Rights Reserved. |
| OriginalFilename: | ipts.exe |
| ProductName: | Traffic Spirit |
| ProductVersion: | 6.5.2.35 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000128 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 7 |
| Time date stamp: | 25-Nov-2019 05:21:51 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000AA451 | 0x000AA600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.56653 |
.rdata | 0x000AC000 | 0x0003A484 | 0x0003A600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.28048 |
.data | 0x000E7000 | 0x00006260 | 0x00003200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.48559 |
.gfids | 0x000EE000 | 0x000002B8 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.98199 |
.tls | 0x000EF000 | 0x00000009 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.0203931 |
.rsrc | 0x000F0000 | 0x00016070 | 0x00016200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.90246 |
.reloc | 0x00107000 | 0x000098AC | 0x00009A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.60637 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.11982 | 803 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 4.07757 | 9640 | UNKNOWN | Chinese - PRC | RT_ICON |
3 | 4.29496 | 4264 | UNKNOWN | Chinese - PRC | RT_ICON |
4 | 4.5289 | 1128 | UNKNOWN | Chinese - PRC | RT_ICON |
5 | 5.58307 | 1128 | UNKNOWN | Chinese - PRC | RT_ICON |
6 | 5.20352 | 1128 | UNKNOWN | Chinese - PRC | RT_ICON |
7 | 5.03695 | 1128 | UNKNOWN | Chinese - PRC | RT_ICON |
8 | 5.26154 | 1128 | UNKNOWN | Chinese - PRC | RT_ICON |
9 | 3.5995 | 1728 | UNKNOWN | Chinese - PRC | RT_STRING |
10 | 3.48705 | 2496 | UNKNOWN | Chinese - PRC | RT_STRING |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
IPHLPAPI.DLL |
KERNEL32.dll |
OLEAUT32.dll |
PSAPI.DLL |
RPCRT4.dll |
SHELL32.dll |
SHLWAPI.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
GetHandleVerifier | 1 | 0x00005620 |
IsSandboxedProcess | 2 | 0x000622C8 |
Total processes
37
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1504 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3316 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3004 | "C:\Users\admin\AppData\Local\Temp\ipts.exe" | C:\Users\admin\AppData\Local\Temp\ipts.exe | — | explorer.exe | |||||||||||
User: admin Company: Spiritsoft Integrity Level: MEDIUM Description: Traffic Spirit Exit code: 6 Version: 2019.11.25.35 Modules
| |||||||||||||||
| 3316 | "C:\Program Files\Internet Explorer\iexplore.exe" http://info.ipts.com/v5/reload.html?q=132 | C:\Program Files\Internet Explorer\iexplore.exe | ipts.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
7 709
Read events
949
Write events
4 516
Delete events
2 244
Modification events
| (PID) Process: | (3316) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 234856034 | |||
| (PID) Process: | (3316) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30808896 | |||
| (PID) Process: | (3316) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3316) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3316) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3004) ipts.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {17FE9752-0B5A-4665-84CD-569794602F5C} {7F9185B0-CB92-43C5-80A9-92277A4F7B54} 0xFFFF |
Value: 0100000000000000DE2306FC3F1BD601 | |||
| (PID) Process: | (3316) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3316) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3316) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3316) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
14
Text files
22
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1504 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\core[1].js | html | |
MD5:— | SHA256:— | |||
| 3316 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 1504 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\MSIMGSIZ.DAT | smt | |
MD5:— | SHA256:— | |||
| 1504 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\file[1].png | image | |
MD5:— | SHA256:— | |||
| 3316 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF938EF5394B92CF9E.TMP | — | |
MD5:— | SHA256:— | |||
| 1504 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\JC0RY2IR.txt | text | |
MD5:— | SHA256:— | |||
| 1504 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\B47TOH0Q.txt | text | |
MD5:— | SHA256:— | |||
| 1504 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\z_stat[1].js | text | |
MD5:— | SHA256:— | |||
| 3316 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Cab3789.tmp | — | |
MD5:— | SHA256:— | |||
| 3316 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Tar378A.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
23
TCP/UDP connections
32
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1504 | iexplore.exe | GET | — | 47.88.65.155:80 | http://up.ipts.com/v5/ipts_851806.7z | US | — | — | unknown |
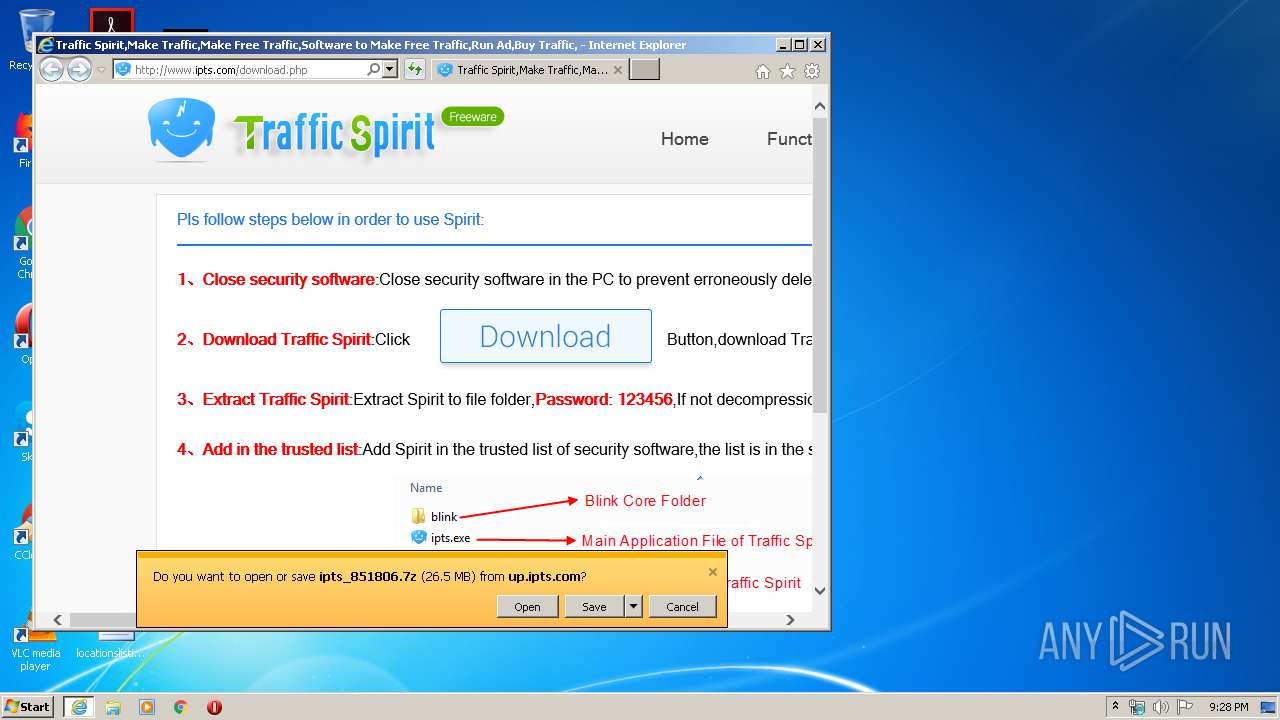
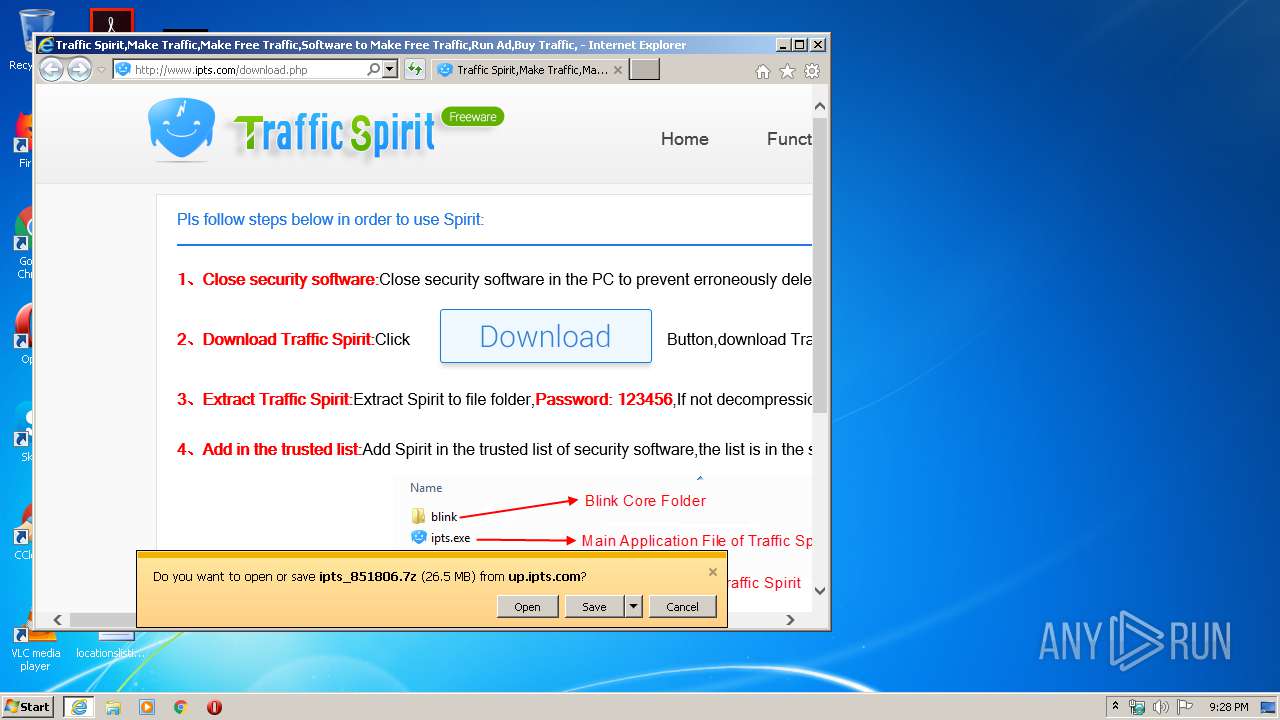
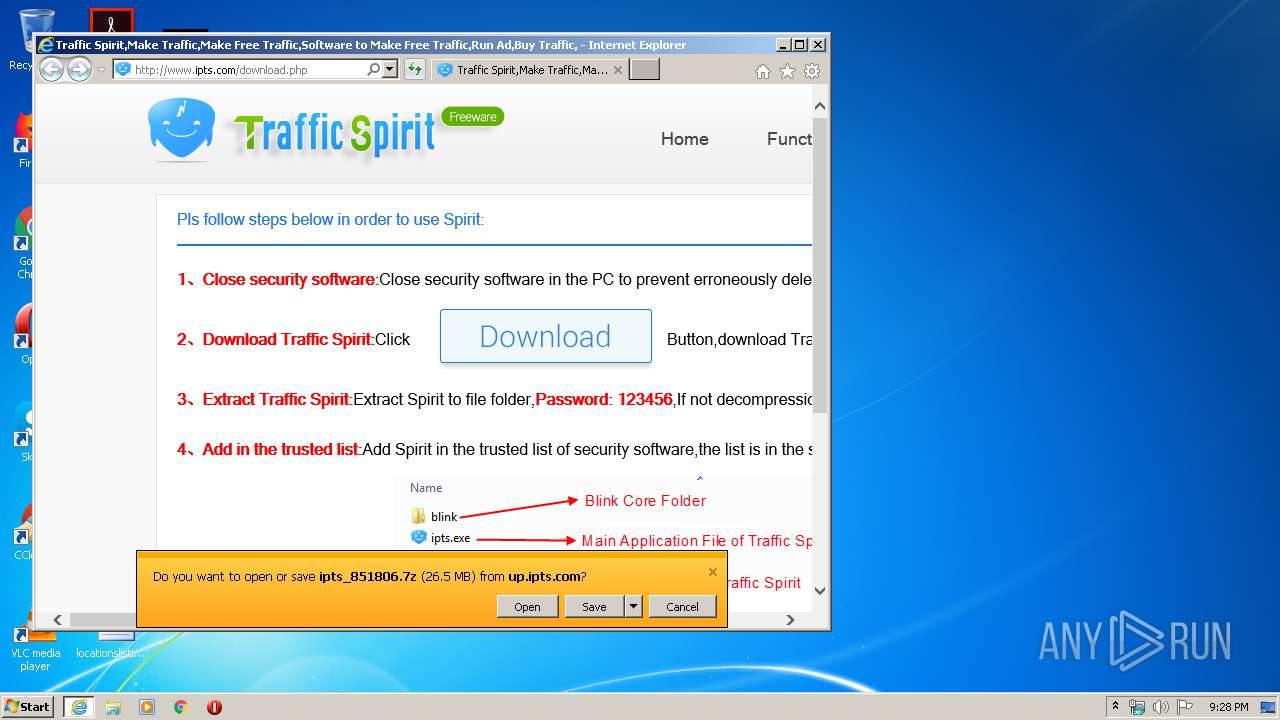
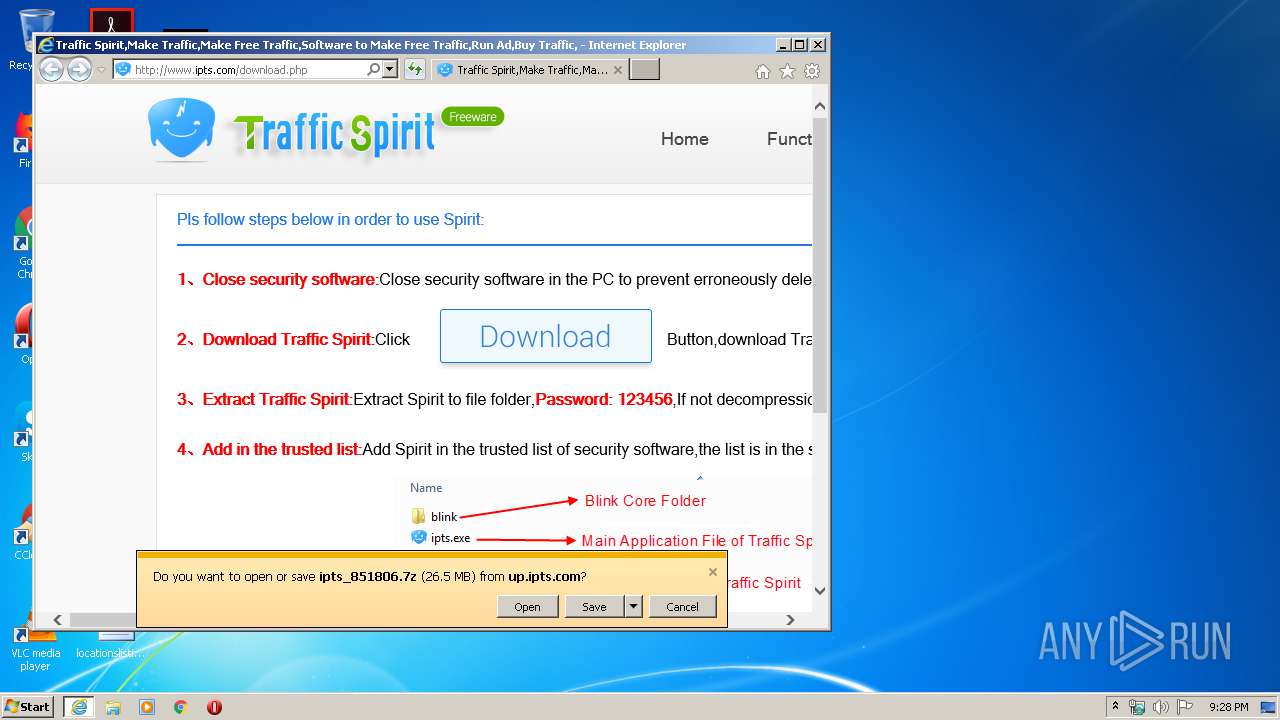
1504 | iexplore.exe | GET | 200 | 198.11.168.38:80 | http://www.ipts.com/download.php | US | html | 2.58 Kb | malicious |
1504 | iexplore.exe | GET | 200 | 198.11.168.38:80 | http://www.ipts.com/images/file.png | US | image | 9.87 Kb | malicious |
1504 | iexplore.exe | GET | 200 | 101.89.124.234:80 | http://s4.cnzz.com/z_stat.php?id=1255129158 | CN | text | 3.99 Kb | whitelisted |
1504 | iexplore.exe | GET | 200 | 101.89.124.234:80 | http://c.cnzz.com/core.php?web_id=1255129158&t=z | CN | html | 621 b | whitelisted |
3316 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
3316 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
1504 | iexplore.exe | GET | 200 | 198.11.168.38:80 | http://www.ipts.com/style/style.css | US | text | 521 b | malicious |
1504 | iexplore.exe | GET | 200 | 198.11.168.38:80 | http://www.ipts.com/images/xz_down.png | US | image | 3.30 Kb | malicious |
1504 | iexplore.exe | GET | 200 | 198.11.168.38:80 | http://www.ipts.com/images/xz_hover.png | US | image | 3.17 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1504 | iexplore.exe | 198.11.168.38:80 | info.ipts.com | Alibaba (China) Technology Co., Ltd. | US | malicious |
1504 | iexplore.exe | 101.89.124.234:80 | s4.cnzz.com | China Telecom (Group) | CN | unknown |
1504 | iexplore.exe | 203.119.215.3:80 | z11.cnzz.com | — | CN | unknown |
1504 | iexplore.exe | 198.11.132.221:80 | cnzz.mmstat.com | Alibaba (China) Technology Co., Ltd. | US | suspicious |
1504 | iexplore.exe | 106.11.92.15:80 | pcookie.cnzz.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | suspicious |
3316 | iexplore.exe | 198.11.168.38:80 | info.ipts.com | Alibaba (China) Technology Co., Ltd. | US | malicious |
3316 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
1504 | iexplore.exe | 47.88.65.155:80 | up.ipts.com | Alibaba (China) Technology Co., Ltd. | US | unknown |
3316 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
— | — | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
info.ipts.com |
| malicious |
www.ipts.com |
| malicious |
s4.cnzz.com |
| whitelisted |
z11.cnzz.com |
| whitelisted |
c.cnzz.com |
| whitelisted |
cnzz.mmstat.com |
| whitelisted |
www.bing.com |
| whitelisted |
api.bing.com |
| whitelisted |
pcookie.cnzz.com |
| whitelisted |
up.ipts.com |
| unknown |