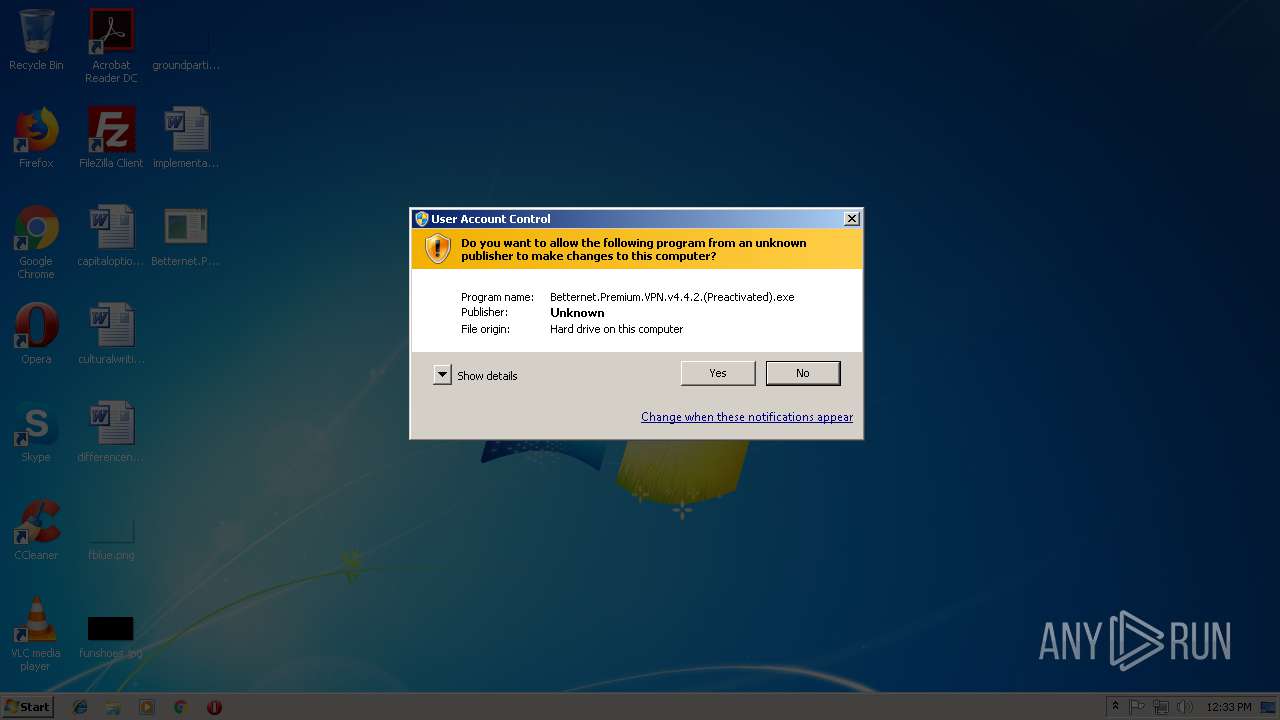
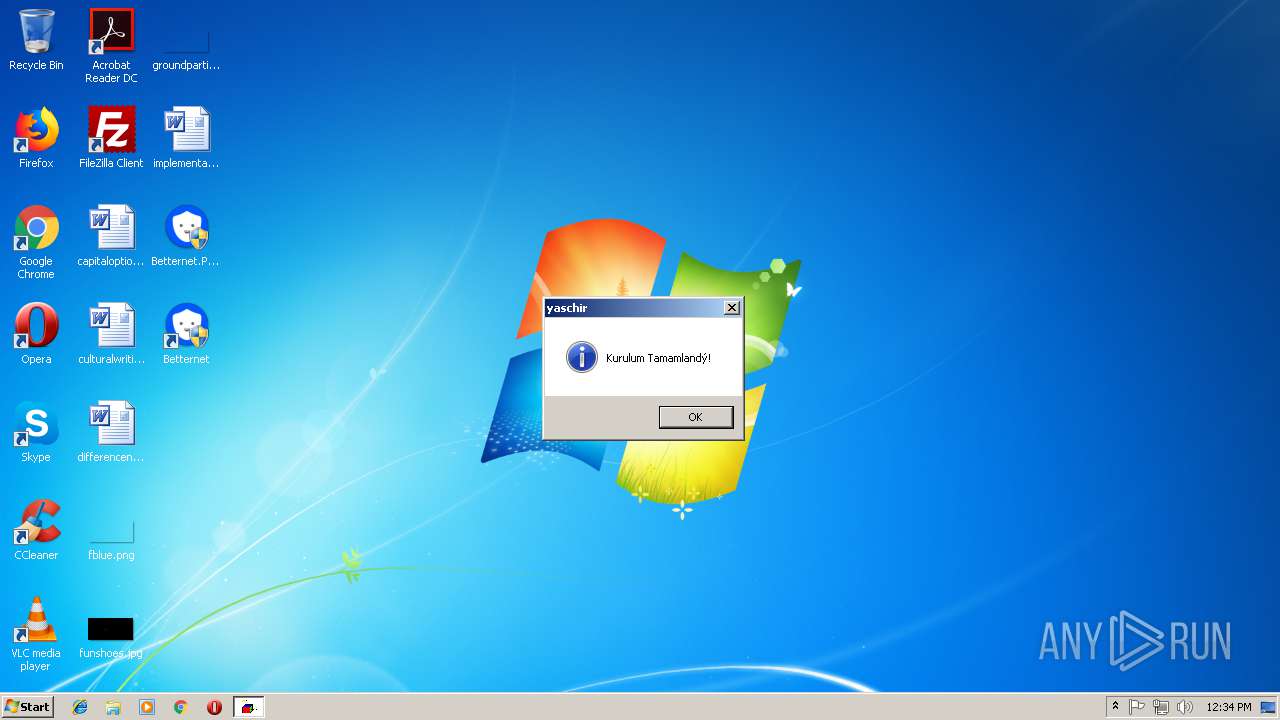
| File name: | Betternet.Premium.VPN.v4.4.2.(Preactivated).exe |
| Full analysis: | https://app.any.run/tasks/74954dd2-fbbc-47dc-af21-fbac226b53ea |
| Verdict: | Malicious activity |
| Analysis date: | November 14, 2018, 12:32:55 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 3D2E8F5A08CFAF4E5F52794F6E46D50F |
| SHA1: | 23085A570F4872700952B9E89737CEED12F04848 |
| SHA256: | B3DD53101B3D2150C6BE9A0EA8EFF63DCD2793D613484E9C56C69B709C2FFF4C |
| SSDEEP: | 98304:H96kQx+/fdAduuRpWHhE7pKtD0Vt92VXH1nqBgAeyQZMkSiShrQD+u9qS0QWnR:7w+Cgu3WHhEMV31SiMkSiShkJqS14 |
MALICIOUS
Changes settings of System certificates
- MsiExec.exe (PID: 3924)
- tapinstall.exe (PID: 944)
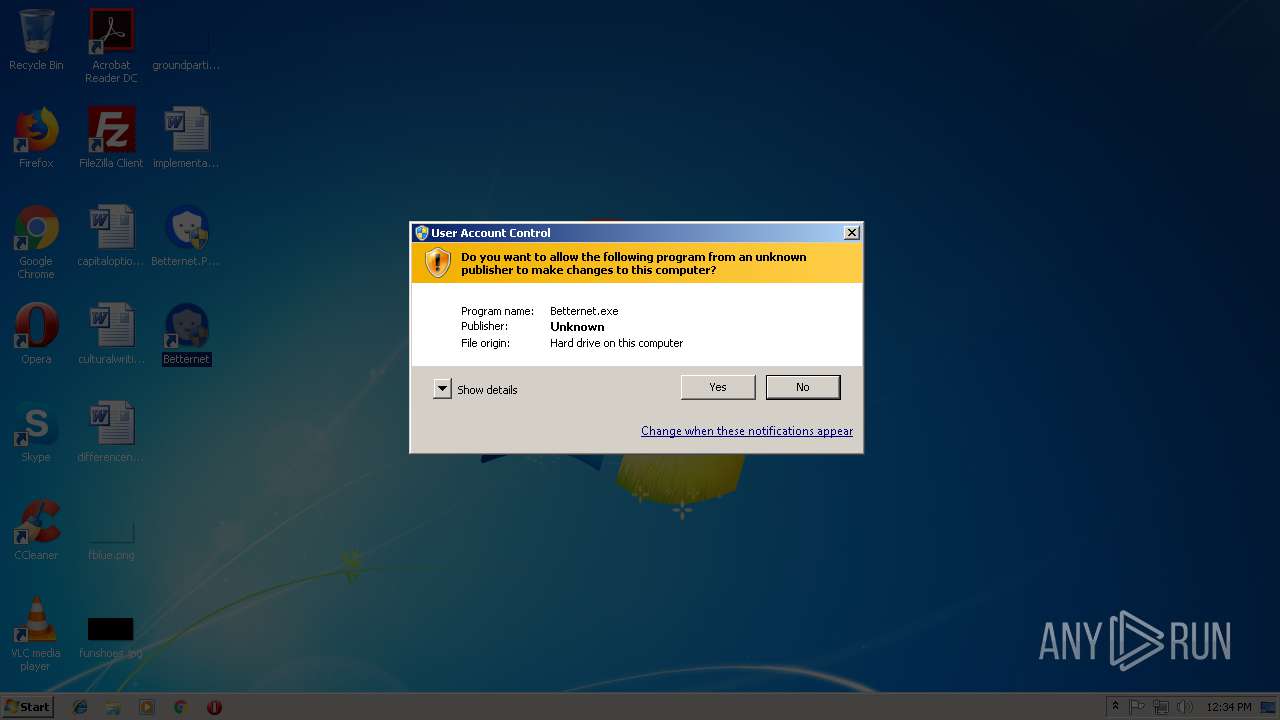
- Betternet.exe (PID: 2516)
Application was dropped or rewritten from another process
- tap-windows-9.21.2.exe (PID: 2448)
- nsF616.tmp (PID: 312)
- tapinstall.exe (PID: 3876)
- tapinstall.exe (PID: 944)
- nsEFDC.tmp (PID: 3552)
- Betternet.exe (PID: 3084)
- Betternet.exe (PID: 2516)
- hydra.exe (PID: 2828)
Loads dropped or rewritten executable
- tap-windows-9.21.2.exe (PID: 2448)
- hydra.exe (PID: 2828)
- Betternet.exe (PID: 2516)
SUSPICIOUS
Executable content was dropped or overwritten
- Betternet.Premium.VPN.v4.4.2.(Preactivated).exe (PID: 1016)
- msiexec.exe (PID: 3028)
- tap-windows-9.21.2.exe (PID: 2448)
- DrvInst.exe (PID: 1548)
- tapinstall.exe (PID: 944)
- DrvInst.exe (PID: 1968)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 3632)
Starts CMD.EXE for commands execution
- Betternet.Premium.VPN.v4.4.2.(Preactivated).exe (PID: 1016)
- WScript.exe (PID: 2692)
Starts Microsoft Installer
- cmd.exe (PID: 3812)
Executes scripts
- cmd.exe (PID: 3632)
- cmd.exe (PID: 3812)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 3812)
Modifies the open verb of a shell class
- msiexec.exe (PID: 3028)
Starts application with an unusual extension
- tap-windows-9.21.2.exe (PID: 2448)
Creates files in the driver directory
- DrvInst.exe (PID: 1968)
- DrvInst.exe (PID: 1548)
Searches for installed software
- DrvInst.exe (PID: 1968)
Removes files from Windows directory
- DrvInst.exe (PID: 1548)
- DrvInst.exe (PID: 1968)
Creates files in the Windows directory
- tapinstall.exe (PID: 944)
- DrvInst.exe (PID: 1968)
- DrvInst.exe (PID: 1548)
Creates or modifies windows services
- DrvInst.exe (PID: 1968)
- DrvInst.exe (PID: 1548)
Creates a software uninstall entry
- tap-windows-9.21.2.exe (PID: 2448)
Reads Environment values
- Betternet.exe (PID: 2516)
Adds / modifies Windows certificates
- Betternet.exe (PID: 2516)
Creates files in the program directory
- Betternet.exe (PID: 2516)
- tap-windows-9.21.2.exe (PID: 2448)
Reads the machine GUID from the registry
- Betternet.exe (PID: 2516)
Reads Internet Cache Settings
- Betternet.exe (PID: 2516)
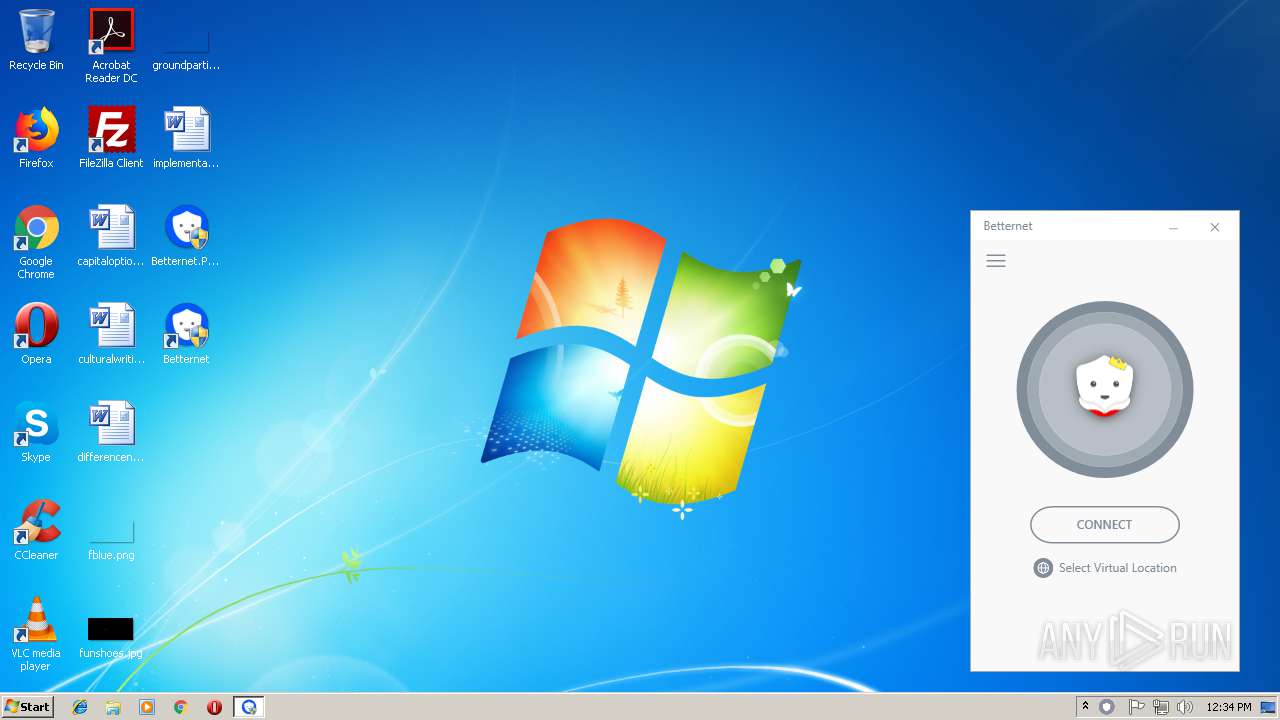
Checks for external IP
- Betternet.exe (PID: 2516)
INFO
Dropped object may contain Bitcoin addresses
- Betternet.Premium.VPN.v4.4.2.(Preactivated).exe (PID: 1016)
- msiexec.exe (PID: 3028)
Application launched itself
- msiexec.exe (PID: 3028)
Creates files in the program directory
- msiexec.exe (PID: 3028)
Creates a software uninstall entry
- msiexec.exe (PID: 3028)
Low-level read access rights to disk partition
- vssvc.exe (PID: 3704)
Reads settings of System Certificates
- Betternet.exe (PID: 2516)
Creates or modifies windows services
- vssvc.exe (PID: 3704)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:05:13 21:06:13+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 190464 |
| InitializedDataSize: | 309248 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1d489 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 13-May-2018 19:06:13 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 13-May-2018 19:06:13 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0002E774 | 0x0002E800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.70012 |
.rdata | 0x00030000 | 0x00009A8C | 0x00009C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.12809 |
.data | 0x0003A000 | 0x000203A0 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.22824 |
.gfids | 0x0005B000 | 0x000000E8 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.09173 |
.rsrc | 0x0005C000 | 0x0003EDE0 | 0x0003EE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.44703 |
.reloc | 0x0009B000 | 0x00001FD0 | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.6649 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.26192 | 1875 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.0143 | 304 | Latin 1 / Western European | Process Default Language | RT_ICON |
3 | 2.31853 | 176 | Latin 1 / Western European | Process Default Language | RT_ICON |
4 | 7.87062 | 8435 | Latin 1 / Western European | Process Default Language | RT_ICON |
5 | 2.91605 | 1640 | Latin 1 / Western European | Process Default Language | RT_ICON |
6 | 3.31112 | 744 | Latin 1 / Western European | Process Default Language | RT_ICON |
7 | 3.1586 | 482 | Latin 1 / Western European | English - United States | RT_STRING |
8 | 3.11685 | 460 | Latin 1 / Western European | English - United States | RT_STRING |
9 | 3.15447 | 494 | Latin 1 / Western European | English - United States | RT_STRING |
10 | 2.99727 | 326 | Latin 1 / Western European | English - United States | RT_STRING |
Imports
KERNEL32.dll |
USER32.dll (delay-loaded) |
gdiplus.dll |
Total processes
77
Monitored processes
30
Malicious processes
6
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 312 | "C:\Users\admin\AppData\Local\Temp\nslEF9C.tmp\nsF616.tmp" "C:\Program Files\TAP-Windows\bin\tapinstall.exe" install "C:\Program Files\TAP-Windows\driver\OemVista.inf" tap0901 | C:\Users\admin\AppData\Local\Temp\nslEF9C.tmp\nsF616.tmp | tap-windows-9.21.2.exe | ||||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Modules
| |||||||||||||||
| 684 | reg add "HKCU\Software\Microsoft\Windows Script Host\Settings" /V Enabled /T REG_DWORD /F /D 1 | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 772 | MsiExec.exe /X{2E77104D-96E1-4A9C-86F2-C7CF8CB06999} /quiet | C:\Windows\system32\msiexec.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 1605 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 944 | "C:\Program Files\TAP-Windows\bin\tapinstall.exe" install "C:\Program Files\TAP-Windows\driver\OemVista.inf" tap0901 | C:\Program Files\TAP-Windows\bin\tapinstall.exe | nsF616.tmp | ||||||||||||
User: SYSTEM Company: Windows (R) Win 7 DDK provider Integrity Level: SYSTEM Description: Windows Setup API Exit code: 0 Version: 6.1.7600.16385 built by: WinDDK Modules
| |||||||||||||||
| 1000 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\Betternet\Betternet.msi" /quiet | C:\Windows\System32\msiexec.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1016 | "C:\Users\admin\Desktop\Betternet.Premium.VPN.v4.4.2.(Preactivated).exe" | C:\Users\admin\Desktop\Betternet.Premium.VPN.v4.4.2.(Preactivated).exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1548 | DrvInst.exe "2" "211" "ROOT\NET\0000" "C:\Windows\INF\oem4.inf" "oemvista.inf:tap0901:tap0901.ndi:9.0.0.21:tap0901" "6d14a44ff" "000003BC" "000005DC" "000005F0" | C:\Windows\system32\DrvInst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1688 | taskkill /IM Son.vbs /F | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1752 | taskkill /IM BetternetUpdater.exe /F | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1968 | DrvInst.exe "4" "0" "C:\Users\admin\AppData\Local\Temp\{4a92a165-3c58-72b7-ff6d-1d50a6f44f41}\oemvista.inf" "0" "6d14a44ff" "000003BC" "WinSta0\Default" "000005BC" "208" "c:\program files\tap-windows\driver" | C:\Windows\system32\DrvInst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
3 058
Read events
2 282
Write events
714
Delete events
62
Modification events
| (PID) Process: | (1016) Betternet.Premium.VPN.v4.4.2.(Preactivated).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1016) Betternet.Premium.VPN.v4.4.2.(Preactivated).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (684) reg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows Script Host\Settings |
| Operation: | write | Name: | Enabled |
Value: 1 | |||
| (PID) Process: | (2116) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Script Host\Settings |
| Operation: | write | Name: | Enabled |
Value: 1 | |||
| (PID) Process: | (3632) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3632) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2692) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2692) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3812) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3812) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
80
Suspicious files
23
Text files
648
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1016 | Betternet.Premium.VPN.v4.4.2.(Preactivated).exe | C:\Users\admin\AppData\Local\Temp\Son.vbs | text | |
MD5:— | SHA256:— | |||
| 1016 | Betternet.Premium.VPN.v4.4.2.(Preactivated).exe | C:\Users\admin\AppData\Local\Temp\Betternet\Betternet.msi | executable | |
MD5:— | SHA256:— | |||
| 1016 | Betternet.Premium.VPN.v4.4.2.(Preactivated).exe | C:\Users\admin\AppData\Local\Temp\Betternet\ProgramFilesFolder\Betternet\4.4.2\Betternet.exe | executable | |
MD5:— | SHA256:— | |||
| 1016 | Betternet.Premium.VPN.v4.4.2.(Preactivated).exe | C:\Users\admin\AppData\Local\Temp\Betternet\ProgramFilesFolder\Betternet\4.4.2\Betternet.Windows.Infrastructure.dll | executable | |
MD5:— | SHA256:— | |||
| 1016 | Betternet.Premium.VPN.v4.4.2.(Preactivated).exe | C:\Users\admin\AppData\Local\Temp\Betternet\ProgramFilesFolder\Betternet\4.4.2\Betternet.Windows.Sdk.dll | executable | |
MD5:— | SHA256:— | |||
| 1016 | Betternet.Premium.VPN.v4.4.2.(Preactivated).exe | C:\Users\admin\AppData\Local\Temp\Betternet\ProgramFilesFolder\Betternet\4.4.2\Foundation.Common.dll | executable | |
MD5:— | SHA256:— | |||
| 1016 | Betternet.Premium.VPN.v4.4.2.(Preactivated).exe | C:\Users\admin\AppData\Local\Temp\Betternet\ProgramFilesFolder\Betternet\4.4.2\AutoMapper.dll | executable | |
MD5:— | SHA256:— | |||
| 1016 | Betternet.Premium.VPN.v4.4.2.(Preactivated).exe | C:\Users\admin\AppData\Local\Temp\Betternet\ProgramFilesFolder\Betternet\4.4.2\Betternet.Windows.Services.dll | executable | |
MD5:— | SHA256:— | |||
| 1016 | Betternet.Premium.VPN.v4.4.2.(Preactivated).exe | C:\Users\admin\AppData\Local\Temp\Betternet\ProgramFilesFolder\Betternet\4.4.2\Betternet.Windows.Dialogs.dll | executable | |
MD5:— | SHA256:— | |||
| 1016 | Betternet.Premium.VPN.v4.4.2.(Preactivated).exe | C:\Users\admin\AppData\Local\Temp\Betternet\ProgramFilesFolder\Betternet\4.4.2\Foundation.Vpn.dll | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
19
DNS requests
11
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2516 | Betternet.exe | GET | — | 185.136.177.192:80 | http://ip-api.com/json | RO | — | — | malicious |
2516 | Betternet.exe | GET | 204 | 172.217.17.35:80 | http://gstatic.com/generate_204 | US | — | — | whitelisted |
2516 | Betternet.exe | POST | 200 | 172.217.16.14:80 | http://www.google-analytics.com/collect | US | image | 35 b | whitelisted |
2516 | Betternet.exe | POST | 200 | 172.217.16.14:80 | http://www.google-analytics.com/collect | US | image | 35 b | whitelisted |
2516 | Betternet.exe | POST | 200 | 172.217.16.14:80 | http://www.google-analytics.com/collect | US | image | 35 b | whitelisted |
2516 | Betternet.exe | POST | 200 | 172.217.16.14:80 | http://www.google-analytics.com/collect | US | image | 35 b | whitelisted |
2516 | Betternet.exe | POST | 200 | 172.217.16.14:80 | http://www.google-analytics.com/collect | US | image | 35 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2828 | hydra.exe | 104.243.211.135:443 | — | Choopa, LLC | US | unknown |
2516 | Betternet.exe | 143.204.65.68:443 | d2fs7vc1nne519.cloudfront.net | — | US | unknown |
2828 | hydra.exe | 104.243.211.121:443 | — | Choopa, LLC | US | unknown |
2516 | Betternet.exe | 216.58.214.68:443 | www.google.com | Google Inc. | US | whitelisted |
2516 | Betternet.exe | 143.204.65.121:443 | d11yeu3zibbmh5.cloudfront.net | — | US | unknown |
2516 | Betternet.exe | 172.217.17.35:80 | — | Google Inc. | US | whitelisted |
2828 | hydra.exe | 104.243.211.107:443 | — | Choopa, LLC | US | unknown |
2516 | Betternet.exe | 172.217.17.46:443 | — | Google Inc. | US | whitelisted |
2516 | Betternet.exe | 143.204.65.78:443 | d1ygoiuoqawp5l.cloudfront.net | — | US | unknown |
2516 | Betternet.exe | 107.178.254.148:443 | control.kochava.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
d1ygoiuoqawp5l.cloudfront.net |
| whitelisted |
control.kochava.com |
| unknown |
ip-api.com |
| malicious |
www.google-analytics.com |
| whitelisted |
d2fs7vc1nne519.cloudfront.net |
| unknown |
google.com |
| malicious |
www.google.com |
| malicious |
d11yeu3zibbmh5.cloudfront.net |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2516 | Betternet.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup ip-api.com |
Process | Message |
|---|---|
hydra.exe | HYDRA_STATE_CONNECTING
|
hydra.exe | HYDRA_STATE_CONNECTED
|
hydra.exe | HYDRA_STATE_DISCONNECTED
|
hydra.exe | AFVpn::FinalRelease
|