| File name: | virtualcage.exe |
| Full analysis: | https://app.any.run/tasks/2bb774c3-0e1c-4d55-9cb1-7d933974d108 |
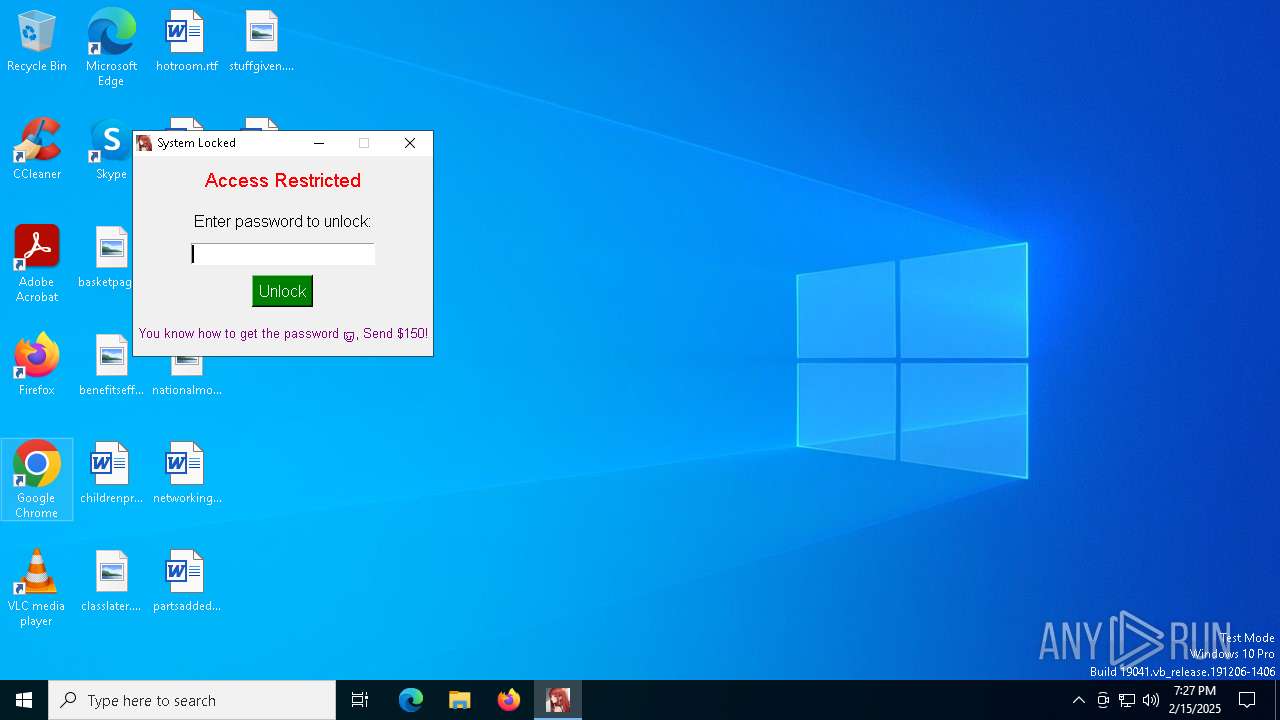
| Verdict: | Malicious activity |
| Analysis date: | February 15, 2025, 19:26:45 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 7 sections |
| MD5: | 4B81EB01271B077DA93801831729C62E |
| SHA1: | C0676576CB38BF33F091D1ABC1B0860056A33C98 |
| SHA256: | B3D92F67686BFB8F0DE831D162841BC1B8E084891CB93CF89BFD88F1EB95266E |
| SSDEEP: | 98304:ZShDLlstK4EDtg3RbOFOpwIsRjoYFr3ZyUuYA3w34MKFtHfktEzafhOsE+XZ0rX1:4oo5rWzFgQztwbG98/YqWaWbO |
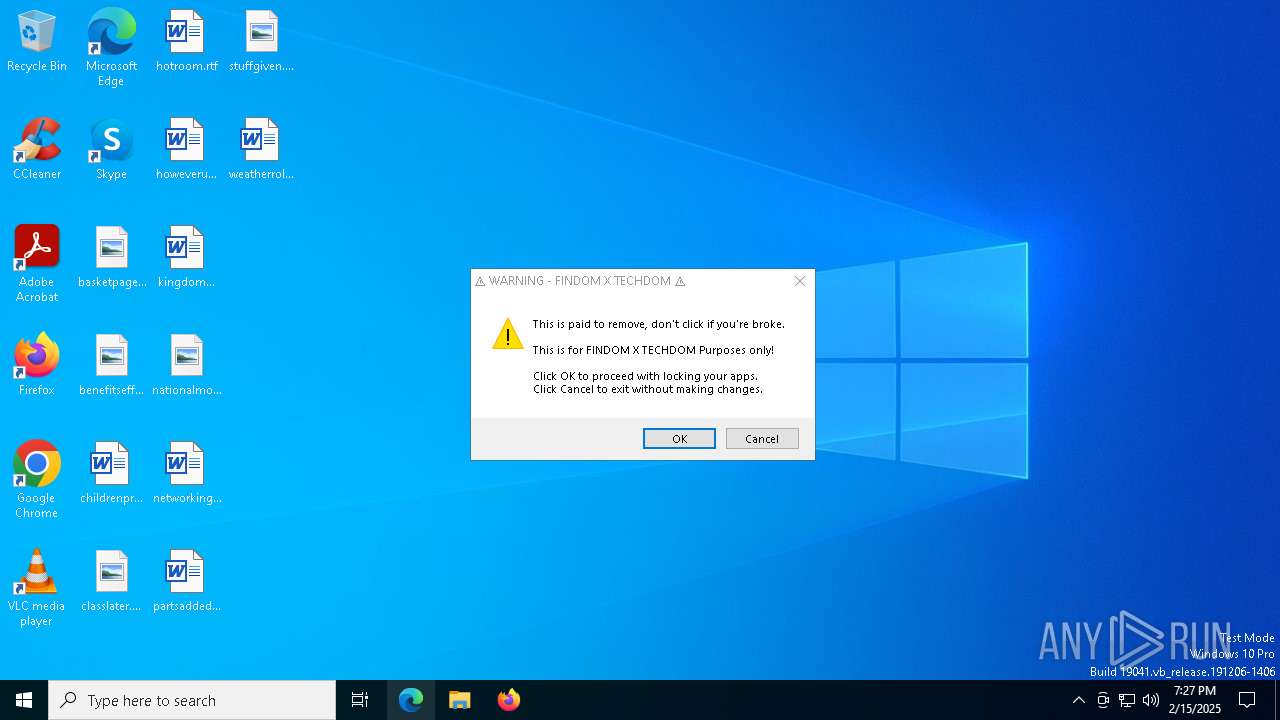
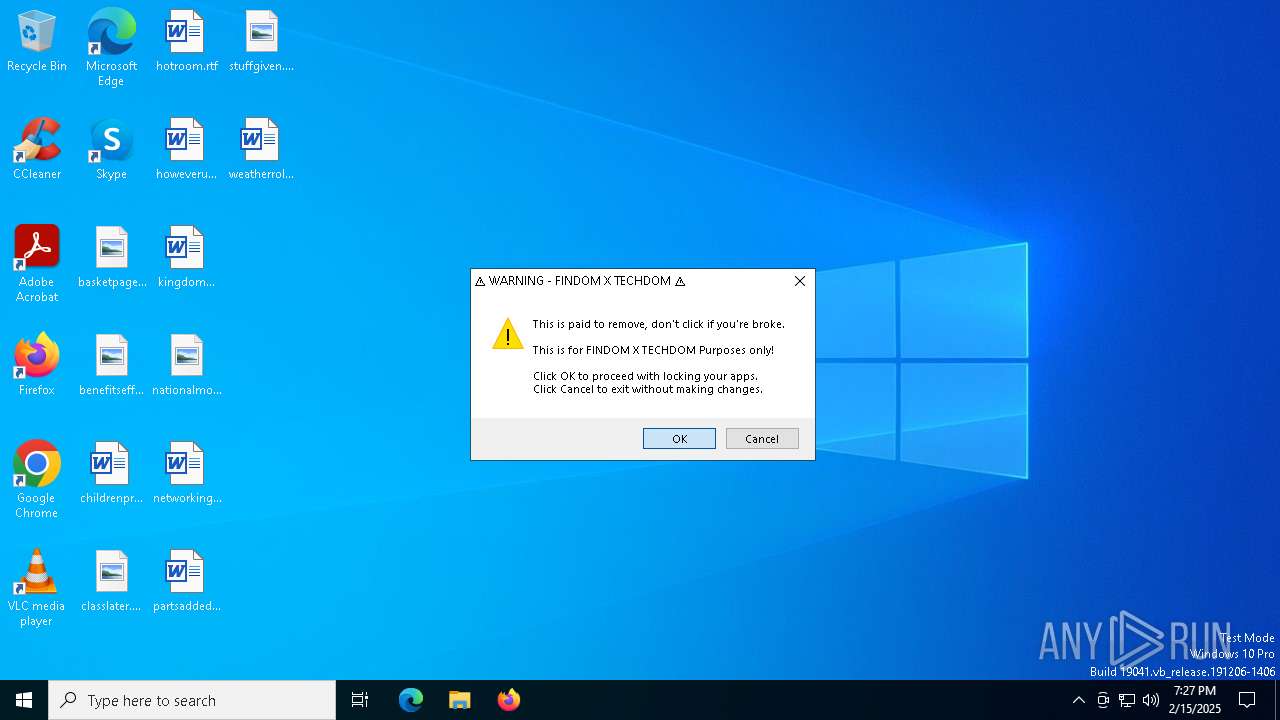
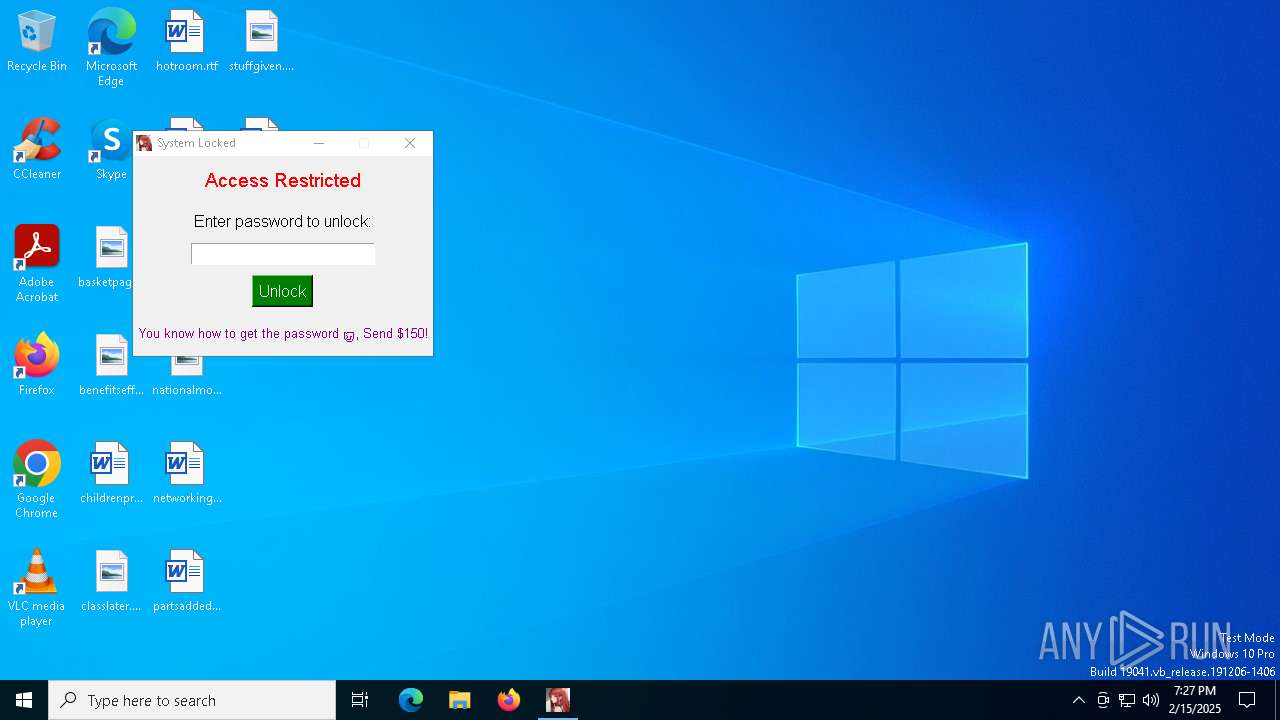
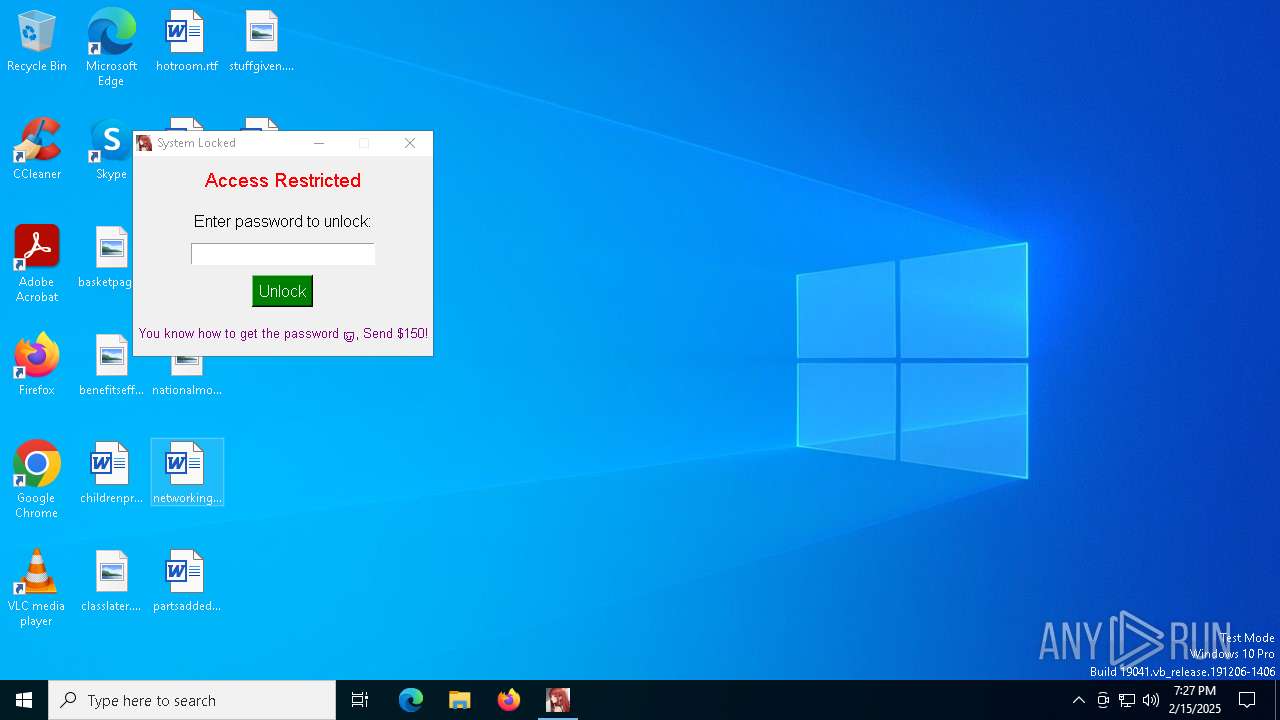
MALICIOUS
Uses Task Scheduler to autorun other applications
- virtualcage.exe (PID: 6976)
Changes the autorun value in the registry
- virtualcage.exe (PID: 6976)
Task Manager has been disabled (taskmgr)
- reg.exe (PID: 6392)
- reg.exe (PID: 6688)
- reg.exe (PID: 6512)
- reg.exe (PID: 5748)
- reg.exe (PID: 2216)
- reg.exe (PID: 1596)
- reg.exe (PID: 1400)
- reg.exe (PID: 6652)
- reg.exe (PID: 6088)
- reg.exe (PID: 7072)
- reg.exe (PID: 4544)
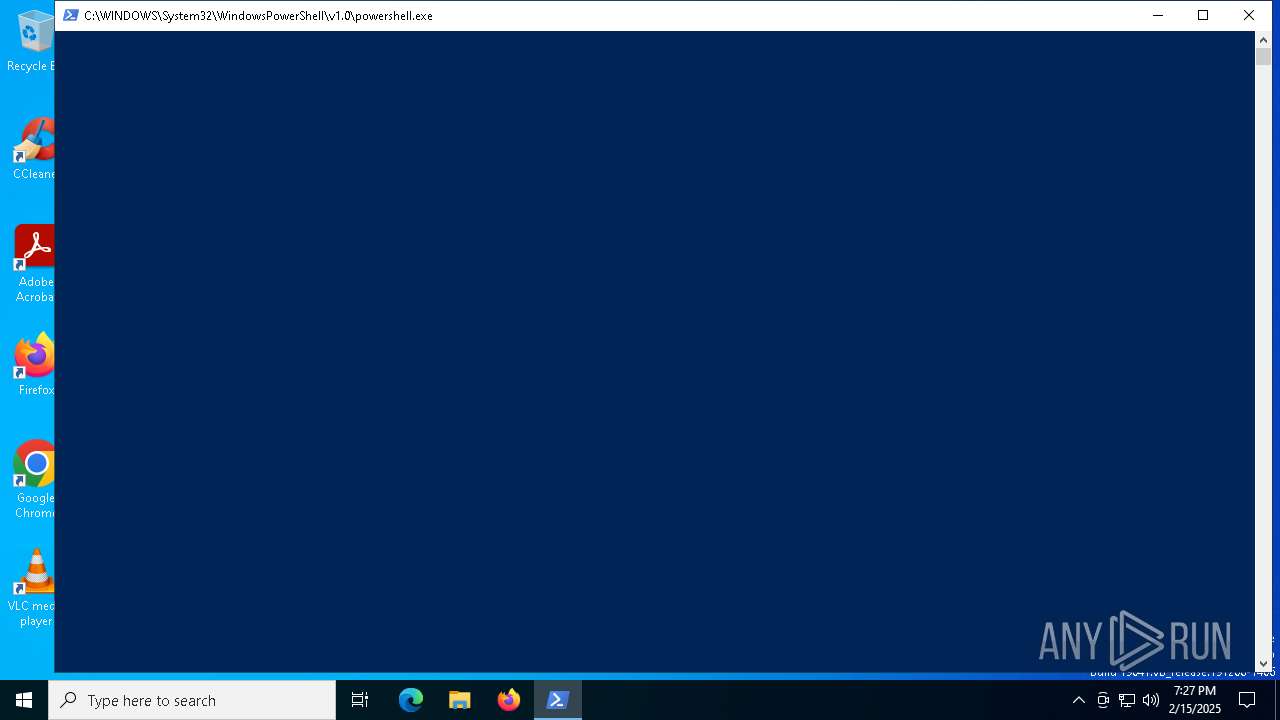
Create files in the Startup directory
- powershell.exe (PID: 6172)
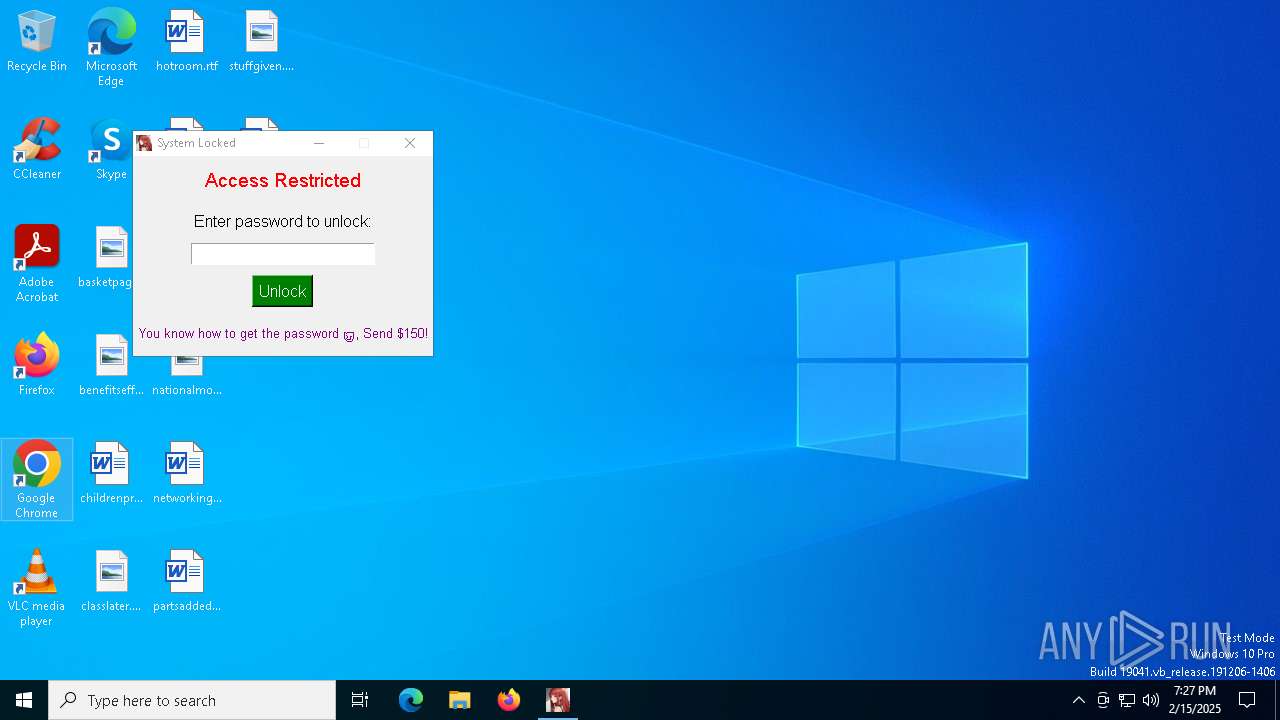
SUSPICIOUS
The process drops C-runtime libraries
- virtualcage.exe (PID: 6184)
Process drops legitimate windows executable
- virtualcage.exe (PID: 6184)
There is functionality for taking screenshot (YARA)
- virtualcage.exe (PID: 6184)
Executable content was dropped or overwritten
- virtualcage.exe (PID: 6184)
- virtualcage.exe (PID: 6976)
Process drops python dynamic module
- virtualcage.exe (PID: 6184)
Application launched itself
- virtualcage.exe (PID: 6184)
Deletes scheduled task without confirmation
- schtasks.exe (PID: 7012)
Starts POWERSHELL.EXE for commands execution
- virtualcage.exe (PID: 6976)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 2940)
- cmd.exe (PID: 4320)
- cmd.exe (PID: 6504)
- cmd.exe (PID: 4548)
- cmd.exe (PID: 2324)
- cmd.exe (PID: 6760)
- cmd.exe (PID: 4120)
- cmd.exe (PID: 6848)
- cmd.exe (PID: 6280)
- cmd.exe (PID: 5872)
- cmd.exe (PID: 6164)
- cmd.exe (PID: 7084)
Starts CMD.EXE for commands execution
- virtualcage.exe (PID: 6976)
Loads Python modules
- virtualcage.exe (PID: 6976)
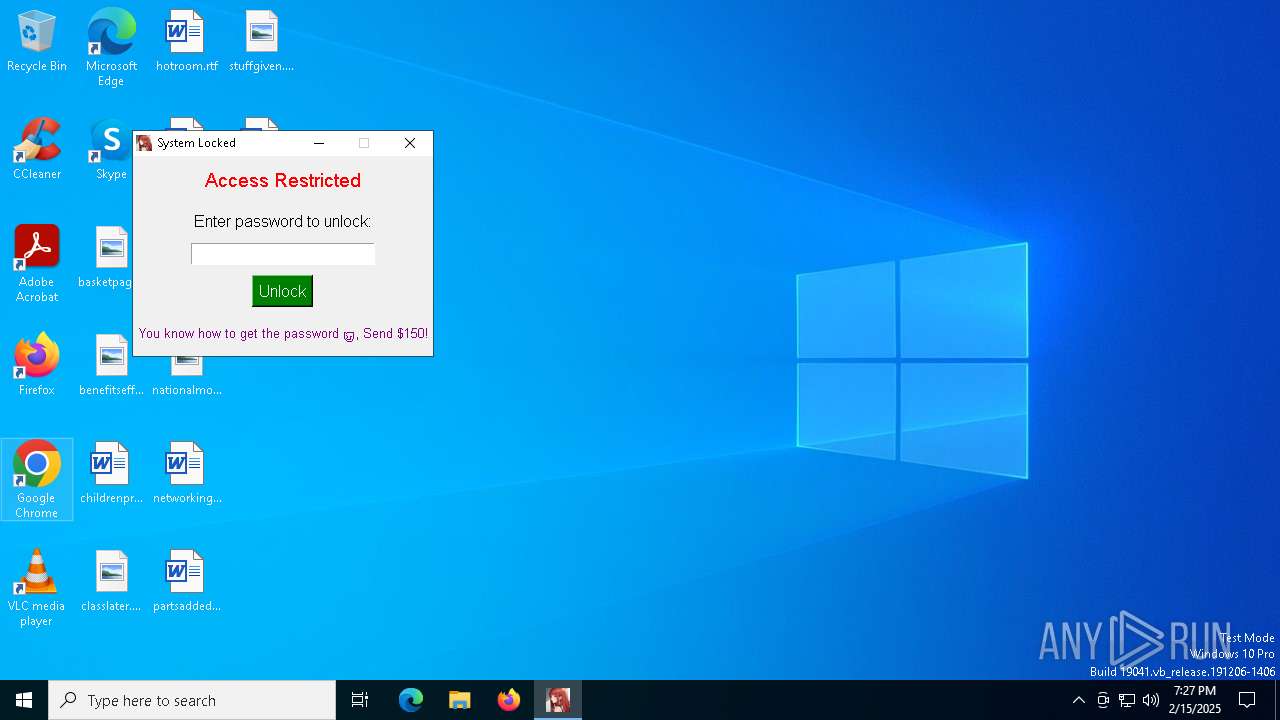
INFO
Checks supported languages
- virtualcage.exe (PID: 6184)
- virtualcage.exe (PID: 6976)
The sample compiled with english language support
- virtualcage.exe (PID: 6184)
Create files in a temporary directory
- virtualcage.exe (PID: 6184)
- powershell.exe (PID: 6172)
- virtualcage.exe (PID: 6976)
PyInstaller has been detected (YARA)
- virtualcage.exe (PID: 6184)
Reads the computer name
- virtualcage.exe (PID: 6184)
- virtualcage.exe (PID: 6976)
Reads the machine GUID from the registry
- virtualcage.exe (PID: 6976)
Reads the software policy settings
- powershell.exe (PID: 6172)
Reads security settings of Internet Explorer
- powershell.exe (PID: 6172)
Creates files or folders in the user directory
- powershell.exe (PID: 6172)
- virtualcage.exe (PID: 6976)
Application launched itself
- chrome.exe (PID: 3560)
- chrome.exe (PID: 1868)
Manual execution by a user
- chrome.exe (PID: 3560)
- chrome.exe (PID: 1868)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:01:24 16:53:08+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.35 |
| CodeSize: | 171008 |
| InitializedDataSize: | 526848 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xc200 |
| OSVersion: | 5.2 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows GUI |
Total processes
171
Monitored processes
49
Malicious processes
2
Suspicious processes
1
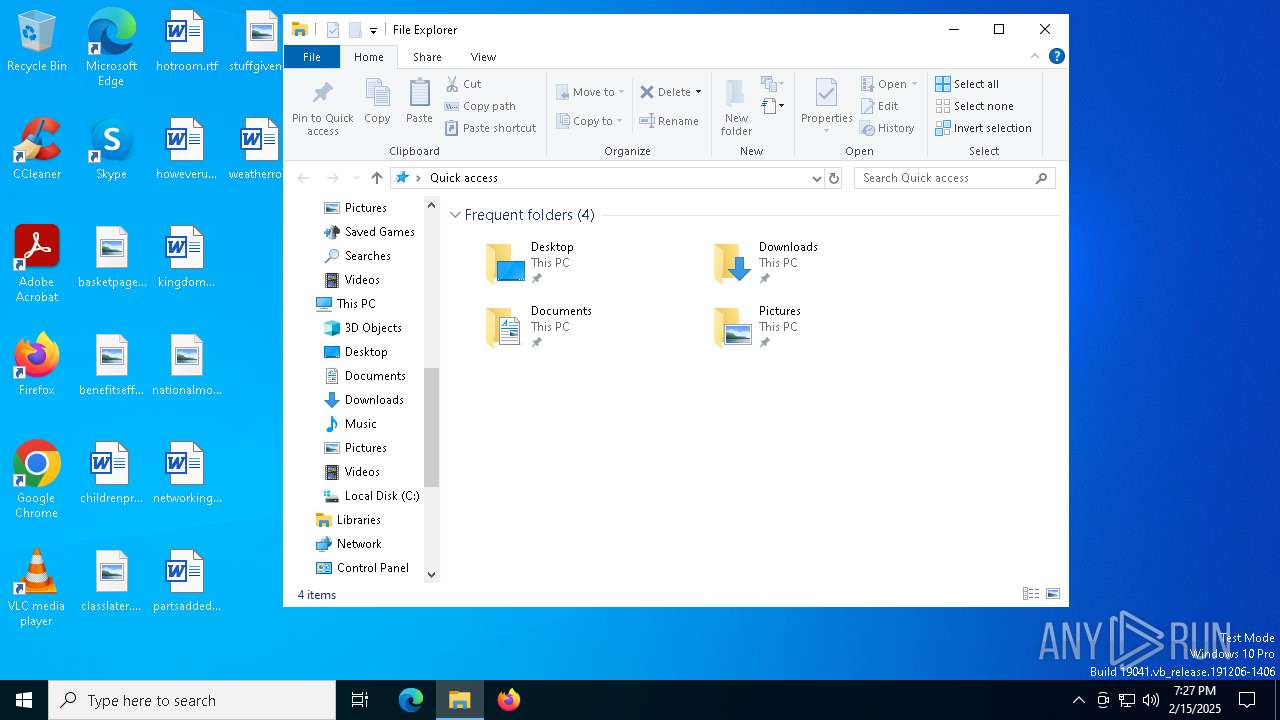
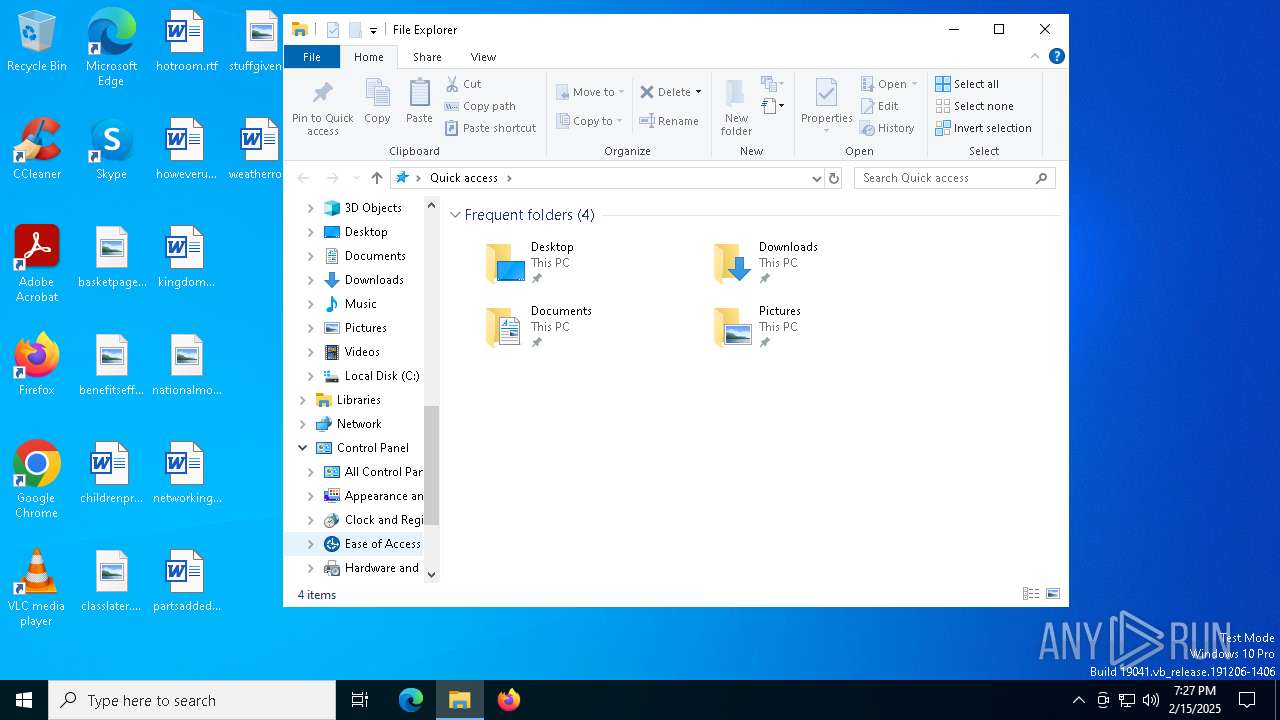
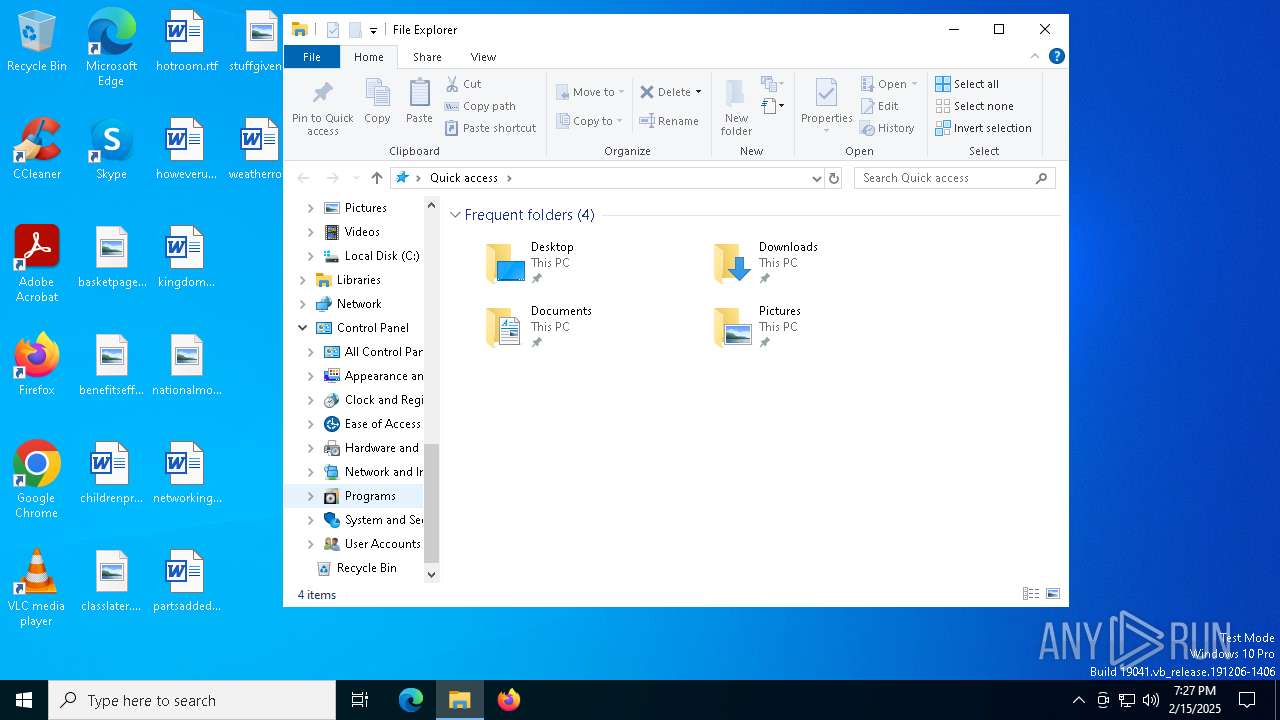
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1400 | reg add "HKCU\Software\Microsoft\Windows\CurrentVersion\Policies\System" /v DisableTaskMgr /t REG_DWORD /d 1 /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1596 | reg add "HKCU\Software\Microsoft\Windows\CurrentVersion\Policies\System" /v DisableTaskMgr /t REG_DWORD /d 1 /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1868 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "--disable-features=OptimizationGuideModelDownloading,OptimizationHintsFetching,OptimizationTargetPrediction,OptimizationHints" | C:\Program Files\Google\Chrome\Application\chrome.exe | — | explorer.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 15 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2132 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2216 | reg add "HKCU\Software\Microsoft\Windows\CurrentVersion\Policies\System" /v DisableTaskMgr /t REG_DWORD /d 1 /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2324 | C:\WINDOWS\system32\cmd.exe /c reg add "HKCU\Software\Microsoft\Windows\CurrentVersion\Policies\System" /v DisableTaskMgr /t REG_DWORD /d 1 /f | C:\Windows\System32\cmd.exe | — | virtualcage.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2828 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win64 --annotation=prod=Chrome --annotation=ver=122.0.6261.70 --initial-client-data=0x21c,0x220,0x224,0x1f8,0x228,0x7ff82120dc40,0x7ff82120dc4c,0x7ff82120dc58 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 15 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2940 | C:\WINDOWS\system32\cmd.exe /c reg add "HKCU\Software\Microsoft\Windows\CurrentVersion\Policies\System" /v DisableTaskMgr /t REG_DWORD /d 1 /f | C:\Windows\System32\cmd.exe | — | virtualcage.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2972 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3296 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
5 763
Read events
5 741
Write events
22
Delete events
0
Modification events
| (PID) Process: | (6976) virtualcage.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | VirtualCageTimer |
Value: "C:\Users\admin\AppData\Local\VirtualCageTimer\virtualcage.exe" | |||
| (PID) Process: | (6976) virtualcage.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | VirtualCageTimer |
Value: "C:\Users\admin\AppData\Local\VirtualCageTimer\virtualcage.exe" | |||
| (PID) Process: | (6976) virtualcage.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | VirtualCageTimer |
Value: "C:\Users\admin\AppData\Local\VirtualCageTimer\virtualcage.exe" | |||
| (PID) Process: | (3688) reg.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | DisableTaskMgr |
Value: 1 | |||
| (PID) Process: | (5748) reg.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | DisableTaskMgr |
Value: 1 | |||
| (PID) Process: | (6392) reg.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | DisableTaskMgr |
Value: 1 | |||
| (PID) Process: | (6688) reg.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | DisableTaskMgr |
Value: 1 | |||
| (PID) Process: | (6512) reg.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | DisableTaskMgr |
Value: 1 | |||
| (PID) Process: | (2216) reg.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | DisableTaskMgr |
Value: 1 | |||
| (PID) Process: | (1596) reg.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | DisableTaskMgr |
Value: 1 | |||
Executable files
71
Suspicious files
8
Text files
928
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6184 | virtualcage.exe | C:\Users\admin\AppData\Local\Temp\_MEI61842\VCRUNTIME140_1.dll | executable | |
MD5:7667B0883DE4667EC87C3B75BED84D84 | SHA256:04E7CCBDCAD7CBAF0ED28692FB08EAB832C38AAD9071749037EE7A58F45E9D7D | |||
| 6184 | virtualcage.exe | C:\Users\admin\AppData\Local\Temp\_MEI61842\_bz2.pyd | executable | |
MD5:B45E82A398713163216984F2FEBA88F6 | SHA256:4C2649DC69A8874B91646723AACB84C565EFEAA4277C46392055BCA9A10497A8 | |||
| 6184 | virtualcage.exe | C:\Users\admin\AppData\Local\Temp\_MEI61842\VCRUNTIME140.dll | executable | |
MD5:11D9AC94E8CB17BD23DEA89F8E757F18 | SHA256:E1D6F78A72836EA120BD27A33AE89CBDC3F3CA7D9D0231AAA3AAC91996D2FA4E | |||
| 6184 | virtualcage.exe | C:\Users\admin\AppData\Local\Temp\_MEI61842\_ctypes.pyd | executable | |
MD5:79F339753DC8954B8EB45FE70910937E | SHA256:35CDD122679041EBEF264DE5626B7805F3F66C8AE6CC451B8BC520BE647FA007 | |||
| 6184 | virtualcage.exe | C:\Users\admin\AppData\Local\Temp\_MEI61842\_tkinter.pyd | executable | |
MD5:0F1AA5B9A82B75B607B4EAD6BB6B8BE6 | SHA256:336BD5BFFDC0229DA4EADDBB0CFC42A9E55459A40E1322B38F7E563BDA8DD190 | |||
| 6184 | virtualcage.exe | C:\Users\admin\AppData\Local\Temp\_MEI61842\_hashlib.pyd | executable | |
MD5:CFB9E0A73A6C9D6D35C2594E52E15234 | SHA256:50DAEB3985302A8D85CE8167B0BF08B9DA43E7D51CEAE50E8E1CDFB0EDF218C6 | |||
| 6184 | virtualcage.exe | C:\Users\admin\AppData\Local\Temp\_MEI61842\api-ms-win-core-heap-l1-1-0.dll | executable | |
MD5:ACCC640D1B06FB8552FE02F823126FF5 | SHA256:332BA469AE84AA72EC8CCE2B33781DB1AB81A42ECE5863F7A3CB5A990059594F | |||
| 6184 | virtualcage.exe | C:\Users\admin\AppData\Local\Temp\_MEI61842\api-ms-win-core-handle-l1-1-0.dll | executable | |
MD5:E89CDCD4D95CDA04E4ABBA8193A5B492 | SHA256:1A489E0606484BD71A0D9CB37A1DC6CA8437777B3D67BFC8C0075D0CC59E6238 | |||
| 6184 | virtualcage.exe | C:\Users\admin\AppData\Local\Temp\_MEI61842\_lzma.pyd | executable | |
MD5:5A77A1E70E054431236ADB9E46F40582 | SHA256:F125A885C10E1BE4B12D988D6C19128890E7ADD75BAA935FE1354721AA2DEA3E | |||
| 6184 | virtualcage.exe | C:\Users\admin\AppData\Local\Temp\_MEI61842\api-ms-win-core-file-l2-1-0.dll | executable | |
MD5:BFFFA7117FD9B1622C66D949BAC3F1D7 | SHA256:1EA267A2E6284F17DD548C6F2285E19F7EDB15D6E737A55391140CE5CB95225E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
27
DNS requests
13
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | DE | binary | 312 b | whitelisted |
1176 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
6832 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 419 b | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 104.124.11.17:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | QA | binary | 973 b | whitelisted |
6832 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 408 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 2.19.122.54:443 | — | Akamai International B.V. | DE | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 104.124.11.17:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
1176 | svchost.exe | 20.190.160.65:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1176 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
1076 | svchost.exe | 2.19.106.8:443 | go.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |