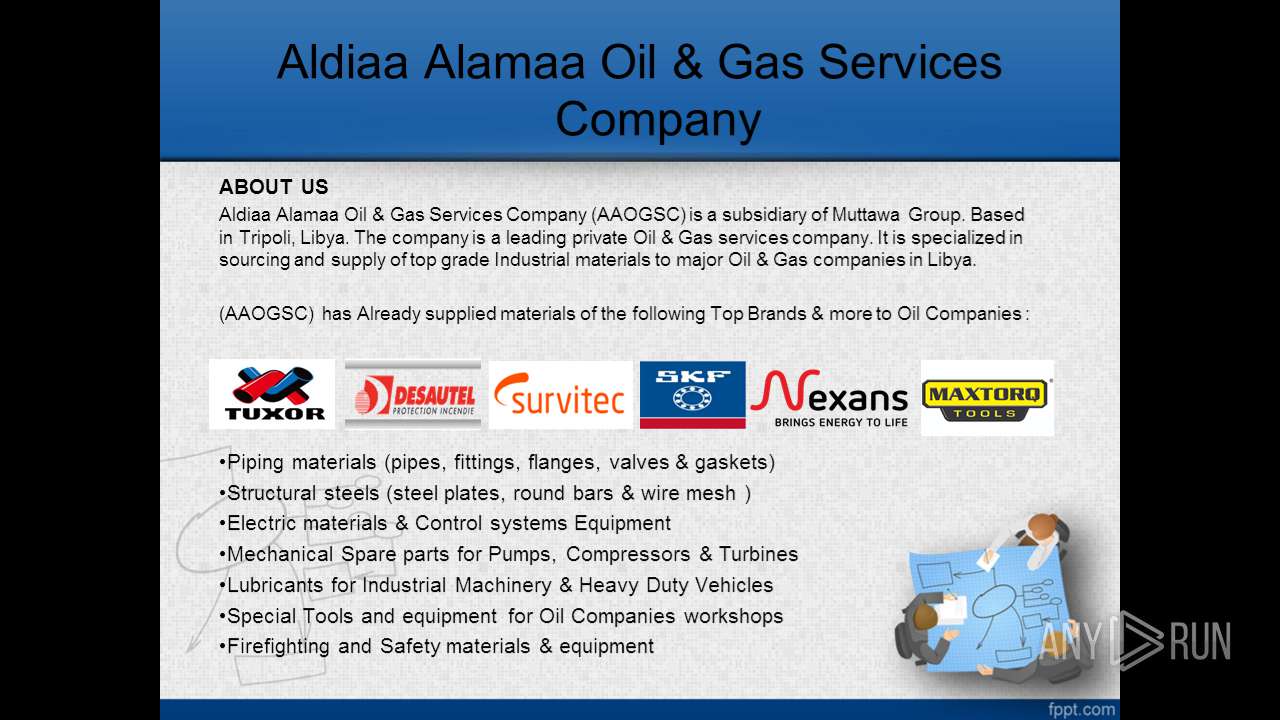
| File name: | our Company.ppt |
| Full analysis: | https://app.any.run/tasks/05d65ce1-1e83-440c-a4f3-a3832c80ff1a |
| Verdict: | No threats detected |
| Analysis date: | November 15, 2019, 21:20:18 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| MIME: | application/vnd.ms-powerpoint |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, Code page: 1252, Title: Diapositiva 1, Author: Mariajose, Last Saved By: HP, Revision Number: 666, Name of Creating Application: Microsoft Office PowerPoint, Total Editing Time: 4d+04:35:04, Create Time/Date: Sun May 23 15:28:12 2010, Last Saved Time/Date: Tue Dec 18 10:12:05 2018, Number of Words: 449 |
| MD5: | C5D26A65A1DAD0BF3DC1AFD4D4D8D487 |
| SHA1: | 9F6E5C652FE43B6A4464E14AA26BDBD3430373E3 |
| SHA256: | B3C750B3577E1E09EE75503353828AF463817AD43748D3A389CDE000D56B0015 |
| SSDEEP: | 49152:RRRXfP24btNI3vPcvOvmvkvLvBvrDvGmvXkvMvm8v/p3:lP2wNI/wqyATBHnQYP/p3 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Checks supported languages
- POWERPNT.EXE (PID: 2144)
INFO
Reads Microsoft Office registry keys
- POWERPNT.EXE (PID: 2144)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .pps/ppt | | | Microsoft PowerPoint document (79.7) |
|---|
EXIF
FlashPix
| CurrentUser: | DELL |
|---|---|
| Title: | Diapositiva 1 |
| Author: | Mariajose |
| LastModifiedBy: | HP |
| RevisionNumber: | 666 |
| Software: | Microsoft Office PowerPoint |
| TotalEditTime: | 4.2 days |
| CreateDate: | 2010:05:23 14:28:12 |
| ModifyDate: | 2018:12:18 10:12:05 |
| Words: | 449 |
| ThumbnailClip: | (Binary data 57736 bytes, use -b option to extract) |
| PresentationTarget: | On-screen Show (4:3) |
| Company: | Toshiba |
| Bytes: | 2466221 |
| Paragraphs: | 117 |
| Slides: | 10 |
| Notes: | 1 |
| HiddenSlides: | - |
| MMClips: | - |
| AppVersion: | 12 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: |
|
| HeadingPairs: |
|
| CodePage: | Windows Latin 1 (Western European) |
| Hyperlinks: |
|
Total processes
35
Monitored processes
1
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2144 | "C:\Program Files\Microsoft Office\Office14\POWERPNT.EXE" /s "C:\Users\admin\AppData\Local\Temp\our Company.ppt.pps" | C:\Program Files\Microsoft Office\Office14\POWERPNT.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft PowerPoint Exit code: 0 Version: 14.0.6009.1000 Modules
| |||||||||||||||
Total events
757
Read events
701
Write events
49
Delete events
7
Modification events
| (PID) Process: | (2144) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\PowerPoint\Resiliency\StartupItems |
| Operation: | write | Name: | }1c |
Value: 7D31630060080000010000000000000000000000 | |||
| (PID) Process: | (2144) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2144) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2144) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2144) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2144) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2144) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2144) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2144) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2144) POWERPNT.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | PPTFiles |
Value: 1332674584 | |||
Executable files
0
Suspicious files
1
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2144 | POWERPNT.EXE | C:\Users\admin\AppData\Local\Temp\CVRAE7A.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2144 | POWERPNT.EXE | C:\Users\admin\AppData\Local\Temp\~DFBE62DE746EDB15CB.TMP | — | |
MD5:— | SHA256:— | |||
| 2144 | POWERPNT.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\C98D82A8.jpeg | — | |
MD5:— | SHA256:— | |||
| 2144 | POWERPNT.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\60A69289.jpeg | — | |
MD5:— | SHA256:— | |||
| 2144 | POWERPNT.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\963906F6.jpeg | — | |
MD5:— | SHA256:— | |||
| 2144 | POWERPNT.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\7B15E7F.jpeg | — | |
MD5:— | SHA256:— | |||
| 2144 | POWERPNT.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\4A0F6674.jpeg | — | |
MD5:— | SHA256:— | |||
| 2144 | POWERPNT.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\E6EE6BE5.jpeg | — | |
MD5:— | SHA256:— | |||
| 2144 | POWERPNT.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\4275B8A2.jpeg | — | |
MD5:— | SHA256:— | |||
| 2144 | POWERPNT.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\4F5CEC3B.jpeg | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report