| File name: | Xeno.exe |
| Full analysis: | https://app.any.run/tasks/da566d79-910c-4a6b-9d3e-97236ece0f18 |
| Verdict: | Malicious activity |
| Analysis date: | November 20, 2024, 17:25:31 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 7 sections |
| MD5: | 6A9C62338C4C9B550396A9D6B6830722 |
| SHA1: | FA09434533FAF5C7BA69A4E2E71499A533139340 |
| SHA256: | B3BF71DEBBB93701A50FB5057AE578E26453E502A746C419A91003A4E0C972D4 |
| SSDEEP: | 98304:fjsMKzPnvEAEZGPBzJx7WQizOMAu8PHieEM1SBkyZiJYfpx7AHHWWmOOei8yRS46:CO41zPuB6ERaqPkERTsgt4vkS6a |
MALICIOUS
No malicious indicators.SUSPICIOUS
Process drops legitimate windows executable
- Xeno.exe (PID: 3692)
Executable content was dropped or overwritten
- Xeno.exe (PID: 3692)
- Xeno.exe (PID: 1348)
Process drops python dynamic module
- Xeno.exe (PID: 3692)
Application launched itself
- Xeno.exe (PID: 3692)
The process drops C-runtime libraries
- Xeno.exe (PID: 3692)
Starts CMD.EXE for commands execution
- Xeno.exe (PID: 1348)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 904)
- cmd.exe (PID: 1804)
Executing commands from a ".bat" file
- Xeno.exe (PID: 1348)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 2260)
- cmd.exe (PID: 5964)
- cmd.exe (PID: 364)
Checks for external IP
- svchost.exe (PID: 2192)
INFO
Checks supported languages
- Xeno.exe (PID: 3692)
- Xeno.exe (PID: 1348)
Create files in a temporary directory
- Xeno.exe (PID: 3692)
- Xeno.exe (PID: 1348)
Reads the computer name
- Xeno.exe (PID: 3692)
- Xeno.exe (PID: 1348)
Checks operating system version
- Xeno.exe (PID: 1348)
Reads the machine GUID from the registry
- Xeno.exe (PID: 1348)
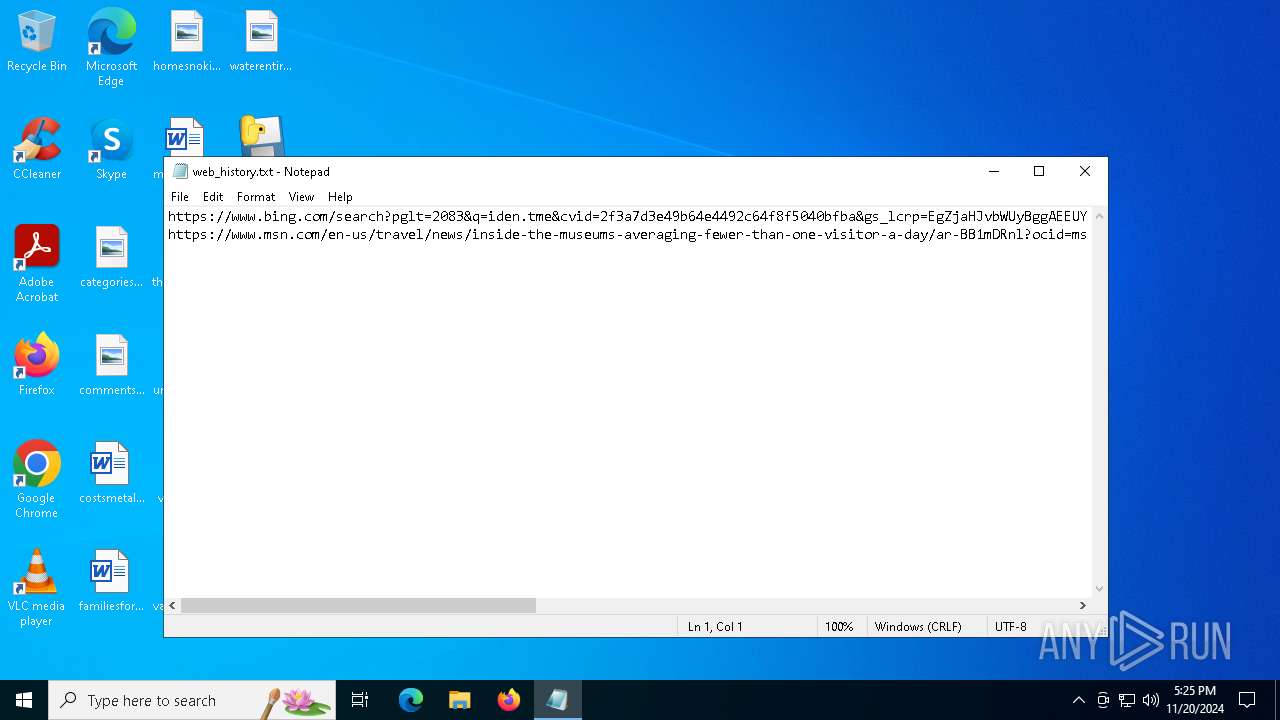
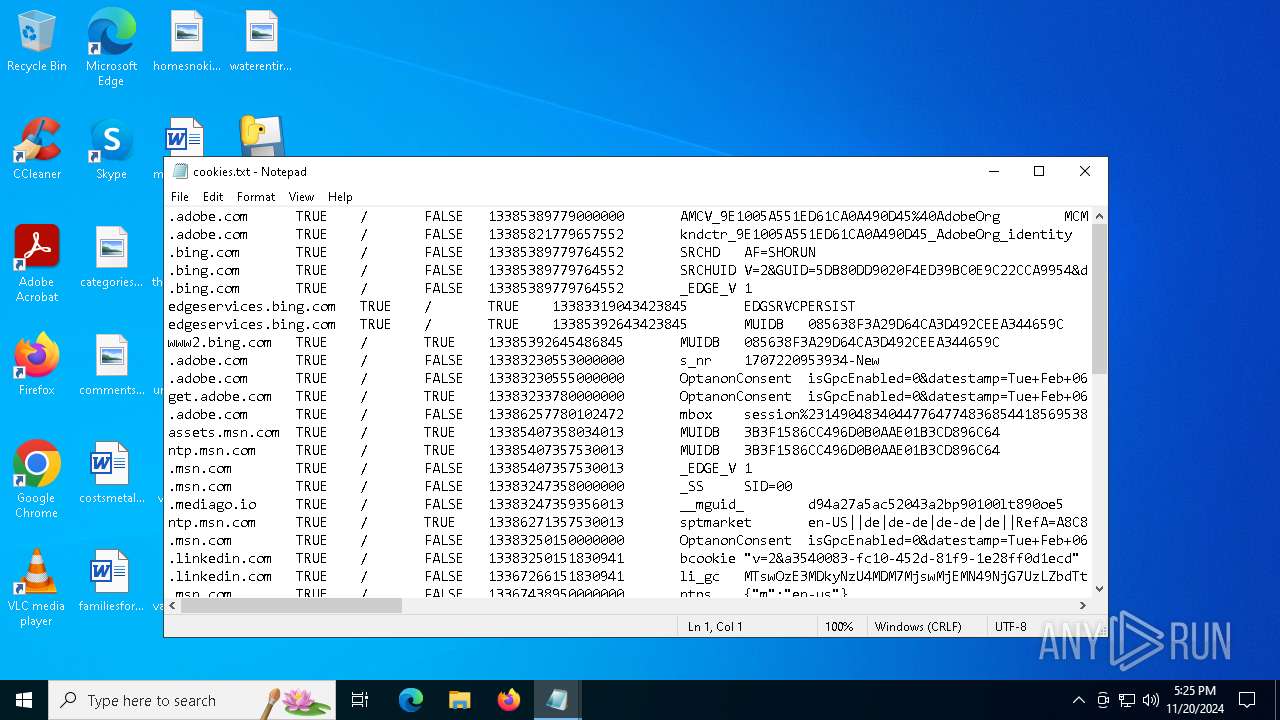
Manual execution by a user
- notepad.exe (PID: 3796)
- notepad.exe (PID: 4044)
PyInstaller has been detected (YARA)
- Xeno.exe (PID: 3692)
Attempting to use instant messaging service
- svchost.exe (PID: 2192)
- Xeno.exe (PID: 1348)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2024:11:01 19:06:40+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.32 |
| CodeSize: | 165888 |
| InitializedDataSize: | 154112 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xafa0 |
| OSVersion: | 5.2 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows GUI |
Total processes
133
Monitored processes
22
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 364 | C:\WINDOWS\system32\cmd.exe /c "C:\Windows\System32\wbem\WMIC.exe csproduct get uuid" | C:\Windows\System32\cmd.exe | — | Xeno.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 904 | C:\WINDOWS\system32\cmd.exe /c "reg delete HKCU\Software\Microsoft\Windows\CurrentVersion\Run /v empyrean /f" | C:\Windows\System32\cmd.exe | — | Xeno.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1348 | "C:\Users\admin\Desktop\Xeno.exe" | C:\Users\admin\Desktop\Xeno.exe | Xeno.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1804 | C:\WINDOWS\system32\cmd.exe /c "reg add HKCU\Software\Microsoft\Windows\CurrentVersion\Run /v empyrean /t REG_SZ /d C:\Users\admin\AppData\Roaming\empyrean\run.bat /f" | C:\Windows\System32\cmd.exe | — | Xeno.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2096 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2160 | C:\Windows\System32\wbem\WMIC.exe csproduct get uuid | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2192 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2260 | C:\WINDOWS\system32\cmd.exe /c "C:\Windows\System32\wbem\WMIC.exe csproduct get uuid" | C:\Windows\System32\cmd.exe | — | Xeno.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2860 | C:\Windows\System32\wbem\WMIC.exe csproduct get uuid | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3560 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
1 493
Read events
1 491
Write events
1
Delete events
1
Modification events
| (PID) Process: | (3936) reg.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | empyrean |
Value: | |||
| (PID) Process: | (5544) reg.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | empyrean |
Value: C:\Users\admin\AppData\Roaming\empyrean\run.bat | |||
Executable files
90
Suspicious files
6
Text files
31
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3692 | Xeno.exe | C:\Users\admin\AppData\Local\Temp\_MEI36922\Crypto\Cipher\_raw_aes.pyd | executable | |
MD5:671100B821EB357CEB5A4C5FF86BC31A | SHA256:803E46354CDAB4AF6FF289E98DE9C56B5B08E3E9AD5F235D5A282005FA9F2D50 | |||
| 3692 | Xeno.exe | C:\Users\admin\AppData\Local\Temp\_MEI36922\Crypto\Cipher\_raw_aesni.pyd | executable | |
MD5:DCD2F68680E2FB83E9FEFA18C7B4B3E0 | SHA256:D63F63985356B7D2E0E61E7968720FB72DC6B57D73BED4F337E372918078F946 | |||
| 3692 | Xeno.exe | C:\Users\admin\AppData\Local\Temp\_MEI36922\Crypto\Cipher\_pkcs1_decode.pyd | executable | |
MD5:3EFFD59CD95B6706C1F2DD661AA943FC | SHA256:4C29950A9EDEDBBC24A813F8178723F049A529605EF6D35F16C7955768AACE9E | |||
| 3692 | Xeno.exe | C:\Users\admin\AppData\Local\Temp\_MEI36922\Crypto\Cipher\_raw_blowfish.pyd | executable | |
MD5:418CEC0CC45B20EE8165E86CAC35963C | SHA256:694BF801227B26DADAF9DDFF373647AB551D7A0B9CFF6DE1B42747F04EFC510E | |||
| 3692 | Xeno.exe | C:\Users\admin\AppData\Local\Temp\_MEI36922\Crypto\Cipher\_Salsa20.pyd | executable | |
MD5:E3AE69E44C4C82D83082BBB8C25AA8DD | SHA256:4229235814BBEE62311E3623C07898B03D3B22281CD4E5F1A87B86450B1B740F | |||
| 3692 | Xeno.exe | C:\Users\admin\AppData\Local\Temp\_MEI36922\Crypto\Cipher\_ARC4.pyd | executable | |
MD5:D9F2264898AAAA9EF6152A1414883D0F | SHA256:836CBA3B83B00427430FE6E1C4E45790616BC85C57DBD6E6D5B6930A9745B715 | |||
| 3692 | Xeno.exe | C:\Users\admin\AppData\Local\Temp\_MEI36922\Crypto\Cipher\_raw_arc2.pyd | executable | |
MD5:3F5FD606893B3DE6116D4A185E713CA3 | SHA256:0898CDE5FCCFA86E2423CDF627A3745B1F59BB30DFEF0DD9423926D4167F9F82 | |||
| 3692 | Xeno.exe | C:\Users\admin\AppData\Local\Temp\_MEI36922\Crypto\Cipher\_chacha20.pyd | executable | |
MD5:ED1BBDC7CC945DA2D1F5A914987EB885 | SHA256:1EECE2F714DC1F520D0608F9F71E692F5B269930603F8AFC330118EA38F16005 | |||
| 3692 | Xeno.exe | C:\Users\admin\AppData\Local\Temp\_MEI36922\Crypto\Cipher\_raw_cbc.pyd | executable | |
MD5:FE44F698198190DE574DC193A0E1B967 | SHA256:32FA416A29802EB0017A2C7360BF942EDB132D4671168DE26BD4C3E94D8DE919 | |||
| 3692 | Xeno.exe | C:\Users\admin\AppData\Local\Temp\_MEI36922\Crypto\Cipher\_raw_ctr.pyd | executable | |
MD5:D67F83D1482D9600AC012868FB49D16E | SHA256:AA463CD4D0B4BBD4159650D66C11A699B23775BF92455FB58A2206B932A65FEC | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
24
DNS requests
10
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4932 | svchost.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4932 | svchost.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4932 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 104.126.37.179:443 | — | Akamai International B.V. | DE | unknown |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4932 | svchost.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4932 | svchost.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
ipapi.co |
| shared |
discord.com |
| whitelisted |
raw.githubusercontent.com |
| shared |
www.cloudflare.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discord .com) |
1348 | Xeno.exe | Misc activity | ET INFO Observed Discord Domain (discord .com in TLS SNI) |
2192 | svchost.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup Domain (ipapi .co in DNS lookup) |
2192 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |