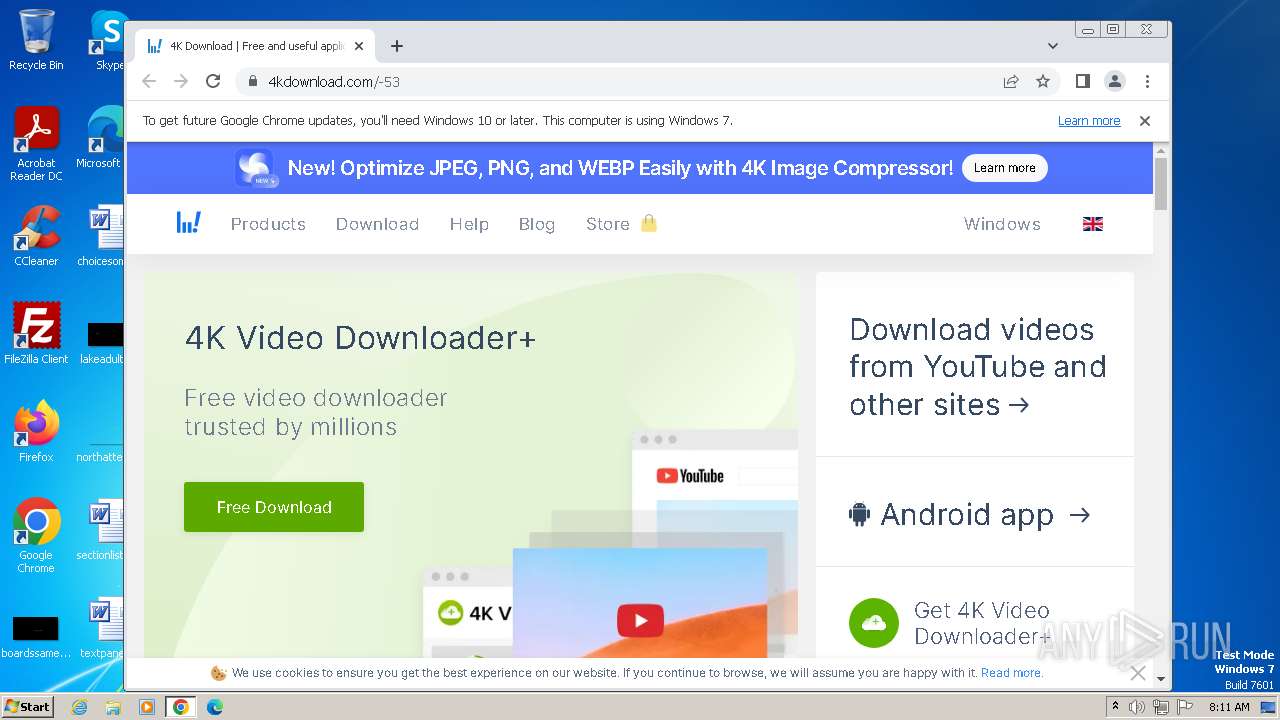
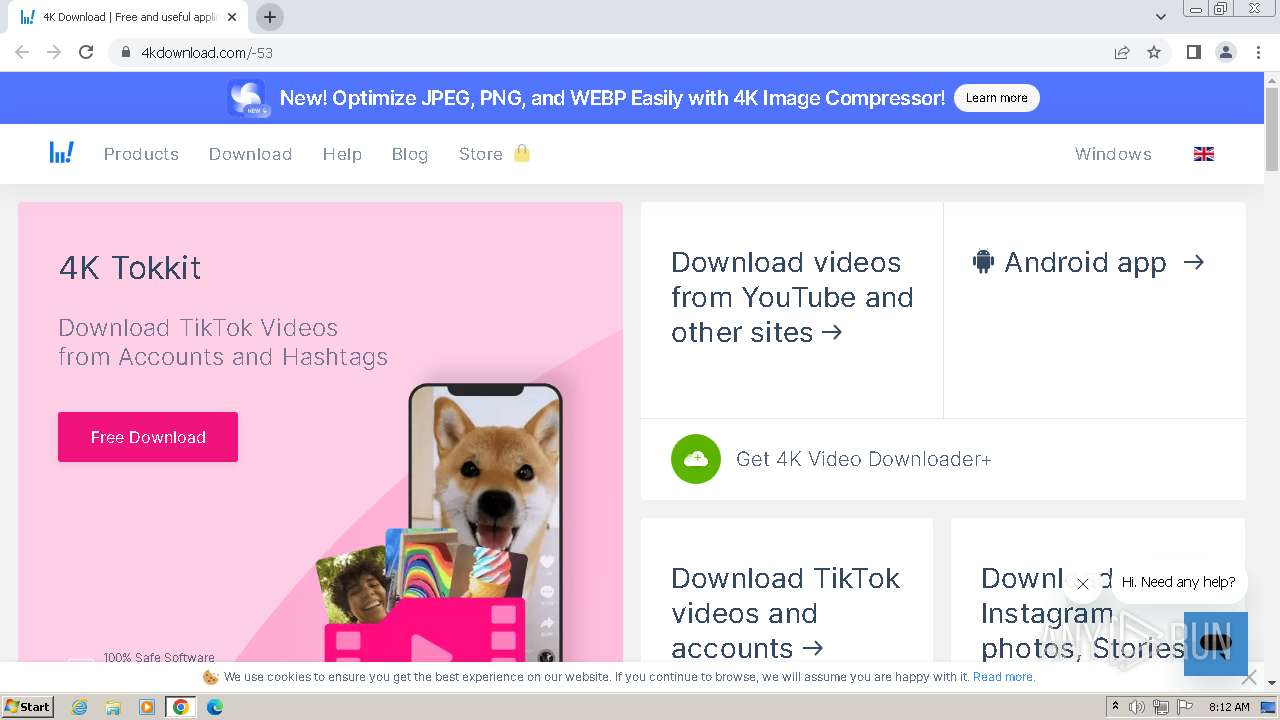
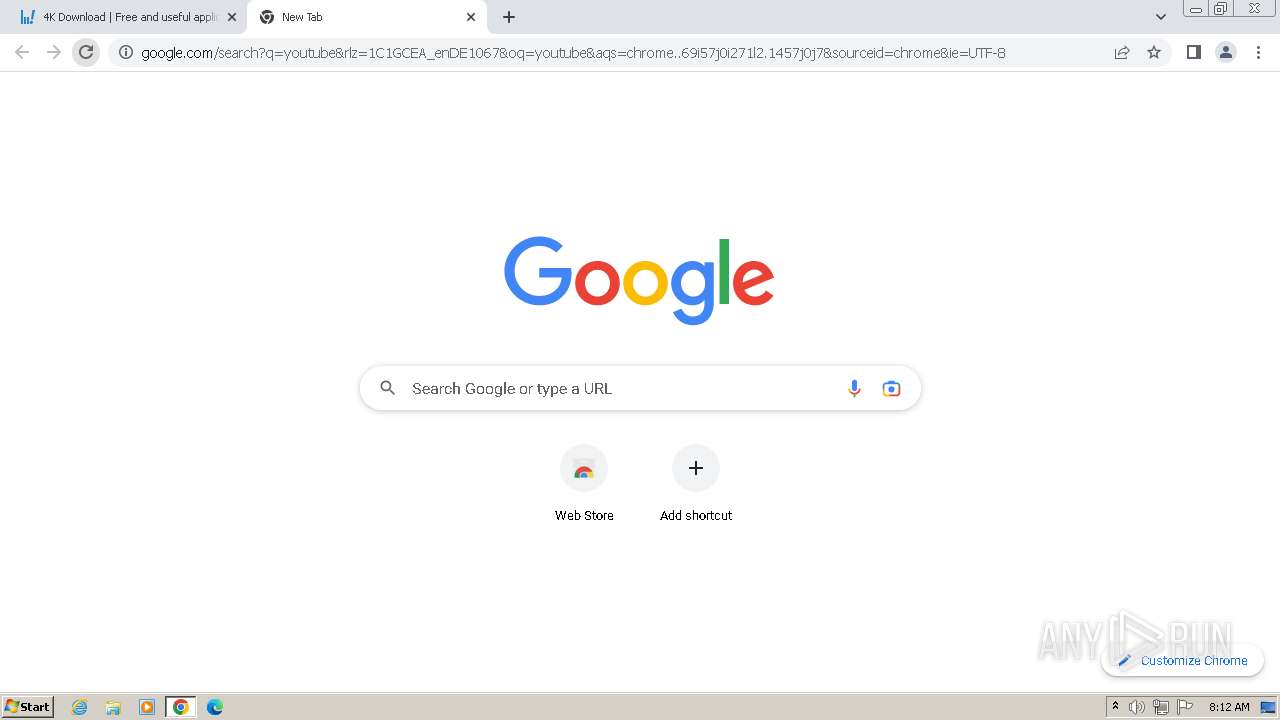
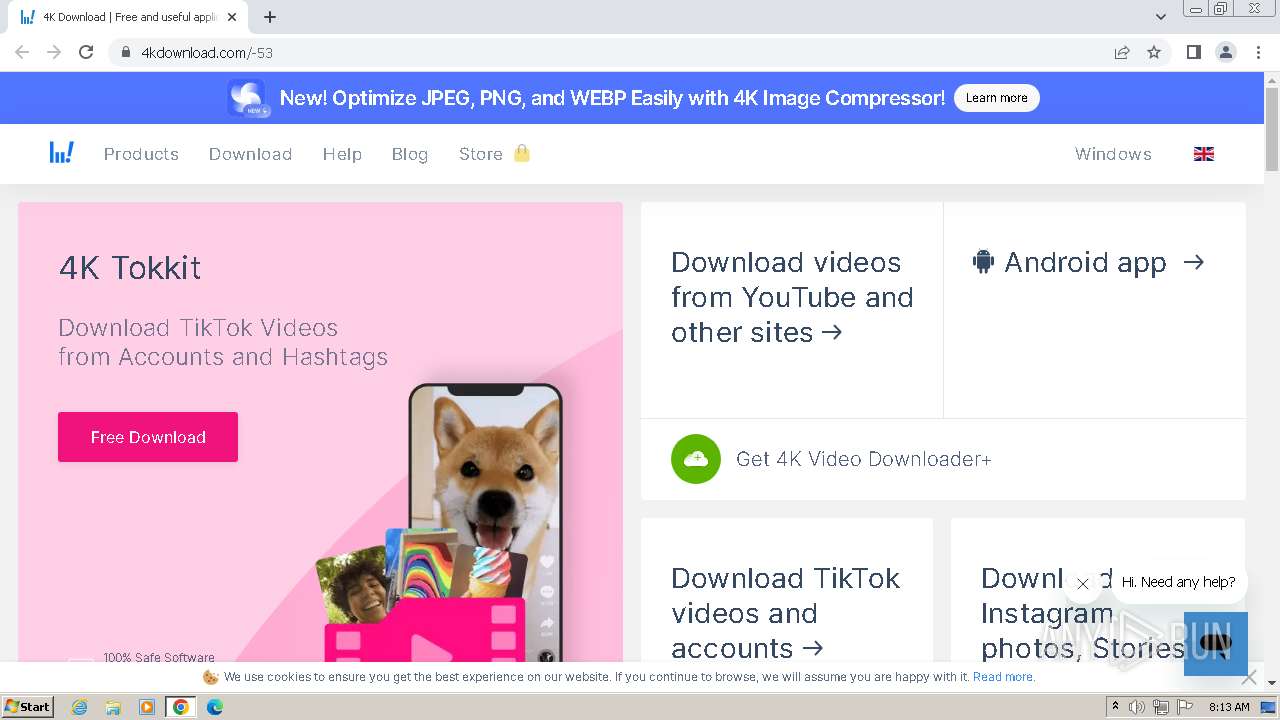
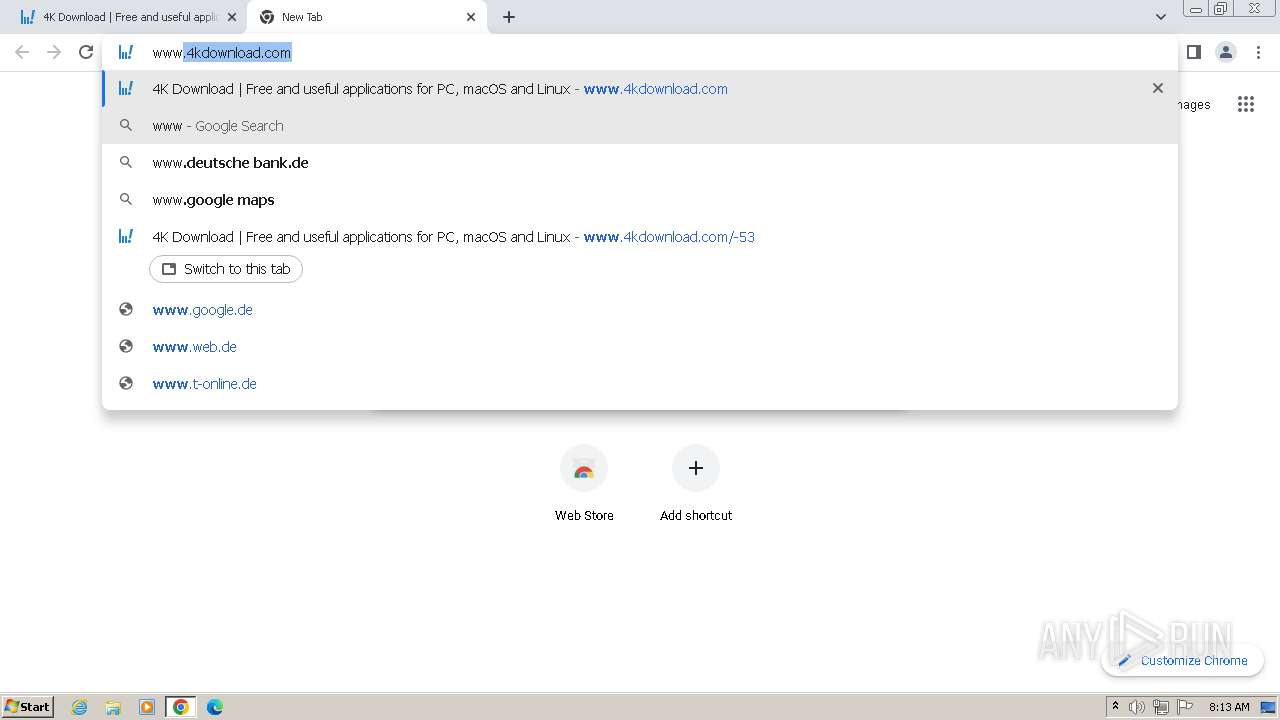
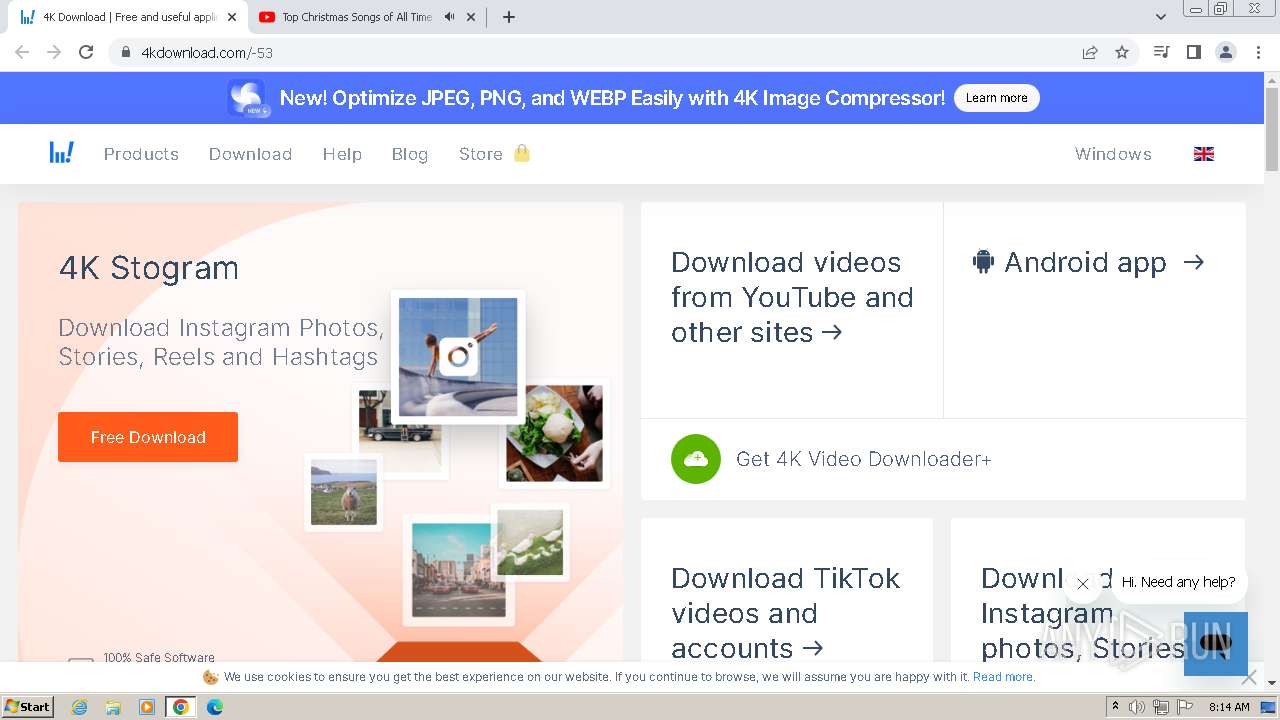
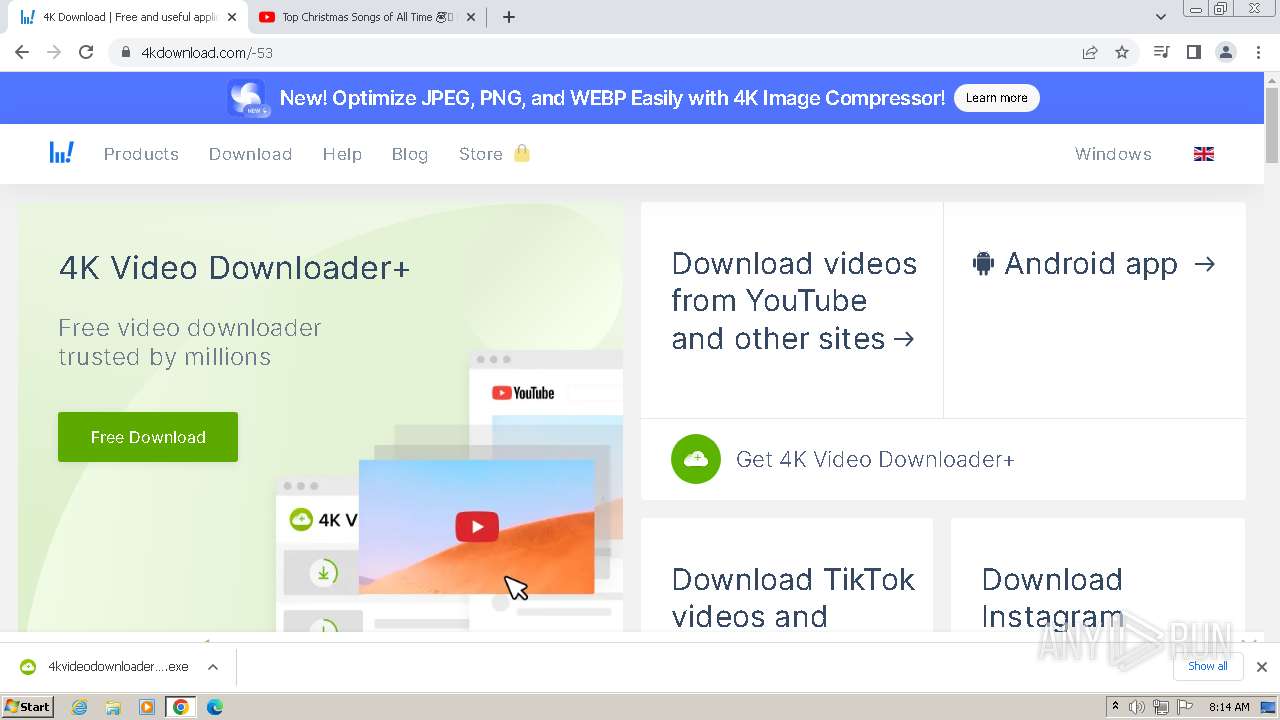
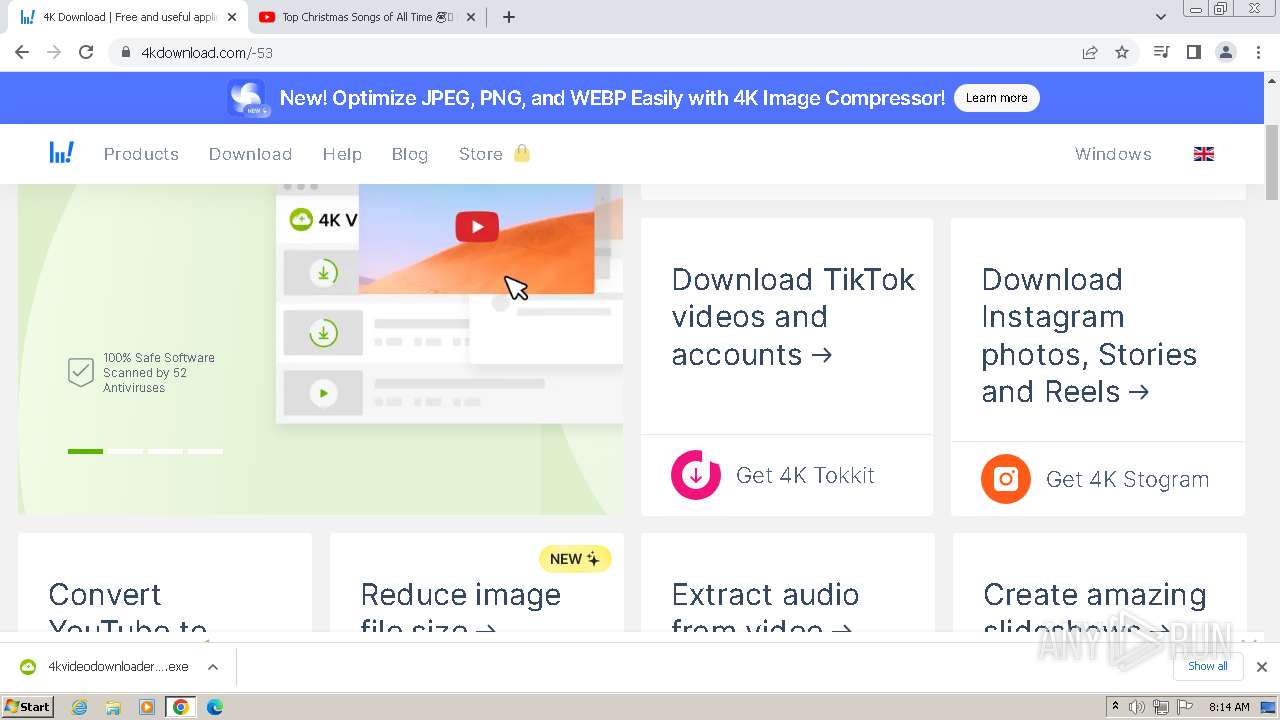
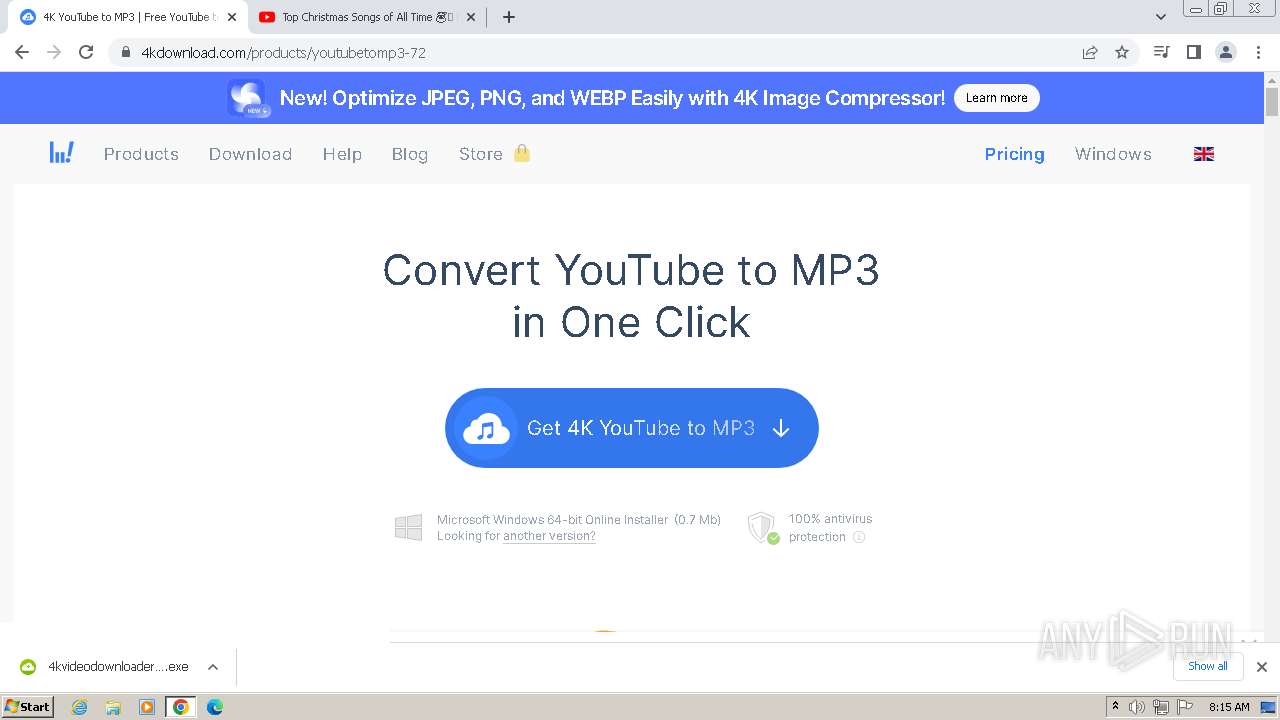
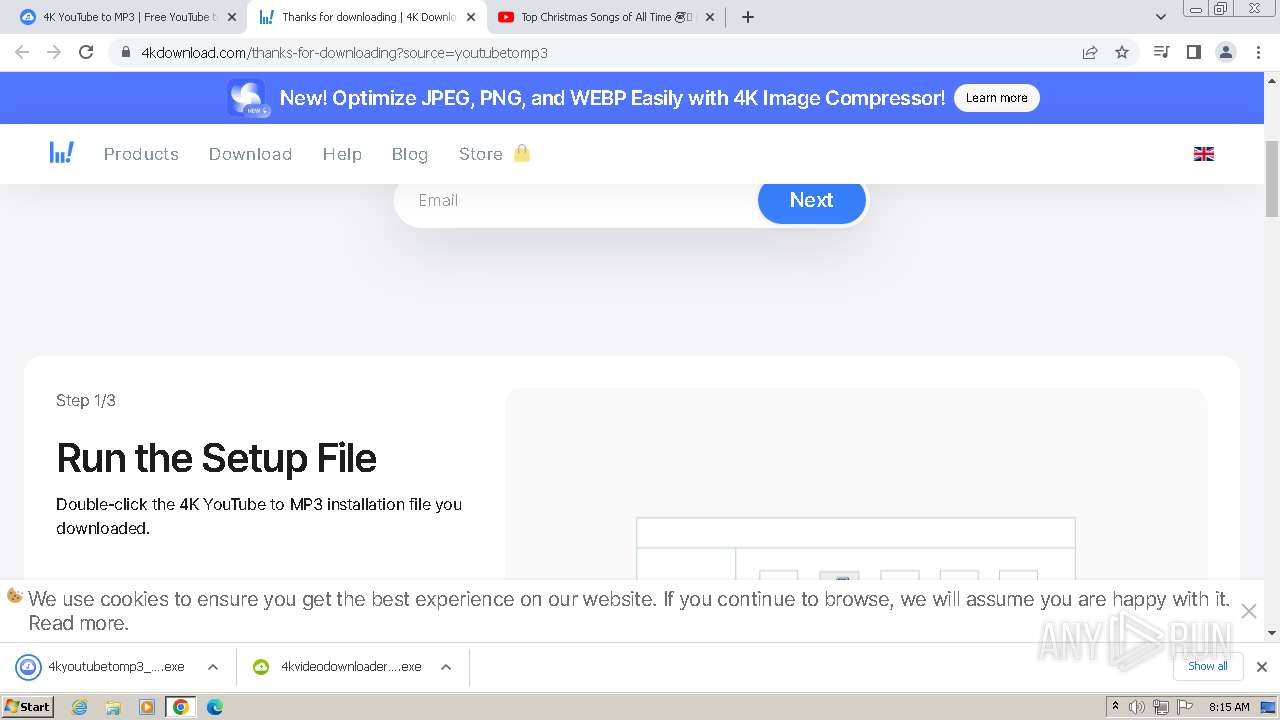
| URL: | www.4kdownload.com |
| Full analysis: | https://app.any.run/tasks/299f3e88-9ea0-4791-aa5f-64b360a96682 |
| Verdict: | Malicious activity |
| Analysis date: | December 05, 2023, 08:11:44 |
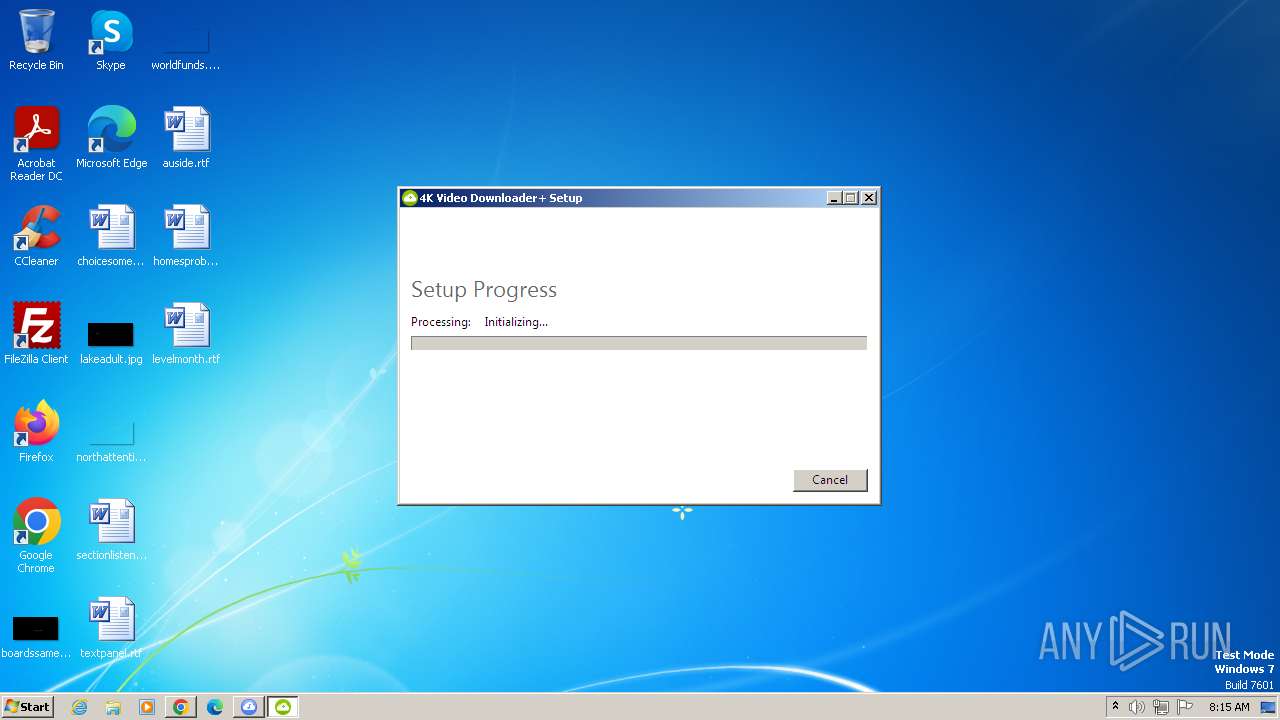
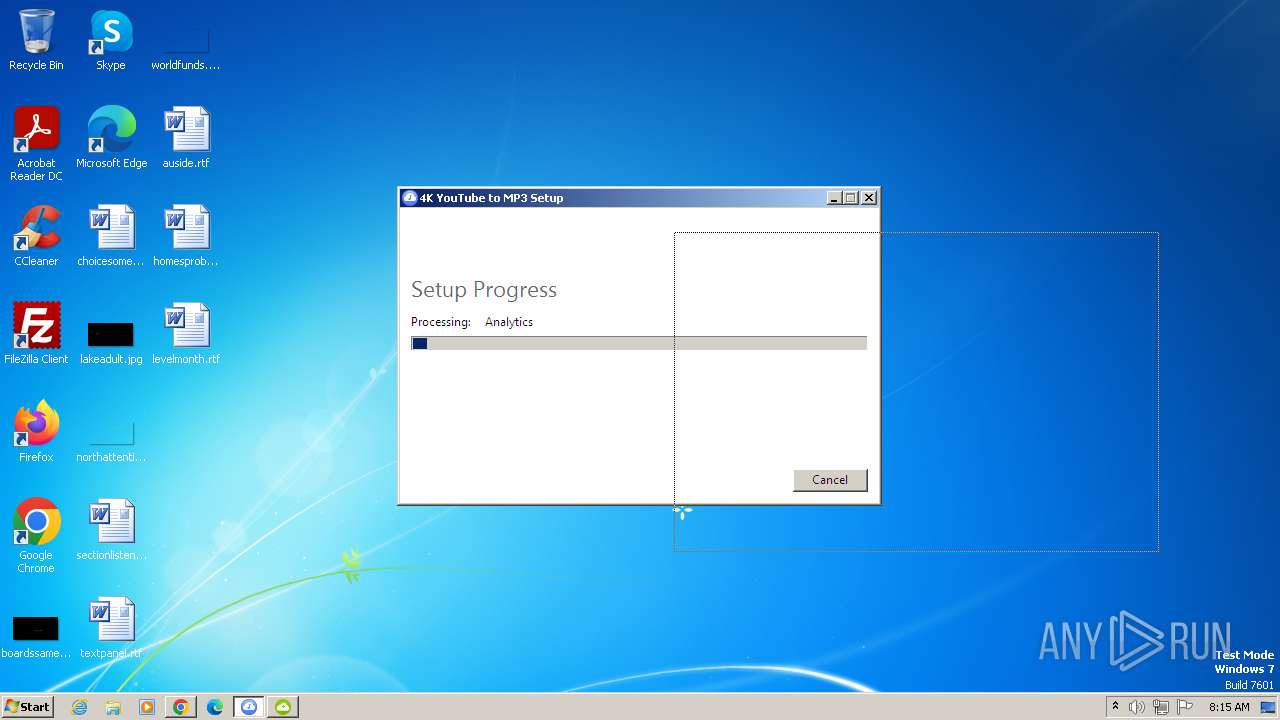
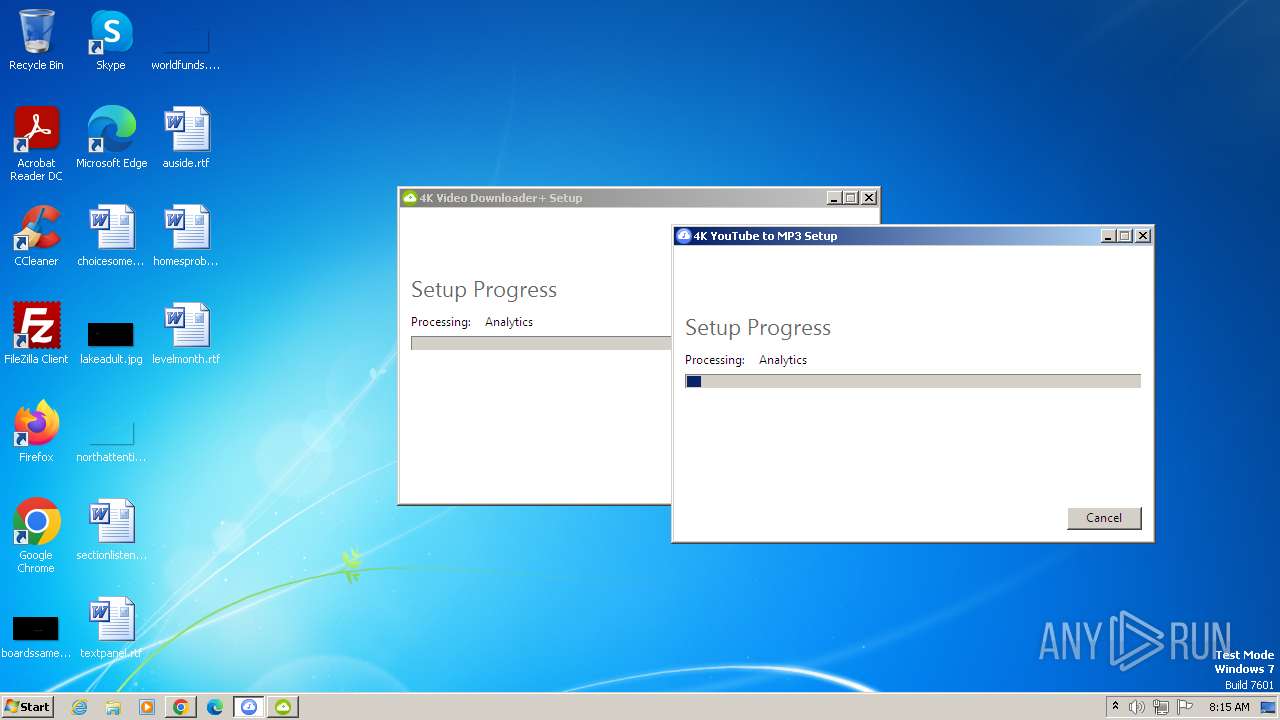
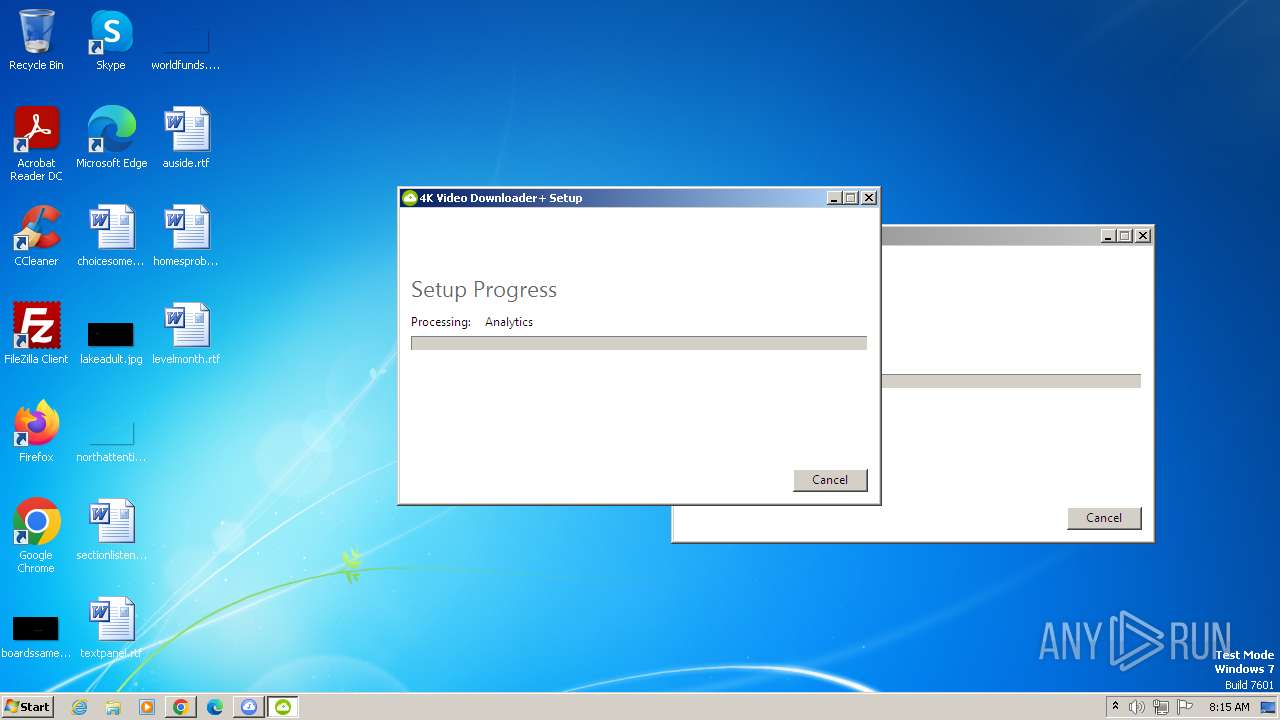
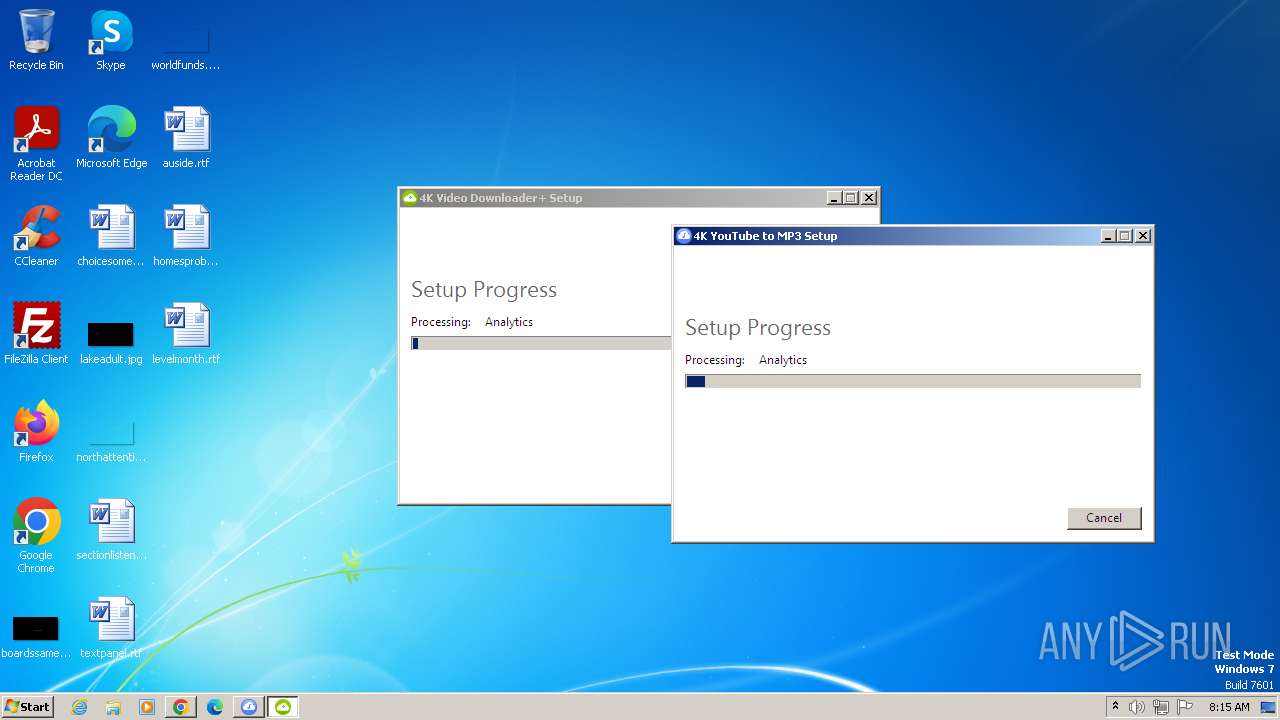
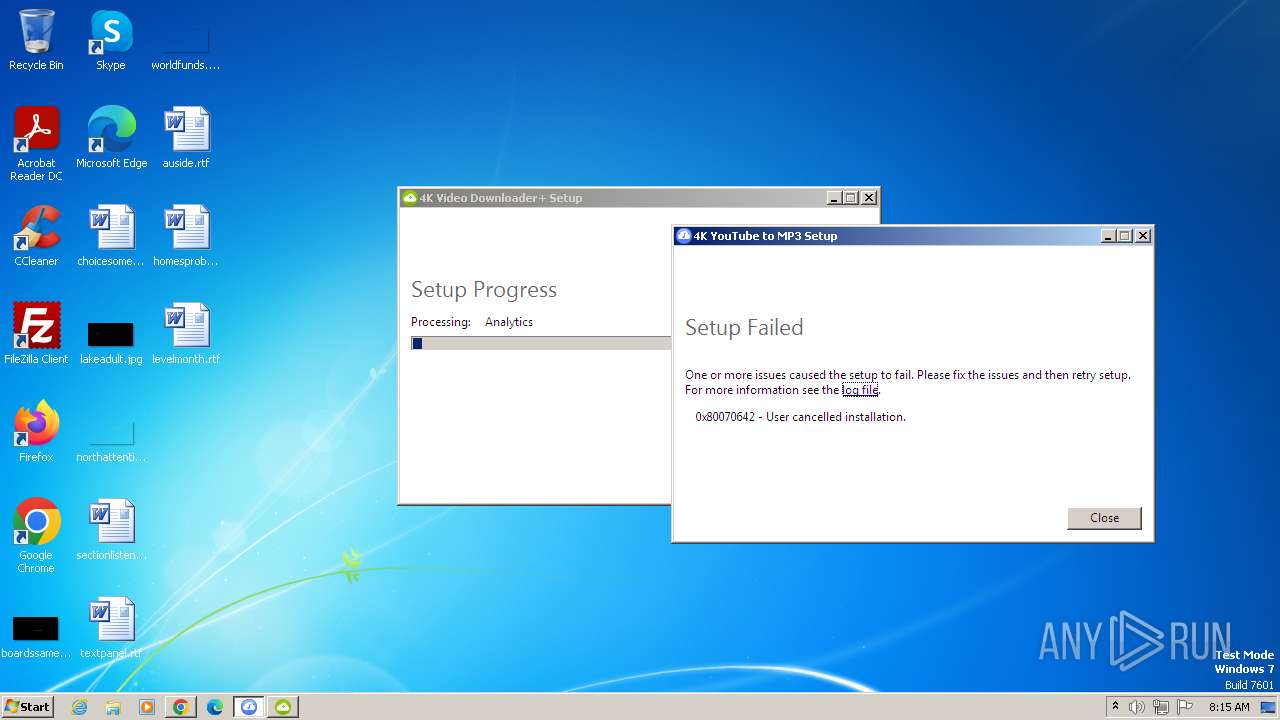
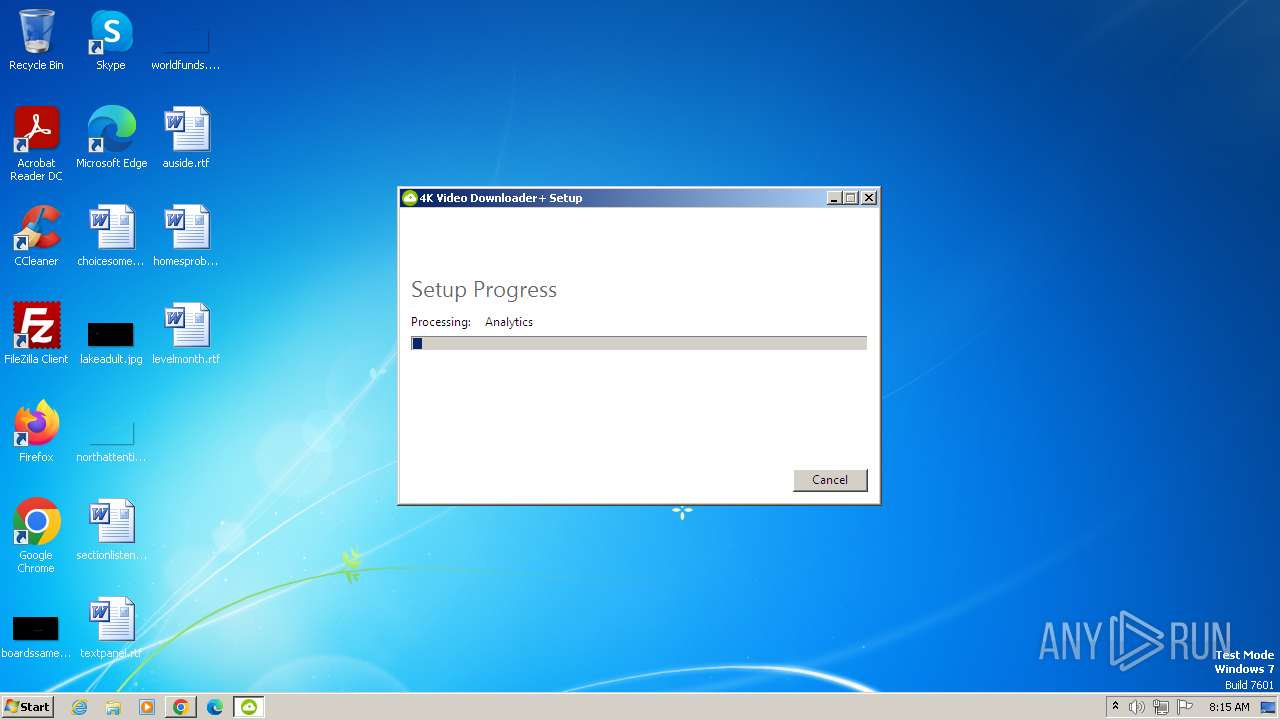
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 059841394C3F755E737B2271BB9B0B5B |
| SHA1: | A9B94CA55203492AEDF590D8455720DEA345A28A |
| SHA256: | B3A9F912ADBBAFA9C4C2AB5D43EE2AEBC5B1C36D1B78DB003354123FF2306758 |
| SSDEEP: | 3:E4JlKn:hnKn |
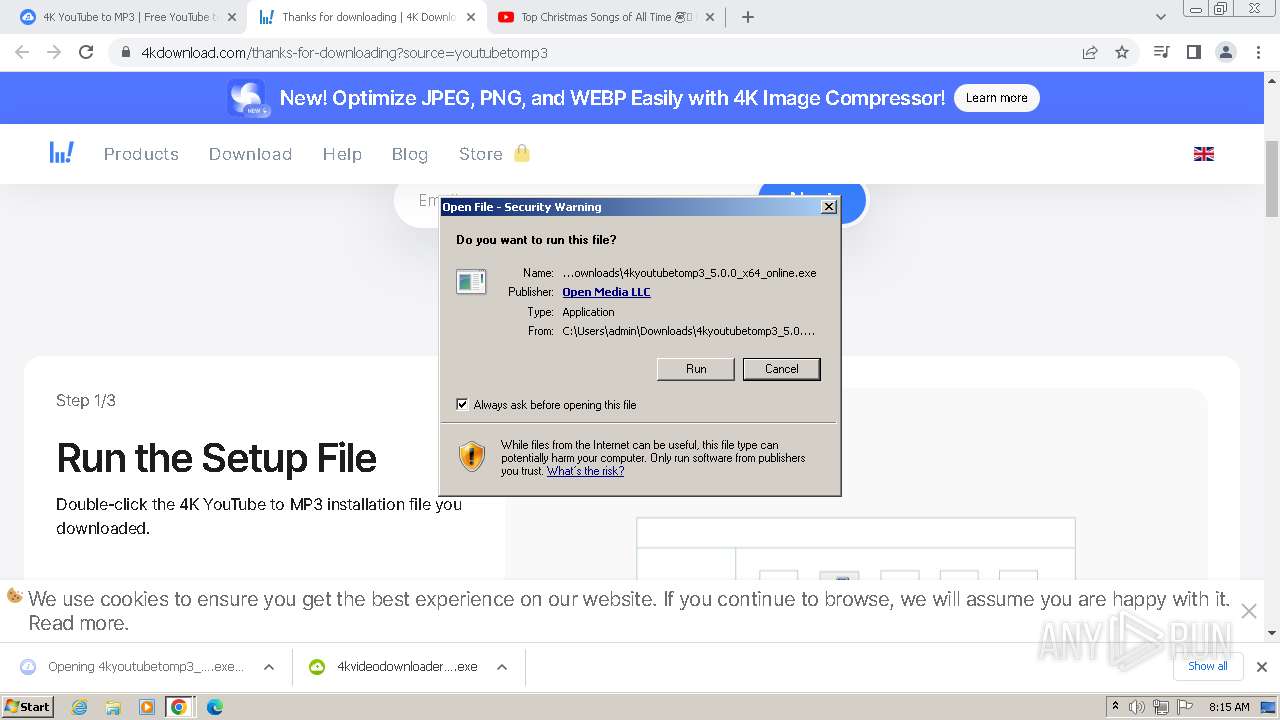
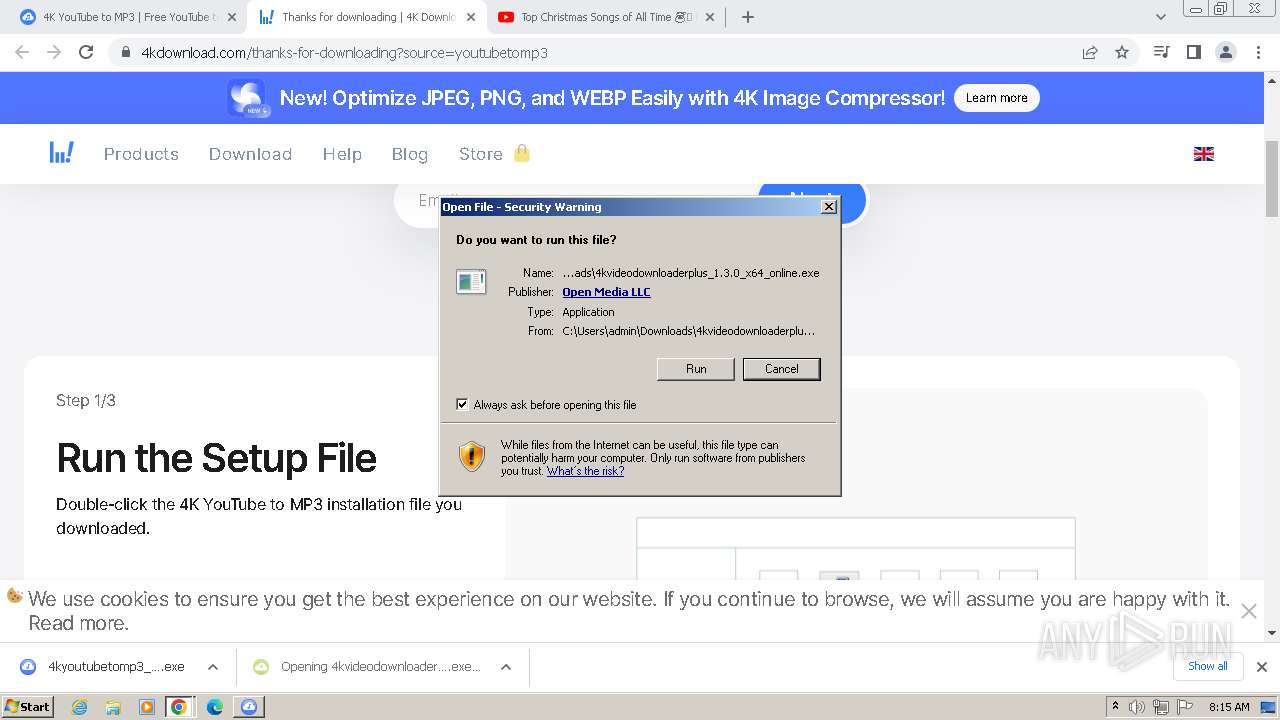
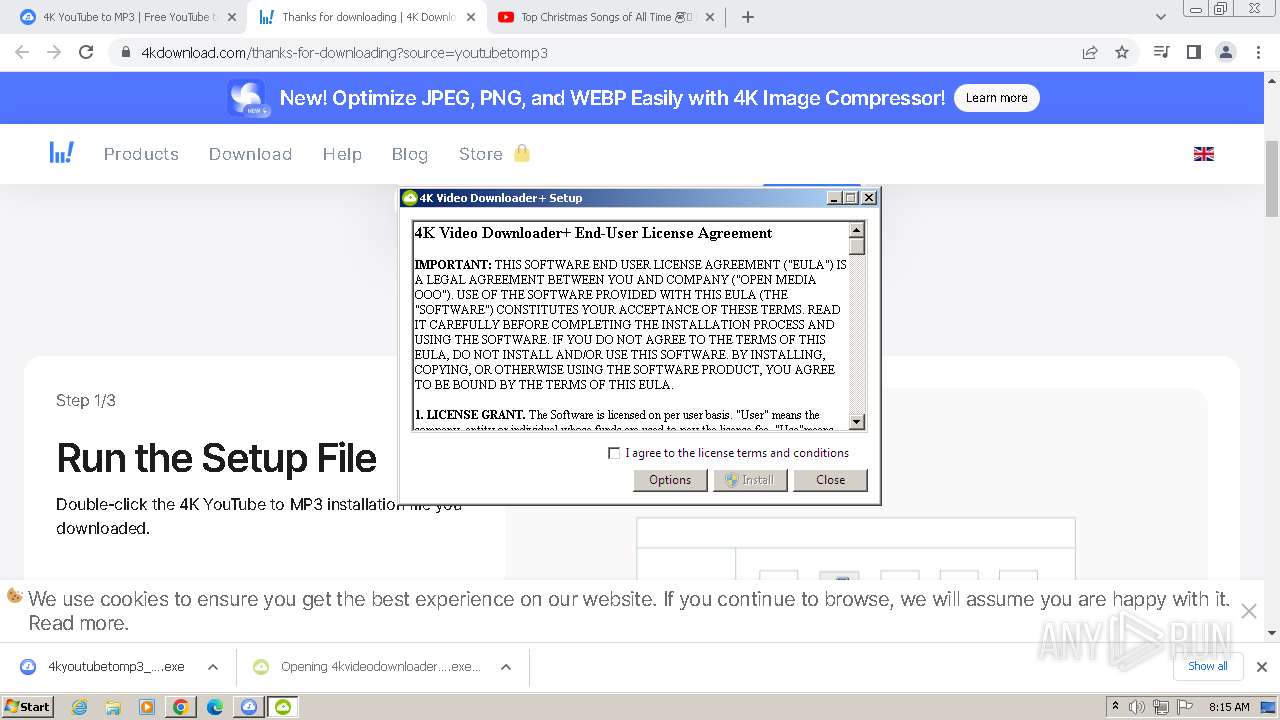
MALICIOUS
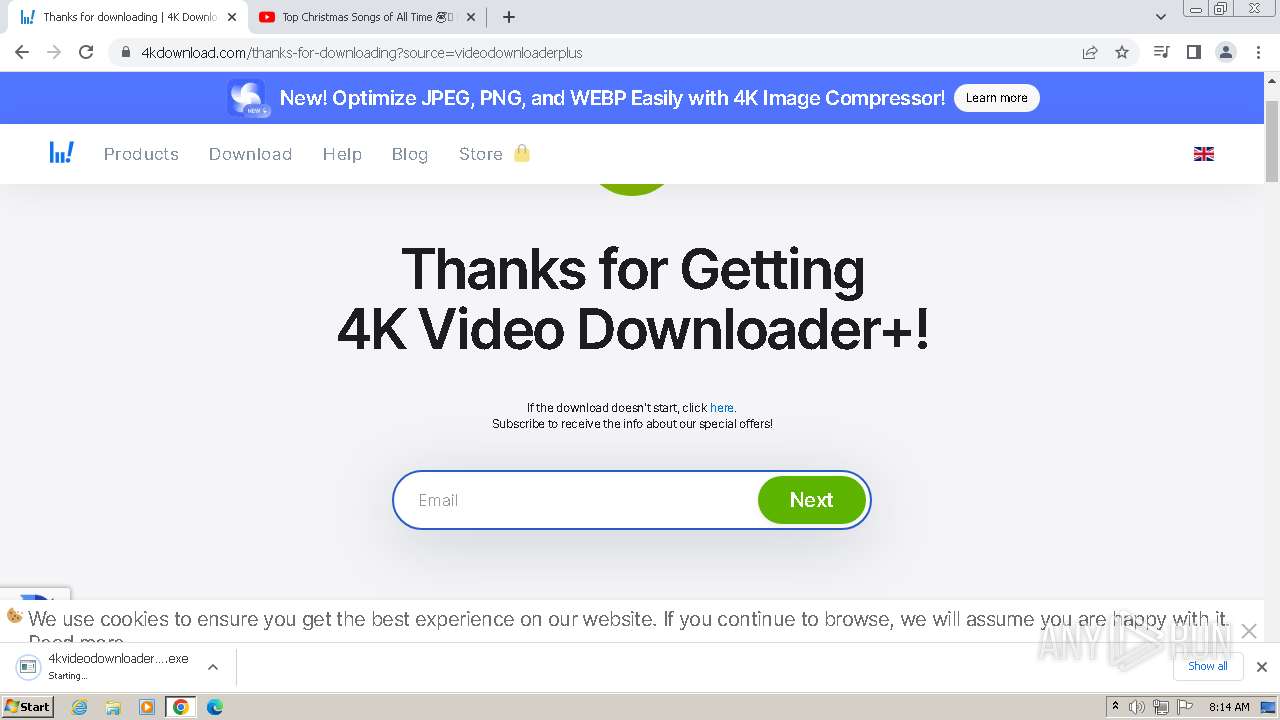
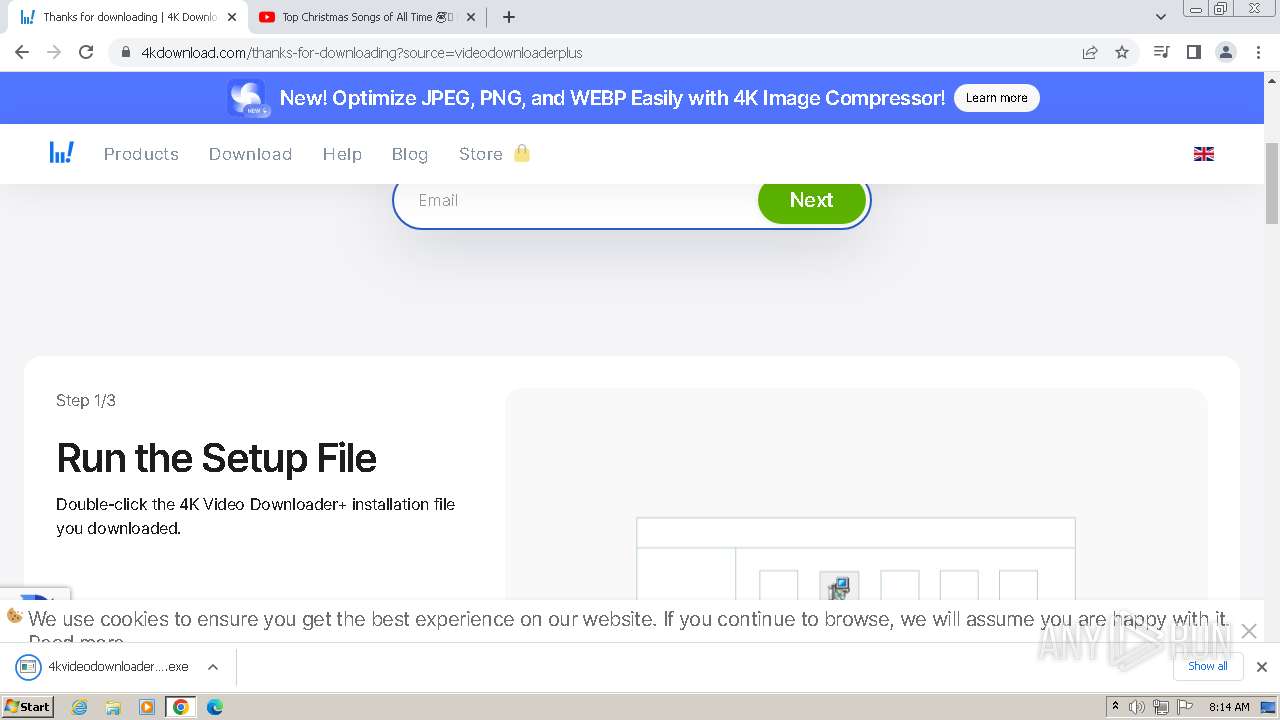
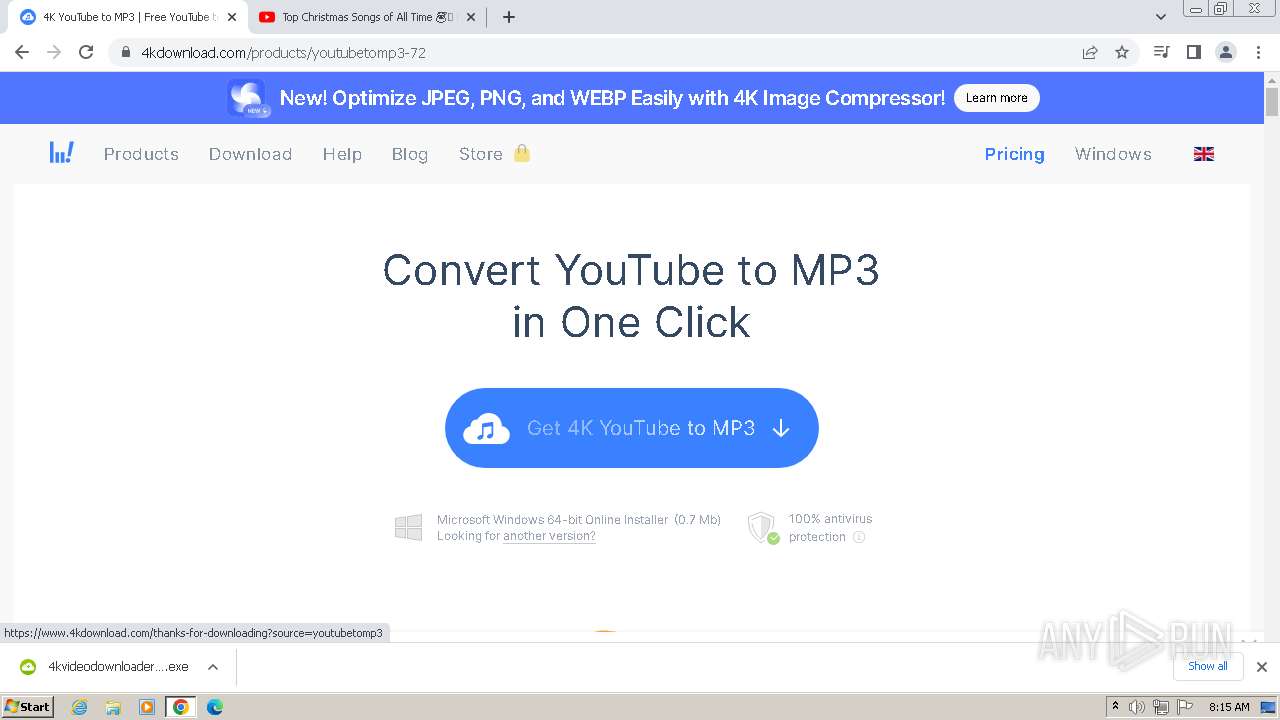
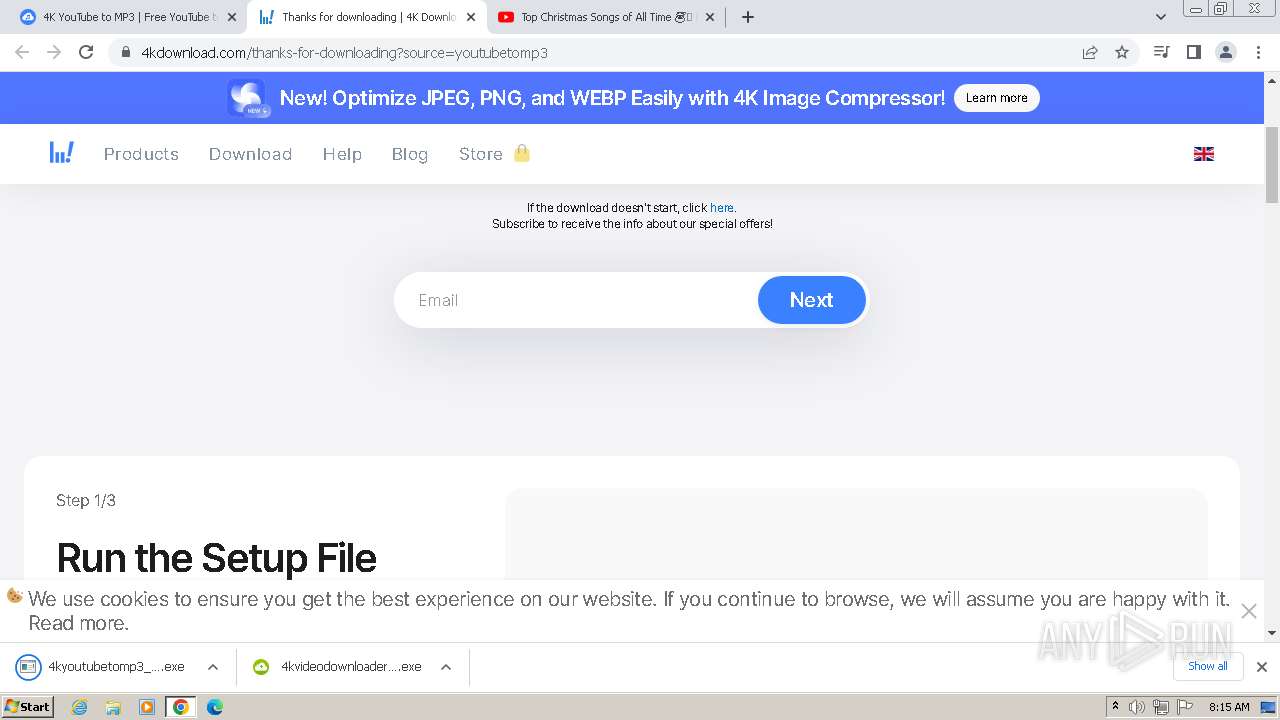
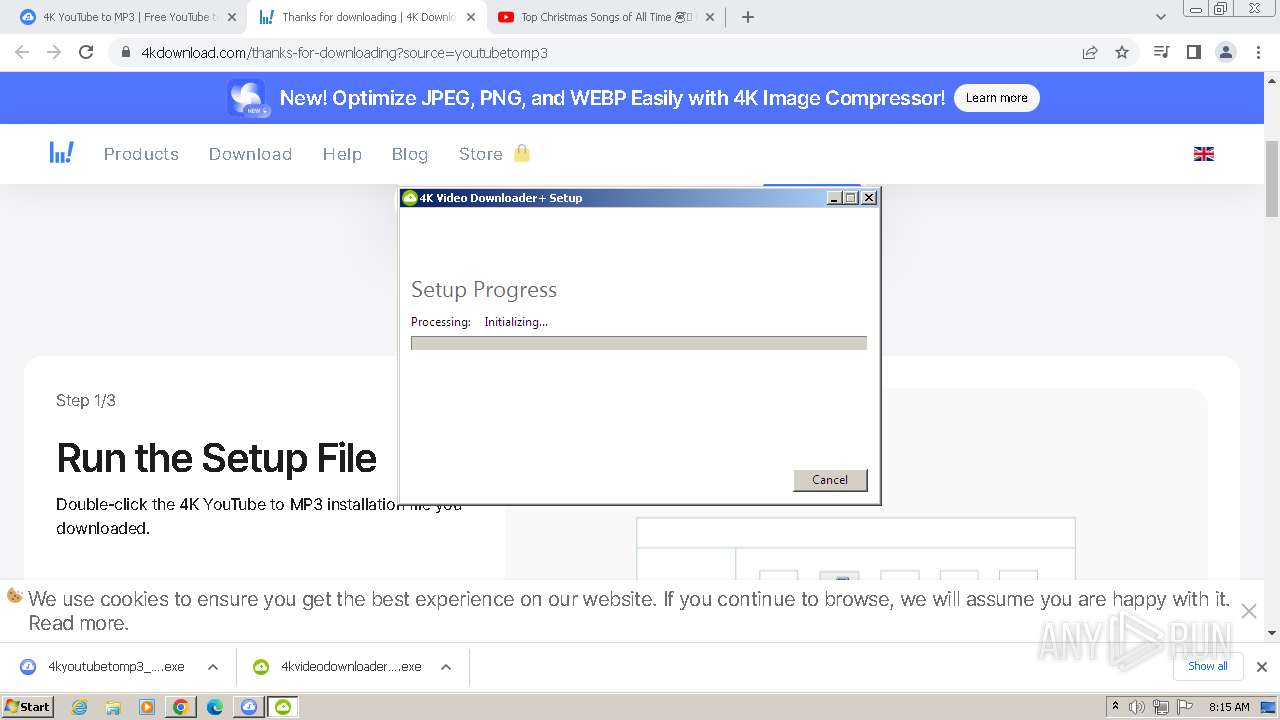
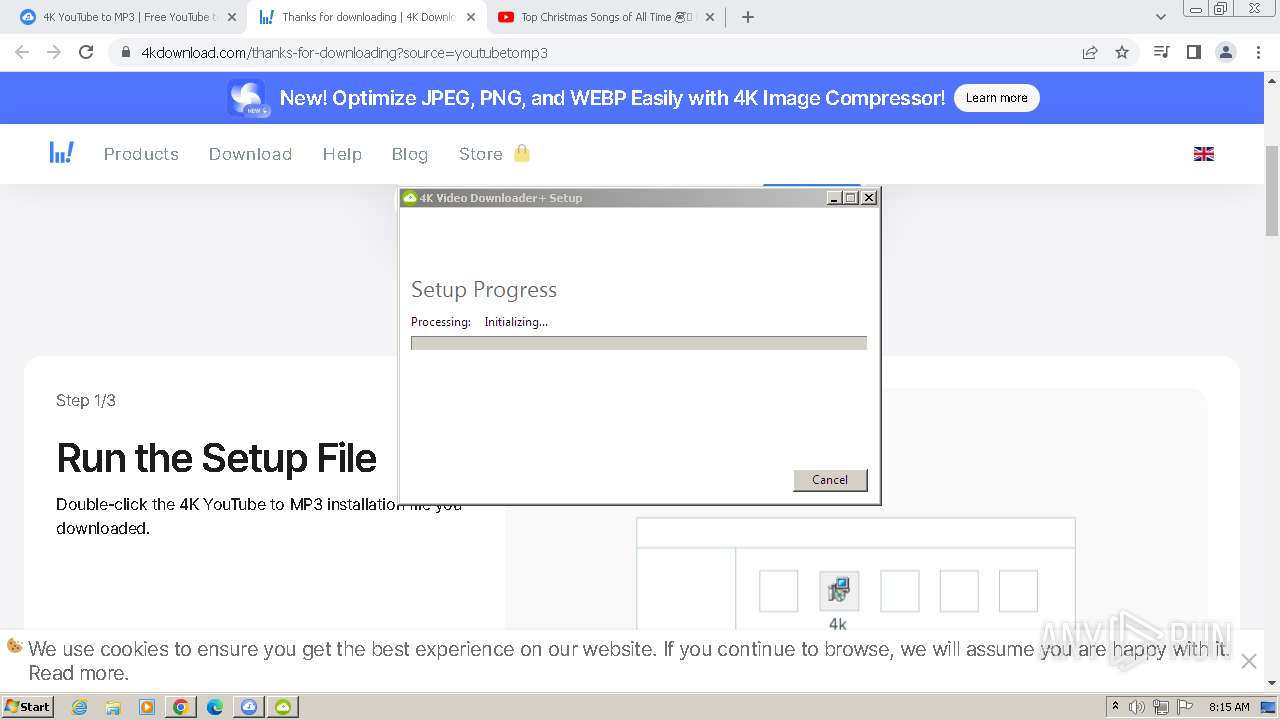
Drops the executable file immediately after the start
- 4kyoutubetomp3_5.0.0_x64_online.exe (PID: 2676)
- 4kyoutubetomp3_5.0.0_x64_online.exe (PID: 188)
- 4kvideodownloaderplus_1.3.0_x64_online.exe (PID: 2912)
- 4kyoutubetomp3_5.0.0_x64_online.exe (PID: 4004)
- 4kvideodownloaderplus_1.3.0_x64_online.exe (PID: 4008)
- 4kvideodownloaderplus_1.3.0_x64_online.exe (PID: 3892)
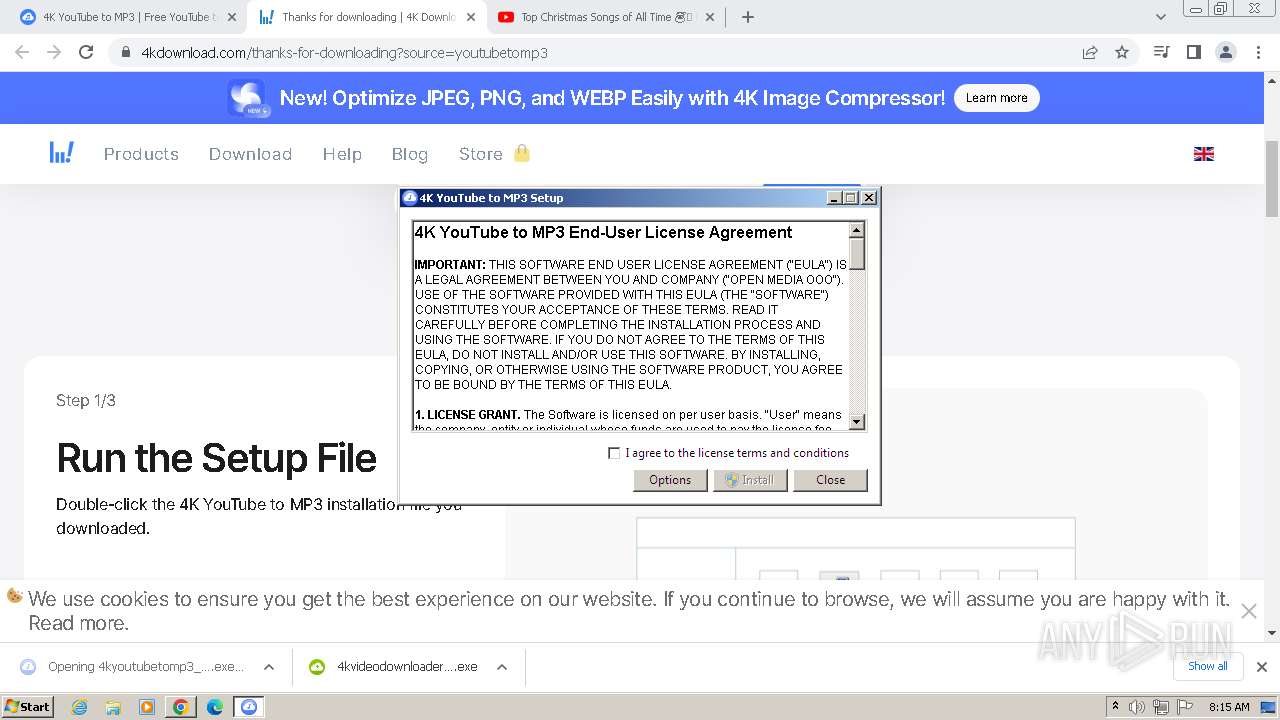
SUSPICIOUS
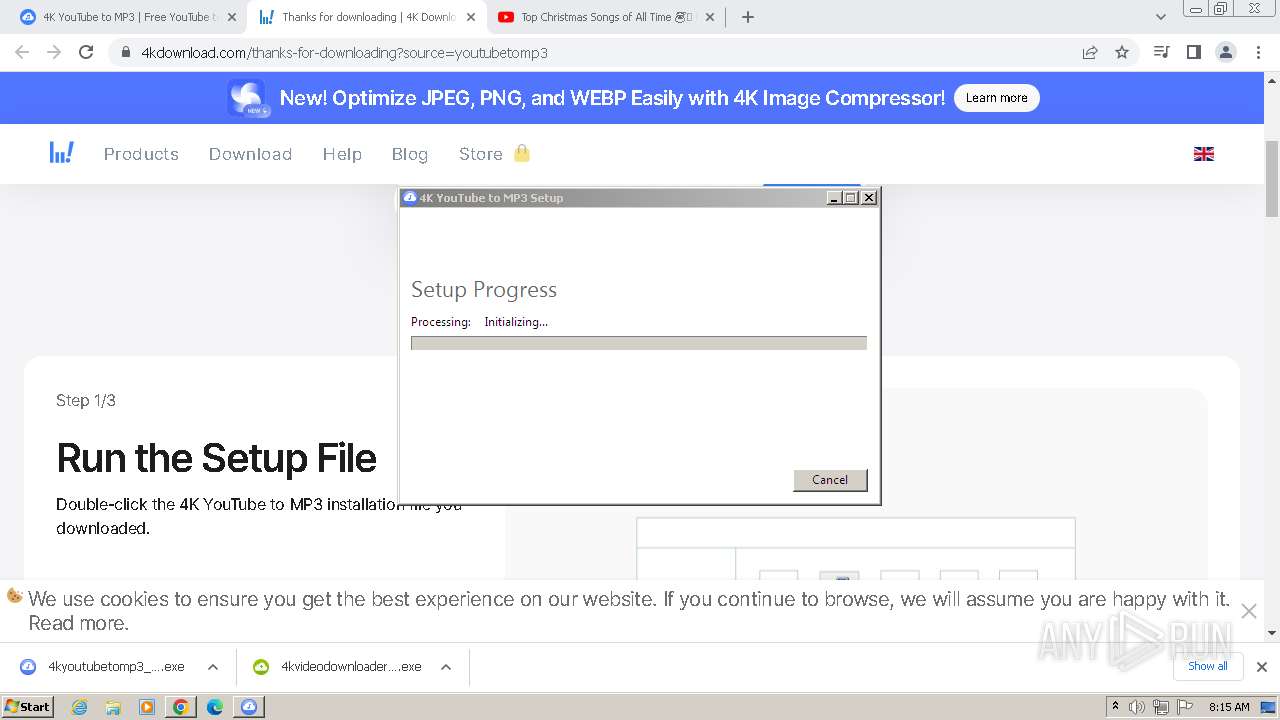
Reads the Internet Settings
- 4kyoutubetomp3_5.0.0_x64_online.exe (PID: 188)
- 4kvideodownloaderplus_1.3.0_x64_online.exe (PID: 2912)
Starts itself from another location
- 4kyoutubetomp3_5.0.0_x64_online.exe (PID: 188)
- 4kvideodownloaderplus_1.3.0_x64_online.exe (PID: 2912)
Searches for installed software
- 4kyoutubetomp3_5.0.0_x64_online.exe (PID: 188)
- 4kyoutubetomp3_5.0.0_x64_online.exe (PID: 4004)
- 4kvideodownloaderplus_1.3.0_x64_online.exe (PID: 3892)
- 4kvideodownloaderplus_1.3.0_x64_online.exe (PID: 2912)
Checks Windows Trust Settings
- 4kyoutubetomp3_5.0.0_x64_online.exe (PID: 188)
- 4kvideodownloaderplus_1.3.0_x64_online.exe (PID: 2912)
- msiexec.exe (PID: 2344)
Reads security settings of Internet Explorer
- 4kyoutubetomp3_5.0.0_x64_online.exe (PID: 188)
- 4kvideodownloaderplus_1.3.0_x64_online.exe (PID: 2912)
Executes as Windows Service
- VSSVC.exe (PID: 3512)
Reads settings of System Certificates
- 4kyoutubetomp3_5.0.0_x64_online.exe (PID: 188)
- 4kvideodownloaderplus_1.3.0_x64_online.exe (PID: 2912)
Adds/modifies Windows certificates
- msiexec.exe (PID: 2344)
INFO
Checks supported languages
- wmpnscfg.exe (PID: 2224)
- 4kyoutubetomp3_5.0.0_x64_online.exe (PID: 2676)
- 4kyoutubetomp3_5.0.0_x64_online.exe (PID: 188)
- 4kyoutubetomp3_5.0.0_x64_online.exe (PID: 4004)
- 4kvideodownloaderplus_1.3.0_x64_online.exe (PID: 4008)
- 4kvideodownloaderplus_1.3.0_x64_online.exe (PID: 2912)
- 4kvideodownloaderplus_1.3.0_x64_online.exe (PID: 3892)
- msiexec.exe (PID: 2344)
Reads the computer name
- wmpnscfg.exe (PID: 2224)
- 4kyoutubetomp3_5.0.0_x64_online.exe (PID: 188)
- 4kyoutubetomp3_5.0.0_x64_online.exe (PID: 4004)
- 4kvideodownloaderplus_1.3.0_x64_online.exe (PID: 3892)
- 4kvideodownloaderplus_1.3.0_x64_online.exe (PID: 2912)
- msiexec.exe (PID: 2344)
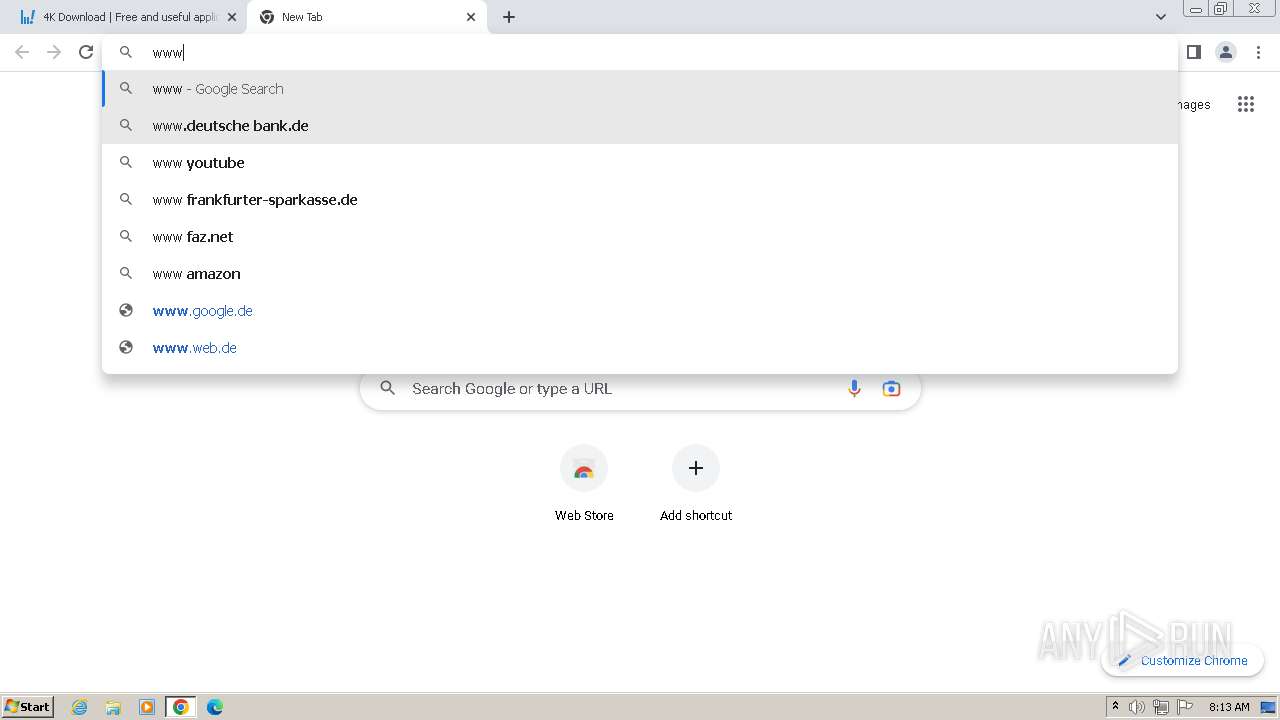
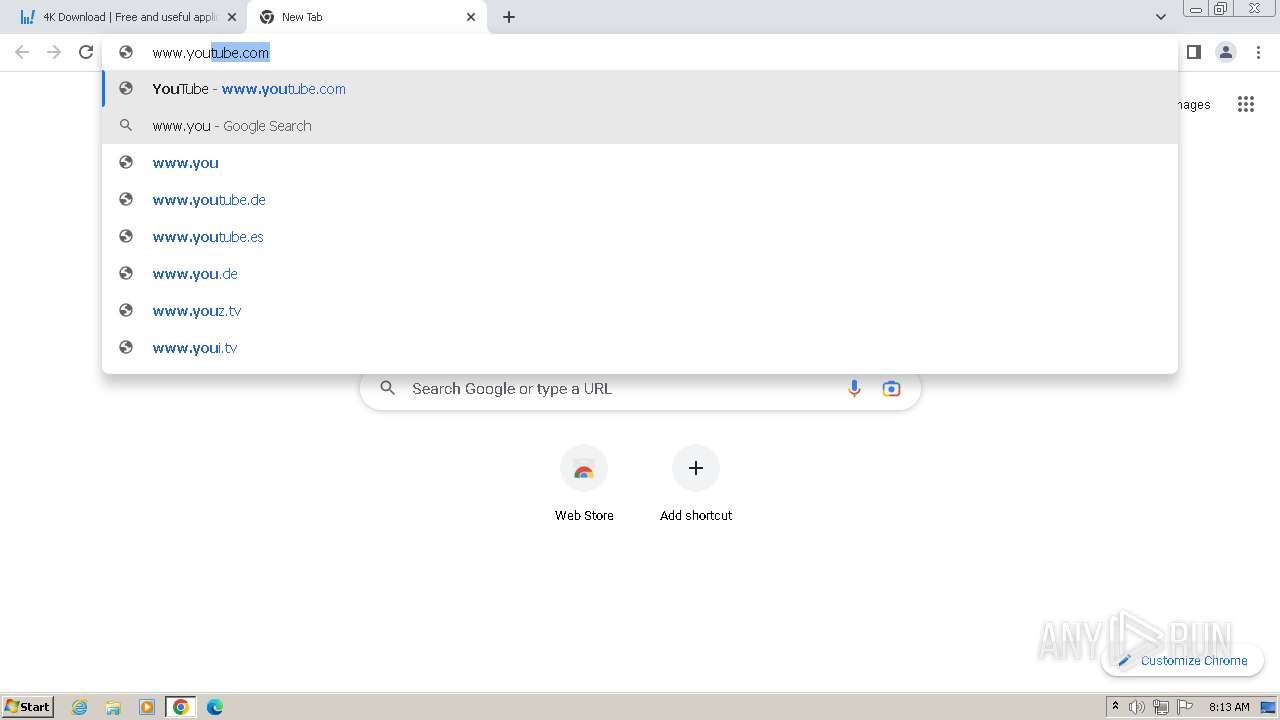
The process uses the downloaded file
- chrome.exe (PID: 1452)
- chrome.exe (PID: 1452)
- chrome.exe (PID: 3612)
- chrome.exe (PID: 2740)
- chrome.exe (PID: 2472)
- chrome.exe (PID: 3432)
Create files in a temporary directory
- 4kyoutubetomp3_5.0.0_x64_online.exe (PID: 2676)
- 4kyoutubetomp3_5.0.0_x64_online.exe (PID: 188)
- 4kvideodownloaderplus_1.3.0_x64_online.exe (PID: 4008)
- 4kvideodownloaderplus_1.3.0_x64_online.exe (PID: 2912)
- 4kvideodownloaderplus_1.3.0_x64_online.exe (PID: 3892)
Drops the executable file immediately after the start
- chrome.exe (PID: 2740)
- chrome.exe (PID: 2128)
Manual execution by a user
- wmpnscfg.exe (PID: 2224)
Reads the machine GUID from the registry
- 4kyoutubetomp3_5.0.0_x64_online.exe (PID: 188)
- 4kyoutubetomp3_5.0.0_x64_online.exe (PID: 4004)
- 4kvideodownloaderplus_1.3.0_x64_online.exe (PID: 2912)
- 4kvideodownloaderplus_1.3.0_x64_online.exe (PID: 3892)
- msiexec.exe (PID: 2344)
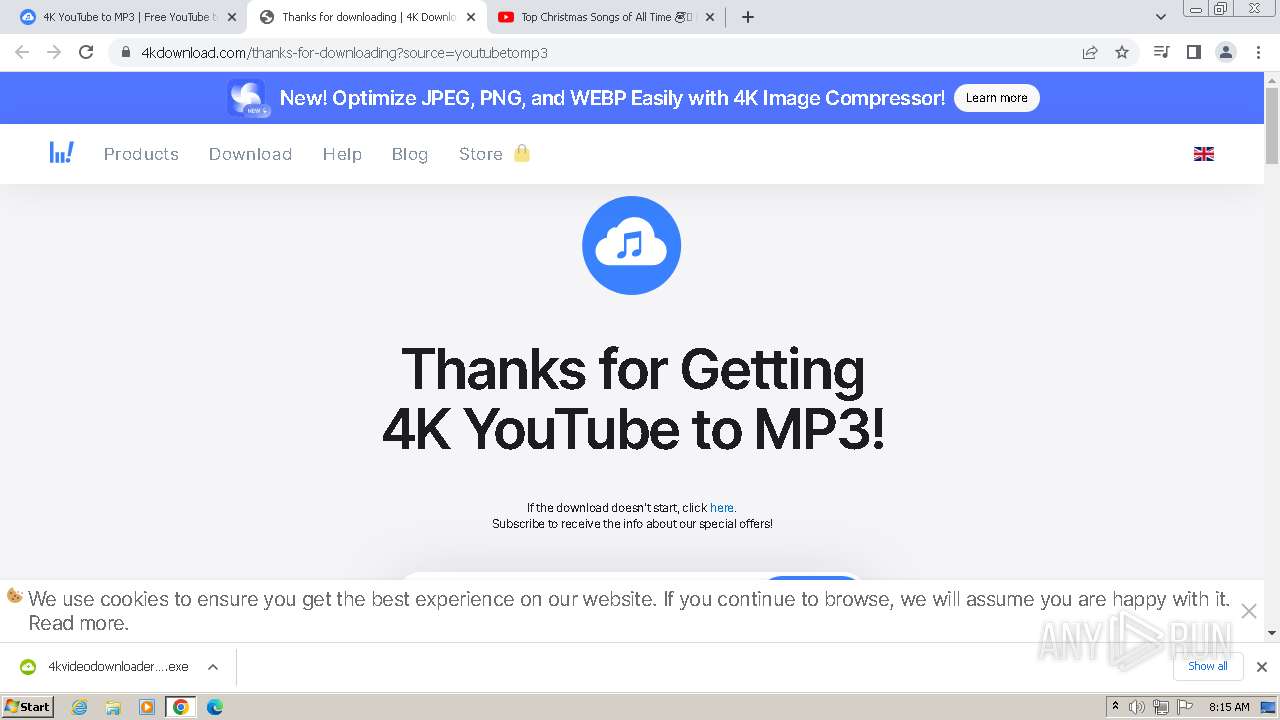
Application launched itself
- chrome.exe (PID: 2740)
Checks proxy server information
- 4kyoutubetomp3_5.0.0_x64_online.exe (PID: 188)
- 4kvideodownloaderplus_1.3.0_x64_online.exe (PID: 2912)
Creates files in the program directory
- 4kyoutubetomp3_5.0.0_x64_online.exe (PID: 4004)
- 4kvideodownloaderplus_1.3.0_x64_online.exe (PID: 3892)
Creates files or folders in the user directory
- 4kyoutubetomp3_5.0.0_x64_online.exe (PID: 188)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
117
Monitored processes
70
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
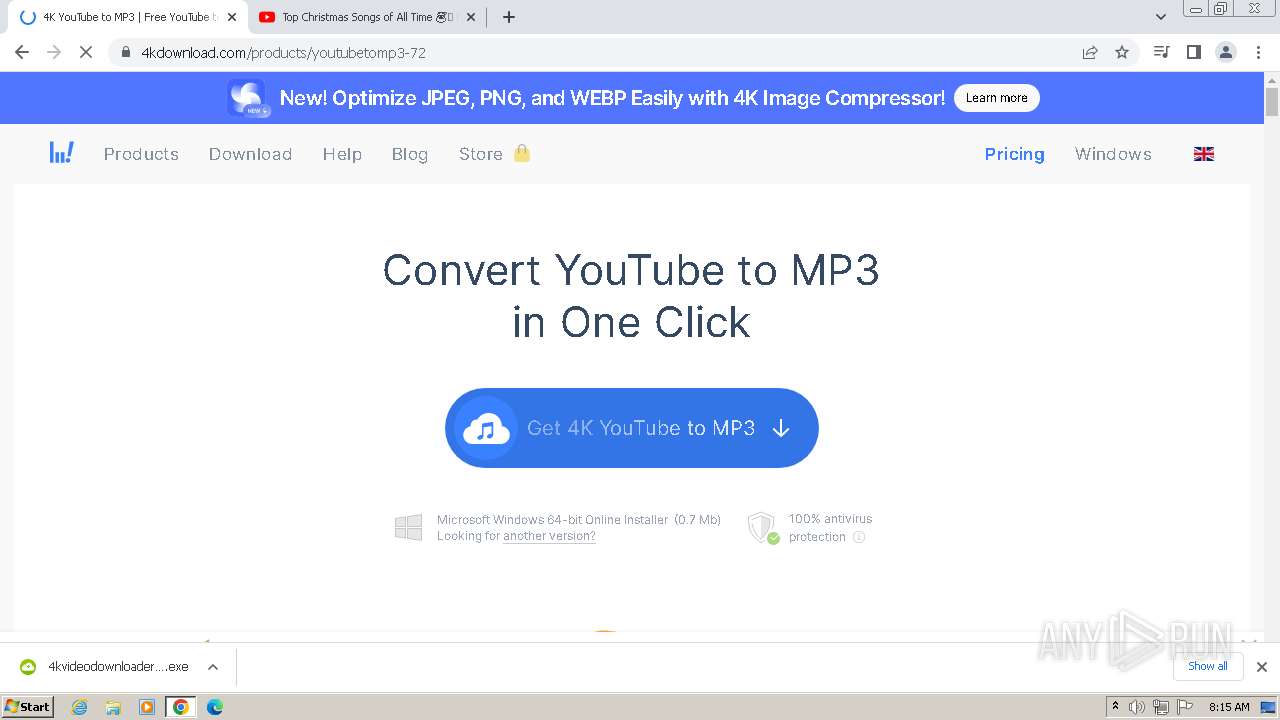
| 188 | "C:\Users\admin\AppData\Local\Temp\{22CA00F5-64BE-4F1E-83B7-83CF9790AA1A}\.cr\4kyoutubetomp3_5.0.0_x64_online.exe" -burn.clean.room="C:\Users\admin\Downloads\4kyoutubetomp3_5.0.0_x64_online.exe" -burn.filehandle.attached=152 -burn.filehandle.self=160 | C:\Users\admin\AppData\Local\Temp\{22CA00F5-64BE-4F1E-83B7-83CF9790AA1A}\.cr\4kyoutubetomp3_5.0.0_x64_online.exe | 4kyoutubetomp3_5.0.0_x64_online.exe | ||||||||||||
User: admin Company: Open Media LLC Integrity Level: MEDIUM Description: 4K YouTube to MP3 Exit code: 1602 Version: 5.0.0.48 Modules
| |||||||||||||||
| 296 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=20 --mojo-platform-channel-handle=3536 --field-trial-handle=1096,i,17791609640188415076,8584844338878508010,131072 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 564 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --mojo-platform-channel-handle=4612 --field-trial-handle=1096,i,17791609640188415076,8584844338878508010,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 668 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=21 --mojo-platform-channel-handle=3688 --field-trial-handle=1096,i,17791609640188415076,8584844338878508010,131072 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 824 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=40 --mojo-platform-channel-handle=4512 --field-trial-handle=1096,i,17791609640188415076,8584844338878508010,131072 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 844 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=41 --mojo-platform-channel-handle=1444 --field-trial-handle=1096,i,17791609640188415076,8584844338878508010,131072 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1028 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --mojo-platform-channel-handle=596 --field-trial-handle=1096,i,17791609640188415076,8584844338878508010,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1448 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=3936 --field-trial-handle=1096,i,17791609640188415076,8584844338878508010,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1452 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=3536 --field-trial-handle=1096,i,17791609640188415076,8584844338878508010,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1452 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=4904 --field-trial-handle=1096,i,17791609640188415076,8584844338878508010,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
26 575
Read events
26 146
Write events
417
Delete events
12
Modification events
| (PID) Process: | (2740) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2740) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2740) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2740) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2740) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2740) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
| (PID) Process: | (2740) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2740) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2740) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
| (PID) Process: | (2740) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_enableddate |
Value: 0 | |||
Executable files
28
Suspicious files
412
Text files
66
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2740 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF206c5a.TMP | — | |
MD5:— | SHA256:— | |||
| 2740 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2740 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 2740 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF207b7d.TMP | — | |
MD5:— | SHA256:— | |||
| 2740 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2740 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF206c5a.TMP | text | |
MD5:E91E138A25FD7E5BCA5E60111F39C91A | SHA256:B1F7E3537A31A4B847F862858E5D2581993CC9372F19ABF19EA2A9185FE42A4F | |||
| 2740 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF206c5a.TMP | text | |
MD5:513218482935B0D388C0A990D868387A | SHA256:8E39CBAAF4AACC3A01AFA74EA8C30FB24FE69A22B8B30728AFB1614FD68809D9 | |||
| 2740 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | text | |
MD5:05387A3C4FCF1F3B992FF9FBF045AA1A | SHA256:B01E9451B8F6ABF03C9CD2E158C02D0A6BFDF771944F5D0B96DAD2DA6A7E3C8F | |||
| 2740 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Extension State\LOG.old~RF206d83.TMP | text | |
MD5:ACAE205AB6BCFD21F8AC19ABBC47BC6A | SHA256:4972E7A3802340F7C5C214DD0CAC645F537BA6937F38CCCC36B0CACEF079F41E | |||
| 2740 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\optimization_guide_model_metadata_store\LOG.old~RF208b1d.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
31
TCP/UDP connections
152
DNS requests
178
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
868 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acu5zi2wnmdcfm7b3qeiu6ibn7ja_423/lmelglejhemejginpboagddgdfbepgmp_423_all_ZZ_bnthb7ria3cilcte5iosztqgn4.crx3 | US | — | — | unknown |
188 | 4kyoutubetomp3_5.0.0_x64_online.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?a3d1dd9738e9f1f1 | GB | compressed | 4.66 Kb | unknown |
188 | 4kyoutubetomp3_5.0.0_x64_online.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?7d99794ed5015127 | GB | compressed | 65.2 Kb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acu5zi2wnmdcfm7b3qeiu6ibn7ja_423/lmelglejhemejginpboagddgdfbepgmp_423_all_ZZ_bnthb7ria3cilcte5iosztqgn4.crx3 | US | binary | 6.00 Kb | unknown |
188 | 4kyoutubetomp3_5.0.0_x64_online.exe | GET | 200 | 2.16.202.115:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgO3QtTg1eKRoR2e%2FsdgRNKuyw%3D%3D | NL | binary | 503 b | unknown |
868 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad3rm3ciqs3fjr4bc4x5vwuildeq_9.49.1/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.49.1_all_ixzyrcu7pvmgu5pjv6enfqq6wa.crx3 | US | binary | 11.7 Kb | unknown |
868 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acf5iuk6pnjlc6lnxtqm5ki6eoqq_112.300.200/gkmgaooipdjhmangpemjhigmamcehddo_112.300.200_win_aclnpjhtsv44pze3qmxsxb7fq66q.crx3 | US | binary | 5.51 Kb | unknown |
868 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYWM3QUFZQV9zN2JXZFNHTWhCbGtIMVUwdw/1.0.0.14_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | US | binary | 34.2 Kb | unknown |
868 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/fzrp6xpdtqq2vakspwulwu2yae_62/khaoiebndkojlmppeemjhbpbandiljpe_62_win_n2jkzx33j3rlsltywormztyyby.crx3 | US | binary | 2.83 Kb | unknown |
868 | svchost.exe | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYWM3QUFZQV9zN2JXZFNHTWhCbGtIMVUwdw/1.0.0.14_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | US | binary | 2.83 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2740 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3592 | chrome.exe | 66.102.1.84:443 | accounts.google.com | GOOGLE | US | unknown |
3592 | chrome.exe | 52.42.15.177:80 | www.4kdownload.com | AMAZON-02 | US | unknown |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3592 | chrome.exe | 52.42.15.177:443 | www.4kdownload.com | AMAZON-02 | US | unknown |
3592 | chrome.exe | 142.250.184.202:443 | fonts.googleapis.com | GOOGLE | US | whitelisted |
3592 | chrome.exe | 172.217.16.195:443 | fonts.gstatic.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
www.4kdownload.com |
| unknown |
fonts.googleapis.com |
| whitelisted |
static.4kdownload.com |
| unknown |
fonts.gstatic.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
cdn.jsdelivr.net |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
script.tapfiliate.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |