| File name: | 16.rar |
| Full analysis: | https://app.any.run/tasks/d9db1023-ab6a-41f0-8bcb-3372d682376b |
| Verdict: | Malicious activity |
| Analysis date: | April 23, 2019, 20:55:53 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
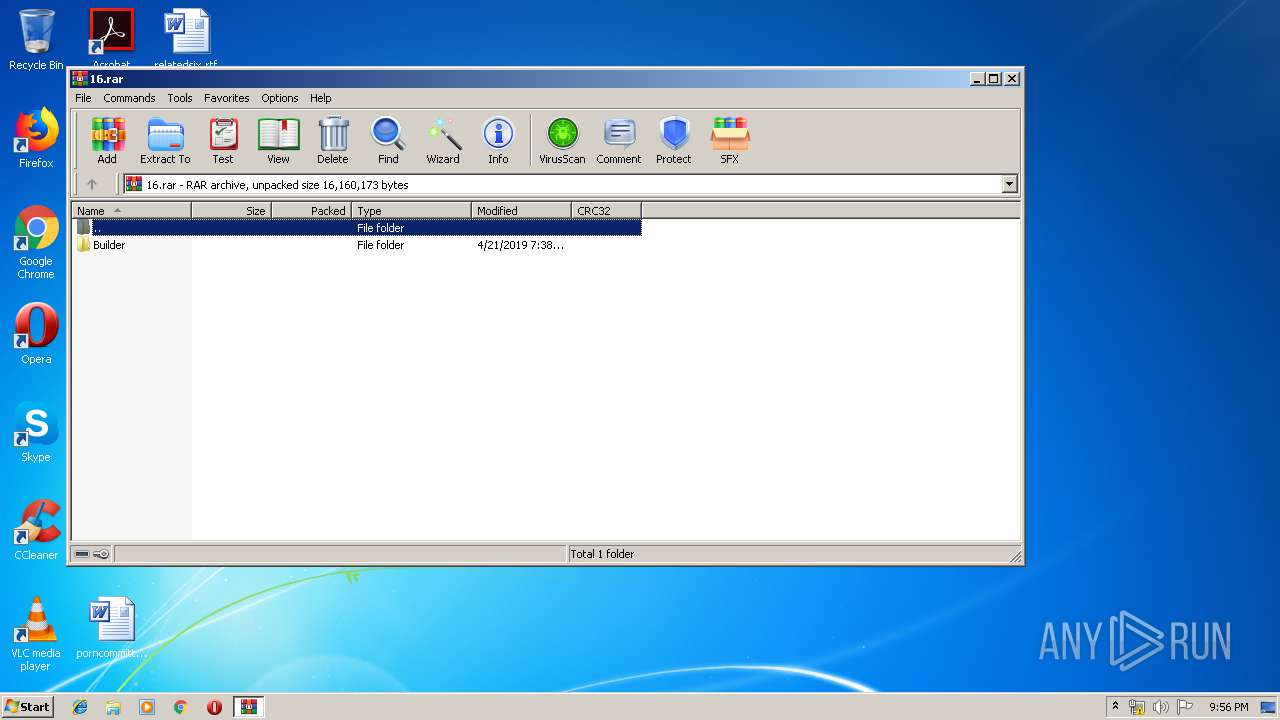
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 4D60BA3D2B25591BD08FBFCC179CDFB6 |
| SHA1: | 59D7DA25146D766FF145DE73A38D439E5F4FD470 |
| SHA256: | B3A87B559DC111E33758034697471580D4E8C50EC1C7E7EF359A32B917FCC422 |
| SSDEEP: | 196608:BqefkrbfJQls7/vl7SCYte9RFSpSeKFm9/B/5A51+15FXY3BOUO9Fk:IN3BQls7XJSxtoR/k9/c51mroa3k |
MALICIOUS
Application was dropped or rewritten from another process
- Ransomware Builder V3 Release.exe (PID: 392)
- ARMIK.EXE (PID: 3848)
- ARM1K.EXE (PID: 832)
Changes the autorun value in the registry
- Ransomware Builder V3 Release.exe (PID: 392)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 2420)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 1452)
Loads dropped or rewritten executable
- ARM1K.EXE (PID: 832)
SUSPICIOUS
Executable content was dropped or overwritten
- Ransomware Builder V3 Release.exe (PID: 392)
- ARM1K.EXE (PID: 832)
- WinRAR.exe (PID: 1136)
Starts itself from another location
- Ransomware Builder V3 Release.exe (PID: 392)
Starts CMD.EXE for commands execution
- ARMIK.EXE (PID: 3848)
Reads the BIOS version
- ARM1K.EXE (PID: 832)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
40
Monitored processes
6
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
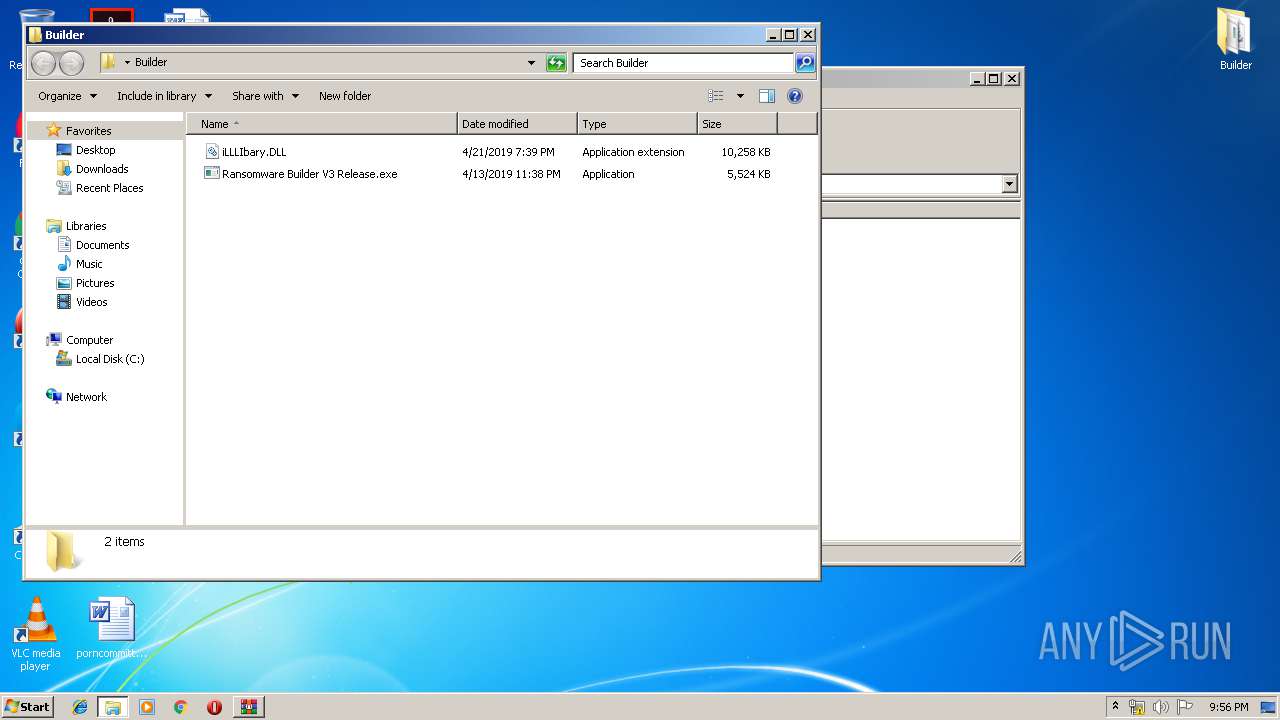
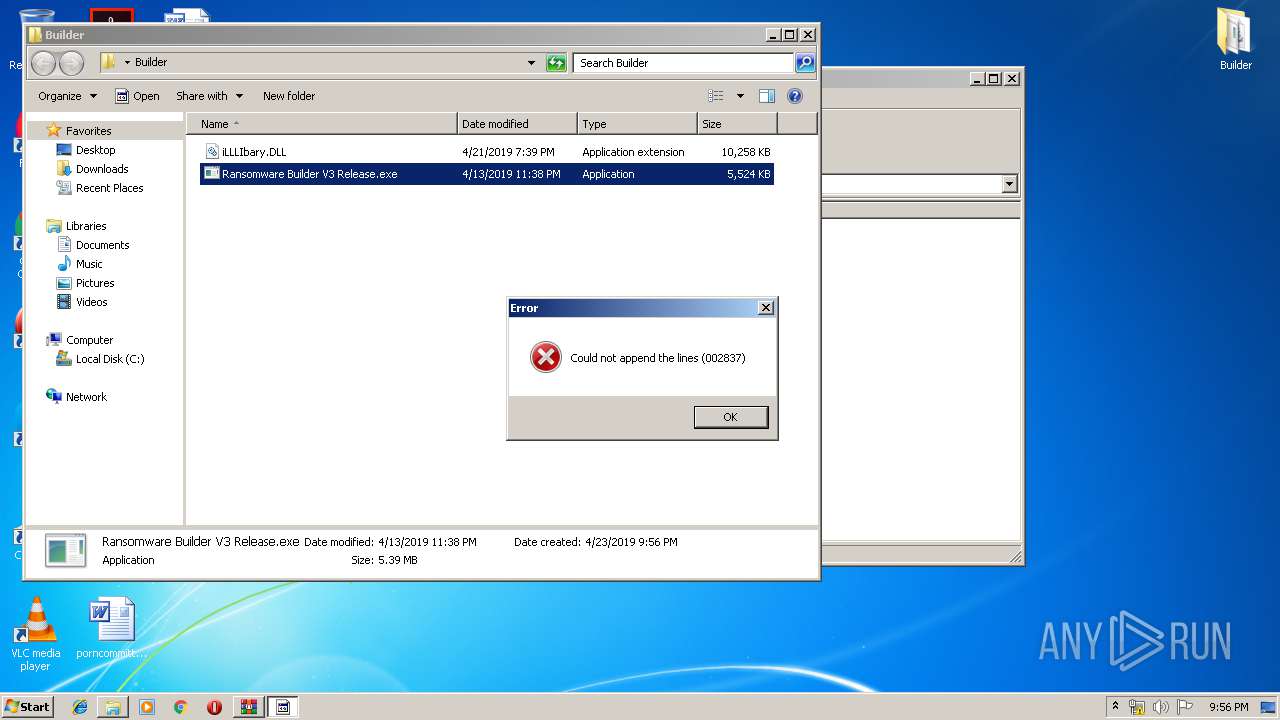
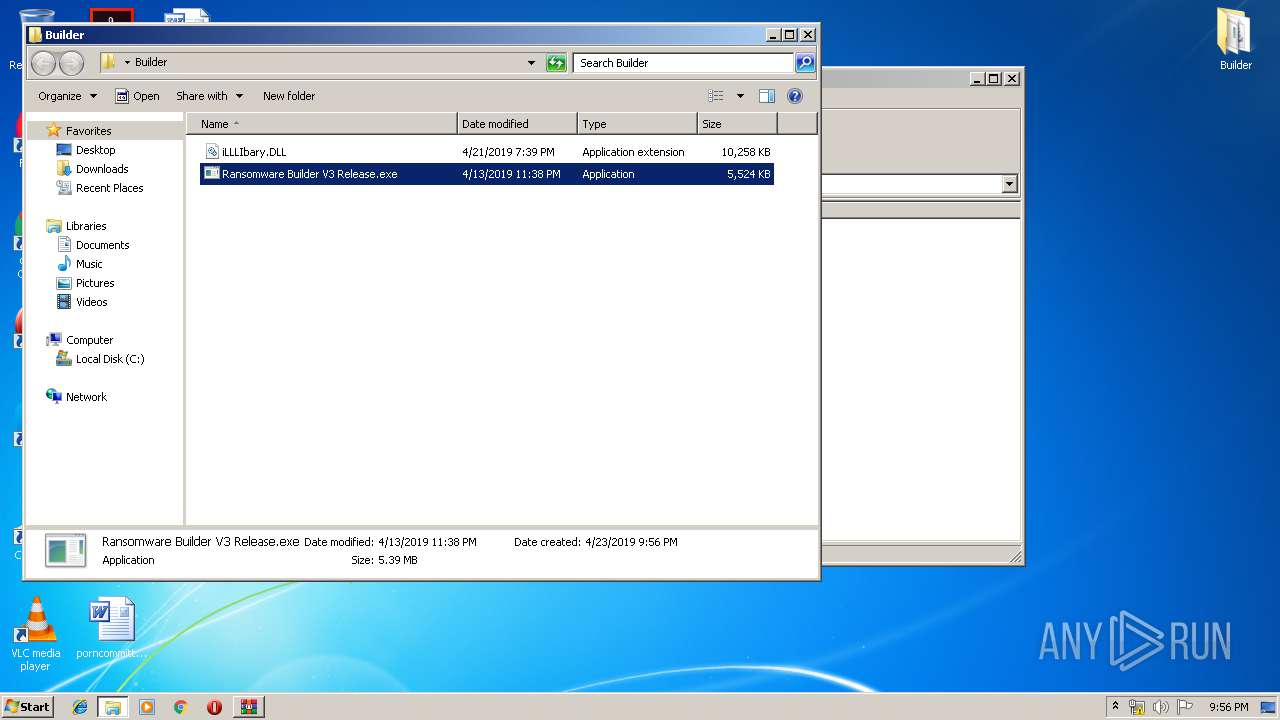
| 392 | "C:\Users\admin\Desktop\Builder\Ransomware Builder V3 Release.exe" | C:\Users\admin\Desktop\Builder\Ransomware Builder V3 Release.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Integrity Level: MEDIUM Description: CrashLog Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 832 | "C:\Users\admin\AppData\Local\Temp\ARM1K.EXE" | C:\Users\admin\AppData\Local\Temp\ARM1K.EXE | Ransomware Builder V3 Release.exe | ||||||||||||
User: admin Company: Microsoft Integrity Level: MEDIUM Description: ShootFramework Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
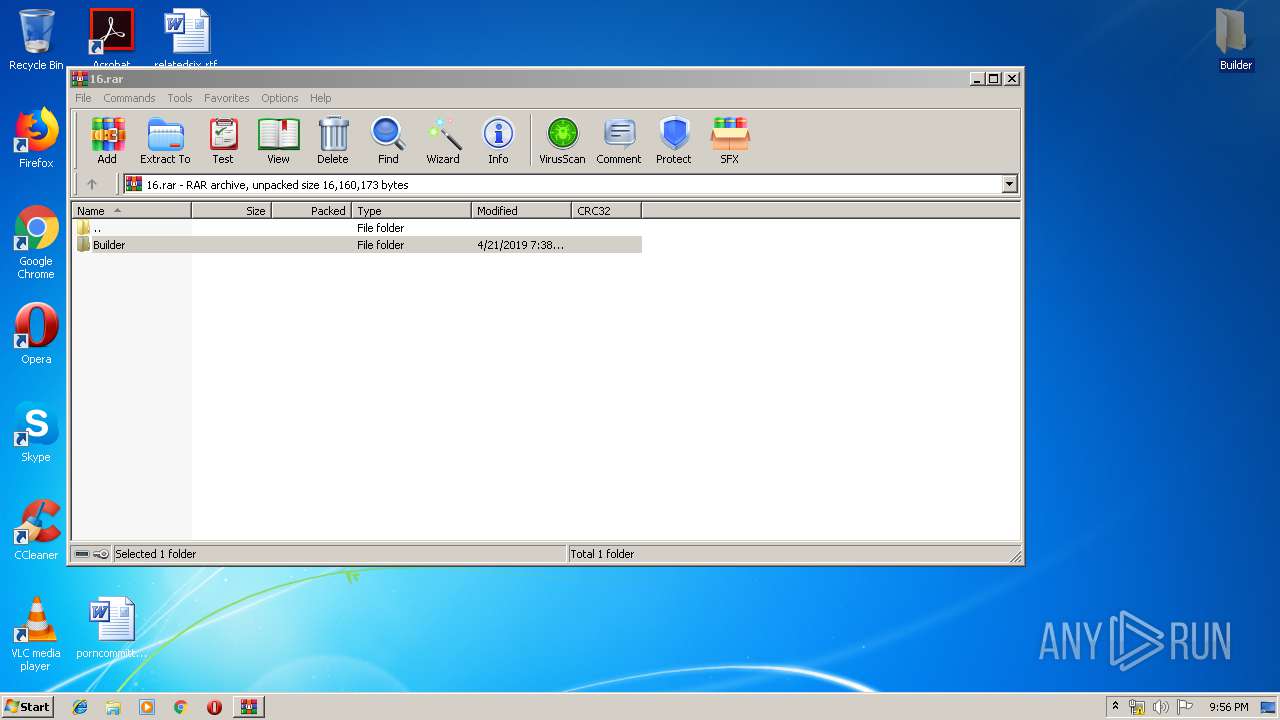
| 1136 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\16.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 1452 | SCHTASKS.exe /DELETE /TN svhost /F | C:\Windows\system32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2420 | "C:\Windows\System32\cmd.exe" /C SCHTASKS.exe /DELETE /TN svhost /F | C:\Windows\System32\cmd.exe | — | ARMIK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3848 | "C:\Users\admin\AppData\Local\Temp\ARMIK.EXE" | C:\Users\admin\AppData\Local\Temp\ARMIK.EXE | — | Ransomware Builder V3 Release.exe | |||||||||||
User: admin Company: Microsoft Integrity Level: MEDIUM Description: CrashLog Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
871
Read events
854
Write events
17
Delete events
0
Modification events
| (PID) Process: | (1136) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1136) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1136) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1136) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\16.rar | |||
| (PID) Process: | (1136) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1136) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1136) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1136) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (392) Ransomware Builder V3 Release.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Winit Updater |
Value: "C:\Users\admin\AppData\Local\Temp\ARMIK.EXE" | |||
| (PID) Process: | (392) Ransomware Builder V3 Release.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
5
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1136 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1136.1045\Builder\Ransomware Builder V3 Release.exe | executable | |
MD5:— | SHA256:— | |||
| 1136 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1136.1045\Builder\iLLLIbary.DLL | executable | |
MD5:— | SHA256:— | |||
| 392 | Ransomware Builder V3 Release.exe | C:\Users\admin\AppData\Local\Temp\ARM1K.EXE | executable | |
MD5:— | SHA256:— | |||
| 392 | Ransomware Builder V3 Release.exe | C:\Users\admin\AppData\Local\Temp\ARMIK.EXE | executable | |
MD5:— | SHA256:— | |||
| 832 | ARM1K.EXE | C:\Users\admin\AppData\Local\Temp\a235f6ef-754a-4fdb-a5b7-f666812c1580\AgileDotNetRT.dll | executable | |
MD5:2D86C4AD18524003D56C1CB27C549BA8 | SHA256:091AB8A1ACDAB40C544BD1E5C91A96881ACC318CAC4DF5235E1B5673F5489280 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report